Comprehensive Review of Electronic and Digital Forensics
VerifiedAdded on 2023/06/03
|13
|3903
|74
Homework Assignment
AI Summary
This assignment solution covers fundamental aspects of electronic and digital forensics, including definitions of forensic copies, compression algorithms, search warrants, and chain of custody. It addresses desirable conditions for forensic hashes, key concerns in RAID server data acquisition, and the differences between computer forensics and data recovery. The solution also delves into disk drive components like geometry, head, tracks, and sectors. It highlights essential items for investigating email abuse and ethical guidelines for forensic investigators, including attorney-client privilege. Furthermore, it discusses differences between law enforcement and corporate investigations, evidence acquisition techniques, the role of rootkits and malware, and data compression methods. The assignment concludes by addressing actions to take when files cannot be opened, questions to ask during computer crime response, and the significance of file timestamps as evidence, offering a comprehensive overview of the field.

Electronic and digital forensic
Student’s Name
Institutional affiliation
Course
Date
Student’s Name
Institutional affiliation
Course
Date
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
QUESTION 1 5 MARKS
a) What is a forensic copy?
In the field of forensic, forensic copy is a bit by bit direct image of a physical storage device. The
forensic image includes files; the files include located and unallocated, slack and free space.
b) Favorite archiving tools, such as PKZip, WinZip, and WinRAR, use an algorithm to
compress files. What type of compression do they use?
The type of compression that remains deployed by this tool is file compression. Technically, file
compression remains performed using the lossless concept of algorithm. This means that there is
no information is lost during compression process and thus, the information compressed can stay
regained to its original state (Sammons 2015).
c) What is a search warrant?
In the discipline of electronic and digital forensic, the search is a concept that is used to refer to
the legal document that allows a police officer or any other relevant officer to enter and perform
searching in a particular premise that the legal document permits him/her.
d) What is “chain of custody”?
Chain custody is ideology when the information remains collected from the place where a crime
happened, and the information is used to create the CoC revealing the location and the condition
of the offense. Chain of custody is vital because it can be used during the court trial against the
criminal.
e) What is an advantage of using a tape backup system for forensic acquisitions of large
datasets?
The sole benefit of tape endorsement system is that it is scalable an ideology that stays not
exploited by the tape driver. Therefore, it is capable of storing more data as compared to the tape
drive, which is scalability infinitely. Additionally, it lowers cost, as there is no need to add disk
arrays, which is expensive (Sammons 2015).
QUESTION 2 6 MARKS
a) Give three rules or desirable conditions required for a forensic hash.
(Two Marks)
The first rule is that if the forensic hash file get altered the has value get changed too
Hashing tends to use the algorithm to convert the evidence file to the hash value
The forensic hash cannot be predicted
a) What is a forensic copy?
In the field of forensic, forensic copy is a bit by bit direct image of a physical storage device. The
forensic image includes files; the files include located and unallocated, slack and free space.
b) Favorite archiving tools, such as PKZip, WinZip, and WinRAR, use an algorithm to
compress files. What type of compression do they use?
The type of compression that remains deployed by this tool is file compression. Technically, file
compression remains performed using the lossless concept of algorithm. This means that there is
no information is lost during compression process and thus, the information compressed can stay
regained to its original state (Sammons 2015).
c) What is a search warrant?
In the discipline of electronic and digital forensic, the search is a concept that is used to refer to
the legal document that allows a police officer or any other relevant officer to enter and perform
searching in a particular premise that the legal document permits him/her.
d) What is “chain of custody”?
Chain custody is ideology when the information remains collected from the place where a crime
happened, and the information is used to create the CoC revealing the location and the condition
of the offense. Chain of custody is vital because it can be used during the court trial against the
criminal.
e) What is an advantage of using a tape backup system for forensic acquisitions of large
datasets?
The sole benefit of tape endorsement system is that it is scalable an ideology that stays not
exploited by the tape driver. Therefore, it is capable of storing more data as compared to the tape
drive, which is scalability infinitely. Additionally, it lowers cost, as there is no need to add disk
arrays, which is expensive (Sammons 2015).
QUESTION 2 6 MARKS
a) Give three rules or desirable conditions required for a forensic hash.
(Two Marks)
The first rule is that if the forensic hash file get altered the has value get changed too
Hashing tends to use the algorithm to convert the evidence file to the hash value
The forensic hash cannot be predicted
b) What are two key concerns when acquiring data from a RAID server?
