HI6008 Assignment 2: Bluetooth Security Research Report
VerifiedAdded on 2023/06/03
|14
|3034
|61
Report
AI Summary
This report delves into the realm of Bluetooth security, examining various aspects of the technology's vulnerabilities and potential threats. It begins with an abstract and an introduction to Bluetooth technology, highlighting its widespread use and susceptibility to security issues like BlueSnarfing. The project objectives focus on detailing BlueSnarfing, a common Bluetooth attack. The scope encompasses an analysis of Bluetooth vulnerabilities, including methods to improve security. The literature review summarizes past research and identifies gaps. The report then presents research questions, a research design employing a deductive approach and exploratory design, and a methodology involving secondary qualitative data analysis. Limitations, a time schedule, and a conclusion are also included, providing a comprehensive overview of Bluetooth security concerns and research approaches. The report is complete with references to support the findings.

Running head: BLUETOOTH SECURITY
Bluetooth Security
Name of the Student:
Name of the University:
Author Note:
Bluetooth Security
Name of the Student:
Name of the University:
Author Note:
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
1BLUETOOTH SECURITY
Abstract
The aim of the study is to discuss various aspects related to the security of Bluetooth technology
and its usage in various devices. The Bluetooth technology is a wireless technology that makes
use of the radio waves instead of the wires or cables. This technology has benefitted the humans
as it freed them from then hassles of wires and cables. However, this Bluetooth technology is
associated with various threats and vulnerabilities. The various methods that are used to enhance
the security of the Bluetooth technology have been discussed in the paper. The paper states the
detailed research methodology that would help to carry out the research in the right track .It is
also expected that the research would be completed within 24 weeks.
Abstract
The aim of the study is to discuss various aspects related to the security of Bluetooth technology
and its usage in various devices. The Bluetooth technology is a wireless technology that makes
use of the radio waves instead of the wires or cables. This technology has benefitted the humans
as it freed them from then hassles of wires and cables. However, this Bluetooth technology is
associated with various threats and vulnerabilities. The various methods that are used to enhance
the security of the Bluetooth technology have been discussed in the paper. The paper states the
detailed research methodology that would help to carry out the research in the right track .It is
also expected that the research would be completed within 24 weeks.
2BLUETOOTH SECURITY
Table of Contents
Abstract............................................................................................................................................1
Introduction......................................................................................................................................3
Project Objective.........................................................................................................................3
Project Scope...............................................................................................................................4
Literature Review........................................................................................................................4
Simple way to improve Bluetooth Security.............................................................................4
Analysis of the Bluetooth Security Vulnerabilities.................................................................4
Secure Connections in Bluetooth Scatternets..........................................................................5
Efficient Intrusion Detection and Prevention System for Bluetooth Networks......................6
Detection and attack on the Bluetooth -enabled Cell phones..................................................6
Research Questions......................................................................................................................6
Research Design and Methodology.............................................................................................7
Research Limitation.....................................................................................................................9
Time Schedule.............................................................................................................................9
Conclusion.....................................................................................................................................10
References......................................................................................................................................11
Table of Contents
Abstract............................................................................................................................................1
Introduction......................................................................................................................................3
Project Objective.........................................................................................................................3
Project Scope...............................................................................................................................4
Literature Review........................................................................................................................4
Simple way to improve Bluetooth Security.............................................................................4
Analysis of the Bluetooth Security Vulnerabilities.................................................................4
Secure Connections in Bluetooth Scatternets..........................................................................5
Efficient Intrusion Detection and Prevention System for Bluetooth Networks......................6
Detection and attack on the Bluetooth -enabled Cell phones..................................................6
Research Questions......................................................................................................................6
Research Design and Methodology.............................................................................................7
Research Limitation.....................................................................................................................9
Time Schedule.............................................................................................................................9
Conclusion.....................................................................................................................................10
References......................................................................................................................................11
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
3BLUETOOTH SECURITY
Introduction
The security is always a concern in all the network setup that includes wireless
connection. Since, the devices have the ability to grab the radio waves from the air, it is essential
for people to take extra precautions or measures when they use any wireless connections. It is to
be ensured that the signals do not intercept. The Bluetooth connection also involves wireless
connection and is very much susceptible to security concerns and issues like spying and remote
access (Zhang et al . 2014) .It is similar to the fact how Wi-Fi is susceptible if the network is not
secured . The Bluetooth is a wireless technology that is used for short-range communication. It
make use of the radio waves instead of the wires or cables .The Bluetooth technology finds its
application in millions of products that are being used in our daily life that includes smart phones
,laptops ,headsets and several other devices(Tao and Dai Javad 2013 ).There are several security
concerns pertaining to the use of the Bluetooth technology . Some of the concerns or issues that
are related to the Bluetooth security includes Blue jacking, Blue Bugging, car whisperer
Bluetooth attack and Blue Snarfing (Wang, Wei and Vangury 2014) .
