Intelligence: Cycle, Computers, and Counterintelligence
VerifiedAdded on 2019/12/28
|15
|5247
|202
Report
AI Summary
This report provides an in-depth analysis of the intelligence cycle, outlining its various stages including planning and direction, collection, processing, source analysis and production, and dissemination. It also critically examines the statement "Computer was born to spy," highlighting the pivotal role of computers in modern intelligence gathering, data storage, and analysis, including the use of signals intelligence and database management. Furthermore, the report addresses counterintelligence, exploring the challenges faced by intelligence agencies in protecting sensitive information and thwarting espionage. The report emphasizes the strategic, operational, and tactical aspects of intelligence, offering a comprehensive overview of the field.

Intelligence Studies
1
1
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
TABLE OF CONTENTS
INTRODUCTION...........................................................................................................................3
Q1. INTELLIGENCE CYCLE CONCEPT.....................................................................................3
Q2. CRITICALLY EXAMINE AND ASSESS “COMPUTER WAS BORN TO SPY”...............7
Q3. COUNTER INTELLIGENCE AND CHALLENGES.............................................................9
CONCLUSION..............................................................................................................................12
REFERENCES..............................................................................................................................14
2
INTRODUCTION...........................................................................................................................3
Q1. INTELLIGENCE CYCLE CONCEPT.....................................................................................3
Q2. CRITICALLY EXAMINE AND ASSESS “COMPUTER WAS BORN TO SPY”...............7
Q3. COUNTER INTELLIGENCE AND CHALLENGES.............................................................9
CONCLUSION..............................................................................................................................12
REFERENCES..............................................................................................................................14
2
INTRODUCTION
Intelligence agencies are having a great involvement in the social and economic
development. These kinds of organizations are focused towards gathering of information and
measuring the security and cross nation measures so that better protection can be provided to
nation. In present study, functional values and challenges of intelligence cycle is being analysed
so that better awareness can be created.
Q1. INTELLIGENCE CYCLE CONCEPT
Intelligence cycle refers to a fundamental cycle which is mainly used in the military
agency or in the development of law enforcement which involves the closed path of the regular
coming nodes. There are several stages which are included in this cycle such as issuance which
are required mainly by the decision makers, analysis, processing and in the publication of
intelligence. The circuit which is formulated of the intelligence cycle is been completed with the
feedback and requirements provided by the decision makers (Ducatelle, Caro and Gambardella,
2010). This cycle is also known as intelligence process. Further, it is been considered as a most
efficient manner for processing the information and converting them into actionable intelligence.
Further, it may be defined as the process for the development of the raw materials to the final
intelligence (Davies and et.al., 2011). This is been used by the policy-makers which is useful in
determining decisions and action. Further, there are mainly five steps which are included in
intelligence cycle:
3
Intelligence agencies are having a great involvement in the social and economic
development. These kinds of organizations are focused towards gathering of information and
measuring the security and cross nation measures so that better protection can be provided to
nation. In present study, functional values and challenges of intelligence cycle is being analysed
so that better awareness can be created.
Q1. INTELLIGENCE CYCLE CONCEPT
Intelligence cycle refers to a fundamental cycle which is mainly used in the military
agency or in the development of law enforcement which involves the closed path of the regular
coming nodes. There are several stages which are included in this cycle such as issuance which
are required mainly by the decision makers, analysis, processing and in the publication of
intelligence. The circuit which is formulated of the intelligence cycle is been completed with the
feedback and requirements provided by the decision makers (Ducatelle, Caro and Gambardella,
2010). This cycle is also known as intelligence process. Further, it is been considered as a most
efficient manner for processing the information and converting them into actionable intelligence.
