Cloud Computing: Architecture and Deployment for Regional Gardens
VerifiedAdded on 2021/06/14
|33
|9354
|47
Report
AI Summary
This report provides a comprehensive analysis of cloud computing architectures suitable for Regional Gardens, focusing on workload distribution, dynamic scalability, resource pooling, elastic resource capability, and hybrid cloud approaches. It describes each architecture, explaining the rationale for its deployment within the context of the organization's strategic goals. The report further details the benefits of adopting these architectures, such as increased flexibility, speed, integration capabilities, cost reduction, automatic software/hardware upgrades, and agility. It also addresses potential issues and risks associated with cloud deployment, including data theft, malware injection attacks, denial of service (DoS) attacks, and licensing issues, providing a balanced perspective on the advantages and challenges of cloud computing implementation. The report is prepared for the Regional Garden organization.

Running head: CLOUD COMPUTING 1
Cloud Computing
Name:
institution Affiliation:
Cloud Computing
Name:
institution Affiliation:
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
CLOUD COMPUTING 2
Introduction
Cloud computing continues to be practice wherein network to the remote servers tend to be
hosted. This had been performed over the internet (Aazam, Khan, Alsaffar & Huh, 2014). It
facilitates storing, managing and processing data (Aazam, Khan, Alsaffar & Huh, 2014). This is
accomplished as opposed to precisely what is taken on the personal computers or maybe the
servers .Regional Garden organization which runs different variety of affiliated gardening
enterprises. It has large show for the garden which it opens for the public assessment several
times over time (Aazam, Khan, Alsaffar & Huh, 2014). The company continues to be
contemplating numerous plans of the strategy which are needed to be analyzed . The following is
report which is prepared for the Regional Garden organization in which discusses numerous
aspects for the cloud computing.
1. Describe which cloud architectures you would employ to assist Regional Gardens to
meet the Board’s strategy?
a) Describe each of architecture you would use, along with your reasons for deploying
it.
The cloud computing architecture is the structure of the system, which comprises on premise
and cloud services, services, middleware as well as the software component along with the
geo-location (Ali, Khan & Vasilakos, 2015).
Cloud Architecture Description Reason to deploy on it
Workload Distribution
Architecture
On this architecture has been
decreasing over usage to the
information technology
Cloud utilization monitors
have been included in this
case. This is carried out
Introduction
Cloud computing continues to be practice wherein network to the remote servers tend to be
hosted. This had been performed over the internet (Aazam, Khan, Alsaffar & Huh, 2014). It
facilitates storing, managing and processing data (Aazam, Khan, Alsaffar & Huh, 2014). This is
accomplished as opposed to precisely what is taken on the personal computers or maybe the
servers .Regional Garden organization which runs different variety of affiliated gardening
enterprises. It has large show for the garden which it opens for the public assessment several
times over time (Aazam, Khan, Alsaffar & Huh, 2014). The company continues to be
contemplating numerous plans of the strategy which are needed to be analyzed . The following is
report which is prepared for the Regional Garden organization in which discusses numerous
aspects for the cloud computing.
1. Describe which cloud architectures you would employ to assist Regional Gardens to
meet the Board’s strategy?
a) Describe each of architecture you would use, along with your reasons for deploying
it.
The cloud computing architecture is the structure of the system, which comprises on premise
and cloud services, services, middleware as well as the software component along with the
geo-location (Ali, Khan & Vasilakos, 2015).
Cloud Architecture Description Reason to deploy on it
Workload Distribution
Architecture
On this architecture has been
decreasing over usage to the
information technology
Cloud utilization monitors
have been included in this
case. This is carried out

CLOUD COMPUTING 3
resources. The under usage
has been also considered. The
organization has been relying
on the ability of runtime logics
as well as load balancing on
the algorithms to some degree
(Ali, Khan & Vasilakos,
2015).
through runtime workload
tracking (Ali, Khan &
Vasilakos, 2015).. Moreover,
it is also useful when it comes
to processing of data.
Dynamic scalability
Architecture
The model lies on the logics
when it comes to the
predefined systems of the
scaling. These triggers on the
allocation of the information
technology resources
dynamically (Zhan, Liu,
Gong, Zhang, Chung & Li,
2015). This could be carried
out from the resources pool.
The monitors to the cloud
usage have capability to track
the usage of the runtime. This
has been in relation to the
dynamic fluctuation due to the
nature of the architecture.
Resource pooling architecture lies on the ground to use
resource pools. There is
grouping of the resources in
information technology (Zhan,
Liu, Gong, Zhang, Chung &
Many cloud usage monitors
they are usually incorporated
during the tracking as well as
synchronization of the aspects
which are needed by the
resources. The under usage
has been also considered. The
organization has been relying
on the ability of runtime logics
as well as load balancing on
the algorithms to some degree
(Ali, Khan & Vasilakos,
2015).
through runtime workload
tracking (Ali, Khan &
Vasilakos, 2015).. Moreover,
it is also useful when it comes
to processing of data.
