International Conference on Data and Software Engineering
VerifiedAdded on 2022/09/02
|13
|2788
|19
AI Summary
Contribute Materials
Your contribution can guide someone’s learning journey. Share your
documents today.

Running head: UNDERSTANDING WORDPRESS CVE-2019-17669
Understanding WordPress CVE-2019-17669
Name of the student:
Name of the university:
Author Note
Understanding WordPress CVE-2019-17669
Name of the student:
Name of the university:
Author Note
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
1UNDERSTANDING WORDPRESS CVE-2019-17669
Executive summary
A kind of critical vulnerability has been there in WordPress till 5.2.3. This has influenced the aspects
that are the unknown functionality regarding the elements of URL Handlers. Apart from that, this
manipulation with different unknown inputs leads to SSRF or the vulnerability of privilege
escalation. This CWE has been put under the category of the issues as CWE-918. This can have the
impact of integrity, confidentiality and availability. In this study, there is a description of various
complex issues with technical and business problems with the evaluation of CVE-2019-17669 and
solutions to the exploit. Apart from that future importance and capabilities of CVE-2019-17669 are
assessed here.
Executive summary
A kind of critical vulnerability has been there in WordPress till 5.2.3. This has influenced the aspects
that are the unknown functionality regarding the elements of URL Handlers. Apart from that, this
manipulation with different unknown inputs leads to SSRF or the vulnerability of privilege
escalation. This CWE has been put under the category of the issues as CWE-918. This can have the
impact of integrity, confidentiality and availability. In this study, there is a description of various
complex issues with technical and business problems with the evaluation of CVE-2019-17669 and
solutions to the exploit. Apart from that future importance and capabilities of CVE-2019-17669 are
assessed here.
2UNDERSTANDING WORDPRESS CVE-2019-17669
Table of Contents
Introduction:..........................................................................................................................................3
Description of Wordpress:.....................................................................................................................3
Demonstrating of CVE-2019-17669:....................................................................................................5
Assessment of the likely future effectiveness and importance of CVE-2019-17669:...........................8
Conclusion:............................................................................................................................................8
References:..........................................................................................................................................10
Table of Contents
Introduction:..........................................................................................................................................3
Description of Wordpress:.....................................................................................................................3
Demonstrating of CVE-2019-17669:....................................................................................................5
Assessment of the likely future effectiveness and importance of CVE-2019-17669:...........................8
Conclusion:............................................................................................................................................8
References:..........................................................................................................................................10
3UNDERSTANDING WORDPRESS CVE-2019-17669
Introduction:
A critical vulnerability is seen in WordPress till 5.2.3. The affected thing was an unknown
functionality related to a component URL Handler. Further, the manipulation with unknown input
gives rise to the SSRF or privilege escalation vulnerability. The CWE has been categorization the
problem as CWE-918. It is going to have an effect on availability, integrity and confidentiality. This
weakness has been shown during 10/17/2019. The vulnerability has been traded as the CVE-109-
1669 FROM 10/1/2019. This exportability has been revealed to be simple. An attack can be
launched here remotely. Moreover, exploitation has never needed any type of authentication. Again,
the technical details have been unknown and the exploit has never been available. Here, the structure
of that vulnerably has been defining the probable price range of 0 to 5k USD dollars at that time.
This up-gradation to version 5.2.4 eradicates the vulnerability. The following report describes the
different critical problems along with the business or technical issues for CVE-2019-17669.
Moreover, its future potentials are also discussed in this evaluation.
Description of Wordpress:
The WordPress is a popular free content management system. This is utilized for creating
and maintaining different websites. It is easy to use and has distinct features of blogging. This helps
become the most popular tool for blogging over the Internet. It delivers the web-based user interface
to update, publish and design sites (Rodas-Silva et al. 2019). Rather than writing in HTML, one
might easily opt for various templates or theme over the websites consisting of the designs liked by
users. Moreover, one can change the layout and create any custom bar for navigation. As the layout
of the site is finished, one can utilize the online interface of WordPress for generating individual
pages. Every page comprises of formatted texts, images, links and additional media (Messenlehner
Introduction:
A critical vulnerability is seen in WordPress till 5.2.3. The affected thing was an unknown
functionality related to a component URL Handler. Further, the manipulation with unknown input
gives rise to the SSRF or privilege escalation vulnerability. The CWE has been categorization the
problem as CWE-918. It is going to have an effect on availability, integrity and confidentiality. This
weakness has been shown during 10/17/2019. The vulnerability has been traded as the CVE-109-
1669 FROM 10/1/2019. This exportability has been revealed to be simple. An attack can be
launched here remotely. Moreover, exploitation has never needed any type of authentication. Again,
the technical details have been unknown and the exploit has never been available. Here, the structure
of that vulnerably has been defining the probable price range of 0 to 5k USD dollars at that time.
This up-gradation to version 5.2.4 eradicates the vulnerability. The following report describes the
different critical problems along with the business or technical issues for CVE-2019-17669.
Moreover, its future potentials are also discussed in this evaluation.
