Cloud Privacy And Security
VerifiedAdded on 2023/06/10
|17
|4510
|54
AI Summary
This article discusses the personal and ethical implications of Government’s Smart Sensor Network and Smart Wi-Fi Network, effectiveness of digital identity for ensuring online privacy and protection of digital identity in public Wi-Fi. It also provides recommendations for protecting sensitive information in public Wi-Fi.
Contribute Materials
Your contribution can guide someone’s learning journey. Share your
documents today.

Running head: CLOUD PRIVACY AND SECURITY
Cloud Privacy And Security
Name of the Student
Name of the University
Author note
Cloud Privacy And Security
Name of the Student
Name of the University
Author note
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
1CLOUD PRIVACY AND SECURITY
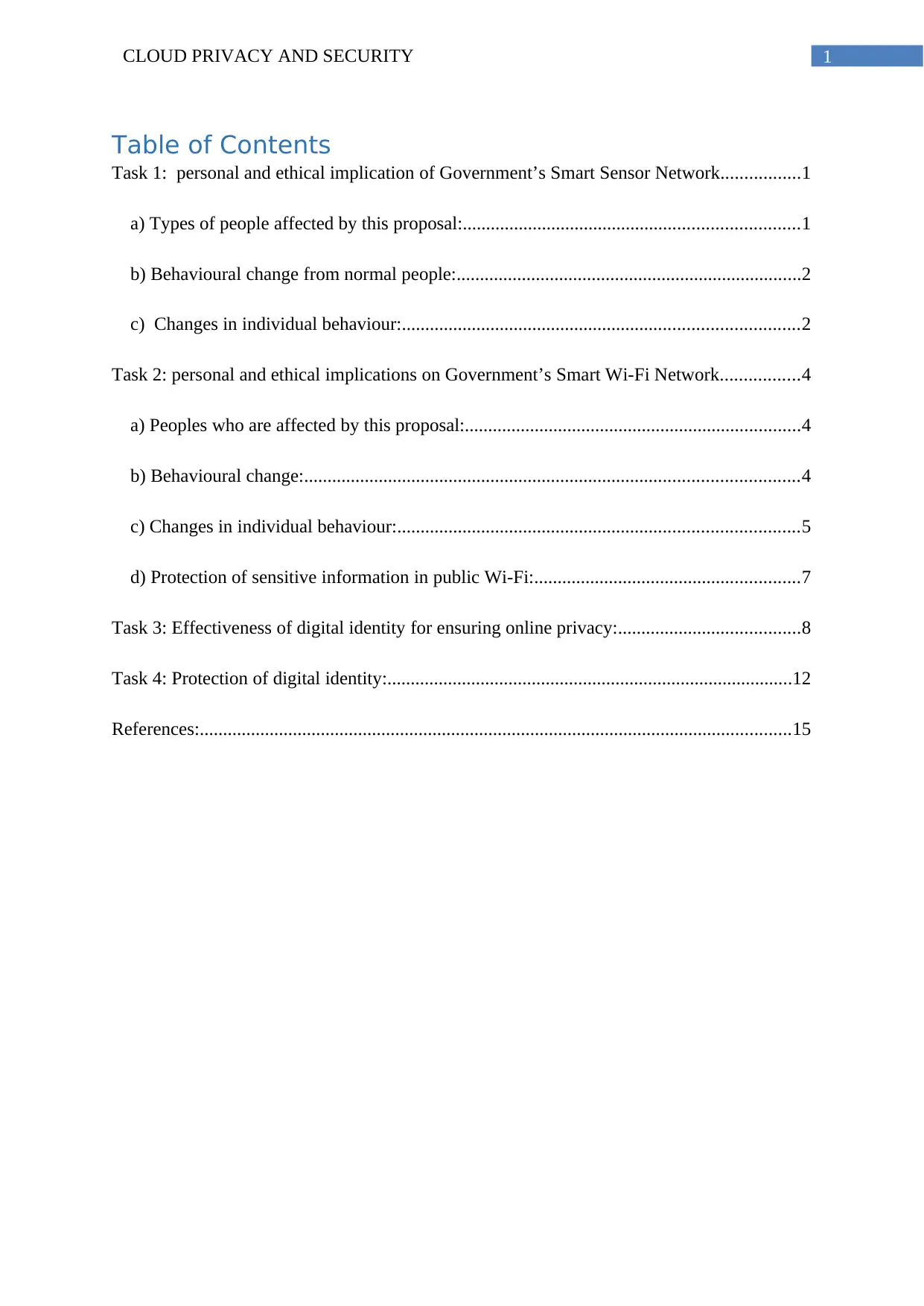
Table of Contents
Task 1: personal and ethical implication of Government’s Smart Sensor Network.................1
a) Types of people affected by this proposal:........................................................................1
b) Behavioural change from normal people:..........................................................................2
c) Changes in individual behaviour:.....................................................................................2
Task 2: personal and ethical implications on Government’s Smart Wi-Fi Network.................4
a) Peoples who are affected by this proposal:........................................................................4
b) Behavioural change:..........................................................................................................4
c) Changes in individual behaviour:......................................................................................5
d) Protection of sensitive information in public Wi-Fi:.........................................................7
Task 3: Effectiveness of digital identity for ensuring online privacy:.......................................8
Task 4: Protection of digital identity:.......................................................................................12
References:...............................................................................................................................15
Table of Contents
Task 1: personal and ethical implication of Government’s Smart Sensor Network.................1
a) Types of people affected by this proposal:........................................................................1
b) Behavioural change from normal people:..........................................................................2
c) Changes in individual behaviour:.....................................................................................2
Task 2: personal and ethical implications on Government’s Smart Wi-Fi Network.................4
a) Peoples who are affected by this proposal:........................................................................4
b) Behavioural change:..........................................................................................................4