Project Objective
The objective of this project is to discus in details about the most widely recognized and
most commonly used assault pertaining to the use of Bluetooth technology, which is Blue
Snarfing (Zhao, Zhang and Zhang 2014). The Blue Snarf are the people who are mostly
responsible for the lack of secrecy while using Bluetooth technology in the most of the products
that we use in our daily life .This shortcoming in the use of Bluetooth technology ,which is the
BlueSnarfing, will be emphasized and discussed in details .
Introduction
The security is always a concern in all the network setup that includes wireless
connection. Since, the devices have the ability to grab the radio waves from the air, it is essential
for people to take extra precautions or measures when they use any wireless connections. It is to
be ensured that the signals do not intercept. The Bluetooth connection also involves wireless
connection and is very much susceptible to security concerns and issues like spying and remote
access (Zhang et al . 2014) .It is similar to the fact how Wi-Fi is susceptible if the network is not
secured . The Bluetooth is a wireless technology that is used for short-range communication. It
make use of the radio waves instead of the wires or cables .The Bluetooth technology finds its
application in millions of products that are being used in our daily life that includes smart phones
,laptops ,headsets and several other devices(Tao and Dai Javad 2013 ).There are several security
concerns pertaining to the use of the Bluetooth technology . Some of the concerns or issues that
are related to the Bluetooth security includes Blue jacking, Blue Bugging, car whisperer
Bluetooth attack and Blue Snarfing (Wang, Wei and Vangury 2014) .
Project Objective
The objective of this project is to discus in details about the most widely recognized and
most commonly used assault pertaining to the use of Bluetooth technology, which is Blue
Snarfing (Zhao, Zhang and Zhang 2014). The Blue Snarf are the people who are mostly
responsible for the lack of secrecy while using Bluetooth technology in the most of the products
that we use in our daily life .This shortcoming in the use of Bluetooth technology ,which is the
BlueSnarfing, will be emphasized and discussed in details .
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
4BLUETOOTH SECURITY
Project Scope
From the project, the readers would be able to get the details of the vulnerabilities that are
associated with the use of Bluetooth in the present era (Cope, Campbell and Hayajneh 2017).
The project will also give the opportunity to the readers to understand the occurrence of these
different vulnerabilities and also propose the solutions pertaining to the vulnerabilities of the
Bluetooth technology. The Bluetooth technology is widely used by all the people in all parts of
the world. Almost all the products used in our daily life, make use of the Bluetooth technology. It
is foreseeable that in the future the more and more products would utilize the technology of
Bluetooth for the benefit of the people. So it is necessary for everyone to be aware of the various
security concern that are related to the Bluetooth technology usage and also it is important ne
aware of the various ways to solve the vulnerabilities associated with Bluetooth usage .
Literature Review
Simple way to improve Bluetooth Security
In the earlier assignment the it was highlighted that the security of the Bluetooth devices
can be enhanced by using simple ways .In the profiles like Advanced Auto Distribution Profile
(A2DP) , there is very little scope so for security breaches to take place (Dell and Ghori 2008) .
On the other hand for the profiles like Dial Up Network (DUN) or Sim Access Profile (SAP), the
hackers have a fair chance to breach the security of the Bluetooth devices (Yang and Wang
2014) . Thus, by using more secure profiles the breach in Bluetooth security can be avoided.
Analysis of the Bluetooth Security Vulnerabilities
Some authors used the methodology of VERDICT in order to analyze the vulnerabilities
that re present in the usage of the Bluetooth technology and the vulnerabilities associated with it .
