Network Security: Organizational Risk Assessment, Policy & Recovery
VerifiedAdded on 2024/05/21
|28
|5139
|104
Report
AI Summary
This report provides a comprehensive overview of network security, focusing on risk assessment, security policies, and disaster recovery planning for an organization. It identifies various security risks, including unauthorized system use, data copying, physical damage, and natural risks, and outlines organizational security procedures such as data backup, testing, database systems, and audits. The report also examines the impact of incorrect firewall configurations and third-party VPNs, along with the benefits of implementing network monitoring systems. Furthermore, it explains how DMZ, static IP, and NAT can enhance network security. The risk assessment process, ISO 31000 methodology, data protection processes, and the role of IT security audits are discussed. Finally, the report includes a security policy design and a disaster recovery plan, emphasizing stakeholder roles in implementing security recommendations. The document is designed to help organizations understand and implement effective network security measures to protect their data and systems.
NETWORK SECURITY
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
TABLE OF CONTENTS
INTRODUCTION...........................................................................................................................1
LO1..................................................................................................................................................2
P1 Identify types of security risks to organizations [M1]............................................................2
P2 Describe organizational security procedures..........................................................................4
LO2..................................................................................................................................................6
P3 Identify the potential impact to IT security of incorrect configuration of firewall policies
and third-party VPNs...................................................................................................................6
M2 Discuss three benefits to implement network monitoring systems with supporting reasons.
.....................................................................................................................................................7
P4 Show, using an example for each, how implementing a DMZ, static IP and NAT in a
network can improve network security........................................................................................8
LO3................................................................................................................................................11
P5 Discuss risk assessment procedure.......................................................................................11
M3 Summarize the ISO 31000 risk management methodology and its application in IT
security.......................................................................................................................................13
P6 Explain data protection processes and regulation as applicable to an organization.............14
M4 Discuss possible impacts to organization security resulting from an IT security audit......15
LO4................................................................................................................................................16
P7 Design and implement security policy for an organization..................................................16
P8 list the main components of an organizational disaster recovery plan, justifying the reasons
for inclusion...............................................................................................................................18
M5 Discuss the roles of stakeholder in the organization to implement security audit
recommendations.......................................................................................................................19
CONCLUSION..............................................................................................................................20
REFERENCES..............................................................................................................................21
INTRODUCTION...........................................................................................................................1
LO1..................................................................................................................................................2
P1 Identify types of security risks to organizations [M1]............................................................2
P2 Describe organizational security procedures..........................................................................4
LO2..................................................................................................................................................6
P3 Identify the potential impact to IT security of incorrect configuration of firewall policies
and third-party VPNs...................................................................................................................6
M2 Discuss three benefits to implement network monitoring systems with supporting reasons.
.....................................................................................................................................................7
P4 Show, using an example for each, how implementing a DMZ, static IP and NAT in a
network can improve network security........................................................................................8
LO3................................................................................................................................................11
P5 Discuss risk assessment procedure.......................................................................................11
M3 Summarize the ISO 31000 risk management methodology and its application in IT
security.......................................................................................................................................13
P6 Explain data protection processes and regulation as applicable to an organization.............14
M4 Discuss possible impacts to organization security resulting from an IT security audit......15
LO4................................................................................................................................................16
P7 Design and implement security policy for an organization..................................................16
P8 list the main components of an organizational disaster recovery plan, justifying the reasons
for inclusion...............................................................................................................................18
M5 Discuss the roles of stakeholder in the organization to implement security audit
recommendations.......................................................................................................................19
CONCLUSION..............................................................................................................................20
REFERENCES..............................................................................................................................21

⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
LIST OF TABLES
Table 1: Organizational security procedure.....................................................................................4
Table 2: Different types of organizational risk..............................................................................11
Table 1: Organizational security procedure.....................................................................................4
Table 2: Different types of organizational risk..............................................................................11
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

LIST OF FIGURES
Figure 1: Different type of security risks for an organization.........................................................2
Figure 2: Configuration of Firewall.................................................................................................6
Figure 3: Demilitarized zone (DMZ)...............................................................................................8
Figure 4: Setting Static IP................................................................................................................9
Figure 5: Network address translator.............................................................................................10
Figure 1: Different type of security risks for an organization.........................................................2
Figure 2: Configuration of Firewall.................................................................................................6
Figure 3: Demilitarized zone (DMZ)...............................................................................................8
Figure 4: Setting Static IP................................................................................................................9
Figure 5: Network address translator.............................................................................................10

INTRODUCTION
In modern days, one of the most important challenge the organization faces are related to
security. For maintenance of proper security and protection of the organization from any kind of
risk various policies and rules must be followed and implemented. In the report IT security for
GHS is studied along with various procedures and policies that are undertaken by the
organization for protecting the organization form any possible risks. Implementation of various
risk assessment procedure is studied for protection of various organizational and patient data
stored and accessed in the organizational network. The report lastly provides a design for
security policies and a plan for disaster recovery for the organization.
