Analysis of Security Risks Affecting Information System Operations
VerifiedAdded on 2021/05/31
|11
|2707
|128
Report
AI Summary
This report provides a comprehensive analysis of security risks affecting information system operations, focusing on a case study of Leasing Information System Company. It begins by identifying common malware and threats, including worms and Trojan horses, and their impact on system integrity. The report then explores the vulnerabilities of networking devices like routers and firewalls, along with strategies for ensuring reliability and availability of web services. Email confidentiality and integrity are discussed, emphasizing the importance of strong passwords and monitoring. The study further delves into web mail and web server malware and security issues, addressing DoS attacks and spam. Approaches to improve email and web server availability, such as load balancing and system monitoring, are examined. Human and organizational factors, including human error and inadequate training, are recognized as significant contributors to IS security risks. The report highlights the use of logs and audit log reports for detecting and analyzing security breaches. Finally, the report recommends the use of network devices like firewalls, routers, and switches to mitigate email and web server threats, concluding with a call for a proactive approach to information system security.
Security and risks management
Name
Institution
Professor
Course
Date
Name
Institution
Professor
Course
Date
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
2. Introduction
Information systems are prone to attacks by malware that are normally sent by hackers
with aim of gaining access to the system. In this regard, Leasing Information System Company
has not been an exception and its operations have been hold at back by malware attackers. The
organization offers data analysis and technological advisory services to its customers. Since
organization supports many clients, it is important to focus on its system security parameters in
order to protect its operational data confidentiality. To make sure data security is met, all the four
data attributes (ACID) must be achieved at all cost (Spears & Barki, 2010). As leasing
information System Company offers its services to customers, it should be aware of
vulnerabilities that can affects its operations. The main goal of the paper is to analyze security
risks that affect information system operations. The objectives to be met are; making information
system available throughout as required by the customers and providing privacy of the data
stored by the company. Similarly, it will focus on achieving efficient and reliable authentication
and authorization to any organizational data. Finally, to facilitate effective data security
implementation as the company would be required to run security checkups to identify any
vulnerability.
3. Common malware and threads that affect information system
Some of the malware that have had effect on operations of the leasing information system
company are; worms which replicates when they are reactivated by the presence of desirable
conditions. The main files targeted by worms is operating system. It destroys files until the entire
disk is empty and the computer is not able to operate any more. The worst part of the attack from
worm affected organizational servers when an infected drive was connected to the system
through a dedicated terminal. After gaining access to the system, it spread through local area
Information systems are prone to attacks by malware that are normally sent by hackers
with aim of gaining access to the system. In this regard, Leasing Information System Company
has not been an exception and its operations have been hold at back by malware attackers. The
organization offers data analysis and technological advisory services to its customers. Since
organization supports many clients, it is important to focus on its system security parameters in
order to protect its operational data confidentiality. To make sure data security is met, all the four
data attributes (ACID) must be achieved at all cost (Spears & Barki, 2010). As leasing
information System Company offers its services to customers, it should be aware of
vulnerabilities that can affects its operations. The main goal of the paper is to analyze security
risks that affect information system operations. The objectives to be met are; making information
system available throughout as required by the customers and providing privacy of the data
stored by the company. Similarly, it will focus on achieving efficient and reliable authentication
and authorization to any organizational data. Finally, to facilitate effective data security
implementation as the company would be required to run security checkups to identify any
vulnerability.
3. Common malware and threads that affect information system
Some of the malware that have had effect on operations of the leasing information system
company are; worms which replicates when they are reactivated by the presence of desirable
conditions. The main files targeted by worms is operating system. It destroys files until the entire
disk is empty and the computer is not able to operate any more. The worst part of the attack from
worm affected organizational servers when an infected drive was connected to the system
through a dedicated terminal. After gaining access to the system, it spread through local area
network until it had access to the server which had weak ant-malware (Takabi, Joshi & Ahn,
2010). Important to note is that, there are some worms which can be termed to be friendly since
they traverse through the documents without harming them. Such worms are commonly known
to cause traffic on the system which in turn affect some processes such as data querying.
