Securing IOT and Cyber-Physical Environment
Added on 2022-11-29
7 Pages1570 Words298 Views
Securing IOT
and Cyber-
Physical
Environment
and Cyber-
Physical
Environment
Securing IOT and Cyber physical assets
Contents
Chapter 1: Understanding Internet of Things.............................................................................2
Introduction.....................................................................................................................2
Growth and Evolution of IOT.........................................................................................2
System architecture for IOT............................................................................................2
Vulnerabilities associated with IOT................................................................................2
Need and Requirement of securing IOT.........................................................................2
Chapter 2: Understanding Cyber Physical Assets......................................................................2
Introduction.....................................................................................................................2
Why cyber physical attacks is an undetectable threat.....................................................2
Chapter 3: IOT and Cyber physical assets are digital twins......................................................2
Chapter 4: Need and Requirement of IOT security architecture................................................3
Chapter 5: Vulnerabilities associated with IOT and Cyber physical assets...............................3
Chapter 6: Use of Cryptography in designing protection solution............................................3
Chapter 7: Securing IOT and Cyber-physical assets environment............................................3
Chapter 8: Selection of Right cryptographic solution for securing IOT....................................3
Chapter 9: IOT security architecture..........................................................................................3
1
Contents
Chapter 1: Understanding Internet of Things.............................................................................2
Introduction.....................................................................................................................2
Growth and Evolution of IOT.........................................................................................2
System architecture for IOT............................................................................................2
Vulnerabilities associated with IOT................................................................................2
Need and Requirement of securing IOT.........................................................................2
Chapter 2: Understanding Cyber Physical Assets......................................................................2
Introduction.....................................................................................................................2
Why cyber physical attacks is an undetectable threat.....................................................2
Chapter 3: IOT and Cyber physical assets are digital twins......................................................2
Chapter 4: Need and Requirement of IOT security architecture................................................3
Chapter 5: Vulnerabilities associated with IOT and Cyber physical assets...............................3
Chapter 6: Use of Cryptography in designing protection solution............................................3
Chapter 7: Securing IOT and Cyber-physical assets environment............................................3
Chapter 8: Selection of Right cryptographic solution for securing IOT....................................3