1
In modern days, one of the most important challenge the organization faces are related to
security. For maintenance of proper security and protection of the organization from any kind of
risk various policies and rules must be followed and implemented. In the report IT security for
GHS is studied along with various procedures and policies that are undertaken by the
organization for protecting the organization form any possible risks. Implementation of various
risk assessment procedure is studied for protection of various organizational and patient data
stored and accessed in the organizational network. The report lastly provides a design for
security policies and a plan for disaster recovery for the organization.
1
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
LO1
P1 Identify types of security risks to organizations [M1]
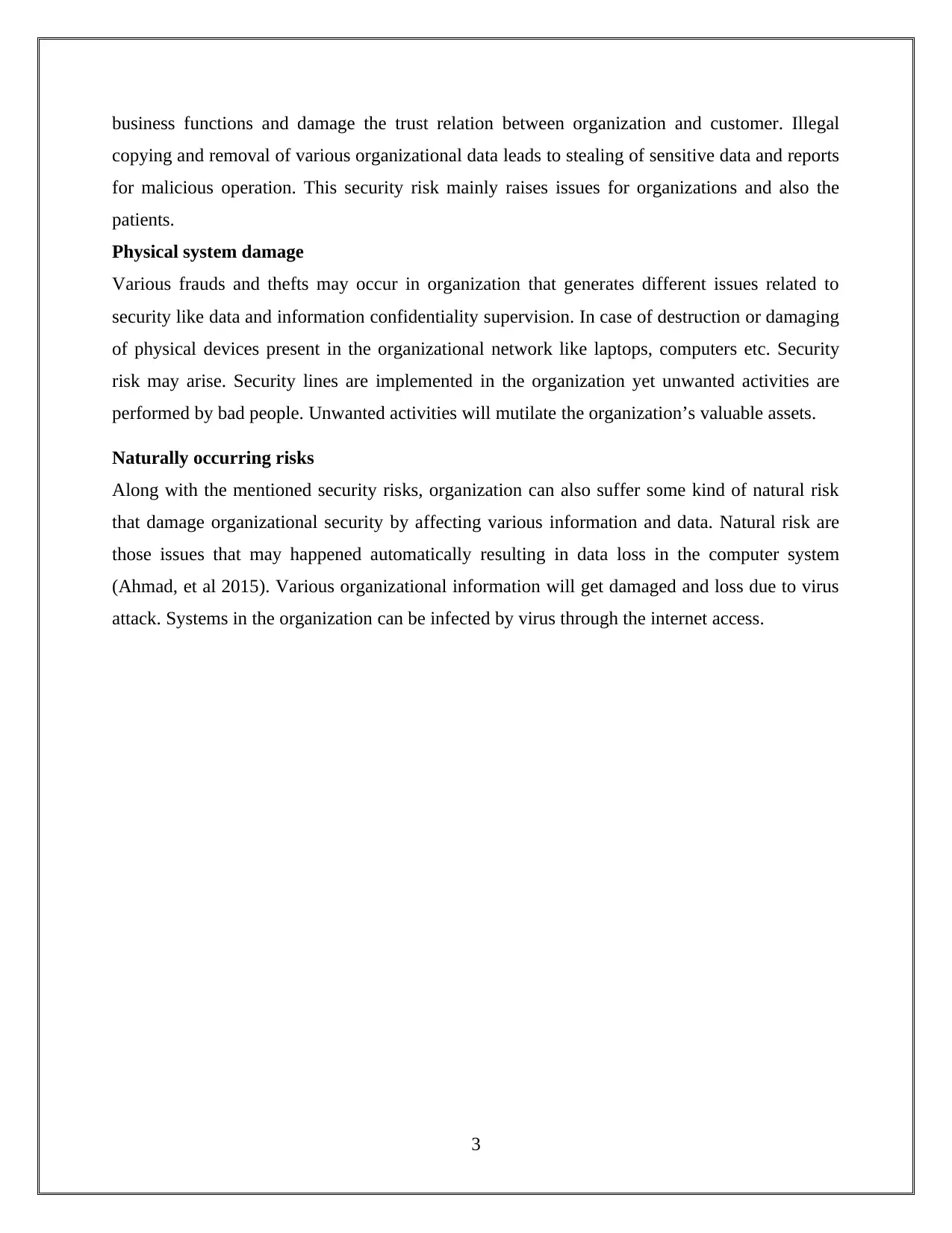
Following are some types of security risks that are involved with the GHS organization:
Figure 1: Different type of security risks for an organization
Unauthorized use of the systems
Security issues for an organization can be raised due to various unauthorized users present in the
organizational network. Global Health System implements various computers for updating and
managing patient’s information and for other business operations and function like bank
transactions. Therefore, accessibility of the computers in the network must be managed
effectively for preserving system security. However, even after taking different control for the
network security there some of the illegal users who find out a way to get system login and
access and damage the confidential information of patient and organization (Acemoglu et al
2016).
Unauthorized data copying
In present days, information burglary is considered to be one of the major problem that
organization like GHS faces. Risk in the organizational security will result in interrupt the whole
2
UNAUTHORIZED
USE OF THE
SYSTEMS
UNAUTHORIZED
DATA COPYING
PHYSICAL
SYSTEM
DAMAGE
NATURALLY
OCCURRING
RISKS
P1 Identify types of security risks to organizations [M1]
Following are some types of security risks that are involved with the GHS organization:
Figure 1: Different type of security risks for an organization
Unauthorized use of the systems