(2 Marks)
The type of form of RAID
The total amount of data storage that is required
c) What are the differences between computer forensics and data recovery?
(2 Marks)
Computer forensics tends to deal with one or more system that may sometime it may be fluid in
the context of the demand and request. In another computer forensic happens to deal with
missing data and need to be defensible while data recovery sells with one hard disk drive.
PART B 24 MARKS
Question 3 8 Marks
A disk drive is a conventional storage device found in computer systems.
(a) Describe the following components of a disk drive briefly:
(i) Geometry,
The geometry of a disk is the organization of data on the platters that are composed within the
hard disk. It is responsible for deciding where and how data/information is stored on the surface
of the shelves. Therefore, the device is responsible for maximizing the storage capacity of the
hard disk (Sammons 2015).
(ii) Head,
Head is s device that is located on the arm of the hard disk, and it is responsible for reading and
writing the information that is the data from the hard drive. Ideally, the hard drivers usually have
one read and write the header on each platter.
(iii) Tracks,
This is the circular part on the surface of the hard disk where information is magnetically
recorded, and it is usually from this recorded information is interpreted.
(iv) Sector. (4 Marks)
The industry is the subdivision of the track on the magnetic disk. It is used to store accessible
user information that is always fixed to a certain number. In that point of view, the sector is the
smallest storage unit of the hard disk.
(2 Marks)
The type of form of RAID
The total amount of data storage that is required
c) What are the differences between computer forensics and data recovery?
(2 Marks)
Computer forensics tends to deal with one or more system that may sometime it may be fluid in
the context of the demand and request. In another computer forensic happens to deal with
missing data and need to be defensible while data recovery sells with one hard disk drive.
PART B 24 MARKS
Question 3 8 Marks
A disk drive is a conventional storage device found in computer systems.
(a) Describe the following components of a disk drive briefly:
(i) Geometry,
The geometry of a disk is the organization of data on the platters that are composed within the
hard disk. It is responsible for deciding where and how data/information is stored on the surface
of the shelves. Therefore, the device is responsible for maximizing the storage capacity of the
hard disk (Sammons 2015).
(ii) Head,
Head is s device that is located on the arm of the hard disk, and it is responsible for reading and
writing the information that is the data from the hard drive. Ideally, the hard drivers usually have
one read and write the header on each platter.
(iii) Tracks,
This is the circular part on the surface of the hard disk where information is magnetically
recorded, and it is usually from this recorded information is interpreted.
(iv) Sector. (4 Marks)
The industry is the subdivision of the track on the magnetic disk. It is used to store accessible
user information that is always fixed to a certain number. In that point of view, the sector is the
smallest storage unit of the hard disk.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
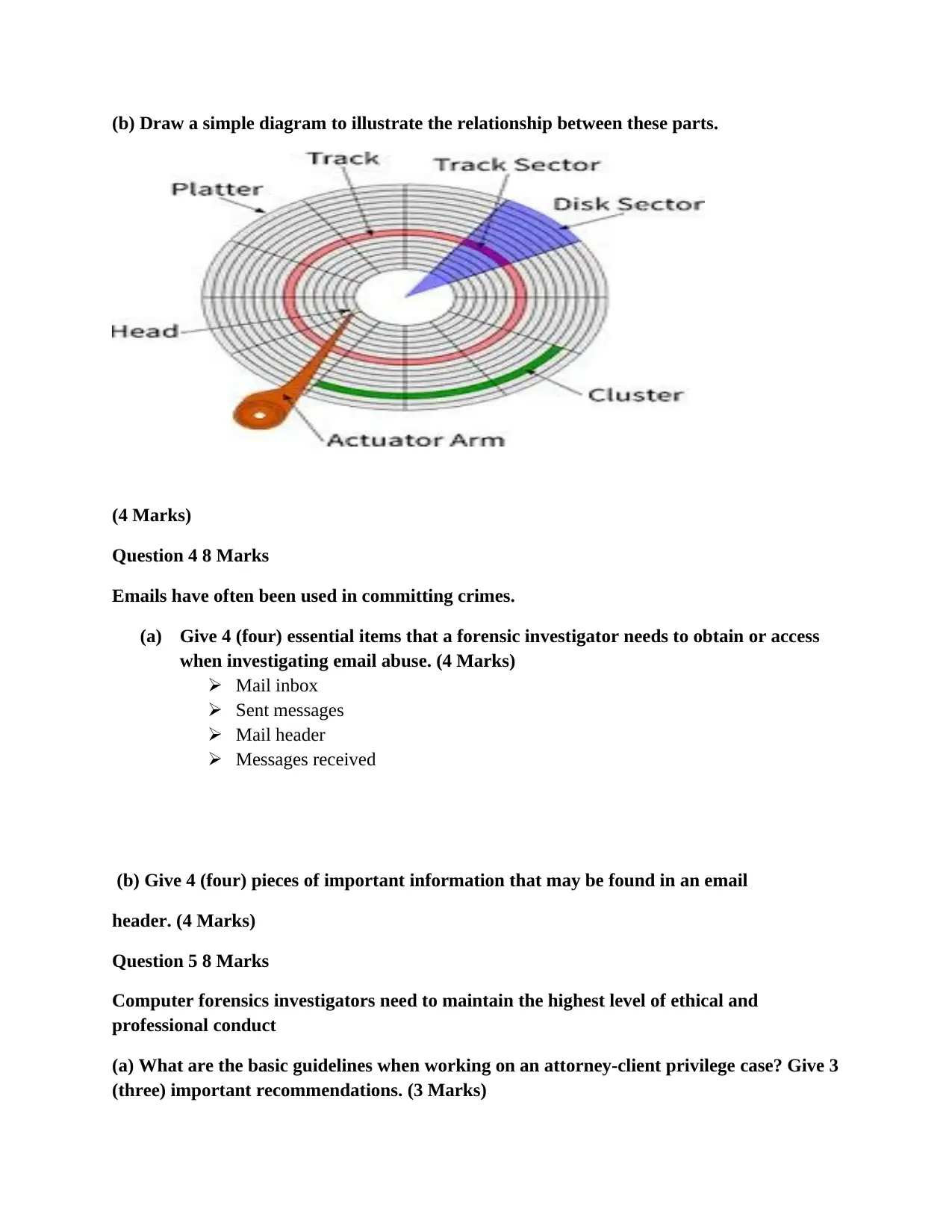
(b) Draw a simple diagram to illustrate the relationship between these parts.
(4 Marks)
Question 4 8 Marks
Emails have often been used in committing crimes.
(a) Give 4 (four) essential items that a forensic investigator needs to obtain or access
