Wireless and BYOD Security Plan
VerifiedAdded on 2022/10/12
|22
|4308
|96
AI Summary
This report discusses the security threats of BYOD and wireless networks, including rogue access points, cyber kill chain, and identity theft. It also covers how to prevent identity theft and MAC spoofing, legal issues for investigation, and the importance of remote configuration management. The report concludes with a discussion of different types of wireless networks and their advantages and disadvantages.
Contribute Materials
Your contribution can guide someone’s learning journey. Share your
documents today.

COMPUTER INFORMATION SYSTEM
STUDENT NAME
PROFESSOR’S NAME
DATE
STUDENT NAME
PROFESSOR’S NAME
DATE
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
Executive Summary
The attacks which comes with BYOD is both passive and active attacks.The passive
attacks are the attacks whereby the person who is not authorized monitors the communication
which takes place in the WLAN. The passive attacker doesn’t alter, generate or rather disrupt the
Wireless Local Area Network Connection. In the passive attacks, it is also categorized into two
type which includes the following, (“NIST Special Publication 800-94, Guide to Intrusion
Detection and Prevention Systems”, n.d);
Eavesdropping: this is the attacker that monitors the data which is being transmitted over
the WLAN in order to get the content of the message.
Traffic Analysis: This is where the attacker just creates an intelligent platform of
monitoring the pattern at which the transmission over the WLAN is done
The active attacks are where the person who is not authorized alters, generates and disrupt
the communication over the WLAN network. In the active security threats, the following are its
sub categories;
Masquerading: this is where the attacker will impersonate as the authorized user of the
system in order to gain access to the privileges which are not authorized.
Replay: This is where the attackers’ monitors data transmission and in turn retransmits the
same data as legitimate user in the network.
Message modification: this is where the attacker recreates the original message by either
adding, changing, editing or deleting the message which was original.
The attacks which comes with BYOD is both passive and active attacks.The passive
attacks are the attacks whereby the person who is not authorized monitors the communication
which takes place in the WLAN. The passive attacker doesn’t alter, generate or rather disrupt the
Wireless Local Area Network Connection. In the passive attacks, it is also categorized into two
type which includes the following, (“NIST Special Publication 800-94, Guide to Intrusion
Detection and Prevention Systems”, n.d);
Eavesdropping: this is the attacker that monitors the data which is being transmitted over
the WLAN in order to get the content of the message.
Traffic Analysis: This is where the attacker just creates an intelligent platform of
monitoring the pattern at which the transmission over the WLAN is done
The active attacks are where the person who is not authorized alters, generates and disrupt
the communication over the WLAN network. In the active security threats, the following are its
sub categories;
Masquerading: this is where the attacker will impersonate as the authorized user of the
system in order to gain access to the privileges which are not authorized.
Replay: This is where the attackers’ monitors data transmission and in turn retransmits the
same data as legitimate user in the network.
Message modification: this is where the attacker recreates the original message by either
adding, changing, editing or deleting the message which was original.
Table of Contents
Executive Summary...................................................................................................................................2
Introduction................................................................................................................................................5
Wireless and BYOD Security Plan............................................................................................................5
Threats of Rogue Access Points................................................................................................................5
Detecting Rogue and authorized Access Points.......................................................................................5
Cyber Kill Chain.........................................................................................................................................5
Tracking Suspicious behavior...................................................................................................................6
How to track location of company asset..................................................................................................6
Identity Theft and MAC Spoofing in workplace........................................................................................7
How to prevent Identity Theft and MAC spoofing....................................................................................7
Legal issues for the investigation action...................................................................................................8
Pre- investigation.....................................................................................................................................8
Authorization............................................................................................................................................8
Continuous Improvement Plan...............................................................................................................10
Wired Equivalent Privacy (WEP).............................................................................................................10
Wi- Fi Protected Access Network...........................................................................................................10
Remote Configuration Management.......................................................................................................14
Removing unauthorized person from the network................................................................................14
Employee Misconduct..............................................................................................................................16
Ad Hoc wireless network........................................................................................................................16
Ad Hoc Threats and Vulnerability to the company.................................................................................17
Ad hoc threats prevention......................................................................................................................17
Self-configuring dynamic networks on open access architecture...........................................................18
SSID........................................................................................................................................................19
Conclusion.................................................................................................................................................20
References..............................................................................................................................................21
Executive Summary...................................................................................................................................2
Introduction................................................................................................................................................5
Wireless and BYOD Security Plan............................................................................................................5
Threats of Rogue Access Points................................................................................................................5
Detecting Rogue and authorized Access Points.......................................................................................5
Cyber Kill Chain.........................................................................................................................................5
Tracking Suspicious behavior...................................................................................................................6
How to track location of company asset..................................................................................................6
Identity Theft and MAC Spoofing in workplace........................................................................................7
How to prevent Identity Theft and MAC spoofing....................................................................................7
Legal issues for the investigation action...................................................................................................8
Pre- investigation.....................................................................................................................................8
Authorization............................................................................................................................................8
Continuous Improvement Plan...............................................................................................................10
Wired Equivalent Privacy (WEP).............................................................................................................10
Wi- Fi Protected Access Network...........................................................................................................10
Remote Configuration Management.......................................................................................................14
Removing unauthorized person from the network................................................................................14
Employee Misconduct..............................................................................................................................16
Ad Hoc wireless network........................................................................................................................16
Ad Hoc Threats and Vulnerability to the company.................................................................................17
Ad hoc threats prevention......................................................................................................................17
Self-configuring dynamic networks on open access architecture...........................................................18
SSID........................................................................................................................................................19
Conclusion.................................................................................................................................................20
References..............................................................................................................................................21
Table Of Figures
Figure 1: Cyber Kill Chain...........................................................................................................................6
Figure 2: Ad Hoc Network diagram...........................................................................................................16
Figure 3: SSID Name.................................................................................................................................19
Figure 4: SSID enabling and disabling.......................................................................................................20
Figure 1: Cyber Kill Chain...........................................................................................................................6
Figure 2: Ad Hoc Network diagram...........................................................................................................16
Figure 3: SSID Name.................................................................................................................................19
Figure 4: SSID enabling and disabling.......................................................................................................20
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
Introduction
The Bring Your Own Device has come with a lot of security threats as each employee in a
company make connection using their own devices.
Wireless and BYOD Security Plan
Threats of Rogue Access Points
Rogue access points are the wireless network which has been set by the attacker with core
intentions of having unauthorized access to the main network. Rogue access point in the company
it regarded as the silent killer of the security in the company premise. The access point opens a
platform for unauthorized parties to gain access to the network system of the company. The
attacker is able of runner different type of the vulnerability scanners which enables them to attack
the system remotely without being inside the company premise (Beyah & Venkataraman, 2011).
Detecting Rogue and authorized Access Points
Rogue networks can be detected by the use of the netstumbler software where the admin
will run the software on the laptop in order to detect all the wireless networks which are available
in the broadcasting area. The software has the GPS integration which identifies the location
where the rogue access point is coming from. This is the most common way of detecting the
rogue Access Points (Beyah & Venkataraman, 2011).
Authorized access point have got identified names when the scanner is done, all the
networks will be listed and the admin will be able to know the rogue and the right access points.
The Bring Your Own Device has come with a lot of security threats as each employee in a
company make connection using their own devices.
Wireless and BYOD Security Plan
Threats of Rogue Access Points
Rogue access points are the wireless network which has been set by the attacker with core
intentions of having unauthorized access to the main network. Rogue access point in the company
it regarded as the silent killer of the security in the company premise. The access point opens a
platform for unauthorized parties to gain access to the network system of the company. The
attacker is able of runner different type of the vulnerability scanners which enables them to attack
the system remotely without being inside the company premise (Beyah & Venkataraman, 2011).
Detecting Rogue and authorized Access Points
Rogue networks can be detected by the use of the netstumbler software where the admin
will run the software on the laptop in order to detect all the wireless networks which are available
in the broadcasting area. The software has the GPS integration which identifies the location
where the rogue access point is coming from. This is the most common way of detecting the
rogue Access Points (Beyah & Venkataraman, 2011).
Authorized access point have got identified names when the scanner is done, all the
networks will be listed and the admin will be able to know the rogue and the right access points.
