Identifying Resources for Performing Audit
VerifiedAdded on 2019/09/18
|23
|4411
|286
Report
AI Summary
The assignment content is about the security audit process for a system. The scope of the audit includes identifying security vulnerabilities, risk evaluation, automated tools, administrative safeguards, penetration testing, and log management. The procedures include access control, planning, and reporting. The report should include project scope, findings, and recommendations to enhance security.
Contribute Materials
Your contribution can guide someone’s learning journey. Share your
documents today.
MakeBelieve, L.L.C:Network Topology
Table of Contents
Company Profile 3
Organizational Roles 5
Network Topology 7
Database Access 10
References 14
Attachment 1: Cyber Risk Assessment Report 15
Attachment 2: System Audit Policy 21
Table of Contents
Company Profile 3
Organizational Roles 5
Network Topology 7
Database Access 10
References 14
Attachment 1: Cyber Risk Assessment Report 15
Attachment 2: System Audit Policy 21
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.

1.Company Profile
MakeBelieve, LLC (MB) is a start-up company, which was founded in 2016. MakeBelieve is a
service-oriented company, which operates as a Networking-as-a-Service (Naas) provider as well
as the provision of customized network monitoring services for organizations that maintain cloud
computing applications. Due to the rise in cloud computing and virtualization technologies,
companies are increasingly opting to adopt services from third party providers as opposed to
owning and maintaining their own systems.
The emerging NaaS market is a market of vendors who provide virtual networking services for
cloud applications. As customers move towards virtualization and cloud applications, NaaS
vendors operate responsibly for handling networking activities as the emerging cloud platforms
have sought to separate segment traditional networking components. These services could
include but are not limited to Virtual Private Network (VPN), bandwidth services, multicast
protocol, security firewall, intrusion detection and prevention, content monitoring and filtering,
and antivirus software. As a relatively new startup, MB primarily focuses upon VPN, security
firewall, intrusion detection and prevention, content monitoring and filtering, and antivirus
software with plans to expand our current offering.
Cloud paradigms have gained significant popularity as customers have sought to focus primarily
on application-based architecture as opposed to maintaining the costly middlewares that are
necessary to ensure product scalability. Currently, the three services being offered besides NaaS
are Infrastructure-as-a-Service (IaaS), Platform-as-a-Service (PaaS), and Software-as-a-Service
2
MakeBelieve, LLC (MB) is a start-up company, which was founded in 2016. MakeBelieve is a
service-oriented company, which operates as a Networking-as-a-Service (Naas) provider as well
as the provision of customized network monitoring services for organizations that maintain cloud
computing applications. Due to the rise in cloud computing and virtualization technologies,
companies are increasingly opting to adopt services from third party providers as opposed to
owning and maintaining their own systems.
The emerging NaaS market is a market of vendors who provide virtual networking services for
cloud applications. As customers move towards virtualization and cloud applications, NaaS
vendors operate responsibly for handling networking activities as the emerging cloud platforms
have sought to separate segment traditional networking components. These services could
include but are not limited to Virtual Private Network (VPN), bandwidth services, multicast
protocol, security firewall, intrusion detection and prevention, content monitoring and filtering,
and antivirus software. As a relatively new startup, MB primarily focuses upon VPN, security
firewall, intrusion detection and prevention, content monitoring and filtering, and antivirus
software with plans to expand our current offering.
Cloud paradigms have gained significant popularity as customers have sought to focus primarily
on application-based architecture as opposed to maintaining the costly middlewares that are
necessary to ensure product scalability. Currently, the three services being offered besides NaaS
are Infrastructure-as-a-Service (IaaS), Platform-as-a-Service (PaaS), and Software-as-a-Service
2

(SaaS). Among these available virtualization services, NaaS operates between the SaaS layer and
the IaaS layer.
Although MakeBelieve is a relatively small company, we also provide analyst monitoring of our
customer's networks. To achieve this tasks, our analyst utilizes open-source network monitoring
tools such as wireshark to monitor our customer's network traffic. This data is directly fed into
our databases, which is directly connected to Tableau to allow for real time analysis of the
network traffic of our customers. Furthermore, our onsite Data Scientist utilizes python to
develop networking specific algorithms to provide more in-depth understanding of network
traffic patterns that could be deemed malicious or otherwise unwanted.
In the next section, we examine the various roles within the MB organization. In this section, we
examine each role and their specific responsibilities.
2. Organizational Roles
Currently, the organization maintains the following employee structure: Chief Operating Officer
(CEO), Chief Technology Officer (CTO), Principal Data Scientist, Database Administrator,
Senior Cyber Network Analyst, and Mid-Level Cyber Network Analyst. Since MakeBelieve is a
small NaaS service provider, it is essential that the organization’s members collaborate and
maintain multiple roles within the organization. Table 1 provides a basic breakdown of the
responsibilities of organization members. As a growing organization, responsibilities are wide
ranging and often times overlap with the duties of other members of the organization.
Table 1: MakeBelieve (MB) Roles and Responsibilities
3
the IaaS layer.
Although MakeBelieve is a relatively small company, we also provide analyst monitoring of our
customer's networks. To achieve this tasks, our analyst utilizes open-source network monitoring
tools such as wireshark to monitor our customer's network traffic. This data is directly fed into
our databases, which is directly connected to Tableau to allow for real time analysis of the
network traffic of our customers. Furthermore, our onsite Data Scientist utilizes python to
develop networking specific algorithms to provide more in-depth understanding of network
traffic patterns that could be deemed malicious or otherwise unwanted.
In the next section, we examine the various roles within the MB organization. In this section, we
examine each role and their specific responsibilities.
2. Organizational Roles
Currently, the organization maintains the following employee structure: Chief Operating Officer
(CEO), Chief Technology Officer (CTO), Principal Data Scientist, Database Administrator,
Senior Cyber Network Analyst, and Mid-Level Cyber Network Analyst. Since MakeBelieve is a
small NaaS service provider, it is essential that the organization’s members collaborate and
maintain multiple roles within the organization. Table 1 provides a basic breakdown of the
responsibilities of organization members. As a growing organization, responsibilities are wide
ranging and often times overlap with the duties of other members of the organization.
Table 1: MakeBelieve (MB) Roles and Responsibilities
3