Security issues for an organization can be raised due to various unauthorized users present in the
organizational network. Global Health System implements various computers for updating and
managing patient’s information and for other business operations and function like bank
transactions. Therefore, accessibility of the computers in the network must be managed
effectively for preserving system security. However, even after taking different control for the
network security there some of the illegal users who find out a way to get system login and
access and damage the confidential information of patient and organization (Acemoglu et al
2016).
Unauthorized data copying
In present days, information burglary is considered to be one of the major problem that
organization like GHS faces. Risk in the organizational security will result in interrupt the whole
2
UNAUTHORIZED
USE OF THE
SYSTEMS
UNAUTHORIZED
DATA COPYING
PHYSICAL
SYSTEM
DAMAGE
NATURALLY
OCCURRING
RISKS
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
business functions and damage the trust relation between organization and customer. Illegal
copying and removal of various organizational data leads to stealing of sensitive data and reports
for malicious operation. This security risk mainly raises issues for organizations and also the
patients.
Physical system damage
Various frauds and thefts may occur in organization that generates different issues related to
security like data and information confidentiality supervision. In case of destruction or damaging
of physical devices present in the organizational network like laptops, computers etc. Security
risk may arise. Security lines are implemented in the organization yet unwanted activities are
performed by bad people. Unwanted activities will mutilate the organization’s valuable assets.
Naturally occurring risks
Along with the mentioned security risks, organization can also suffer some kind of natural risk
that damage organizational security by affecting various information and data. Natural risk are
those issues that may happened automatically resulting in data loss in the computer system
(Ahmad, et al 2015). Various organizational information will get damaged and loss due to virus
attack. Systems in the organization can be infected by virus through the internet access.
