Smart Cards: RFID, Security, and Implementation
VerifiedAdded on 2023/06/15
|38
|8487
|390
AI Summary
This study material covers topics such as RFID, security, and implementation of smart cards. It includes questions and answers related to passive and active RFIDs, symmetric and asymmetric algorithms, and TPM. The material also discusses the implementation of ID card systems and new developments in contactless payment cards.
Contribute Materials
Your contribution can guide someone’s learning journey. Share your
documents today.

Running head: SMART CARDS
Smart Cards
[Name of the Student]
[Name of the University]
[Author note]
Smart Cards
[Name of the Student]
[Name of the University]
[Author note]
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
1SMART CARDS
Table of Contents
2013.................................................................................................................................................2
2014.................................................................................................................................................8
2015...............................................................................................................................................15
2016...............................................................................................................................................18
2017...............................................................................................................................................25
Table of Contents
2013.................................................................................................................................................2
2014.................................................................................................................................................8
2015...............................................................................................................................................15
2016...............................................................................................................................................18
2017...............................................................................................................................................25
2SMART CARDS
2013
Question 1
(a)(i)What is the literal definition of an RFID and does it imply any security protection
capabilities?
Ans: RFID or Radio Frequency Identification generally refers to the automated technology for
identification by making use of the radio frequency electromagnetic fields. The objects can be
identified by making use of tags when the tags comes closer to a reader. There are three parts in a
RFID and this includes one scanning antenna, a transceiver, and a transponder. RFID implies
various types of protection capabilities as well. Some of this includes tracking of the goods
inside a large store, tracking of animals in a farm and many more.
(a)(ii)Explain the main difference between an ID card based on a secured memory chip and
one based on an unsecured memory chip, and how this would affect the resistance to card
cloning.
Ans: ID Cards on secured memory chips provides higher security including electrically erasable
programmable read-only-memory unlike the unsecured ones. Card cloning gets resistance
through comprehensive data protection and mutual authentication between host and device.
(a)(iii)The data held in a printed 2-D bar-code could be encrypted and/or have a Message
Authentication Code (MAC). What would be the point of these measures when a bar-code
is easily read and copied?
Ans: The main reason for using of 2-D barcode despite of being easily read and copied is
because of it is having a strong focus on the consumers and are free to use. Along with this type
of barcodes are flexible in size and have a high fault tolerance. This codes have high readability
2013
Question 1
(a)(i)What is the literal definition of an RFID and does it imply any security protection
capabilities?
Ans: RFID or Radio Frequency Identification generally refers to the automated technology for
identification by making use of the radio frequency electromagnetic fields. The objects can be
identified by making use of tags when the tags comes closer to a reader. There are three parts in a
RFID and this includes one scanning antenna, a transceiver, and a transponder. RFID implies
various types of protection capabilities as well. Some of this includes tracking of the goods
inside a large store, tracking of animals in a farm and many more.
(a)(ii)Explain the main difference between an ID card based on a secured memory chip and
one based on an unsecured memory chip, and how this would affect the resistance to card
cloning.
Ans: ID Cards on secured memory chips provides higher security including electrically erasable
programmable read-only-memory unlike the unsecured ones. Card cloning gets resistance
through comprehensive data protection and mutual authentication between host and device.
(a)(iii)The data held in a printed 2-D bar-code could be encrypted and/or have a Message
Authentication Code (MAC). What would be the point of these measures when a bar-code
is easily read and copied?
Ans: The main reason for using of 2-D barcode despite of being easily read and copied is
because of it is having a strong focus on the consumers and are free to use. Along with this type
of barcodes are flexible in size and have a high fault tolerance. This codes have high readability
3SMART CARDS
and supports different types of data. This type of barcodes remain legible even when they are
printed at a small size or etched into a product.
(b)(i) Describe the levels, and the equipment required to complete verification.
Ans: The various levels are the hardware and software levels. In the former level, inputs are
synthesized to generate a transistor constituting a chip. Software-level represent view of the card
on which programmer has written the software.
The first equipment needed is the bit-true model where computed results are compared according
to every bit that produces the hardware, The next tool is the cycle-accurate model where outcome
or change in output signals are generated exactly with the similar speed of hardware.
(b)(ii) For each verification level, describe two anti-counterfeit measures.
Ans: For hardware-level with various high-level description languages bear structural similarity
with hardware. Thus as a result it is slow and complex. In case of software-model, software
developers at many cases are unaware of the details dealing with pipeline. Thus this execution of
instruction result a change for stable architectural state to new one. Thus as an anti-counterfeit
measure parallel execution whose execution includes various cycles are involved.
(c) Implementation of ID card system
(i) Ans: For this Supplier A must be chosen using Banker’s Algorithm. This is because it is a
deadlock avoidance and resource allocation algorithm. It is helpful to check whether allocation
of any resource might result in deadlock or not. It also analyzes whether it is safe to allocate
resource to process and then it is allocated to that process. Finding a safe sequence ensures that
the system would not move to a deadlock. The data structures used are need matrix, allocation
matrix, max matrix and available vector.
and supports different types of data. This type of barcodes remain legible even when they are
printed at a small size or etched into a product.
(b)(i) Describe the levels, and the equipment required to complete verification.
Ans: The various levels are the hardware and software levels. In the former level, inputs are
synthesized to generate a transistor constituting a chip. Software-level represent view of the card
on which programmer has written the software.
The first equipment needed is the bit-true model where computed results are compared according
to every bit that produces the hardware, The next tool is the cycle-accurate model where outcome
or change in output signals are generated exactly with the similar speed of hardware.
(b)(ii) For each verification level, describe two anti-counterfeit measures.
Ans: For hardware-level with various high-level description languages bear structural similarity
with hardware. Thus as a result it is slow and complex. In case of software-model, software
developers at many cases are unaware of the details dealing with pipeline. Thus this execution of
instruction result a change for stable architectural state to new one. Thus as an anti-counterfeit
measure parallel execution whose execution includes various cycles are involved.
(c) Implementation of ID card system
(i) Ans: For this Supplier A must be chosen using Banker’s Algorithm. This is because it is a
deadlock avoidance and resource allocation algorithm. It is helpful to check whether allocation
of any resource might result in deadlock or not. It also analyzes whether it is safe to allocate
resource to process and then it is allocated to that process. Finding a safe sequence ensures that
the system would not move to a deadlock. The data structures used are need matrix, allocation
matrix, max matrix and available vector.
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
4SMART CARDS
(ii) Ans: PKI includes various set of roles, procedures and policies required to revoke, store, use,
distribute, manage and create digital certificates and control public-key encryption. Static data on
is proposed by the second consultant because here information never change after it gets
recorded. It comprises of a fixed data set. Unlike dynamic data, here data gets changed after it
gets recorded and needs to be updated continually.
The first one is more accurate advice since here user provides anyone with public key and
sender utilizes that to encrypt data. Next the owner uses through private key for decrypting that
data.
(ii) Ans: PKI includes various set of roles, procedures and policies required to revoke, store, use,
distribute, manage and create digital certificates and control public-key encryption. Static data on
is proposed by the second consultant because here information never change after it gets
recorded. It comprises of a fixed data set. Unlike dynamic data, here data gets changed after it
gets recorded and needs to be updated continually.
The first one is more accurate advice since here user provides anyone with public key and
sender utilizes that to encrypt data. Next the owner uses through private key for decrypting that
data.
5SMART CARDS
Question 2
(a)(i) Suggest one operational and one security benefit from using magnetic stripe cards
instead of simple paper tickets.
Ans: Magnetic strip cards are much more reliable and has been tested thoroughly over years. It
has a much more longevity than simple paper tickets. Magnetic strips are also responsible for
holding data. The data that are stored in the magnetic strip cards are not in the readable form
which initially provides an added security to the user.
(a)(ii) A chip card ticket could be based on a secure memory card or a secure
microprocessor card. Which do you think is the most likely considering cost and
performance issues?
Ans:
The first one is to be considered though it is cost expensive. However its performance is better
and more rugged than secure microprocessor card. It consists of high-capacity memory and
different portable devices.
(a)(iii) Explain why symmetric algorithms are more likely to be used than asymmetric
algorithms in existing smart ticket to reader protocols.
Ans: The primary disadvantage of symmetric algorithm is that every involved parties need to
exchange the key utilized to encrypt data prior they are decrypted. This perquisite to distribute
securely and control huge number of keys indicates most cryptographic services using other
kinds of encryption algorithms.
(b)(i) Compare these two options, giving an advantage and disadvantage for each, and
suggest which solution is most likely in practice.
Question 2
(a)(i) Suggest one operational and one security benefit from using magnetic stripe cards
instead of simple paper tickets.
Ans: Magnetic strip cards are much more reliable and has been tested thoroughly over years. It
has a much more longevity than simple paper tickets. Magnetic strips are also responsible for
holding data. The data that are stored in the magnetic strip cards are not in the readable form
which initially provides an added security to the user.
(a)(ii) A chip card ticket could be based on a secure memory card or a secure
microprocessor card. Which do you think is the most likely considering cost and
performance issues?
Ans:
The first one is to be considered though it is cost expensive. However its performance is better
and more rugged than secure microprocessor card. It consists of high-capacity memory and
different portable devices.
(a)(iii) Explain why symmetric algorithms are more likely to be used than asymmetric
algorithms in existing smart ticket to reader protocols.
Ans: The primary disadvantage of symmetric algorithm is that every involved parties need to
exchange the key utilized to encrypt data prior they are decrypted. This perquisite to distribute
securely and control huge number of keys indicates most cryptographic services using other
kinds of encryption algorithms.
(b)(i) Compare these two options, giving an advantage and disadvantage for each, and
suggest which solution is most likely in practice.
6SMART CARDS
Ans: Symmetric encryption utilizes single key unit requiring to get shared among people who
require getting message. Asymmetric algorithm on the other hand utilizes pair of private and
public key for encrypting and decrypting messages while making communication. Symmetric
encryption is a conventional technique whereas the asymmetric one is latest. Asymmetric
complements inherent problem of the requirement for sharing key in symmetric model. It
eliminates necessity to share keys through private and public keys. The symmetric one is more
suitable here because of the above reasons. Further it takes more time than symmetric
encryption.
(b)(ii) What is card key diversification and why is it important? Suggest a simple way of
creating diversified card keys from a master key.
Ans: Key diversification denotes to the process to derive keys from base key using unique
inputs. Every card gets distinct values for every key and as one key gets broken the vulnerability
is limited to that key instead of affecting the while system.
(b)(iii) Explain if you think it likely that the transport system readers will store the
diversified keys for all issued cards, or use some other mechanism.
Ans: Key diversification is generally utilized to work with smart cards. It is helpful to secure
interactions with population of cards.
(c) New developments.
(c)(i) Ans: Modern contactless payment card make system key management simpler through
various ways. First of all it is simple and quick to use along with reliable operation. It avoids
long queues and accesses every major debit and credit cards.