Dynamic scalability
Architecture
The model lies on the logics
when it comes to the
predefined systems of the
scaling. These triggers on the
allocation of the information
technology resources
dynamically (Zhan, Liu,
Gong, Zhang, Chung & Li,
2015). This could be carried
out from the resources pool.
The monitors to the cloud
usage have capability to track
the usage of the runtime. This
has been in relation to the
dynamic fluctuation due to the
nature of the architecture.
Resource pooling architecture lies on the ground to use
resource pools. There is
grouping of the resources in
information technology (Zhan,
Liu, Gong, Zhang, Chung &
Many cloud usage monitors
they are usually incorporated
during the tracking as well as
synchronization of the aspects
which are needed by the
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
CLOUD COMPUTING 4
Li, 2015). Moreover, it
ensures there is
synchronization in an
automatic manner.
information technology
resources which are pooled
(Almorsy, Grundy & Müller,
2016). There is also
consideration to other
management systems.
Elastic Resource Capability
Architecture
This has been related to the
provisioning to the virtual
servers especially in the
dynamics aspects (Almorsy,
Grundy & Müller, 2016). It
has been using allocating as
well as reclaiming of RAM
along with CPUs.
Cloud usage monitors have
been gathering data which are
utilized in the resources in
relation to IT previously and
lastly after carrying out
scaling.
Hybrid cloud architecture
The hybrid cloud is the cloud computing setting wherein utilizes a mix on premises, private
cloud and third party, public cloud services with an orchestration that is between the a few
platforms (Armbrust, Fox, Griffith, Joseph, Katz, Konwinski & Zaharia, 2010). By way of
enabling the workloads to move between the private and public clouds as the computing
necessitates and costs modify, the hybrid provides the business a larger flexibility and more
data when it comes to the deployment options (Zhan, Liu, Gong, Zhang, Chung & Li, 2015).
Li, 2015). Moreover, it
ensures there is
synchronization in an
automatic manner.
information technology
resources which are pooled
(Almorsy, Grundy & Müller,
2016). There is also
consideration to other
management systems.
Elastic Resource Capability
Architecture
This has been related to the
provisioning to the virtual
servers especially in the
dynamics aspects (Almorsy,
Grundy & Müller, 2016). It
has been using allocating as
well as reclaiming of RAM
along with CPUs.
Cloud usage monitors have
been gathering data which are
utilized in the resources in
relation to IT previously and
lastly after carrying out
scaling.
Hybrid cloud architecture
The hybrid cloud is the cloud computing setting wherein utilizes a mix on premises, private
cloud and third party, public cloud services with an orchestration that is between the a few
platforms (Armbrust, Fox, Griffith, Joseph, Katz, Konwinski & Zaharia, 2010). By way of
enabling the workloads to move between the private and public clouds as the computing
necessitates and costs modify, the hybrid provides the business a larger flexibility and more