Further, it may be defined as the process for the development of the raw materials to the final
intelligence (Davies and et.al., 2011). This is been used by the policy-makers which is useful in
determining decisions and action. Further, there are mainly five steps which are included in
intelligence cycle:
3
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
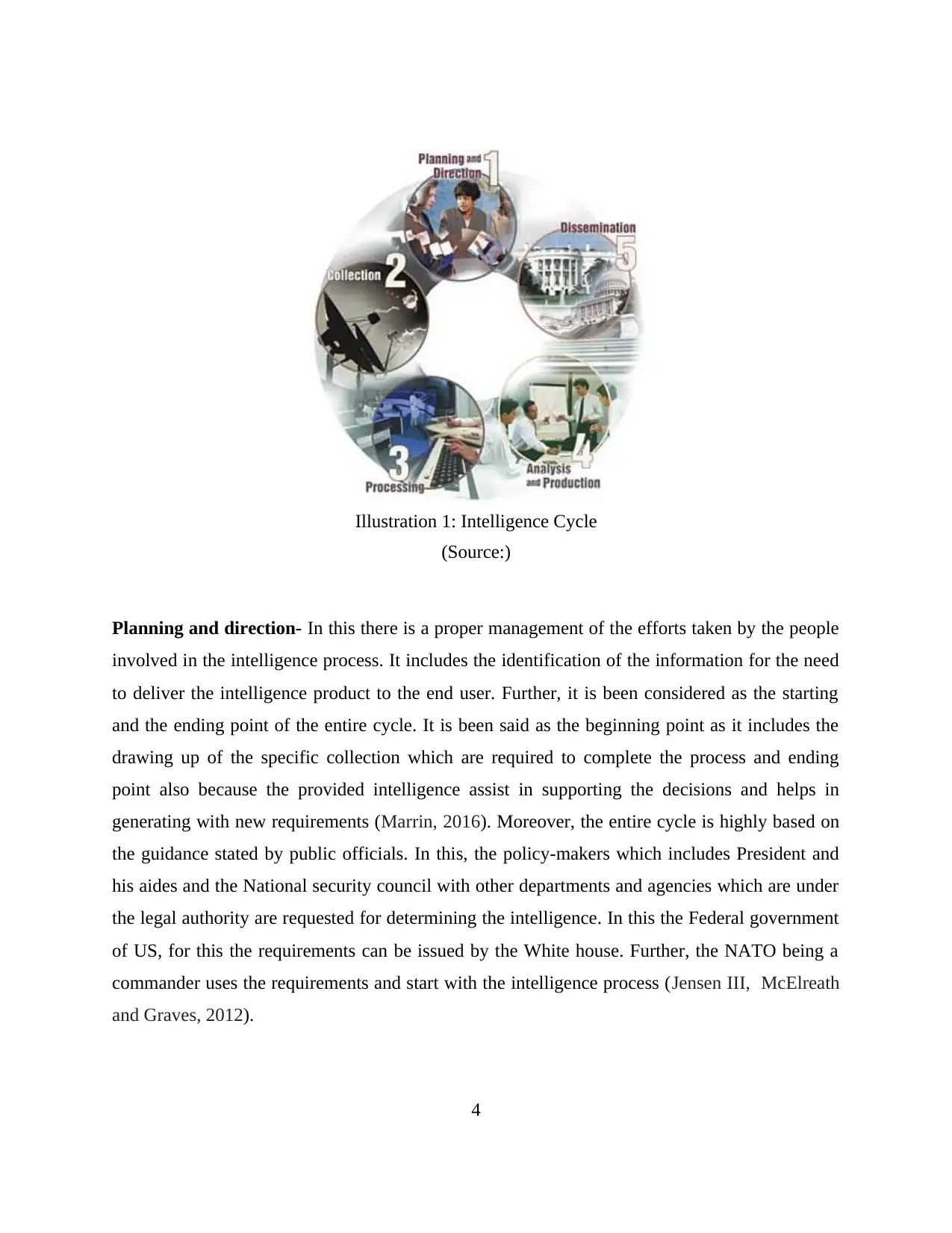
Planning and direction- In this there is a proper management of the efforts taken by the people
involved in the intelligence process. It includes the identification of the information for the need
to deliver the intelligence product to the end user. Further, it is been considered as the starting
and the ending point of the entire cycle. It is been said as the beginning point as it includes the
drawing up of the specific collection which are required to complete the process and ending
point also because the provided intelligence assist in supporting the decisions and helps in
generating with new requirements (Marrin, 2016). Moreover, the entire cycle is highly based on
the guidance stated by public officials. In this, the policy-makers which includes President and
his aides and the National security council with other departments and agencies which are under
the legal authority are requested for determining the intelligence. In this the Federal government
of US, for this the requirements can be issued by the White house. Further, the NATO being a
commander uses the requirements and start with the intelligence process (Jensen III, McElreath
and Graves, 2012).
4
Illustration 1: Intelligence Cycle
(Source:)
involved in the intelligence process. It includes the identification of the information for the need
to deliver the intelligence product to the end user. Further, it is been considered as the starting
and the ending point of the entire cycle. It is been said as the beginning point as it includes the
drawing up of the specific collection which are required to complete the process and ending
point also because the provided intelligence assist in supporting the decisions and helps in
generating with new requirements (Marrin, 2016). Moreover, the entire cycle is highly based on
the guidance stated by public officials. In this, the policy-makers which includes President and
his aides and the National security council with other departments and agencies which are under
the legal authority are requested for determining the intelligence. In this the Federal government
of US, for this the requirements can be issued by the White house. Further, the NATO being a
commander uses the requirements and start with the intelligence process (Jensen III, McElreath
and Graves, 2012).
4
Illustration 1: Intelligence Cycle
(Source:)
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

Collection- In this the collection of different raw information which are highly required for
producing the finished intelligence is included. Further, for collecting the data there are several
sources which mainly includes open sources such as foreign broadcasts, periodicals, books and
newspapers. Further, the open source reporting is highly integral to CIA's analytical capabilities.
Moreover, there are several secret sources for gathering the information. In addition to this,
CIA's officers are obliged to collect the data from several agents who are residing in abroad and
also from various defectors who provide with the information which can be obtained in no other
manner (Deary, Penke and Johnson, 2010). Further, the data in context to the technical terms are
been collected by electronics and satellite photography. This plays an indispensable role in
determining with the modern intelligence which includes monitoring arms control agreements
and further assist in supporting the military forces. Further, while collecting the information it is
important to be careful about that if the data is open or closed source of information as this may
confine the ways for disseminating the information (Tapia and et.al., 2010). Moreover, the data
collected may involve the general as well as the specific information. The prior one determines
the data about the environment surroundings which may be required for coming up with the
intelligence products. Further, the later one includes the data which highly addresses with the
appropriate one for coming up with the decision. It mainly relates to the entity, event and the
phenomenon which is subject to the relevant data.