Similarly, leasing system have been fighting attacker from Trojan horses which mainly looks like
genuine applications which can be installed on PCs. Due to employees online activities and
download of some programs, Trojan horse infection has been a problem to the organization.
Though they have no impact on their own, they can allow other malicious software and attackers
in to the system (Peltier, 2010). Trojan are quite dangerous because some of them try to steal
confidential information from the systems.
4. Networking devices
In the organization, network is one of the most vulnerable tool used by hackers to access
organizational data. Network is supported by variety of devices such as; router which is used to
forward data packets from one network segment to another. Router can be set to operate like
intelligence hub by keeping record of both sending and receiving machine. It is mainly prone to
destruction when exposed to higher electricity voltage as well as temperatures. Next, routers are
vulnerable to errors when higher rate of data packet collision takes place or when there is wrong
cabling to router (Sequeira, 2013). Similarly, routers are usually abused when required security
parameters are not configured once set to provide networking services. The setting need to
follow very advanced security recommendations in order to protect them from being
compromised by hackers. The next device applicable in networking is firewall which is used to
screen all incoming and outgoing signals. Firewall is vulnerable to destruction when exposed to
high power voltage than recommended or humid weather conditions. Next, with poor
2010). Important to note is that, there are some worms which can be termed to be friendly since
they traverse through the documents without harming them. Such worms are commonly known
to cause traffic on the system which in turn affect some processes such as data querying.
Similarly, leasing system have been fighting attacker from Trojan horses which mainly looks like
genuine applications which can be installed on PCs. Due to employees online activities and
download of some programs, Trojan horse infection has been a problem to the organization.
Though they have no impact on their own, they can allow other malicious software and attackers
in to the system (Peltier, 2010). Trojan are quite dangerous because some of them try to steal
confidential information from the systems.
4. Networking devices
In the organization, network is one of the most vulnerable tool used by hackers to access
organizational data. Network is supported by variety of devices such as; router which is used to
forward data packets from one network segment to another. Router can be set to operate like
intelligence hub by keeping record of both sending and receiving machine. It is mainly prone to
destruction when exposed to higher electricity voltage as well as temperatures. Next, routers are
vulnerable to errors when higher rate of data packet collision takes place or when there is wrong
cabling to router (Sequeira, 2013). Similarly, routers are usually abused when required security
parameters are not configured once set to provide networking services. The setting need to
follow very advanced security recommendations in order to protect them from being
compromised by hackers. The next device applicable in networking is firewall which is used to
screen all incoming and outgoing signals. Firewall is vulnerable to destruction when exposed to
high power voltage than recommended or humid weather conditions. Next, with poor
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
configuration, it can be prone to errors such that it cannot differentiate either incoming or
outgoing signals. When poorly configured, it is still prone to abuse by either employees or
external entities (Tang & Musa, 2011). Finally, firewall can face quality problems if
recommended instructions are not followed as required when it being configured for use.
5. Reliability and availability of web services
The leasing information system company can use the following ways to make sure its
services are reliable and available to its customers. First, data replication in a distributed system
is very essential way of making sure system is reliable. When system is available for use when
needed, system reliability is automatically met (Ciccarelli, 2013). Secondly, preventing
organizational system attacker through unauthorized users from either within or outside the
organization eliminates Denial of Services (DoS). Without DoS, system would be always
available for use by the target customers whenever they need it. DoS can be used to prevent
system access or make it very slow by imposing undesirable traffic such that its important users
are unable to execute routine duties. Consequently, web services can be made reliable by making
sure in case of upgrade or updates that might render system working inefficient, its users being
customers or internal users are aware in order to schedule their web access services (Siponen &
Vance, 2010). Finally, organization can make its web services readily available by making sure
system is easy and simple to use. This makes it understandable to users such that no errors during
operations that might compromise the system.