data when it comes to the deployment options (Zhan, Liu, Gong, Zhang, Chung & Li, 2015).
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
CLOUD COMPUTING 5
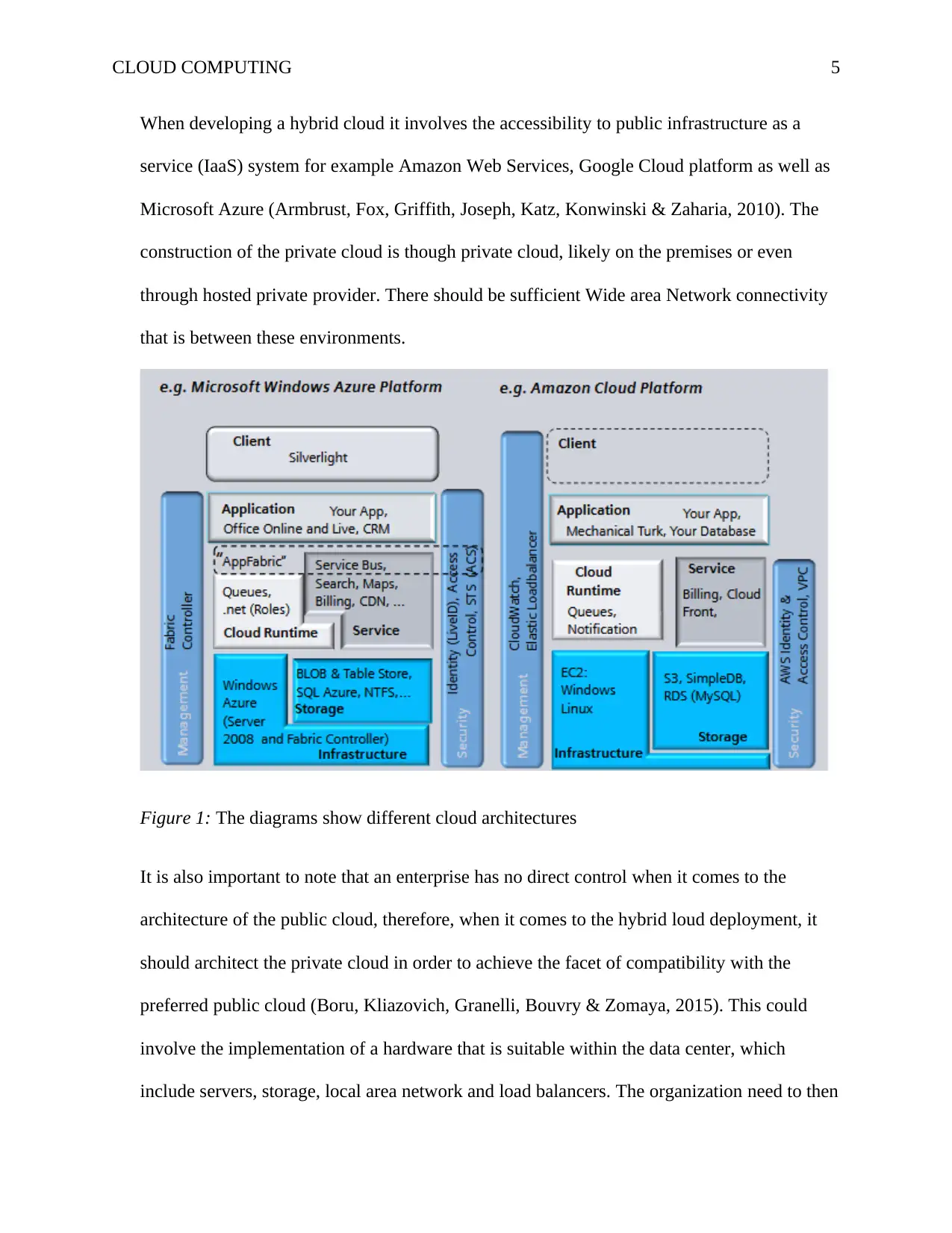
When developing a hybrid cloud it involves the accessibility to public infrastructure as a
service (IaaS) system for example Amazon Web Services, Google Cloud platform as well as
Microsoft Azure (Armbrust, Fox, Griffith, Joseph, Katz, Konwinski & Zaharia, 2010). The
construction of the private cloud is though private cloud, likely on the premises or even
through hosted private provider. There should be sufficient Wide area Network connectivity
that is between these environments.
Figure 1: The diagrams show different cloud architectures
It is also important to note that an enterprise has no direct control when it comes to the
architecture of the public cloud, therefore, when it comes to the hybrid loud deployment, it
should architect the private cloud in order to achieve the facet of compatibility with the
preferred public cloud (Boru, Kliazovich, Granelli, Bouvry & Zomaya, 2015). This could
involve the implementation of a hardware that is suitable within the data center, which
include servers, storage, local area network and load balancers. The organization need to then
When developing a hybrid cloud it involves the accessibility to public infrastructure as a
service (IaaS) system for example Amazon Web Services, Google Cloud platform as well as
Microsoft Azure (Armbrust, Fox, Griffith, Joseph, Katz, Konwinski & Zaharia, 2010). The
construction of the private cloud is though private cloud, likely on the premises or even
through hosted private provider. There should be sufficient Wide area Network connectivity
that is between these environments.
Figure 1: The diagrams show different cloud architectures
It is also important to note that an enterprise has no direct control when it comes to the
architecture of the public cloud, therefore, when it comes to the hybrid loud deployment, it
should architect the private cloud in order to achieve the facet of compatibility with the
preferred public cloud (Boru, Kliazovich, Granelli, Bouvry & Zomaya, 2015). This could
involve the implementation of a hardware that is suitable within the data center, which
include servers, storage, local area network and load balancers. The organization need to then
CLOUD COMPUTING 6
deploy the virtualization layer, or perhaps a hypervisor, to manage to generate and support on
the virtual machines (Boru, Kliazovich, Granelli, Bouvry & Zomaya, 2015). The IT team
must then deploy the private cloud software layer for instance, OpenStack, on top of the
hypervisor to manage to deliver the capabilities of the cloud for instance, self service,
automation and orchestration , billing and chargeback and reliability along resilience (Boru,
Kliazovich, Granelli, Bouvry & Zomaya, 2015). With regards to the private cloud architect it
could generate a menu of the majority of the local services for example, compute instances or
even the database situations, from which the users could choose.