Processing- This is the step in which involves the conversion of bulk information which is been
collected or gathered through different means to be used by different analysts by decryption, data
reduction and lastly by language translations. This will help ion sorting with the important things
from the irrelevant data so that it become easy for the analysts to come up with the final
intelligence products for the customers (Woolley And et.al.,2010). This mainly involves with the
translation of raw materials of intelligence which are provided from foreign language and the
evaluation is done on the basis of reliability and further the collation of the raw material in the
preparation of exploitation.
Sources analysis and production- In this the conversion of basic information in the finished
intelligence. This mainly includes the integration, evaluation and analysis of the data which is
been collected which may be fragmentary or contradictory. Further, these information is required
for formulating the intelligence products. Moreover, the analysts involved which are mainly the
5
producing the finished intelligence is included. Further, for collecting the data there are several
sources which mainly includes open sources such as foreign broadcasts, periodicals, books and
newspapers. Further, the open source reporting is highly integral to CIA's analytical capabilities.
Moreover, there are several secret sources for gathering the information. In addition to this,
CIA's officers are obliged to collect the data from several agents who are residing in abroad and
also from various defectors who provide with the information which can be obtained in no other
manner (Deary, Penke and Johnson, 2010). Further, the data in context to the technical terms are
been collected by electronics and satellite photography. This plays an indispensable role in
determining with the modern intelligence which includes monitoring arms control agreements
and further assist in supporting the military forces. Further, while collecting the information it is
important to be careful about that if the data is open or closed source of information as this may
confine the ways for disseminating the information (Tapia and et.al., 2010). Moreover, the data
collected may involve the general as well as the specific information. The prior one determines
the data about the environment surroundings which may be required for coming up with the
intelligence products. Further, the later one includes the data which highly addresses with the
appropriate one for coming up with the decision. It mainly relates to the entity, event and the
phenomenon which is subject to the relevant data.
Processing- This is the step in which involves the conversion of bulk information which is been
collected or gathered through different means to be used by different analysts by decryption, data
reduction and lastly by language translations. This will help ion sorting with the important things
from the irrelevant data so that it become easy for the analysts to come up with the final
intelligence products for the customers (Woolley And et.al.,2010). This mainly involves with the
translation of raw materials of intelligence which are provided from foreign language and the
evaluation is done on the basis of reliability and further the collation of the raw material in the
preparation of exploitation.
Sources analysis and production- In this the conversion of basic information in the finished
intelligence. This mainly includes the integration, evaluation and analysis of the data which is
been collected which may be fragmentary or contradictory. Further, these information is required
for formulating the intelligence products. Moreover, the analysts involved which are mainly the
5
subject-matter specialists highly take into consideration the reliability, relevance and validity of
the information. Further, the given data is been integrated with the coherent whole which
determine the evaluated data into a meaningful context and develop with the finished intelligence
(Kacprzyk, 2010). This mainly includes the assessment of the events as well as the judgements
which is highly about they implications regarding the information. Further, the CIA provides the
bulk of there information to the policymakers which develop with the strategic intelligence. This
function is been performed by monitoring the events properly, warning the decision makers
about the upcoming threats for US and also forecasting the future developments. Further, the
subjects which are been associated with different regions, problems in different contexts such as
geographic, military, biographic, economic, political etc. Moreover, the recent events, future
trends and capabilities are also examined efficiently before developing with the intelligence
products. In addition this, CIA are developing with the number of written reports which may be
in brief or very lengthy. Further, it also involves with the current intelligence which is having
high importance or long range assessments. Moreover, the agency determines the final
intelligence in oral manner (Moravej and Diaz, 2007). In addition to this, CIA also participates in
drafting and also producing with the National intelligence estimates which are the major
reflection of the judgement made collectively by the Intelligence community.
Dissemination- It is the last step involved in the Intelligence cycle, which highly includes the
distribution of the final intelligence to the customers or end users. Moreover, these are provided
to policy makers which are required with the intelligence products. Further, the intelligence is
been hand-taken to the President on the regular basis and also to the key national security
advisers (Intelligence Cycle and Process, 2016). Further, the policy makers take the information
and from it come to the final decisions and these are been used for further requirements which
ultimately triggers the intelligence process.