6. Email confidentiality and integrity
These two factors are key when it comes to any online data services. Confidentiality
works to make email communication personal rather than public. Any organizational email
outgoing signals. When poorly configured, it is still prone to abuse by either employees or
external entities (Tang & Musa, 2011). Finally, firewall can face quality problems if
recommended instructions are not followed as required when it being configured for use.
5. Reliability and availability of web services
The leasing information system company can use the following ways to make sure its
services are reliable and available to its customers. First, data replication in a distributed system
is very essential way of making sure system is reliable. When system is available for use when
needed, system reliability is automatically met (Ciccarelli, 2013). Secondly, preventing
organizational system attacker through unauthorized users from either within or outside the
organization eliminates Denial of Services (DoS). Without DoS, system would be always
available for use by the target customers whenever they need it. DoS can be used to prevent
system access or make it very slow by imposing undesirable traffic such that its important users
are unable to execute routine duties. Consequently, web services can be made reliable by making
sure in case of upgrade or updates that might render system working inefficient, its users being
customers or internal users are aware in order to schedule their web access services (Siponen &
Vance, 2010). Finally, organization can make its web services readily available by making sure
system is easy and simple to use. This makes it understandable to users such that no errors during
operations that might compromise the system.
6. Email confidentiality and integrity
These two factors are key when it comes to any online data services. Confidentiality
works to make email communication personal rather than public. Any organizational email
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
communication should be made private and cannot be subject to external use. All email sent in to
the or outside the organization should conform to operational policies as outlined to make sure
privacy is achieved. To make sure there is privacy in email communication, all outgoing mails
from the company should be monitored to make sure privacy is given the highest priority
(Clemm & Wolter, 2013). On the same note, it is important to note internal privacy is also
required and where possible no exposure of data to unauthorized employees is permitted.
Similarly, integrity of email should be adhered to by making sure all email accounts have strong
passwords. If mail accounts are not well protected, they can be used by other people to send
unauthorized messages. Integrity can be achieved by securing mails with strong passwords as
well as avoiding setting mail accounts to be default. Emails setting should allow timeout after a
short period of time. Finally, email account passwords should be changed frequently to avoid
being monitored by other people.
7. Web mail and web server malware and security issues
The discussion of web mails and web server security would be done in the order of their
priority. Mails and web servers are prone to hacking with aim of retrieving organizational
communication. Both web mail and server can be used by hackers to get sensitive organizational
communication. Next, there is widespread DoS on web mails and servers once they are
compromised by unauthorized persons which result to data leaks (Dubois et al., 2010).
Additionally, spam mails are a common phenomenon in the organization. They are mainly used
to collect some information that can be used to gain access to organizational network.
Consequently, web mails and server are all prone to malware attacker because malware spreads
faster on networks. Finally, being ignorant to recommended security practices puts both web
mail and web server at risk.
the or outside the organization should conform to operational policies as outlined to make sure
privacy is achieved. To make sure there is privacy in email communication, all outgoing mails
from the company should be monitored to make sure privacy is given the highest priority
(Clemm & Wolter, 2013). On the same note, it is important to note internal privacy is also
required and where possible no exposure of data to unauthorized employees is permitted.
Similarly, integrity of email should be adhered to by making sure all email accounts have strong
passwords. If mail accounts are not well protected, they can be used by other people to send
unauthorized messages. Integrity can be achieved by securing mails with strong passwords as
well as avoiding setting mail accounts to be default. Emails setting should allow timeout after a
short period of time. Finally, email account passwords should be changed frequently to avoid
being monitored by other people.
7. Web mail and web server malware and security issues
The discussion of web mails and web server security would be done in the order of their
priority. Mails and web servers are prone to hacking with aim of retrieving organizational
communication. Both web mail and server can be used by hackers to get sensitive organizational
communication. Next, there is widespread DoS on web mails and servers once they are
compromised by unauthorized persons which result to data leaks (Dubois et al., 2010).