when investigating email abuse. (4 Marks)
Mail inbox
Sent messages
Mail header
Messages received
(b) Give 4 (four) pieces of important information that may be found in an email
header. (4 Marks)
Question 5 8 Marks
Computer forensics investigators need to maintain the highest level of ethical and
professional conduct
(a) What are the basic guidelines when working on an attorney-client privilege case? Give 3
(three) important recommendations. (3 Marks)
(4 Marks)
Question 4 8 Marks
Emails have often been used in committing crimes.
(a) Give 4 (four) essential items that a forensic investigator needs to obtain or access
when investigating email abuse. (4 Marks)
Mail inbox
Sent messages
Mail header
Messages received
(b) Give 4 (four) pieces of important information that may be found in an email
header. (4 Marks)
Question 5 8 Marks
Computer forensics investigators need to maintain the highest level of ethical and
professional conduct
(a) What are the basic guidelines when working on an attorney-client privilege case? Give 3
(three) important recommendations. (3 Marks)
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
When dealing with attorney-client privilege, for the investigator to invoke them, the
communication model that remains deployed should stay based on the legal advice.
When dealing with the attorney-client privilege, the legal advice must remain kept
confidential.
When working with the attorney-client case, the investigator must ensure that they are
working on the best practice to preserve the attorney-client privilege.
(b) An effect of violating court rules or laws is the disqualification. List any 5 (five)
factors that courts have used in determining whether to disqualify an Expert Witness for a
given case. (5 Marks)
The court figures out the extent to which the expert erudite on the [party’s court case
strategies
It considers whether the expert involved was paid a fee
It also looks whether the expert retained the experts to help in the court case
It also examines if the work that i9s discussed was provided to the experts
It looks at the total number of meetings that are held between the expert and the attorneys
PART C 15 MARKS
Question 6 15 Marks
Discuss the difference between law enforcement agency investigations and corporate
investigations in the area of searches and seizures, specifically, concerning (i) the scope of
authority, (ii) its motivation or purpose, and (iii) the effects of the acquisition process
Criminal investigators are expertly trained to enforce the law with an aim to prevent future
crimes from happening by searching and seizing suspects. Therefore, as far as this concept is
concerned, there are two forms of law enforcement agencies, which include the private and
public criminal investigators (Sammons 2015). One of the differences that are exploited by the
law enforcement agencies and the corporate investigators is the fourth amendment search and
seizure. According to this amendment, the law enforcement experts have the power for the real
apprehension of the individuals by the mandate of arrest and stop a while, and the corporate
officers when performing the search, the individual has the ability to privacy. Technically, all
individual who pursues law enforcement career is driven by the factor that they are called to
protect and serve. Therefore, their commander is well aware that fir these officers to work well
there is the need for motivation that they need to increase their productivity. For instance, law
enforcement officers use the concept of reducing stress, provision of basic needs, provision of
medical covers and so on (Sammons 2015).