Role Responsibility
Chief Executive Officer
(CEO)
Responsible for developing and implementing the long-term
strategy of the organization
Chief Technology Officer
(CTO)
Responsible for technical and scientific components of
organization development
Database Administrator Responsible for managing and maintaining various database
systems
Principal Data Scientist Responsible for developing Machine learning algorithms
that can be used to process data within the company
Senior Cyber Network
Analyst
Provides direct leadership to Cyber Analyst Team
Cyber Network Analyst Analyzes network traffic behavior and provides real-time
analyses for customers
Operations Staff Manages the daily operations of MB
As presented in Table 1, the division of responsibility among members of MB is quite diverse.
As an organization, the CEO is responsible for developing and implementing the long-term
strategy of the organization. Given the relatively small stature of our organization, the CEO is
also responsible for ensuring the financial longevity of the company. Within the organization, the
CTO is responsible for overseeing the technical implementation of new technologies and
techniques within the organization. As the company continues to grow within the emerging cloud
market, the CTO is responsible for understanding and harnessing these emerging cloud
technologies for our customers. Outside of the executive personnel, MB relies heavily upon its
operations team to provide top quality service and spur the growth of our organization.
The Principal Data Scientist is primarily concerned with developing and optimizing the various
machine learning algorithms that are implemented to process the network data in real-time. The
role of the Data Scientist is essential, as the algorithms that are used to process network activity
must constantly be optimized as new patterns emerge.
4
Chief Executive Officer
(CEO)
Responsible for developing and implementing the long-term
strategy of the organization
Chief Technology Officer
(CTO)
Responsible for technical and scientific components of
organization development
Database Administrator Responsible for managing and maintaining various database
systems
Principal Data Scientist Responsible for developing Machine learning algorithms
that can be used to process data within the company
Senior Cyber Network
Analyst
Provides direct leadership to Cyber Analyst Team
Cyber Network Analyst Analyzes network traffic behavior and provides real-time
analyses for customers
Operations Staff Manages the daily operations of MB
As presented in Table 1, the division of responsibility among members of MB is quite diverse.
As an organization, the CEO is responsible for developing and implementing the long-term
strategy of the organization. Given the relatively small stature of our organization, the CEO is
also responsible for ensuring the financial longevity of the company. Within the organization, the
CTO is responsible for overseeing the technical implementation of new technologies and
techniques within the organization. As the company continues to grow within the emerging cloud
market, the CTO is responsible for understanding and harnessing these emerging cloud
technologies for our customers. Outside of the executive personnel, MB relies heavily upon its
operations team to provide top quality service and spur the growth of our organization.
The Principal Data Scientist is primarily concerned with developing and optimizing the various
machine learning algorithms that are implemented to process the network data in real-time. The
role of the Data Scientist is essential, as the algorithms that are used to process network activity
must constantly be optimized as new patterns emerge.
4
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

The Database Administrator manages the databases throughout the organization by creating,
modifying and updating the organization’s tables while ensuring the integrity of the data. As an
analytics company, which uses data to develop a platform for our service, we are highly
dependent upon the work of our Database Administrator to assist with developing and
maintaining our database system. The Database Administrator also is the responsible for
configuring our database and ensuring that the integrity of the data is maintained.
The Senior Cyber Network Analyst is responsible for coordinating the overall customer efforts
of the Cyber Network Analyst. The Senior Cyber Analyst is also responsible for overseeing the
work and activities of the more junior cyber analyst. Finally, Cyber Network Analysts are
responsible for analyzing the network activities and relaying their insights to customers. The
Operations staff assist in maintaining the daily operations of the MB organization.
3. Network Topology
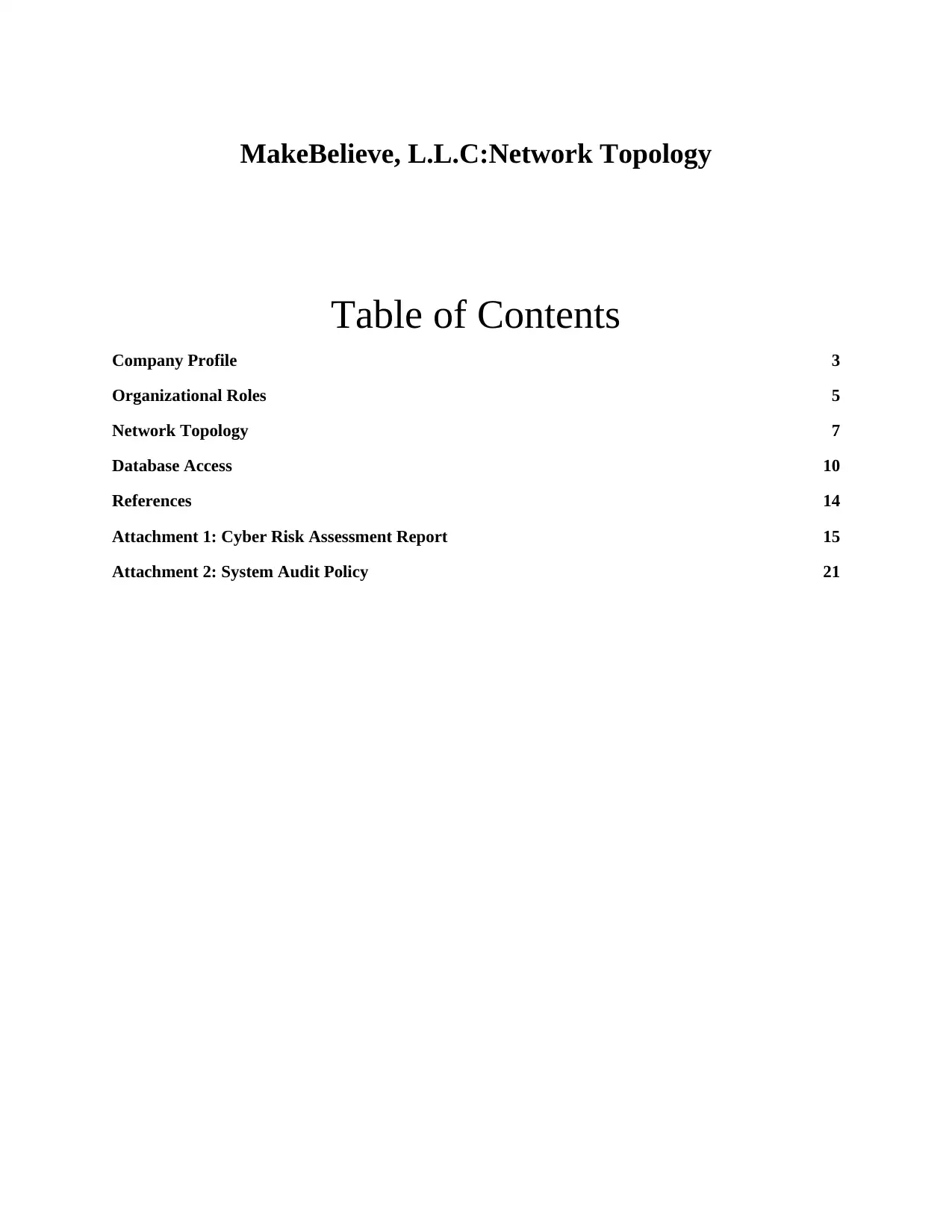
Diagram 1: MakeBelieve External Network Topology
5
modifying and updating the organization’s tables while ensuring the integrity of the data. As an
analytics company, which uses data to develop a platform for our service, we are highly
dependent upon the work of our Database Administrator to assist with developing and
maintaining our database system. The Database Administrator also is the responsible for
configuring our database and ensuring that the integrity of the data is maintained.
The Senior Cyber Network Analyst is responsible for coordinating the overall customer efforts
of the Cyber Network Analyst. The Senior Cyber Analyst is also responsible for overseeing the
work and activities of the more junior cyber analyst. Finally, Cyber Network Analysts are
responsible for analyzing the network activities and relaying their insights to customers. The
Operations staff assist in maintaining the daily operations of the MB organization.
3. Network Topology
Diagram 1: MakeBelieve External Network Topology
5
Diagram 1 was created using Creately Software
In Diagram 1, we present the external MB network topology. Within our organization, we have a
wireless router as each of our employees is provided with a MacBook Pro for work-related
activities. Given that we operate in an open work environment, work laptops provide optimal
mobility for our employees. Within the work environment, we employ wireless network
architecture, while within our wireless network, we employ both an external and internal
firewall. To ensure that we maintain a secured connection to our application, we also utilize a
Virtual Private Network (VPN) to connect directly to our cloud application.
Diagram 2: MakeBelieve Internal Cloud Application
6
In Diagram 1, we present the external MB network topology. Within our organization, we have a
wireless router as each of our employees is provided with a MacBook Pro for work-related
activities. Given that we operate in an open work environment, work laptops provide optimal
mobility for our employees. Within the work environment, we employ wireless network
architecture, while within our wireless network, we employ both an external and internal
firewall. To ensure that we maintain a secured connection to our application, we also utilize a
Virtual Private Network (VPN) to connect directly to our cloud application.
Diagram 2: MakeBelieve Internal Cloud Application
6