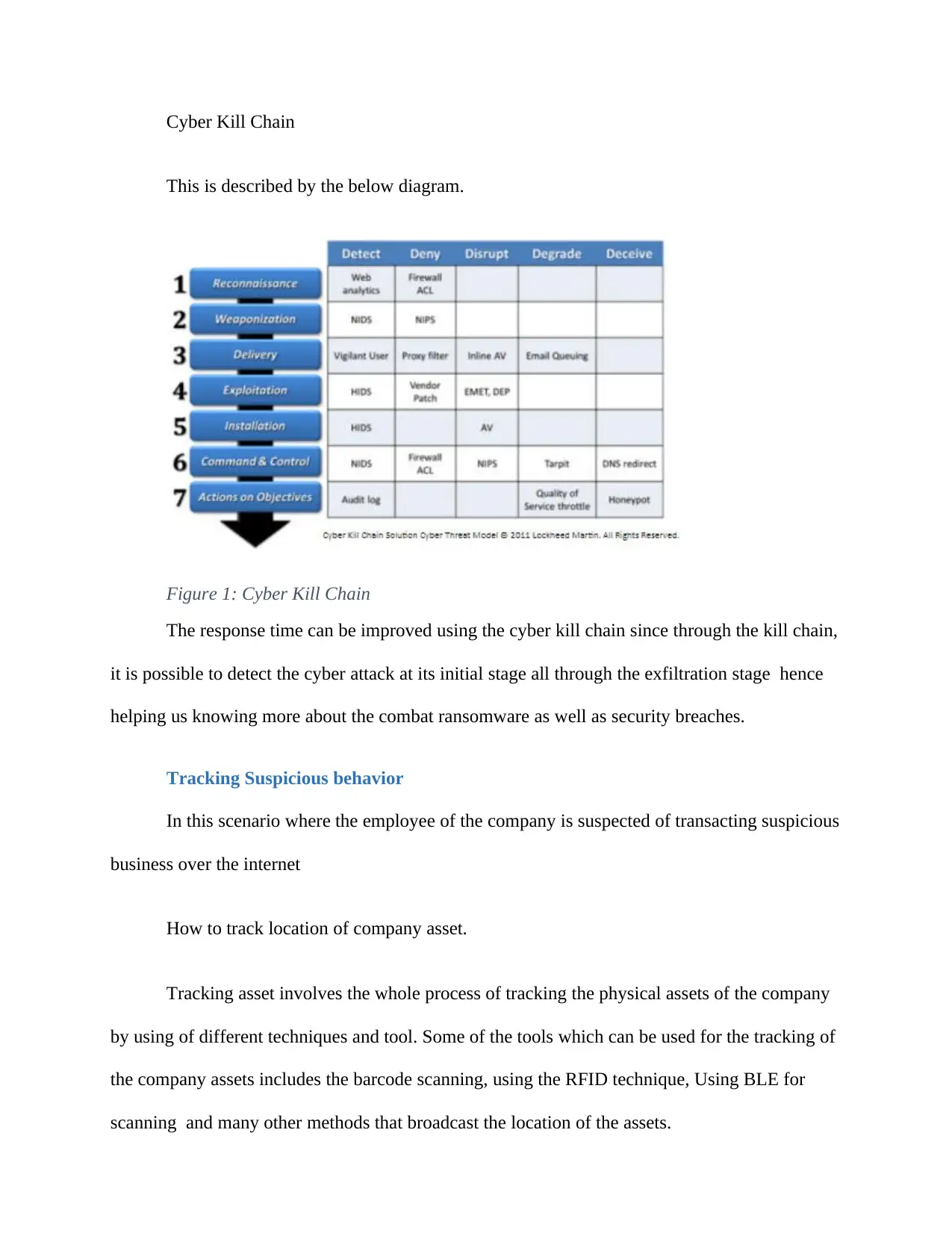
Cyber Kill Chain
This is described by the below diagram.
Figure 1: Cyber Kill Chain
The response time can be improved using the cyber kill chain since through the kill chain,
it is possible to detect the cyber attack at its initial stage all through the exfiltration stage hence
helping us knowing more about the combat ransomware as well as security breaches.
Tracking Suspicious behavior
In this scenario where the employee of the company is suspected of transacting suspicious
business over the internet
How to track location of company asset.
Tracking asset involves the whole process of tracking the physical assets of the company
by using of different techniques and tool. Some of the tools which can be used for the tracking of
the company assets includes the barcode scanning, using the RFID technique, Using BLE for
scanning and many other methods that broadcast the location of the assets.
This is described by the below diagram.
Figure 1: Cyber Kill Chain
The response time can be improved using the cyber kill chain since through the kill chain,
it is possible to detect the cyber attack at its initial stage all through the exfiltration stage hence
helping us knowing more about the combat ransomware as well as security breaches.
Tracking Suspicious behavior
In this scenario where the employee of the company is suspected of transacting suspicious
business over the internet
How to track location of company asset.
Tracking asset involves the whole process of tracking the physical assets of the company
by using of different techniques and tool. Some of the tools which can be used for the tracking of
the company assets includes the barcode scanning, using the RFID technique, Using BLE for
scanning and many other methods that broadcast the location of the assets.
A company has different types of assets; hence different methods will be used for tracking
them. We have the assets which are portable and movable and other which are stationary.
Security concerns is always on the assets which are mobile and portable. In a company where
there are employees, it becomes very vital to do tracking of assets. For assets which can move or
moved from one place to another, GPS tracking technique can be used. Using this type of
tracking, the GPS device will be attached to each and every mobile assets within the company,
the device will be showing the current location of the assets in there real time basis. The general
Positioning System will be sending signals with updates on the current position and location of
the assets hence making it very possible for the company to know where there assets are exactly.
Identity Theft and MAC Spoofing in workplace
Identity theft is when an imposter stages and impersonates as someone else in the work
place. In the place where the company is employing the use of BYOD technique, identity fraud is
commonly witnessed. Since each person is able to create connection to the network and do
transactions over the network, another person can get an employees login credentials to the
system, use his/her own device to login and impersonate as the employee ("3 Ways to Spoof a
MAC Address - wikihow.tech", n.d.). Hence making transaction freely over the internet using the
security keys of another person.
MAC spoofing which is the process where the MAC address of the networked device is
altered and redirected to another device, can also happen in the company where BYOD has been
employed. This is where the attacker will just come and make changes to another person device
MAC address so that when the attacker operates the device, it will be like the other person since
the MAC address of the other person is what is active in the network ("How (and Why) to
Change Your MAC Address on Windows, Linux ...", n.d.).
them. We have the assets which are portable and movable and other which are stationary.
Security concerns is always on the assets which are mobile and portable. In a company where
there are employees, it becomes very vital to do tracking of assets. For assets which can move or
moved from one place to another, GPS tracking technique can be used. Using this type of
tracking, the GPS device will be attached to each and every mobile assets within the company,
the device will be showing the current location of the assets in there real time basis. The general
Positioning System will be sending signals with updates on the current position and location of
the assets hence making it very possible for the company to know where there assets are exactly.
Identity Theft and MAC Spoofing in workplace
Identity theft is when an imposter stages and impersonates as someone else in the work
place. In the place where the company is employing the use of BYOD technique, identity fraud is
commonly witnessed. Since each person is able to create connection to the network and do
transactions over the network, another person can get an employees login credentials to the
system, use his/her own device to login and impersonate as the employee ("3 Ways to Spoof a
MAC Address - wikihow.tech", n.d.). Hence making transaction freely over the internet using the
security keys of another person.
MAC spoofing which is the process where the MAC address of the networked device is
altered and redirected to another device, can also happen in the company where BYOD has been
employed. This is where the attacker will just come and make changes to another person device
MAC address so that when the attacker operates the device, it will be like the other person since
the MAC address of the other person is what is active in the network ("How (and Why) to
Change Your MAC Address on Windows, Linux ...", n.d.).
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
How to prevent Identity Theft and MAC spoofing
Identity theft in a company which has allowed BYOD can be protected by taking into
account the following measures, this includes the following;
a. Advising the employees to guard there social security numbers for there
devices so prevent attackers and identity frauds from accessing there system.
b. Being careful while entering their login credential especially while in
public as the identity thieves are very creative, they can steal information secretly.
MAC spoofing can be prevented but encouraging the employees to configure there
devices for VPN connection in order to prevent the attackers from identifying them on a network.