Further, there are mainly three major categories of Intelligence cycle which mainly
includes Strategic, operational and tactical intelligence. Further, in the strategic intelligence it
provides with understanding, and contribute in making decisions on broader context strategies,
policies and resources are been used and directing them for the achievement of long term
objectives (Ducatelle, Di Caro and Gambardella, 2010). On the other hand, operational
intelligence refers to the product which is assisting in supporting the national and regional
6
the information. Further, the given data is been integrated with the coherent whole which
determine the evaluated data into a meaningful context and develop with the finished intelligence
(Kacprzyk, 2010). This mainly includes the assessment of the events as well as the judgements
which is highly about they implications regarding the information. Further, the CIA provides the
bulk of there information to the policymakers which develop with the strategic intelligence. This
function is been performed by monitoring the events properly, warning the decision makers
about the upcoming threats for US and also forecasting the future developments. Further, the
subjects which are been associated with different regions, problems in different contexts such as
geographic, military, biographic, economic, political etc. Moreover, the recent events, future
trends and capabilities are also examined efficiently before developing with the intelligence
products. In addition this, CIA are developing with the number of written reports which may be
in brief or very lengthy. Further, it also involves with the current intelligence which is having
high importance or long range assessments. Moreover, the agency determines the final
intelligence in oral manner (Moravej and Diaz, 2007). In addition to this, CIA also participates in
drafting and also producing with the National intelligence estimates which are the major
reflection of the judgement made collectively by the Intelligence community.
Dissemination- It is the last step involved in the Intelligence cycle, which highly includes the
distribution of the final intelligence to the customers or end users. Moreover, these are provided
to policy makers which are required with the intelligence products. Further, the intelligence is
been hand-taken to the President on the regular basis and also to the key national security
advisers (Intelligence Cycle and Process, 2016). Further, the policy makers take the information
and from it come to the final decisions and these are been used for further requirements which
ultimately triggers the intelligence process.
Further, there are mainly three major categories of Intelligence cycle which mainly
includes Strategic, operational and tactical intelligence. Further, in the strategic intelligence it
provides with understanding, and contribute in making decisions on broader context strategies,
policies and resources are been used and directing them for the achievement of long term
objectives (Ducatelle, Di Caro and Gambardella, 2010). On the other hand, operational
intelligence refers to the product which is assisting in supporting the national and regional
6
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
managers of the line areas which are been used in activities involved in planning and deploying
the resources for the achievement of objectives. Further, tactical intelligence refers to the
products which highly supports the line areas as well as other operational ones which are been
involved in taking the case specific action for achieving with the compliance and enforcement
objectives.
Q2. CRITICALLY EXAMINE AND ASSESS “COMPUTER WAS BORN TO
SPY”
As per the detailed study, it can be said that the first computer was born to spy. According
to the statement of Gordon Corera the computer was born to spy and number of intelligence
agencies are having use of it. In order to have better spy and other intelligence activities the
communities has started adopted digital tools and computer system. It is because it helps in
monitoring system so that goals and objectives can be accomplished in desired manner. It has
been noticed that earliest computers about by the Britain and America intelligence are named as
Colossus and SEAC. Such kind of computer systems are being adopted by signals intelligence
which is framed under the SIGNIT network. It helps in coding system and analyse the any kind
of risk which is associated with the intelligence. But computers also happen to have become
supremely good at storing information. It means the intelligence agencies has started the
application of computer system in operations so that information about diverse policies and
factors can be stored effectively (Marrin, 2016). Information about the cross nation activities can
also be stored in appropriate manner by having a use of computer system. Along with this, the
searching of data base can also be improved by having an application of data base system. For
example, the national intelligence agency wants to search any kind of information about the
border security then using a computer system applications the issue can be resolved effectively. It
assists in meeting objectives and helps in accomplishment of intelligence cycle.
In addition to this, it can be stated that searching a data base is easier as compared to
searching an information from the files. It provides better effectiveness and helps in make sure
that operational activities of intelligence agencies are being taken into account as per standards
(Deary, Penke and Johnson, 2010). Along with this, the application of computer system is also
beneficial to make sure that what partner nations and rival nations are performing in context to
7
the resources for the achievement of objectives. Further, tactical intelligence refers to the
products which highly supports the line areas as well as other operational ones which are been
involved in taking the case specific action for achieving with the compliance and enforcement
objectives.
Q2. CRITICALLY EXAMINE AND ASSESS “COMPUTER WAS BORN TO
SPY”
As per the detailed study, it can be said that the first computer was born to spy. According
to the statement of Gordon Corera the computer was born to spy and number of intelligence
agencies are having use of it. In order to have better spy and other intelligence activities the
communities has started adopted digital tools and computer system. It is because it helps in
monitoring system so that goals and objectives can be accomplished in desired manner. It has
been noticed that earliest computers about by the Britain and America intelligence are named as
Colossus and SEAC. Such kind of computer systems are being adopted by signals intelligence
which is framed under the SIGNIT network. It helps in coding system and analyse the any kind
of risk which is associated with the intelligence. But computers also happen to have become
supremely good at storing information. It means the intelligence agencies has started the
application of computer system in operations so that information about diverse policies and
factors can be stored effectively (Marrin, 2016). Information about the cross nation activities can
also be stored in appropriate manner by having a use of computer system. Along with this, the
searching of data base can also be improved by having an application of data base system. For
example, the national intelligence agency wants to search any kind of information about the
border security then using a computer system applications the issue can be resolved effectively. It
assists in meeting objectives and helps in accomplishment of intelligence cycle.