GIVE CLEAR AND COMPLETE ANSWERS. (35 MARKS)
Question 1 (5 marks)
communication model that remains deployed should stay based on the legal advice.
When dealing with the attorney-client privilege, the legal advice must remain kept
confidential.
When working with the attorney-client case, the investigator must ensure that they are
working on the best practice to preserve the attorney-client privilege.
(b) An effect of violating court rules or laws is the disqualification. List any 5 (five)
factors that courts have used in determining whether to disqualify an Expert Witness for a
given case. (5 Marks)
The court figures out the extent to which the expert erudite on the [party’s court case
strategies
It considers whether the expert involved was paid a fee
It also looks whether the expert retained the experts to help in the court case
It also examines if the work that i9s discussed was provided to the experts
It looks at the total number of meetings that are held between the expert and the attorneys
PART C 15 MARKS
Question 6 15 Marks
Discuss the difference between law enforcement agency investigations and corporate
investigations in the area of searches and seizures, specifically, concerning (i) the scope of
authority, (ii) its motivation or purpose, and (iii) the effects of the acquisition process
Criminal investigators are expertly trained to enforce the law with an aim to prevent future
crimes from happening by searching and seizing suspects. Therefore, as far as this concept is
concerned, there are two forms of law enforcement agencies, which include the private and
public criminal investigators (Sammons 2015). One of the differences that are exploited by the
law enforcement agencies and the corporate investigators is the fourth amendment search and
seizure. According to this amendment, the law enforcement experts have the power for the real
apprehension of the individuals by the mandate of arrest and stop a while, and the corporate
officers when performing the search, the individual has the ability to privacy. Technically, all
individual who pursues law enforcement career is driven by the factor that they are called to
protect and serve. Therefore, their commander is well aware that fir these officers to work well
there is the need for motivation that they need to increase their productivity. For instance, law
enforcement officers use the concept of reducing stress, provision of basic needs, provision of
medical covers and so on (Sammons 2015).
GIVE CLEAR AND COMPLETE ANSWERS. (35 MARKS)
Question 1 (5 marks)
Evidence acquisition techniques
Evidence acquisition remains to be a proactive critical activity that is carried out in the digital
forensic investigation. The most used technology to acquire evidence currently is the live
acquisition (Sammons 2015). In this method, data remain retrieved from the digital system
directly through its standard interface. Additionally, this method of data acquisition has its
importance because it allows the investigator to collect the information from the RAM in cases
where the machine is found turned on, earlier to seizure. However, the three main method used
in the acquisition of evidence is the logical acquisition, the bitstream that is the disk to image,
and bitstream that is disk to disk.
The integrity of a digital image
Digital image acquisition is the concept of creating a digital image. This creation tends to involve
the nature of the natural scene or interior structure of an object (Sammons 2015). Therefore, the
ideology of integrity is a paramount aspect in the field of forensics. Ideally, this philosophy is
important because courts tend to decide on all case depending on the evidence that is presented
to the judges. Additionally, most of the forensic professional may need to make correction and
adjustment to the images such as the separation of the cells from one person to under with aim to
enhance a fingerprint. In that regard, it is vital for the professional to maintain the highest
integrity throughout the process so that the evidence brought out from the image is valid and
accurate.
Question 2(5 marks)
Rootkits as the collection of data for investigation or evidence Malware as acquired
evidence in the digital forensics investigation
Rootkits are subprogram that tends to allow someone to access and gain control of a computer
system without being noticed. Therefore, rootkits with their payload have numerous uses such as
it will enable the attacker to gain access and steal the documents’ from the computer, conceal
other software to gain critical logins such as passwords of machines. On the other hand, Malware
is software that is used to interrupt the computer, network, and server so that it gains access to
the laptop and fetch the information to be used as evidence.