c) Changes in individual behaviour:......................................................................................5
d) Protection of sensitive information in public Wi-Fi:.........................................................7
Task 3: Effectiveness of digital identity for ensuring online privacy:.......................................8
Task 4: Protection of digital identity:.......................................................................................12
References:...............................................................................................................................15
2CLOUD PRIVACY AND SECURITY
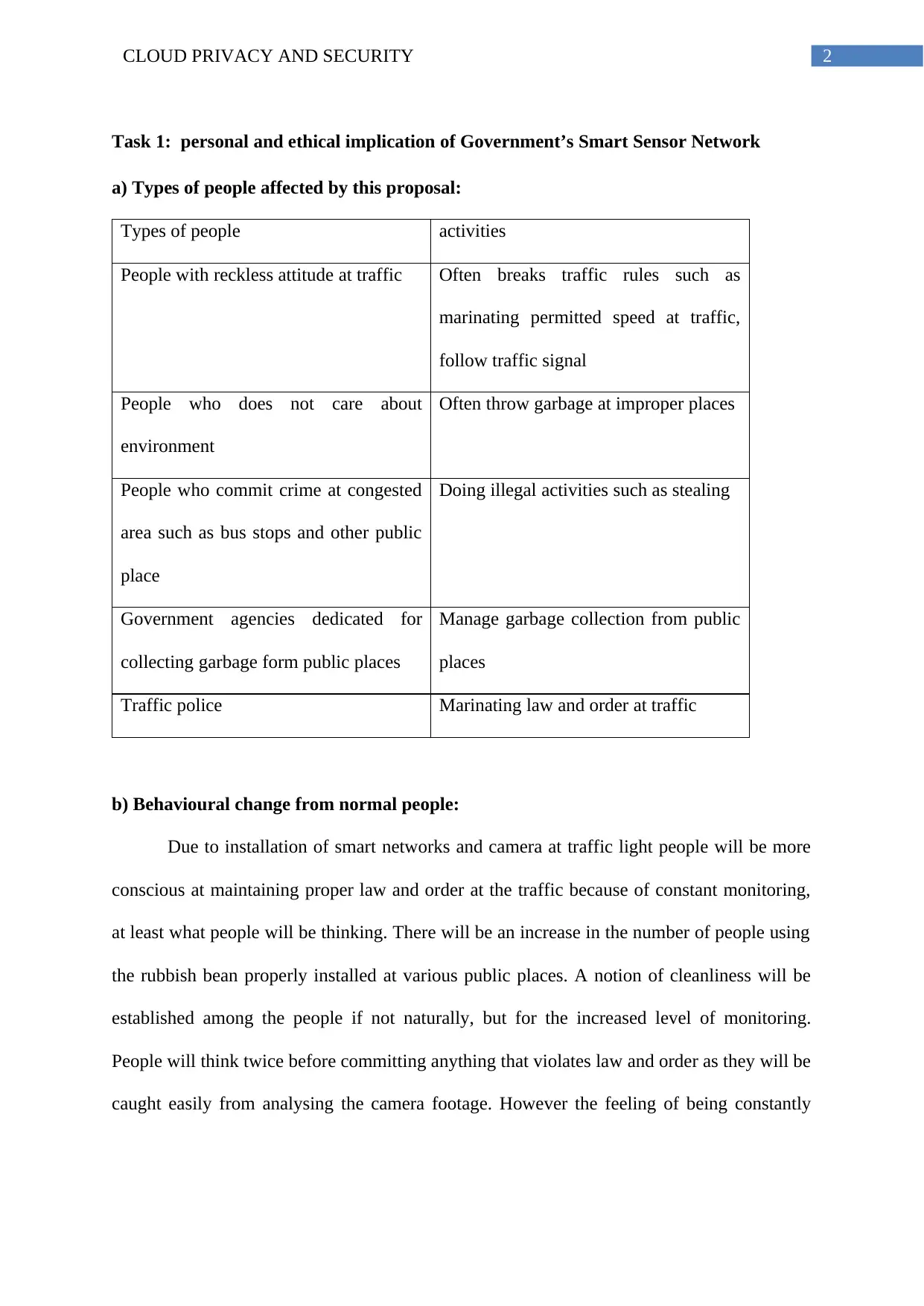
Task 1: personal and ethical implication of Government’s Smart Sensor Network
a) Types of people affected by this proposal:
Types of people activities
People with reckless attitude at traffic Often breaks traffic rules such as
marinating permitted speed at traffic,
follow traffic signal
People who does not care about
environment
Often throw garbage at improper places
People who commit crime at congested
area such as bus stops and other public
place
Doing illegal activities such as stealing
Government agencies dedicated for
collecting garbage form public places
Manage garbage collection from public
places
Traffic police Marinating law and order at traffic
b) Behavioural change from normal people:
Due to installation of smart networks and camera at traffic light people will be more
conscious at maintaining proper law and order at the traffic because of constant monitoring,
at least what people will be thinking. There will be an increase in the number of people using
the rubbish bean properly installed at various public places. A notion of cleanliness will be
established among the people if not naturally, but for the increased level of monitoring.
People will think twice before committing anything that violates law and order as they will be
caught easily from analysing the camera footage. However the feeling of being constantly
Task 1: personal and ethical implication of Government’s Smart Sensor Network
a) Types of people affected by this proposal:
Types of people activities
People with reckless attitude at traffic Often breaks traffic rules such as
marinating permitted speed at traffic,
follow traffic signal
People who does not care about
environment
Often throw garbage at improper places
People who commit crime at congested
area such as bus stops and other public
place
Doing illegal activities such as stealing
Government agencies dedicated for
collecting garbage form public places
Manage garbage collection from public
places
Traffic police Marinating law and order at traffic
b) Behavioural change from normal people:
Due to installation of smart networks and camera at traffic light people will be more
conscious at maintaining proper law and order at the traffic because of constant monitoring,
at least what people will be thinking. There will be an increase in the number of people using
the rubbish bean properly installed at various public places. A notion of cleanliness will be
established among the people if not naturally, but for the increased level of monitoring.
