Computer Security Analysis Report: Threat Landscape Overview
VerifiedAdded on 2019/09/30
|8
|1292
|197
Report
AI Summary
This report offers a comprehensive analysis of the current computer security landscape. It begins by examining the evolving nature of cyber threats, highlighting the increasing opportunities for cybercrime due to the growing reliance on cloud storage and internet-connected devices. The report then delves into specific threats, including coin mining attacks, the rise of mobile malware, and software-based attacks. It categorizes threat actors, detailing their techniques and procedures, and explores exploit vectors and network vulnerabilities. The report also provides an in-depth look at Advanced Persistent Threats (APTs), including their tactics, tools, and objectives, with references to recent research and industry reports. This report is designed to provide students with a thorough understanding of the dynamic challenges and complexities within the field of computer security.

Running Head: Computer Security 1
Computer Network and Security
Computer Network and Security
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Computer Security 2
Contents
Analysis of threat landscape............................................................................................................3
Coin mining attacks.....................................................................................................................3
Mobile malware...........................................................................................................................3
Spike on software.........................................................................................................................4
Procedure in threat actor type..........................................................................................................4
Exploit vectors and vulnerabilities threat actors..............................................................................4
Exploit vectors.............................................................................................................................4
Vulnerabilities threat actors.........................................................................................................5
Advanced Persistent Threat.............................................................................................................5
Specific tactics.............................................................................................................................5
Tools.............................................................................................................................................6
Objectives.....................................................................................................................................6
References........................................................................................................................................8
Contents
Analysis of threat landscape............................................................................................................3
Coin mining attacks.....................................................................................................................3
Mobile malware...........................................................................................................................3
Spike on software.........................................................................................................................4
Procedure in threat actor type..........................................................................................................4
Exploit vectors and vulnerabilities threat actors..............................................................................4
Exploit vectors.............................................................................................................................4
Vulnerabilities threat actors.........................................................................................................5
Advanced Persistent Threat.............................................................................................................5
Specific tactics.............................................................................................................................5
Tools.............................................................................................................................................6
Objectives.....................................................................................................................................6
References........................................................................................................................................8
Computer Security 3
Analysis of threat landscape
The threat landscape is continuously changing and adversaries are evolving to enhance
the capabilities and stay ahead of defensive measures. As the companies are storing more data in
the cloud and number of internet devices are continuously increasing. So the opportunity and
appeal of cybercrime is also continuously increasing. But, technological advances have
developed various new products and defense mechanism and those are continuously emerging
throughout the years (Durbin, 2018). There are various threat landscapes in 2018 which are
discussed below:
Coin mining attacks
Cyber criminals are focused on the ransom ware for the generation of revenue which are
giving new opportunities to them. During the last year 2017, the astronomical rise in the
currency values due to various cyber criminals who are shifting to coin mining as the alternative
source of revenue. In 2017, the coin mining gold rush which result an increase in the detection of
coin minors on computers. Cyber criminals are stealing computer processing power and CPU
storage with the help of coin minors. There are various impacts of this kind of cyber crime i.e.
overheating batteries, slowing down devices and rendering devices unusable. Along with this,
corporate networks are also at the risk of shutdown. There can also be financial implications for
the organizations who find themselves for cloud CPU used by coin miners. These are also known
as supply chain attacks. The attack has increased by 600 percent as compared to 2017; it means
that cyber criminals are continuously increasing (Symantec, 2018).
Mobile malware
Threats of mobile malware are also growing continuously in every year. The number of
new malware attacks is increased by 54 percent in 2018 as compared to 2018. Last year, around
24,000 malicious mobile were blocked every day. With the increment of threats, the problems
are also increasing by the continuous use of older operating system. In the android mobile
phones, 20 percent of devices are running with the newest version and only 2.3 percent are on
latest releases. Further, users are facing privacy risks from the malicious activities and these can
be problematic. These malwares leak the phone numbers of devices and this problem is
increasing every day (Cisco, 2018).
Analysis of threat landscape
The threat landscape is continuously changing and adversaries are evolving to enhance
the capabilities and stay ahead of defensive measures. As the companies are storing more data in
the cloud and number of internet devices are continuously increasing. So the opportunity and
appeal of cybercrime is also continuously increasing. But, technological advances have
developed various new products and defense mechanism and those are continuously emerging
throughout the years (Durbin, 2018). There are various threat landscapes in 2018 which are
discussed below:
Coin mining attacks
Cyber criminals are focused on the ransom ware for the generation of revenue which are
giving new opportunities to them. During the last year 2017, the astronomical rise in the
currency values due to various cyber criminals who are shifting to coin mining as the alternative
source of revenue. In 2017, the coin mining gold rush which result an increase in the detection of
coin minors on computers. Cyber criminals are stealing computer processing power and CPU
storage with the help of coin minors. There are various impacts of this kind of cyber crime i.e.
overheating batteries, slowing down devices and rendering devices unusable. Along with this,
corporate networks are also at the risk of shutdown. There can also be financial implications for
the organizations who find themselves for cloud CPU used by coin miners. These are also known
as supply chain attacks. The attack has increased by 600 percent as compared to 2017; it means
that cyber criminals are continuously increasing (Symantec, 2018).