Project Scope
From the project, the readers would be able to get the details of the vulnerabilities that are
associated with the use of Bluetooth in the present era (Cope, Campbell and Hayajneh 2017).
The project will also give the opportunity to the readers to understand the occurrence of these
different vulnerabilities and also propose the solutions pertaining to the vulnerabilities of the
Bluetooth technology. The Bluetooth technology is widely used by all the people in all parts of
the world. Almost all the products used in our daily life, make use of the Bluetooth technology. It
is foreseeable that in the future the more and more products would utilize the technology of
Bluetooth for the benefit of the people. So it is necessary for everyone to be aware of the various
security concern that are related to the Bluetooth technology usage and also it is important ne
aware of the various ways to solve the vulnerabilities associated with Bluetooth usage .
Literature Review
Simple way to improve Bluetooth Security
In the earlier assignment the it was highlighted that the security of the Bluetooth devices
can be enhanced by using simple ways .In the profiles like Advanced Auto Distribution Profile
(A2DP) , there is very little scope so for security breaches to take place (Dell and Ghori 2008) .
On the other hand for the profiles like Dial Up Network (DUN) or Sim Access Profile (SAP), the
hackers have a fair chance to breach the security of the Bluetooth devices (Yang and Wang
2014) . Thus, by using more secure profiles the breach in Bluetooth security can be avoided.
Analysis of the Bluetooth Security Vulnerabilities
Some authors used the methodology of VERDICT in order to analyze the vulnerabilities
that re present in the usage of the Bluetooth technology and the vulnerabilities associated with it .
5BLUETOOTH SECURITY
The VERDICT includes the validation, Exposure, Randomness, Deallocation, improper,
conditions and taxonomy (Hager and MidKiff 2003). The VERDICT methodology is used in
order to find the weakness in the authentication, encryption and key generation. From the
VERDICT analysis it can be concluded that the Bluetooth system that are used has
vulnerabilities in terms of the validation, unnecessary exposure and randomness. However , the
research gap has identified and raised question over the VERDICT methodology as it fails to
affirm that whether it will be able to provide solution to all the all the significant threats that are
generated from, the use of Bluetooth technology in devices .
Secure Connections in Bluetooth Scatternets
There have been some researches that suggests that the Bluetooth connections can be
secured over wireless connection in Scatternets ,The use of the scatternets arrangements was
emphasized and highlighted .The research suggests that the scatternets are the threat which
cannot be stopped from occurring pertaining to Bluetooth security and thus they cannot be
neglected (Persson and Manivannan 2003). The scatternets are formed after the accumulation of
piconets . Several investigations have been done that assesses the situation during the assault of
Bluetooth technology usage in the devices. It was confirmed that the usage of Private Area
Network (PAN) that involves the connection of gadgets or devices within the similar
arrangement and they are known as entity in the Private Area Network (Martini and Guichard
2014). It was recommended that for creation of shared connection keys ,new calculations arte to
be done .However , the research gap in the research persists as these calculations have not be
executed so the outcome of the calculations and its implementation is highly questionable .
The VERDICT includes the validation, Exposure, Randomness, Deallocation, improper,
conditions and taxonomy (Hager and MidKiff 2003). The VERDICT methodology is used in
order to find the weakness in the authentication, encryption and key generation. From the
VERDICT analysis it can be concluded that the Bluetooth system that are used has
vulnerabilities in terms of the validation, unnecessary exposure and randomness. However , the
research gap has identified and raised question over the VERDICT methodology as it fails to
affirm that whether it will be able to provide solution to all the all the significant threats that are
generated from, the use of Bluetooth technology in devices .
Secure Connections in Bluetooth Scatternets
There have been some researches that suggests that the Bluetooth connections can be
secured over wireless connection in Scatternets ,The use of the scatternets arrangements was
emphasized and highlighted .The research suggests that the scatternets are the threat which
cannot be stopped from occurring pertaining to Bluetooth security and thus they cannot be
neglected (Persson and Manivannan 2003). The scatternets are formed after the accumulation of
piconets . Several investigations have been done that assesses the situation during the assault of
Bluetooth technology usage in the devices. It was confirmed that the usage of Private Area
Network (PAN) that involves the connection of gadgets or devices within the similar
arrangement and they are known as entity in the Private Area Network (Martini and Guichard
2014). It was recommended that for creation of shared connection keys ,new calculations arte to
be done .However , the research gap in the research persists as these calculations have not be
executed so the outcome of the calculations and its implementation is highly questionable .