People will think twice before committing anything that violates law and order as they will be
caught easily from analysing the camera footage. However the feeling of being constantly
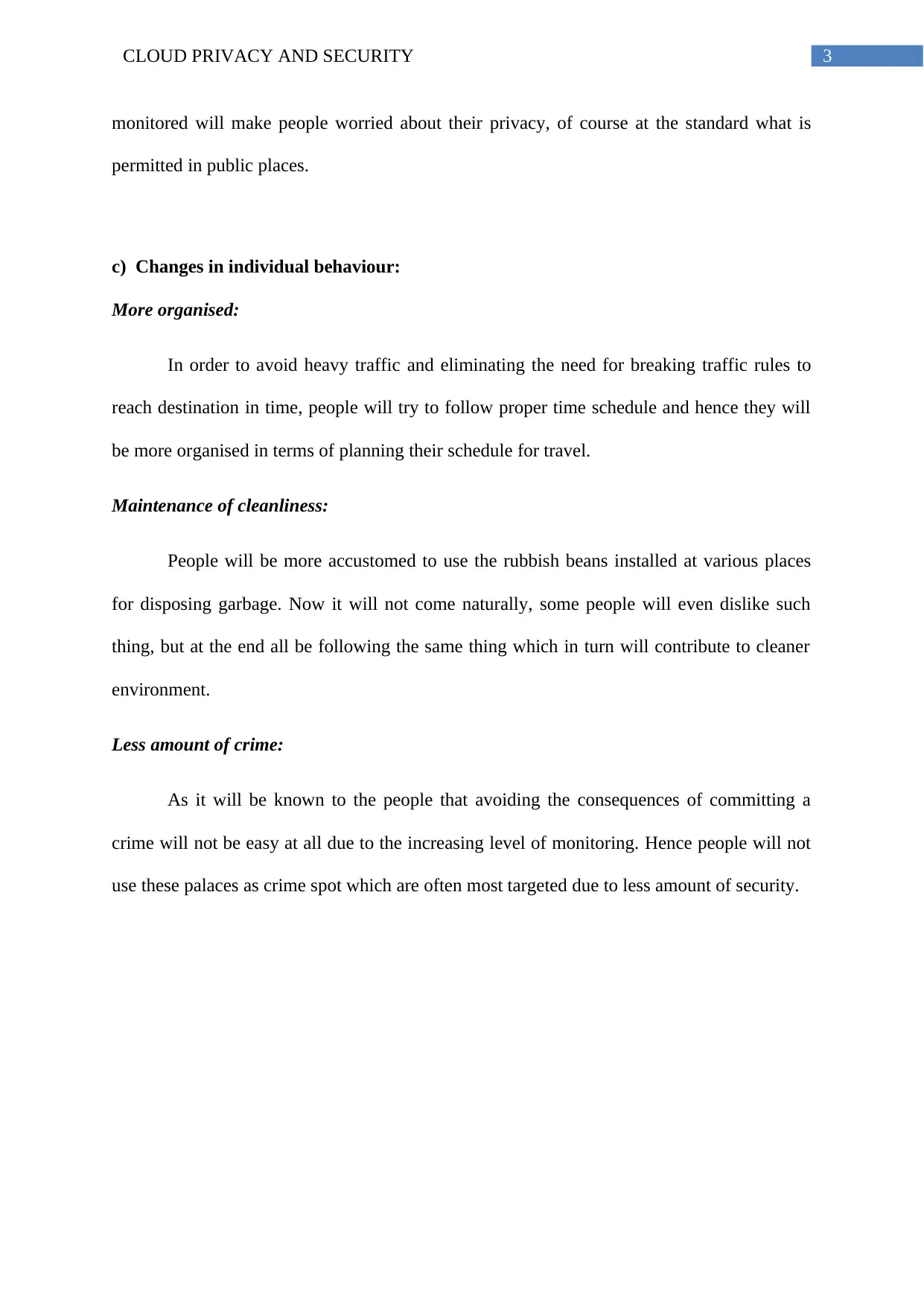
3CLOUD PRIVACY AND SECURITY
monitored will make people worried about their privacy, of course at the standard what is
permitted in public places.
c) Changes in individual behaviour:
More organised:
In order to avoid heavy traffic and eliminating the need for breaking traffic rules to
reach destination in time, people will try to follow proper time schedule and hence they will
be more organised in terms of planning their schedule for travel.
Maintenance of cleanliness:
People will be more accustomed to use the rubbish beans installed at various places
for disposing garbage. Now it will not come naturally, some people will even dislike such
thing, but at the end all be following the same thing which in turn will contribute to cleaner
environment.
Less amount of crime:
As it will be known to the people that avoiding the consequences of committing a
crime will not be easy at all due to the increasing level of monitoring. Hence people will not
use these palaces as crime spot which are often most targeted due to less amount of security.
monitored will make people worried about their privacy, of course at the standard what is
permitted in public places.
c) Changes in individual behaviour:
More organised:
In order to avoid heavy traffic and eliminating the need for breaking traffic rules to
reach destination in time, people will try to follow proper time schedule and hence they will
be more organised in terms of planning their schedule for travel.
Maintenance of cleanliness:
People will be more accustomed to use the rubbish beans installed at various places
for disposing garbage. Now it will not come naturally, some people will even dislike such
thing, but at the end all be following the same thing which in turn will contribute to cleaner
environment.
Less amount of crime:
As it will be known to the people that avoiding the consequences of committing a
crime will not be easy at all due to the increasing level of monitoring. Hence people will not
use these palaces as crime spot which are often most targeted due to less amount of security.
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
4CLOUD PRIVACY AND SECURITY
Task 2: personal and ethical implications on Government’s Smart Wi-Fi Network
a) Peoples who are affected by this proposal:
The proposal of the free Wi-Fi in the CBD will affect a range of people based on their
activity. Bellow it is presented in a table format
Types of people activities
Peoples who likes online entertainment Downloading, viewing and sharing content
across various genre
Peoples who like social engagement More and more engagement with social
media platform
Peoples who like to study Accessing study material from online
Peoples who travels a lot Checking travel related info for hassle free
travel experience
Peoples who are not so good in managing
household activities
Managing household activities like
shopping , paying bills for various
household needs
Peoples who have online business Advertise online for attracting people to
grow business.
