Second level Second level 7. Experimental Design First level Second level 5. Introduction First level Second level 5. References Harvad APA version 6 3
This is the highlights only not an introduction The key points of the work that you have undertaken
3 Pages5435 Words421 Views
Added on 2022-08-20
About This Document
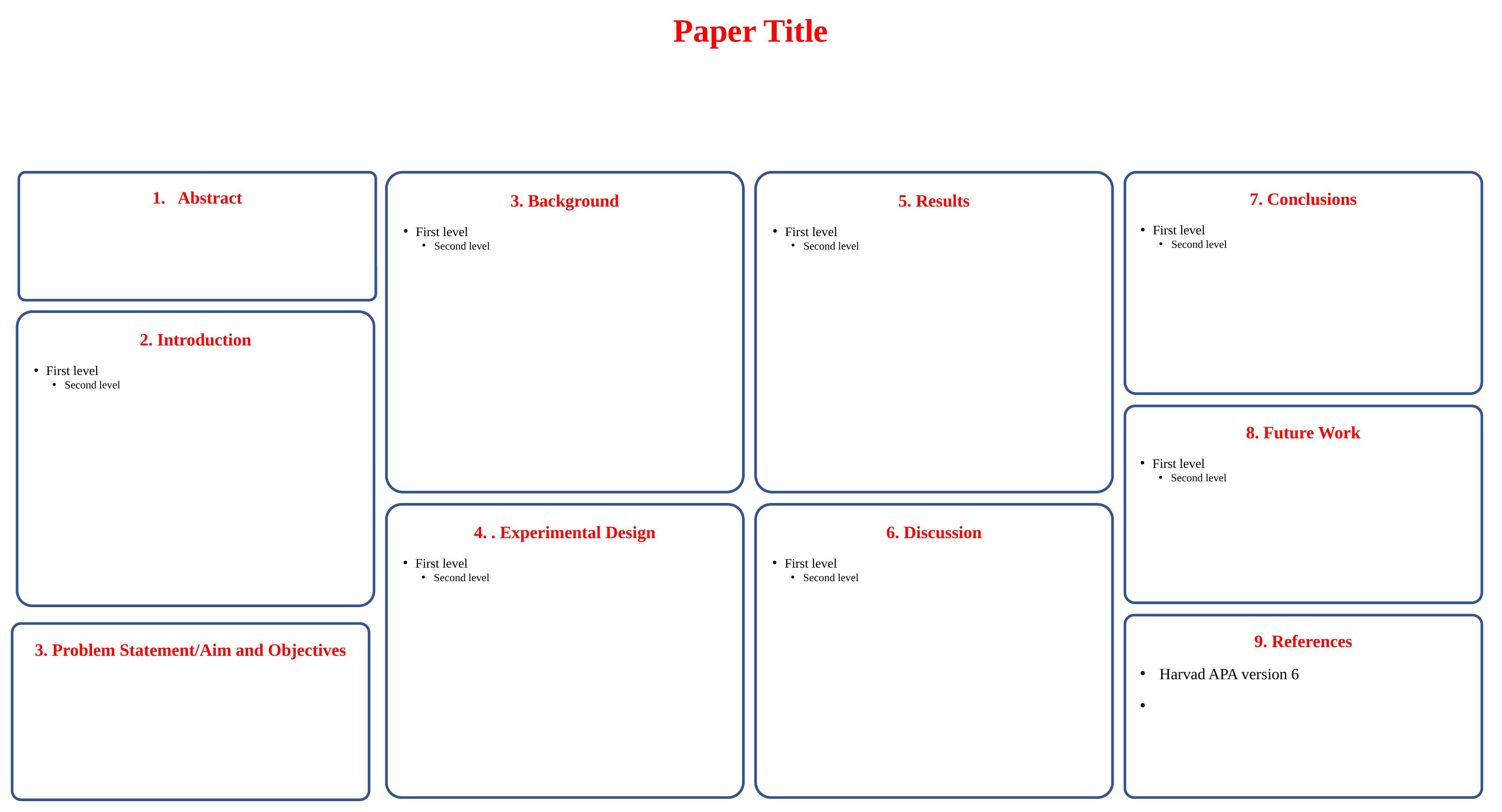
Introduction First level Second level Abstract The aim of the poster is to create an experimental design for analysing the traffic of IoT devices with the use of network monitoring tools and identify the source of data traffic. A flooding attack is performed on an IoT device and traffic is analysed for identification of the source of the attack and verification of the integrity of the evidence such that investigation can be performed. Results It can be found from the figure 3 that for the IP address of IPv4 reading 192.168.0.221 the source
Second level Second level 7. Experimental Design First level Second level 5. Introduction First level Second level 5. References Harvad APA version 6 3
This is the highlights only not an introduction The key points of the work that you have undertaken
Added on 2022-08-20
ShareRelated Documents
End of preview
Want to access all the pages? Upload your documents or become a member.