(ConceptDraw 2017)
Diagram 2 highlights the architecture of the MakeBelieve Cloud application. Within our
application, we utilize a full AWS cloud platform suite. Our organization opted for the private
cloud suite to allow for optimal control of our platform and to provide the greatest means of
control over our platform application. For our base infrastructure, we use the AWS cloud
application with the cloud application using an AWS Infrastructure-as-a-Service (IaaS) to host
our various databases as well as provide the computational resources for our application. As we
are a growing analytics company, the flexibility provided by IaaS offers unique opportunities for
growth as we only pay for the infrastructure services that we use. As the cloud platform is our
platform of choice, we must be cognizant of the security risks that are associated with the
platform.
7
Diagram 2 highlights the architecture of the MakeBelieve Cloud application. Within our
application, we utilize a full AWS cloud platform suite. Our organization opted for the private
cloud suite to allow for optimal control of our platform and to provide the greatest means of
control over our platform application. For our base infrastructure, we use the AWS cloud
application with the cloud application using an AWS Infrastructure-as-a-Service (IaaS) to host
our various databases as well as provide the computational resources for our application. As we
are a growing analytics company, the flexibility provided by IaaS offers unique opportunities for
growth as we only pay for the infrastructure services that we use. As the cloud platform is our
platform of choice, we must be cognizant of the security risks that are associated with the
platform.
7
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.