Forensic tool testing program of NIST
Forensic tool testing program of NIST is a methodology developed with an aim to testing
computers forensic software by the usage of the general tool of necessities. The mentioned
specifications are examined criteria, test procedures, test sets, and test hardware. The information
that is collected from this process is used by the toolmaker to improve on the tools so that the
users are capable of making informed choices on the acquisition and usage of the forensic tools.
Question 3 (5 marks)
Evidence acquisition remains to be a proactive critical activity that is carried out in the digital
forensic investigation. The most used technology to acquire evidence currently is the live
acquisition (Sammons 2015). In this method, data remain retrieved from the digital system
directly through its standard interface. Additionally, this method of data acquisition has its
importance because it allows the investigator to collect the information from the RAM in cases
where the machine is found turned on, earlier to seizure. However, the three main method used
in the acquisition of evidence is the logical acquisition, the bitstream that is the disk to image,
and bitstream that is disk to disk.
The integrity of a digital image
Digital image acquisition is the concept of creating a digital image. This creation tends to involve
the nature of the natural scene or interior structure of an object (Sammons 2015). Therefore, the
ideology of integrity is a paramount aspect in the field of forensics. Ideally, this philosophy is
important because courts tend to decide on all case depending on the evidence that is presented
to the judges. Additionally, most of the forensic professional may need to make correction and
adjustment to the images such as the separation of the cells from one person to under with aim to
enhance a fingerprint. In that regard, it is vital for the professional to maintain the highest
integrity throughout the process so that the evidence brought out from the image is valid and
accurate.
Question 2(5 marks)
Rootkits as the collection of data for investigation or evidence Malware as acquired
evidence in the digital forensics investigation
Rootkits are subprogram that tends to allow someone to access and gain control of a computer
system without being noticed. Therefore, rootkits with their payload have numerous uses such as
it will enable the attacker to gain access and steal the documents’ from the computer, conceal
other software to gain critical logins such as passwords of machines. On the other hand, Malware
is software that is used to interrupt the computer, network, and server so that it gains access to
the laptop and fetch the information to be used as evidence.
Forensic tool testing program of NIST
Forensic tool testing program of NIST is a methodology developed with an aim to testing
computers forensic software by the usage of the general tool of necessities. The mentioned
specifications are examined criteria, test procedures, test sets, and test hardware. The information
that is collected from this process is used by the toolmaker to improve on the tools so that the
users are capable of making informed choices on the acquisition and usage of the forensic tools.
Question 3 (5 marks)
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Corporate investigation of an employee for inappropriate use of his work computer
Data compression techniques
Lossless compression, in this types of compression no data or information is lost. It is
mainly used for text files, important files such as spreadsheets. The original document/
files can be regained from the compression.
Lossy compression techniques, in this method, there is data loss during the compression
process. This method is used to compress video and sound where on the small part of the
information is there and the user can be recognized. In the case of reconstruction, all
small part of the original information/ data is still there (Quick, D., & Choo 2016).
Question 4 (5 marks)
Evidence acquisition techniques
Logical acquisition
Bit-stream disk to disk
Bit-stream disk to image
Actions to take by a forensic investigator for the files cannot be opened Bad sector of the
hard disk
Recover the lousy industry Retrieve the obscured files
Question 5 (5 marks)
Questions to ask when responding to a computer crime
How do you conduct your internal and external system test?
Which tool do you use to perform the internal and external analysis?
How do you conduct client-side attack simulations?
How do you secure your firewalls?
Questions to ask before starting the acquisition process
Where did all this start?
Suppose new evidence come up, will it supplement this evidence.
What is the procedure for acquiring this evidence?
What is the intended intention of this action?
What is the battle plan?
Copying the files vs. preserving digital evidence
Copying of record is not an important method of presenting evidence, some of the data may be
changed from the default location, all they can be accessed with unauthorized personal and alter
Data compression techniques
Lossless compression, in this types of compression no data or information is lost. It is
mainly used for text files, important files such as spreadsheets. The original document/
files can be regained from the compression.
Lossy compression techniques, in this method, there is data loss during the compression
process. This method is used to compress video and sound where on the small part of the
information is there and the user can be recognized. In the case of reconstruction, all
small part of the original information/ data is still there (Quick, D., & Choo 2016).
Question 4 (5 marks)
Evidence acquisition techniques
Logical acquisition
Bit-stream disk to disk
Bit-stream disk to image
Actions to take by a forensic investigator for the files cannot be opened Bad sector of the
hard disk
Recover the lousy industry Retrieve the obscured files
Question 5 (5 marks)
Questions to ask when responding to a computer crime
How do you conduct your internal and external system test?