The fundamental key to creating a successful hybrid cloud is deciding on a hypervisor and
cloud software layers which are more compatible to the desired public cloud, which assures
there surely is a suitable interoperability with the public cloud application programming
interfaces as well as services (Ren, Zhang, Tao, Zhao, Chai & Zhao, 2015). When it comes to
the implementation of the compatible software as well as services they enable instances of
migrating between the private and the public clouds (Zhan, Liu, Gong, Zhang, Chung & Li,
2015). Moreover, a developer could create advanced applications through use of the mix of
services as well as resources between both the public and the private platforms (Buyya,
Vecchiola & Selvi, 2013). When it comes to the hybrid cloud approach it should also have a
management tools such as Egenera PAN Cloud Director, Cisco Cloud Center which would
assist the business when it comes to handling the workflow that is created (Buyya, Vecchiola
& Selvi, 2013). There are other tasks such as service catalogs, billings along with the other
tasks which are related to the hybrid cloud (Buyya, Vecchiola & Selvi, 2013). It is important
to note that given the sheer volume of the potential tools which are readily available, it is
deploy the virtualization layer, or perhaps a hypervisor, to manage to generate and support on
the virtual machines (Boru, Kliazovich, Granelli, Bouvry & Zomaya, 2015). The IT team
must then deploy the private cloud software layer for instance, OpenStack, on top of the
hypervisor to manage to deliver the capabilities of the cloud for instance, self service,
automation and orchestration , billing and chargeback and reliability along resilience (Boru,
Kliazovich, Granelli, Bouvry & Zomaya, 2015). With regards to the private cloud architect it
could generate a menu of the majority of the local services for example, compute instances or
even the database situations, from which the users could choose.
The fundamental key to creating a successful hybrid cloud is deciding on a hypervisor and
cloud software layers which are more compatible to the desired public cloud, which assures
there surely is a suitable interoperability with the public cloud application programming
interfaces as well as services (Ren, Zhang, Tao, Zhao, Chai & Zhao, 2015). When it comes to
the implementation of the compatible software as well as services they enable instances of
migrating between the private and the public clouds (Zhan, Liu, Gong, Zhang, Chung & Li,
2015). Moreover, a developer could create advanced applications through use of the mix of
services as well as resources between both the public and the private platforms (Buyya,
Vecchiola & Selvi, 2013). When it comes to the hybrid cloud approach it should also have a
management tools such as Egenera PAN Cloud Director, Cisco Cloud Center which would
assist the business when it comes to handling the workflow that is created (Buyya, Vecchiola
& Selvi, 2013). There are other tasks such as service catalogs, billings along with the other
tasks which are related to the hybrid cloud (Buyya, Vecchiola & Selvi, 2013). It is important
to note that given the sheer volume of the potential tools which are readily available, it is
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
CLOUD COMPUTING 7
crucial to the potential adapters to test as well as evaluate the candidates well in their own
hybrid cloud environment before they could make commitment to any given tool.
b) Benefits and issues that would result from deployment of these architecture
Benefits
Scale
One of the benefits is that of flexibility (Buyya, Vecchiola & Selvi, 2013). Most of the
organization might choose to adopt the cloud architecture since they can increase the flexibility
of the business (Buyya, Vecchiola & Selvi, 2013). It could allow the workers to be more flexible
in or out of their workplace. The workers could gain access to the data so long as they might
have internet connection through any kind of the devices.
Speed
The virtual resources they might use on the requirements of the business objectives with ease.
There have been fast expansions with regards to the speeds of bandwidth based on the needs
(Buyya, Vecchiola & Selvi, 2013).
Integration
It assists with regards to delivering of easy accessibility to the traditional SQL databases.
Moreover, it might provide further analytical opportunities regarding the limitless needs of the
business (Buyya, Vecchiola & Selvi, 2013).
Cost reduction
The main reason as to why the organization could adopt on the cloud architecture n their
enterprise is the fact that it assists in the cost reduction (Buyya, Vecchiola & Selvi , 2013). The
crucial to the potential adapters to test as well as evaluate the candidates well in their own
hybrid cloud environment before they could make commitment to any given tool.
b) Benefits and issues that would result from deployment of these architecture
Benefits
Scale
One of the benefits is that of flexibility (Buyya, Vecchiola & Selvi, 2013). Most of the
organization might choose to adopt the cloud architecture since they can increase the flexibility
of the business (Buyya, Vecchiola & Selvi, 2013). It could allow the workers to be more flexible
in or out of their workplace. The workers could gain access to the data so long as they might
have internet connection through any kind of the devices.
Speed
The virtual resources they might use on the requirements of the business objectives with ease.
There have been fast expansions with regards to the speeds of bandwidth based on the needs
(Buyya, Vecchiola & Selvi, 2013).