Mobile malware
Threats of mobile malware are also growing continuously in every year. The number of
new malware attacks is increased by 54 percent in 2018 as compared to 2018. Last year, around
24,000 malicious mobile were blocked every day. With the increment of threats, the problems
are also increasing by the continuous use of older operating system. In the android mobile
phones, 20 percent of devices are running with the newest version and only 2.3 percent are on
latest releases. Further, users are facing privacy risks from the malicious activities and these can
be problematic. These malwares leak the phone numbers of devices and this problem is
increasing every day (Cisco, 2018).
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Computer Security 4
Spike on software
Cyber attackers are spiking on the software to hack the data. It is observed that there is an
increment in attackers implanting malware in the software so that important data can be hacked.
Further, it is also observed that there is 200 percent increment in attackers in 2018 as compared
to previous year as four attacks are increasing every year.
Procedure in threat actor type
Threat of cyber security has affected every industry. In order to avoid the risks on data
and information, it is important to understand threat actor type and techniques and procedures
used by them. There are four main group of threat actor type who have their own techniques and
procedures.
Cyber criminals- They use malware payloads, emails and social engineering components.
Along with this, they activate malicious software in the systems.
Hacktivists – They are motivated by money. They use attacking websites and distributed denial
of services to attack on favorite firm. Along with this, they use malware spam campaigns.
State-sponsor attacks- They are famous in IT infrastructure and their preferred technique is
advanced persistent threat (Jose, 2018).
Insider threat- These threats are dangerous and hard to spot. Under this threat, information is
usually target of insider threats and leaks the confidential data of organization (Trend Micro,
2018).
Exploit vectors and vulnerabilities threat actors
Exploit vectors
This is the path or the tool which is used by threat actors to attack of targets. Exploit vectors
can be anything that can provide value to threat actor. Those are as follows:
Web- Session hacking, fake sites etc
Wireless unsecured hotspots
Email- link and attachments
Spike on software
Cyber attackers are spiking on the software to hack the data. It is observed that there is an
increment in attackers implanting malware in the software so that important data can be hacked.
Further, it is also observed that there is 200 percent increment in attackers in 2018 as compared
to previous year as four attacks are increasing every year.
Procedure in threat actor type
Threat of cyber security has affected every industry. In order to avoid the risks on data
and information, it is important to understand threat actor type and techniques and procedures
used by them. There are four main group of threat actor type who have their own techniques and
procedures.
Cyber criminals- They use malware payloads, emails and social engineering components.
Along with this, they activate malicious software in the systems.
Hacktivists – They are motivated by money. They use attacking websites and distributed denial
of services to attack on favorite firm. Along with this, they use malware spam campaigns.
State-sponsor attacks- They are famous in IT infrastructure and their preferred technique is
advanced persistent threat (Jose, 2018).
Insider threat- These threats are dangerous and hard to spot. Under this threat, information is
usually target of insider threats and leaks the confidential data of organization (Trend Micro,
2018).
Exploit vectors and vulnerabilities threat actors
Exploit vectors
This is the path or the tool which is used by threat actors to attack of targets. Exploit vectors
can be anything that can provide value to threat actor. Those are as follows:
Web- Session hacking, fake sites etc
Wireless unsecured hotspots
Email- link and attachments
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Computer Security 5
Mobile devices and social networking
Social engineering
Malware and USB media (Diaz, 2011)
Vulnerabilities threat actors
Vulnerabilities in the network security can be considered as the spots which are presented in
each network. The vulnerabilities are presented in the networks which make up network. Key
vulnerabilities threat actors are as follows:
Configuration weakness
Technology weakness
Security policy weakness
Advanced Persistent Threat
This is the network attack in which an unauthorized person gets access to the network
and stays undetected for the long period of time. The objectives of APT attack are to leak the
data rather damaging the network or organization. APT attacks the organizations in the sector to
get high-volume information like manufacturing, financial and national defense industry
(Secureworks, 2016).