b) Behavioural change:
Whenever people associate with new activities, it is most probable that their
behaviour is likely to be effected. In the age of technology, the behaviour of people has
changed dramatically than what it used to be before. In the age of internet, a lot of people are
connected, yet there are so many people that still don’t have access to internet or better to say
a lot of people has a limited internet connection. Hence, when these people will be introduced
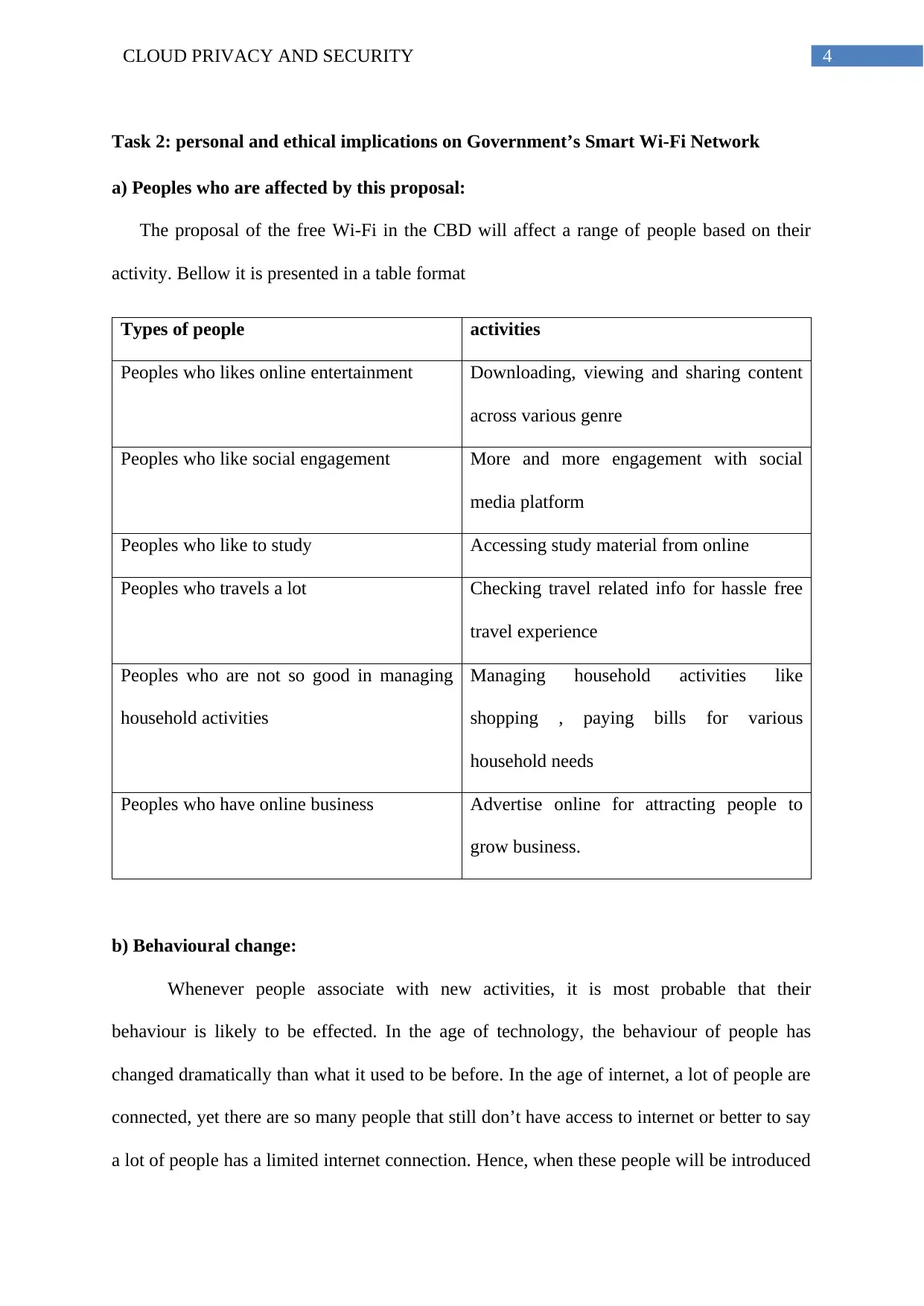
Task 2: personal and ethical implications on Government’s Smart Wi-Fi Network
a) Peoples who are affected by this proposal:
The proposal of the free Wi-Fi in the CBD will affect a range of people based on their
activity. Bellow it is presented in a table format
Types of people activities
Peoples who likes online entertainment Downloading, viewing and sharing content
across various genre
Peoples who like social engagement More and more engagement with social
media platform
Peoples who like to study Accessing study material from online
Peoples who travels a lot Checking travel related info for hassle free
travel experience
Peoples who are not so good in managing
household activities
Managing household activities like
shopping , paying bills for various
household needs
Peoples who have online business Advertise online for attracting people to
grow business.
b) Behavioural change:
Whenever people associate with new activities, it is most probable that their
behaviour is likely to be effected. In the age of technology, the behaviour of people has
changed dramatically than what it used to be before. In the age of internet, a lot of people are
connected, yet there are so many people that still don’t have access to internet or better to say
a lot of people has a limited internet connection. Hence, when these people will be introduced
5CLOUD PRIVACY AND SECURITY
to an internet connection that is free, the impact will be on this people more. A public Wi-Fi
is always an attraction to the people as it provide free connectivity to all the people. A free
connectivity will result in increased online activities. A lot of people loves to embrace the
digital world but does not afford it due to cost of having internet everywhere. A behavioural
change is expected form this people as they will prefer online activities over obtaining it
offline. Such activities include purchase of product, make payment. People will visit less to
the offline store for shopping as it is much more convenient to order them online. People will
then pay less attention for organising thing as they will tend to manage everything online.
This fact that internet makes people less organised is not blame on the internet alone, it has
something to do with the behavioural approach of the people who associate with it. People
will try to be updated with the news around the world as it will be easier to access. Social
engagement will increase through the virtual platform due to easier access to the online
world. Overall there will be increased online activities among the people in collective. As it
will be easier to connect with the virtual social life, people who finds it difficult to
communicate in public, will be more inclined towards it and as they will be more comfortable
in this form of communication they are likely to share with others more easily. This will
bring behavioural change in this group of people for sure.
c) Changes in individual behaviour:
Entertainment on the go:
Now a days, thanks to the advancement, a new form of entertainment is now taking
precedence. Everything people finds entertaining, is available online. Everything from
movies, plays, song, and tech is available online. Now with the free Wi-Fi, the preference for
the digital entertainment will increase. A lot of users will now download movies, song from
the internet and will less likely prefer to buy or rent it offline. In addition to the free versions,
contents that needs to be purchased or needs to be rented, is also available online. Although
to an internet connection that is free, the impact will be on this people more. A public Wi-Fi
is always an attraction to the people as it provide free connectivity to all the people. A free
connectivity will result in increased online activities. A lot of people loves to embrace the
digital world but does not afford it due to cost of having internet everywhere. A behavioural
change is expected form this people as they will prefer online activities over obtaining it
offline. Such activities include purchase of product, make payment. People will visit less to
the offline store for shopping as it is much more convenient to order them online. People will
then pay less attention for organising thing as they will tend to manage everything online.
This fact that internet makes people less organised is not blame on the internet alone, it has
something to do with the behavioural approach of the people who associate with it. People
will try to be updated with the news around the world as it will be easier to access. Social
engagement will increase through the virtual platform due to easier access to the online
world. Overall there will be increased online activities among the people in collective. As it
will be easier to connect with the virtual social life, people who finds it difficult to
communicate in public, will be more inclined towards it and as they will be more comfortable
in this form of communication they are likely to share with others more easily. This will
bring behavioural change in this group of people for sure.
c) Changes in individual behaviour:
Entertainment on the go:
Now a days, thanks to the advancement, a new form of entertainment is now taking
precedence. Everything people finds entertaining, is available online. Everything from
movies, plays, song, and tech is available online. Now with the free Wi-Fi, the preference for
the digital entertainment will increase. A lot of users will now download movies, song from
the internet and will less likely prefer to buy or rent it offline. In addition to the free versions,
contents that needs to be purchased or needs to be rented, is also available online. Although
6CLOUD PRIVACY AND SECURITY
this will influence people of all age groups, but it is expected to see more participants from
the younger groups.