Integration
It assists with regards to delivering of easy accessibility to the traditional SQL databases.
Moreover, it might provide further analytical opportunities regarding the limitless needs of the
business (Buyya, Vecchiola & Selvi, 2013).
Cost reduction
The main reason as to why the organization could adopt on the cloud architecture n their
enterprise is the fact that it assists in the cost reduction (Buyya, Vecchiola & Selvi , 2013). The
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
CLOUD COMPUTING 8
organization is enamored by the chance for the cost reduction as the cloud providers (Buyya,
Vecchiola & Selvi, 2013). This implies the organization could merely pay for the services which
they will use after they get access to the cloud services.
Automatic software/ Hardware Upgrades
When information technology solution continues to be implemented in the organization, this
creates an issue which is unable to have an appropriate financing because of the high cost which
is associated to the purchasing and maintaining the hardware as well as software (Buyya,
Vecchiola & Selvi, 2013). This could offer a negative effect (Buyya, Vecchiola & Selvi, 2013).
These issues could be addressed when adopting the cloud computing architecture approach. The
business could shift on their capital expenses to the operating expenses (Avram, 2014). This
might not reduce on the cost, but it would assist to develop a better relationship , stay in the
technological improvements and improve on the profit and standardized and low cost services
(Buyya, Vecchiola & Selvi, 2013).
Agility
Currently, in such a highly competitive business such as that of the Regional Gardens, it is
important to stay competitive (Avram, 2014). This is one way in which makes the business to be
different from the others and the time which is used to respond on the customers changing needs
(Avram, 2014). The use of this architecture could attain this in a more effective manner.
Issues of deployment of these architectures
Regional Gardens adopting these architectures could have issues when it comes to deployment.
These issues are as follows;
organization is enamored by the chance for the cost reduction as the cloud providers (Buyya,
Vecchiola & Selvi, 2013). This implies the organization could merely pay for the services which
they will use after they get access to the cloud services.
Automatic software/ Hardware Upgrades
When information technology solution continues to be implemented in the organization, this
creates an issue which is unable to have an appropriate financing because of the high cost which
is associated to the purchasing and maintaining the hardware as well as software (Buyya,
Vecchiola & Selvi, 2013). This could offer a negative effect (Buyya, Vecchiola & Selvi, 2013).
These issues could be addressed when adopting the cloud computing architecture approach. The
business could shift on their capital expenses to the operating expenses (Avram, 2014). This
might not reduce on the cost, but it would assist to develop a better relationship , stay in the
technological improvements and improve on the profit and standardized and low cost services
(Buyya, Vecchiola & Selvi, 2013).
Agility
Currently, in such a highly competitive business such as that of the Regional Gardens, it is
important to stay competitive (Avram, 2014). This is one way in which makes the business to be
different from the others and the time which is used to respond on the customers changing needs
(Avram, 2014). The use of this architecture could attain this in a more effective manner.
Issues of deployment of these architectures
Regional Gardens adopting these architectures could have issues when it comes to deployment.
These issues are as follows;
CLOUD COMPUTING 9
Stealing of data
The number of the users and organization would be linked to the internet is increasing. This
might also enhance on the probability of probing and attacking utilizing the viruses, worms as
well as cyber terrorists (Avram, 2014). There have been incidents which previously occurred to
service providers for example Google Inc .where there server got hacked.
Malware injection attack
A hacker might try to damage on the application on the cloud. In most of the cases the hacker
might find vulnerabilities on the web application making changes to it hence change on the
normal execution ( Avram, 2014). The hacker might program a risky application and use the
virtual machine to be able to inject the malware into the cloud services. The hackers might do
what they want for instance the data theft or even eavesdropping. The aspects of the SQL
injection could change on the query structure of the system. The hacker could use improper
validation of the data in order to take advantage (Botta, De Donato, Persico & Pescapé, 2016).
The main target is usually SQL servers or the databases. Moreover, the hackers could inject the
malicious code particularly the web server when it comes to bypassing the login stage and the
gain access to the databases (Buyya, Vecchiola & Selvi, 2013). They would then try to modify
on the databases, retrieve business data and even take control to the entire web server.
DoS (Denial of Service)
The Denial of Service attack has become one of the most concern issues when it comes to the
cloud architecture and a trouble when it comes to the services availability (Buyya, Vecchiola &
Selvi, 2013). This attack has grown and has more effect recently than in the past. There are
various type of this attack such as SYN flood attack, PING of death attack and Smurf attack
Stealing of data
The number of the users and organization would be linked to the internet is increasing. This
might also enhance on the probability of probing and attacking utilizing the viruses, worms as
well as cyber terrorists (Avram, 2014). There have been incidents which previously occurred to
service providers for example Google Inc .where there server got hacked.