Description of Wordpress:
The WordPress is a popular free content management system. This is utilized for creating
and maintaining different websites. It is easy to use and has distinct features of blogging. This helps
become the most popular tool for blogging over the Internet. It delivers the web-based user interface
to update, publish and design sites (Rodas-Silva et al. 2019). Rather than writing in HTML, one
might easily opt for various templates or theme over the websites consisting of the designs liked by
users. Moreover, one can change the layout and create any custom bar for navigation. As the layout
of the site is finished, one can utilize the online interface of WordPress for generating individual
pages. Every page comprises of formatted texts, images, links and additional media (Messenlehner
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
4UNDERSTANDING WORDPRESS CVE-2019-17669
and Coleman 2019). One is able to publish the webpages completed or updates of blogs through a
simple click on the publish button. Its interface makes that simple for people despite experience of
web development for publishing and creating any site. The blogging tools deliver the easy way for
tracking distinct visitors, user comments and individual posts. The built-in capabilities of Word
Press are never enough for the needs (Jones 2018). Here, one must install a distinct type of plug-ins
providing additional features. Instances of that are web forum tools, image galleries and social media
buttons. As there are many WordPress templates and available plug-ins, the system also has some
drawbacks. This, being a template-based system, one must start with the pre-built site instead of
developing different pages from scratch. Moreover, one might never include the scripts and then
maintain database having similar control level offered by the custom website. Thus a maximum of
the business and huge companies have been still hand-coding the sites and developing them through
WYSIWYG editor such as Dreamweaver (Nurmi 2018). One of its usage lies in e-commerce. One
requires the tool for adding e-commerce functionality to WordPress like product pages, payment
gateways and carts. Many options are there (Perry 2018). Nevertheless, WordPress one of the
standout choice for maximum users. The Installing of the plugins adds much as require to develop
the store and sell products with WordPress. Through the WordCommerce one might search for the
dedicated theme for e-commerce. It is essential for various stores due to its multipurpose and default
choices that are never suited for e-commerce (Jones 2018). Additionally, as one run the parallel
website, one requires the theme integrating the couple aspects in smooth manner. Next, there is a
reliable solution for security. Here, the selling of services or products for the online necessitates
handling the sensitive data for customers. As WordPress is secured inherently, one can gain
advantages from including security to the store as much as possible. Here, Jetpack is a smart option
since this is a dedicated type of security plugin such as Wordfence (Lassila 2016). Besides, one must
assure to pick the host of WordPress, making that simple to utilize HTTPS. Lastly, there is a built-in
and Coleman 2019). One is able to publish the webpages completed or updates of blogs through a
simple click on the publish button. Its interface makes that simple for people despite experience of
web development for publishing and creating any site. The blogging tools deliver the easy way for
tracking distinct visitors, user comments and individual posts. The built-in capabilities of Word
Press are never enough for the needs (Jones 2018). Here, one must install a distinct type of plug-ins
providing additional features. Instances of that are web forum tools, image galleries and social media
buttons. As there are many WordPress templates and available plug-ins, the system also has some
drawbacks. This, being a template-based system, one must start with the pre-built site instead of
developing different pages from scratch. Moreover, one might never include the scripts and then
maintain database having similar control level offered by the custom website. Thus a maximum of
the business and huge companies have been still hand-coding the sites and developing them through
WYSIWYG editor such as Dreamweaver (Nurmi 2018). One of its usage lies in e-commerce. One
requires the tool for adding e-commerce functionality to WordPress like product pages, payment
gateways and carts. Many options are there (Perry 2018). Nevertheless, WordPress one of the
standout choice for maximum users. The Installing of the plugins adds much as require to develop
the store and sell products with WordPress. Through the WordCommerce one might search for the
dedicated theme for e-commerce. It is essential for various stores due to its multipurpose and default
choices that are never suited for e-commerce (Jones 2018). Additionally, as one run the parallel
website, one requires the theme integrating the couple aspects in smooth manner. Next, there is a
reliable solution for security. Here, the selling of services or products for the online necessitates
handling the sensitive data for customers. As WordPress is secured inherently, one can gain
advantages from including security to the store as much as possible. Here, Jetpack is a smart option
since this is a dedicated type of security plugin such as Wordfence (Lassila 2016). Besides, one must
assure to pick the host of WordPress, making that simple to utilize HTTPS. Lastly, there is a built-in
5UNDERSTANDING WORDPRESS CVE-2019-17669
functionality of backup. The store must be consistently changing and collecting the latest data. Here,
a slid tool for backup is the must. This is helpful never to risk losing any sort of information.
However, it is fortunate that many WordPress backup plugins are there up to that task (Silaen and
Lim 2016).
Demonstrating of CVE-2019-17669:
The vulnerability s modified from the time it was assessed last by NVD. This is a type of
awaiting reanalysis resulting in future modifications to the provided information. At present
WordPress prior 5.2.4 comprise of SSRF of Server Side Request Forgery vulnerability (Nackerud
and McCready 2016). This is due to the fact the validation of URL never considered the
interpretation as per the names as the series of hexadecimal characters. Further, the vulnerability has
permitted the distant attackers in executing the arbitrary code on the vulnerable installations of the
“Foxer Reader 9.2.0.9297” (Jacob 2018). Moreover, the interaction of the users is needed for
exploiting the vulnerability in the way that the target can access the malicious page and open the
malicious file. Furthermore, the particular flaw is there under the controlling as per the property
name of the XFA project. Here, the challenges come out from lack to validate the presence of an
object from before for performing the activities on that object. Again, the attackers are able to
leverage vulnerabilities in executing codes under the context of the present process (Zhang 2018).