Exploring the city like never before:
A free public will be of great benefits for the traveller. A lot of travellers like to
explore the city on their own than to be guided by someone else as they are completely
strangers. Now it is not difficult to find information about a place from finding best
attractions to visit to book cabs and hotel at the best price. A free and public Wi-Fi will surely
make the travel experience easier and they will be much more confident and independent
while exploring the city comfortable on their own.
Education that is free:
People who love to study often find it difficult to go to public library to borrow book
and return it in time to avoid extra charges. The presence of a free Wi-Fi will help to
download books online and read it anywhere anytime. In addition to that there will be no
requirement of returning the book. Hence people might access the library less and prefer
reading online for convenience.
Social affair with more engagement:
An easier access to the internet will increase the number of people who wants to
connect with friends all over the world in the shortest time possible. A more social
engagement will make people less focused in the world that actually exists around them.
People will be busier in chatting, updating status, sharing pictures with friends and followers
which people might find hard to refrain from.
this will influence people of all age groups, but it is expected to see more participants from
the younger groups.
Exploring the city like never before:
A free public will be of great benefits for the traveller. A lot of travellers like to
explore the city on their own than to be guided by someone else as they are completely
strangers. Now it is not difficult to find information about a place from finding best
attractions to visit to book cabs and hotel at the best price. A free and public Wi-Fi will surely
make the travel experience easier and they will be much more confident and independent
while exploring the city comfortable on their own.
Education that is free:
People who love to study often find it difficult to go to public library to borrow book
and return it in time to avoid extra charges. The presence of a free Wi-Fi will help to
download books online and read it anywhere anytime. In addition to that there will be no
requirement of returning the book. Hence people might access the library less and prefer
reading online for convenience.
Social affair with more engagement:
An easier access to the internet will increase the number of people who wants to
connect with friends all over the world in the shortest time possible. A more social
engagement will make people less focused in the world that actually exists around them.
People will be busier in chatting, updating status, sharing pictures with friends and followers
which people might find hard to refrain from.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
7CLOUD PRIVACY AND SECURITY
Work from anywhere:
Today jobs not only require to be present at the office and performs duty that
individuals are assigned to. As the technology is shaping the world, it is also influencing the
way communication takes place. Electronic communications like email are more preferred
today for it much more effective. A seamless access to this is required to manage the job life
more easily. Professionals and to some extents the students too will make use of the free
internet to see emails, reply to them so that no important message is missed that matters most.
Embracing the digital economy:
The presence of digital economy is already becoming strong. People these days prefer
to go cashless as the payment with digital wallets are much easier and hassle free. No
requirement for carrying cash and cards, all it needs is a smart phone with an active internet
connection. Hence with the free Wi-Fi it is expected that there will be increased number of
users opting for digital payments for all payment related matters.
d) Protection of sensitive information in public Wi-Fi:
In order to protect sensitive information while using the mobile device in the public Wi-Fi,
some steps are recommended bellow (Sathiaseelan et al., 2016):
The internet traffic must be secured with the help of VPN. An active VPN connection
while surfing the internet will ensure that the all the internet traffic will be transferred
through a secured and encrypted data tunnel,, thus increasing the security
If VPN is not configured, it should be made sure that each time the device is
connected to the internet via the public Wi-Fi, the session is encrypted. For this, sites
which have HTTPS in the URL instead of HTTP, should be used.
Transaction which uses FTP or the file transfer protocol should be avoided.
Work from anywhere:
Today jobs not only require to be present at the office and performs duty that
individuals are assigned to. As the technology is shaping the world, it is also influencing the
way communication takes place. Electronic communications like email are more preferred
today for it much more effective. A seamless access to this is required to manage the job life
more easily. Professionals and to some extents the students too will make use of the free
internet to see emails, reply to them so that no important message is missed that matters most.
Embracing the digital economy:
The presence of digital economy is already becoming strong. People these days prefer
to go cashless as the payment with digital wallets are much easier and hassle free. No
requirement for carrying cash and cards, all it needs is a smart phone with an active internet
connection. Hence with the free Wi-Fi it is expected that there will be increased number of
users opting for digital payments for all payment related matters.
d) Protection of sensitive information in public Wi-Fi:
In order to protect sensitive information while using the mobile device in the public Wi-Fi,
some steps are recommended bellow (Sathiaseelan et al., 2016):
The internet traffic must be secured with the help of VPN. An active VPN connection
while surfing the internet will ensure that the all the internet traffic will be transferred
through a secured and encrypted data tunnel,, thus increasing the security
If VPN is not configured, it should be made sure that each time the device is
connected to the internet via the public Wi-Fi, the session is encrypted. For this, sites
which have HTTPS in the URL instead of HTTP, should be used.
Transaction which uses FTP or the file transfer protocol should be avoided.
8CLOUD PRIVACY AND SECURITY
When connecting to a public Wi-Fi hotspot it should be checked whether there more
than one hotspot with the same name. These hotspots should be avoided as they are
often hard to recognize which one is more legitimate and hence should be avoided to
be in the safer side for protecting sensitive information on the mobile device.
Task 3: Effectiveness of digital identity for ensuring online privacy:
A digital identity is the information that is stored online to identify the presence of the
individual, organizations or the electronic devices that are operated online. The presence of
unique identifiers or the user patterns generated through the interactions of the system with
the network makes it possible. As the users share personal informations to avail some service
online like shopping, social networking , this adds to the digital identities of the individual or
the devices used. Digital data are often contextual as it contains sensitive information
(Abelson et al., 2016). The data is collected by the service provider for authenticating the
user online. In a world where digitalization is major trend, the protection of user’s data is
major issue. Hence, maintain online privacy is an important issue. Hackers are in constant
effort to steal these sensitive data available online for financial gain. Hence the online data
are not safe as people thinks. Digital identity is an important step towards securing these data
and maintain privacy. Digital identity is capable of addressing these issues which makes it an
effective choice for the online data security:
Increased transactions volume:
Due to an increased demand in online purchase, there is an increase in the transaction
volume. Now in order to maintain these transaction customised and safe for individuals,
digital identity important. The presence of digital identity makes it possible to authenticate
the transaction by individual users so that the transaction is only performed for whom it
When connecting to a public Wi-Fi hotspot it should be checked whether there more
than one hotspot with the same name. These hotspots should be avoided as they are
often hard to recognize which one is more legitimate and hence should be avoided to
be in the safer side for protecting sensitive information on the mobile device.