Additionally, spam mails are a common phenomenon in the organization. They are mainly used
to collect some information that can be used to gain access to organizational network.
Consequently, web mails and server are all prone to malware attacker because malware spreads
faster on networks. Finally, being ignorant to recommended security practices puts both web
mail and web server at risk.

8. Approaches to improve email and web servers availability
Availability of both mail and web server is very critical as it facilities organizational
communication. To make sure they are stable, it is important to make sure there is load balancing
on web servers. This is achieved by distributing all workloads on various servers (Siponen &
Vance, 2010). Failing of one server does not affect the performance of the system because
processing is picked by the other servers.
Figure 1: Load balancing- https://www.digitalocean.com/community/tutorials/5-ways-to-improve-your-production-
web-application-server-setup
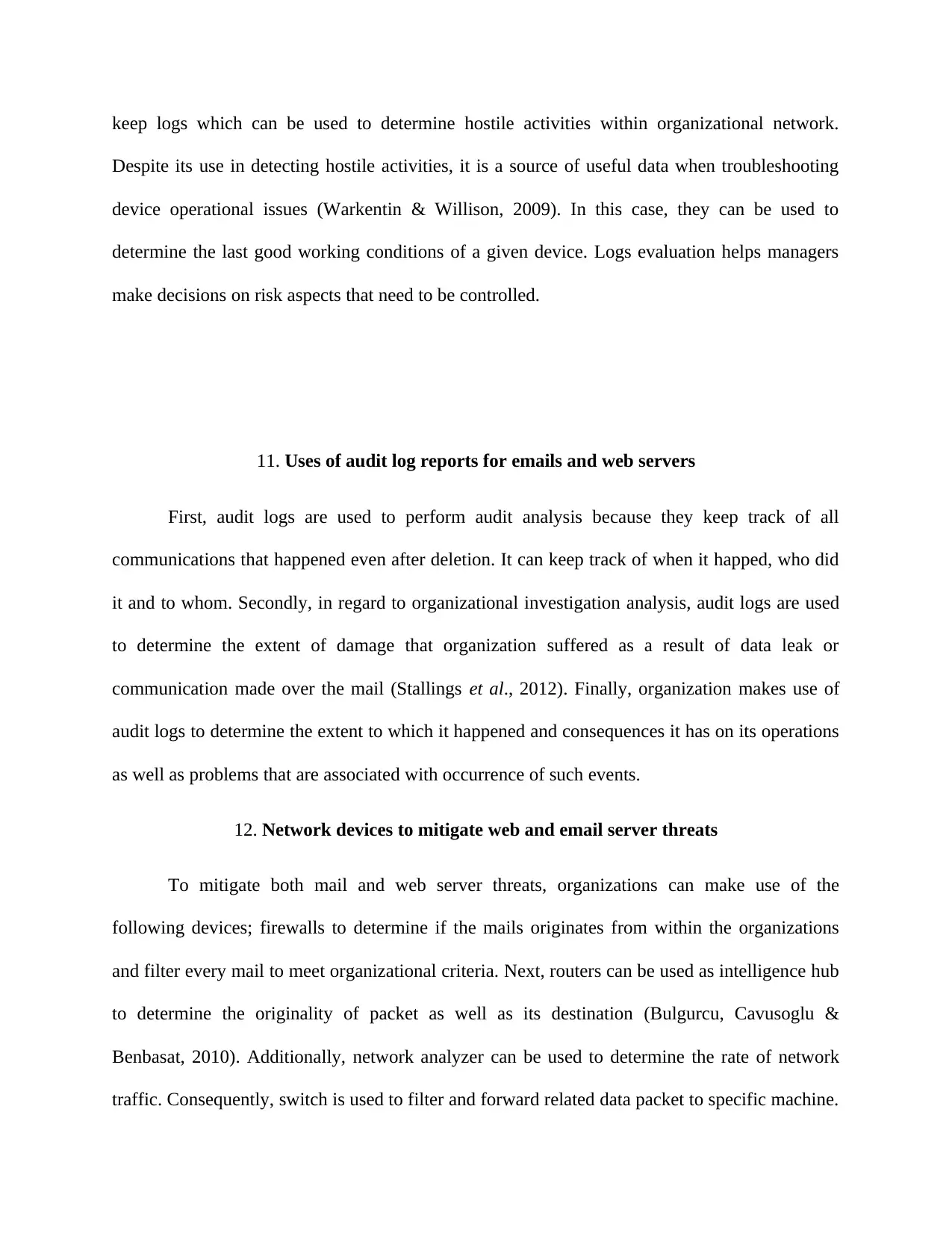
Similarly, monitoring of system performance can help to detect any malicious activities.