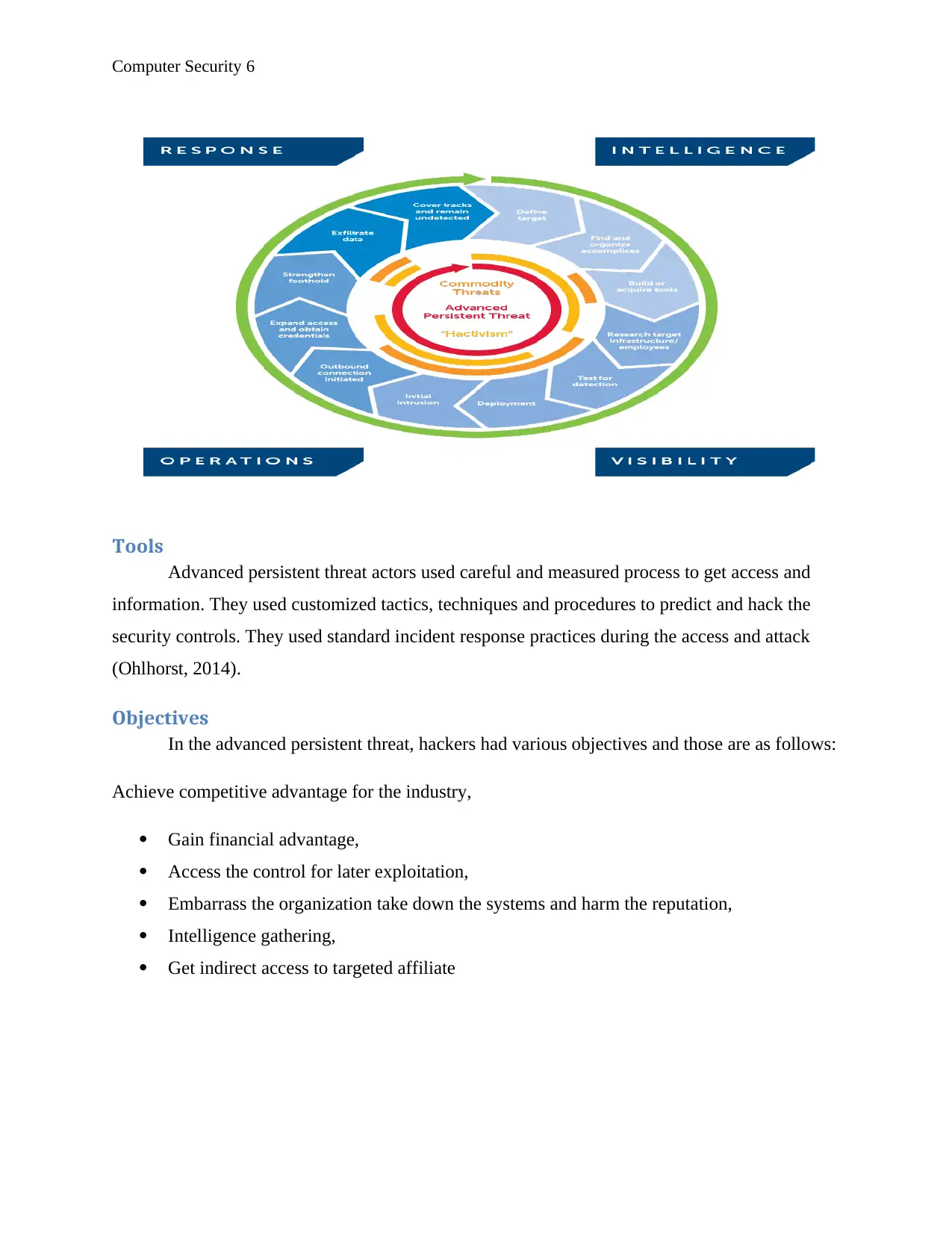
Specific tactics
In the advanced persistent threat, threat actors use social engineering which is the
common tactic to get information from the target organizations. Further, phishing and spear-
phishing are also used in such malicious programs. APT actors use wide range of tools in the
cycle process. This includes root kits, downloader kits, exploit kits, DNS and routing
modifications, drive by downloads, use of unsafe Wi-Fi devices and much more. Some of they
also have resources to enhance custom hacking tools and prepare zero-day exploits (Rouse,
2018).
Mobile devices and social networking
Social engineering
Malware and USB media (Diaz, 2011)
Vulnerabilities threat actors
Vulnerabilities in the network security can be considered as the spots which are presented in
each network. The vulnerabilities are presented in the networks which make up network. Key
vulnerabilities threat actors are as follows:
Configuration weakness
Technology weakness
Security policy weakness
Advanced Persistent Threat
This is the network attack in which an unauthorized person gets access to the network
and stays undetected for the long period of time. The objectives of APT attack are to leak the
data rather damaging the network or organization. APT attacks the organizations in the sector to
get high-volume information like manufacturing, financial and national defense industry
(Secureworks, 2016).
Specific tactics
In the advanced persistent threat, threat actors use social engineering which is the
common tactic to get information from the target organizations. Further, phishing and spear-
phishing are also used in such malicious programs. APT actors use wide range of tools in the
cycle process. This includes root kits, downloader kits, exploit kits, DNS and routing
modifications, drive by downloads, use of unsafe Wi-Fi devices and much more. Some of they
also have resources to enhance custom hacking tools and prepare zero-day exploits (Rouse,
2018).