Ans: Symmetric encryption utilizes single key unit requiring to get shared among people who
require getting message. Asymmetric algorithm on the other hand utilizes pair of private and
public key for encrypting and decrypting messages while making communication. Symmetric
encryption is a conventional technique whereas the asymmetric one is latest. Asymmetric
complements inherent problem of the requirement for sharing key in symmetric model. It
eliminates necessity to share keys through private and public keys. The symmetric one is more
suitable here because of the above reasons. Further it takes more time than symmetric
encryption.
(b)(ii) What is card key diversification and why is it important? Suggest a simple way of
creating diversified card keys from a master key.
Ans: Key diversification denotes to the process to derive keys from base key using unique
inputs. Every card gets distinct values for every key and as one key gets broken the vulnerability
is limited to that key instead of affecting the while system.
(b)(iii) Explain if you think it likely that the transport system readers will store the
diversified keys for all issued cards, or use some other mechanism.
Ans: Key diversification is generally utilized to work with smart cards. It is helpful to secure
interactions with population of cards.
(c) New developments.
(c)(i) Ans: Modern contactless payment card make system key management simpler through
various ways. First of all it is simple and quick to use along with reliable operation. It avoids
long queues and accesses every major debit and credit cards.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

7SMART CARDS
8SMART CARDS
(c)(ii) How would the fare then be calculated and paid, and is there any change in the
certainty of receiving payment?
Ans: Fares can be calculated and then paid for customers through using near field
communication of NFC or RFID technology. Here the allowable quantity for contactless
transaction has been varying from country and bank. Yes, there is a certainty to receive
payments. They are developed using similar secure system. Hence one can be fully confident
while paying. There have been never any reports confirmed regarding money stolen from
contactless card still in possession of cardholder.
(c)(iii) Ans: Both of the card types uses distinct interface mechanisms and are automatically
distinguished through the very activity to read them. Contact based cards are accessed only
through contact technology reader and non-contact card should use RFID or any capacitive or
additional method on which the card is based. Thus the phone gets aware of what has been
interfaced with.
(c)(ii) How would the fare then be calculated and paid, and is there any change in the
certainty of receiving payment?
Ans: Fares can be calculated and then paid for customers through using near field
communication of NFC or RFID technology. Here the allowable quantity for contactless
transaction has been varying from country and bank. Yes, there is a certainty to receive
payments. They are developed using similar secure system. Hence one can be fully confident
while paying. There have been never any reports confirmed regarding money stolen from
contactless card still in possession of cardholder.
(c)(iii) Ans: Both of the card types uses distinct interface mechanisms and are automatically
distinguished through the very activity to read them. Contact based cards are accessed only
through contact technology reader and non-contact card should use RFID or any capacitive or
additional method on which the card is based. Thus the phone gets aware of what has been
interfaced with.
9SMART CARDS
2014
Question 1
(a)(i) Very briefly describe three main categories of attacks that may be used against
security modules.
Ans: The three main categories of attacks which may be against the security modules are listed
below:
• Insider Attack (Koeberl et al., 2014)
– Significant percentage of breaches
– Ex.: Run-on fraud, disgruntled employees
• Lunchtime Attack (Koeberl et al., 2014)
– Take place during a small window of opportunity
– Ex.: During a lunch or coffee break
• Focused Attack (Koeberl et al., 2014)
– Time, money, and resources not an issue
Question 4
(a)(i) What does RFID stand for?
And: RFID generally stands for Radio Frequency Identification.
(a)(ii) Describe passive and active RFIDs and give an example of each.
Ans: Passive RFID tags are those tags which do not have any internal power source. This are
generally powered by the electromagnetic energy that are transmitted by the RFID readers. This
types of tags are generally used for the tracking of files, controlling access, race timing and many
more (Ahson & Ilyas, 2017). They are having a shorter range.
2014
Question 1
(a)(i) Very briefly describe three main categories of attacks that may be used against
security modules.
Ans: The three main categories of attacks which may be against the security modules are listed
below:
• Insider Attack (Koeberl et al., 2014)
– Significant percentage of breaches
– Ex.: Run-on fraud, disgruntled employees
• Lunchtime Attack (Koeberl et al., 2014)
– Take place during a small window of opportunity
– Ex.: During a lunch or coffee break
• Focused Attack (Koeberl et al., 2014)
– Time, money, and resources not an issue
Question 4
(a)(i) What does RFID stand for?
And: RFID generally stands for Radio Frequency Identification.
(a)(ii) Describe passive and active RFIDs and give an example of each.
Ans: Passive RFID tags are those tags which do not have any internal power source. This are
generally powered by the electromagnetic energy that are transmitted by the RFID readers. This
types of tags are generally used for the tracking of files, controlling access, race timing and many
more (Ahson & Ilyas, 2017). They are having a shorter range.
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
10SMART CARDS
Active RFID tags are those tags which are powered by the battery and are associated with
continuous broadcasting of their signals. This are also known as “Beacons” and are associated
with accurate tracking if the real time locations of any type of assets (Zhong et al., 2013). They
are having a longer range than passive tags.
(a)(iii) Give a reasoned opinion of whether an RFID necessarily implies any security.
Ans: RFID is a shortwave communication technology that has the capability of identifying any
items that are within the range of the RFID reader. Therefore it can be stated that tracking of
items becomes very much easy with the use of RFID tags (Amendola et al., 2014). This initially
leads to elimination of threats related to stealing or theft.
(a)(iv) Comment on the shapes and operational ranges of RFIDs.
Ans: RFID system generally consists of an antenna or coil, a transceiver which consists of a
decoder and a transponder which is programmed with a unique information and this is the RFID
tag. RFID operates at various frequencies (Chae et al., 2013). The low frequency range is around
30 KHz to 500 KHz. And the highest frequency range is 850 MHz to 950 MHz and 2.4 GHz to
2.5 GHz.
(b)(i) Ranges of Generic RFID tags
Ans: The four ranges of generic RFID devices are 30 KHz-5.8 GHz which is the low frequency,
high frequency, ultrahigh frequency and lastly the microwave frequency. The frequency is
chosen according to the application, the tags size, and the ranges of the reader which is required.
The rate of data transfer or the throughput rates is faster when the frequency is high but the
system becomes more expensive with higher frequency (Hanwate & Thakare, 2015). The RFD
systems mainly operates in the low frequency having a long band ranging from 125 to 135 KHz.
The passive RFID tags makes use of the low frequency which are having a short read range. The
Active RFID tags are those tags which are powered by the battery and are associated with
continuous broadcasting of their signals. This are also known as “Beacons” and are associated
with accurate tracking if the real time locations of any type of assets (Zhong et al., 2013). They
are having a longer range than passive tags.
(a)(iii) Give a reasoned opinion of whether an RFID necessarily implies any security.
Ans: RFID is a shortwave communication technology that has the capability of identifying any
items that are within the range of the RFID reader. Therefore it can be stated that tracking of
items becomes very much easy with the use of RFID tags (Amendola et al., 2014). This initially
leads to elimination of threats related to stealing or theft.
(a)(iv) Comment on the shapes and operational ranges of RFIDs.
Ans: RFID system generally consists of an antenna or coil, a transceiver which consists of a
decoder and a transponder which is programmed with a unique information and this is the RFID
tag. RFID operates at various frequencies (Chae et al., 2013). The low frequency range is around
30 KHz to 500 KHz. And the highest frequency range is 850 MHz to 950 MHz and 2.4 GHz to
2.5 GHz.
(b)(i) Ranges of Generic RFID tags
Ans: The four ranges of generic RFID devices are 30 KHz-5.8 GHz which is the low frequency,
high frequency, ultrahigh frequency and lastly the microwave frequency. The frequency is
chosen according to the application, the tags size, and the ranges of the reader which is required.
The rate of data transfer or the throughput rates is faster when the frequency is high but the
system becomes more expensive with higher frequency (Hanwate & Thakare, 2015). The RFD
systems mainly operates in the low frequency having a long band ranging from 125 to 135 KHz.
The passive RFID tags makes use of the low frequency which are having a short read range. The
11SMART CARDS
high frequency ranges from 3MHz to 30 MHz but most of the high frequency RFID tags operate
at a range of 13.56 MHz. ultra-high frequency ranges from 300 MHz to 1000 MHz. the operating
range of the passive tags are 865-868 MHz in Europe and 902-928 MHz in the United States.
Whereas the operating range of active ultra-high frequency ranges from 315 MHz and 433 MHz.
the operating range of typical microwave frequency is 2.45 GHz or 5.8 GHz.
(b)(ii) What differences are there, if any, between a sophisticated RFID and a contact-less
smart card?
Ans: The contactless cards are much more advanced and secure than the RFID. The tracking
range of RFID is much more than the Smart contact-less cards as contact-less cards have a range
of about four to five inches so as to prevent the tracking and eavesdropping.
(b)(iii) What attacks may be possible against an RFID that are not possible against a smart
card with contacts?
Ans: RFID tags can be read by making use of any compatible reader whereas in case of contact
less cards this is not at all possible.
high frequency ranges from 3MHz to 30 MHz but most of the high frequency RFID tags operate
at a range of 13.56 MHz. ultra-high frequency ranges from 300 MHz to 1000 MHz. the operating
range of the passive tags are 865-868 MHz in Europe and 902-928 MHz in the United States.
Whereas the operating range of active ultra-high frequency ranges from 315 MHz and 433 MHz.
the operating range of typical microwave frequency is 2.45 GHz or 5.8 GHz.
(b)(ii) What differences are there, if any, between a sophisticated RFID and a contact-less
smart card?
Ans: The contactless cards are much more advanced and secure than the RFID. The tracking
range of RFID is much more than the Smart contact-less cards as contact-less cards have a range
of about four to five inches so as to prevent the tracking and eavesdropping.
(b)(iii) What attacks may be possible against an RFID that are not possible against a smart
card with contacts?
Ans: RFID tags can be read by making use of any compatible reader whereas in case of contact
less cards this is not at all possible.
12SMART CARDS
Question 5
(a) (i) What does TPM stand for?
Ans: TMP stands for Trusted Platform Module. This is a specialized chip on an end point device
that is responsible for storage of the RSA encryption keys which are specific to the host system
for authentication of the hardware (Arthur & Challener, 2015).
(a)(ii) What role does it play in providing assurance of expected behavior of the platform?
Ans: The TPM chip consists of the RSA key pair known as the Endorsement key which is
present inside the chip and cannot be accessed by any software. The storage of SRK or Storage
Root Key takes place when ownership of the system is taken over by the user or administrator
(McGill, 2013). Secondly there is Attestation Identity Key which is associated with the
protection of device against any type of unauthorized firmware or software modification by
altering any key sections of firmware or software before execution.
Question 5
(a) (i) What does TPM stand for?
Ans: TMP stands for Trusted Platform Module. This is a specialized chip on an end point device
that is responsible for storage of the RSA encryption keys which are specific to the host system
for authentication of the hardware (Arthur & Challener, 2015).
(a)(ii) What role does it play in providing assurance of expected behavior of the platform?