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
6BLUETOOTH SECURITY
Efficient Intrusion Detection and Prevention System for Bluetooth Networks
To overcome and prevent the threat to the usage of the Bluetooth technology in devices ,
two latest techniques can be used . These techniques include, Intrusion Detection and Prevention
System (Patel, Taghavi, Bakhtiyari and JúNior 2013). These two broad terms are used for the
mitigation of attacks and block new threats emerging in the Bluetooth connection of devices
(Haataja 2008). The intrusion detection system uses a reactive measure to mitigate the incoming
attacks or threats by eliminating malware and also by detecting assaults pertaining to social
engineering which manipulates the users to reveal important and confidential information (Liao,
Lin, Lin and Tung 2013). The Prevention system is proactive, method that is used for blocking
application attacks. However, the research gap persists in the research as the researcher did not
provide the comparison about the affectivity in comparison to the other frameworks or how
productive would be this method in comparison to other alternative systems.
Detection and attack on the Bluetooth -enabled Cell phones
It has been found that even in renowned and technologically advanced mobile brands like
Apple ,Samsung, LG ,Motorola and Nokia , the cell phones can be hacked by the assault of the
BlueSnarfs (Ballmann 2015) .Certain shortcomings have been identified in the Bluetooth
protocol that suggests that these Bluetooth protocols arte vulnerable to attacks (Herfurt 2004).
However the research gap persists in the research did not clearly state whether the hack was done
with authorization of the clients or without their consent, which is an unethical issue.
Research Questions
Then research questions, which have identified from the research, can be divided into two
parts. The first part consists of the primary question, which is the first research question. The
second part consists of the secondary research questions, which includes the question, numbered
Efficient Intrusion Detection and Prevention System for Bluetooth Networks
To overcome and prevent the threat to the usage of the Bluetooth technology in devices ,
two latest techniques can be used . These techniques include, Intrusion Detection and Prevention
System (Patel, Taghavi, Bakhtiyari and JúNior 2013). These two broad terms are used for the
mitigation of attacks and block new threats emerging in the Bluetooth connection of devices
(Haataja 2008). The intrusion detection system uses a reactive measure to mitigate the incoming
attacks or threats by eliminating malware and also by detecting assaults pertaining to social
engineering which manipulates the users to reveal important and confidential information (Liao,
Lin, Lin and Tung 2013). The Prevention system is proactive, method that is used for blocking
application attacks. However, the research gap persists in the research as the researcher did not
provide the comparison about the affectivity in comparison to the other frameworks or how
productive would be this method in comparison to other alternative systems.
Detection and attack on the Bluetooth -enabled Cell phones
It has been found that even in renowned and technologically advanced mobile brands like
Apple ,Samsung, LG ,Motorola and Nokia , the cell phones can be hacked by the assault of the
BlueSnarfs (Ballmann 2015) .Certain shortcomings have been identified in the Bluetooth
protocol that suggests that these Bluetooth protocols arte vulnerable to attacks (Herfurt 2004).
However the research gap persists in the research did not clearly state whether the hack was done
with authorization of the clients or without their consent, which is an unethical issue.
Research Questions
Then research questions, which have identified from the research, can be divided into two
parts. The first part consists of the primary question, which is the first research question. The
second part consists of the secondary research questions, which includes the question, numbered
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
7BLUETOOTH SECURITY
second and third. The research questions for the research pertaining to the blue tooth security are
as follows:
Primary Question
1) What are the different Bluetooth Security modes?
Secondary Questions
1) What are the common Bluetooth security issues?
2) How has BlueSnarfing become the most commonly used Bluetooth assault?
Research Design and Methodology
The research methodology is the method and process in which a particular research is
conducted in a particular way. It is of utmost importance to decide on the research methodology
even before the research takes place. This is the process of setting how the whole research will
be conducted by the researcher. The data which will be used in this research will be qualitative
secondary data. Secondary data are the information that can be found in existing researches done
by other credible researchers published in peer reviewed journals.