3
copying and removal of various organizational data leads to stealing of sensitive data and reports
for malicious operation. This security risk mainly raises issues for organizations and also the
patients.
Physical system damage
Various frauds and thefts may occur in organization that generates different issues related to
security like data and information confidentiality supervision. In case of destruction or damaging
of physical devices present in the organizational network like laptops, computers etc. Security
risk may arise. Security lines are implemented in the organization yet unwanted activities are
performed by bad people. Unwanted activities will mutilate the organization’s valuable assets.
Naturally occurring risks
Along with the mentioned security risks, organization can also suffer some kind of natural risk
that damage organizational security by affecting various information and data. Natural risk are
those issues that may happened automatically resulting in data loss in the computer system
(Ahmad, et al 2015). Various organizational information will get damaged and loss due to virus
attack. Systems in the organization can be infected by virus through the internet access.
3
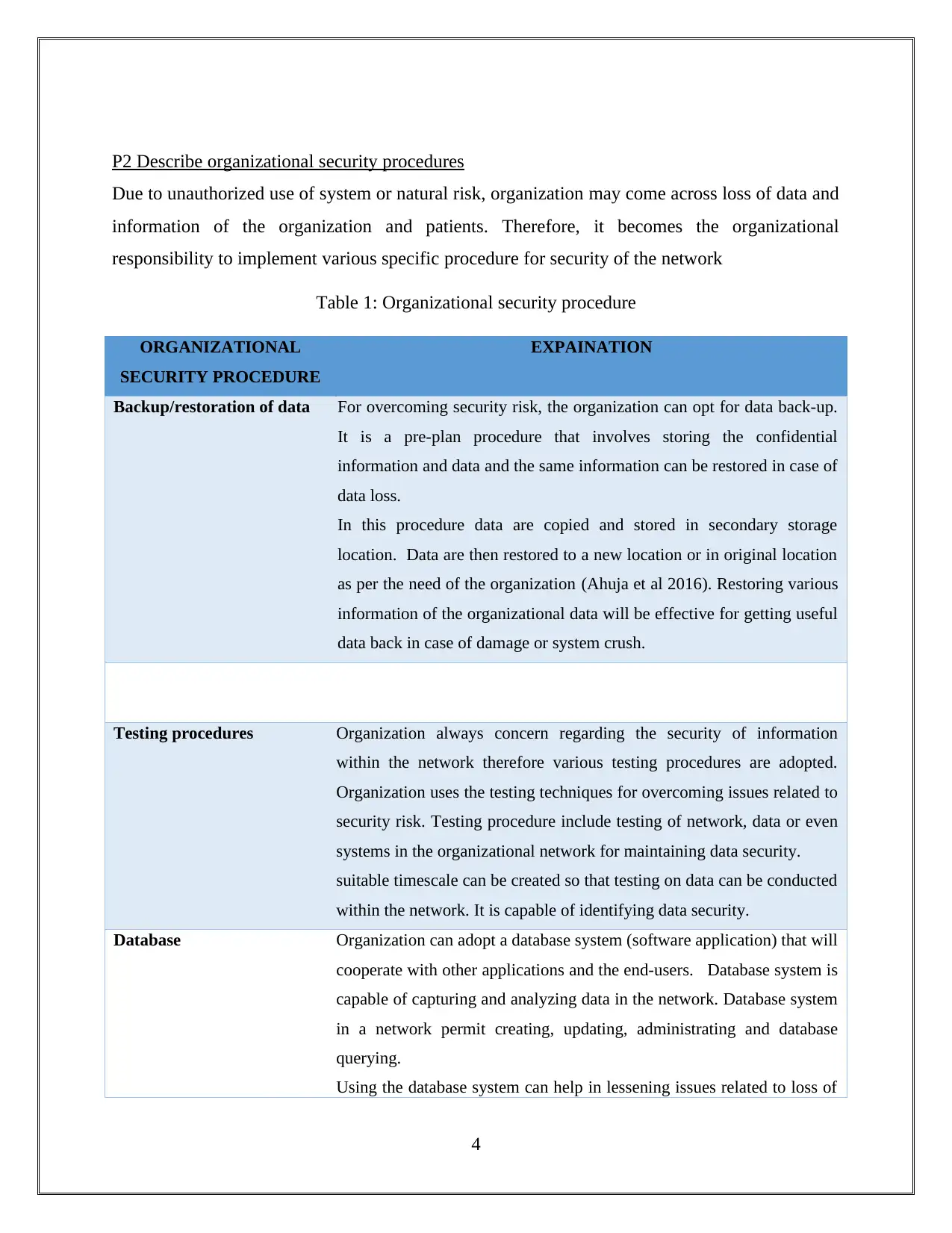
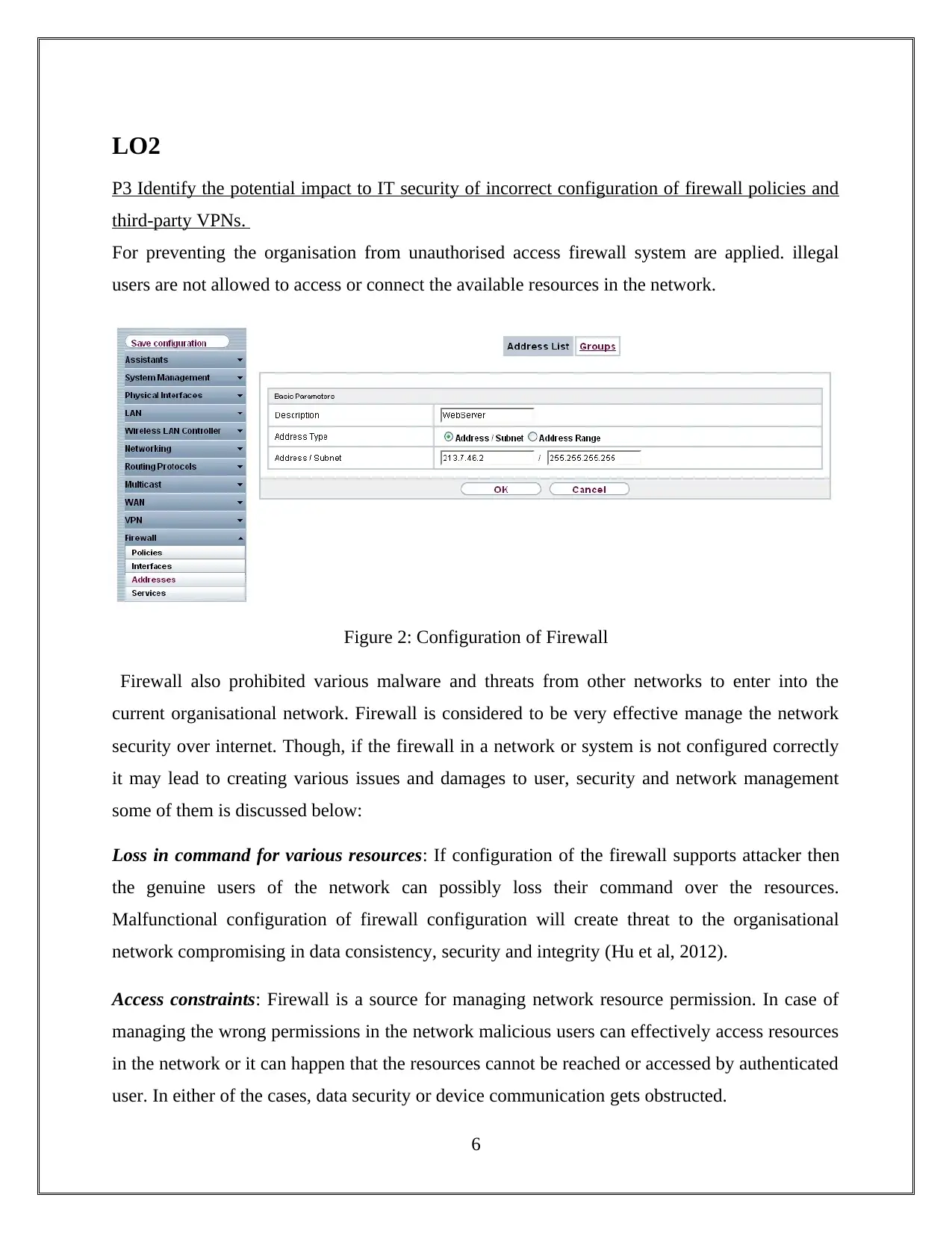
P2 Describe organizational security procedures
Due to unauthorized use of system or natural risk, organization may come across loss of data and
information of the organization and patients. Therefore, it becomes the organizational
responsibility to implement various specific procedure for security of the network
Table 1: Organizational security procedure
ORGANIZATIONAL
SECURITY PROCEDURE
EXPAINATION
Backup/restoration of data For overcoming security risk, the organization can opt for data back-up.