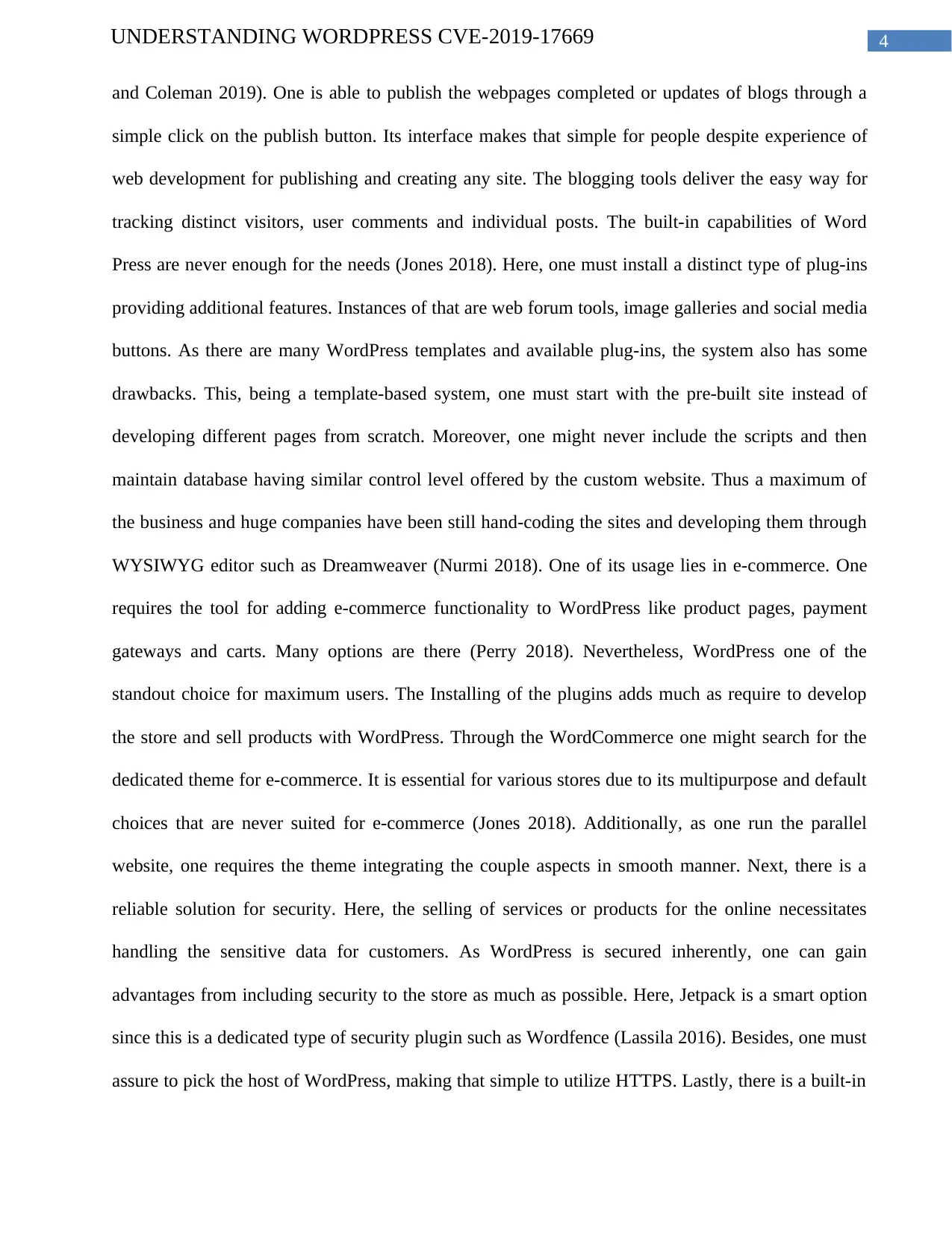
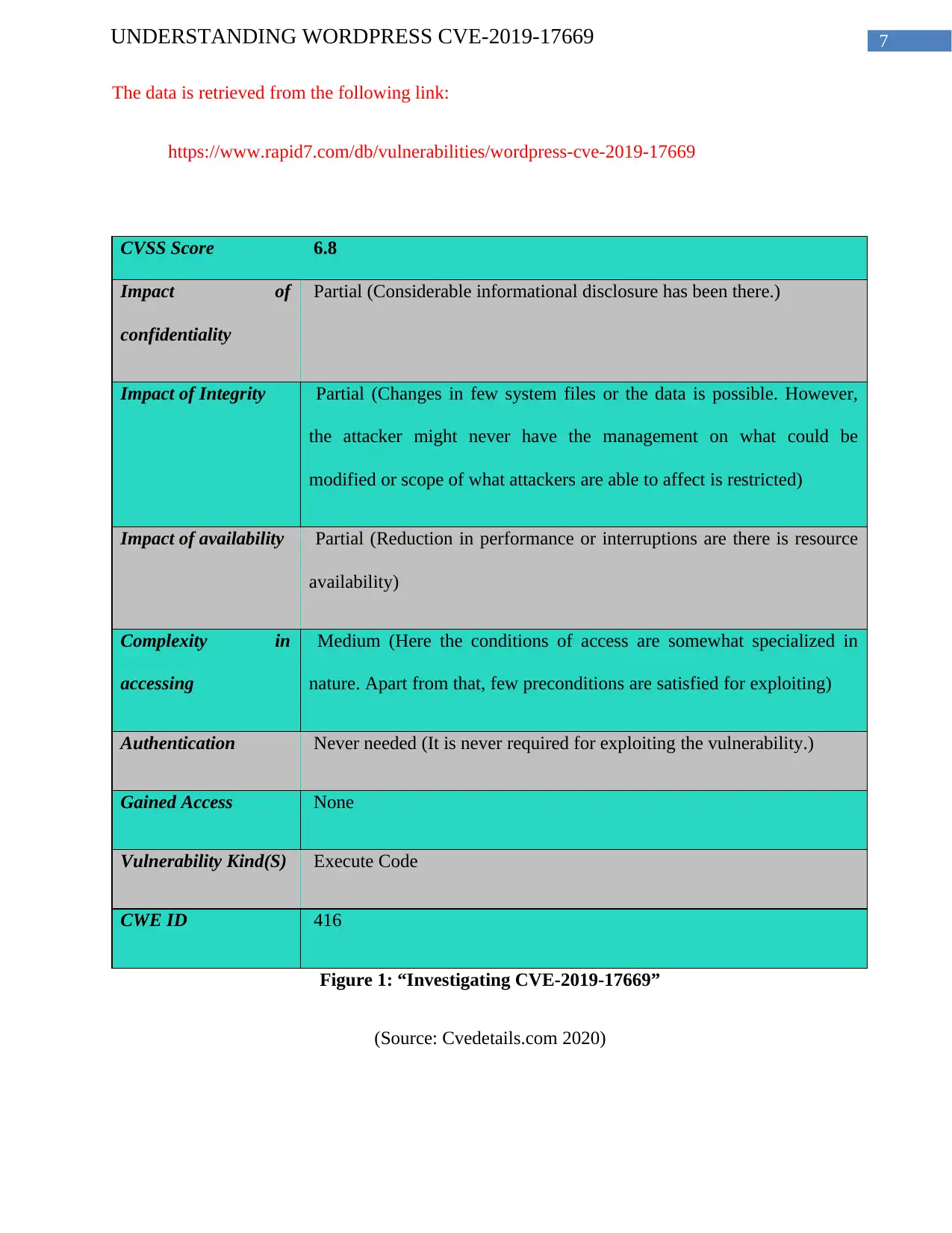
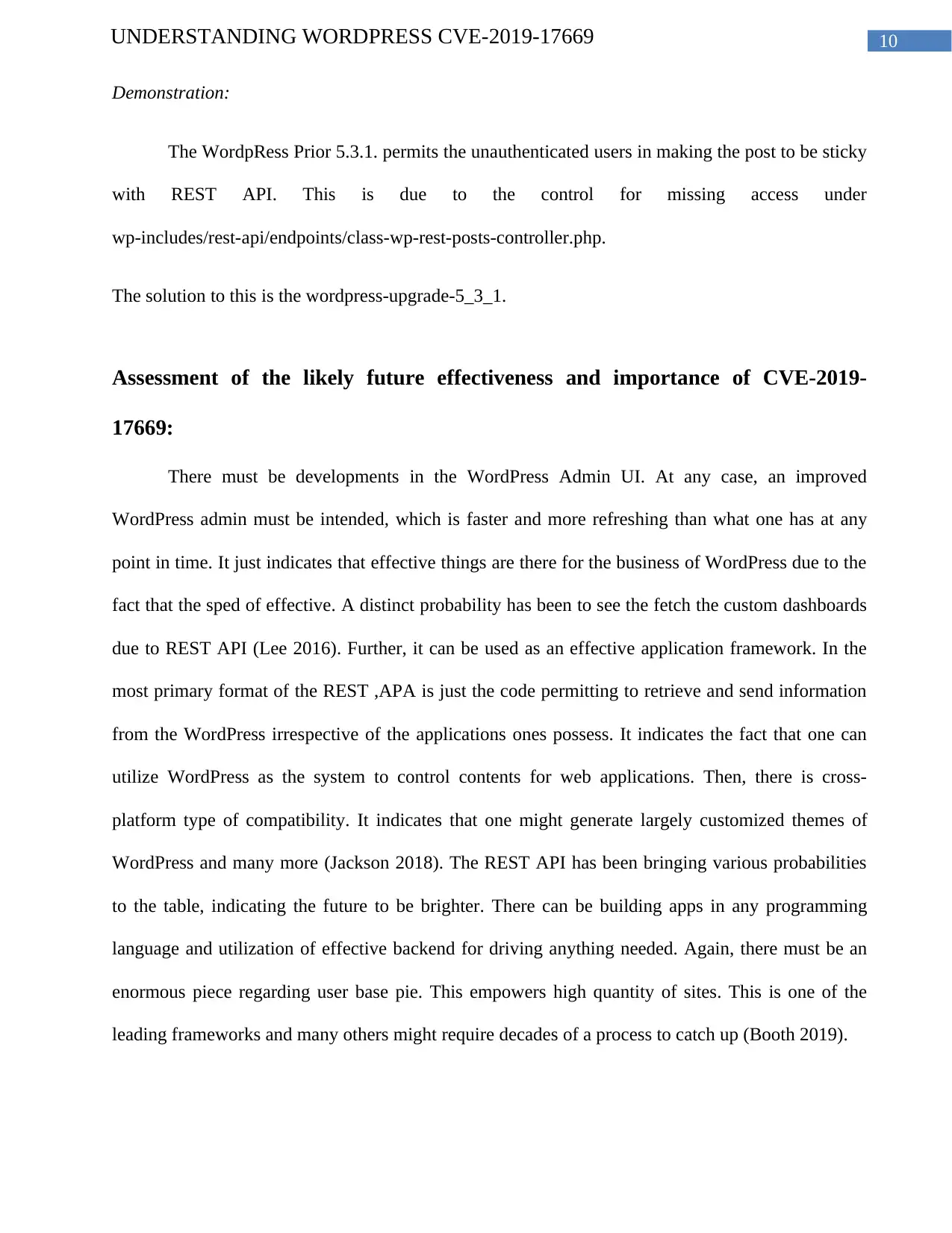
In the following table the data retrieved from the case of WordPress till5.2.3 URL Server-
Side Request Forgery is highlighted. Here, the vulnerability categorized critical is seen from
WordPress till 5.2.3 which is a type of content management system. There are some unknown
functionalities affected of the URL Handler’s component. Further, the manipulation with unknown
input results to the SSRF or privilege escalation vulnerability. As per CWE, the issue is classified as
CWE-918. Updating to version 5.2.4 eradicates the vulnerability.