Ans: The TPM chip consists of the RSA key pair known as the Endorsement key which is
present inside the chip and cannot be accessed by any software. The storage of SRK or Storage
Root Key takes place when ownership of the system is taken over by the user or administrator
(McGill, 2013). Secondly there is Attestation Identity Key which is associated with the
protection of device against any type of unauthorized firmware or software modification by
altering any key sections of firmware or software before execution.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
13SMART CARDS
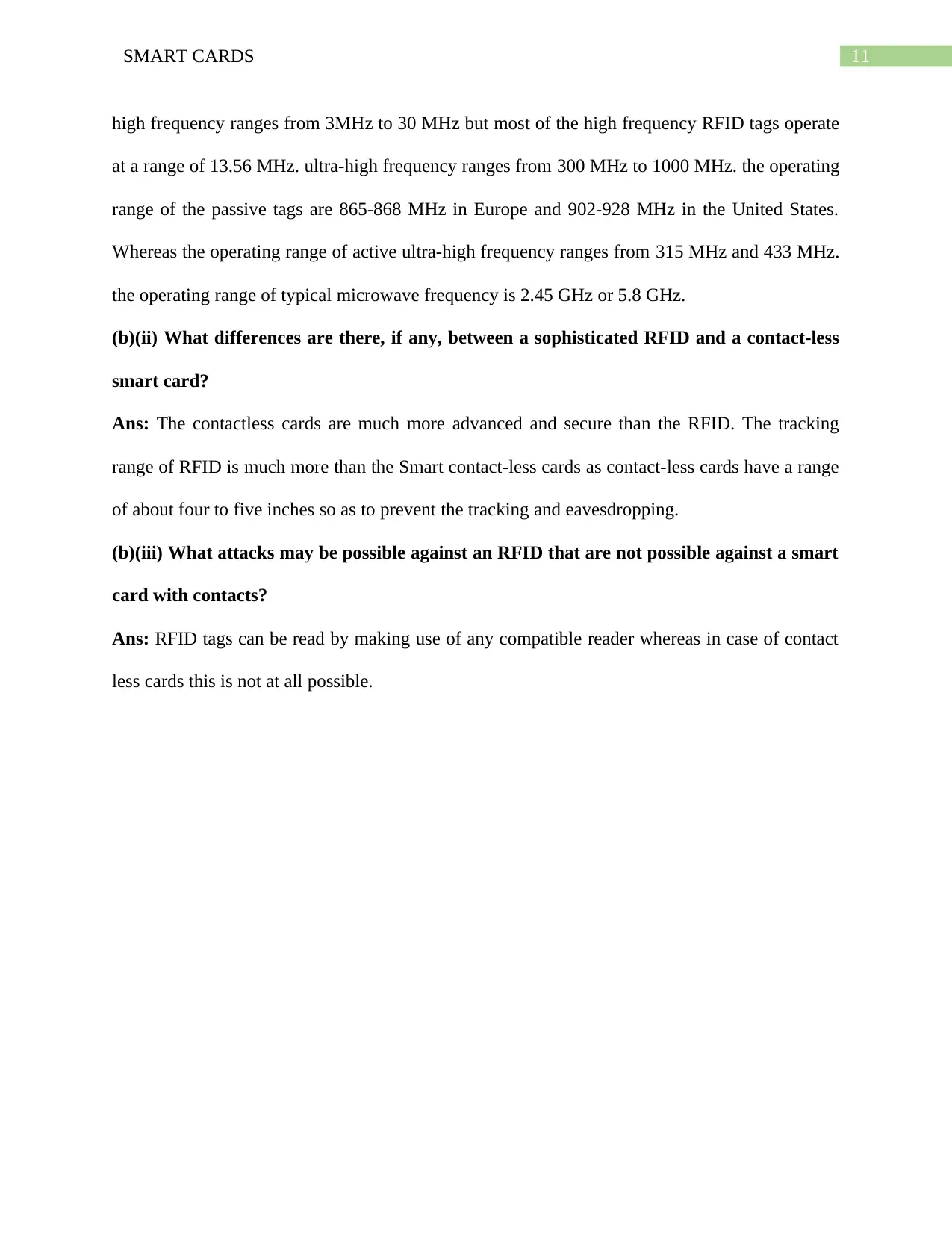
(a)(iii) Diagram, describing the TPM’s internal building blocks.
Fig: Internal Building Block of TPM
(a)(iv) Three types of cryptographic key found in a TPM.
Ans: The three types of cryptographic keys found in the TPM are Endorsement Key, Storage
Root Key and Attestation Identity Key. Each TPM mainly consists of an RSA key pair which is
known as the Endorsement Key. The pair is generally maintained inside the chip and is not
accessible by the software. Whenever the user or administrator takes the ownership of the system
then The SRK or Storage Rot Key is created. Based on the Endorsement Key and the password
specified by the owner the key pair is generated by the TPM (Akram, Markantonakis & Mayes,
2014). Lastly the second key known as the Attestation Key is associated with the protection of
the device against any type of unauthorized firmware software modification and this is done by
hashing all the critical sections of the software and firmware before they are executed.
(a)(iii) Diagram, describing the TPM’s internal building blocks.
Fig: Internal Building Block of TPM
(a)(iv) Three types of cryptographic key found in a TPM.
Ans: The three types of cryptographic keys found in the TPM are Endorsement Key, Storage
Root Key and Attestation Identity Key. Each TPM mainly consists of an RSA key pair which is
known as the Endorsement Key. The pair is generally maintained inside the chip and is not
accessible by the software. Whenever the user or administrator takes the ownership of the system
then The SRK or Storage Rot Key is created. Based on the Endorsement Key and the password
specified by the owner the key pair is generated by the TPM (Akram, Markantonakis & Mayes,
2014). Lastly the second key known as the Attestation Key is associated with the protection of
the device against any type of unauthorized firmware software modification and this is done by
hashing all the critical sections of the software and firmware before they are executed.
14SMART CARDS
(b) (i) Opt-in for a TPM
Ans: Opt-in is one of the component which is generally associated with indicating the difference
between smart cards and TPM. The TCM enabled platforms are controlled by the large remote
organizations. This is associated with providing a mechanism which generally ensures the fact
that it is the owner who is solely responsible for taking the ownership and configuring the TPM.
According to the TCG policy the TCM is to be delivered to the customer in the form desired by
the customer (Ekberg, Kostiainen & Asokan, 2013).
(b)(ii) The process of taking ownership of a TPM.
Ans: Whenever a user is taking over the ownership of the TPM they are establishing a secret
which is shared and is generally refers to as the owner authentication data and initially stores the
data in the secure storage of the TPM (Ekberg, Kostiainen & Asokan, 2014). Once a user
becomes an owner then they are capable of controlling the access to certain protected operations
and this is done by requiring proof of the ownership which is generally demonstrated by entering
the owner authentication data so as to authenticate the owner.
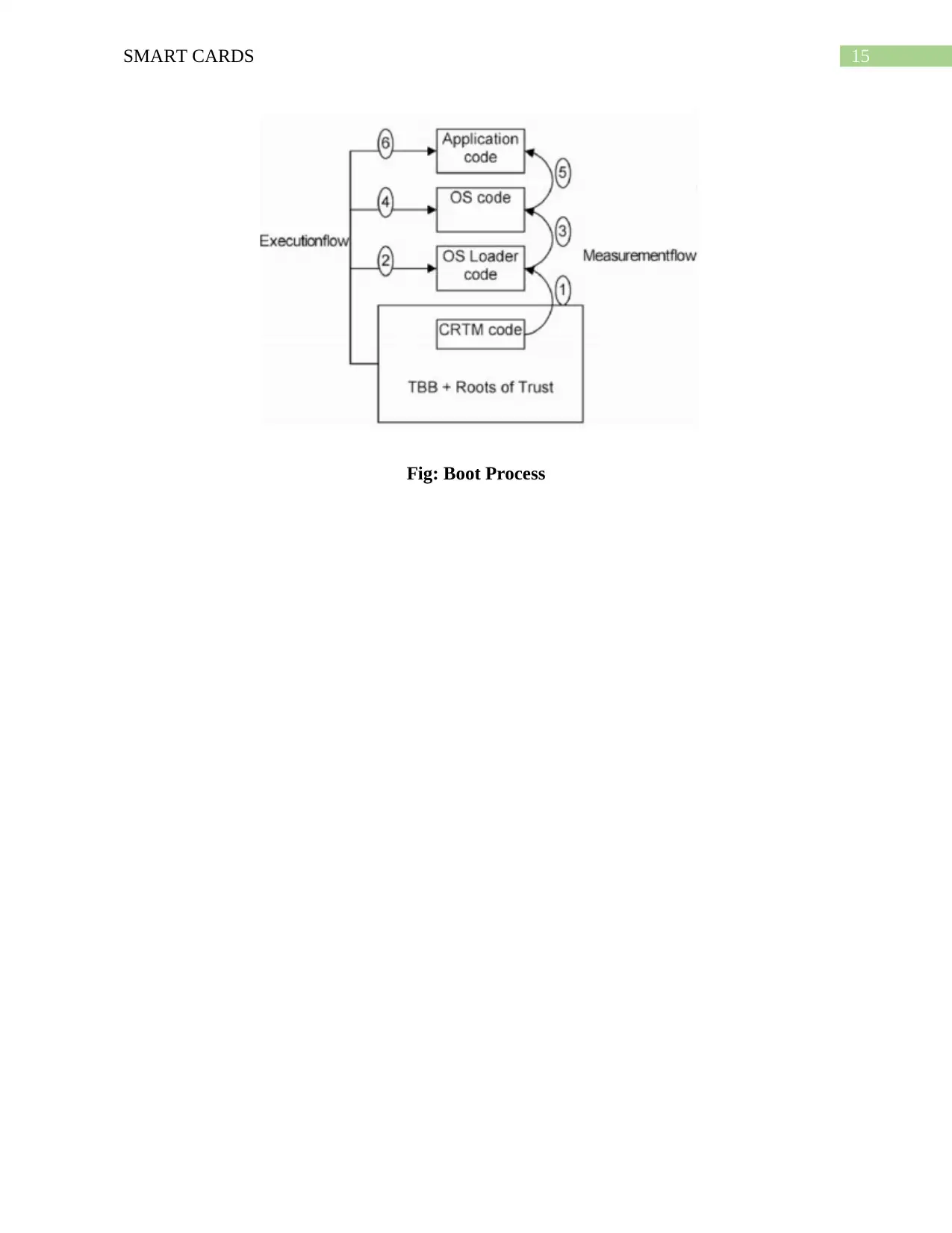
(b)(iii) Typical boot process for a platform with a TPM.
Ans: The trusted Boot Block consists of CRTM which is the first process of the boot. CRTM is
one of the trusted components and the integrity of this cannot be measured by the external code
(Osborn & Challener, 2013). Despite of this this might perform a self-check of its own integrity.
The CRTM is responsible for measuring the rest of the BIOS before loading it. Followed by the
Loaded of the BIOS the taking of control is successful and measurement of the integrity if the
OS loader is done (Tomlinson, 2017). Then the control is passed to the loader which is followed
by measuring of the integrity of the operating system by the loader. This continues unless and
until all the applications are loaded and executed.
