Ethical Hacking: Case Study on Virtual Machine with Flags and Techniques
Write a report outlining each test/attack run against the system and the result, including flags and credentials uncovered during the hacking process.
21 Pages2782 Words194 Views
Added on 2023-06-03
About This Document
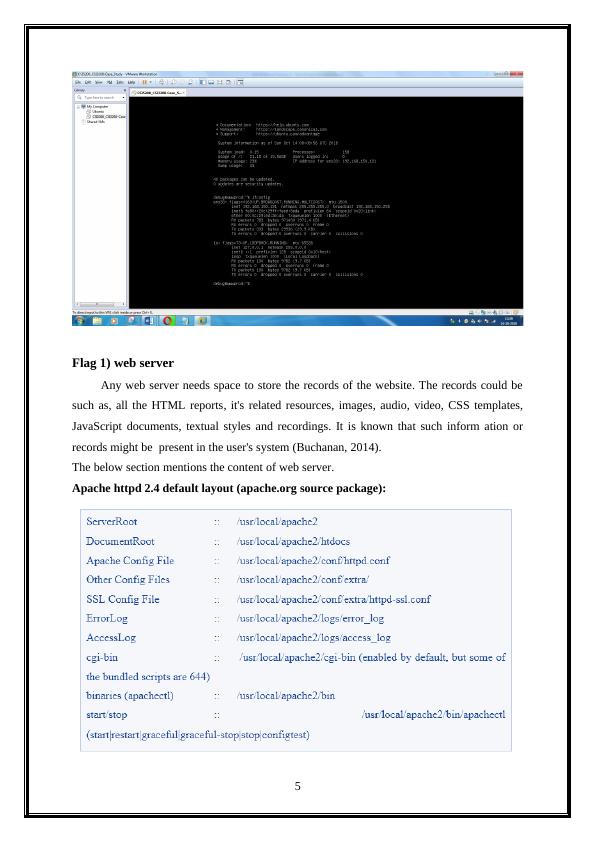
This report focuses on ethical hacking with a case study on virtual machine and flags. It covers web server content, web shells, password cracking, TCP port scanner and Linux privilege escalation. The report provides insights on tools and techniques for ethical hacking.
Ethical Hacking: Case Study on Virtual Machine with Flags and Techniques
Write a report outlining each test/attack run against the system and the result, including flags and credentials uncovered during the hacking process.
Added on 2023-06-03
ShareRelated Documents
End of preview
Want to access all the pages? Upload your documents or become a member.
Ethical Hacking: Case Study on Virtual Machine with Flags, Web Server, Web Shells, Password Cracker, TCP Port Scanner and Privilege Escalation
|21
|2782
|157
Ethical Hacking and Defense: Case Study Analysis
|11
|2129
|440
Ethical Hacking Report: Penetration Testing and Techniques
|16
|3773
|437
Ethical Hacking: Techniques and Case Study
|24
|3516
|371
Ethical Hacking: Web Shell, Apache, Nmap, Linux Privilege Escalation
|18
|1965
|111
ICT Ethical Hacking: Prevention and Exploration
|18
|1628
|242