Research Philosophy
The research philosophy that is taken in this particular case is positivism (Ormston,
Spencer, Barnard and Snape 2014) . This theory is based on the idea that positive knowledge is
based on the phenomenon that are natural and the various relations and properties.
second and third. The research questions for the research pertaining to the blue tooth security are
as follows:
Primary Question
1) What are the different Bluetooth Security modes?
Secondary Questions
1) What are the common Bluetooth security issues?
2) How has BlueSnarfing become the most commonly used Bluetooth assault?
Research Design and Methodology
The research methodology is the method and process in which a particular research is
conducted in a particular way. It is of utmost importance to decide on the research methodology
even before the research takes place. This is the process of setting how the whole research will
be conducted by the researcher. The data which will be used in this research will be qualitative
secondary data. Secondary data are the information that can be found in existing researches done
by other credible researchers published in peer reviewed journals.
Research Philosophy
The research philosophy that is taken in this particular case is positivism (Ormston,
Spencer, Barnard and Snape 2014) . This theory is based on the idea that positive knowledge is
based on the phenomenon that are natural and the various relations and properties.
8BLUETOOTH SECURITY
Research Approach
The approach of the researcher in which he conducts the whole research and handles
every part of it is known as the research approach. The reasoning which is also known as logical
reasoning usually has two parts known as inductive approach and deductive approach. The
approach taken in this case is the deductive approach. In this particular case the research begins
with a phase of a general information and slowly it becomes concentrated into specific
information. This is known as the research approach.
Research Design
In this particular research the design will be exploratory. The exploratory research design
is particularly followed and utilized in areas where the existing researches are not very much
detailed to the core and there is a need of further exploration into the subject. where the best and
most relevant research approach, data collection methods are used this particular design of
exploratory research is utilized.
Data Collection Method
The data collection method is the method in which the information is collected from
various sources which are to be utilized in the research. Secondary data will be collected in this
particular case secondary qualitative data will be collected from the existing researches, articles,
and credible write ups about this particular topic of Bluetooth security.
Research Approach
The approach of the researcher in which he conducts the whole research and handles
every part of it is known as the research approach. The reasoning which is also known as logical
reasoning usually has two parts known as inductive approach and deductive approach. The
approach taken in this case is the deductive approach. In this particular case the research begins
with a phase of a general information and slowly it becomes concentrated into specific
information. This is known as the research approach.
Research Design
In this particular research the design will be exploratory. The exploratory research design
is particularly followed and utilized in areas where the existing researches are not very much
detailed to the core and there is a need of further exploration into the subject. where the best and
most relevant research approach, data collection methods are used this particular design of
exploratory research is utilized.
Data Collection Method
The data collection method is the method in which the information is collected from
various sources which are to be utilized in the research. Secondary data will be collected in this
particular case secondary qualitative data will be collected from the existing researches, articles,
and credible write ups about this particular topic of Bluetooth security.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
9BLUETOOTH SECURITY
Data Analysis
The collected raw information or data must be analyzed properly so that the desired
results can be got. The data analysis will be done in a thematic method, therefore thematic data
analysis will be followed in this case.
Research Limitation
During conducting the research, several limitations are faced by the researcher, which
depends on several factors. There are bound to be limitation in the research even it is well
planned and well organized. The first instance that comes with very research is that the, time
frame always becomes a hindrance and creates a problem or limitation in every research. Even
while conducting this research , the time frame has turned out to be the major problem or
limitation in this research . The other limitation that can be encountered is that few resources can
remain unavailable or inaccessible while collecting the secondary data sources required for the
research, which includes the peer viewed articles, books and journals. The other problem that
may arise while conducting the surveys in order to obtain the quantitative data is that the
response that arte obtained from the respondents might not be adequate for coming to a particular
conclusion or outcome as a result the research outcome may remain faulty or ambiguous.
However, it should be ensured that despite these limitations, the research should be planned well
and should be done in a most appropriate way so that the research is collected in a most
appropriate way.