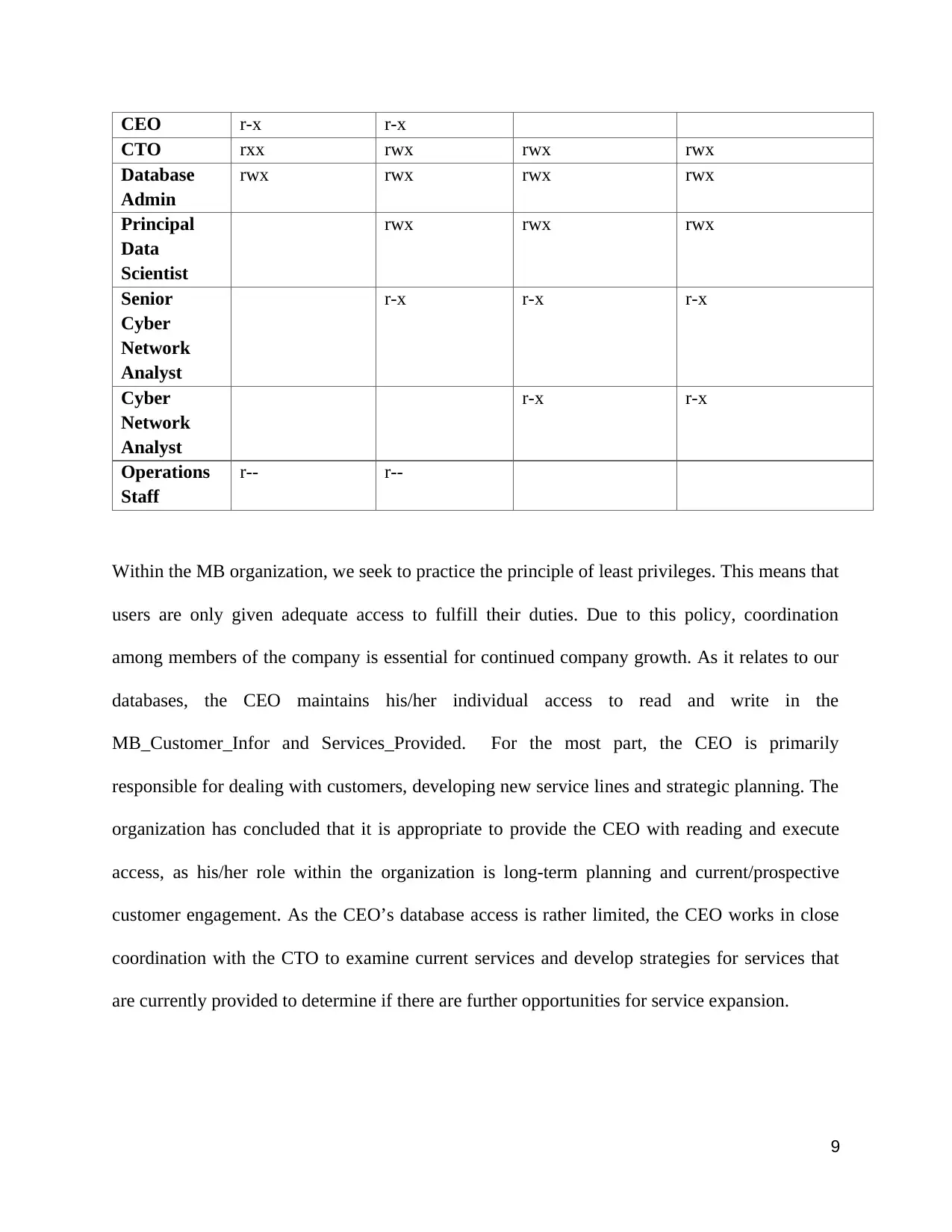
In Table 2, we highlight the various tables that are used throughout our organization. The first
database is MB_Customers, which contains data directly related to the customers. This table is
mostly used to assist with business related analysis. The next table used within our
organizational database is the Services_Provided table. This table contains data related to the
current services provided to our customers. MB uses this table to run analysis regarding the
outlook of our company. The next table in the database is Network_Packet_Data. This table
breaks down the data related to the network packets that are passing through our customer
network layer. Our data scientist uses this table to feed through the algorithms to describe how
activity patterns are flowing for our customers. The last data table within our database is the
Customers_Network_Activity table. Within this table, we house information directly related to
the network activity on our customer's pages. This table is often used in coordination with the
Network_Packet_Table to provide more detailed analyst-led conversations with our customers.
Table 2: MakeBelieve Database Tables
MB_Customers Services_Provided Network_Packet_Data Customers_Networ
k_Activity
Customer_Name SP_Provided Port_Number IP_Address
Customer_Industry Tier_Type Protocol_Number Time_Of_Visit
Active_Account Contract_Length File_Attached_Y_N Target_Page
Customer_Type Packet_Data Last_Page_Visited
SP_Provided IP_Location
Contact_Info
4. Database Access
Table 3: Employee Access Privileges
Role MB_Customers_
Info
Services_Provi
ded
Network_Packet_
Data
Customers_Network_A
ctivity
8
database is MB_Customers, which contains data directly related to the customers. This table is
mostly used to assist with business related analysis. The next table used within our
organizational database is the Services_Provided table. This table contains data related to the
current services provided to our customers. MB uses this table to run analysis regarding the
outlook of our company. The next table in the database is Network_Packet_Data. This table
breaks down the data related to the network packets that are passing through our customer
network layer. Our data scientist uses this table to feed through the algorithms to describe how
activity patterns are flowing for our customers. The last data table within our database is the
Customers_Network_Activity table. Within this table, we house information directly related to
the network activity on our customer's pages. This table is often used in coordination with the
Network_Packet_Table to provide more detailed analyst-led conversations with our customers.
Table 2: MakeBelieve Database Tables
MB_Customers Services_Provided Network_Packet_Data Customers_Networ
k_Activity
Customer_Name SP_Provided Port_Number IP_Address
Customer_Industry Tier_Type Protocol_Number Time_Of_Visit
Active_Account Contract_Length File_Attached_Y_N Target_Page
Customer_Type Packet_Data Last_Page_Visited
SP_Provided IP_Location
Contact_Info
4. Database Access
Table 3: Employee Access Privileges
Role MB_Customers_
Info
Services_Provi
ded
Network_Packet_
Data
Customers_Network_A
ctivity
8
CEO r-x r-x
CTO rxx rwx rwx rwx
Database
Admin
rwx rwx rwx rwx
Principal
Data
Scientist
rwx rwx rwx
Senior
Cyber
Network
Analyst
r-x r-x r-x
Cyber
Network
Analyst
r-x r-x
Operations
Staff
r-- r--
Within the MB organization, we seek to practice the principle of least privileges. This means that
users are only given adequate access to fulfill their duties. Due to this policy, coordination
among members of the company is essential for continued company growth. As it relates to our
databases, the CEO maintains his/her individual access to read and write in the
MB_Customer_Infor and Services_Provided. For the most part, the CEO is primarily
responsible for dealing with customers, developing new service lines and strategic planning. The
organization has concluded that it is appropriate to provide the CEO with reading and execute
access, as his/her role within the organization is long-term planning and current/prospective
customer engagement. As the CEO’s database access is rather limited, the CEO works in close
coordination with the CTO to examine current services and develop strategies for services that
are currently provided to determine if there are further opportunities for service expansion.
9
CTO rxx rwx rwx rwx
Database
Admin
rwx rwx rwx rwx
Principal
Data
Scientist
rwx rwx rwx
Senior
Cyber
Network
Analyst
r-x r-x r-x
Cyber
Network
Analyst
r-x r-x
Operations
Staff
r-- r--
Within the MB organization, we seek to practice the principle of least privileges. This means that
users are only given adequate access to fulfill their duties. Due to this policy, coordination
among members of the company is essential for continued company growth. As it relates to our
databases, the CEO maintains his/her individual access to read and write in the
MB_Customer_Infor and Services_Provided. For the most part, the CEO is primarily
responsible for dealing with customers, developing new service lines and strategic planning. The
organization has concluded that it is appropriate to provide the CEO with reading and execute
access, as his/her role within the organization is long-term planning and current/prospective
customer engagement. As the CEO’s database access is rather limited, the CEO works in close
coordination with the CTO to examine current services and develop strategies for services that
are currently provided to determine if there are further opportunities for service expansion.
9

Within the organization, the CTO is one of two individuals within the organization with full
access to all the databases. We determined that it would be most appropriate to provide the CTO
with full access rights as they are responsible for both handling corporate responsibilities as well
as ensuring that the current technologies and algorithms being deployed within the organization
are optimized for the clients’ needs.
The Database Administrator has full read, write and execute access to all databases within the
organization. This is because he/she is fully responsible for developing and maintaining of all
our database systems. Within each table, the Database Administrator has read, write and execute
privileges. This individual works in close coordination with the CTO, Data Scientist and Senior
Cyber Analyst to develop new table schemas that could assist the team in providing effective
customer service.
One of the most central figures in the MB organization is our Principal Data Scientist. Within
this role, the Principal Data Science is responsible for reviewing and developing new algorithms
that are used by our Cyber Analyst team to establish patterns in networking behaviors. The
Principal Data Scientist has read, write and execute access to the following tables:
Services_Provided table, Network_Packet_Data, and the Customers_Network_Activity table.
The access provided to our Data Scientist is as in the previously mentioned table that provides
opportunities for algorithm development and maintenance.
The Cyber Analyst team is the most customer-facing component of our organization. These
individuals are directly responsible for providing weekly reports on networking activities for
customers. As these are regular meetings, the cyber analyst team conducts standing meetings on
10
access to all the databases. We determined that it would be most appropriate to provide the CTO
with full access rights as they are responsible for both handling corporate responsibilities as well
as ensuring that the current technologies and algorithms being deployed within the organization
are optimized for the clients’ needs.
The Database Administrator has full read, write and execute access to all databases within the
organization. This is because he/she is fully responsible for developing and maintaining of all
our database systems. Within each table, the Database Administrator has read, write and execute
privileges. This individual works in close coordination with the CTO, Data Scientist and Senior
Cyber Analyst to develop new table schemas that could assist the team in providing effective
customer service.
One of the most central figures in the MB organization is our Principal Data Scientist. Within
this role, the Principal Data Science is responsible for reviewing and developing new algorithms
that are used by our Cyber Analyst team to establish patterns in networking behaviors. The
Principal Data Scientist has read, write and execute access to the following tables:
Services_Provided table, Network_Packet_Data, and the Customers_Network_Activity table.
The access provided to our Data Scientist is as in the previously mentioned table that provides
opportunities for algorithm development and maintenance.
The Cyber Analyst team is the most customer-facing component of our organization. These
individuals are directly responsible for providing weekly reports on networking activities for
customers. As these are regular meetings, the cyber analyst team conducts standing meetings on
10
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