It is a pre-plan procedure that involves storing the confidential
information and data and the same information can be restored in case of
data loss.
In this procedure data are copied and stored in secondary storage
location. Data are then restored to a new location or in original location
as per the need of the organization (Ahuja et al 2016). Restoring various
information of the organizational data will be effective for getting useful
data back in case of damage or system crush.
Testing procedures Organization always concern regarding the security of information
within the network therefore various testing procedures are adopted.
Organization uses the testing techniques for overcoming issues related to
security risk. Testing procedure include testing of network, data or even
systems in the organizational network for maintaining data security.
suitable timescale can be created so that testing on data can be conducted
within the network. It is capable of identifying data security.
Database Organization can adopt a database system (software application) that will
cooperate with other applications and the end-users. Database system is
capable of capturing and analyzing data in the network. Database system
in a network permit creating, updating, administrating and database
querying.
Using the database system can help in lessening issues related to loss of
4
Due to unauthorized use of system or natural risk, organization may come across loss of data and
information of the organization and patients. Therefore, it becomes the organizational
responsibility to implement various specific procedure for security of the network
Table 1: Organizational security procedure
ORGANIZATIONAL
SECURITY PROCEDURE
EXPAINATION
Backup/restoration of data For overcoming security risk, the organization can opt for data back-up.
It is a pre-plan procedure that involves storing the confidential
information and data and the same information can be restored in case of
data loss.
In this procedure data are copied and stored in secondary storage
location. Data are then restored to a new location or in original location
as per the need of the organization (Ahuja et al 2016). Restoring various
information of the organizational data will be effective for getting useful
data back in case of damage or system crush.
Testing procedures Organization always concern regarding the security of information
within the network therefore various testing procedures are adopted.
Organization uses the testing techniques for overcoming issues related to
security risk. Testing procedure include testing of network, data or even
systems in the organizational network for maintaining data security.
suitable timescale can be created so that testing on data can be conducted
within the network. It is capable of identifying data security.
Database Organization can adopt a database system (software application) that will
cooperate with other applications and the end-users. Database system is
capable of capturing and analyzing data in the network. Database system
in a network permit creating, updating, administrating and database
querying.
Using the database system can help in lessening issues related to loss of
4
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
data. This application helps in controlling user for accessing the data and
securing data of the whole network from any kind of illegal users.
Audits The organization should follow and conduct audit for data security. In
case of audit, auditor deployed in the organization must checks
information or data types in the organizational network. By
understanding the information and the way they are access well-
structured flow document can be created. Data security audit effectively
helps organization to know about all the sensitive information within the
organization.
Auditing can help an organization for identifying the appropriate method
regarding the maintaining data security in the systems. Data theft can be
minimizing the as auditor can identify all the situations related to
security risk.
5
securing data of the whole network from any kind of illegal users.
Audits The organization should follow and conduct audit for data security. In
case of audit, auditor deployed in the organization must checks
information or data types in the organizational network. By
understanding the information and the way they are access well-
structured flow document can be created. Data security audit effectively
helps organization to know about all the sensitive information within the
organization.
Auditing can help an organization for identifying the appropriate method
regarding the maintaining data security in the systems. Data theft can be
minimizing the as auditor can identify all the situations related to
security risk.