Chapter 9: IOT security architecture..........................................................................................3
1
Securing IOT and Cyber physical assets
Chapter 1: Understanding Internet of Things
Chapter 1: Understanding Internet of Things
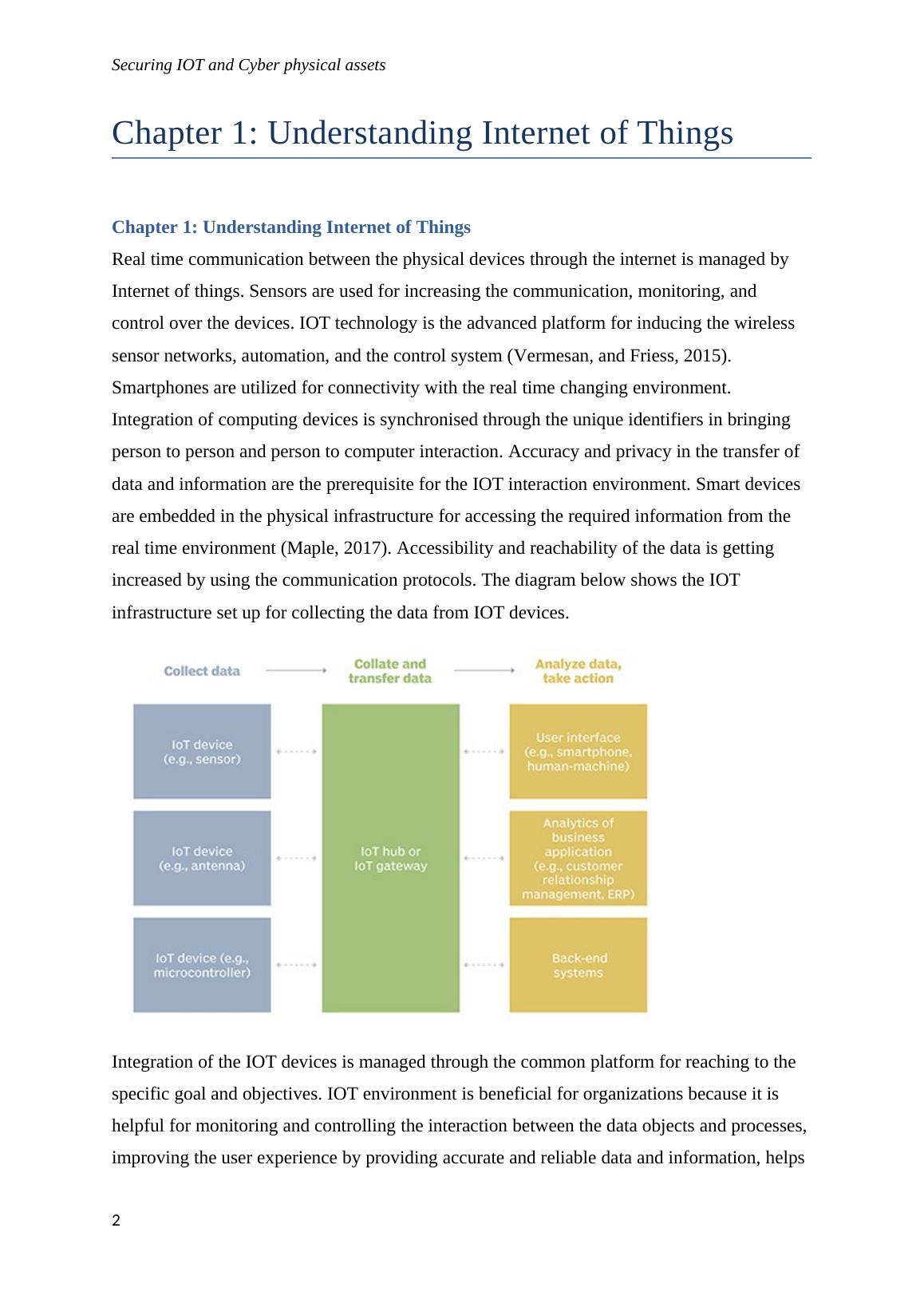
Real time communication between the physical devices through the internet is managed by
Internet of things. Sensors are used for increasing the communication, monitoring, and
control over the devices. IOT technology is the advanced platform for inducing the wireless
sensor networks, automation, and the control system (Vermesan, and Friess, 2015).
Smartphones are utilized for connectivity with the real time changing environment.
Integration of computing devices is synchronised through the unique identifiers in bringing
person to person and person to computer interaction. Accuracy and privacy in the transfer of
data and information are the prerequisite for the IOT interaction environment. Smart devices
are embedded in the physical infrastructure for accessing the required information from the
real time environment (Maple, 2017). Accessibility and reachability of the data is getting
increased by using the communication protocols. The diagram below shows the IOT
infrastructure set up for collecting the data from IOT devices.
Integration of the IOT devices is managed through the common platform for reaching to the
specific goal and objectives. IOT environment is beneficial for organizations because it is
helpful for monitoring and controlling the interaction between the data objects and processes,
improving the user experience by providing accurate and reliable data and information, helps
2
Chapter 1: Understanding Internet of Things
Chapter 1: Understanding Internet of Things
Real time communication between the physical devices through the internet is managed by
Internet of things. Sensors are used for increasing the communication, monitoring, and
control over the devices. IOT technology is the advanced platform for inducing the wireless
sensor networks, automation, and the control system (Vermesan, and Friess, 2015).
Smartphones are utilized for connectivity with the real time changing environment.
Integration of computing devices is synchronised through the unique identifiers in bringing
person to person and person to computer interaction. Accuracy and privacy in the transfer of
data and information are the prerequisite for the IOT interaction environment. Smart devices
are embedded in the physical infrastructure for accessing the required information from the
real time environment (Maple, 2017). Accessibility and reachability of the data is getting
increased by using the communication protocols. The diagram below shows the IOT
infrastructure set up for collecting the data from IOT devices.
Integration of the IOT devices is managed through the common platform for reaching to the
specific goal and objectives. IOT environment is beneficial for organizations because it is
helpful for monitoring and controlling the interaction between the data objects and processes,
improving the user experience by providing accurate and reliable data and information, helps
2
End of preview
Want to access all the pages? Upload your documents or become a member.
Related Documents
Internet of Things: Privacy Issues and Contentslg...
|9
|1402
|116
Lightweight Encryption Algorithm for Secure Communication in IoTlg...
|1
|1217
|307
IoT and Cyber Securitylg...
|15
|4234
|395
Lightweight Encryption Algorithm for Secure IOTlg...
|53
|14901
|228
The Internet of Thin Films: Research Limitation, Future Scope and Conclusionlg...
|42
|10071
|480
ITC595 Information Security - Research Projectlg...
|3
|3400
|25