Malware injection attack
A hacker might try to damage on the application on the cloud. In most of the cases the hacker
might find vulnerabilities on the web application making changes to it hence change on the
normal execution ( Avram, 2014). The hacker might program a risky application and use the
virtual machine to be able to inject the malware into the cloud services. The hackers might do
what they want for instance the data theft or even eavesdropping. The aspects of the SQL
injection could change on the query structure of the system. The hacker could use improper
validation of the data in order to take advantage (Botta, De Donato, Persico & Pescapé, 2016).
The main target is usually SQL servers or the databases. Moreover, the hackers could inject the
malicious code particularly the web server when it comes to bypassing the login stage and the
gain access to the databases (Buyya, Vecchiola & Selvi, 2013). They would then try to modify
on the databases, retrieve business data and even take control to the entire web server.
DoS (Denial of Service)
The Denial of Service attack has become one of the most concern issues when it comes to the
cloud architecture and a trouble when it comes to the services availability (Buyya, Vecchiola &
Selvi, 2013). This attack has grown and has more effect recently than in the past. There are
various type of this attack such as SYN flood attack, PING of death attack and Smurf attack
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
CLOUD COMPUTING 10
(Zhan, Liu, Gong, Zhang, Chung & Li, 2015). This attack makes the services on the cloud
inaccessible, at the same time intolerable and this could degrade on the quality of the services
and the connectivity (Buyya, Vecchiola & Selvi, 2013).
Licensing issues
If the license offered supplied to the organization is violated, it could lead to the disruption of the
services or the financial penalties (Zhan, Liu, Gong, Zhang, Chung & Li, 2015). In case there is
an attack to the cloud architecture penalties are going to be high as the software licensing
agreements are not conscious of ‘cloud aware’.
2. Describe the risks that you see associated with this new Hybrid Cloud and Miscro-
services strategy.
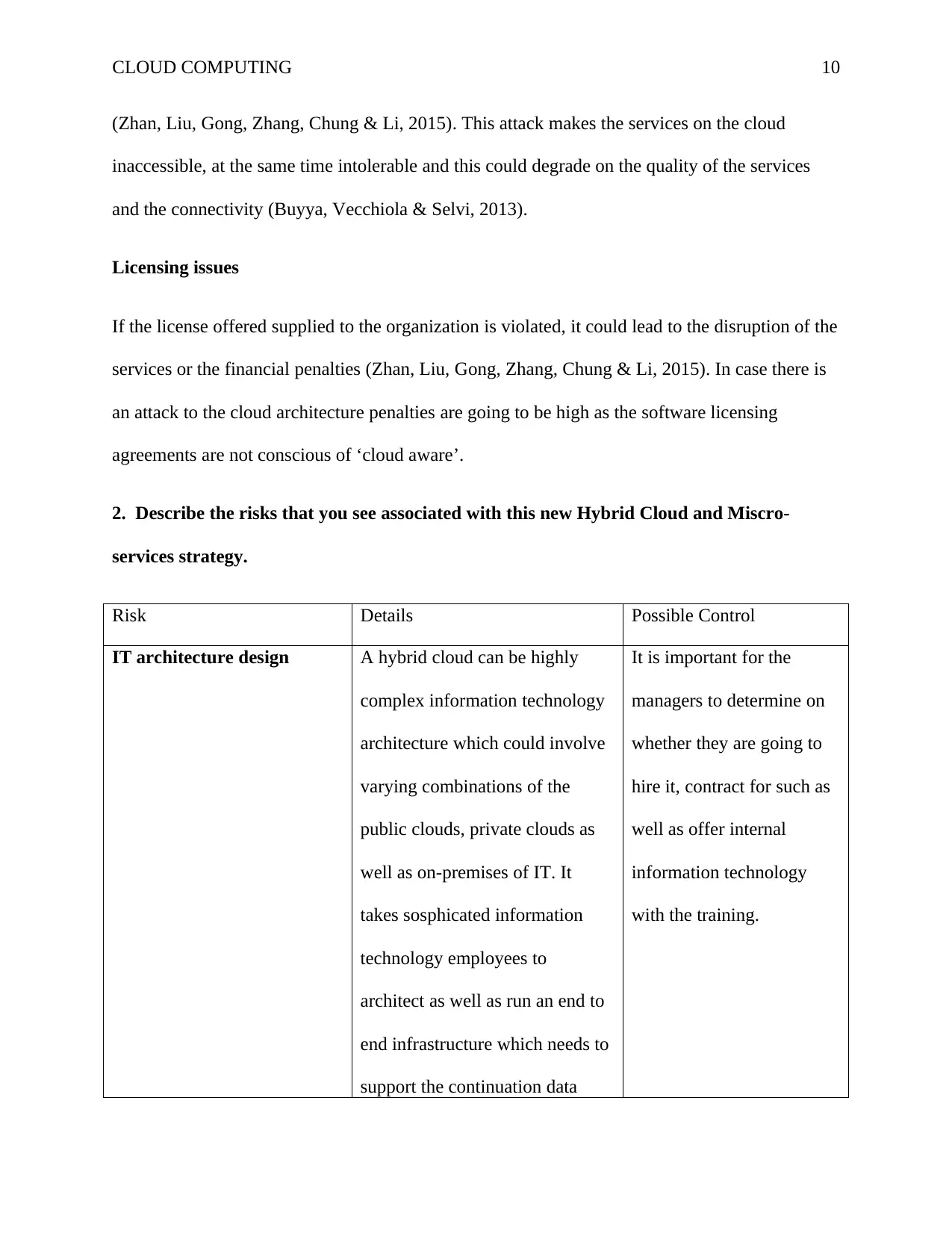
Risk Details Possible Control
IT architecture design A hybrid cloud can be highly
complex information technology
architecture which could involve
varying combinations of the
public clouds, private clouds as
well as on-premises of IT. It
takes sosphicated information
technology employees to
architect as well as run an end to
end infrastructure which needs to
support the continuation data
It is important for the
managers to determine on
whether they are going to
hire it, contract for such as
well as offer internal
information technology
with the training.