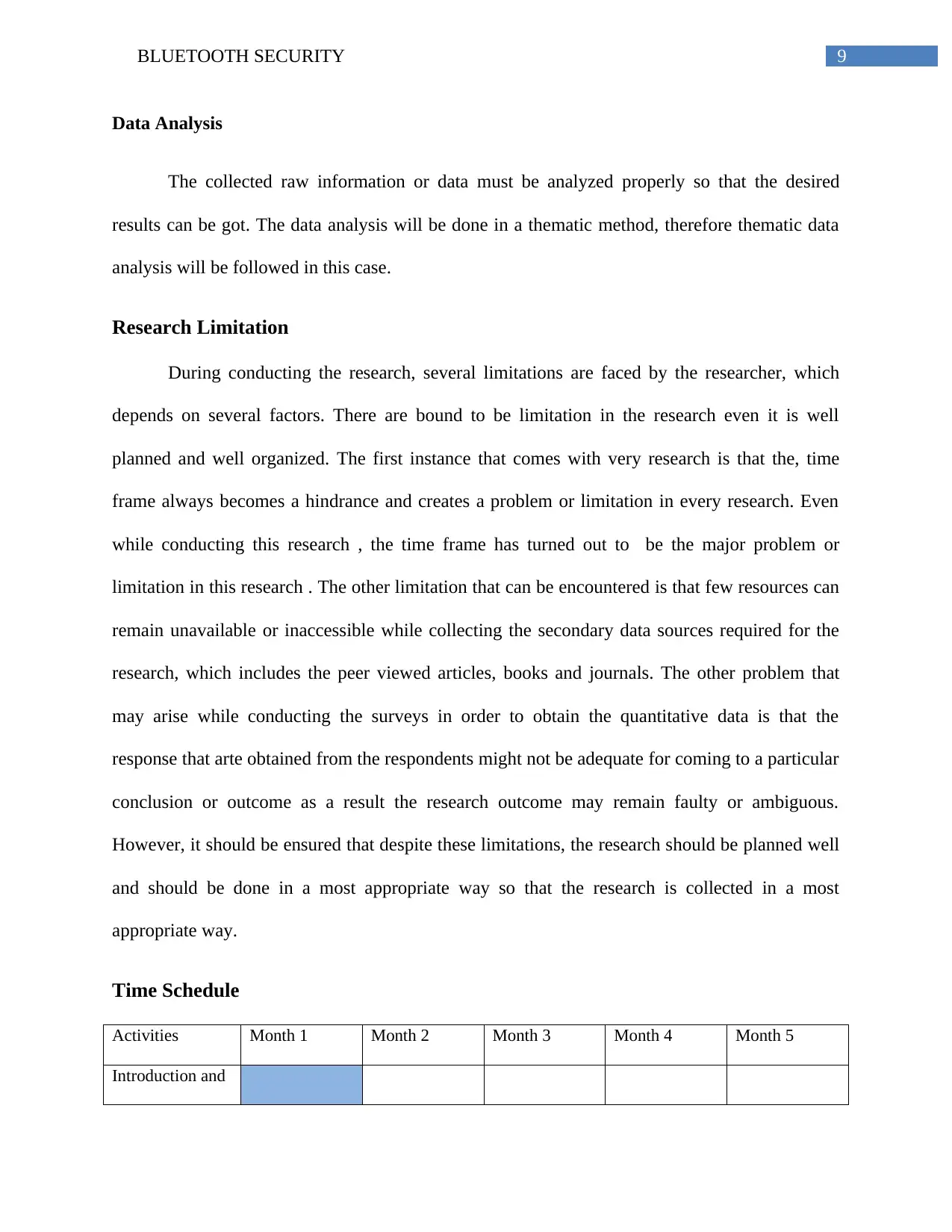
Time Schedule
Activities Month 1 Month 2 Month 3 Month 4 Month 5
Introduction and
Data Analysis
The collected raw information or data must be analyzed properly so that the desired
results can be got. The data analysis will be done in a thematic method, therefore thematic data
analysis will be followed in this case.