(b) (i) Opt-in for a TPM
Ans: Opt-in is one of the component which is generally associated with indicating the difference
between smart cards and TPM. The TCM enabled platforms are controlled by the large remote
organizations. This is associated with providing a mechanism which generally ensures the fact
that it is the owner who is solely responsible for taking the ownership and configuring the TPM.
According to the TCG policy the TCM is to be delivered to the customer in the form desired by
the customer (Ekberg, Kostiainen & Asokan, 2013).
(b)(ii) The process of taking ownership of a TPM.
Ans: Whenever a user is taking over the ownership of the TPM they are establishing a secret
which is shared and is generally refers to as the owner authentication data and initially stores the
data in the secure storage of the TPM (Ekberg, Kostiainen & Asokan, 2014). Once a user
becomes an owner then they are capable of controlling the access to certain protected operations
and this is done by requiring proof of the ownership which is generally demonstrated by entering
the owner authentication data so as to authenticate the owner.
(b)(iii) Typical boot process for a platform with a TPM.
Ans: The trusted Boot Block consists of CRTM which is the first process of the boot. CRTM is
one of the trusted components and the integrity of this cannot be measured by the external code
(Osborn & Challener, 2013). Despite of this this might perform a self-check of its own integrity.
The CRTM is responsible for measuring the rest of the BIOS before loading it. Followed by the
Loaded of the BIOS the taking of control is successful and measurement of the integrity if the
OS loader is done (Tomlinson, 2017). Then the control is passed to the loader which is followed
by measuring of the integrity of the operating system by the loader. This continues unless and
until all the applications are loaded and executed.
15SMART CARDS
Fig: Boot Process
Fig: Boot Process
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
16SMART CARDS
2015
Question 1
(a)(i) The difference between the terms trusted and trustworthy.
Ans: Trustworthy generally refers to the quality of being reliable, dependable and honest. In
other words it can be stated that it is the ability of being relied on as honesty or truthful. Whereas
trusted refers to the position of trust- which means the credibility, dependability and favored by
precious experiences or dealings or by making use of general reputations (Akram,
Markantonakis, & Mayes, 2013).
(a)(ii) Justification for the fact that majority of smart phone platforms and smart cards are
trusted and/or trustworthy.
Ans: Most of the smartphone platforms and the smart cards can be considered as trustworthy as
well as trusted this is due to the fact that are responsible for holding large amount of data and the
security features of this helps in protecting the data and the other facilities provided by this smart
devices are also very much reliable (Smith, 2013).
(a)(iii) Trusted Execution Environment.
Ans: Trusted Execution Environment generally refers to the secure area of the main processor
which usually guarantees the codes and the data which are loaded inside so as to be protected
according to their confidentiality and integrity (Jang et al., 2015).
(b) (i) Physical, side-channel and fault attack
Ans: Fault attack refers to the technique which is based upon the fault injection so as to modify
the behavior of the application (Gruss, Maurice & Mangard, 2016). For smart cards this type of
attack might be diverse in nature but despite of this it is a successful one.
2015
Question 1
(a)(i) The difference between the terms trusted and trustworthy.
Ans: Trustworthy generally refers to the quality of being reliable, dependable and honest. In
other words it can be stated that it is the ability of being relied on as honesty or truthful. Whereas
trusted refers to the position of trust- which means the credibility, dependability and favored by
precious experiences or dealings or by making use of general reputations (Akram,
Markantonakis, & Mayes, 2013).
(a)(ii) Justification for the fact that majority of smart phone platforms and smart cards are
trusted and/or trustworthy.
Ans: Most of the smartphone platforms and the smart cards can be considered as trustworthy as
well as trusted this is due to the fact that are responsible for holding large amount of data and the
security features of this helps in protecting the data and the other facilities provided by this smart
devices are also very much reliable (Smith, 2013).
(a)(iii) Trusted Execution Environment.
Ans: Trusted Execution Environment generally refers to the secure area of the main processor
which usually guarantees the codes and the data which are loaded inside so as to be protected
according to their confidentiality and integrity (Jang et al., 2015).
(b) (i) Physical, side-channel and fault attack
Ans: Fault attack refers to the technique which is based upon the fault injection so as to modify
the behavior of the application (Gruss, Maurice & Mangard, 2016). For smart cards this type of
attack might be diverse in nature but despite of this it is a successful one.
17SMART CARDS
Question 4
(a) (i) Definition of the IoT.
Ans: IoT or internet of. things generally refers to the network of physical devices like vehicles,
home appliances embedded with electronics, software’s, sensors, actuators and connectivity
which is responsible for connectivity of this devices and help them in exchanging of data (Gubbi
et al., 2013).
(a)(ii) IoT by the year of 2020
Ans: IoT enabled things might increase to an amount of 25 billion connected devices by the year
of 2020. This is due to the fact that the use of internet growing at a very fast rate and almost
every person of today’s world makes use of the internet (Lee & Lee, 2015)
(a) (iii) The security vulnerabilities of existing IoT devices.
Ans: Along with advantages there are several security vulnerabilities of IoT devices. This might
include security breaches, insecure web interface, ineffective authentication or authorization
process, insecure network services, Lack of transport encryption and many more (Kelly,
Suryadevara & Mukhopadhyay, 2013).
(b)(i) Definition of completion, initialization, and personalization.
Ans: initialization and personalization are the decisive step from the perspective of an
informatics. The entire generic data that is all the data which is same for all the cards are written
in the memory during the initialization stage. Along with this all the data which are related to the
individual cards or users are written in the personalization stage and due to this fact it is also
known as individualization. Both this stages are performed in a secure area (Akram,
Markantonakis & Mayes, 2013). There is an enormous amount of advantage that is there is no
Question 4
(a) (i) Definition of the IoT.
Ans: IoT or internet of. things generally refers to the network of physical devices like vehicles,
home appliances embedded with electronics, software’s, sensors, actuators and connectivity
which is responsible for connectivity of this devices and help them in exchanging of data (Gubbi
et al., 2013).
(a)(ii) IoT by the year of 2020
Ans: IoT enabled things might increase to an amount of 25 billion connected devices by the year
of 2020. This is due to the fact that the use of internet growing at a very fast rate and almost
every person of today’s world makes use of the internet (Lee & Lee, 2015)
(a) (iii) The security vulnerabilities of existing IoT devices.
Ans: Along with advantages there are several security vulnerabilities of IoT devices. This might
include security breaches, insecure web interface, ineffective authentication or authorization
process, insecure network services, Lack of transport encryption and many more (Kelly,
Suryadevara & Mukhopadhyay, 2013).
(b)(i) Definition of completion, initialization, and personalization.
Ans: initialization and personalization are the decisive step from the perspective of an
informatics. The entire generic data that is all the data which is same for all the cards are written
in the memory during the initialization stage. Along with this all the data which are related to the
individual cards or users are written in the personalization stage and due to this fact it is also
known as individualization. Both this stages are performed in a secure area (Akram,
Markantonakis & Mayes, 2013). There is an enormous amount of advantage that is there is no
18SMART CARDS
need of secure communication with the smart cards as it is considerably simple and is somewhat
faster than transmission of the data by making use of the secure messaging.
need of secure communication with the smart cards as it is considerably simple and is somewhat
faster than transmission of the data by making use of the secure messaging.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
19SMART CARDS
2016
Question 1
(a)(i) Definition of” biometric feature”
Ans: Biometrics is nothing but measurement of statistical analysis of data which focus on people
unique physical behavior and characteristics (He & Wang, 2015). This kind of technology is
mainly used for identification and control of access, individual. The basics of biometrics
authentication is nothing but a person can be easily used by identified by his or her physical
kinds of behavior.
(a)(ii) Describe the typical factors in three factor authentication
Ans: Three factor authentication (3FA) is generally used for identifying conforming various
parts from various kinds of three kinds of separate categories related to authentication ports (He
& Wang, 2015). Authentication factors are generally classified into three kinds of categories
namely like:
Knowledge factors is generally inclusive of things which focus on certain number of
users like User names, password and personal identification numbers.
Possession factors like anything which a user must have in his possession to log in. This
category is generally inclusive of OTP tokens, smartphones, employee ID and SIM cards.
Inherence factors is generally inclusive of certain number of biological traits.
(a)(iii) Authentication factors that is kept secret
Ans: Authentication is nothing but a process which is used for analyzing someone or something
which is declared on a daily basis (Bo et al., 2013). Authentication generally proceeds
authorization and by combing of each of the term. Authorization is nothing but a process in
2016
Question 1
(a)(i) Definition of” biometric feature”
Ans: Biometrics is nothing but measurement of statistical analysis of data which focus on people
unique physical behavior and characteristics (He & Wang, 2015). This kind of technology is
mainly used for identification and control of access, individual. The basics of biometrics
authentication is nothing but a person can be easily used by identified by his or her physical
kinds of behavior.
(a)(ii) Describe the typical factors in three factor authentication
Ans: Three factor authentication (3FA) is generally used for identifying conforming various
parts from various kinds of three kinds of separate categories related to authentication ports (He
& Wang, 2015). Authentication factors are generally classified into three kinds of categories
namely like:
Knowledge factors is generally inclusive of things which focus on certain number of
users like User names, password and personal identification numbers.
Possession factors like anything which a user must have in his possession to log in. This
category is generally inclusive of OTP tokens, smartphones, employee ID and SIM cards.
Inherence factors is generally inclusive of certain number of biological traits.
(a)(iii) Authentication factors that is kept secret
Ans: Authentication is nothing but a process which is used for analyzing someone or something
which is declared on a daily basis (Bo et al., 2013). Authentication generally proceeds
authorization and by combing of each of the term. Authorization is nothing but a process in
20SMART CARDS
which various kinds of credentials are provided and the files on the database can be easily
accessed.
(b) Biometric verification system
Ans: Biometric verification can be considered to be any kind of means by which a person can
easily identify by evaluation of one or more kind of biometric traits. Unique identifiers are
generally inclusive of fingerprints, hand geometry, retina and iris kind of pattern and voice
waves and signatures (Shekhar et al., 2014). The oldest form of biometric verification is nothing
but a fingerprint. Iris-pattern and retina pattern authentication methods are generally used for
employing in banks by making use of automatic teller machines. Voice waveforms recognition
methods has been used for large number of years with tape recordings. Face-recognition
technology has been generally used in large crowds while hand geometry is considered to have
easy access to provide easy kind of access (Chuang & Chen, 2014). No matter what kind of
biometric methodology is used, the identification process will always remain the same. A record
of person’s unique verification remains the same. When biometric methodology is used the
identification verification process still remains the same.
which various kinds of credentials are provided and the files on the database can be easily
accessed.
(b) Biometric verification system
Ans: Biometric verification can be considered to be any kind of means by which a person can
easily identify by evaluation of one or more kind of biometric traits. Unique identifiers are
generally inclusive of fingerprints, hand geometry, retina and iris kind of pattern and voice
waves and signatures (Shekhar et al., 2014). The oldest form of biometric verification is nothing
but a fingerprint. Iris-pattern and retina pattern authentication methods are generally used for
employing in banks by making use of automatic teller machines. Voice waveforms recognition
methods has been used for large number of years with tape recordings. Face-recognition
technology has been generally used in large crowds while hand geometry is considered to have
easy access to provide easy kind of access (Chuang & Chen, 2014). No matter what kind of
biometric methodology is used, the identification process will always remain the same. A record
of person’s unique verification remains the same. When biometric methodology is used the
identification verification process still remains the same.