(Zhan, Liu, Gong, Zhang, Chung & Li, 2015). This attack makes the services on the cloud
inaccessible, at the same time intolerable and this could degrade on the quality of the services
and the connectivity (Buyya, Vecchiola & Selvi, 2013).
Licensing issues
If the license offered supplied to the organization is violated, it could lead to the disruption of the
services or the financial penalties (Zhan, Liu, Gong, Zhang, Chung & Li, 2015). In case there is
an attack to the cloud architecture penalties are going to be high as the software licensing
agreements are not conscious of ‘cloud aware’.
2. Describe the risks that you see associated with this new Hybrid Cloud and Miscro-
services strategy.
Risk Details Possible Control
IT architecture design A hybrid cloud can be highly
complex information technology
architecture which could involve
varying combinations of the
public clouds, private clouds as
well as on-premises of IT. It
takes sosphicated information
technology employees to
architect as well as run an end to
end infrastructure which needs to
support the continuation data
It is important for the
managers to determine on
whether they are going to
hire it, contract for such as
well as offer internal
information technology
with the training.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
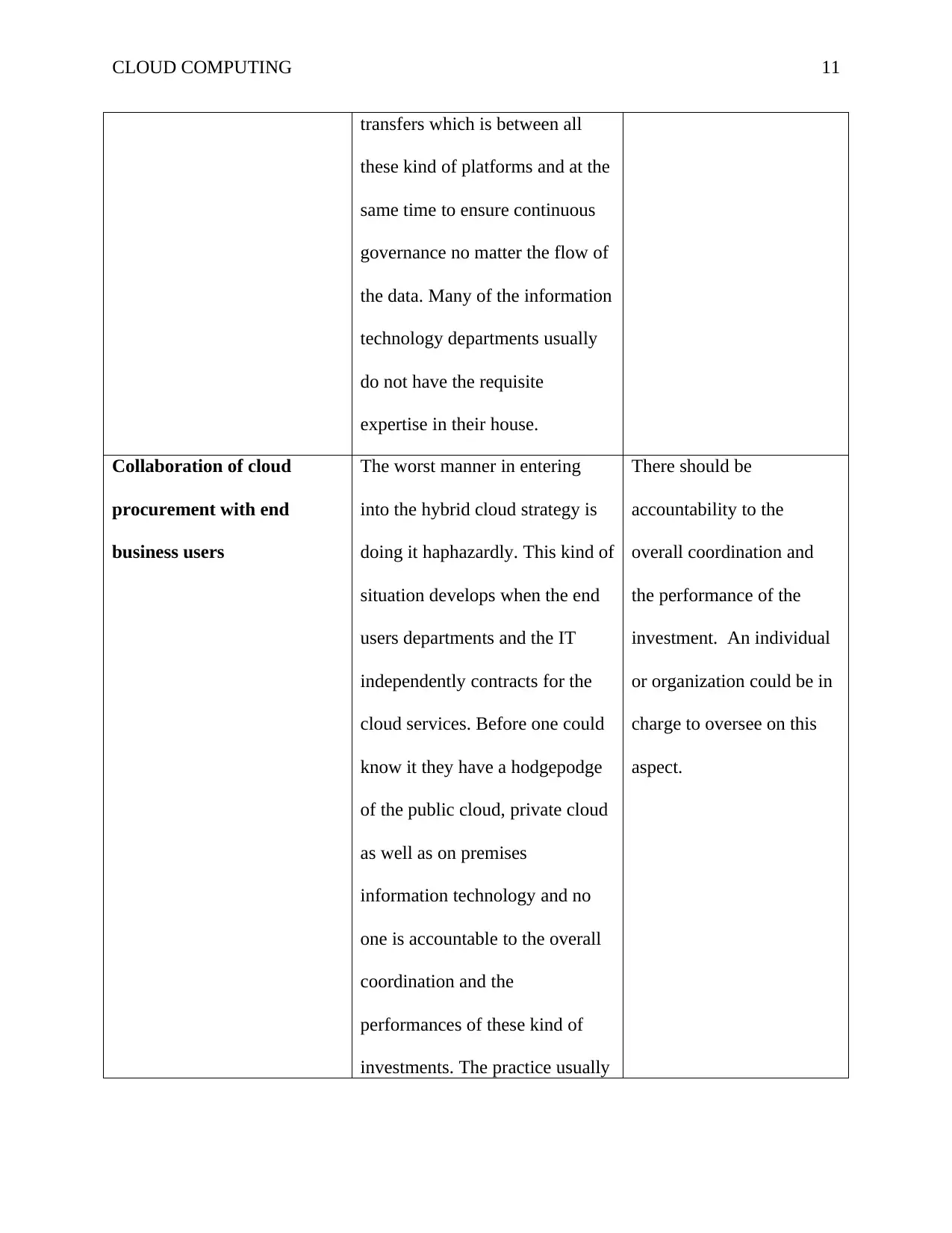
CLOUD COMPUTING 11
transfers which is between all
these kind of platforms and at the
same time to ensure continuous
governance no matter the flow of
the data. Many of the information
technology departments usually
do not have the requisite
expertise in their house.
Collaboration of cloud
procurement with end
business users
The worst manner in entering
into the hybrid cloud strategy is
doing it haphazardly. This kind of
situation develops when the end
users departments and the IT
independently contracts for the
cloud services. Before one could
know it they have a hodgepodge
of the public cloud, private cloud
as well as on premises
information technology and no
one is accountable to the overall
coordination and the
performances of these kind of
investments. The practice usually
There should be
accountability to the
overall coordination and
the performance of the
investment. An individual
or organization could be in
charge to oversee on this
aspect.
transfers which is between all
these kind of platforms and at the
same time to ensure continuous
governance no matter the flow of
the data. Many of the information
technology departments usually
do not have the requisite
expertise in their house.
Collaboration of cloud
procurement with end
business users
The worst manner in entering
into the hybrid cloud strategy is
doing it haphazardly. This kind of
situation develops when the end
users departments and the IT
independently contracts for the
cloud services. Before one could
know it they have a hodgepodge