5
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
LO2
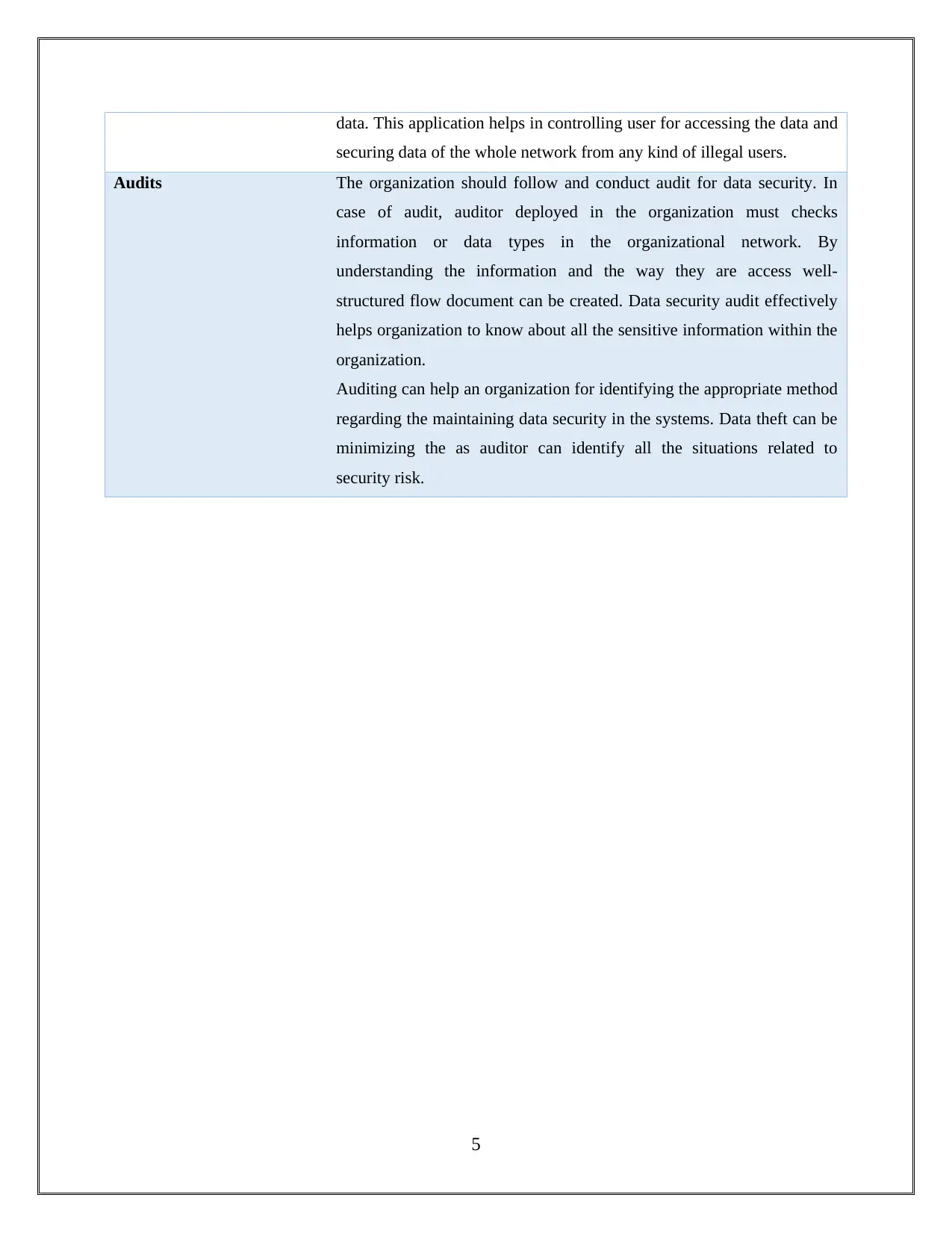
P3 Identify the potential impact to IT security of incorrect configuration of firewall policies and
third-party VPNs.
For preventing the organisation from unauthorised access firewall system are applied. illegal
users are not allowed to access or connect the available resources in the network.