Normally, increase in traffic results to reduced system access capability and this minimizes
system availability (Siponen & Vance, 2010). When monitoring is done, it is easy to control
some activities as they occur such that availability is improved.
Availability of both mail and web server is very critical as it facilities organizational
communication. To make sure they are stable, it is important to make sure there is load balancing
on web servers. This is achieved by distributing all workloads on various servers (Siponen &
Vance, 2010). Failing of one server does not affect the performance of the system because
processing is picked by the other servers.
Figure 1: Load balancing- https://www.digitalocean.com/community/tutorials/5-ways-to-improve-your-production-
web-application-server-setup
Similarly, monitoring of system performance can help to detect any malicious activities.
Normally, increase in traffic results to reduced system access capability and this minimizes
system availability (Siponen & Vance, 2010). When monitoring is done, it is easy to control
some activities as they occur such that availability is improved.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
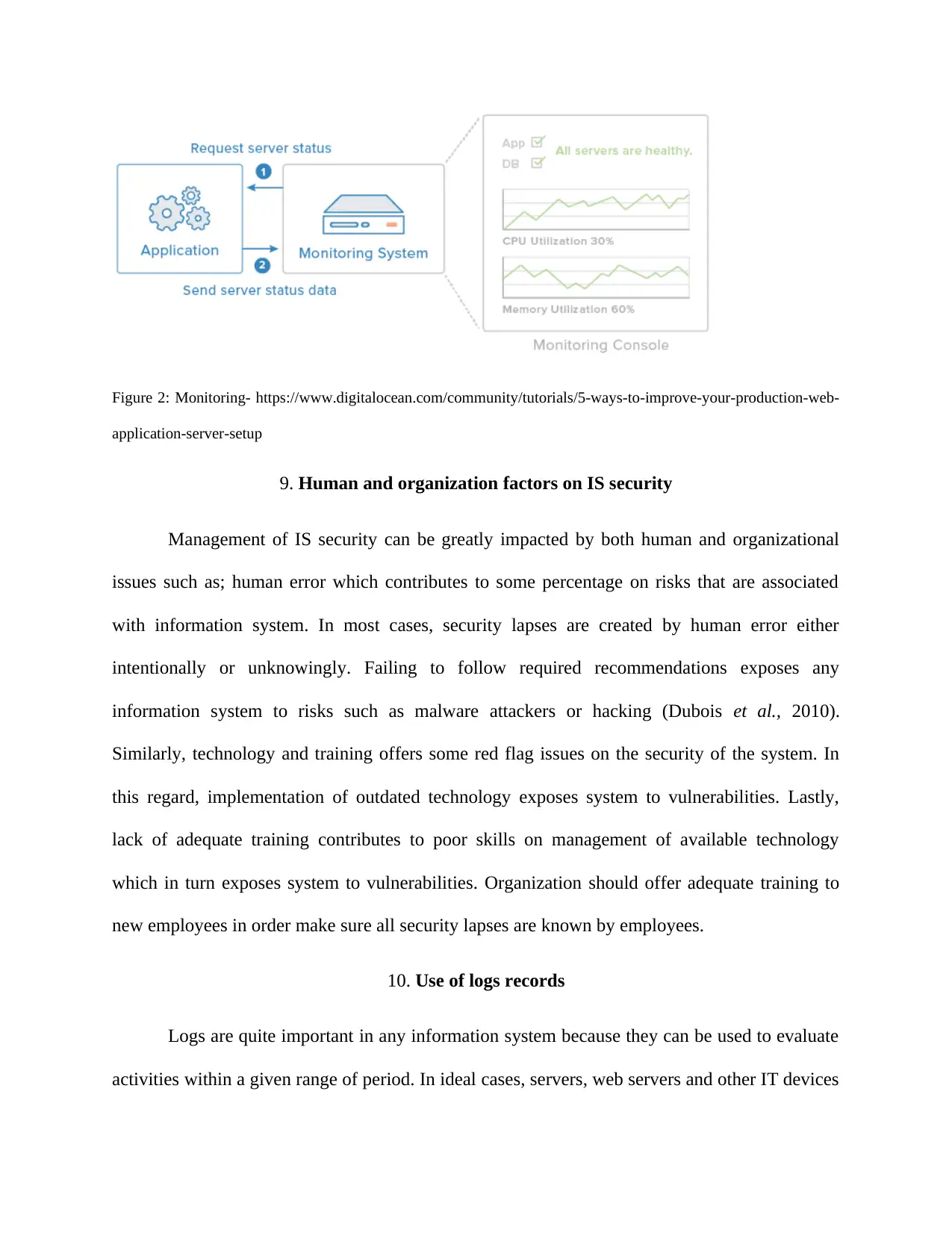
Figure 2: Monitoring- https://www.digitalocean.com/community/tutorials/5-ways-to-improve-your-production-web-
application-server-setup
9. Human and organization factors on IS security
Management of IS security can be greatly impacted by both human and organizational
issues such as; human error which contributes to some percentage on risks that are associated
with information system. In most cases, security lapses are created by human error either
intentionally or unknowingly. Failing to follow required recommendations exposes any
information system to risks such as malware attackers or hacking (Dubois et al., 2010).
Similarly, technology and training offers some red flag issues on the security of the system. In
this regard, implementation of outdated technology exposes system to vulnerabilities. Lastly,
lack of adequate training contributes to poor skills on management of available technology