functionality of backup. The store must be consistently changing and collecting the latest data. Here,
a slid tool for backup is the must. This is helpful never to risk losing any sort of information.
However, it is fortunate that many WordPress backup plugins are there up to that task (Silaen and
Lim 2016).
Demonstrating of CVE-2019-17669:
The vulnerability s modified from the time it was assessed last by NVD. This is a type of
awaiting reanalysis resulting in future modifications to the provided information. At present
WordPress prior 5.2.4 comprise of SSRF of Server Side Request Forgery vulnerability (Nackerud
and McCready 2016). This is due to the fact the validation of URL never considered the
interpretation as per the names as the series of hexadecimal characters. Further, the vulnerability has
permitted the distant attackers in executing the arbitrary code on the vulnerable installations of the
“Foxer Reader 9.2.0.9297” (Jacob 2018). Moreover, the interaction of the users is needed for
exploiting the vulnerability in the way that the target can access the malicious page and open the
malicious file. Furthermore, the particular flaw is there under the controlling as per the property
name of the XFA project. Here, the challenges come out from lack to validate the presence of an
object from before for performing the activities on that object. Again, the attackers are able to
leverage vulnerabilities in executing codes under the context of the present process (Zhang 2018).
In the following table the data retrieved from the case of WordPress till5.2.3 URL Server-
Side Request Forgery is highlighted. Here, the vulnerability categorized critical is seen from
WordPress till 5.2.3 which is a type of content management system. There are some unknown
functionalities affected of the URL Handler’s component. Further, the manipulation with unknown
input results to the SSRF or privilege escalation vulnerability. As per CWE, the issue is classified as
CWE-918. Updating to version 5.2.4 eradicates the vulnerability.

6UNDERSTANDING WORDPRESS CVE-2019-17669
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
7UNDERSTANDING WORDPRESS CVE-2019-17669
The data is retrieved from the following link:
https://www.rapid7.com/db/vulnerabilities/wordpress-cve-2019-17669
CVSS Score 6.8
Impact of
confidentiality
Partial (Considerable informational disclosure has been there.)
Impact of Integrity Partial (Changes in few system files or the data is possible. However,
the attacker might never have the management on what could be
modified or scope of what attackers are able to affect is restricted)
Impact of availability Partial (Reduction in performance or interruptions are there is resource
availability)
Complexity in
accessing
Medium (Here the conditions of access are somewhat specialized in
nature. Apart from that, few preconditions are satisfied for exploiting)
Authentication Never needed (It is never required for exploiting the vulnerability.)
Gained Access None
Vulnerability Kind(S) Execute Code
CWE ID 416
Figure 1: “Investigating CVE-2019-17669”
(Source: Cvedetails.com 2020)
The data is retrieved from the following link:
https://www.rapid7.com/db/vulnerabilities/wordpress-cve-2019-17669
CVSS Score 6.8
Impact of
confidentiality
Partial (Considerable informational disclosure has been there.)
Impact of Integrity Partial (Changes in few system files or the data is possible. However,
the attacker might never have the management on what could be
modified or scope of what attackers are able to affect is restricted)
Impact of availability Partial (Reduction in performance or interruptions are there is resource
availability)
Complexity in
accessing
Medium (Here the conditions of access are somewhat specialized in
nature. Apart from that, few preconditions are satisfied for exploiting)
Authentication Never needed (It is never required for exploiting the vulnerability.)