Monday to review activity from the previous week. As the most customer-facing component of
our organization, the Senior Cyber Analyst has read and executed access to the
Services_Provided table, the Network_Packet_Data, and the Customers_Network_Activity table.
The non-senior members of the Cyber Analyst team have read and executed access to the the
Network_Packet_Data table and the Customers_Network_Activity table.
5. Platform Threats, Risks, and Vulnerabilities
As cloud platforms continue to grow in popularity, the relative risks associated with them also
continues to grow. According to a 2016 report released by Cloud Security Alliance, there are
Data Breaches, weak identity credential, insecure APi’s, application hijacking and data loss were
considered to be some of the biggest threats to cloud platforms (CSA 2016). Given the increasing
risks associated with cloud applications, MB has a sought to take additional steps to ensure the
integrity of our platform. In the report entitled, “MakeBelieve L.L.C. Cyber Risk Assessment
Report”, MB outlines further outlines the risks associated with our system as well as the steps
that MB has taken to mitigate that risk.
Table 4: Cloud Threat Types
Threat Type Description
Data breaches the incident where information is released without
proper approval or authorization to do so
Weak identity Credentials instances where authorized uses do not have strong
credentials to log into the site
11
our organization, the Senior Cyber Analyst has read and executed access to the
Services_Provided table, the Network_Packet_Data, and the Customers_Network_Activity table.
The non-senior members of the Cyber Analyst team have read and executed access to the the
Network_Packet_Data table and the Customers_Network_Activity table.
5. Platform Threats, Risks, and Vulnerabilities
As cloud platforms continue to grow in popularity, the relative risks associated with them also
continues to grow. According to a 2016 report released by Cloud Security Alliance, there are
Data Breaches, weak identity credential, insecure APi’s, application hijacking and data loss were
considered to be some of the biggest threats to cloud platforms (CSA 2016). Given the increasing
risks associated with cloud applications, MB has a sought to take additional steps to ensure the
integrity of our platform. In the report entitled, “MakeBelieve L.L.C. Cyber Risk Assessment
Report”, MB outlines further outlines the risks associated with our system as well as the steps
that MB has taken to mitigate that risk.
Table 4: Cloud Threat Types
Threat Type Description
Data breaches the incident where information is released without
proper approval or authorization to do so
Weak identity Credentials instances where authorized uses do not have strong
credentials to log into the site
11

System and application
vulnerability
instance where there are exploitable issues within
the code base for the system
Account hijacking the incident where a user an attack form to gain
control of the credentials of a verified user
Denial of service incident when illegitimate traffic is used to remove
availability of a website
MB Auditing
System auditing is considered the systematic process of reviewing internal records and
documentation to determine if company employees or software are adhering to predetermined
criteria. As MB is contractually obligated to perform regular audits of the MB, we have outlined
our policy in the MB System Audit attachment.
12
vulnerability
instance where there are exploitable issues within
the code base for the system
Account hijacking the incident where a user an attack form to gain
control of the credentials of a verified user
Denial of service incident when illegitimate traffic is used to remove
availability of a website
MB Auditing
System auditing is considered the systematic process of reviewing internal records and
documentation to determine if company employees or software are adhering to predetermined
criteria. As MB is contractually obligated to perform regular audits of the MB, we have outlined
our policy in the MB System Audit attachment.
12

References
ConceptDraw. 2017. “Introduction to Cloud Computing Architecture.” Concept Draw -
Introduction to Cloud Computing Architecture. Accessed October 15.
http://www.conceptdraw.com/How-To-Guide/introduction-to-cloud-computing-architecture.
CSA. 2016. “The Treacherous 12 Cloud Computing Top Threats in 2016.” Cloud Security
Alliance. https://downloads.cloudsecurityalliance.org/assets/research/top-threats/
Treacherous-12_Cloud-Computing_Top-Threats.pdf.
13
ConceptDraw. 2017. “Introduction to Cloud Computing Architecture.” Concept Draw -
Introduction to Cloud Computing Architecture. Accessed October 15.
http://www.conceptdraw.com/How-To-Guide/introduction-to-cloud-computing-architecture.
CSA. 2016. “The Treacherous 12 Cloud Computing Top Threats in 2016.” Cloud Security
Alliance. https://downloads.cloudsecurityalliance.org/assets/research/top-threats/
Treacherous-12_Cloud-Computing_Top-Threats.pdf.
13
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.

Attachment 1: Cyber Risk Assessment Report
MakeBelieve L.L.C. Cyber Risk
Assessment Report
Executive Summary
This is a detailed Risk Assessment for the MakeBelieve L.L.C. Online Network Assessment
system. This assessment seeks to provide a comprehensive review of our private cloud
application with the purpose of addressing and mitigating both future and potential cyber
threats.
The issues identified in this assessment will be highlighted and addressed by the MakeBelieve
L.L.C. organization. This document was modified from an online sample.
14
MakeBelieve L.L.C. Cyber Risk
Assessment Report
Executive Summary
This is a detailed Risk Assessment for the MakeBelieve L.L.C. Online Network Assessment
system. This assessment seeks to provide a comprehensive review of our private cloud
application with the purpose of addressing and mitigating both future and potential cyber
threats.
The issues identified in this assessment will be highlighted and addressed by the MakeBelieve
L.L.C. organization. This document was modified from an online sample.
14

Detailed Assessment
1. Introduction
1.1 Purpose
The purpose of this cyber risk assessment is to identify threats and vulnerabilities related to the
Makebelieve (MB) Online Network Assessment system. This Risk Assessment is meant to
identify risk related to the MB Online Network Assessment system while also developing
outlining an enterprise risk mitigation plan.
1.2 Scope of Risk Assessment
The MB online Network Assessment system is composed of several parts. The external
interface is an online application that allows customers and vendors to review online reports and
receive information directly related to their own network activity. The application is built using
the Amazon Web Services platform, therefore, the entire application is housed on a private
cloud platform. The three components of the cloud application are infrastructure, platform, and
the software.
The scope of this assessment includes all of the components of the application mentioned
above.
15
1. Introduction
1.1 Purpose
The purpose of this cyber risk assessment is to identify threats and vulnerabilities related to the
Makebelieve (MB) Online Network Assessment system. This Risk Assessment is meant to
identify risk related to the MB Online Network Assessment system while also developing
outlining an enterprise risk mitigation plan.
1.2 Scope of Risk Assessment
The MB online Network Assessment system is composed of several parts. The external
interface is an online application that allows customers and vendors to review online reports and
receive information directly related to their own network activity. The application is built using
the Amazon Web Services platform, therefore, the entire application is housed on a private
cloud platform. The three components of the cloud application are infrastructure, platform, and
the software.
The scope of this assessment includes all of the components of the application mentioned
above.
15