21SMART CARDS
Question 3
(a)(i) Passive and active RFIDs
Ans: Passive RFID: Passive RFID system makes use of no kind of internal power source and
instead of that power is manly used by various electromagnetic energy which is transmitted from
RFID reader (Haghighat, Zonouz & Abdel-Mottaleb, 2013). Passive RFID tags are generally
makes use of certain number of application like access control, tracking of file, racing time,
smart labels and many other things.
Active RFID: It is nothing but an active kind of RFID systems which makes use of
battery powered or dependent RFID tags which can continuously broadcast their signal
(Haghighat, Zonouz & Abdel-Mottaleb, 2013). Active RFID are generally used like beacons so
that they can accurately track real time location of various kinds of assets or in high kind of
environment like tolling. Active tags generally provide much longer read ranges in comparison
to passive tags and they considered to be much more expensive also.
(a)(ii) Explain how a mobile phone, without Near Field Communication (NFC), overlaps
with these definitions.
Ans: Near field Communication is nothing but a kind of short range wireless standard of
connectivity which makes use of magnetic field induction. It makes use of magnetic induction
for enabling communication between various kinds of devices when they are touched together
(Haghighat, Zonouz & Abdel-Mottaleb, 2013). With the help of NFC in a cellphone one can
easily take pictures which is enabled in transmitting of images for display.
(b)(i) For the open tag type, describe two cryptographic measures that can be used in a
data handling application
Question 3
(a)(i) Passive and active RFIDs
Ans: Passive RFID: Passive RFID system makes use of no kind of internal power source and
instead of that power is manly used by various electromagnetic energy which is transmitted from
RFID reader (Haghighat, Zonouz & Abdel-Mottaleb, 2013). Passive RFID tags are generally
makes use of certain number of application like access control, tracking of file, racing time,
smart labels and many other things.
Active RFID: It is nothing but an active kind of RFID systems which makes use of
battery powered or dependent RFID tags which can continuously broadcast their signal
(Haghighat, Zonouz & Abdel-Mottaleb, 2013). Active RFID are generally used like beacons so
that they can accurately track real time location of various kinds of assets or in high kind of
environment like tolling. Active tags generally provide much longer read ranges in comparison
to passive tags and they considered to be much more expensive also.
(a)(ii) Explain how a mobile phone, without Near Field Communication (NFC), overlaps
with these definitions.
Ans: Near field Communication is nothing but a kind of short range wireless standard of
connectivity which makes use of magnetic field induction. It makes use of magnetic induction
for enabling communication between various kinds of devices when they are touched together
(Haghighat, Zonouz & Abdel-Mottaleb, 2013). With the help of NFC in a cellphone one can
easily take pictures which is enabled in transmitting of images for display.
(b)(i) For the open tag type, describe two cryptographic measures that can be used in a
data handling application
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
22SMART CARDS
Ans: RFID generally acts like an anti-counterfeiting technology at present rather than primitive.
The whole security generally depends on RFID tag is compare to be harder to copy than a bar
code which is provided (The et al., 2013). Sound technologies solution for counterfeiting
problems need to be properly developed.
(b)(ii) For the secured memory tag type, suggest where the secret keys are stored and used,
and offer opinion on whether they are, or are not, adequately protected.
Ans: For checking the validating of authentication of a replaceable kind of consumable or
replace thing it has a system which is connected to a host. There should be should be some kind
of information should be stored in both and clients (Abaza et al.,2013). CryptoRF chips generally
provide some secure kinds of location where secret kind of data in the client side should be
stored. The companion chip generally provides certain good quality of algorithm and entire kind
of protocol which is needed to be completely used in hardware.
(b)(iii) Give a reasoned opinion on how well the open or secured memory tags prevent
cloning.
Ans: RFID tags generally do not have any kind of protection against cloning. Such kind of tags
generally contain freely readable data. Anyone can easily read NDEF tags from one and
duplicate data.
(c) RFID disadvatages
Ans: Some disadvantages of RFID are:
RFID system are considered to be more expensive than any other system like barcode
system.
RFID technology is considered to be much harder to understand.
It generally considered to be much reliable
Ans: RFID generally acts like an anti-counterfeiting technology at present rather than primitive.
The whole security generally depends on RFID tag is compare to be harder to copy than a bar
code which is provided (The et al., 2013). Sound technologies solution for counterfeiting
problems need to be properly developed.
(b)(ii) For the secured memory tag type, suggest where the secret keys are stored and used,
and offer opinion on whether they are, or are not, adequately protected.
Ans: For checking the validating of authentication of a replaceable kind of consumable or
replace thing it has a system which is connected to a host. There should be should be some kind
of information should be stored in both and clients (Abaza et al.,2013). CryptoRF chips generally
provide some secure kinds of location where secret kind of data in the client side should be
stored. The companion chip generally provides certain good quality of algorithm and entire kind
of protocol which is needed to be completely used in hardware.
(b)(iii) Give a reasoned opinion on how well the open or secured memory tags prevent
cloning.
Ans: RFID tags generally do not have any kind of protection against cloning. Such kind of tags
generally contain freely readable data. Anyone can easily read NDEF tags from one and
duplicate data.
(c) RFID disadvatages
Ans: Some disadvantages of RFID are:
RFID system are considered to be more expensive than any other system like barcode
system.
RFID technology is considered to be much harder to understand.
It generally considered to be much reliable
23SMART CARDS
RFID tags are considered to be much larger in size.
It generally comes up with the idea of unauthorized reading of passports and credit cards.
More than one kind of tag can be easily responded at the same time.
Question 4
(a) (i) Suggest three different classes of implementation attack that a HSM should resist,
and give an example of each.
Ans: Cryptography generally provides secure kind of communication in presence of malicious
kinds of third parties which are known as adversaries (Bowyer, Hollingsworth, & Flynn, 2016).
Encryption generally makes use of new kind of algorithms and a key of transformation which
has an encrypted kind of output. A given kind of algorithm will always transform plaintext into
cipher text only and only if same kind of key is used.
(a)(ii) Two different types of security action that the server may request of the HSM, and
how they may help secure the server.
Ans: A hardware security module is nothing but a hardware kind of encryption device which is
generally connected to a server at the level of device. A HSM is nothing but a kind of hardware
device which is managed separately from various kinds of operating system. This kind of module
makes use of task makes use of operating system.
(a)(iii) Encrypting the database and advantages and disadvantages there could be with
database back-ups.
Ans: Database encryption is nothing but a process which can be used for converting of data
within a database in plain kind of text format it makes use of cipher text by making use of
suitable algorithm (Bowyer, Hollingsworth, & Flynn, 2016). Database decryption is nothing but
RFID tags are considered to be much larger in size.
It generally comes up with the idea of unauthorized reading of passports and credit cards.
More than one kind of tag can be easily responded at the same time.
Question 4
(a) (i) Suggest three different classes of implementation attack that a HSM should resist,
and give an example of each.
Ans: Cryptography generally provides secure kind of communication in presence of malicious
kinds of third parties which are known as adversaries (Bowyer, Hollingsworth, & Flynn, 2016).
Encryption generally makes use of new kind of algorithms and a key of transformation which
has an encrypted kind of output. A given kind of algorithm will always transform plaintext into
cipher text only and only if same kind of key is used.
(a)(ii) Two different types of security action that the server may request of the HSM, and
how they may help secure the server.
Ans: A hardware security module is nothing but a hardware kind of encryption device which is
generally connected to a server at the level of device. A HSM is nothing but a kind of hardware
device which is managed separately from various kinds of operating system. This kind of module
makes use of task makes use of operating system.
(a)(iii) Encrypting the database and advantages and disadvantages there could be with
database back-ups.
Ans: Database encryption is nothing but a process which can be used for converting of data
within a database in plain kind of text format it makes use of cipher text by making use of
suitable algorithm (Bowyer, Hollingsworth, & Flynn, 2016). Database decryption is nothing but
24SMART CARDS
the method of converting of cipher text into original kind of information by making use of
certain number of keys which is generated by encryption algorithm.
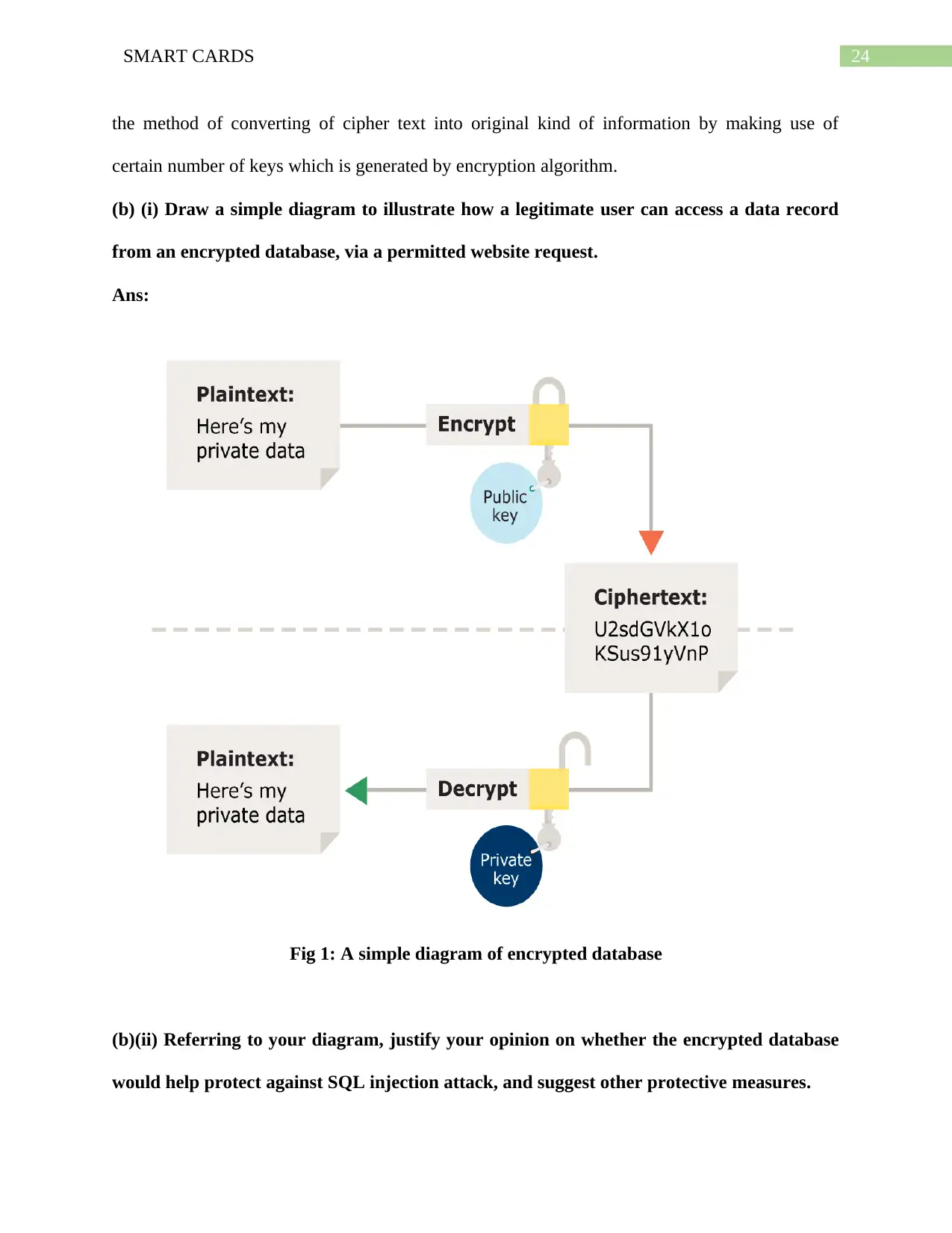
(b) (i) Draw a simple diagram to illustrate how a legitimate user can access a data record
from an encrypted database, via a permitted website request.