Gained Access None
Vulnerability Kind(S) Execute Code
CWE ID 416
Figure 1: “Investigating CVE-2019-17669”
(Source: Cvedetails.com 2020)
8UNDERSTANDING WORDPRESS CVE-2019-17669
In the above table the CVSS or Common Vulnerability Scoring System is evaluated. This
open and free industry standard has been helpful to analyze the severity of the security
vulnerabilities in the present case. The CVSS has been taking the attempt to assign the scores of
severity to the vulnerabilities. This permits the responders in prioritizing the resources and responses
as per the threat. The principle characteristics of the vulnerabilities are understood from the above
Table and a numerical score is generated that reflects the severity. Those numerical scores are
translated to qualitative representations (Nvd.nist.gov 2020). For example, in the above table the
instances of partial and medium can be understood. These are useful to assess properly and then
prioritize the process of vulnerability management.
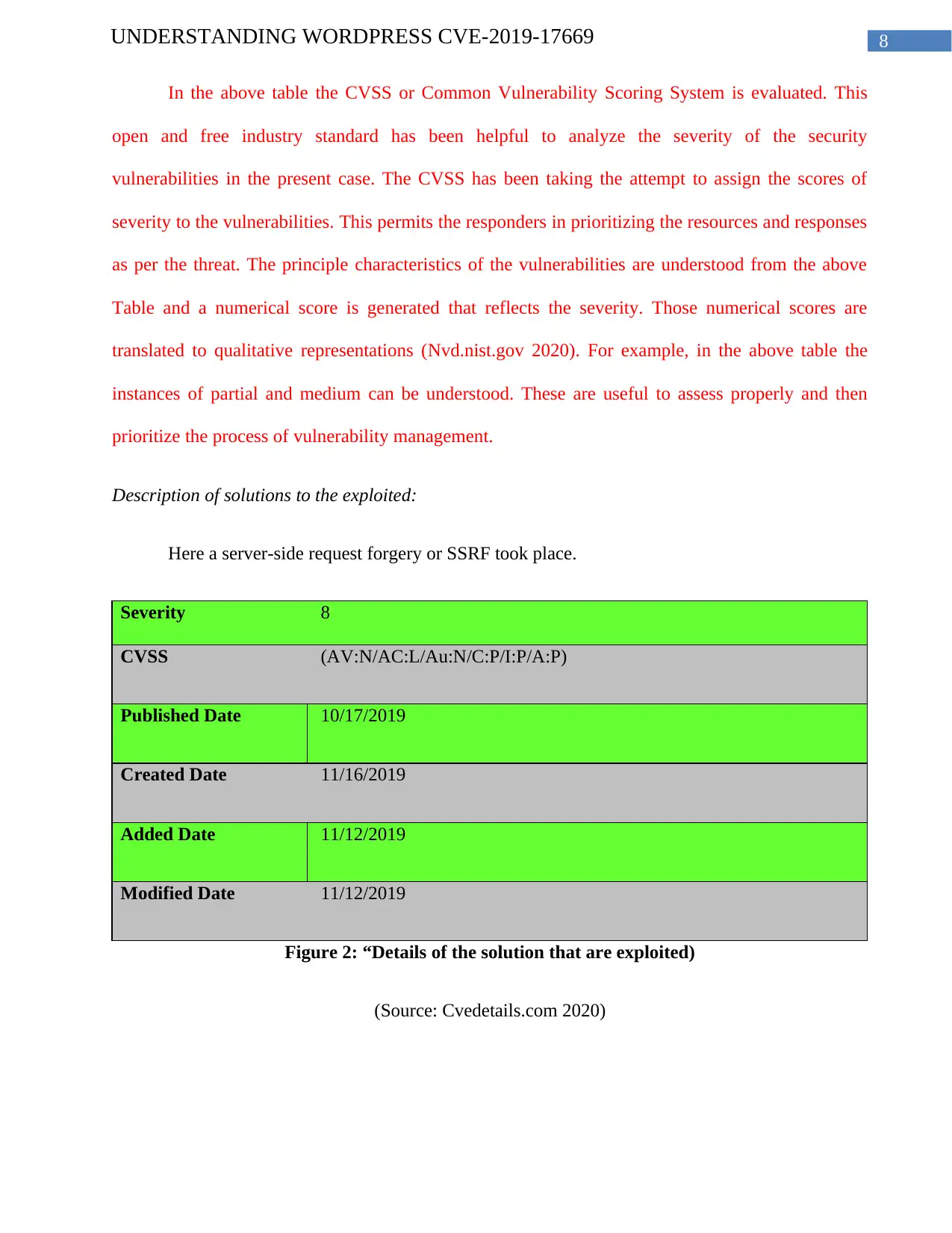
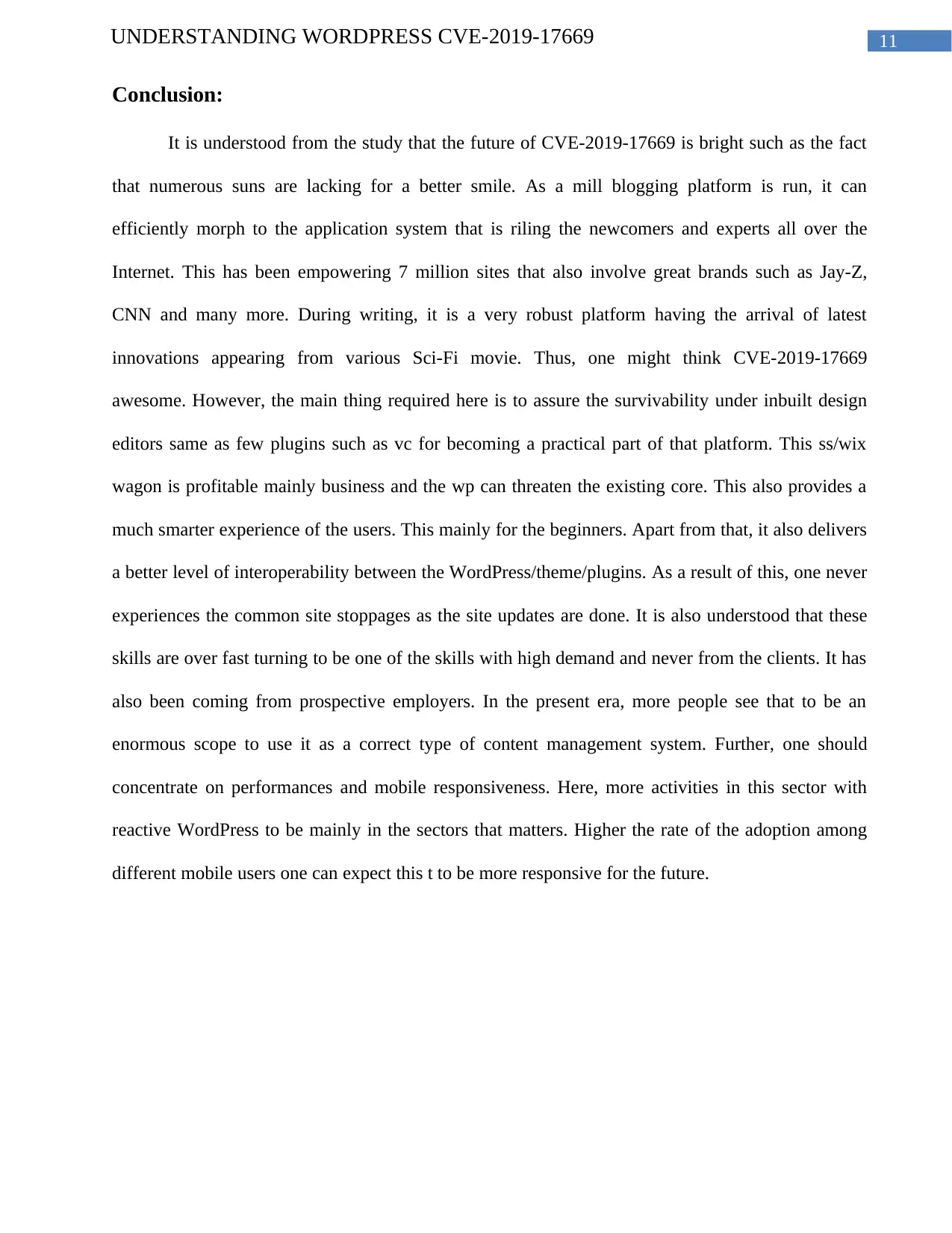
Description of solutions to the exploited:
Here a server-side request forgery or SSRF took place.
Severity 8
CVSS (AV:N/AC:L/Au:N/C:P/I:P/A:P)
Published Date 10/17/2019
Created Date 11/16/2019
Added Date 11/12/2019
Modified Date 11/12/2019
Figure 2: “Details of the solution that are exploited)
(Source: Cvedetails.com 2020)
In the above table the CVSS or Common Vulnerability Scoring System is evaluated. This
open and free industry standard has been helpful to analyze the severity of the security
vulnerabilities in the present case. The CVSS has been taking the attempt to assign the scores of
severity to the vulnerabilities. This permits the responders in prioritizing the resources and responses