of the public cloud, private cloud
as well as on premises
information technology and no
one is accountable to the overall
coordination and the
performances of these kind of
investments. The practice usually
There should be
accountability to the
overall coordination and
the performance of the
investment. An individual
or organization could be in
charge to oversee on this
aspect.

CLOUD COMPUTING 12
invites risk and the inefficiencies.
The security and privacy of
the data
Security and privacy are
nowadays improving in the
cloud, but this does not change
on the facts the corporate
information technology has direct
governance, security as well as
privacy control over the data
which the organization would
keep on their own data center and
they do not have this direct
control to the cloud. Organization
has the responsibilities to their
clients to ensure that they keep
the data safe and secure (Hwang,
Dongarra & Fox, 2013). They
need to weigh on the
responsibilities against the
advantages to store data in the
cloud where security of the data
and safeguarding control are
much reduced.
To address on this risk it is
important that the vendors
could understand the
organization data privacy
as well as security needs.
Moreover, they also need
to make sure that the cloud
provider are aware of the
particular data security as
well as privacy rules and
the regulations which could
apply to the entity such as
HIPAA, payment Card
Industry Data Security
Standards or the privacy
consideration.
Disaster recovery and When organization are moving Organization to identify
invites risk and the inefficiencies.
The security and privacy of
the data
Security and privacy are
nowadays improving in the
cloud, but this does not change
on the facts the corporate
information technology has direct
governance, security as well as
privacy control over the data
which the organization would
keep on their own data center and
they do not have this direct
control to the cloud. Organization
has the responsibilities to their
clients to ensure that they keep
the data safe and secure (Hwang,
Dongarra & Fox, 2013). They
need to weigh on the
responsibilities against the
advantages to store data in the
cloud where security of the data
and safeguarding control are
much reduced.
To address on this risk it is
important that the vendors
could understand the
organization data privacy
as well as security needs.
Moreover, they also need
to make sure that the cloud
provider are aware of the
particular data security as
well as privacy rules and
the regulations which could
apply to the entity such as
HIPAA, payment Card
Industry Data Security
Standards or the privacy
consideration.
Disaster recovery and When organization are moving Organization to identify
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 33
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