Task 3: Effectiveness of digital identity for ensuring online privacy:
A digital identity is the information that is stored online to identify the presence of the
individual, organizations or the electronic devices that are operated online. The presence of
unique identifiers or the user patterns generated through the interactions of the system with
the network makes it possible. As the users share personal informations to avail some service
online like shopping, social networking , this adds to the digital identities of the individual or
the devices used. Digital data are often contextual as it contains sensitive information
(Abelson et al., 2016). The data is collected by the service provider for authenticating the
user online. In a world where digitalization is major trend, the protection of user’s data is
major issue. Hence, maintain online privacy is an important issue. Hackers are in constant
effort to steal these sensitive data available online for financial gain. Hence the online data
are not safe as people thinks. Digital identity is an important step towards securing these data
and maintain privacy. Digital identity is capable of addressing these issues which makes it an
effective choice for the online data security:
Increased transactions volume:
Due to an increased demand in online purchase, there is an increase in the transaction
volume. Now in order to maintain these transaction customised and safe for individuals,
digital identity important. The presence of digital identity makes it possible to authenticate
the transaction by individual users so that the transaction is only performed for whom it
9CLOUD PRIVACY AND SECURITY
actually belongs to (Costa & Torres, 2015). Thus making the process much more customised
and easier to organise.
Increase in complexity of transactions:
With addition to the volume, the financial activities has become much more complex
with addition to new technology to make it much more convenient and attractive. Although
this has improved consumer experience, it has made the process complex in nature. In order
to address this complexity the users should be identified properly to enable the service
correctly. This is where digital identity is an effective choice.
Effective regulations:
Digital identity enforces strong regulatory standards for data protections. The
standards make it mandatory for the service provider to ensure that the data is protected with
strong security measures and it must be made clear to the users that how the data is collected
and share across networks. However, to ensure that the users have to provide necessary
informations identified as digital identity as demanded by the service provider to avail a
particular service (Diamandaki, 2014).
Digital identity consist of several layers (Kennedy, 2016), serving different purpose ensures
data privacy in the following way:
Consistency and coordination:
This layer ensure that the online activities is governed in a such a way that there is no
issue with the data consistency and the data is perfectly coordinated for better security. If the
data is inconsistence or not coordinated properly, it is easier to hack or steal.
Attribute collection:
actually belongs to (Costa & Torres, 2015). Thus making the process much more customised
and easier to organise.
Increase in complexity of transactions:
With addition to the volume, the financial activities has become much more complex
with addition to new technology to make it much more convenient and attractive. Although
this has improved consumer experience, it has made the process complex in nature. In order
to address this complexity the users should be identified properly to enable the service
correctly. This is where digital identity is an effective choice.
Effective regulations:
Digital identity enforces strong regulatory standards for data protections. The
standards make it mandatory for the service provider to ensure that the data is protected with
strong security measures and it must be made clear to the users that how the data is collected
and share across networks. However, to ensure that the users have to provide necessary
informations identified as digital identity as demanded by the service provider to avail a
particular service (Diamandaki, 2014).
Digital identity consist of several layers (Kennedy, 2016), serving different purpose ensures
data privacy in the following way:
Consistency and coordination:
This layer ensure that the online activities is governed in a such a way that there is no
issue with the data consistency and the data is perfectly coordinated for better security. If the
data is inconsistence or not coordinated properly, it is easier to hack or steal.
Attribute collection:
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
10CLOUD PRIVACY AND SECURITY
This layer ensure that all the user attributes are properly collected , stored and most
importantly protected with strong security standards. Data attribute is an important step
towards data security. It identifies data in terms of the sensitivity and importance and thus
applying stronger security for the data that needs more protection.
This layer ensure that all the user attributes are properly collected , stored and most
importantly protected with strong security standards. Data attribute is an important step
towards data security. It identifies data in terms of the sensitivity and importance and thus
applying stronger security for the data that needs more protection.
11CLOUD PRIVACY AND SECURITY
Authentication:
This layer deals with the user authentication. Authentication is important measure of
data security. A lot of inconsistence authentication is performed for acquiring digital data.
However, this particular layer ensures that inconsistent authentication is avoided to ensure
optimal data security.
Exchange of attributes:
This layer provide mechanism to exchange attributes between different parties.
Although the data is exchanged across different platforms, the exchange of attributes ensures
that the importance and privacy of the data is consistent throughout the process.
Drawback:
The above discussion might give the impression that the data is highly secure with
digital identity. Although this is true that digital identity is an effective way to maintain data
security, it has limitations too. Before identifying the limitations, it is important to have a
look at the level of information that is collected with the digital identity (Buccafurri, 2015).
Some services that are available online only requires some basic information like username,
password and an email address register for a service. However, the information that the user
wants to share with the service completely depends on the individual users. Sometimes
people often creates password that are not so strong and it can be easily interpreted by the
hackers (Mosco, 2016). If one becomes successful in stealing the password, it is easier to
steal the identity of the owner and hence becomes easier to perform actions on behalf of the
owner. Although some service provides two step verification before the information becomes
accessible, but it is not impossible to hack that too. Some services makes it optional for the
user that what kind of informations is shared online, other services makes it mandatory to
share the details such as passport scans, physical addresses, Social Security numbers, and
Authentication:
This layer deals with the user authentication. Authentication is important measure of
data security. A lot of inconsistence authentication is performed for acquiring digital data.
However, this particular layer ensures that inconsistent authentication is avoided to ensure
optimal data security.
Exchange of attributes:
This layer provide mechanism to exchange attributes between different parties.
Although the data is exchanged across different platforms, the exchange of attributes ensures
that the importance and privacy of the data is consistent throughout the process.
Drawback:
The above discussion might give the impression that the data is highly secure with
digital identity. Although this is true that digital identity is an effective way to maintain data
security, it has limitations too. Before identifying the limitations, it is important to have a
look at the level of information that is collected with the digital identity (Buccafurri, 2015).
Some services that are available online only requires some basic information like username,
password and an email address register for a service. However, the information that the user
wants to share with the service completely depends on the individual users. Sometimes
people often creates password that are not so strong and it can be easily interpreted by the
hackers (Mosco, 2016). If one becomes successful in stealing the password, it is easier to
steal the identity of the owner and hence becomes easier to perform actions on behalf of the
owner. Although some service provides two step verification before the information becomes
accessible, but it is not impossible to hack that too. Some services makes it optional for the
user that what kind of informations is shared online, other services makes it mandatory to
share the details such as passport scans, physical addresses, Social Security numbers, and
12CLOUD PRIVACY AND SECURITY
birthdate details to form digital identity. These information are highly sensitive in nature and
reveals a lot of personal information about the user. Services that asks for such sensitive
information are opening of savings account or availing passport and specially services offered
by government (Khatchatourov, Laurent & Levallois-Barth, 2015). One problem with the
digital identity is that the concept is still relatively new as compared to the physical identity
(Laurent & Bouzefrane, 2015). Due to this techniques that are deployed for securing these
data, still requires modifications and a lot of issues needs to be addressed. Although,
companies claims that they ensures the privacy of the customer data, security flaws is there.