In addition to this, it can be stated that searching a data base is easier as compared to
searching an information from the files. It provides better effectiveness and helps in make sure
that operational activities of intelligence agencies are being taken into account as per standards
(Deary, Penke and Johnson, 2010). Along with this, the application of computer system is also
beneficial to make sure that what partner nations and rival nations are performing in context to
7
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
nation security. Number of spy projects are being taken into account and their recording is being
accomplished with an assistance of computer system. Telephone taping and other essential
activities of intelligence agencies can be taken into account with a help of computer. Such kind
of activities indicates that computer was mainly born to spy (Kacprzyk, 2010). It has been
witnessed that attaching crocodile clips to the telephone is also one of critical aspect which need
to be referred effectively so that functional activities can be accomplished in desired manner.
Moreover, the computer system is also being used by the intelligence agencies to make sure that
nation security is being well maintained. Conversation between terrorist group can be trapped
effectively through use of computer. Along with this, interception of the communication and
codes identified can be analysed effectively so that key aspect of security can be improved.
Number of intelligence agencies has started the use of computer system to track the war
activities and terrorist activities so that corrective measures can be taken into account. It has been
witnessed that national intelligence activities strength has been improved through application of
diverse digital and computerised activities (Duckworth and et.al., 2011). Monitoring process
under intelligence agencies has been advanced so that goals and objectives can be accomplished
in desired manner. Telephonic lines between different embassy offices are being trapped so that it
can be make sure that any kind of illegal and hazardous activity is not being employed by other
countries. I help in improving the intelligence activities so that goals and objectives can be
accomplished in desired manner. Decrypting the code is one of most essential act of the
intelligence process. By having use of digital tools the description of information collected can
be accomplished in desired manner. It has been noticed that Breaking code was laborious, but
once you had succeeded the results attained can be effective (Kim, Cramond and VanTassel-
Baska, 2010). In order to provide the support to such kind of activities the use of computer
system has been adopted by intelligence communities.
It has been witnessed that before the use of computer the point to point communication
was there which was creating an issue for intelligence process. By having use of Colossus and
SEAC the issue is being resolved in desired manner. New technology of communication has
been introduced which allowed to improve the overall working and lead to better operations
(Nisbett and et.al., 2012). Intelligence officers of different agencies has also stated that use of
computer system has improved the communication with members which is beneficial for
8
accomplished with an assistance of computer system. Telephone taping and other essential
activities of intelligence agencies can be taken into account with a help of computer. Such kind
of activities indicates that computer was mainly born to spy (Kacprzyk, 2010). It has been
witnessed that attaching crocodile clips to the telephone is also one of critical aspect which need
to be referred effectively so that functional activities can be accomplished in desired manner.
Moreover, the computer system is also being used by the intelligence agencies to make sure that
nation security is being well maintained. Conversation between terrorist group can be trapped
effectively through use of computer. Along with this, interception of the communication and
codes identified can be analysed effectively so that key aspect of security can be improved.
Number of intelligence agencies has started the use of computer system to track the war
activities and terrorist activities so that corrective measures can be taken into account. It has been
witnessed that national intelligence activities strength has been improved through application of
diverse digital and computerised activities (Duckworth and et.al., 2011). Monitoring process
under intelligence agencies has been advanced so that goals and objectives can be accomplished
in desired manner. Telephonic lines between different embassy offices are being trapped so that it
can be make sure that any kind of illegal and hazardous activity is not being employed by other
countries. I help in improving the intelligence activities so that goals and objectives can be
accomplished in desired manner. Decrypting the code is one of most essential act of the
intelligence process. By having use of digital tools the description of information collected can
be accomplished in desired manner. It has been noticed that Breaking code was laborious, but
once you had succeeded the results attained can be effective (Kim, Cramond and VanTassel-
Baska, 2010). In order to provide the support to such kind of activities the use of computer
system has been adopted by intelligence communities.