2. Risk Assessment Approach
2.1 Participants
Role Participant
System Owner CEO
System Custodian CTO
Security Administrator Senior Cyber Analyst
Database Administrator DBA
2.2 Techniques Used
Technique Description
Risk Assessment Questionnaire
Assessment Tools The assessment team used security
testing tools to review system configurations
and identify vulnerabilities in the application.
The tools included: WebSAINT, BeyondSaaS, and nmap.
Vulnerability sources The team accessed several vulnerabilities
sources to help identify potential
vulnerabilities. The sources consulted
Included:
● SANS Top 20 (www.sans.org/top20/)
● OWASP Top 10
(www.owasp.org/documentation/topte
n.html)
● NIST I-CAT vulnerability database
(icat.nist.gov)
Review of Documentation The assessment team reviewed MakeBelieve
security policies, system documentation,
network diagrams and operational manuals related to the
Network Assessment system.
2.3 Risk Model
In determining the risks associated with the MB Network Assessment system, we used the
following classification risk model:
Risk = Threat Likelihodd x Magnitude of Impact
Likelihood (Weight Factor) Definition
High (1.0) The threat-source is highly motivated and
sufficiently capable, and controls to prevent the
vulnerability from being exercised are
ineffective
Medium (0.5) The threat-source is motivated and capable, but
16
2.1 Participants
Role Participant
System Owner CEO
System Custodian CTO
Security Administrator Senior Cyber Analyst
Database Administrator DBA
2.2 Techniques Used
Technique Description
Risk Assessment Questionnaire
Assessment Tools The assessment team used security
testing tools to review system configurations
and identify vulnerabilities in the application.
The tools included: WebSAINT, BeyondSaaS, and nmap.
Vulnerability sources The team accessed several vulnerabilities
sources to help identify potential
vulnerabilities. The sources consulted
Included:
● SANS Top 20 (www.sans.org/top20/)
● OWASP Top 10
(www.owasp.org/documentation/topte
n.html)
● NIST I-CAT vulnerability database
(icat.nist.gov)
Review of Documentation The assessment team reviewed MakeBelieve
security policies, system documentation,
network diagrams and operational manuals related to the
Network Assessment system.
2.3 Risk Model
In determining the risks associated with the MB Network Assessment system, we used the
following classification risk model:
Risk = Threat Likelihodd x Magnitude of Impact
Likelihood (Weight Factor) Definition
High (1.0) The threat-source is highly motivated and
sufficiently capable, and controls to prevent the
vulnerability from being exercised are
ineffective
Medium (0.5) The threat-source is motivated and capable, but
16
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

controls are in place that may impede
successful exercise of the vulnerability.
Low (0.1) The threat-source lacks motivation or capability,
or controls are in place to prevent, or at least
significantly impede, the vulnerability from being
exercised.
2.4 Magnitude of Impact
Impact (Score) Definition
High (100) The loss of confidentiality, integrity, or
availability could be expected to have a severe
or catastrophic adverse effect on organizational
operations, organizational assets, or
individuals.
Examples:
● A severe degradation in or loss of
mission capability to an extent and
duration that the organization is not able
to perform one or more of its primary
functions.
● Major damage to organizational assets
Medium (50) The loss of confidentiality, integrity, or
availability could be expected to have a serious
adverse effect on organizational operations,
organizational assets, or individuals.
Examples:
● Significant degradation in mission
capability to an extent and duration that
the organization is able to perform its
primary functions, but the effectiveness
of the functions is significantly reduced
● • Significant damage to organizational
assets.
Low (10) The loss of confidentiality, integrity, or
availability could be expected to have a limited
adverse effect on organizational operations,
organizational assets, or individuals.
Examples:
● Degradation in mission capability to an
extent and duration that the organization
is able to perform its primary functions,
but the effectiveness of the functions is
17
successful exercise of the vulnerability.
Low (0.1) The threat-source lacks motivation or capability,
or controls are in place to prevent, or at least
significantly impede, the vulnerability from being
exercised.
2.4 Magnitude of Impact
Impact (Score) Definition
High (100) The loss of confidentiality, integrity, or
availability could be expected to have a severe
or catastrophic adverse effect on organizational
operations, organizational assets, or
individuals.
Examples:
● A severe degradation in or loss of
mission capability to an extent and
duration that the organization is not able
to perform one or more of its primary
functions.
● Major damage to organizational assets
Medium (50) The loss of confidentiality, integrity, or
availability could be expected to have a serious
adverse effect on organizational operations,
organizational assets, or individuals.
Examples:
● Significant degradation in mission
capability to an extent and duration that
the organization is able to perform its
primary functions, but the effectiveness
of the functions is significantly reduced
● • Significant damage to organizational
assets.
Low (10) The loss of confidentiality, integrity, or
availability could be expected to have a limited
adverse effect on organizational operations,
organizational assets, or individuals.
Examples:
● Degradation in mission capability to an
extent and duration that the organization
is able to perform its primary functions,
but the effectiveness of the functions is
17

noticeably reduced
● Minor damage to organizational assets
● Minor harm to companies.
3. System Characterization
3.1 Technology Components
Component Description
Applications Network Assessment system is built upon Amazon VPC platform which
is an isolated cloud content delivery service provided by Amazon
Databases The application database is made with Amazon’s RDS IaaS service.
Networks
Protocols HTTPS is used for transmission between customer web browser and
cloud server
3.2 Data Used By System
Data Description
MB Customers ● Customer Name
● Customer Industry
● Active Account
● Customer Type
● SP Provided
● Contact Info
Services Provided ● SP Provided
● Tier Type
● Contract Length
Network Packet Data ● Port Number
● Protocol Number
● File Attached
● Packet Data
● IP Location
Customer Network Activity ● IP Address
● Time Of Visit
● Target Page
● Last Page Visited
3.4: Users
Users Description
Customers Access the system via a web browser. Can
review reports and discuss directly examine
18
● Minor damage to organizational assets
● Minor harm to companies.
3. System Characterization
3.1 Technology Components
Component Description
Applications Network Assessment system is built upon Amazon VPC platform which
is an isolated cloud content delivery service provided by Amazon
Databases The application database is made with Amazon’s RDS IaaS service.
Networks
Protocols HTTPS is used for transmission between customer web browser and
cloud server
3.2 Data Used By System
Data Description
MB Customers ● Customer Name
● Customer Industry
● Active Account
● Customer Type
● SP Provided
● Contact Info
Services Provided ● SP Provided
● Tier Type
● Contract Length
Network Packet Data ● Port Number
● Protocol Number
● File Attached
● Packet Data
● IP Location
Customer Network Activity ● IP Address
● Time Of Visit
● Target Page
● Last Page Visited
3.4: Users
Users Description
Customers Access the system via a web browser. Can
review reports and discuss directly examine
18

network behavior network activity
Executive Staff (CEO/CTO) Review customer profiles, existing contracting,
and networking activities of customers
Data Scientist Develop networking centered algorithms to
improve malicious networking activity
predictability
Cyber Analyst Review network activity to discuss reports with
customers
Staff Review customer data for operational purposes
19
Executive Staff (CEO/CTO) Review customer profiles, existing contracting,
and networking activities of customers
Data Scientist Develop networking centered algorithms to
improve malicious networking activity
predictability
Cyber Analyst Review network activity to discuss reports with
customers
Staff Review customer data for operational purposes
19
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.