Using VPN, it is very hard for the attacker to know the MAC address of another networked
device ("How to spoof a MAC address - TechRepublic", n.d.).
It is not feasible to determine if MAC spoofing has taken place in the workplace since
during investigation, there was no trace of MAC spoofing which was noted as the suspicious
actions of the employee was on identify theft.
Legal issues for the investigation action
Under normal circumstances, if there is suspicion over unwarranted behavior for one of
the employees, the investigation team is free to carry out the investigation without interfering
with the confidential information of another person. As far as investigation is allowed, them there
are limited as far as protection over another persons confidential information is concerned.
Pre- investigation
Identity theft in a company which has allowed BYOD can be protected by taking into
account the following measures, this includes the following;
a. Advising the employees to guard there social security numbers for there
devices so prevent attackers and identity frauds from accessing there system.
b. Being careful while entering their login credential especially while in
public as the identity thieves are very creative, they can steal information secretly.
MAC spoofing can be prevented but encouraging the employees to configure there
devices for VPN connection in order to prevent the attackers from identifying them on a network.
Using VPN, it is very hard for the attacker to know the MAC address of another networked
device ("How to spoof a MAC address - TechRepublic", n.d.).
It is not feasible to determine if MAC spoofing has taken place in the workplace since
during investigation, there was no trace of MAC spoofing which was noted as the suspicious
actions of the employee was on identify theft.
Legal issues for the investigation action
Under normal circumstances, if there is suspicion over unwarranted behavior for one of
the employees, the investigation team is free to carry out the investigation without interfering
with the confidential information of another person. As far as investigation is allowed, them there
are limited as far as protection over another persons confidential information is concerned.
Pre- investigation
Before any kind of investigation is done, them the investigator has to be authorized to
carry out the said investigation by the legal departments in the government and the company. The
suspect has to be notified and to be given consent of the upcoming investigation over suspicious
behavior noted in the past.
Authorization
Yes, I was authorized before investigation begun. The matter was reported to the central
department and was authorized to carry on with the investigation for the same. The notification
was valid over the investigation as the person was consent of the upcoming investigation which
was to take place on his/her docket.
carry out the said investigation by the legal departments in the government and the company. The
suspect has to be notified and to be given consent of the upcoming investigation over suspicious
behavior noted in the past.
Authorization
Yes, I was authorized before investigation begun. The matter was reported to the central
department and was authorized to carry on with the investigation for the same. The notification
was valid over the investigation as the person was consent of the upcoming investigation which
was to take place on his/her docket.
Continuous Improvement Plan
Wired Equivalent Privacy (WEP)
The WEP is a protocol of security which is also specified in the standards of the Wireless
Fidelity, which is designed in order to provide the WLAN with a security level and privacy that is
compared to the Wired LAN. USING THE Wired equivalent privacy, the radio waves are
encrypted over the WLAN. This in turn gives protection to the wireless link which is vulnerable
in between the access point and the client (Mohapatra & Prakash, 2010). This type of privacy has
made it possible for the Wireless local area network to have the same type and level of security
which the Wired local area network has.
Wi- Fi Protected Access Network
This is also called WPA2, which is a standard of security for all the users of computer
based devices which is equipped with the Wireless Connection of internet. This was developed
by the Wi Fi alliance in order to give a provision of the most complex encryption of data as well
as the best authentication of the user as compared to the Wired equivalent Privacy (Eissa, Ali &
Abdel-Latif, 2013). The WPA has the personal and the enterprise mode of discretion. For the
enterprise use, the privacy makes use of the 802.1x stringent mode of authentication together
with the Extensible Authentication Protocol also abbreviated as the EAP. For the enterprise use,
the use of authentication server is required. For the personal use, the privacy makes use of the pre
shared keys in order to make is simple for the management as well as implementation among the
consumers (Eissa, Ali & Abdel-Latif, 2013). The Pre shared key is the secret key that is shared
previously just between only tow parties by the use of some connections and channels which are
Wired Equivalent Privacy (WEP)
The WEP is a protocol of security which is also specified in the standards of the Wireless
Fidelity, which is designed in order to provide the WLAN with a security level and privacy that is
compared to the Wired LAN. USING THE Wired equivalent privacy, the radio waves are
encrypted over the WLAN. This in turn gives protection to the wireless link which is vulnerable
in between the access point and the client (Mohapatra & Prakash, 2010). This type of privacy has
made it possible for the Wireless local area network to have the same type and level of security
which the Wired local area network has.
Wi- Fi Protected Access Network
This is also called WPA2, which is a standard of security for all the users of computer
based devices which is equipped with the Wireless Connection of internet. This was developed
by the Wi Fi alliance in order to give a provision of the most complex encryption of data as well
as the best authentication of the user as compared to the Wired equivalent Privacy (Eissa, Ali &
Abdel-Latif, 2013). The WPA has the personal and the enterprise mode of discretion. For the
enterprise use, the privacy makes use of the 802.1x stringent mode of authentication together
with the Extensible Authentication Protocol also abbreviated as the EAP. For the enterprise use,
the use of authentication server is required. For the personal use, the privacy makes use of the pre
shared keys in order to make is simple for the management as well as implementation among the
consumers (Eissa, Ali & Abdel-Latif, 2013). The Pre shared key is the secret key that is shared
previously just between only tow parties by the use of some connections and channels which are
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
very much secure just before it is used. In order to build the key from the secret shared. The
derivation key function is supposed to be used.
Wireless network are of different types, each and every wireless network has its
advantages and disadvantages. In this report, only four types of wireless networks will be
discussed. This includes the following.
a. Bluetooth
This is a wireless technology which allows the exchange of data between devices
which are fixed in nature. The range at which Bluetooth is able to create connection is a
very short distance of up to 10 meters. The Bluetooth is in the Wireless Personal Area
network category of the wireless networks.
b. Wireless Local Area Network
This is the network which creates link with two and more devices in a short
distance by the use of the wireless method of distribution by providing connection over
the access point in order for the internet to be accessed (Eissa, Ali & Abdel-Latif, 2013).
c. Wireless ad hoc network
This is also called the mesh network, this is a network which is made up of the
nodes of radio which is organized in the mesh technology. In this type of a network, every
node of the network forwards the messages in place of the other node and each and every
node perform the routing.
derivation key function is supposed to be used.
Wireless network are of different types, each and every wireless network has its
advantages and disadvantages. In this report, only four types of wireless networks will be
discussed. This includes the following.
a. Bluetooth
This is a wireless technology which allows the exchange of data between devices
which are fixed in nature. The range at which Bluetooth is able to create connection is a
very short distance of up to 10 meters. The Bluetooth is in the Wireless Personal Area
network category of the wireless networks.
b. Wireless Local Area Network
This is the network which creates link with two and more devices in a short
distance by the use of the wireless method of distribution by providing connection over
the access point in order for the internet to be accessed (Eissa, Ali & Abdel-Latif, 2013).
c. Wireless ad hoc network
This is also called the mesh network, this is a network which is made up of the
nodes of radio which is organized in the mesh technology. In this type of a network, every
node of the network forwards the messages in place of the other node and each and every
node perform the routing.
d. Wireless Metropolitan Area Network
This is the type of network which is made up of the connection of several wireless
Local Area Network put in place. It serves at least an larger area since several WLAN
have been connected together.
Advantages of the wireless network
i. This technology is very much affordable in terms of cost
ii. It does not need any extra space for its operation
iii. It does not need cable or wired connection in order to connect with other
devices
iv. This technology is very reliable and easy in terms of usage.
v. The network is fully secure as it involves the exchange of data between
only two devices.
Disadvantages of the wireless network
i. Wireless network can only serve within the shortest range of at least 10 m
to 30 meters.
ii. They are always interfered with the radio signals
iii. The rate at which data is being transferred over the wireless network is
very slow as compared to the wired network.
iv. The wireless network always has health problems that comes with it.
v. The cost of purchasing communication devices is very high.
This is the type of network which is made up of the connection of several wireless
Local Area Network put in place. It serves at least an larger area since several WLAN
have been connected together.
Advantages of the wireless network
i. This technology is very much affordable in terms of cost
ii. It does not need any extra space for its operation
iii. It does not need cable or wired connection in order to connect with other
devices
iv. This technology is very reliable and easy in terms of usage.
v. The network is fully secure as it involves the exchange of data between
only two devices.