Ans:
Fig 1: A simple diagram of encrypted database
(b)(ii) Referring to your diagram, justify your opinion on whether the encrypted database
would help protect against SQL injection attack, and suggest other protective measures.
the method of converting of cipher text into original kind of information by making use of
certain number of keys which is generated by encryption algorithm.
(b) (i) Draw a simple diagram to illustrate how a legitimate user can access a data record
from an encrypted database, via a permitted website request.
Ans:
Fig 1: A simple diagram of encrypted database
(b)(ii) Referring to your diagram, justify your opinion on whether the encrypted database
would help protect against SQL injection attack, and suggest other protective measures.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
25SMART CARDS
Ans: There are large number of protective measures of encrypted database which can easily
protect against SQL injection attack.
SQL server generally has in-built encryption of protection of various kinds of sensitive
data.
SQL server automatically encrypts various kinds of password which is used for login and
various kinds of application roles.
SQL server makes use of support of encrypting of data which can be sent to server and
other kinds of associated clients.
SQL injection is nothing but a name which is used for general kinds of attacks for
nefarious users for retrieving of data.
Ans: There are large number of protective measures of encrypted database which can easily
protect against SQL injection attack.
SQL server generally has in-built encryption of protection of various kinds of sensitive
data.
SQL server automatically encrypts various kinds of password which is used for login and
various kinds of application roles.
SQL server makes use of support of encrypting of data which can be sent to server and
other kinds of associated clients.
SQL injection is nothing but a name which is used for general kinds of attacks for
nefarious users for retrieving of data.

26SMART CARDS
2017
Question 2
(a) (i) For a traditional card purchase in a physical shop, draw a diagram of the five
entities involved in the financial transaction and describe the general process flows.
Ans:
Fig 1: Five entities involved in financial transaction
(Source: Created by Author)
In a traditional card purchase five entities involved in financial transaction are
identification of contracts with customers, identification of performance in a contract, analyzing
the price of transaction in a medium (Roland & Langer, 2013). Proper allocation of transaction
of price to help in obligation of performance, proper recognition of revenue when a particular
kind of entity has satisfied a performance related obligation.
(a)(ii) EMV cards are also capable of off-line data authentication. Describe Static Data
Authentication (SDA) with the aid of a diagram.
2017
Question 2
(a) (i) For a traditional card purchase in a physical shop, draw a diagram of the five
entities involved in the financial transaction and describe the general process flows.
Ans:
Fig 1: Five entities involved in financial transaction
(Source: Created by Author)
In a traditional card purchase five entities involved in financial transaction are
identification of contracts with customers, identification of performance in a contract, analyzing
the price of transaction in a medium (Roland & Langer, 2013). Proper allocation of transaction
of price to help in obligation of performance, proper recognition of revenue when a particular
kind of entity has satisfied a performance related obligation.
(a)(ii) EMV cards are also capable of off-line data authentication. Describe Static Data
Authentication (SDA) with the aid of a diagram.
27SMART CARDS
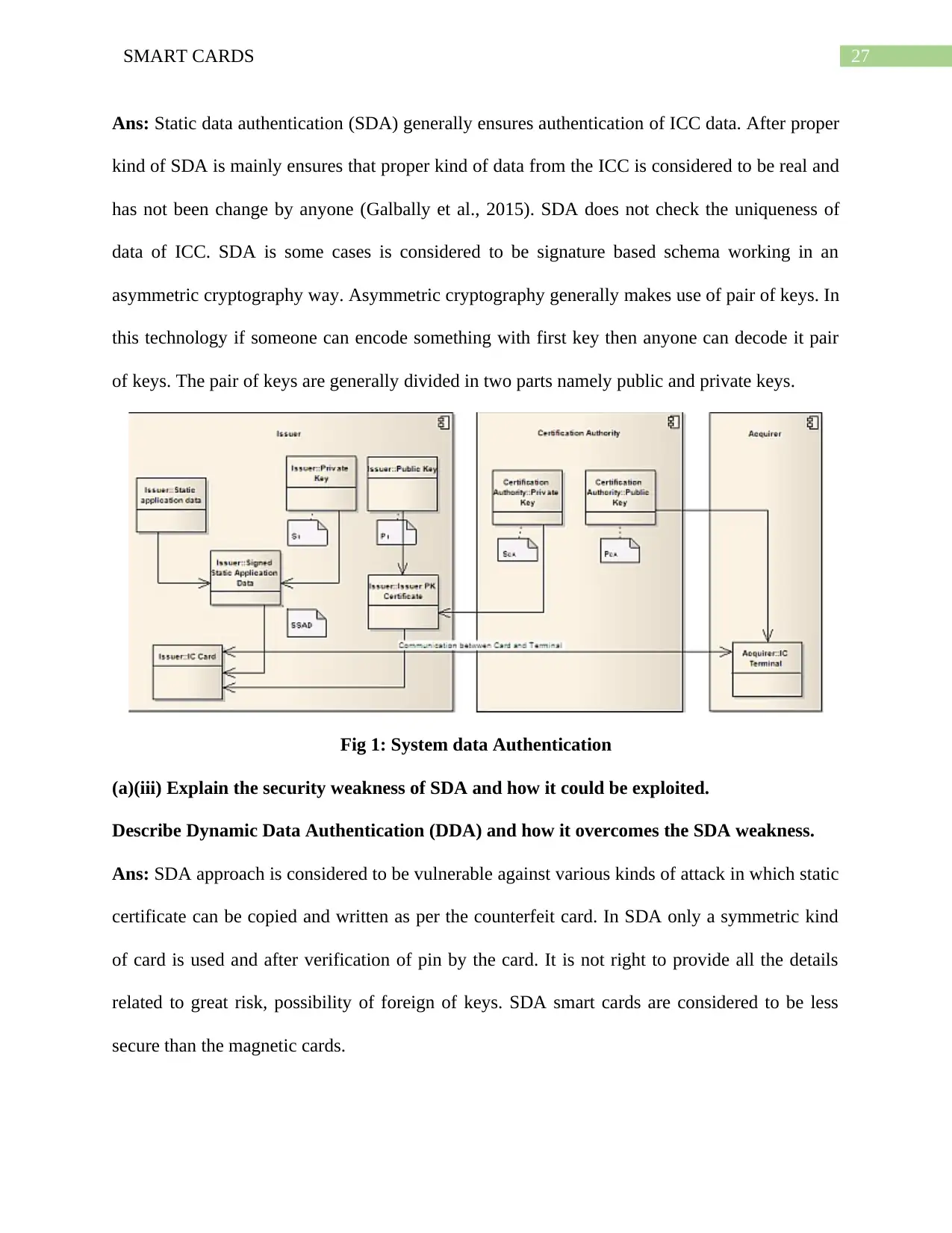
Ans: Static data authentication (SDA) generally ensures authentication of ICC data. After proper
kind of SDA is mainly ensures that proper kind of data from the ICC is considered to be real and
has not been change by anyone (Galbally et al., 2015). SDA does not check the uniqueness of
data of ICC. SDA is some cases is considered to be signature based schema working in an
asymmetric cryptography way. Asymmetric cryptography generally makes use of pair of keys. In
this technology if someone can encode something with first key then anyone can decode it pair
of keys. The pair of keys are generally divided in two parts namely public and private keys.
Fig 1: System data Authentication
(a)(iii) Explain the security weakness of SDA and how it could be exploited.
Describe Dynamic Data Authentication (DDA) and how it overcomes the SDA weakness.
Ans: SDA approach is considered to be vulnerable against various kinds of attack in which static
certificate can be copied and written as per the counterfeit card. In SDA only a symmetric kind
of card is used and after verification of pin by the card. It is not right to provide all the details
related to great risk, possibility of foreign of keys. SDA smart cards are considered to be less
secure than the magnetic cards.
Ans: Static data authentication (SDA) generally ensures authentication of ICC data. After proper
kind of SDA is mainly ensures that proper kind of data from the ICC is considered to be real and
has not been change by anyone (Galbally et al., 2015). SDA does not check the uniqueness of
data of ICC. SDA is some cases is considered to be signature based schema working in an
asymmetric cryptography way. Asymmetric cryptography generally makes use of pair of keys. In
this technology if someone can encode something with first key then anyone can decode it pair
of keys. The pair of keys are generally divided in two parts namely public and private keys.
Fig 1: System data Authentication
(a)(iii) Explain the security weakness of SDA and how it could be exploited.
Describe Dynamic Data Authentication (DDA) and how it overcomes the SDA weakness.
Ans: SDA approach is considered to be vulnerable against various kinds of attack in which static
certificate can be copied and written as per the counterfeit card. In SDA only a symmetric kind
of card is used and after verification of pin by the card. It is not right to provide all the details
related to great risk, possibility of foreign of keys. SDA smart cards are considered to be less
secure than the magnetic cards.
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
28SMART CARDS
In comparison to SDA, DDA requires a chip card is required which can easily perform
algorithm. This method in particular needs to generate dynamic kind of cryptogram for each and
every kind of transaction. In this method, each kind of card has a secret kind of key for
confirming authentication.
Question 3
(a)(i) Describe what is meant by the initialization and personalization processes of a smart
card.
Ans: One of the key challenges of smart card industry is to easily cope up with increasing size of
various kinds of memory size. While in the few years there are few kinds of kilobytes of energy
to handle. Based on the content of overloading the file structure is loaded afterwards and also
partly amount of content is loaded and various kinds of application should be available.
(a)(ii) Describe three different attack classes that are relevant to smart cards and give an
example of each.
Ans: The three level attack classes which is relevant to smart cards are:
OS-level attack: Smart card operating system can easily organize data in three level of
hierarchy. At root level it can easily hold dedicated files and elementary files.
Host based Security: System and Networks generally makes use of host based security
which is similar to smart cards which is used as simple carrier of information. Making use of
smart card with a password mechanism generally prevents unauthorized reading kinds of offers
but in many cases it can easily become accessible to hackers by making use of unencrypted
transmission between card and available host (Bernstein et al., 2013).
