Security Risk Analysis and Management: A Comprehensive Guide
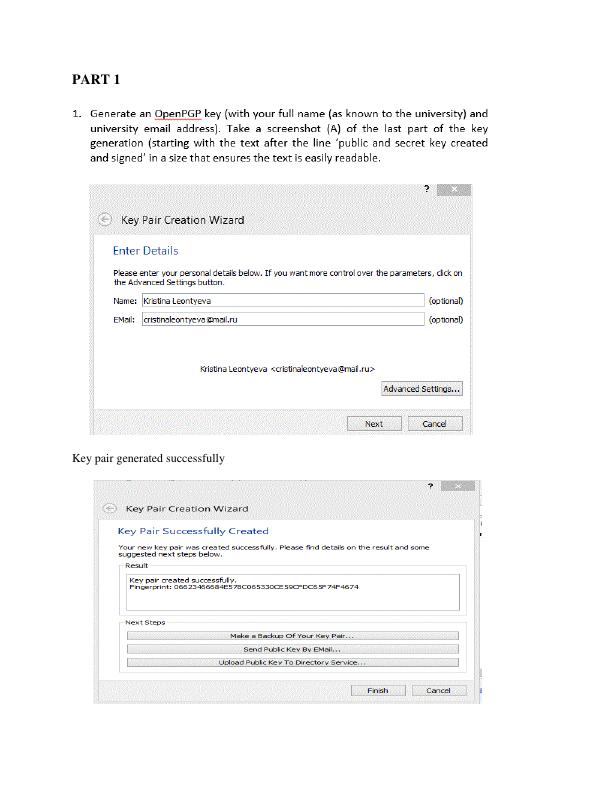
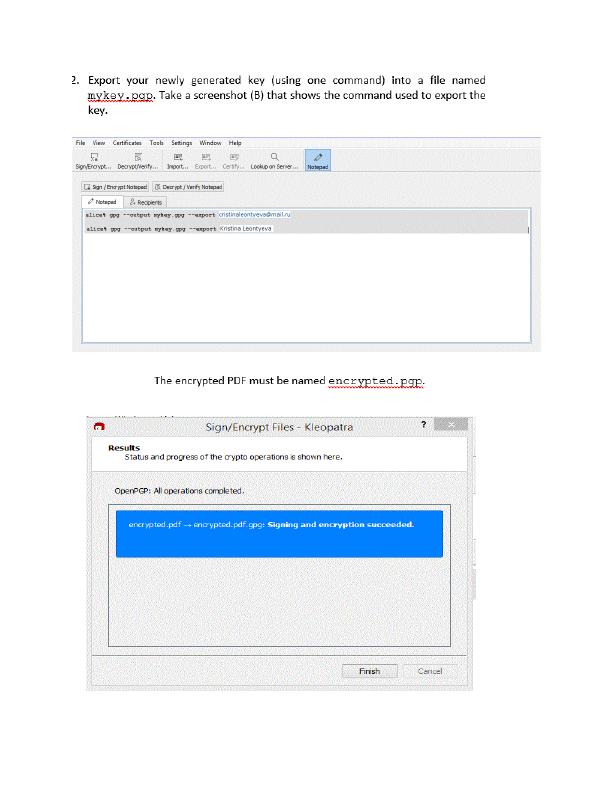
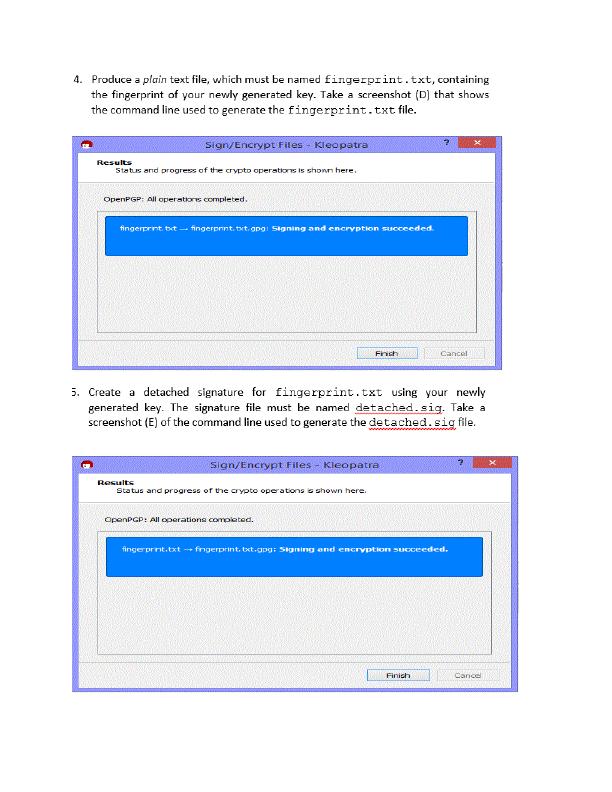
Use of GnuPG to achieve results for a series of tasks and design of a simple security-related application.
20 Pages2542 Words272 Views
Added on 2023-06-12
About This Document
This article provides a comprehensive guide on security risk analysis and management. It covers the terminology, risk analysis process, risk control strategies, and specific requirements. It also discusses the impact of threat occurrence, vulnerability assessment, and benchmarking. Additionally, it sheds light on ethical and social issues of security in information technology. The article is a valuable resource for anyone interested in understanding security risk analysis and management.
Security Risk Analysis and Management: A Comprehensive Guide
Use of GnuPG to achieve results for a series of tasks and design of a simple security-related application.
Added on 2023-06-12
ShareRelated Documents
End of preview
Want to access all the pages? Upload your documents or become a member.
Network Security Assessment: Part 1 - Vulnerabilities Assessment
|9
|1577
|381
Network Security Assessment: Part 1 - Vulnerabilities Assessment
|9
|1749
|483
Network Security & Its Vulnerabilities | Document
|9
|1749
|130
Investigation into Cyber Security
|13
|3064
|80
Assignment on Cyber Security 2022
|7
|712
|26
Cyber Security Applied Research 2022
|8
|2211
|24