Hence it is not possible to protect the digital data by just having digital identity. The presence
of digital identity helps the users to have secure accounts but it exposes a lot of data online
about than the individual think. Hence a lot of criminal activities are performed online to steal
these data, which is relatively easier (Laurent et al., 2015). The problem with the digital
identity is not exchange of data, it is how the data is actually exchanged online and the
activities performed with it after it is shared by the users. Hence, it can be said that digital
identity is an effective approach for creating online data privacy but requires some issues to
be addressed for strengthening the security techniques (Kolko, 2015).
Task 4: Protection of digital identity:
The digital identity, as it contains a lot of information about the person online is
always at target of the hackers. Once the identity is stolen, a lot of activities like financial
transaction is easier to perform on behalf of the identity owner. Now although it is possible to
protect the identity completely, some actions should be initiated from the user side so that it
is not possible for the hackers to steal that identity easily (Elbirt, 2015). These steps are:
Strong password:
birthdate details to form digital identity. These information are highly sensitive in nature and
reveals a lot of personal information about the user. Services that asks for such sensitive
information are opening of savings account or availing passport and specially services offered
by government (Khatchatourov, Laurent & Levallois-Barth, 2015). One problem with the
digital identity is that the concept is still relatively new as compared to the physical identity
(Laurent & Bouzefrane, 2015). Due to this techniques that are deployed for securing these
data, still requires modifications and a lot of issues needs to be addressed. Although,
companies claims that they ensures the privacy of the customer data, security flaws is there.
Hence it is not possible to protect the digital data by just having digital identity. The presence
of digital identity helps the users to have secure accounts but it exposes a lot of data online
about than the individual think. Hence a lot of criminal activities are performed online to steal
these data, which is relatively easier (Laurent et al., 2015). The problem with the digital
identity is not exchange of data, it is how the data is actually exchanged online and the
activities performed with it after it is shared by the users. Hence, it can be said that digital
identity is an effective approach for creating online data privacy but requires some issues to
be addressed for strengthening the security techniques (Kolko, 2015).
Task 4: Protection of digital identity:
The digital identity, as it contains a lot of information about the person online is
always at target of the hackers. Once the identity is stolen, a lot of activities like financial
transaction is easier to perform on behalf of the identity owner. Now although it is possible to
protect the identity completely, some actions should be initiated from the user side so that it
is not possible for the hackers to steal that identity easily (Elbirt, 2015). These steps are:
Strong password:
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
13CLOUD PRIVACY AND SECURITY
Whenever any account is created online, it should be made sure that password created
for the account should be strong. A preferred way to create a strong password is to make the
password at least 8 character long with a combination of alphabets and special cases. Another
thing which should be remembered is that every account related to the financial activities
should be secured with different password (Windley, 2015). Otherwise, a hack into one of the
account will put all the accounts at risk.
Verification of authenticate site:
One thing that should always be remembered that not every site exist on the internet is
authenticate one. Some sites are created for stealing user data and some site even do not have
enough security for preventing data hack. Hence, it is important to identify which sites are
authentic and have better security in place. Although nothing on the internet is secure as such,
however visiting trusted sites will make it relatively more secure. There are some possible
and verified ways which let the user know about the authenticity and security of the site.
The sites which are secured must have the symbol “s” in the URL of the website. The
letter s confirms that the site is secured via strong encryption technology. Sites which does
not have this feature should be avoided, especially for doing any financial related activities.
Selective about information shared online:
People, in order to make the social networking profile more attractive or without any
special purpose often share personal information more than what is needed. It might have
broader impact on the security than what people thinks or ignore in most of the cases. If the
social profile is somehow hacked, a lot of information put there will be visible to the hackers
and that might be used for exploiting other profiles that contains similar information (Ribble,
Bailey & Ross, 2015). Hence it is advisable to be selective about what and how much
information is shared online for create better protection for the digital identity.
Whenever any account is created online, it should be made sure that password created
for the account should be strong. A preferred way to create a strong password is to make the
password at least 8 character long with a combination of alphabets and special cases. Another
thing which should be remembered is that every account related to the financial activities
should be secured with different password (Windley, 2015). Otherwise, a hack into one of the
account will put all the accounts at risk.
Verification of authenticate site:
One thing that should always be remembered that not every site exist on the internet is
authenticate one. Some sites are created for stealing user data and some site even do not have
enough security for preventing data hack. Hence, it is important to identify which sites are
authentic and have better security in place. Although nothing on the internet is secure as such,
however visiting trusted sites will make it relatively more secure. There are some possible
and verified ways which let the user know about the authenticity and security of the site.
The sites which are secured must have the symbol “s” in the URL of the website. The
letter s confirms that the site is secured via strong encryption technology. Sites which does
not have this feature should be avoided, especially for doing any financial related activities.
Selective about information shared online:
People, in order to make the social networking profile more attractive or without any
special purpose often share personal information more than what is needed. It might have
broader impact on the security than what people thinks or ignore in most of the cases. If the
social profile is somehow hacked, a lot of information put there will be visible to the hackers
and that might be used for exploiting other profiles that contains similar information (Ribble,
Bailey & Ross, 2015). Hence it is advisable to be selective about what and how much
information is shared online for create better protection for the digital identity.
14CLOUD PRIVACY AND SECURITY
Identify emails and messages:
Emails and messages that are lucrative in nature, especially those promises giveaway
of prize money, should be avoided at any cost. These emails and messages, in most of the
cases turns out to be an easier way for the hackers to steal personal information about the
users. Another things to be noted that links provided in the emails and messages should not
be clicked as this another way to extract personal information by hacking the devices from
where those links are accessed (Liginlal, Sim & Khansa, 2014). The system once hacked,
becomes vulnerable and becomes easier for others to obtain whatever data they want to
extract. Hence these steps should be avoided for better security of the digital identity.
Two step verification:
The safest way as recommended by expert is to form some kind of smart card that will
provide digital security in a personalised way. Another effective approach is to turn on the
two step verification process for accessing all kind of digital data related to the digital
identity of any individual. The combination of both will ensure optimal security as it will
require others to prove the required authentication through this two-step verification process
before the data become accessible to anyone else other than the owner (Palfrey & Gasser,
2015).
These are the several possible ways that are recommended for securing the digital
identity online as there are constant effort to steal these data that are of major importance.
Identify emails and messages:
Emails and messages that are lucrative in nature, especially those promises giveaway
of prize money, should be avoided at any cost. These emails and messages, in most of the
cases turns out to be an easier way for the hackers to steal personal information about the
users. Another things to be noted that links provided in the emails and messages should not
be clicked as this another way to extract personal information by hacking the devices from
where those links are accessed (Liginlal, Sim & Khansa, 2014). The system once hacked,
becomes vulnerable and becomes easier for others to obtain whatever data they want to
extract. Hence these steps should be avoided for better security of the digital identity.