Attachment 2: Systems Audit Policy
MakeBelieve L.L.C. Systems Audit Policy
The policy outlined in this document is meant to provide the requirements for the regular
collection, maintenance and review of audit logs for MakeBelieve L.L.C. applications and its
related network activity. These security audits are meant to ensure that the proper security
controls that are in place are both sufficient and effective at protecting the information of both
the MB employees and customers.
Note: This policy was crafted based upon an online sample.
1. Scope
This policy applies to all management and staff involved in the creation, deployment, operations,
or support of application and system software used throughout the MB.
2. General Policy
A regular and proactive audit policy helps to manage and reduce risks to MB’s
information systems, the data it manages, and the users it services. A security auditor
is usually an external/independent third party (or at a minimum someone who is not
operationally responsible for the area being audited), who evaluates systems for best
practices and ensures compliance with an established set of requirements and
controls.
The contracting organization or their designee uses independent security audits to
assist in ensuring security controls and safeguards are appropriate, sufficient, and
effective at treating operational and security risks. Within this framework, the
contracting organization works with MB management to define:
● Resources – Identify resources to perform the audit
● Audit Scope – Define the scope of the systems being certified and their
boundaries
● Requirements – Prepare a list of security and/or privacy requirements that are
relevant to the system
● Description – Technically and functionally describe the system including
functional systems description, system operational environment, criticality,
system architecture, interfaces, data flow, and any data privacy/system
security requirements
20
MakeBelieve L.L.C. Systems Audit Policy
The policy outlined in this document is meant to provide the requirements for the regular
collection, maintenance and review of audit logs for MakeBelieve L.L.C. applications and its
related network activity. These security audits are meant to ensure that the proper security
controls that are in place are both sufficient and effective at protecting the information of both
the MB employees and customers.
Note: This policy was crafted based upon an online sample.
1. Scope
This policy applies to all management and staff involved in the creation, deployment, operations,
or support of application and system software used throughout the MB.
2. General Policy
A regular and proactive audit policy helps to manage and reduce risks to MB’s
information systems, the data it manages, and the users it services. A security auditor
is usually an external/independent third party (or at a minimum someone who is not
operationally responsible for the area being audited), who evaluates systems for best
practices and ensures compliance with an established set of requirements and
controls.
The contracting organization or their designee uses independent security audits to
assist in ensuring security controls and safeguards are appropriate, sufficient, and
effective at treating operational and security risks. Within this framework, the
contracting organization works with MB management to define:
● Resources – Identify resources to perform the audit
● Audit Scope – Define the scope of the systems being certified and their
boundaries
● Requirements – Prepare a list of security and/or privacy requirements that are
relevant to the system
● Description – Technically and functionally describe the system including
functional systems description, system operational environment, criticality,
system architecture, interfaces, data flow, and any data privacy/system
security requirements
20
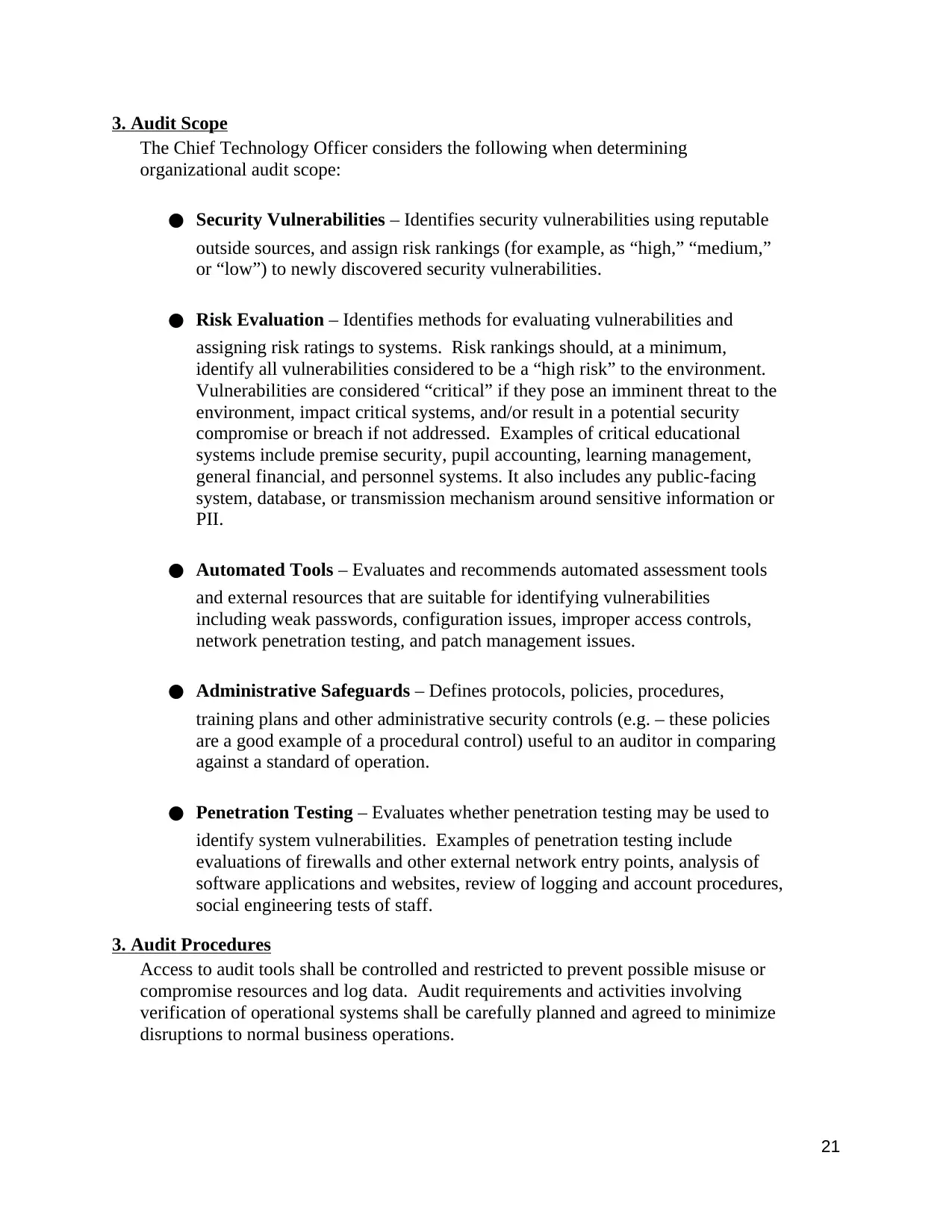
3. Audit Scope
The Chief Technology Officer considers the following when determining
organizational audit scope:
● Security Vulnerabilities – Identifies security vulnerabilities using reputable
outside sources, and assign risk rankings (for example, as “high,” “medium,”
or “low”) to newly discovered security vulnerabilities.
● Risk Evaluation – Identifies methods for evaluating vulnerabilities and
assigning risk ratings to systems. Risk rankings should, at a minimum,
identify all vulnerabilities considered to be a “high risk” to the environment.
Vulnerabilities are considered “critical” if they pose an imminent threat to the
environment, impact critical systems, and/or result in a potential security
compromise or breach if not addressed. Examples of critical educational
systems include premise security, pupil accounting, learning management,
general financial, and personnel systems. It also includes any public-facing
system, database, or transmission mechanism around sensitive information or
PII.
● Automated Tools – Evaluates and recommends automated assessment tools
and external resources that are suitable for identifying vulnerabilities
including weak passwords, configuration issues, improper access controls,
network penetration testing, and patch management issues.
● Administrative Safeguards – Defines protocols, policies, procedures,
training plans and other administrative security controls (e.g. – these policies
are a good example of a procedural control) useful to an auditor in comparing
against a standard of operation.
● Penetration Testing – Evaluates whether penetration testing may be used to
identify system vulnerabilities. Examples of penetration testing include
evaluations of firewalls and other external network entry points, analysis of
software applications and websites, review of logging and account procedures,
social engineering tests of staff.
3. Audit Procedures
Access to audit tools shall be controlled and restricted to prevent possible misuse or
compromise resources and log data. Audit requirements and activities involving
verification of operational systems shall be carefully planned and agreed to minimize
disruptions to normal business operations.
21
The Chief Technology Officer considers the following when determining
organizational audit scope:
● Security Vulnerabilities – Identifies security vulnerabilities using reputable
outside sources, and assign risk rankings (for example, as “high,” “medium,”
or “low”) to newly discovered security vulnerabilities.
● Risk Evaluation – Identifies methods for evaluating vulnerabilities and
assigning risk ratings to systems. Risk rankings should, at a minimum,
identify all vulnerabilities considered to be a “high risk” to the environment.
Vulnerabilities are considered “critical” if they pose an imminent threat to the
environment, impact critical systems, and/or result in a potential security
compromise or breach if not addressed. Examples of critical educational
systems include premise security, pupil accounting, learning management,
general financial, and personnel systems. It also includes any public-facing
system, database, or transmission mechanism around sensitive information or
PII.
● Automated Tools – Evaluates and recommends automated assessment tools
and external resources that are suitable for identifying vulnerabilities
including weak passwords, configuration issues, improper access controls,
network penetration testing, and patch management issues.
● Administrative Safeguards – Defines protocols, policies, procedures,
training plans and other administrative security controls (e.g. – these policies
are a good example of a procedural control) useful to an auditor in comparing
against a standard of operation.
● Penetration Testing – Evaluates whether penetration testing may be used to
identify system vulnerabilities. Examples of penetration testing include
evaluations of firewalls and other external network entry points, analysis of
software applications and websites, review of logging and account procedures,
social engineering tests of staff.
3. Audit Procedures
Access to audit tools shall be controlled and restricted to prevent possible misuse or
compromise resources and log data. Audit requirements and activities involving
verification of operational systems shall be carefully planned and agreed to minimize
disruptions to normal business operations.
21