Which tool do you use to perform the internal and external analysis?
How do you conduct client-side attack simulations?
How do you secure your firewalls?
Questions to ask before starting the acquisition process
Where did all this start?
Suppose new evidence come up, will it supplement this evidence.
What is the procedure for acquiring this evidence?
What is the intended intention of this action?
What is the battle plan?
Copying the files vs. preserving digital evidence
Copying of record is not an important method of presenting evidence, some of the data may be
changed from the default location, all they can be accessed with unauthorized personal and alter
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
the information. Preserving of the evidence is quite reasonable, as it will allow an individual to
confirm that there are no missing links in the CoC.
Question 6 (5 marks)
File timestamps as an evidence
The timestamp is the filing date created by the mapping subprogram such as ArcCatalog. This
file contains useful information about the edits that have remained undertaken to the file
geodatabase. The geodatabase tends to store the geographical information. This is a reliable
source of evidence, as it is not easy to forge date on this file. Therefore, this concept can remain
used as evidence in court trials (Quick, D., & Choo 2016).
Actions to take by a forensic investigator for the files cannot be opened
Recover the bad sector
Retrieve the obscured files
Question 7 (5 marks)
Emails stored on a local server vs in a cloud server?
Emails stored on the server are more secure as compared to the email stored on the local server.
This sense, server bears more advantage than cloud server. For instance, the individual who is
using it while a cloud server, he /she is renting the remote server space owns the server. For that
matter, data stored on the local server is more accessible as compared to data that is stored on the
cloud.
Hidden partition
Hidden partition is a special section that is typically set aside on the OEM hard drive on the
computer. It remains used to restore the computer system, in any case, there is a problem
PART B 30 MARKS
Question 1
List three items that should be in your case report. (3 marks)
Demographic profile
Judicial opinions
Case description
Diagnosis of the crime
confirm that there are no missing links in the CoC.
Question 6 (5 marks)
File timestamps as an evidence
The timestamp is the filing date created by the mapping subprogram such as ArcCatalog. This
file contains useful information about the edits that have remained undertaken to the file
geodatabase. The geodatabase tends to store the geographical information. This is a reliable
source of evidence, as it is not easy to forge date on this file. Therefore, this concept can remain
used as evidence in court trials (Quick, D., & Choo 2016).
Actions to take by a forensic investigator for the files cannot be opened
Recover the bad sector
Retrieve the obscured files
Question 7 (5 marks)
Emails stored on a local server vs in a cloud server?
Emails stored on the server are more secure as compared to the email stored on the local server.
This sense, server bears more advantage than cloud server. For instance, the individual who is
using it while a cloud server, he /she is renting the remote server space owns the server. For that
matter, data stored on the local server is more accessible as compared to data that is stored on the
cloud.
Hidden partition
Hidden partition is a special section that is typically set aside on the OEM hard drive on the
computer. It remains used to restore the computer system, in any case, there is a problem
PART B 30 MARKS
Question 1
List three items that should be in your case report. (3 marks)
Demographic profile
Judicial opinions
Case description
Diagnosis of the crime
Question 2
Three items found on an evidence custody form. (3 marks)
Case Id
Case lead investigator
Report of the evidence
Question 3
List three features familiar with proprietary format acquisition files. (3 marks)
Ability to split an image into further small files
Ability to integrate metadata into image files
Ability to compress or not to compress
Question 4
(a) What are the encryption algorithms used by ProDiscover to encrypt the connection
between the examiner’s and suspect’s computers? (2 marks)
Advanced cipher standard
Triple data encryption standard
(b) What to consider when determining which data acquisition method to use (2 scores)
Data size and source hard drive
Time to perform the acquisition
Is the source disk retainable as the evidence it is it a must to return to the original owner
The place that is the location for the evidence
Question 5
Items that should be in an initial-response field kit and justify their inclusion using one
line.
Laptop, the laptop is included on the initial-response kit to help analyze data that can be
used in court as evidence.
The digital camera that with the flashlight, this is carried in the equipment to capture the
image that is useful in the analysis of the digital imaging to produce it as evidence in the
court
USB cable, this cables remains used to transfer information from the suspect computer to
your laptop for investigation.