as per the threat. The principle characteristics of the vulnerabilities are understood from the above
Table and a numerical score is generated that reflects the severity. Those numerical scores are
translated to qualitative representations (Nvd.nist.gov 2020). For example, in the above table the
instances of partial and medium can be understood. These are useful to assess properly and then
prioritize the process of vulnerability management.
Description of solutions to the exploited:
Here a server-side request forgery or SSRF took place.
Severity 8
CVSS (AV:N/AC:L/Au:N/C:P/I:P/A:P)
Published Date 10/17/2019
Created Date 11/16/2019
Added Date 11/12/2019
Modified Date 11/12/2019
Figure 2: “Details of the solution that are exploited)
(Source: Cvedetails.com 2020)
9UNDERSTANDING WORDPRESS CVE-2019-17669
From the above table the event of server-side forgery is understood how the attacker has
abused the server functionality. This has resulted in the manipulation and access of data in the realm
of the current server which has been otherwise never directly accessible to that attacker (Security-
database.com 2020).
From the above table the event of server-side forgery is understood how the attacker has
abused the server functionality. This has resulted in the manipulation and access of data in the realm
of the current server which has been otherwise never directly accessible to that attacker (Security-
database.com 2020).
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
10UNDERSTANDING WORDPRESS CVE-2019-17669
Demonstration:
The WordpRess Prior 5.3.1. permits the unauthenticated users in making the post to be sticky
with REST API. This is due to the control for missing access under
wp-includes/rest-api/endpoints/class-wp-rest-posts-controller.php.
The solution to this is the wordpress-upgrade-5_3_1.