Disadvantages of the wireless network
i. Wireless network can only serve within the shortest range of at least 10 m
to 30 meters.
ii. They are always interfered with the radio signals
iii. The rate at which data is being transferred over the wireless network is
very slow as compared to the wired network.
iv. The wireless network always has health problems that comes with it.
v. The cost of purchasing communication devices is very high.
vi. The wireless network makes use of the infrared signals which only travels
in a straight line and they are always interfered with the objects and walls.
For the company, the WLAN is therefore the most suitable to be used.
in a straight line and they are always interfered with the objects and walls.
For the company, the WLAN is therefore the most suitable to be used.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Remote Configuration Management
The remote configuration management is defined as the process under which the admin of
the company takes the full management and control of the operations of the company by the use
of the remote. This type of management enables the admin of the network system to be able to
control the overall activities which are taking place in the network at central place remotely ("An
Introduction to Configuration Management | DigitalOcean", n.d.).
This method is very important in for the security enhancement. This is because the admin
is able to check and view everything which is taking place over the network. All the transactions
which are being done on the network is monitored centrally and remotely (Fu, Peng, Chen &
Yang, 2013). Any suspicious activity like unauthorized login by another person can be quickly
handled remotely and instantly. This has limited the number of MAC address spoofing in the
network and they are identified and removed as fast a s possible. Identity theft is also limited as
the transaction are being monitored remotely ("Installation and Configuration for Windows
Remote ...", n.d.).
Removing unauthorized person from the network
After identifying that there is undocumented person who has made the connection to the
network. The remote configuration management system will be able to list all the connections
which have been made to the network. The time at which the connection was made and the time
in which the connection has been will also be listed. All the connections which have been made
legally are always documented in the remote management system. Any other connection made
apart of the legal connections are regarded as undocumented and therefore they are suspicious
The remote configuration management is defined as the process under which the admin of
the company takes the full management and control of the operations of the company by the use
of the remote. This type of management enables the admin of the network system to be able to
control the overall activities which are taking place in the network at central place remotely ("An
Introduction to Configuration Management | DigitalOcean", n.d.).
This method is very important in for the security enhancement. This is because the admin
is able to check and view everything which is taking place over the network. All the transactions
which are being done on the network is monitored centrally and remotely (Fu, Peng, Chen &
Yang, 2013). Any suspicious activity like unauthorized login by another person can be quickly
handled remotely and instantly. This has limited the number of MAC address spoofing in the
network and they are identified and removed as fast a s possible. Identity theft is also limited as
the transaction are being monitored remotely ("Installation and Configuration for Windows
Remote ...", n.d.).
Removing unauthorized person from the network
After identifying that there is undocumented person who has made the connection to the
network. The remote configuration management system will be able to list all the connections
which have been made to the network. The time at which the connection was made and the time
in which the connection has been will also be listed. All the connections which have been made
legally are always documented in the remote management system. Any other connection made
apart of the legal connections are regarded as undocumented and therefore they are suspicious
connections. The management system has the action perform to each and every connection made
("Installation and Configuration for Windows Remote ...", n.d.). The option to made deletion,
pause and many other necessary actions. Therefore, the connection is deleted from the system
and immediately it is halted. This is the easiest way to manage connections which are suspicious
to be illegal and unwarranted.
In order to show proof that the device has indeed been removed from the connection. First
the system will list all the removed device and will be listed in the removed section. All the
devices which has been removed from the system due to different reasons are always listed with
the MAC address and the time removed (Levin, 2009).
("Installation and Configuration for Windows Remote ...", n.d.). The option to made deletion,
pause and many other necessary actions. Therefore, the connection is deleted from the system
and immediately it is halted. This is the easiest way to manage connections which are suspicious
to be illegal and unwarranted.
In order to show proof that the device has indeed been removed from the connection. First
the system will list all the removed device and will be listed in the removed section. All the
devices which has been removed from the system due to different reasons are always listed with
the MAC address and the time removed (Levin, 2009).
Employee Misconduct
Ad Hoc wireless network
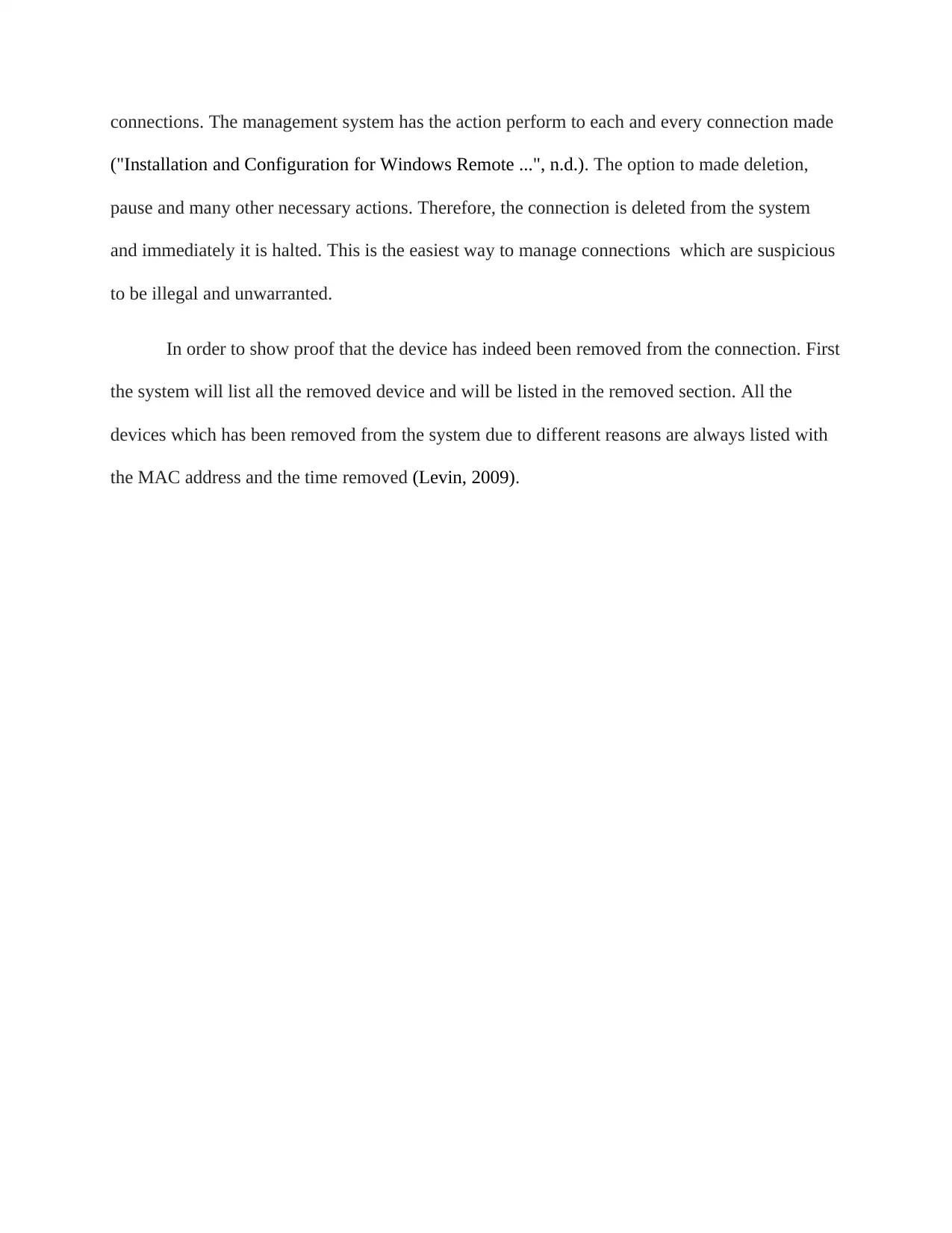
The term Ad hoc simply means the improvised or the makeshift. In its definition, the ad
hoc wireless network is defined as the impromptu, on demand device to device network type. By
the use of the ad hoc network mode, its is easy to set up the wireless connection which is direct to
any other device or the computer without connecting to the wifi or the router access point
(Pietrabissa, Liberati & Oddi, 2016). Naturally, the ad hoc connection does not at all need any
infrastructure to set it up or to get sustained in the network, the ad hoc is decentralized and
therefore is considered as the peer to peer network. Apart from making use of the router whereby
the users makes connections using other devices like the phones and the computers, in the ad hoc
network, any node which makes connections to each other, sends data in the whole structure of
connection (Schweitzer, Stulman, Hirst, Margalit & Shabtai, 2019).