Cable tag, this is used to tag the different wire tends to show malicious activities in the
crime scene
Three items found on an evidence custody form. (3 marks)
Case Id
Case lead investigator
Report of the evidence
Question 3
List three features familiar with proprietary format acquisition files. (3 marks)
Ability to split an image into further small files
Ability to integrate metadata into image files
Ability to compress or not to compress
Question 4
(a) What are the encryption algorithms used by ProDiscover to encrypt the connection
between the examiner’s and suspect’s computers? (2 marks)
Advanced cipher standard
Triple data encryption standard
(b) What to consider when determining which data acquisition method to use (2 scores)
Data size and source hard drive
Time to perform the acquisition
Is the source disk retainable as the evidence it is it a must to return to the original owner
The place that is the location for the evidence
Question 5
Items that should be in an initial-response field kit and justify their inclusion using one
line.
Laptop, the laptop is included on the initial-response kit to help analyze data that can be
used in court as evidence.
The digital camera that with the flashlight, this is carried in the equipment to capture the
image that is useful in the analysis of the digital imaging to produce it as evidence in the
court
USB cable, this cables remains used to transfer information from the suspect computer to
your laptop for investigation.
Cable tag, this is used to tag the different wire tends to show malicious activities in the
crime scene
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Stick on labels, applied to the mark the different part of the crime scenes under which the
investigation process can stay analyzed from.
Question 6
Items stored in the FAT database. (3 marks)
File attributes
Date
Timestamp
Directories and file names
Question 7
List three sub-functions of the extraction function. (3 scores)
It is used for curving
Used for data viewing
Used for bookmaking
Question 8
Explain how to identify an unknown graphics file format that your digital forensics tool
doesn’t recognize. (3 marks)
To define the graphics file format, the first step is to inspect the hidden file by deploying
the hexadecimal editor to determine the hex code for the first few bytes of the data. After
that, there is a need to inspect the known file types, which have identical header values so
that you can confirm its file form (Sammons 2015).
Question 9
What are the necessary components of a search warrant? (3 marks)
The search warrant has four main parts bust some of the scholars say that it is three. The
central element of a search warrant includes;
Order
Return
Application
Affidavit
PART C (10 MARKS)
Question 1
investigation process can stay analyzed from.
Question 6
Items stored in the FAT database. (3 marks)
File attributes
Date
Timestamp
Directories and file names
Question 7
List three sub-functions of the extraction function. (3 scores)
It is used for curving
Used for data viewing
Used for bookmaking
Question 8
Explain how to identify an unknown graphics file format that your digital forensics tool
doesn’t recognize. (3 marks)
To define the graphics file format, the first step is to inspect the hidden file by deploying
the hexadecimal editor to determine the hex code for the first few bytes of the data. After
that, there is a need to inspect the known file types, which have identical header values so
that you can confirm its file form (Sammons 2015).
Question 9
What are the necessary components of a search warrant? (3 marks)
The search warrant has four main parts bust some of the scholars say that it is three. The
central element of a search warrant includes;
Order
Return
Application
Affidavit
PART C (10 MARKS)
Question 1
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
You’re a detective for the local police. Thomas Brown, the primary suspect in a murder
investigation, works at a large regional firm and is reported to have two computers at work in
addition to one at home. What do you need to do to gather evidence from these computers, and
what obstacles can you expect to encounter during this process?
Case description
Murder is the case according to the above description under which Mr. Brown is the primary
suspect. According to the report above, brown works in a large local firm and he possess two
computers in the firm and one at home. In the line of the forensics, the investigations of a murder
case I will start to identify the main reason why Mr. Brown is the prime suspect. After
determining, the reasons try to relate the relationship that exists between the criminal and injured
party.
Evidence collection
To obtain complete information between the prime suspect and the injured party, I will
investigate by searching all the computers. Additionally, I will check the emails that the criminal
receives and the massages that he sends. I will use software to access Mr. Brown’s network to
get detailed information about the victim’s work (Quick, D., & Choo 2016).
Obstacles during evidence collection
The possibility of hiding and deleting the information
Lack of search warrant to performing the investigation
Report compilation is very complicated. Therefore, it sounded critical for me generating
the report to remain used in the court of law as evidence
Privacy violation during the investigation, during the process of finding out the evidence-
searching place that is not recommended in the search warrant it leads to abuse of the
Fourth amendment in Law.
Write a one- to two paragraph stating
• What you would do if the company had its own Computer Forensics and
Investigations Department
If there is a computer forensic department in the firm, I will meet the attorney general and
present the information in have found about the suspect (Quick, D., & Choo 2016). After, that
the department needs to telephone the forensic professional to provide with related data about the
victim with the employees. According to the law, the company is capable of searching Mr.