which in turn exposes system to vulnerabilities. Organization should offer adequate training to
new employees in order make sure all security lapses are known by employees.
10. Use of logs records
Logs are quite important in any information system because they can be used to evaluate
activities within a given range of period. In ideal cases, servers, web servers and other IT devices
application-server-setup
9. Human and organization factors on IS security
Management of IS security can be greatly impacted by both human and organizational
issues such as; human error which contributes to some percentage on risks that are associated
with information system. In most cases, security lapses are created by human error either
intentionally or unknowingly. Failing to follow required recommendations exposes any
information system to risks such as malware attackers or hacking (Dubois et al., 2010).
Similarly, technology and training offers some red flag issues on the security of the system. In
this regard, implementation of outdated technology exposes system to vulnerabilities. Lastly,
lack of adequate training contributes to poor skills on management of available technology
which in turn exposes system to vulnerabilities. Organization should offer adequate training to
new employees in order make sure all security lapses are known by employees.
10. Use of logs records
Logs are quite important in any information system because they can be used to evaluate
activities within a given range of period. In ideal cases, servers, web servers and other IT devices
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
keep logs which can be used to determine hostile activities within organizational network.
Despite its use in detecting hostile activities, it is a source of useful data when troubleshooting
device operational issues (Warkentin & Willison, 2009). In this case, they can be used to
determine the last good working conditions of a given device. Logs evaluation helps managers
make decisions on risk aspects that need to be controlled.