Ad Hoc wireless network
The term Ad hoc simply means the improvised or the makeshift. In its definition, the ad
hoc wireless network is defined as the impromptu, on demand device to device network type. By
the use of the ad hoc network mode, its is easy to set up the wireless connection which is direct to
any other device or the computer without connecting to the wifi or the router access point
(Pietrabissa, Liberati & Oddi, 2016). Naturally, the ad hoc connection does not at all need any
infrastructure to set it up or to get sustained in the network, the ad hoc is decentralized and
therefore is considered as the peer to peer network. Apart from making use of the router whereby
the users makes connections using other devices like the phones and the computers, in the ad hoc
network, any node which makes connections to each other, sends data in the whole structure of
connection (Schweitzer, Stulman, Hirst, Margalit & Shabtai, 2019).
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
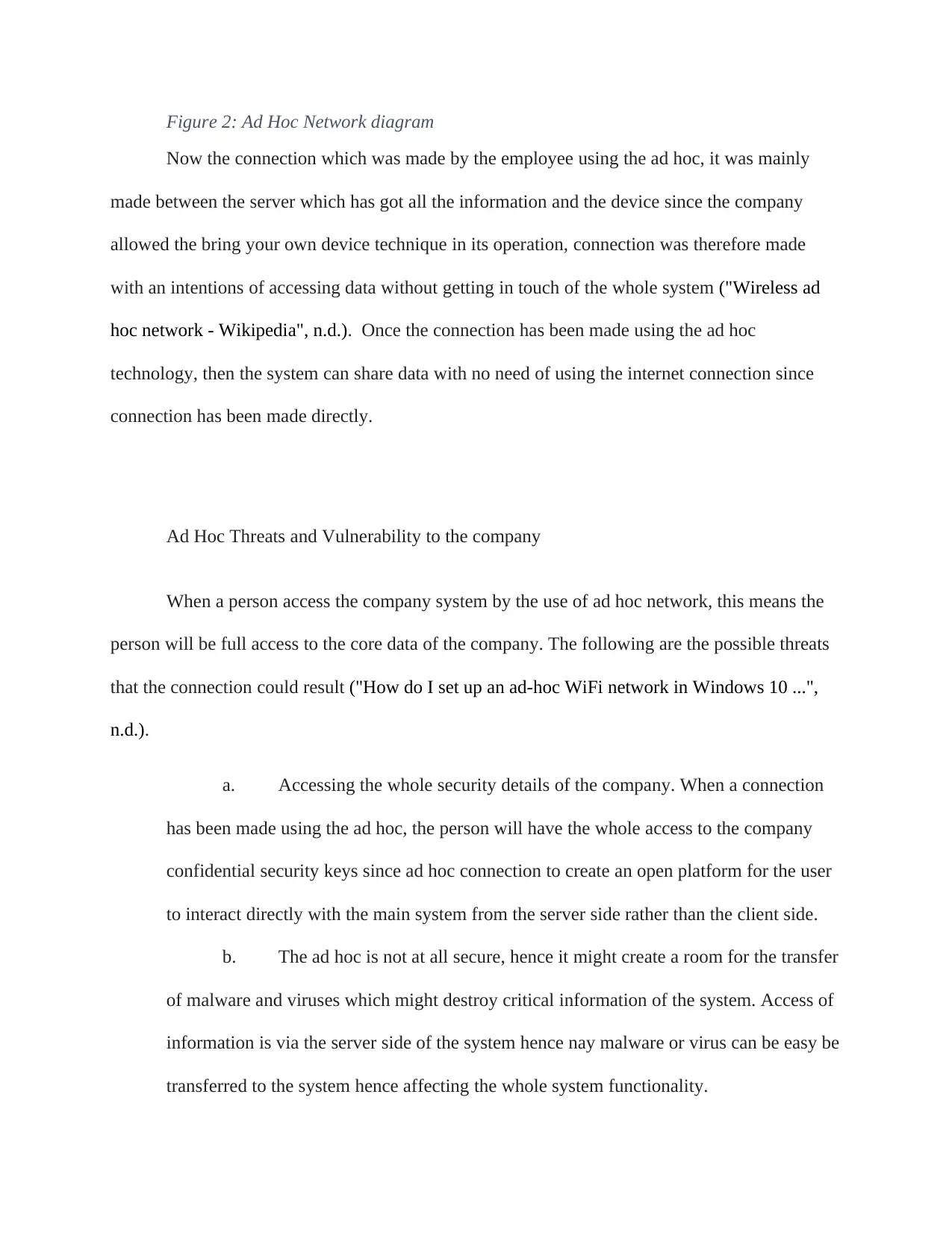
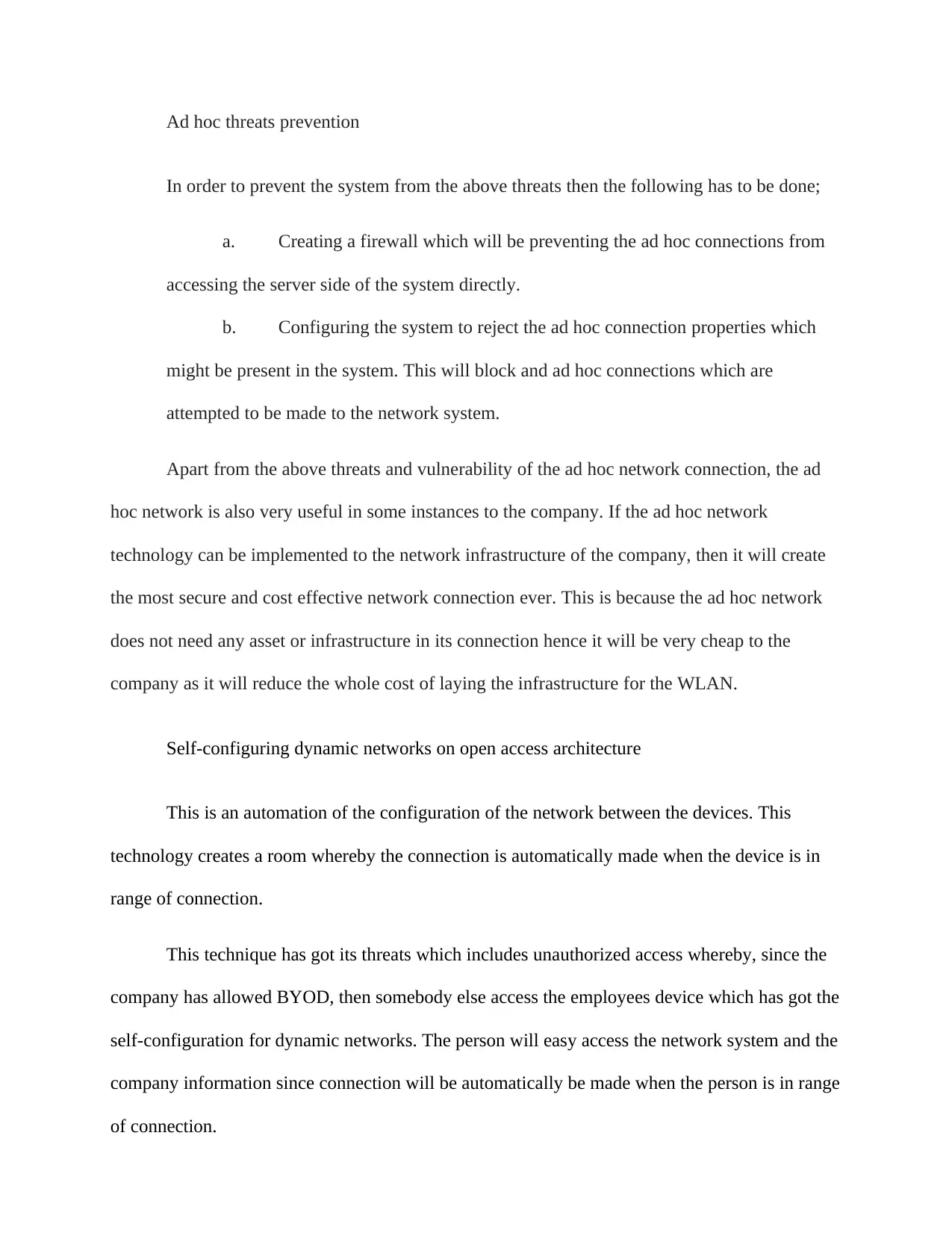
Figure 2: Ad Hoc Network diagram
Now the connection which was made by the employee using the ad hoc, it was mainly
made between the server which has got all the information and the device since the company
allowed the bring your own device technique in its operation, connection was therefore made
with an intentions of accessing data without getting in touch of the whole system ("Wireless ad
hoc network - Wikipedia", n.d.). Once the connection has been made using the ad hoc
technology, then the system can share data with no need of using the internet connection since
connection has been made directly.