It has been witnessed that before the use of computer the point to point communication
was there which was creating an issue for intelligence process. By having use of Colossus and
SEAC the issue is being resolved in desired manner. New technology of communication has
been introduced which allowed to improve the overall working and lead to better operations
(Nisbett and et.al., 2012). Intelligence officers of different agencies has also stated that use of
computer system has improved the communication with members which is beneficial for
8
improvement in monitoring standards. It has been noticed that the intelligence process
effectiveness is depended upon data collected in last 30 years. Along with this, use of computer
allows to make sure that 30 years data base system is effectively analysed so that issues can be
resolved. In addition to this, with a promotion of computer the internet network promotion has
also improved (Nilsson, 2014). It is one of key reason that networked computer and phones
investment ratio has also been improved. Use of software has also been advanced in order to
make sure that overall outcome has been improved. Nowadays, working of intelligence agencies
is well focused towards use of digital tools. With an assistance of this, information about the
nation security and activities can easily be shared with the agents. Password and special access is
being required which also improves the security aspect. Along with this, use of computer for
intelligence activities is beneficial because it hacking of security server is not so easy for other
nations or terrorist (Cole and et.al., 2012). It means the level of national security measures has
been improved in appropriate manner for sustainable development of nation. Signal intelligence
use is critical task because it can be tracked by the other nation intelligence agencies. By having
a use of computer and digital tools the risk of hacking and tracking can be reduced because it
allows to set out new measures. In signal intelligence the radio frequency can be trapped by other
intelligence agencies and terrorist groups. Civil service work activities has also been improved
by diverse nation through application of computer (Batey, Furnham and Safiullina, 2010). In
addition to this, it can be said that opportunities for surveillance can be advanced in appropriate
manner. NSA and GCHQ has also started the use of computer for better monitoring of covert
operations. With an assistance of this, anti-terrorism policies can be framed in appropriate
manner. Monitoring of local criminal activities has also been improved through use of digital
tools. The technical possibilities for obtaining information are now endless. It means the
functional policies of intelligence communities can be improved in desired manner. It has been
noticed that CIA unit has also stated that use of computer and digital technology is framed to
boost intelligence services (Kim, Cramond and VanTassel-Baska, 2010). It is one of key reason
that during the operations of OSINT the agency has used diverse sources through computer
system in order to gather information about the Bin Laden. Private data can be obtained by
warrant. Data sets are especially powerful in combination. It means use of technology is
9
effectiveness is depended upon data collected in last 30 years. Along with this, use of computer
allows to make sure that 30 years data base system is effectively analysed so that issues can be
resolved. In addition to this, with a promotion of computer the internet network promotion has
also improved (Nilsson, 2014). It is one of key reason that networked computer and phones
investment ratio has also been improved. Use of software has also been advanced in order to
make sure that overall outcome has been improved. Nowadays, working of intelligence agencies
is well focused towards use of digital tools. With an assistance of this, information about the
nation security and activities can easily be shared with the agents. Password and special access is
being required which also improves the security aspect. Along with this, use of computer for
intelligence activities is beneficial because it hacking of security server is not so easy for other
nations or terrorist (Cole and et.al., 2012). It means the level of national security measures has
been improved in appropriate manner for sustainable development of nation. Signal intelligence
use is critical task because it can be tracked by the other nation intelligence agencies. By having
a use of computer and digital tools the risk of hacking and tracking can be reduced because it
allows to set out new measures. In signal intelligence the radio frequency can be trapped by other
intelligence agencies and terrorist groups. Civil service work activities has also been improved
by diverse nation through application of computer (Batey, Furnham and Safiullina, 2010). In
addition to this, it can be said that opportunities for surveillance can be advanced in appropriate
manner. NSA and GCHQ has also started the use of computer for better monitoring of covert
operations. With an assistance of this, anti-terrorism policies can be framed in appropriate
manner. Monitoring of local criminal activities has also been improved through use of digital
tools. The technical possibilities for obtaining information are now endless. It means the
functional policies of intelligence communities can be improved in desired manner. It has been
noticed that CIA unit has also stated that use of computer and digital technology is framed to
boost intelligence services (Kim, Cramond and VanTassel-Baska, 2010). It is one of key reason
that during the operations of OSINT the agency has used diverse sources through computer
system in order to gather information about the Bin Laden. Private data can be obtained by
warrant. Data sets are especially powerful in combination. It means use of technology is
9
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
beneficial for the intelligence agencies which has also improved the overall working in diverse
manner.
Q3. COUNTER INTELLIGENCE AND CHALLENGES
In addition to this, it can be said that counter intelligence is a considered as process in
which agencies focuses on collection of information and activities which are conducted to
protect against spying. Along with this, it also focuses on the intelligence activities which are
taken into account from any other organization and terrorist group (Duckworth and et.al., 2011).
It has been noticed that any kind of personnel, physical, communication security programs are
not being covered under counter intelligence. There are number of factors that need to be
consider effectively by the intelligence agencies so that goals and objectives can be
accomplished in desired manner. It is significant for agencies to ensure about the offensive
aspects. It is necessary to make sure that the aggressive double agent concept is being adopted in
order to make sure that CI program can be accomplished effectively (Grasso and Convertino,
2012). Proper monitoring of opposition is essential for appropriate understanding. Such kind of
intelligence aspects are being framed for effective control over friendly nations. Along with this,
agents must have honour on the profession so that goals and objectives can be accomplished
effectively. It has been noticed that if members are does not feel proud then it will impact the
overall outcome in diverse manner. CI program must be designed according to capabilities of
professional so that issues can be overcome in desired manner. In addition to this, it can be stated
that one of key commanded is that professional must have actual information about the history
(Herrnstein and Murray, 2010). It is significant to make sure that historical aspect in regard to
nation, intelligence agency, friendly nations and rival nations are being considered as critical
aspect. In 21st century it is necessary for CI officers to find out untold facts of nation so that
better decisions can be taken into account. It will improve the process so that issues can be
overcome in appropriate manner. In addition to this, it can be said that actual information in
regard to the historical events need to be gathered so that better decisions in context to CI can be
taken into account (Kacprzyk, 2010). Moreover, in order to improve the functionality of the CI
process, it is necessary to make sure that any kind of information regarding intelligence must not
be ignored so that goals and objectives can be accomplished.