Figure 2: Configuration of Firewall
Firewall also prohibited various malware and threats from other networks to enter into the
current organisational network. Firewall is considered to be very effective manage the network
security over internet. Though, if the firewall in a network or system is not configured correctly
it may lead to creating various issues and damages to user, security and network management
some of them is discussed below:
Loss in command for various resources: If configuration of the firewall supports attacker then
the genuine users of the network can possibly loss their command over the resources.
Malfunctional configuration of firewall configuration will create threat to the organisational
network compromising in data consistency, security and integrity (Hu et al, 2012).
Access constraints: Firewall is a source for managing network resource permission. In case of
managing the wrong permissions in the network malicious users can effectively access resources
in the network or it can happen that the resources cannot be reached or accessed by authenticated
user. In either of the cases, data security or device communication gets obstructed.
6
P3 Identify the potential impact to IT security of incorrect configuration of firewall policies and
third-party VPNs.
For preventing the organisation from unauthorised access firewall system are applied. illegal
users are not allowed to access or connect the available resources in the network.
Figure 2: Configuration of Firewall
Firewall also prohibited various malware and threats from other networks to enter into the
current organisational network. Firewall is considered to be very effective manage the network
security over internet. Though, if the firewall in a network or system is not configured correctly
it may lead to creating various issues and damages to user, security and network management
some of them is discussed below:
Loss in command for various resources: If configuration of the firewall supports attacker then
the genuine users of the network can possibly loss their command over the resources.
Malfunctional configuration of firewall configuration will create threat to the organisational
network compromising in data consistency, security and integrity (Hu et al, 2012).
Access constraints: Firewall is a source for managing network resource permission. In case of
managing the wrong permissions in the network malicious users can effectively access resources
in the network or it can happen that the resources cannot be reached or accessed by authenticated
user. In either of the cases, data security or device communication gets obstructed.
6

Improper connectivity: In case the user has blocked a service misguidedly and services of other
network cannot be use then it can impact the communication of the network. It may lead to
delivering of deprived connectivity between all the internal users and the private networks.
M2 Discuss three benefits to implement network monitoring systems with supporting reasons.
Network Monitoring system is considered to be a very important aspect of the network
management solution for an organization. It helps in keeping tracks of different network
component within the organization. implementation of the network monitoring system is very
beneficial to the organizational (Network monitoring, 2018).
1. Fixes issues faster: network monitoring tool in the network is capable of solving any
issues in minimum time with the help of a live networking map that find the issue (related
to traffic fluctuation, configuration errors etc.) and its place of origin.
2. Identifies security threats: network monitoring helps in securing the sensitive data of the
organization. it provides first level security any kind of malicious activities are spotted.
3. Manages the growing and changing network: IT environment is rapidly growing in term
of size due to the involvement of various technological innovations. With the growing
network complexities associated with it also rise. Network Monitoring system helps in
monitoring any kind of malicious activities and fluctuation. It also helps in monitoring IP
assets and maintains performance of the network.
7
network cannot be use then it can impact the communication of the network. It may lead to
delivering of deprived connectivity between all the internal users and the private networks.
M2 Discuss three benefits to implement network monitoring systems with supporting reasons.
Network Monitoring system is considered to be a very important aspect of the network
management solution for an organization. It helps in keeping tracks of different network
component within the organization. implementation of the network monitoring system is very
beneficial to the organizational (Network monitoring, 2018).
1. Fixes issues faster: network monitoring tool in the network is capable of solving any
issues in minimum time with the help of a live networking map that find the issue (related
to traffic fluctuation, configuration errors etc.) and its place of origin.
2. Identifies security threats: network monitoring helps in securing the sensitive data of the
organization. it provides first level security any kind of malicious activities are spotted.
3. Manages the growing and changing network: IT environment is rapidly growing in term
of size due to the involvement of various technological innovations. With the growing
network complexities associated with it also rise. Network Monitoring system helps in
monitoring any kind of malicious activities and fluctuation. It also helps in monitoring IP
assets and maintains performance of the network.
7
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 28
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2025 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.




