Digital Forensics - Assignments
39 Pages3425 Words103 Views
Added on 2020-03-23
Digital Forensics - Assignments
Added on 2020-03-23
ShareRelated Documents
ELECTRONICCRIME
Table of Contents1.Introduction........................................................................................................................................22.Digital Forensics Tools........................................................................................................................22.1FTK.............................................................................................................................................22.2Sluethkit.......................................................................................................................................82.3Autopsy.....................................................................................................................................182.4Volatility....................................................................................................................................202.5OSForensics...............................................................................................................................223.Usage of OS Forensics to examine USB, RAM dumps and Hard disk........................................233.1Using OS Forensics to investigates USB drive.........................................................................233.2Using OS Forensics to investigates RAM dumps.....................................................................253.3Using OS Forensics to investigates Hard disk images...............................................................294.Flow and details of investigation....................................................................................................304.1Section 1....................................................................................................................................304.1.1Part A.................................................................................................................................304.1.2Part B.................................................................................................................................324.2Section 2....................................................................................................................................334.2.1Part A.................................................................................................................................334.2.2Part B.....................................................................................................................................344.3Section 3....................................................................................................................................344.3.1Part A.................................................................................................................................344.3.2Part B.................................................................................................................................354.4Investigation results...................................................................................................................354Conclusion........................................................................................................................................37References................................................................................................................................................382
1.IntroductionThe main objective of the project is To find out crimes on the system such as hiding files, tracking someone credentials.To find out the spyTo identify the specific methods or the software used for facilitating.To find out the reason for spyingTo find out whether any other person is involved in it and to finally characterize them.2.Digital Forensics ToolsOSForensics , FTK , SleuthKit , autopsy , ProDiscover Basic , Volatility are usual and famous tools for forensic investigation.2.1FTKDESCRIPTIONThe abbreviation of FTK is "Forensic Toolkit" which is used for investigation purposes isa simple and faster tool. It does scans the hard drive and gives the variety of information. It is asoftware made by AccessData which is easy to use and reduces case backlog. FTK has thefeature to get the lost personal passwords and locate the deleted emails. It is easy to analyze andmakes the evidence effectively. FTK is database driven with stability and ease of use. Once thecase investigation is completed a report can be created regarding the evidence collected from thecase.3
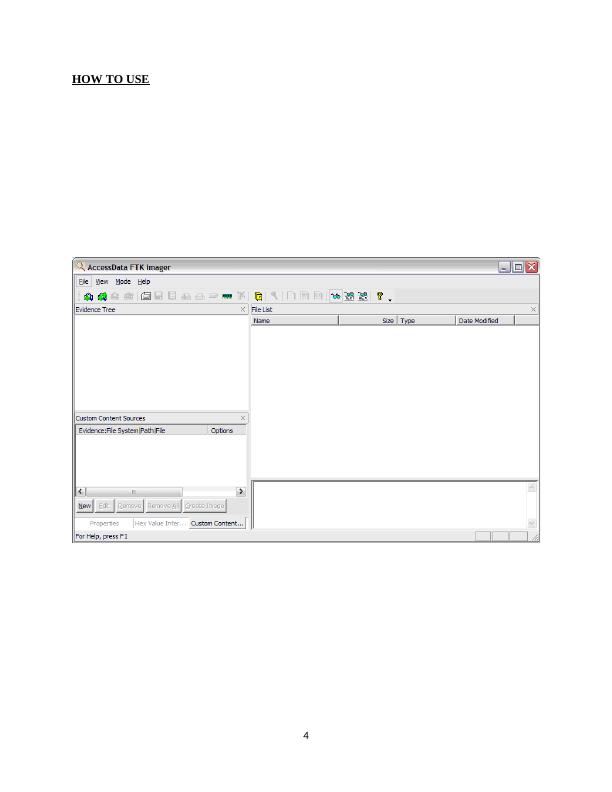
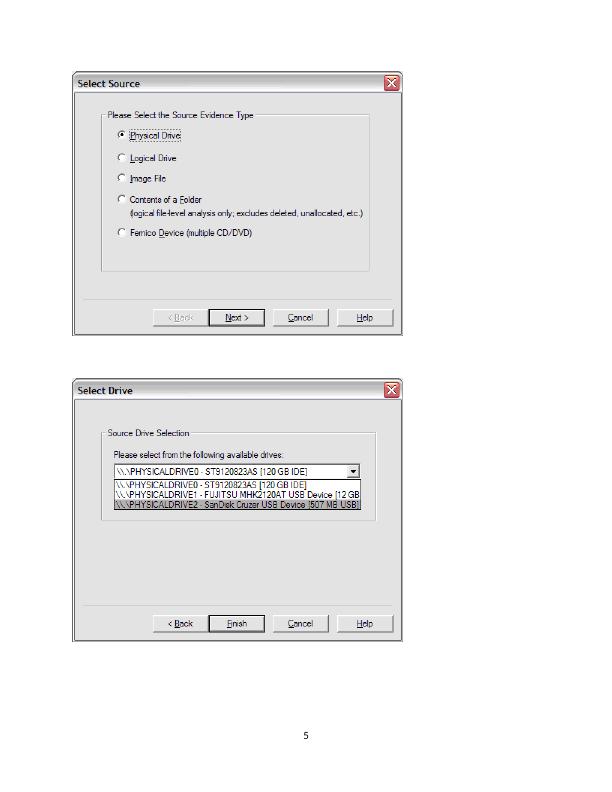
HOW TO USE4
5
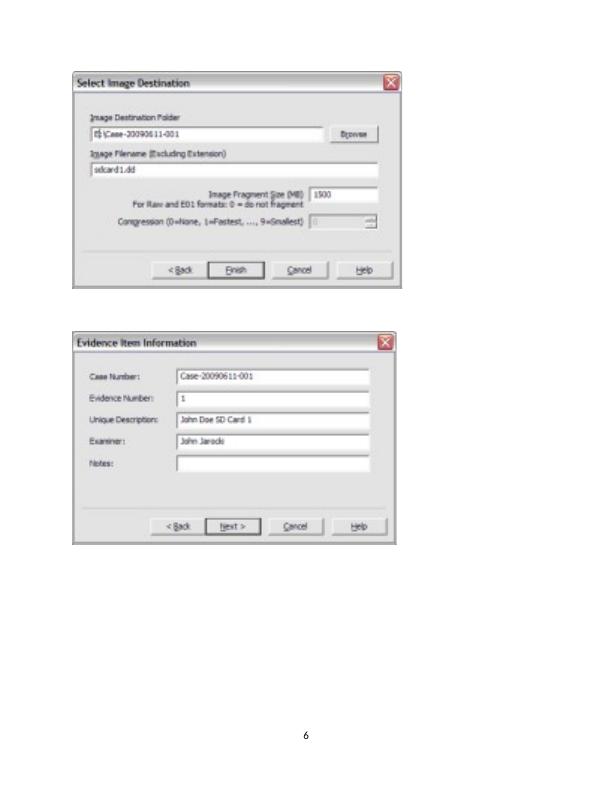
6
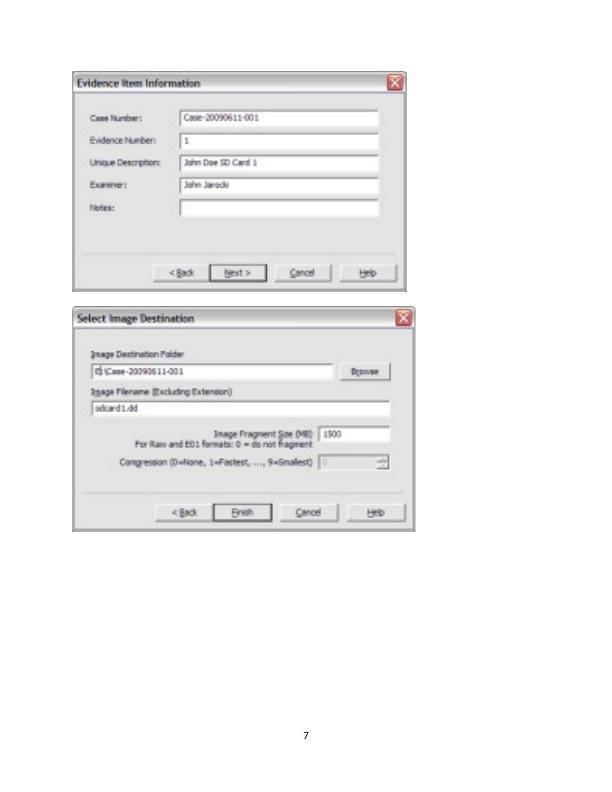
7
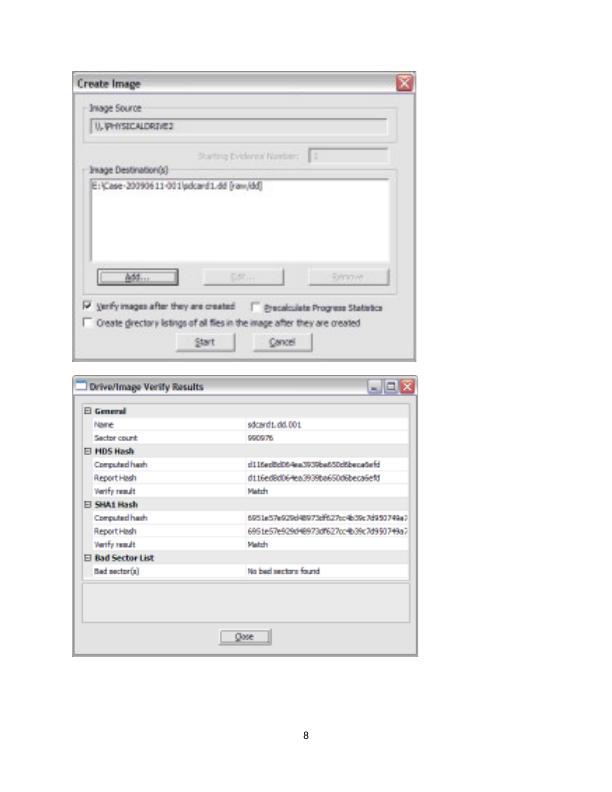
8
End of preview
Want to access all the pages? Upload your documents or become a member.
Related Documents
MN624 Digital Forensics - Assignmentlg...
|19
|1225
|41
Cyber Forensic and Information Technology Assignmentlg...
|28
|2755
|50
Computer Forensics Investigation on Clown Content Offence in Western Australialg...
|47
|6608
|329
Principles of Digital Forensics PDFlg...
|22
|1932
|375
(Solution) Digital Forensics : PDFlg...
|22
|2968
|39
Digital Forensic Project 2022lg...
|5
|740
|15