Brown’s computers without the search warrant. In other words, if there is a department in the
firm, it will be much more comfortable handling the case and get more evidence in the case.
• What would you do if the company did not?
investigation, works at a large regional firm and is reported to have two computers at work in
addition to one at home. What do you need to do to gather evidence from these computers, and
what obstacles can you expect to encounter during this process?
Case description
Murder is the case according to the above description under which Mr. Brown is the primary
suspect. According to the report above, brown works in a large local firm and he possess two
computers in the firm and one at home. In the line of the forensics, the investigations of a murder
case I will start to identify the main reason why Mr. Brown is the prime suspect. After
determining, the reasons try to relate the relationship that exists between the criminal and injured
party.
Evidence collection
To obtain complete information between the prime suspect and the injured party, I will
investigate by searching all the computers. Additionally, I will check the emails that the criminal
receives and the massages that he sends. I will use software to access Mr. Brown’s network to
get detailed information about the victim’s work (Quick, D., & Choo 2016).
Obstacles during evidence collection
The possibility of hiding and deleting the information
Lack of search warrant to performing the investigation
Report compilation is very complicated. Therefore, it sounded critical for me generating
the report to remain used in the court of law as evidence
Privacy violation during the investigation, during the process of finding out the evidence-
searching place that is not recommended in the search warrant it leads to abuse of the
Fourth amendment in Law.
Write a one- to two paragraph stating
• What you would do if the company had its own Computer Forensics and
Investigations Department
If there is a computer forensic department in the firm, I will meet the attorney general and
present the information in have found about the suspect (Quick, D., & Choo 2016). After, that
the department needs to telephone the forensic professional to provide with related data about the
victim with the employees. According to the law, the company is capable of searching Mr.
Brown’s computers without the search warrant. In other words, if there is a department in the
firm, it will be much more comfortable handling the case and get more evidence in the case.
• What would you do if the company did not?
For the case that the company does not have the forensic department, this means that I will need
to work more hard to fetch details of the worker who is the primary suspect. Additionally, it also
says that the total time required to solve the problem will increase so that I can get the detailed
information to present in the court of law.
Question 2
A cloud customer has asked you to do a forensic analysis of data stored on a CSP’s server. The
customer’s attorney explains that the CSP offers little support for data acquisition and analysis
but will help with data collection for a fee. The attorney asks you to prepare a memo with
detailed questions of what you need to know to perform this task. She plans to use this memo to
negotiate for services you’ll provide in collecting and analyzing evidence (Sammons 2015).
Write a one- to two paragraph report with questions to ask the CSP. (5 marks)
When conducting cloud investigation, a systematic approach needs to remain followed so that
the information captured is relevant. This is vital because the type of activity help to figure out
the planning of the investigation (Sammons 2015). Suppose the research tends to involve
searching for the data, recovering data from the cloud customer like this, I will follow the
procedure correctly and keenly to ensure that I capture the right information. For this context, I
will develop the following questions for the customer to understand how the CSP stays created
and used;
Are there restrictions on the collection of digital evidence from the remote cloud storage?
Does the client have the detailed knowledge of the cloud’s topology?
Does the investigator have the mandate to use cloud staff to perform an investigation?
to work more hard to fetch details of the worker who is the primary suspect. Additionally, it also
says that the total time required to solve the problem will increase so that I can get the detailed
information to present in the court of law.
Question 2
A cloud customer has asked you to do a forensic analysis of data stored on a CSP’s server. The
customer’s attorney explains that the CSP offers little support for data acquisition and analysis
but will help with data collection for a fee. The attorney asks you to prepare a memo with
detailed questions of what you need to know to perform this task. She plans to use this memo to
negotiate for services you’ll provide in collecting and analyzing evidence (Sammons 2015).
Write a one- to two paragraph report with questions to ask the CSP. (5 marks)
When conducting cloud investigation, a systematic approach needs to remain followed so that
the information captured is relevant. This is vital because the type of activity help to figure out
the planning of the investigation (Sammons 2015). Suppose the research tends to involve
searching for the data, recovering data from the cloud customer like this, I will follow the
procedure correctly and keenly to ensure that I capture the right information. For this context, I
will develop the following questions for the customer to understand how the CSP stays created
and used;
Are there restrictions on the collection of digital evidence from the remote cloud storage?
Does the client have the detailed knowledge of the cloud’s topology?
Does the investigator have the mandate to use cloud staff to perform an investigation?
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 13
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.