11. Uses of audit log reports for emails and web servers
First, audit logs are used to perform audit analysis because they keep track of all
communications that happened even after deletion. It can keep track of when it happed, who did
it and to whom. Secondly, in regard to organizational investigation analysis, audit logs are used
to determine the extent of damage that organization suffered as a result of data leak or
communication made over the mail (Stallings et al., 2012). Finally, organization makes use of
audit logs to determine the extent to which it happened and consequences it has on its operations
as well as problems that are associated with occurrence of such events.
12. Network devices to mitigate web and email server threats
To mitigate both mail and web server threats, organizations can make use of the
following devices; firewalls to determine if the mails originates from within the organizations
and filter every mail to meet organizational criteria. Next, routers can be used as intelligence hub
to determine the originality of packet as well as its destination (Bulgurcu, Cavusoglu &
Benbasat, 2010). Additionally, network analyzer can be used to determine the rate of network
traffic. Consequently, switch is used to filter and forward related data packet to specific machine.
Despite its use in detecting hostile activities, it is a source of useful data when troubleshooting
device operational issues (Warkentin & Willison, 2009). In this case, they can be used to
determine the last good working conditions of a given device. Logs evaluation helps managers
make decisions on risk aspects that need to be controlled.
11. Uses of audit log reports for emails and web servers
First, audit logs are used to perform audit analysis because they keep track of all
communications that happened even after deletion. It can keep track of when it happed, who did
it and to whom. Secondly, in regard to organizational investigation analysis, audit logs are used
to determine the extent of damage that organization suffered as a result of data leak or
communication made over the mail (Stallings et al., 2012). Finally, organization makes use of
audit logs to determine the extent to which it happened and consequences it has on its operations
as well as problems that are associated with occurrence of such events.
12. Network devices to mitigate web and email server threats
To mitigate both mail and web server threats, organizations can make use of the
following devices; firewalls to determine if the mails originates from within the organizations
and filter every mail to meet organizational criteria. Next, routers can be used as intelligence hub
to determine the originality of packet as well as its destination (Bulgurcu, Cavusoglu &
Benbasat, 2010). Additionally, network analyzer can be used to determine the rate of network
traffic. Consequently, switch is used to filter and forward related data packet to specific machine.
If its origin is not identifiable, the packet is not routed. Finally, Modem provides network
capability to a specific machine which is not discoverable to other people. In this case, when
used in web servers it cannot be detected by the other machines.
13. Conclusion and recommendations
It is important to recognize the security issues that are associated with information
system. Generally, systems are prone to hacking, malware and catastrophic effects. Similarly,
human and organizational factors contribute greatly to information system risks due to human
errors and negligence. Organizational factors such as inadequate employees training and failure
to either upgrade or update information systems to match with current technology also contribute
to system risks. Despite these notable challenges, some networking devices such as; routers,
firewalls and switches can be used to mitigate mail and web server communication risks. To
solve organizational issues, audit logs server can be used as a tool to evaluate the source of the
problem as well as determine the extent of damage from an occurrence of some events. Having
analyzed various security and risks related to information systems, I would focus on advising
organizational management to align organizations operations to proposed security measures in
order to benefit maximally from implementation of information system. Finally, it would be
advisable for all information system security officers to make use of log data and make sure they
are turned on at all times.
capability to a specific machine which is not discoverable to other people. In this case, when
used in web servers it cannot be detected by the other machines.