Two step verification:
The safest way as recommended by expert is to form some kind of smart card that will
provide digital security in a personalised way. Another effective approach is to turn on the
two step verification process for accessing all kind of digital data related to the digital
identity of any individual. The combination of both will ensure optimal security as it will
require others to prove the required authentication through this two-step verification process
before the data become accessible to anyone else other than the owner (Palfrey & Gasser,
2015).
These are the several possible ways that are recommended for securing the digital
identity online as there are constant effort to steal these data that are of major importance.
15CLOUD PRIVACY AND SECURITY
References:
Abelson, H., Lessig, L., Covell, P., Gordon, S., Hochberger, A., & Kovacs, J. (2016). Digital
identity in cyberspace. White paper submitted for, 6.
Buccafurri, F., Fotia, L., Lax, G., & Mammoliti, R. (2015, September). Enhancing Public
Digital Identity System (SPID) to Prevent Information Leakage. In International
Conference on Electronic Government and the Information Systems Perspective (pp.
57-70). Springer, Cham.
Costa, C., & Torres, R. (2015). To be or not to be, the importance of Digital Identity in the
networked society. Educação, Formação & Tecnologias-ISSN 1646-933X, 47-53.
Diamandaki, K. (2014). Virtual ethnicity and digital diasporas: Identity construction in
cyberspace. Global Media Journal, 2(2), 26.
Elbirt, A. J. (2016). Who are you? How to protect against identity theft. IEEE Technology
and Society Magazine, 24(2), 5-8.
Kennedy, H. (2016). Beyond anonymity, or future directions for internet identity
research. New media & society, 8(6), 859-876.
Khatchatourov, A., Laurent, M., & Levallois-Barth, C. (2015, August). Privacy in Digital
Identity Systems: Models, Assessment, and User Adoption. In International
Conference on Electronic Government (pp. 273-290). Springer, Cham.
Kolko, B., Nakamura, L., & Rodman, G. (2015). Race in cyberspace. Routledge.
Laurent, M., & Bouzefrane, S. (2015). Digital identity management. Elsevier.
Laurent, M., Denouël, J., Levallois-Barth, C., & Waelbroeck, P. (2015). Digital identity.
In Digital identity management (pp. 1-45).
References:
Abelson, H., Lessig, L., Covell, P., Gordon, S., Hochberger, A., & Kovacs, J. (2016). Digital
identity in cyberspace. White paper submitted for, 6.
Buccafurri, F., Fotia, L., Lax, G., & Mammoliti, R. (2015, September). Enhancing Public
Digital Identity System (SPID) to Prevent Information Leakage. In International
Conference on Electronic Government and the Information Systems Perspective (pp.
57-70). Springer, Cham.
Costa, C., & Torres, R. (2015). To be or not to be, the importance of Digital Identity in the
networked society. Educação, Formação & Tecnologias-ISSN 1646-933X, 47-53.
Diamandaki, K. (2014). Virtual ethnicity and digital diasporas: Identity construction in
cyberspace. Global Media Journal, 2(2), 26.
Elbirt, A. J. (2016). Who are you? How to protect against identity theft. IEEE Technology
and Society Magazine, 24(2), 5-8.
Kennedy, H. (2016). Beyond anonymity, or future directions for internet identity
research. New media & society, 8(6), 859-876.
Khatchatourov, A., Laurent, M., & Levallois-Barth, C. (2015, August). Privacy in Digital
Identity Systems: Models, Assessment, and User Adoption. In International
Conference on Electronic Government (pp. 273-290). Springer, Cham.
Kolko, B., Nakamura, L., & Rodman, G. (2015). Race in cyberspace. Routledge.
Laurent, M., & Bouzefrane, S. (2015). Digital identity management. Elsevier.
Laurent, M., Denouël, J., Levallois-Barth, C., & Waelbroeck, P. (2015). Digital identity.
In Digital identity management (pp. 1-45).
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
16CLOUD PRIVACY AND SECURITY
Liginlal, D., Sim, I., & Khansa, L. (2009). How significant is human error as a cause of
privacy breaches? An empirical study and a framework for error
management. computers & security, 28(3-4), 215-228.
Mosco, V. (2016). The digital identity: Myth, power, and cyberspace. Mit Press.
Palfrey, J. G., & Gasser, U. (2015). Born digital: Understanding the first generation of
digital natives. ReadHowYouWant. com.
Reeder, R., & Schechter, S. (2015). When the password doesn't work: Secondary
authentication for websites. IEEE Security and Privacy, 9.
Ribble, M. S., Bailey, G. D., & Ross, T. W. (2014). Digital citizenship: Addressing
appropriate technology behavior. Learning & Leading with technology, 32(1), 6.
Sathiaseelan, A., Mortier, R., Goulden, M., Greiffenhagen, C., Radenkovic, M., Crowcroft,
J., & McAuley, D. (2014, December). A feasibility study of an in-the-wild
experimental public access wifi network. In Proceedings of the Fifth ACM
Symposium on Computing for Development (pp. 33-42). ACM.
Windley, P. J. (2015). Digital Identity: Unmasking identity management architecture (IMA).
" O'Reilly Media, Inc.".
Liginlal, D., Sim, I., & Khansa, L. (2009). How significant is human error as a cause of
privacy breaches? An empirical study and a framework for error
management. computers & security, 28(3-4), 215-228.
Mosco, V. (2016). The digital identity: Myth, power, and cyberspace. Mit Press.
Palfrey, J. G., & Gasser, U. (2015). Born digital: Understanding the first generation of
digital natives. ReadHowYouWant. com.
Reeder, R., & Schechter, S. (2015). When the password doesn't work: Secondary
authentication for websites. IEEE Security and Privacy, 9.
Ribble, M. S., Bailey, G. D., & Ross, T. W. (2014). Digital citizenship: Addressing
appropriate technology behavior. Learning & Leading with technology, 32(1), 6.
Sathiaseelan, A., Mortier, R., Goulden, M., Greiffenhagen, C., Radenkovic, M., Crowcroft,
J., & McAuley, D. (2014, December). A feasibility study of an in-the-wild
experimental public access wifi network. In Proceedings of the Fifth ACM
Symposium on Computing for Development (pp. 33-42). ACM.
Windley, P. J. (2015). Digital Identity: Unmasking identity management architecture (IMA).
" O'Reilly Media, Inc.".
1 out of 17
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
© 2024 | Zucol Services PVT LTD | All rights reserved.