Research Limitation
During conducting the research, several limitations are faced by the researcher, which
depends on several factors. There are bound to be limitation in the research even it is well
planned and well organized. The first instance that comes with very research is that the, time
frame always becomes a hindrance and creates a problem or limitation in every research. Even
while conducting this research , the time frame has turned out to be the major problem or
limitation in this research . The other limitation that can be encountered is that few resources can
remain unavailable or inaccessible while collecting the secondary data sources required for the
research, which includes the peer viewed articles, books and journals. The other problem that
may arise while conducting the surveys in order to obtain the quantitative data is that the
response that arte obtained from the respondents might not be adequate for coming to a particular
conclusion or outcome as a result the research outcome may remain faulty or ambiguous.
However, it should be ensured that despite these limitations, the research should be planned well
and should be done in a most appropriate way so that the research is collected in a most
appropriate way.
Time Schedule
Activities Month 1 Month 2 Month 3 Month 4 Month 5
Introduction and
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
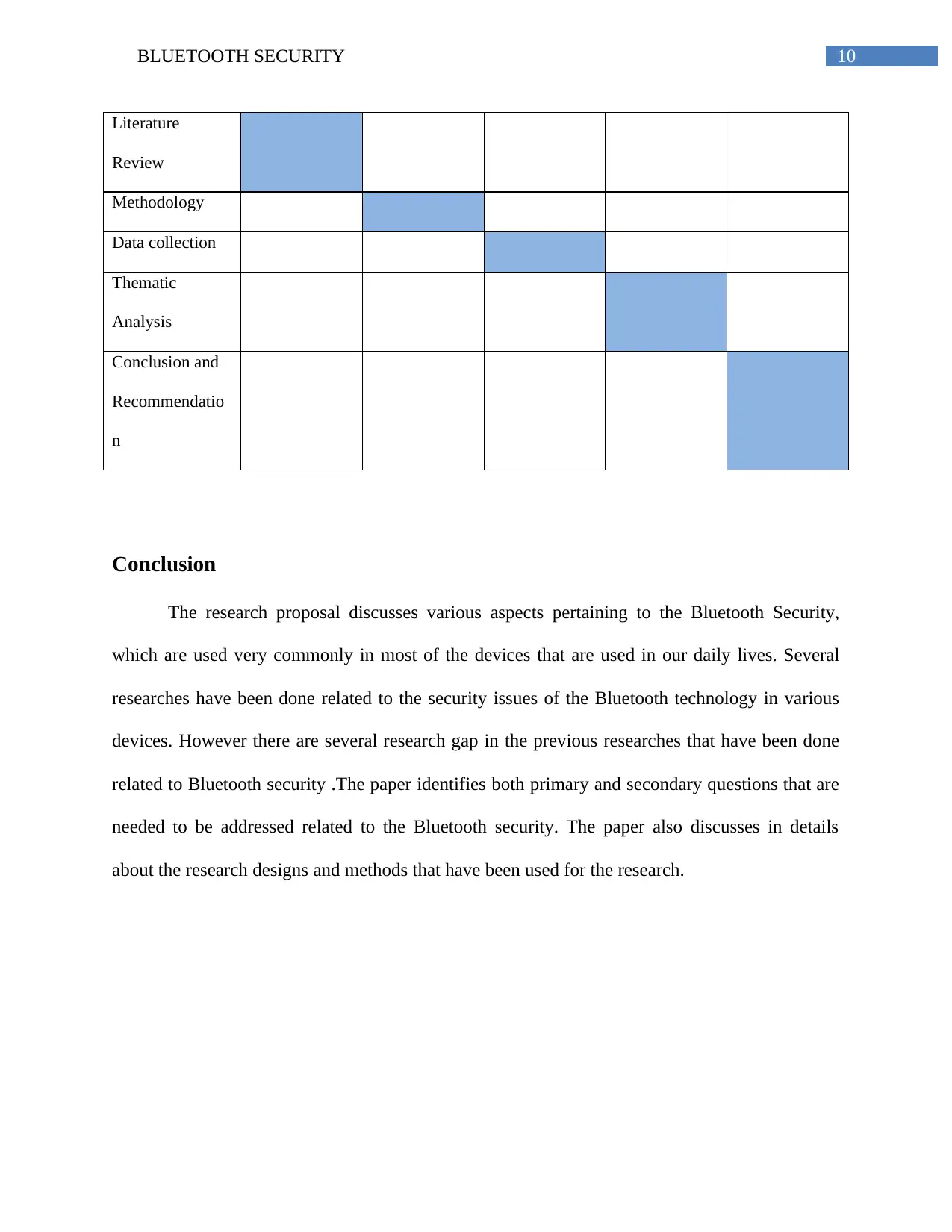
10BLUETOOTH SECURITY
Literature
Review
Methodology
Data collection
Thematic
Analysis
Conclusion and
Recommendatio
n
Conclusion
The research proposal discusses various aspects pertaining to the Bluetooth Security,
which are used very commonly in most of the devices that are used in our daily lives. Several
researches have been done related to the security issues of the Bluetooth technology in various
devices. However there are several research gap in the previous researches that have been done
related to Bluetooth security .The paper identifies both primary and secondary questions that are
needed to be addressed related to the Bluetooth security. The paper also discusses in details
about the research designs and methods that have been used for the research.
