Ask a question from expert
COIT20262 Assignment on Advanced Network Security
7 Pages3001 Words163 Views
Advanced Network Security (COIT20262)
Added on 2019-10-09
COIT20262 Assignment on Advanced Network Security
Advanced Network Security (COIT20262)
Added on 2019-10-09
BookmarkShareRelated Documents
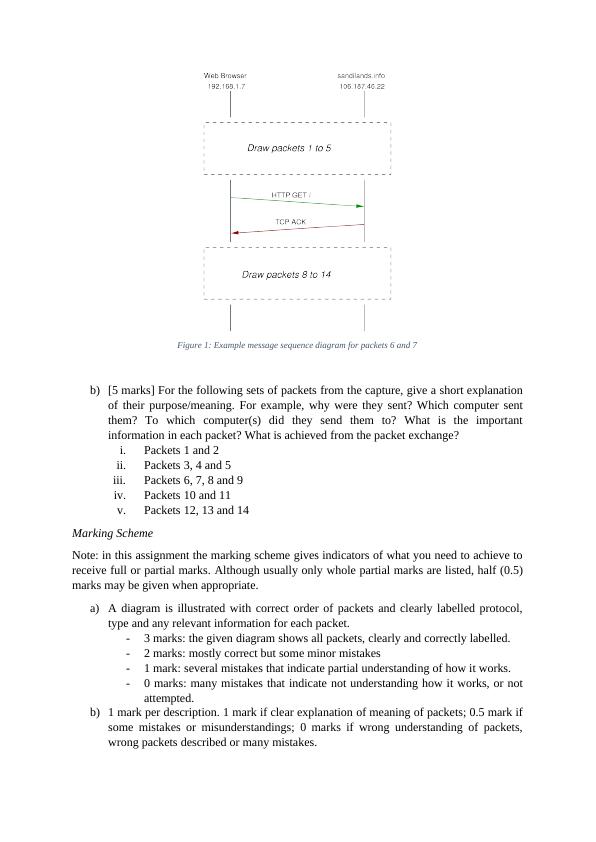
COIT20262 – Advanced Network Security, Term 2, 2016Assignment 1Due date:5pm Friday 26 August 2016 (Week 6)ASSESSMENTWeighting:40%1Length:N/ANote: Attempt all questionsAssignment SubmissionYour assignment must be in Microsoft Word format, and must be submitted electronically bythe due date via the Moodle website.Question 1 - Protocol Analysis with Wireshark[8 marks]Objective: gain a good understanding of common Internet protocols as well as using packetcapture software (Wireshark).The file a01-assignment-1-question-1-capture.pcap on Moodle contains packetscaptured in an exchange between several computers. Use the file to answer the following sub-questions. Some sub-questions refer to only a specific set of packets in the capture.a)[3 marks] Considering all the packets in the file, draw a message sequence diagramthat illustrates the packets. A message sequence diagram uses vertical lines torepresent events that happen at a computer over time (time is increasing as the linegoes down). Addresses of the computers/software are given at the top of the verticallines. Horizontal or sloped arrows are used to show messages (packets) being sentbetween computers. Each arrow should be labelled with the protocol, packet type andimportant information of the message. An example of a portion of the messagesequence diagram for packets 6 and 7 are shown below. You must draw a diagramthat shows all packets. Hints:-The packet times do not need to be shown, and the diagram does not have to bescale.-The example shows vertical lines representing two computers. You may needanother vertical line.
Figure 1: Example message sequence diagram for packets 6 and 7b)[5 marks] For the following sets of packets from the capture, give a short explanationof their purpose/meaning. For example, why were they sent? Which computer sentthem? To which computer(s) did they send them to? What is the importantinformation in each packet? What is achieved from the packet exchange?i.Packets 1 and 2ii.Packets 3, 4 and 5iii.Packets 6, 7, 8 and 9iv.Packets 10 and 11v.Packets 12, 13 and 14Marking SchemeNote: in this assignment the marking scheme gives indicators of what you need to achieve toreceive full or partial marks. Although usually only whole partial marks are listed, half (0.5)marks may be given when appropriate. a)A diagram is illustrated with correct order of packets and clearly labelled protocol,type and any relevant information for each packet. -3 marks: the given diagram shows all packets, clearly and correctly labelled. -2 marks: mostly correct but some minor mistakes-1 mark: several mistakes that indicate partial understanding of how it works.-0 marks: many mistakes that indicate not understanding how it works, or notattempted.b)1 mark per description. 1 mark if clear explanation of meaning of packets; 0.5 mark ifsome mistakes or misunderstandings; 0 marks if wrong understanding of packets,wrong packets described or many mistakes.
Question 2 – Application Attacks[14 marks]Objective: be able to interpret packet captures and identify security weaknesses in webapplications.You have performed a man-in-the-middle attack allowing you to capture packets betweentwo computers. The two computers are named/addressed as follows:Web Browser computer: 192.168.1.11Web Server computer: 192.168.2.21The website is a university grading system: students and staff can log in and view grades ofcourses they are involved with (staff or admin users can also edit grades). Students should notbe able to view other students’ grades, nor edit grades. The packets you captured are in file a01-assignment-1-question-2-capture.pcap (onMoodle). They involve a student, with student ID 5012345678, on the web browser computerusing the grading website. Unfortunately (for you) the actual login packets were encrypted(using HTTPS) and therefore are not included in the file. Only the packets from after thelogin are in the file.By using only the file a01-assignment-1-question-2-capture.pcap and the informationin this question, answer the following sub-questions.a)[3 marks] Describe the actions of the student using the web browser. That is, give thelinks they clicked on (or typed in), the exact time when they clicked on it (relative tothe first packet captured), any parameters or form fields they filled in, and what wasdisplayed on their web browser as a result. You may give your answer as a list, forexample:-At time 0.0 the student clicked on link ... . As a result they were shown a webpagethat welcomed them, had a link to “View grades”, “Logout” and to several helppages.-At time ...b)[2 marks] List all information you know about the student’s computer (includingaddresses and software it uses). For each item of information, explain where youfound the item in the capture. For example, one item of information is the IP address:-The student’s computer has IP address 192.168.1.11 as identified in the IP headerof each packet.-The student’s computer ...c)[3 marks] Explain how you could use the captured packets to perform an attack thatallows you to login as the student. In your answer, refer to the packets (andinformation in them) that allow the attack and give a general explanation of how toperform the attack.
End of preview
Want to access all the pages? Upload your documents or become a member.
Related Documents
COIT20262 - Advanced Network Security | Wiresharklg...
|3
|978
|100
Wireshark: Analyzing Load Distribution, Throughput, Time Sequence and Flow Graphslg...
|22
|1577
|403
COIT20262 - Advanced Network Security | Assignmentlg...
|3
|999
|253
COIT20261 Network Routing and Switching Term 1, 2019 - Written Assessment-1lg...
|4
|740
|36
COIT20261 Network Routing and SwitchingTerm 1, 2019 - Written Assessment-1lg...
|4
|741
|56