Ad Hoc Threats and Vulnerability to the company
When a person access the company system by the use of ad hoc network, this means the
person will be full access to the core data of the company. The following are the possible threats
that the connection could result ("How do I set up an ad-hoc WiFi network in Windows 10 ...",
n.d.).
a. Accessing the whole security details of the company. When a connection
has been made using the ad hoc, the person will have the whole access to the company
confidential security keys since ad hoc connection to create an open platform for the user
to interact directly with the main system from the server side rather than the client side.
b. The ad hoc is not at all secure, hence it might create a room for the transfer
of malware and viruses which might destroy critical information of the system. Access of
information is via the server side of the system hence nay malware or virus can be easy be
transferred to the system hence affecting the whole system functionality.
Now the connection which was made by the employee using the ad hoc, it was mainly
made between the server which has got all the information and the device since the company
allowed the bring your own device technique in its operation, connection was therefore made
with an intentions of accessing data without getting in touch of the whole system ("Wireless ad
hoc network - Wikipedia", n.d.). Once the connection has been made using the ad hoc
technology, then the system can share data with no need of using the internet connection since
connection has been made directly.
Ad Hoc Threats and Vulnerability to the company
When a person access the company system by the use of ad hoc network, this means the
person will be full access to the core data of the company. The following are the possible threats
that the connection could result ("How do I set up an ad-hoc WiFi network in Windows 10 ...",
n.d.).
a. Accessing the whole security details of the company. When a connection
has been made using the ad hoc, the person will have the whole access to the company
confidential security keys since ad hoc connection to create an open platform for the user
to interact directly with the main system from the server side rather than the client side.
b. The ad hoc is not at all secure, hence it might create a room for the transfer
of malware and viruses which might destroy critical information of the system. Access of
information is via the server side of the system hence nay malware or virus can be easy be
transferred to the system hence affecting the whole system functionality.
Ad hoc threats prevention
In order to prevent the system from the above threats then the following has to be done;
a. Creating a firewall which will be preventing the ad hoc connections from
accessing the server side of the system directly.
b. Configuring the system to reject the ad hoc connection properties which
might be present in the system. This will block and ad hoc connections which are
attempted to be made to the network system.
Apart from the above threats and vulnerability of the ad hoc network connection, the ad
hoc network is also very useful in some instances to the company. If the ad hoc network
technology can be implemented to the network infrastructure of the company, then it will create
the most secure and cost effective network connection ever. This is because the ad hoc network
does not need any asset or infrastructure in its connection hence it will be very cheap to the
company as it will reduce the whole cost of laying the infrastructure for the WLAN.
Self-configuring dynamic networks on open access architecture
This is an automation of the configuration of the network between the devices. This
technology creates a room whereby the connection is automatically made when the device is in
range of connection.
This technique has got its threats which includes unauthorized access whereby, since the