13. Conclusion and recommendations
It is important to recognize the security issues that are associated with information
system. Generally, systems are prone to hacking, malware and catastrophic effects. Similarly,
human and organizational factors contribute greatly to information system risks due to human
errors and negligence. Organizational factors such as inadequate employees training and failure
to either upgrade or update information systems to match with current technology also contribute
to system risks. Despite these notable challenges, some networking devices such as; routers,
firewalls and switches can be used to mitigate mail and web server communication risks. To
solve organizational issues, audit logs server can be used as a tool to evaluate the source of the
problem as well as determine the extent of damage from an occurrence of some events. Having
analyzed various security and risks related to information systems, I would focus on advising
organizational management to align organizations operations to proposed security measures in
order to benefit maximally from implementation of information system. Finally, it would be
advisable for all information system security officers to make use of log data and make sure they
are turned on at all times.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
References
Bulgurcu, B., Cavusoglu, H., & Benbasat, I. (2010). Information security policy compliance: an
empirical study of rationality-based beliefs and information security awareness. MIS
quarterly, 34(3), 523-548.
Ciccarelli, P. (2013). Networking basics. New York: Wiley.
Clemm, A., & Wolter, R. (2013). Network-embedded management and applications:
Understanding programmable networking infrastructure. New York, NY: Springer.
Dubois, E., Heymans, P., Mayer, N., & Matulevicius, R. (2010). A systematic approach to define
the domain of information system security risk management. In Intentional Perspectives
on Information Systems Engineering (pp. 289-306). Springer, Berlin, Heidelberg.
Peltier, T. R. (2010). Information security risk analysis. Auerbach publications.
Sequeira, A. (2013). Interconnecting Cisco network devices. Indianapolis, Ind: Cisco Press.
Siponen, M., & Vance, A. (2010). Neutralization: new insights into the problem of employee
information systems security policy violations. MIS quarterly, 487-502.
Spears, J. L., & Barki, H. (2010). User participation in information systems security risk
management. MIS quarterly, 503-522.
Stallings, W., Brown, L., Bauer, M. D., & Bhattacharjee, A. K. (2012). Computer security:
principles and practice (pp. 978-0). Pearson Education.
Takabi, H., Joshi, J. B., & Ahn, G. J. (2010). Security and privacy challenges in cloud
computing environments. IEEE Security & Privacy, 8(6), 24-31.
Bulgurcu, B., Cavusoglu, H., & Benbasat, I. (2010). Information security policy compliance: an
empirical study of rationality-based beliefs and information security awareness. MIS
quarterly, 34(3), 523-548.
Ciccarelli, P. (2013). Networking basics. New York: Wiley.
Clemm, A., & Wolter, R. (2013). Network-embedded management and applications:
Understanding programmable networking infrastructure. New York, NY: Springer.
Dubois, E., Heymans, P., Mayer, N., & Matulevicius, R. (2010). A systematic approach to define
the domain of information system security risk management. In Intentional Perspectives
on Information Systems Engineering (pp. 289-306). Springer, Berlin, Heidelberg.
Peltier, T. R. (2010). Information security risk analysis. Auerbach publications.
Sequeira, A. (2013). Interconnecting Cisco network devices. Indianapolis, Ind: Cisco Press.
Siponen, M., & Vance, A. (2010). Neutralization: new insights into the problem of employee
information systems security policy violations. MIS quarterly, 487-502.
Spears, J. L., & Barki, H. (2010). User participation in information systems security risk
management. MIS quarterly, 503-522.
Stallings, W., Brown, L., Bauer, M. D., & Bhattacharjee, A. K. (2012). Computer security:
principles and practice (pp. 978-0). Pearson Education.
Takabi, H., Joshi, J. B., & Ahn, G. J. (2010). Security and privacy challenges in cloud
computing environments. IEEE Security & Privacy, 8(6), 24-31.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

Tang, O., & Musa, S. N. (2011). Identifying risk issues and research advancements in supply
chain risk management. International journal of production economics, 133(1), 25-34.
Warkentin, M., & Willison, R. (2009). Behavioral and policy issues in information systems
security: the insider threat. European Journal of Information Systems, 18(2), 101-105.
chain risk management. International journal of production economics, 133(1), 25-34.
Warkentin, M., & Willison, R. (2009). Behavioral and policy issues in information systems
security: the insider threat. European Journal of Information Systems, 18(2), 101-105.
1 out of 11
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





