Create and Delete Files on USB Drive: Data Acquisition, Recovery, Analysis and Validation
Added on 2023-06-07
14 Pages1404 Words192 Views
0

Table of Contents
1. Case Study I: Create and Delete Files on USB Drive......................................................................................2
1. Data Acquisition.......................................................................................................................................2
2. Data Recovery..........................................................................................................................................3
3. Data Analysis...........................................................................................................................................5
4. Data Validation......................................................................................................................................10
2. Case Study II: Investing a Case....................................................................................................................11
References...........................................................................................................................................................12
1. Case Study I: Create and Delete Files on USB Drive......................................................................................2
1. Data Acquisition.......................................................................................................................................2
2. Data Recovery..........................................................................................................................................3
3. Data Analysis...........................................................................................................................................5
4. Data Validation......................................................................................................................................10
2. Case Study II: Investing a Case....................................................................................................................11
References...........................................................................................................................................................12
1. Case Study I: Create and Delete Files on USB Drive
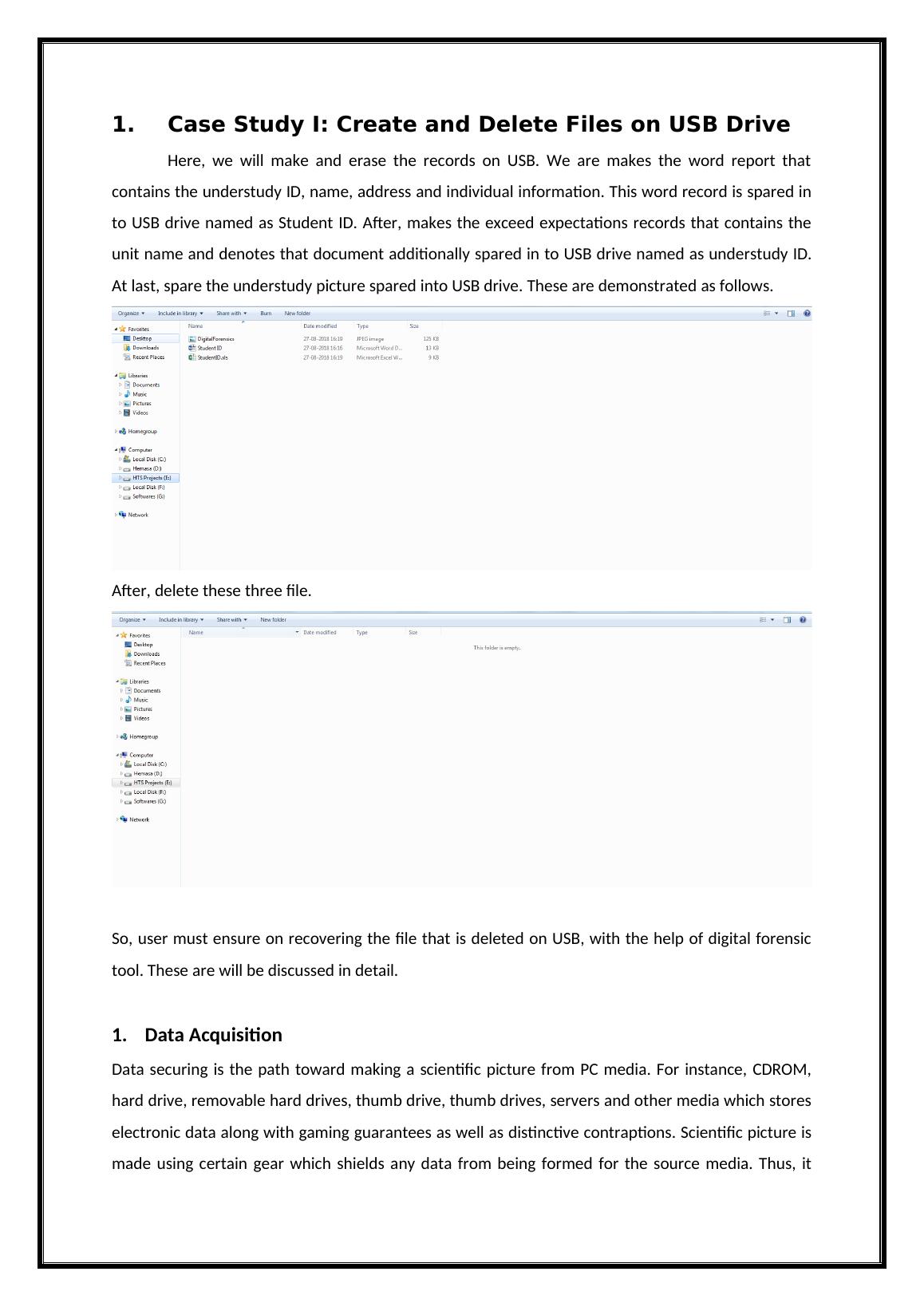
Here, we will make and erase the records on USB. We are makes the word report that
contains the understudy ID, name, address and individual information. This word record is spared in
to USB drive named as Student ID. After, makes the exceed expectations records that contains the
unit name and denotes that document additionally spared in to USB drive named as understudy ID.