10
manner.
Q3. COUNTER INTELLIGENCE AND CHALLENGES
In addition to this, it can be said that counter intelligence is a considered as process in
which agencies focuses on collection of information and activities which are conducted to
protect against spying. Along with this, it also focuses on the intelligence activities which are
taken into account from any other organization and terrorist group (Duckworth and et.al., 2011).
It has been noticed that any kind of personnel, physical, communication security programs are
not being covered under counter intelligence. There are number of factors that need to be
consider effectively by the intelligence agencies so that goals and objectives can be
accomplished in desired manner. It is significant for agencies to ensure about the offensive
aspects. It is necessary to make sure that the aggressive double agent concept is being adopted in
order to make sure that CI program can be accomplished effectively (Grasso and Convertino,
2012). Proper monitoring of opposition is essential for appropriate understanding. Such kind of
intelligence aspects are being framed for effective control over friendly nations. Along with this,
agents must have honour on the profession so that goals and objectives can be accomplished
effectively. It has been noticed that if members are does not feel proud then it will impact the
overall outcome in diverse manner. CI program must be designed according to capabilities of
professional so that issues can be overcome in desired manner. In addition to this, it can be stated
that one of key commanded is that professional must have actual information about the history
(Herrnstein and Murray, 2010). It is significant to make sure that historical aspect in regard to
nation, intelligence agency, friendly nations and rival nations are being considered as critical
aspect. In 21st century it is necessary for CI officers to find out untold facts of nation so that
better decisions can be taken into account. It will improve the process so that issues can be
overcome in appropriate manner. In addition to this, it can be said that actual information in
regard to the historical events need to be gathered so that better decisions in context to CI can be
taken into account (Kacprzyk, 2010). Moreover, in order to improve the functionality of the CI
process, it is necessary to make sure that any kind of information regarding intelligence must not
be ignored so that goals and objectives can be accomplished.
10
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
It has been noticed that there are number of challenges that an intelligence agency might
face in regard to CI. It is one of critical aspect conducting a sensitive operation because number
of intelligence agency also focused towards CI. It means maintaining a confidentiality aspect is
one of critical aspect which might affect the effectiveness of functional values (Martins, Ramalh
and Morin, 2010). If confidential aspects are not well maintained then intelligence aspects might
get affected. Hazardous situation of nation can be created which might impact the overall
outcome. Hiding the adaptation of new technology is also significant to consider. If new
technology information is hacked then effectiveness of CI activities will also get affected in
diverse manner. Providing a restrict to the internal information sharing is also a key issue which
might impact the overall working (Bobrow, 2014). It has been noticed that if internal information
sharing is not according to the standards then it will impact the overall outcome in diverse
manner. By having lack of collaboration with other agencies might affect the intelligence
process. In order to overcome such kind of issues the improvement in measures is significant so
that goals and objectives can be taken into account. Along with this, improved focus on risk
management is beneficial which helps in understanding the challenges so that better measures
can be taken into account (Kacprzyk, 2010). For effective accomplishment of the objectives the
strategic advantage also need to be referred in appropriate manner. It is necessary for intelligence
agencies to make sure that protection and confidentiality must be well maintained so that issues
can be overcome. Aggressive strategies' application is also beneficial for the agency because it
allows to make sure that key aspect is being developed effectively so that objectives can be
overcome in desired manner (Woolley and et.al.,2010). Application of new technology is also
significant because it assists in make sure that proper sharing of information is being taken into
account. A proper approach to CI takes account of both specific and systemic national
vulnerabilities.
Counter intelligence refers to both which includes the activity and product. Further, the
products includes reliable data which is mainly about the enemies for the country which can
harm the people and property of the nation (Tapia and et.al., 2010). Thus, some of the enemies
are mainly the professional intelligence officers and also the agents which are serving them.
Further, the other people who act as a cover for promoting the subversion rather than counter
intelligence. Moreover, the individuals may be the communists or the anti-communists who
11
face in regard to CI. It is one of critical aspect conducting a sensitive operation because number
of intelligence agency also focused towards CI. It means maintaining a confidentiality aspect is
one of critical aspect which might affect the effectiveness of functional values (Martins, Ramalh
and Morin, 2010). If confidential aspects are not well maintained then intelligence aspects might
get affected. Hazardous situation of nation can be created which might impact the overall
outcome. Hiding the adaptation of new technology is also significant to consider. If new
technology information is hacked then effectiveness of CI activities will also get affected in
diverse manner. Providing a restrict to the internal information sharing is also a key issue which
might impact the overall working (Bobrow, 2014). It has been noticed that if internal information
sharing is not according to the standards then it will impact the overall outcome in diverse
manner. By having lack of collaboration with other agencies might affect the intelligence
process. In order to overcome such kind of issues the improvement in measures is significant so
that goals and objectives can be taken into account. Along with this, improved focus on risk
management is beneficial which helps in understanding the challenges so that better measures
can be taken into account (Kacprzyk, 2010). For effective accomplishment of the objectives the
strategic advantage also need to be referred in appropriate manner. It is necessary for intelligence
agencies to make sure that protection and confidentiality must be well maintained so that issues
can be overcome. Aggressive strategies' application is also beneficial for the agency because it
allows to make sure that key aspect is being developed effectively so that objectives can be
overcome in desired manner (Woolley and et.al.,2010). Application of new technology is also
significant because it assists in make sure that proper sharing of information is being taken into
account. A proper approach to CI takes account of both specific and systemic national
vulnerabilities.