Assessment of the likely future effectiveness and importance of CVE-2019-
17669:
There must be developments in the WordPress Admin UI. At any case, an improved
WordPress admin must be intended, which is faster and more refreshing than what one has at any
point in time. It just indicates that effective things are there for the business of WordPress due to the
fact that the sped of effective. A distinct probability has been to see the fetch the custom dashboards
due to REST API (Lee 2016). Further, it can be used as an effective application framework. In the
most primary format of the REST ,APA is just the code permitting to retrieve and send information
from the WordPress irrespective of the applications ones possess. It indicates the fact that one can
utilize WordPress as the system to control contents for web applications. Then, there is cross-
platform type of compatibility. It indicates that one might generate largely customized themes of
WordPress and many more (Jackson 2018). The REST API has been bringing various probabilities
to the table, indicating the future to be brighter. There can be building apps in any programming
language and utilization of effective backend for driving anything needed. Again, there must be an
enormous piece regarding user base pie. This empowers high quantity of sites. This is one of the
leading frameworks and many others might require decades of a process to catch up (Booth 2019).
Demonstration:
The WordpRess Prior 5.3.1. permits the unauthenticated users in making the post to be sticky
with REST API. This is due to the control for missing access under
wp-includes/rest-api/endpoints/class-wp-rest-posts-controller.php.
The solution to this is the wordpress-upgrade-5_3_1.
Assessment of the likely future effectiveness and importance of CVE-2019-
17669:
There must be developments in the WordPress Admin UI. At any case, an improved
WordPress admin must be intended, which is faster and more refreshing than what one has at any
point in time. It just indicates that effective things are there for the business of WordPress due to the
fact that the sped of effective. A distinct probability has been to see the fetch the custom dashboards
due to REST API (Lee 2016). Further, it can be used as an effective application framework. In the
most primary format of the REST ,APA is just the code permitting to retrieve and send information
from the WordPress irrespective of the applications ones possess. It indicates the fact that one can
utilize WordPress as the system to control contents for web applications. Then, there is cross-
platform type of compatibility. It indicates that one might generate largely customized themes of
WordPress and many more (Jackson 2018). The REST API has been bringing various probabilities
to the table, indicating the future to be brighter. There can be building apps in any programming
language and utilization of effective backend for driving anything needed. Again, there must be an
enormous piece regarding user base pie. This empowers high quantity of sites. This is one of the
leading frameworks and many others might require decades of a process to catch up (Booth 2019).
11UNDERSTANDING WORDPRESS CVE-2019-17669
Conclusion:
It is understood from the study that the future of CVE-2019-17669 is bright such as the fact
that numerous suns are lacking for a better smile. As a mill blogging platform is run, it can
efficiently morph to the application system that is riling the newcomers and experts all over the
Internet. This has been empowering 7 million sites that also involve great brands such as Jay-Z,
CNN and many more. During writing, it is a very robust platform having the arrival of latest
innovations appearing from various Sci-Fi movie. Thus, one might think CVE-2019-17669
awesome. However, the main thing required here is to assure the survivability under inbuilt design
editors same as few plugins such as vc for becoming a practical part of that platform. This ss/wix
wagon is profitable mainly business and the wp can threaten the existing core. This also provides a
much smarter experience of the users. This mainly for the beginners. Apart from that, it also delivers
a better level of interoperability between the WordPress/theme/plugins. As a result of this, one never
experiences the common site stoppages as the site updates are done. It is also understood that these
skills are over fast turning to be one of the skills with high demand and never from the clients. It has
also been coming from prospective employers. In the present era, more people see that to be an
enormous scope to use it as a correct type of content management system. Further, one should
concentrate on performances and mobile responsiveness. Here, more activities in this sector with
reactive WordPress to be mainly in the sectors that matters. Higher the rate of the adoption among
different mobile users one can expect this t to be more responsive for the future.
Conclusion:
It is understood from the study that the future of CVE-2019-17669 is bright such as the fact
that numerous suns are lacking for a better smile. As a mill blogging platform is run, it can
efficiently morph to the application system that is riling the newcomers and experts all over the
Internet. This has been empowering 7 million sites that also involve great brands such as Jay-Z,
CNN and many more. During writing, it is a very robust platform having the arrival of latest
innovations appearing from various Sci-Fi movie. Thus, one might think CVE-2019-17669
awesome. However, the main thing required here is to assure the survivability under inbuilt design
editors same as few plugins such as vc for becoming a practical part of that platform. This ss/wix
wagon is profitable mainly business and the wp can threaten the existing core. This also provides a
much smarter experience of the users. This mainly for the beginners. Apart from that, it also delivers
a better level of interoperability between the WordPress/theme/plugins. As a result of this, one never
experiences the common site stoppages as the site updates are done. It is also understood that these
skills are over fast turning to be one of the skills with high demand and never from the clients. It has
also been coming from prospective employers. In the present era, more people see that to be an
enormous scope to use it as a correct type of content management system. Further, one should
concentrate on performances and mobile responsiveness. Here, more activities in this sector with
reactive WordPress to be mainly in the sectors that matters. Higher the rate of the adoption among
different mobile users one can expect this t to be more responsive for the future.

12UNDERSTANDING WORDPRESS CVE-2019-17669
1 out of 13
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
© 2024 | Zucol Services PVT LTD | All rights reserved.