company has allowed BYOD, then somebody else access the employees device which has got the
self-configuration for dynamic networks. The person will easy access the network system and the
company information since connection will be automatically be made when the person is in range
of connection.
In order to prevent the system from the above threats then the following has to be done;
a. Creating a firewall which will be preventing the ad hoc connections from
accessing the server side of the system directly.
b. Configuring the system to reject the ad hoc connection properties which
might be present in the system. This will block and ad hoc connections which are
attempted to be made to the network system.
Apart from the above threats and vulnerability of the ad hoc network connection, the ad
hoc network is also very useful in some instances to the company. If the ad hoc network
technology can be implemented to the network infrastructure of the company, then it will create
the most secure and cost effective network connection ever. This is because the ad hoc network
does not need any asset or infrastructure in its connection hence it will be very cheap to the
company as it will reduce the whole cost of laying the infrastructure for the WLAN.
Self-configuring dynamic networks on open access architecture
This is an automation of the configuration of the network between the devices. This
technology creates a room whereby the connection is automatically made when the device is in
range of connection.
This technique has got its threats which includes unauthorized access whereby, since the
company has allowed BYOD, then somebody else access the employees device which has got the
self-configuration for dynamic networks. The person will easy access the network system and the
company information since connection will be automatically be made when the person is in range
of connection.
This can be prevented by creating a two way authentication where when connection is
made, the admin in the remote configuration management system will be the one to authorize
connection.
As an incident manager, in order to detect an employee making connection to the self
configuration or the ad hoc network, the remote configuration manager will help in creating a
tracking of the devices which are being connected to the network.
Signal hiding in wireless network helps the attackers from accessing the network as the
signal that are responsible for creating connection would have been hidden from the unauthorized
connections.
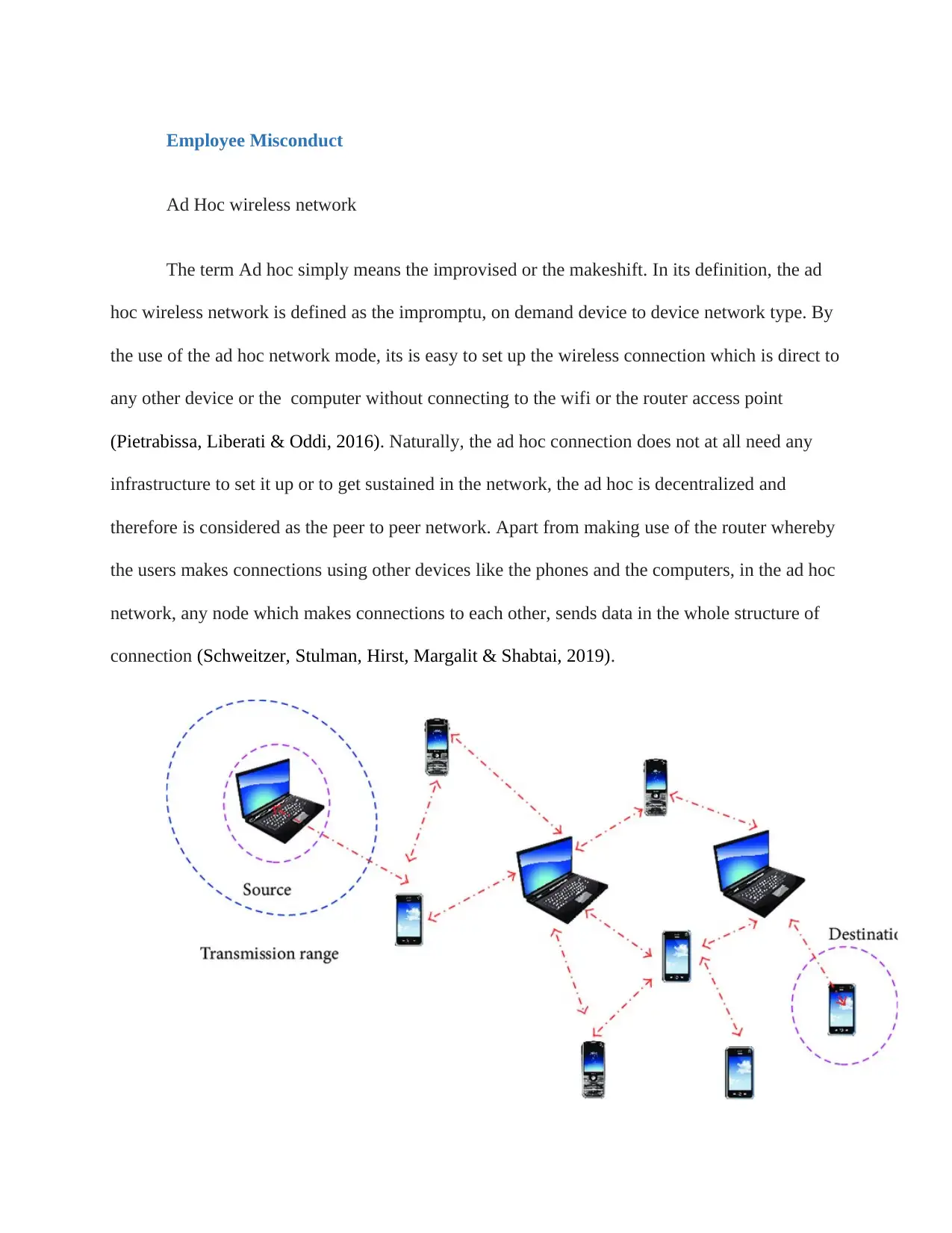
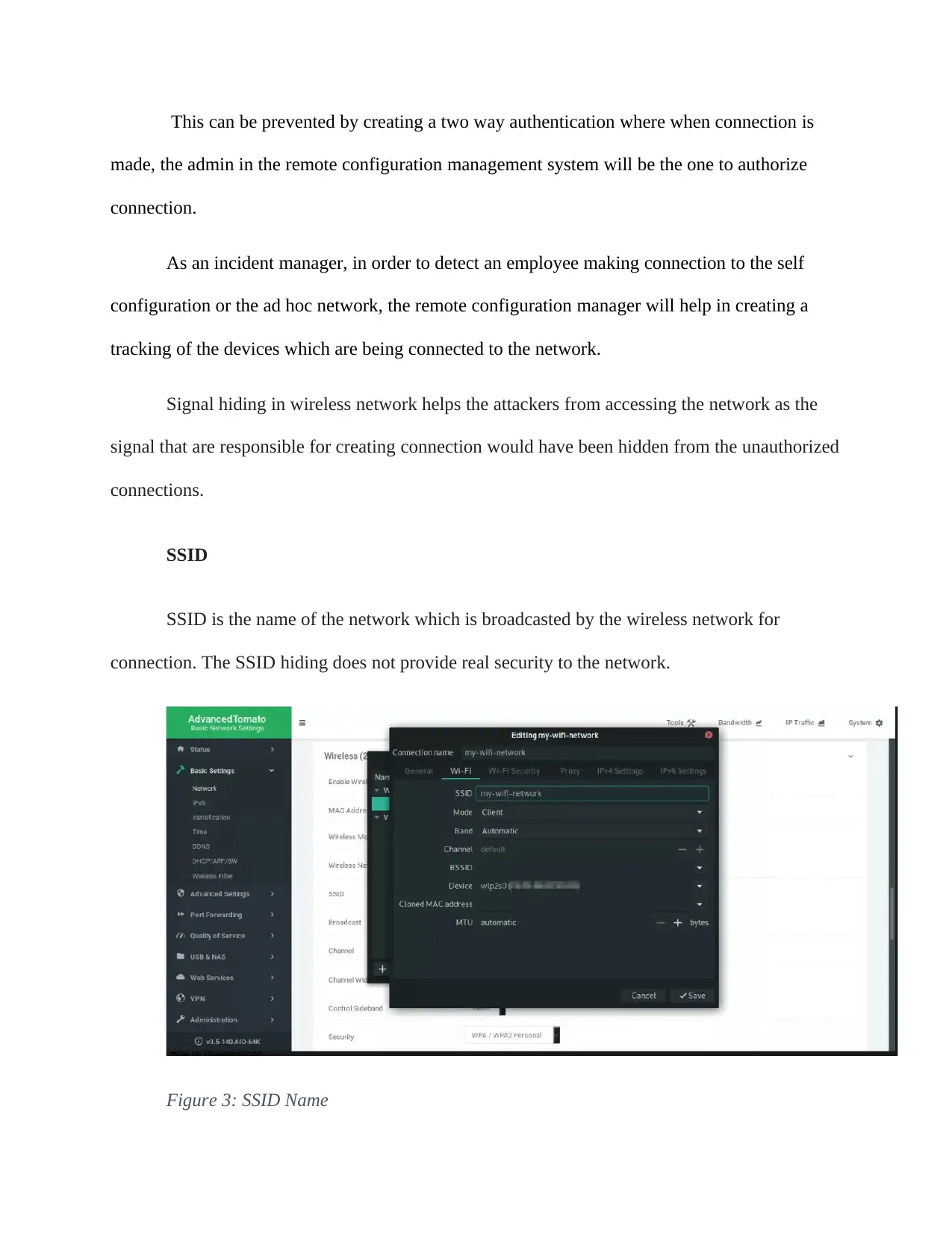
SSID
SSID is the name of the network which is broadcasted by the wireless network for
connection. The SSID hiding does not provide real security to the network.
Figure 3: SSID Name
made, the admin in the remote configuration management system will be the one to authorize
connection.
As an incident manager, in order to detect an employee making connection to the self
configuration or the ad hoc network, the remote configuration manager will help in creating a
tracking of the devices which are being connected to the network.
Signal hiding in wireless network helps the attackers from accessing the network as the
signal that are responsible for creating connection would have been hidden from the unauthorized
connections.
SSID
SSID is the name of the network which is broadcasted by the wireless network for
connection. The SSID hiding does not provide real security to the network.
Figure 3: SSID Name
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
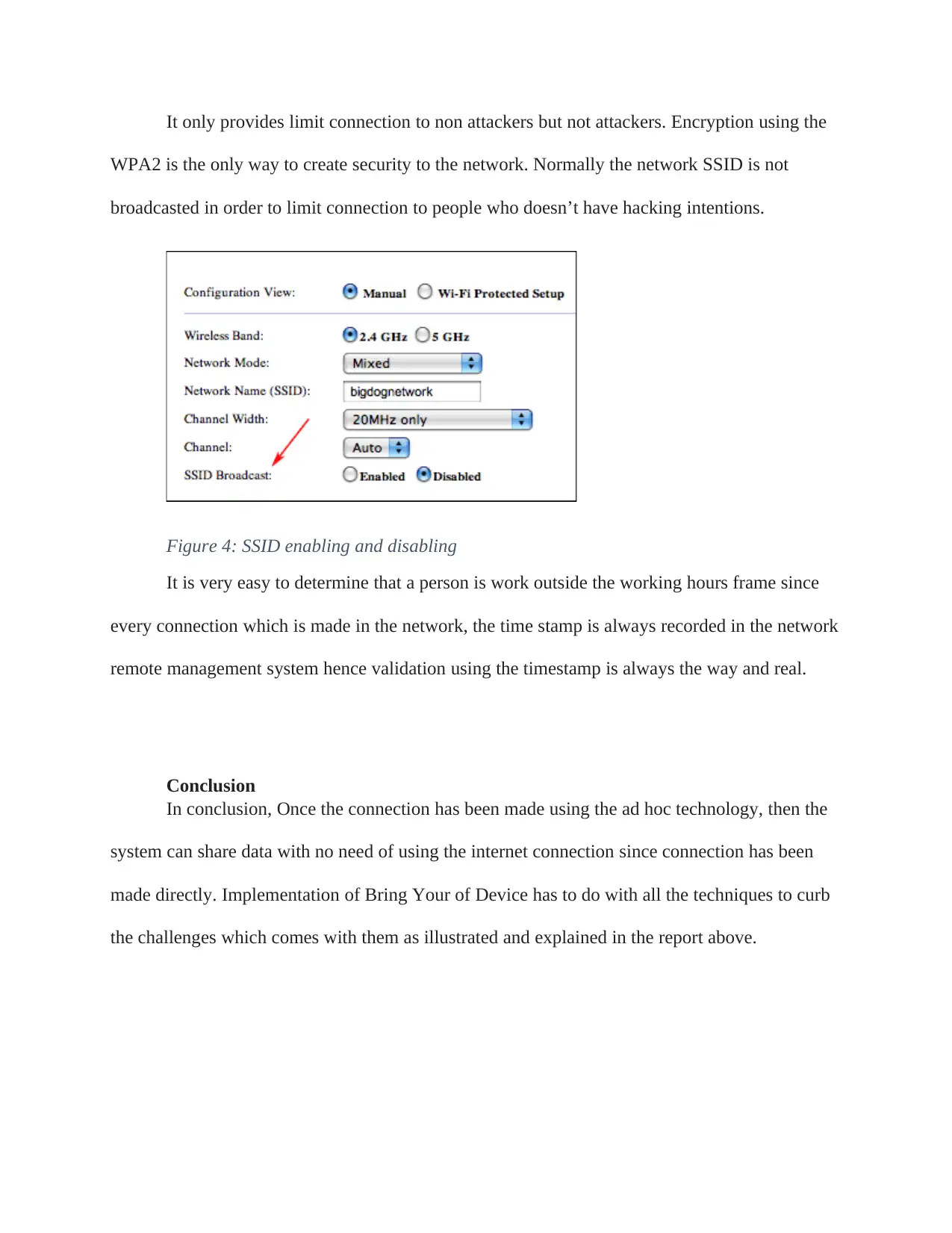
It only provides limit connection to non attackers but not attackers. Encryption using the
WPA2 is the only way to create security to the network. Normally the network SSID is not
broadcasted in order to limit connection to people who doesn’t have hacking intentions.