Literature
Review
Methodology
Data collection
Thematic
Analysis
Conclusion and
Recommendatio
n
Conclusion
The research proposal discusses various aspects pertaining to the Bluetooth Security,
which are used very commonly in most of the devices that are used in our daily lives. Several
researches have been done related to the security issues of the Bluetooth technology in various
devices. However there are several research gap in the previous researches that have been done
related to Bluetooth security .The paper identifies both primary and secondary questions that are
needed to be addressed related to the Bluetooth security. The paper also discusses in details
about the research designs and methods that have been used for the research.
11BLUETOOTH SECURITY
References
Ballmann, B., 2015. Feeling Bluetooth on the Tooth. In Understanding Network Hacks (pp. 137-
148). Springer, Berlin, Heidelberg.
Cope, P., Campbell, J. and Hayajneh, T., 2017, January. An investigation of Bluetooth security
vulnerabilities. In Computing and Communication Workshop and Conference (CCWC), 2017
IEEE 7th Annual (pp. 1-7). IEEE.
Dell, P. and Ghori, K.S.U.H., 2008, July. A simple way to improve the security of bluetooth
devices. In Applications and the Internet, 2008. SAINT 2008. International Symposium on(pp.
444-447). IEEE.
Haataja, K.M., 2008, February. New efficient intrusion detection and prevention system for
Bluetooth networks. In Proceedings of the 1st international conference on MOBILe Wireless
MiddleWARE, Operating Systems, and Applications(p. 16). ICST (Institute for Computer
Sciences, Social-Informatics and Telecommunications Engineering).
Hager, C.T. and MidKiff, S.F., 2003, March. An analysis of Bluetooth security vulnerabilities.
In Wireless Communications and Networking, 2003. WCNC 2003. 2003 IEEE (Vol. 3, pp. 1825-
1831). IEEE.
Herfurt, M., 2004. Detecting and Attacking bluetooth-enabled Cellphones at the Hannover
Fairground. CeBIT 2004.
References
Ballmann, B., 2015. Feeling Bluetooth on the Tooth. In Understanding Network Hacks (pp. 137-
148). Springer, Berlin, Heidelberg.
Cope, P., Campbell, J. and Hayajneh, T., 2017, January. An investigation of Bluetooth security
vulnerabilities. In Computing and Communication Workshop and Conference (CCWC), 2017
IEEE 7th Annual (pp. 1-7). IEEE.
Dell, P. and Ghori, K.S.U.H., 2008, July. A simple way to improve the security of bluetooth
devices. In Applications and the Internet, 2008. SAINT 2008. International Symposium on(pp.
444-447). IEEE.
Haataja, K.M., 2008, February. New efficient intrusion detection and prevention system for
Bluetooth networks. In Proceedings of the 1st international conference on MOBILe Wireless
MiddleWARE, Operating Systems, and Applications(p. 16). ICST (Institute for Computer
Sciences, Social-Informatics and Telecommunications Engineering).
Hager, C.T. and MidKiff, S.F., 2003, March. An analysis of Bluetooth security vulnerabilities.
In Wireless Communications and Networking, 2003. WCNC 2003. 2003 IEEE (Vol. 3, pp. 1825-
1831). IEEE.
Herfurt, M., 2004. Detecting and Attacking bluetooth-enabled Cellphones at the Hannover
Fairground. CeBIT 2004.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 14
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.