At last, spare the understudy picture spared into USB drive. These are demonstrated as follows.
After, delete these three file.
So, user must ensure on recovering the file that is deleted on USB, with the help of digital forensic
tool. These are will be discussed in detail.
1. Data Acquisition
Data securing is the path toward making a scientific picture from PC media. For instance, CDROM,
hard drive, removable hard drives, thumb drive, thumb drives, servers and other media which stores
electronic data along with gaming guarantees as well as distinctive contraptions. Scientific picture is
made using certain gear which shields any data from being formed for the source media. Thus, it
Here, we will make and erase the records on USB. We are makes the word report that
contains the understudy ID, name, address and individual information. This word record is spared in
to USB drive named as Student ID. After, makes the exceed expectations records that contains the
unit name and denotes that document additionally spared in to USB drive named as understudy ID.
At last, spare the understudy picture spared into USB drive. These are demonstrated as follows.
After, delete these three file.
So, user must ensure on recovering the file that is deleted on USB, with the help of digital forensic
tool. These are will be discussed in detail.
1. Data Acquisition
Data securing is the path toward making a scientific picture from PC media. For instance, CDROM,
hard drive, removable hard drives, thumb drive, thumb drives, servers and other media which stores
electronic data along with gaming guarantees as well as distinctive contraptions. Scientific picture is
made using certain gear which shields any data from being formed for the source media. Thus, it
remains consummate. Criminological picture, not the primary media, is used by the legal analyst for
leading examination. The data getting process fuses the record of each serial number and distinctive
markings using a propelled camera. Measurable picture is affirmed against the first to ensure the
criminological picture is a right duplicate of the primary media. To do data securing by utilizing the
star find fundamental device. The prodiscover legal sciences device is most intense PC security
instrument that used to empower the criminology agent to decide the every one of the data on the
PC framework while ensuring the proof and making the evidentiary quality reports. This device has
different highlights and advantages, for example,
It makes the bit stream duplicate of circle to be dissected to protect the first
confirmation.
It effectively look through the whole circle and records including the PC data streams
which is utilized for finish plate scientific investigation [1].
It keep up the multi instrument similarity by composing and perusing the pictures.
It inspect the PC document to give the data uprightness.
It additionally analyse the all record frameworks for most extreme adaptability.
It used the Perl contents to mechanize the examination undertakings.
It personality the record makers to separates the EXIF data from JPEG documents.
It enhances the similarity and precision via robotized the report age in XML design.
It intended to NIST plate imaging instrument to guarantee the high calibre.
It bolster for VM product to run a caught pictures.
2. Data Recovery
Open Pro discover basic Tool.
leading examination. The data getting process fuses the record of each serial number and distinctive
markings using a propelled camera. Measurable picture is affirmed against the first to ensure the
criminological picture is a right duplicate of the primary media. To do data securing by utilizing the
star find fundamental device. The prodiscover legal sciences device is most intense PC security
instrument that used to empower the criminology agent to decide the every one of the data on the
PC framework while ensuring the proof and making the evidentiary quality reports. This device has
different highlights and advantages, for example,
It makes the bit stream duplicate of circle to be dissected to protect the first
confirmation.
It effectively look through the whole circle and records including the PC data streams
which is utilized for finish plate scientific investigation [1].
It keep up the multi instrument similarity by composing and perusing the pictures.
It inspect the PC document to give the data uprightness.
It additionally analyse the all record frameworks for most extreme adaptability.
It used the Perl contents to mechanize the examination undertakings.
It personality the record makers to separates the EXIF data from JPEG documents.
It enhances the similarity and precision via robotized the report age in XML design.
It intended to NIST plate imaging instrument to guarantee the high calibre.
It bolster for VM product to run a caught pictures.
2. Data Recovery
Open Pro discover basic Tool.
End of preview
Want to access all the pages? Upload your documents or become a member.
Related Documents
DIGITAL EVIDENCE CASE STUDY 2022lg...
|4
|582
|22
Digital Forensics Report for Scrambled Bits Recoverylg...
|14
|2446
|219
Developments in Mobile Device Evidence and Investigationlg...
|16
|3343
|98
Digital Forensic Collection of Data from a Specific Devicelg...
|15
|1369
|94