Counter intelligence refers to both which includes the activity and product. Further, the
products includes reliable data which is mainly about the enemies for the country which can
harm the people and property of the nation (Tapia and et.al., 2010). Thus, some of the enemies
are mainly the professional intelligence officers and also the agents which are serving them.
Further, the other people who act as a cover for promoting the subversion rather than counter
intelligence. Moreover, the individuals may be the communists or the anti-communists who
11
employ with the same tactics for taking the stealth when are not able to attain them by winning
with the open allegiance of the people. Furthermore, the counter intelligence mainly includes two
things which include security and counter espionage (Deary, Penke and Johnson, 2010). In this
the security mainly includes the establishment off passive defences over the concealed acts
without regarding the people who are carrying this out. On the other hand counter espionage
mainly requires the identification about the adversary, adequate knowledge about the specific
operations which is to be conducted by the person and countering these operations by
penetrating and manipulating with the motive to turn the thrust back against the aggressor
(Jensen III, McElreath and Graves, 2012). Further, all the functions related to the counter
intelligence are been formulated by the nature and the resultant activities of the adversary. Its
core function is to protect the government in adopting lawful means against the attack.
Moreover, legal authority are are having several defenders for dealing with the open aggression.
Further, the CI service which is mainly concerned with the covert activity and hostile clandestine
(Marrin, 2016). The former is not totally be concealed rather it takes the form of article, radio
telecast or in newspaper. Further, the later one refers to the activity in which the enemy for the
country try to conceal fully. In addition to this, it takes the form of subversion, espionage etc.
The functions of counter sabotage officers are similar to the experts in counter espionage.
Further there is no major difference in the personnel qualification of both the officers for these
assignments. Moreover, there main protection is to catch the saboteur prior to the operations he
do as the physical protection is highly impossible. Further, in the eyes of counter intelligence
officer the espionage agents and saboteurs are mainly identical (Davies and et.al., 2011).
Further, for the first line of defence the appointed operation officer is rampant to the second line
which are involved with the obstacles which are major hindrance to achieve targets. Further,
these obstacles are animate or inanimate. Moreover, the number and characteristics mainly differ
with the importance of the determined targets. To ensure the attainment of the objectives, than
the high-priority must be flood-lighted, surrounded by fences and must be guarded by the armed
sentries (Ducatelle, Di Caro and Gambardella, 2010). However, the most of the targets lack with
such type of protection and they are dependent mainly on the physical defence which includes
walls, locks, bars and ditches. Further, the physical defences can be easily breached.
12
with the open allegiance of the people. Furthermore, the counter intelligence mainly includes two
things which include security and counter espionage (Deary, Penke and Johnson, 2010). In this
the security mainly includes the establishment off passive defences over the concealed acts
without regarding the people who are carrying this out. On the other hand counter espionage
mainly requires the identification about the adversary, adequate knowledge about the specific
operations which is to be conducted by the person and countering these operations by
penetrating and manipulating with the motive to turn the thrust back against the aggressor
(Jensen III, McElreath and Graves, 2012). Further, all the functions related to the counter
intelligence are been formulated by the nature and the resultant activities of the adversary. Its
core function is to protect the government in adopting lawful means against the attack.
Moreover, legal authority are are having several defenders for dealing with the open aggression.
Further, the CI service which is mainly concerned with the covert activity and hostile clandestine
(Marrin, 2016). The former is not totally be concealed rather it takes the form of article, radio
telecast or in newspaper. Further, the later one refers to the activity in which the enemy for the
country try to conceal fully. In addition to this, it takes the form of subversion, espionage etc.
The functions of counter sabotage officers are similar to the experts in counter espionage.
Further there is no major difference in the personnel qualification of both the officers for these
assignments. Moreover, there main protection is to catch the saboteur prior to the operations he
do as the physical protection is highly impossible. Further, in the eyes of counter intelligence
officer the espionage agents and saboteurs are mainly identical (Davies and et.al., 2011).
Further, for the first line of defence the appointed operation officer is rampant to the second line
which are involved with the obstacles which are major hindrance to achieve targets. Further,
these obstacles are animate or inanimate. Moreover, the number and characteristics mainly differ
with the importance of the determined targets. To ensure the attainment of the objectives, than
the high-priority must be flood-lighted, surrounded by fences and must be guarded by the armed
sentries (Ducatelle, Di Caro and Gambardella, 2010). However, the most of the targets lack with
such type of protection and they are dependent mainly on the physical defence which includes
walls, locks, bars and ditches. Further, the physical defences can be easily breached.
12
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 15
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