Computer Security 6
Tools
Advanced persistent threat actors used careful and measured process to get access and
information. They used customized tactics, techniques and procedures to predict and hack the
security controls. They used standard incident response practices during the access and attack
(Ohlhorst, 2014).
Objectives
In the advanced persistent threat, hackers had various objectives and those are as follows:
Achieve competitive advantage for the industry,
Gain financial advantage,
Access the control for later exploitation,
Embarrass the organization take down the systems and harm the reputation,
Intelligence gathering,
Get indirect access to targeted affiliate
Tools
Advanced persistent threat actors used careful and measured process to get access and
information. They used customized tactics, techniques and procedures to predict and hack the
security controls. They used standard incident response practices during the access and attack
(Ohlhorst, 2014).
Objectives
In the advanced persistent threat, hackers had various objectives and those are as follows:
Achieve competitive advantage for the industry,
Gain financial advantage,
Access the control for later exploitation,
Embarrass the organization take down the systems and harm the reputation,
Intelligence gathering,
Get indirect access to targeted affiliate
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide

Computer Security 7
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Computer Security 8
References
Cisco. (2018). Annual Cyber security Report. Retrieved from
https://www.cisco.com/c/dam/m/hu_hu/campaigns/security-hub/pdf/acr-2018.pdf
Diaz, V. (2011). Exploit kits attack vector – mid-year update. Retrieved from
https://securelist.com/exploit-kits-attack-vector-mid-year-update/35986/
Durbin, S. (2018). The Top Five Global Cyber Security Threats for 2018. Retrieved from
https://www.cso.com.au/article/632468/top-five-global-cyber-security-threats-2018/
Jose, S. (2018). Cisco Cyber security Report Maps Threat Landscape for 2018. Retrieved
from https://www.lightreading.com/carrier-security/security-strategies/cisco-
cybersecurity-report-maps-threat-landscape-for-2018/d/d-id/740752
Ohlhorst, F. (2014). Proven tactics for preventing Advanced Persistent Threat incursions.
Retrieved from https://www.techrepublic.com/article/proven-tactics-for-preventing-
advanced-persistent-threat-incursions/
Rouse, M. (2018). Advanced persistent threat (APT). Retrieved from
https://searchsecurity.techtarget.com/definition/advanced-persistent-threat-APT
Secureworks, (2016). Advanced Persistent Threats: Learn the ABCs of APTs - Part A.
Retrieved from https://www.secureworks.com/blog/advanced-persistent-threats-apt-a
Symantec, (2018). 2018 Internet Security Threat Report. Retrieved from
https://www.symantec.com/content/dam/symantec/docs/reports/istr-23-executive-
summary-en.pdf
Trend Micro, (2018). The New Mobile Threat Landscape, circa 2017 to 2018. Retrieved
from https://blog.trendmicro.com/the-new-mobile-threat-landscape-circa-2017-to-
2018/
References
Cisco. (2018). Annual Cyber security Report. Retrieved from
https://www.cisco.com/c/dam/m/hu_hu/campaigns/security-hub/pdf/acr-2018.pdf
Diaz, V. (2011). Exploit kits attack vector – mid-year update. Retrieved from
https://securelist.com/exploit-kits-attack-vector-mid-year-update/35986/
Durbin, S. (2018). The Top Five Global Cyber Security Threats for 2018. Retrieved from
https://www.cso.com.au/article/632468/top-five-global-cyber-security-threats-2018/
Jose, S. (2018). Cisco Cyber security Report Maps Threat Landscape for 2018. Retrieved
from https://www.lightreading.com/carrier-security/security-strategies/cisco-
cybersecurity-report-maps-threat-landscape-for-2018/d/d-id/740752
Ohlhorst, F. (2014). Proven tactics for preventing Advanced Persistent Threat incursions.
Retrieved from https://www.techrepublic.com/article/proven-tactics-for-preventing-
advanced-persistent-threat-incursions/
Rouse, M. (2018). Advanced persistent threat (APT). Retrieved from
https://searchsecurity.techtarget.com/definition/advanced-persistent-threat-APT
Secureworks, (2016). Advanced Persistent Threats: Learn the ABCs of APTs - Part A.
Retrieved from https://www.secureworks.com/blog/advanced-persistent-threats-apt-a
Symantec, (2018). 2018 Internet Security Threat Report. Retrieved from
https://www.symantec.com/content/dam/symantec/docs/reports/istr-23-executive-
summary-en.pdf
Trend Micro, (2018). The New Mobile Threat Landscape, circa 2017 to 2018. Retrieved
from https://blog.trendmicro.com/the-new-mobile-threat-landscape-circa-2017-to-
2018/
1 out of 8
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