In comparison to SDA, DDA requires a chip card is required which can easily perform
algorithm. This method in particular needs to generate dynamic kind of cryptogram for each and
every kind of transaction. In this method, each kind of card has a secret kind of key for
confirming authentication.
Question 3
(a)(i) Describe what is meant by the initialization and personalization processes of a smart
card.
Ans: One of the key challenges of smart card industry is to easily cope up with increasing size of
various kinds of memory size. While in the few years there are few kinds of kilobytes of energy
to handle. Based on the content of overloading the file structure is loaded afterwards and also
partly amount of content is loaded and various kinds of application should be available.
(a)(ii) Describe three different attack classes that are relevant to smart cards and give an
example of each.
Ans: The three level attack classes which is relevant to smart cards are:
OS-level attack: Smart card operating system can easily organize data in three level of
hierarchy. At root level it can easily hold dedicated files and elementary files.
Host based Security: System and Networks generally makes use of host based security
which is similar to smart cards which is used as simple carrier of information. Making use of
smart card with a password mechanism generally prevents unauthorized reading kinds of offers
but in many cases it can easily become accessible to hackers by making use of unencrypted
transmission between card and available host (Bernstein et al., 2013).
29SMART CARDS
Card based security: System with card or token based security can easily treat smart
cards with various kinds of microprocessors like independent computing. During the time of card
and host users generally identifies the authentication.
(a)(iii) Propose a countermeasure against each of the attack examples you have described.
Ans: The countermeasures which can be used for preventing attacks are:
Making use of secret pin.
Bodily kind of failure.
(b) (i) Why is satellite broadcast decryption security more challenging than point-to-point
security?
Ans: Point to point security are nothing secured configuration are nothing but configured pairs
which can be used for communication between node points. While in Point to Multi-point
communication required data is needed for point to many communications (Karaklajić, Schmidt,
& Verbauwhede, 2013).
(ii) Suggest strategies to reduce the practical usefulness of discovered decryption keys?
Ans: Decryption key is nothing but the use of process of taking encoded or encrypted kind of
text or other data. It is followed by converting the text which the system can easily read. There
are some kind of difference between encryption and decryption. Encryption is nothing but a
process which can be used for translating plain text into something which generally appears to be
random and meaningless (Miao et al., 2015). For encryption of small amount of data symmetric
kind of encryption is used.
Card based security: System with card or token based security can easily treat smart
cards with various kinds of microprocessors like independent computing. During the time of card
and host users generally identifies the authentication.
(a)(iii) Propose a countermeasure against each of the attack examples you have described.
Ans: The countermeasures which can be used for preventing attacks are:
Making use of secret pin.
Bodily kind of failure.
(b) (i) Why is satellite broadcast decryption security more challenging than point-to-point
security?
Ans: Point to point security are nothing secured configuration are nothing but configured pairs
which can be used for communication between node points. While in Point to Multi-point
communication required data is needed for point to many communications (Karaklajić, Schmidt,
& Verbauwhede, 2013).
(ii) Suggest strategies to reduce the practical usefulness of discovered decryption keys?
Ans: Decryption key is nothing but the use of process of taking encoded or encrypted kind of
text or other data. It is followed by converting the text which the system can easily read. There
are some kind of difference between encryption and decryption. Encryption is nothing but a
process which can be used for translating plain text into something which generally appears to be
random and meaningless (Miao et al., 2015). For encryption of small amount of data symmetric
kind of encryption is used.
30SMART CARDS
(b)(iii) Assuming the CAM is not fast enough alone to decode the encrypted film broadcast,
propose a simple architecture for the STB and describe how it exploits the CAM to decode
the film.
Ans: STB stands consist of power port, Zener diode, Volt IC, RAM and CPU, Tunner IC and
some other kinds of things. Conditional Module Access is nothing but a technology which allows
paid TV providers to stop the access to the broadcasts. A Conditional Access Module (CAM) is
nothing but a combination of encryption keys, smart cards and computer code with various
electronics components.
Question 5
(a)(i) Identify, justify and compare the security requirements for each of the listed uses.
Ans: A set of security controls are needed for security controls which the university campus
needs to be implemented to protection of data of credit card. The security requirement for the
above mention processes is
Installation and maintenance of firewall.
Not making use of vendor suppliers for system passwords and other kinds of parameters.
Encryption transmission of cardholder for data across open and public networks.
Making use of regular use of secure systems and application.
Assign a unique ID to each kind of person with proper kind of computer access.
Restriction to physical access to several of computer data.
Tracking and monitoring of access to network resources and data of cardholder.
Testing of security systems and processes.
Maintenance of security policy which can address the information security.
(b)(iii) Assuming the CAM is not fast enough alone to decode the encrypted film broadcast,
propose a simple architecture for the STB and describe how it exploits the CAM to decode
the film.
Ans: STB stands consist of power port, Zener diode, Volt IC, RAM and CPU, Tunner IC and
some other kinds of things. Conditional Module Access is nothing but a technology which allows
paid TV providers to stop the access to the broadcasts. A Conditional Access Module (CAM) is
nothing but a combination of encryption keys, smart cards and computer code with various
electronics components.
Question 5
(a)(i) Identify, justify and compare the security requirements for each of the listed uses.
Ans: A set of security controls are needed for security controls which the university campus
needs to be implemented to protection of data of credit card. The security requirement for the
above mention processes is
Installation and maintenance of firewall.
Not making use of vendor suppliers for system passwords and other kinds of parameters.
Encryption transmission of cardholder for data across open and public networks.
Making use of regular use of secure systems and application.
Assign a unique ID to each kind of person with proper kind of computer access.
Restriction to physical access to several of computer data.
Tracking and monitoring of access to network resources and data of cardholder.
Testing of security systems and processes.
Maintenance of security policy which can address the information security.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

31SMART CARDS
(a)(ii) Propose a design for a smart card that would be suitable for all listed uses, then
describe the processes involved in preparing, issuing, using and terminating the cards. [10]
Fig 2: Sample Smart Card for students
The smart card should be prepared and issued by university. All the forthcoming stages
like preparing, issues and termination of card should be handled by university. A department
should be there to easily handle the above processes of smart card.
(a) (iii) Pick one of the listed uses and describe in detail how the card is practically used to
add security.
Ans: A smart card is nothing but a payment which is embedded with RFID technology and
function. The smart card can easily add benefit to students by student tracking:
Provides real time information about students and various vehicles
Provides GPS safety and security to various kinds of vehicles
Provides automated SMS notification to parents.
Generate various kinds of report related to Management Information system.
Various data of students, Parents, Vehicle can be easily stored.
Students can easily make use of smart cards for various kinds of purchase.
Parents can easily have information related to statement of purchase.
Can easily provide school fees payment information easily.
(a)(ii) Propose a design for a smart card that would be suitable for all listed uses, then
describe the processes involved in preparing, issuing, using and terminating the cards. [10]
Fig 2: Sample Smart Card for students
The smart card should be prepared and issued by university. All the forthcoming stages
like preparing, issues and termination of card should be handled by university. A department
should be there to easily handle the above processes of smart card.
(a) (iii) Pick one of the listed uses and describe in detail how the card is practically used to
add security.
Ans: A smart card is nothing but a payment which is embedded with RFID technology and
function. The smart card can easily add benefit to students by student tracking:
Provides real time information about students and various vehicles
Provides GPS safety and security to various kinds of vehicles
Provides automated SMS notification to parents.
Generate various kinds of report related to Management Information system.
Various data of students, Parents, Vehicle can be easily stored.
Students can easily make use of smart cards for various kinds of purchase.
Parents can easily have information related to statement of purchase.
Can easily provide school fees payment information easily.

32SMART CARDS
Student can easily get books and other kinds of utilities from various kinds of
information.
Student can easily get books and other kinds of utilities from various kinds of
information.
33SMART CARDS
References:
Abaza, A., Ross, A., Hebert, C., Harrison, M. A. F., & Nixon, M. S. (2013). A survey on ear
biometrics. ACM computing surveys (CSUR), 45(2), 22.
Ahson, S. A., & Ilyas, M. (2017). RFID handbook: applications, technology, security, and
privacy. CRC press.
Akram, R. N., Markantonakis, K., & Mayes, K. (2013, July). A secure and trusted channel
protocol for the user centric smart card ownership model. In Trust, Security and Privacy
in Computing and Communications (TrustCom), 2013 12th IEEE International
Conference on (pp. 336-345). IEEE.
Akram, R. N., Markantonakis, K., & Mayes, K. (2014, March). Trusted platform module for
smart cards. In New Technologies, Mobility and Security (NTMS), 2014 6th International
Conference on (pp. 1-5). IEEE.
Amendola, S., Lodato, R., Manzari, S., Occhiuzzi, C., & Marrocco, G. (2014). RFID technology
for IoT-based personal healthcare in smart spaces. IEEE Internet of things journal, 1(2),
144-152.
Arthur, W., & Challener, D. (2015). A Practical Guide to TPM 2.0: Using the Trusted Platform
Module in the New Age of Security. Apress.
Bernstein, D. J., Chang, Y. A., Cheng, C. M., Chou, L. P., Heninger, N., Lange, T., & Van
Someren, N. (2013, December). Factoring RSA keys from certified smart cards:
Coppersmith in the wild. In International Conference on the Theory and Application of
Cryptology and Information Security(pp. 341-360). Springer, Berlin, Heidelberg.
Bo, C., Zhang, L., Li, X. Y., Huang, Q., & Wang, Y. (2013, September). Silentsense: silent user
identification via touch and movement behavioral biometrics. In Proceedings of the 19th
References:
Abaza, A., Ross, A., Hebert, C., Harrison, M. A. F., & Nixon, M. S. (2013). A survey on ear
biometrics. ACM computing surveys (CSUR), 45(2), 22.
Ahson, S. A., & Ilyas, M. (2017). RFID handbook: applications, technology, security, and
privacy. CRC press.
Akram, R. N., Markantonakis, K., & Mayes, K. (2013, July). A secure and trusted channel
protocol for the user centric smart card ownership model. In Trust, Security and Privacy
in Computing and Communications (TrustCom), 2013 12th IEEE International
Conference on (pp. 336-345). IEEE.
Akram, R. N., Markantonakis, K., & Mayes, K. (2014, March). Trusted platform module for
smart cards. In New Technologies, Mobility and Security (NTMS), 2014 6th International
Conference on (pp. 1-5). IEEE.
Amendola, S., Lodato, R., Manzari, S., Occhiuzzi, C., & Marrocco, G. (2014). RFID technology
for IoT-based personal healthcare in smart spaces. IEEE Internet of things journal, 1(2),
144-152.
Arthur, W., & Challener, D. (2015). A Practical Guide to TPM 2.0: Using the Trusted Platform
Module in the New Age of Security. Apress.
Bernstein, D. J., Chang, Y. A., Cheng, C. M., Chou, L. P., Heninger, N., Lange, T., & Van
Someren, N. (2013, December). Factoring RSA keys from certified smart cards:
Coppersmith in the wild. In International Conference on the Theory and Application of
Cryptology and Information Security(pp. 341-360). Springer, Berlin, Heidelberg.