Figure 4: SSID enabling and disabling
It is very easy to determine that a person is work outside the working hours frame since
every connection which is made in the network, the time stamp is always recorded in the network
remote management system hence validation using the timestamp is always the way and real.
Conclusion
In conclusion, Once the connection has been made using the ad hoc technology, then the
system can share data with no need of using the internet connection since connection has been
made directly. Implementation of Bring Your of Device has to do with all the techniques to curb
the challenges which comes with them as illustrated and explained in the report above.
WPA2 is the only way to create security to the network. Normally the network SSID is not
broadcasted in order to limit connection to people who doesn’t have hacking intentions.
Figure 4: SSID enabling and disabling
It is very easy to determine that a person is work outside the working hours frame since
every connection which is made in the network, the time stamp is always recorded in the network
remote management system hence validation using the timestamp is always the way and real.
Conclusion
In conclusion, Once the connection has been made using the ad hoc technology, then the
system can share data with no need of using the internet connection since connection has been
made directly. Implementation of Bring Your of Device has to do with all the techniques to curb
the challenges which comes with them as illustrated and explained in the report above.
References
3 Ways to Spoof a MAC Address - wikihow.tech. Retrieved 2019, from
https://www.wikihow.tech/Spoof-a-MAC-Address
An Introduction to Configuration Management | DigitalOcean. Retrieved 2019, from
https://www.digitalocean.com/community/tutorials/an-introduction-to-configuration-
management
Eissa, M., Ali, I., & Abdel-Latif, K. (2013). Wi-Fi protected access for secure power network
protection scheme. International Journal Of Electrical Power & Energy Systems, 46, 414-424.
doi: 10.1016/j.ijepes.2012.10.034
FU, D., PENG, X., CHEN, G., & YANG, Q. (2013). Remote attestation mechanism of platform
configuration based on dynamic Huffman tree. Journal Of Computer Applications, 32(8),
2275-2279. doi: 10.3724/sp.j.1087.2012.02275
How (and Why) to Change Your MAC Address on Windows, Linux ... Retrieved 2019, from
https://www.howtogeek.com/192173/HOW-AND-WHY-TO-CHANGE-YOUR-MAC-
ADDRESS-ON-WINDOWS-LINUX-AND-MAC/
How do I set up an ad-hoc WiFi network in Windows 10 ... Retrieved 2019, from
https://answers.microsoft.com/en-us/windows/forum/windows_10-networking/how-do-i-set-
up-an-ad-hoc-wifi-network-in-windows/0caa92d8-e02f-4e7f-aa5c-0abf10ed2039
How to spoof a MAC address - TechRepublic. Retrieved 2019, from
https://www.techrepublic.com/blog/it-security/how-to-spoof-a-mac-address/
Installation and Configuration for Windows Remote ... Retrieved 2019, from
https://docs.microsoft.com/en-us/windows/win32/winrm/installation-and-configuration-for-
windows-remote-management
Levin, M. (2009). Combinatorial optimization in system configuration design. Automation And
Remote Control, 70(3), 519-561. doi: 10.1134/s0005117909030187
Mohapatra, A., & Prakash, N. (2010). Wired equivalent privacy reinvestigated. Journal Of
Discrete Mathematical Sciences And Cryptography, 13(2), 141-151. doi:
10.1080/09720529.2010.10698282
Guide to Intrusion Detection and Prevention Systems (IDPS), NIST Special Publication 800-94,
Retrieved 2007 from http://csrc.nist.gov/publications/PubsSPs.html#800-94.
Pietrabissa, A., Liberati, F., & Oddi, G. (2016). A distributed algorithm for Ad-hoc network
partitioning based on Voronoi Tessellation. Ad Hoc Networks, 46, 37-47. doi:
10.1016/j.adhoc.2016.03.008
3 Ways to Spoof a MAC Address - wikihow.tech. Retrieved 2019, from
https://www.wikihow.tech/Spoof-a-MAC-Address
An Introduction to Configuration Management | DigitalOcean. Retrieved 2019, from
https://www.digitalocean.com/community/tutorials/an-introduction-to-configuration-
management
Eissa, M., Ali, I., & Abdel-Latif, K. (2013). Wi-Fi protected access for secure power network
protection scheme. International Journal Of Electrical Power & Energy Systems, 46, 414-424.
doi: 10.1016/j.ijepes.2012.10.034
FU, D., PENG, X., CHEN, G., & YANG, Q. (2013). Remote attestation mechanism of platform
configuration based on dynamic Huffman tree. Journal Of Computer Applications, 32(8),
2275-2279. doi: 10.3724/sp.j.1087.2012.02275
How (and Why) to Change Your MAC Address on Windows, Linux ... Retrieved 2019, from
https://www.howtogeek.com/192173/HOW-AND-WHY-TO-CHANGE-YOUR-MAC-
ADDRESS-ON-WINDOWS-LINUX-AND-MAC/
How do I set up an ad-hoc WiFi network in Windows 10 ... Retrieved 2019, from
https://answers.microsoft.com/en-us/windows/forum/windows_10-networking/how-do-i-set-
up-an-ad-hoc-wifi-network-in-windows/0caa92d8-e02f-4e7f-aa5c-0abf10ed2039
How to spoof a MAC address - TechRepublic. Retrieved 2019, from
https://www.techrepublic.com/blog/it-security/how-to-spoof-a-mac-address/
Installation and Configuration for Windows Remote ... Retrieved 2019, from
https://docs.microsoft.com/en-us/windows/win32/winrm/installation-and-configuration-for-
windows-remote-management
Levin, M. (2009). Combinatorial optimization in system configuration design. Automation And
Remote Control, 70(3), 519-561. doi: 10.1134/s0005117909030187
Mohapatra, A., & Prakash, N. (2010). Wired equivalent privacy reinvestigated. Journal Of
Discrete Mathematical Sciences And Cryptography, 13(2), 141-151. doi:
10.1080/09720529.2010.10698282
Guide to Intrusion Detection and Prevention Systems (IDPS), NIST Special Publication 800-94,
Retrieved 2007 from http://csrc.nist.gov/publications/PubsSPs.html#800-94.
Pietrabissa, A., Liberati, F., & Oddi, G. (2016). A distributed algorithm for Ad-hoc network
partitioning based on Voronoi Tessellation. Ad Hoc Networks, 46, 37-47. doi:
10.1016/j.adhoc.2016.03.008
Schweitzer, N., Stulman, A., Hirst, T., Margalit, R., & Shabtai, A. (2019). Network bottlenecks in
OLSR based ad-hoc networks. Ad Hoc Networks, 88, 36-54. doi: 10.1016/j.adhoc.2018.12.002
Wireless ad hoc network - Wikipedia. Retrieved 2019, from
https://en.wikipedia.org/wiki/Wireless_ad_hoc_network
OLSR based ad-hoc networks. Ad Hoc Networks, 88, 36-54. doi: 10.1016/j.adhoc.2018.12.002
Wireless ad hoc network - Wikipedia. Retrieved 2019, from
https://en.wikipedia.org/wiki/Wireless_ad_hoc_network
1 out of 22
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
© 2024 | Zucol Services PVT LTD | All rights reserved.