Where possible, the contracted organization to audit the security controls of MB
systems. Audits shall be performed on a regular basis as defined by best practices for
companies that utilize cloud applications.
The auditor’s report shall include their project scope, findings, and recommendations
to enhance security. The CTO shall:
● Review the security auditor’s report to confirm the findings and verify the
security recommendations are sufficient and effective.
● Convey the findings to the company Board and appropriate MB heads so that
findings and resolutions can be reviewed, understood, and remedied.
4. Security Audit Log Management
Security Audit log (“audit logs”) management includes:
● Maintain Integrity, Confidentiality, and accessibility to Agency logs.
● Creation and Storage of Audit Logs – Audit logs must be retained in sufficient detail to
facilitate reconstruction of events and determination of the causes of compromise and
magnitude of damage, in response to a malfunction or a security violation.
● Review and Analysis – Timely and effective review of audit logs is required to allow
identification of security incidents, policy violations, fraudulent activity, and operational
problems; while providing information useful for resolving such problems.
● Establishment of Supporting Processes and Resources – Processes and resources must be
established to support internal investigations, forensic analysis, the establishment of
baselines, and identification of operational trends and long-term issues.
5. Content of Audit Records
The following policy provides guidance to ensure that the information that is included in audit
records is sufficient in detail to facilitate the reconstruction of events upon a suspected or actual
system compromise or malfunction.
● MB information systems shall, at a minimum, record the following information:
● Timestamp
● Domain
● Source IP address or application
22
systems. Audits shall be performed on a regular basis as defined by best practices for
companies that utilize cloud applications.
The auditor’s report shall include their project scope, findings, and recommendations
to enhance security. The CTO shall:
● Review the security auditor’s report to confirm the findings and verify the
security recommendations are sufficient and effective.
● Convey the findings to the company Board and appropriate MB heads so that
findings and resolutions can be reviewed, understood, and remedied.
4. Security Audit Log Management
Security Audit log (“audit logs”) management includes:
● Maintain Integrity, Confidentiality, and accessibility to Agency logs.
● Creation and Storage of Audit Logs – Audit logs must be retained in sufficient detail to
facilitate reconstruction of events and determination of the causes of compromise and
magnitude of damage, in response to a malfunction or a security violation.
● Review and Analysis – Timely and effective review of audit logs is required to allow
identification of security incidents, policy violations, fraudulent activity, and operational
problems; while providing information useful for resolving such problems.
● Establishment of Supporting Processes and Resources – Processes and resources must be
established to support internal investigations, forensic analysis, the establishment of
baselines, and identification of operational trends and long-term issues.
5. Content of Audit Records
The following policy provides guidance to ensure that the information that is included in audit
records is sufficient in detail to facilitate the reconstruction of events upon a suspected or actual
system compromise or malfunction.
● MB information systems shall, at a minimum, record the following information:
● Timestamp
● Domain
● Source IP address or application
22
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

● Application or service accessed
● Resource or complete URL
● Module/Function accessed
● Unique Action performed (Read/Update/Create/Delete)
● Primary record identifier
● Data field accessed/updated.
Audit Controls and Management
On-demand documented procedures and evidence of practice should be in place for this
operational policy as part of the day to day operations. Examples of controls and practices
include:
● Software Tools and logs of usage related to penetration testing
● Procedures around audit processes and response
● Documented audit results, finding, action plans, and results
Annual audit calendar schedules as appropriate.
Enforcement
Staff members found in policy violation may be subject to disciplinary action, up to and
including termination.
23
● Resource or complete URL
● Module/Function accessed
● Unique Action performed (Read/Update/Create/Delete)
● Primary record identifier
● Data field accessed/updated.
Audit Controls and Management
On-demand documented procedures and evidence of practice should be in place for this
operational policy as part of the day to day operations. Examples of controls and practices
include:
● Software Tools and logs of usage related to penetration testing
● Procedures around audit processes and response
● Documented audit results, finding, action plans, and results
Annual audit calendar schedules as appropriate.
Enforcement
Staff members found in policy violation may be subject to disciplinary action, up to and
including termination.
23
1 out of 23
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