Bo, C., Zhang, L., Li, X. Y., Huang, Q., & Wang, Y. (2013, September). Silentsense: silent user
identification via touch and movement behavioral biometrics. In Proceedings of the 19th
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
34SMART CARDS
annual international conference on Mobile computing & networking (pp. 187-190).
ACM.
Bowyer, K. W., Hollingsworth, K. P., & Flynn, P. J. (2016). A survey of iris biometrics research:
2008–2010. In Handbook of iris recognition (pp. 23-61). Springer, London.
Chae, H. J., Salajegheh, M., Yeager, D. J., Smith, J. R., & Fu, K. (2013). Maximalist
cryptography and computation on the WISP UHF RFID tag. In Wirelessly Powered
Sensor Networks and Computational RFID (pp. 175-187). Springer, New York, NY.
Chuang, M. C., & Chen, M. C. (2014). An anonymous multi-server authenticated key agreement
scheme based on trust computing using smart cards and biometrics. Expert Systems with
Applications, 41(4), 1411-1418.
Ekberg, J. E., Kostiainen, K., & Asokan, N. (2013, November). Trusted execution environments
on mobile devices. In Proceedings of the 2013 ACM SIGSAC conference on Computer &
communications security (pp. 1497-1498). ACM.
Ekberg, J. E., Kostiainen, K., & Asokan, N. (2014). The untapped potential of trusted execution
environments on mobile devices. IEEE Security & Privacy, 12(4), 29-37.
Galbally, J., Diaz-Cabrera, M., Ferrer, M. A., Gomez-Barrero, M., Morales, A., & Fierrez, J.
(2015). On-line signature recognition through the combination of real dynamic data and
synthetically generated static data. Pattern Recognition, 48(9), 2921-2934.
Gruss, D., Maurice, C., & Mangard, S. (2016, July). Rowhammer. js: A remote software-induced
fault attack in javascript. In International Conference on Detection of Intrusions and
Malware, and Vulnerability Assessment (pp. 300-321). Springer, Cham.
annual international conference on Mobile computing & networking (pp. 187-190).
ACM.
Bowyer, K. W., Hollingsworth, K. P., & Flynn, P. J. (2016). A survey of iris biometrics research:
2008–2010. In Handbook of iris recognition (pp. 23-61). Springer, London.
Chae, H. J., Salajegheh, M., Yeager, D. J., Smith, J. R., & Fu, K. (2013). Maximalist
cryptography and computation on the WISP UHF RFID tag. In Wirelessly Powered
Sensor Networks and Computational RFID (pp. 175-187). Springer, New York, NY.
Chuang, M. C., & Chen, M. C. (2014). An anonymous multi-server authenticated key agreement
scheme based on trust computing using smart cards and biometrics. Expert Systems with
Applications, 41(4), 1411-1418.
Ekberg, J. E., Kostiainen, K., & Asokan, N. (2013, November). Trusted execution environments
on mobile devices. In Proceedings of the 2013 ACM SIGSAC conference on Computer &
communications security (pp. 1497-1498). ACM.
Ekberg, J. E., Kostiainen, K., & Asokan, N. (2014). The untapped potential of trusted execution
environments on mobile devices. IEEE Security & Privacy, 12(4), 29-37.
Galbally, J., Diaz-Cabrera, M., Ferrer, M. A., Gomez-Barrero, M., Morales, A., & Fierrez, J.
(2015). On-line signature recognition through the combination of real dynamic data and
synthetically generated static data. Pattern Recognition, 48(9), 2921-2934.
Gruss, D., Maurice, C., & Mangard, S. (2016, July). Rowhammer. js: A remote software-induced
fault attack in javascript. In International Conference on Detection of Intrusions and
Malware, and Vulnerability Assessment (pp. 300-321). Springer, Cham.
35SMART CARDS
Gubbi, J., Buyya, R., Marusic, S., & Palaniswami, M. (2013). Internet of Things (IoT): A vision,
architectural elements, and future directions. Future generation computer systems, 29(7),
1645-1660.
Haghighat, M., Zonouz, S., & Abdel-Mottaleb, M. (2013, August). Identification using
encrypted biometrics. In International Conference on Computer Analysis of Images and
Patterns (pp. 440-448). Springer, Berlin, Heidelberg.
Hanwate, A., & Thakare, P. (2015). SMART TROLLEY USING RFID. International Journal of
Research In Science and Engineering e-ISSN, 2394-8299.
He, D., & Wang, D. (2015). Robust biometrics-based authentication scheme for multiserver
environment. IEEE Systems Journal, 9(3), 816-823.
Jang, J. S., Kong, S., Kim, M., Kim, D., & Kang, B. B. (2015, February). SeCReT: Secure
Channel between Rich Execution Environment and Trusted Execution Environment.
In NDSS.
Karaklajić, D., Schmidt, J. M., & Verbauwhede, I. (2013). Hardware designer's guide to fault
attacks. IEEE Transactions on Very Large Scale Integration (VLSI) Systems, 21(12),
2295-2306.
Kelly, S. D. T., Suryadevara, N. K., & Mukhopadhyay, S. C. (2013). Towards the
implementation of IoT for environmental condition monitoring in homes. IEEE Sensors
Journal, 13(10), 3846-3853.
Lee, I., & Lee, K. (2015). The Internet of Things (IoT): Applications, investments, and
challenges for enterprises. Business Horizons, 58(4), 431-440.
Gubbi, J., Buyya, R., Marusic, S., & Palaniswami, M. (2013). Internet of Things (IoT): A vision,
architectural elements, and future directions. Future generation computer systems, 29(7),
1645-1660.
Haghighat, M., Zonouz, S., & Abdel-Mottaleb, M. (2013, August). Identification using
encrypted biometrics. In International Conference on Computer Analysis of Images and
Patterns (pp. 440-448). Springer, Berlin, Heidelberg.
Hanwate, A., & Thakare, P. (2015). SMART TROLLEY USING RFID. International Journal of
Research In Science and Engineering e-ISSN, 2394-8299.
He, D., & Wang, D. (2015). Robust biometrics-based authentication scheme for multiserver
environment. IEEE Systems Journal, 9(3), 816-823.
Jang, J. S., Kong, S., Kim, M., Kim, D., & Kang, B. B. (2015, February). SeCReT: Secure
Channel between Rich Execution Environment and Trusted Execution Environment.
In NDSS.
Karaklajić, D., Schmidt, J. M., & Verbauwhede, I. (2013). Hardware designer's guide to fault
attacks. IEEE Transactions on Very Large Scale Integration (VLSI) Systems, 21(12),
2295-2306.
Kelly, S. D. T., Suryadevara, N. K., & Mukhopadhyay, S. C. (2013). Towards the
implementation of IoT for environmental condition monitoring in homes. IEEE Sensors
Journal, 13(10), 3846-3853.
Lee, I., & Lee, K. (2015). The Internet of Things (IoT): Applications, investments, and
challenges for enterprises. Business Horizons, 58(4), 431-440.
36SMART CARDS
Koeberl, P., Schulz, S., Sadeghi, A. R., & Varadharajan, V. (2014, April). TrustLite: A security
architecture for tiny embedded devices. In Proceedings of the Ninth European
Conference on Computer Systems (p. 10). ACM.
McGill, K. N. (2013). Trusted mobile devices: Requirements for a mobile trusted platform
module. Johns hopkins apl technical digest, 32(2), 544-554.
Miao, C., Jiang, W., Su, L., Li, Y., Guo, S., Qin, Z., ... & Ren, K. (2015, November). Cloud-
enabled privacy-preserving truth discovery in crowd sensing systems. In Proceedings of
the 13th ACM Conference on Embedded Networked Sensor Systems (pp. 183-196). ACM.
Osborn, J. D., & Challener, D. C. (2013). Trusted platform Module evolution. Johns Hopkins
APL Technical Digest (Applied Physics Laboratory), 32(2), 536-543.
Roland, M., & Langer, J. (2013, August). Cloning Credit Cards: A Combined Pre-play and
Downgrade Attack on EMV Contactless. In WOOT.
Shekhar, S., Patel, V. M., Nasrabadi, N. M., & Chellappa, R. (2014). Joint sparse representation
for robust multimodal biometrics recognition. IEEE Transactions on Pattern Analysis
and Machine Intelligence, 36(1), 113-126.
Smith, S. W. (2013). Trusted computing platforms: design and applications. Springer.
Teh, P. S., Teoh, A. B. J., & Yue, S. (2013). A survey of keystroke dynamics biometrics. The
Scientific World Journal, 2013.
Tomlinson, A. (2017). Introduction to the TPM. In Smart Cards, Tokens, Security and
Applications (pp. 173-191). Springer, Cham.
Zhong, R. Y., Dai, Q. Y., Qu, T., Hu, G. J., & Huang, G. Q. (2013). RFID-enabled real-time
manufacturing execution system for mass-customization production. Robotics and
Computer-Integrated Manufacturing, 29(2), 283-292.
Koeberl, P., Schulz, S., Sadeghi, A. R., & Varadharajan, V. (2014, April). TrustLite: A security
architecture for tiny embedded devices. In Proceedings of the Ninth European
Conference on Computer Systems (p. 10). ACM.
McGill, K. N. (2013). Trusted mobile devices: Requirements for a mobile trusted platform
module. Johns hopkins apl technical digest, 32(2), 544-554.
Miao, C., Jiang, W., Su, L., Li, Y., Guo, S., Qin, Z., ... & Ren, K. (2015, November). Cloud-
enabled privacy-preserving truth discovery in crowd sensing systems. In Proceedings of
the 13th ACM Conference on Embedded Networked Sensor Systems (pp. 183-196). ACM.
Osborn, J. D., & Challener, D. C. (2013). Trusted platform Module evolution. Johns Hopkins
APL Technical Digest (Applied Physics Laboratory), 32(2), 536-543.
Roland, M., & Langer, J. (2013, August). Cloning Credit Cards: A Combined Pre-play and
Downgrade Attack on EMV Contactless. In WOOT.
Shekhar, S., Patel, V. M., Nasrabadi, N. M., & Chellappa, R. (2014). Joint sparse representation
for robust multimodal biometrics recognition. IEEE Transactions on Pattern Analysis
and Machine Intelligence, 36(1), 113-126.
Smith, S. W. (2013). Trusted computing platforms: design and applications. Springer.
Teh, P. S., Teoh, A. B. J., & Yue, S. (2013). A survey of keystroke dynamics biometrics. The
Scientific World Journal, 2013.
Tomlinson, A. (2017). Introduction to the TPM. In Smart Cards, Tokens, Security and
Applications (pp. 173-191). Springer, Cham.
Zhong, R. Y., Dai, Q. Y., Qu, T., Hu, G. J., & Huang, G. Q. (2013). RFID-enabled real-time
manufacturing execution system for mass-customization production. Robotics and
Computer-Integrated Manufacturing, 29(2), 283-292.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

37SMART CARDS
1 out of 38
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
© 2024 | Zucol Services PVT LTD | All rights reserved.