VPN Network Design for SME - Network and VPN Services
VerifiedAdded on 2023/04/24
|15
|1437
|299
Presentation
AI Summary
This report discusses the design of a virtual private network for small and medium enterprises, including the scope, limitations, requirements, solution design, network topologies, IP addressing, security features and policies, redundancy and failover plans, and VPN service implementation.
Contribute Materials
Your contribution can guide someone’s learning journey. Share your
documents today.
VPN Network Design for SME
network and VPN services
NAME OF THE STUDENT
NAME OF THE UNIVERSITY
network and VPN services
NAME OF THE STUDENT
NAME OF THE UNIVERSITY
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
Introduction
A virtual private network is designed for a small and medium enterprise
after the analysis of the service requirement and the protocols used for
the development of a VPN network solution. An analysis is made on the
architecture that should be used for the development of the network
and a road map of the process is interpreted in the report for following
it and support the administrator for the management of the
development process of the project.
A virtual private network is designed for a small and medium enterprise
after the analysis of the service requirement and the protocols used for
the development of a VPN network solution. An analysis is made on the
architecture that should be used for the development of the network
and a road map of the process is interpreted in the report for following
it and support the administrator for the management of the
development process of the project.
Scope of the project
The scope of designing the VPN network design are as follows:
Use of secure authentication mechanism and changing password on regular
basis for increasing the security of VPN network
Selection of type of VPN depending on the requirement and structure of the
organization.
Bypassing the filtered and blocked websites and access all the websites and
services
Increasing the efficiency of bandwidth and network with the implementation of
VPN.
Reducing the cost of maintenance and communication for communicating with
the remote branches
The scope of designing the VPN network design are as follows:
Use of secure authentication mechanism and changing password on regular
basis for increasing the security of VPN network
Selection of type of VPN depending on the requirement and structure of the
organization.
Bypassing the filtered and blocked websites and access all the websites and
services
Increasing the efficiency of bandwidth and network with the implementation of
VPN.
Reducing the cost of maintenance and communication for communicating with
the remote branches
Limitation of the project
The limitation for designing the VPN network are as follows:
Understanding the installation and configuration of the security
issues of the network for ensuring sufficient protection is
implemented for the network
Ensuring reliability and performance for the internet based VPN and
application of sufficient protection for the organizational resources
Compatibility of the different VPN product with the equipment used
for the development of the network
Selection of the router and the transmission link for eliminating the
risk of slower VPN speed and testing it according to the requirement.
The limitation for designing the VPN network are as follows:
Understanding the installation and configuration of the security
issues of the network for ensuring sufficient protection is
implemented for the network
Ensuring reliability and performance for the internet based VPN and
application of sufficient protection for the organizational resources
Compatibility of the different VPN product with the equipment used
for the development of the network
Selection of the router and the transmission link for eliminating the
risk of slower VPN speed and testing it according to the requirement.
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
Requirements
There are different component that are needed for the development of
the network solution and there are different elements that are needed
for the management of the components. A client VPN software is
needed for establishment of secure connection with the remote branch.
The routers should be selected such that it have support of VPN and
firewalls should be deployed such that legitimate VPN traffic are
allowed to access the internal network of the organization. A VPN
server is needed to be installed in the network for management of the
session and management of the incoming data traffic for maintaining
access of the network resources. The channels used for communication
should be encrypted and the physical access of the VPN server should
be restricted for the management of high level security.
There are different component that are needed for the development of
the network solution and there are different elements that are needed
for the management of the components. A client VPN software is
needed for establishment of secure connection with the remote branch.
The routers should be selected such that it have support of VPN and
firewalls should be deployed such that legitimate VPN traffic are
allowed to access the internal network of the organization. A VPN
server is needed to be installed in the network for management of the
session and management of the incoming data traffic for maintaining
access of the network resources. The channels used for communication
should be encrypted and the physical access of the VPN server should
be restricted for the management of high level security.
Solution Design
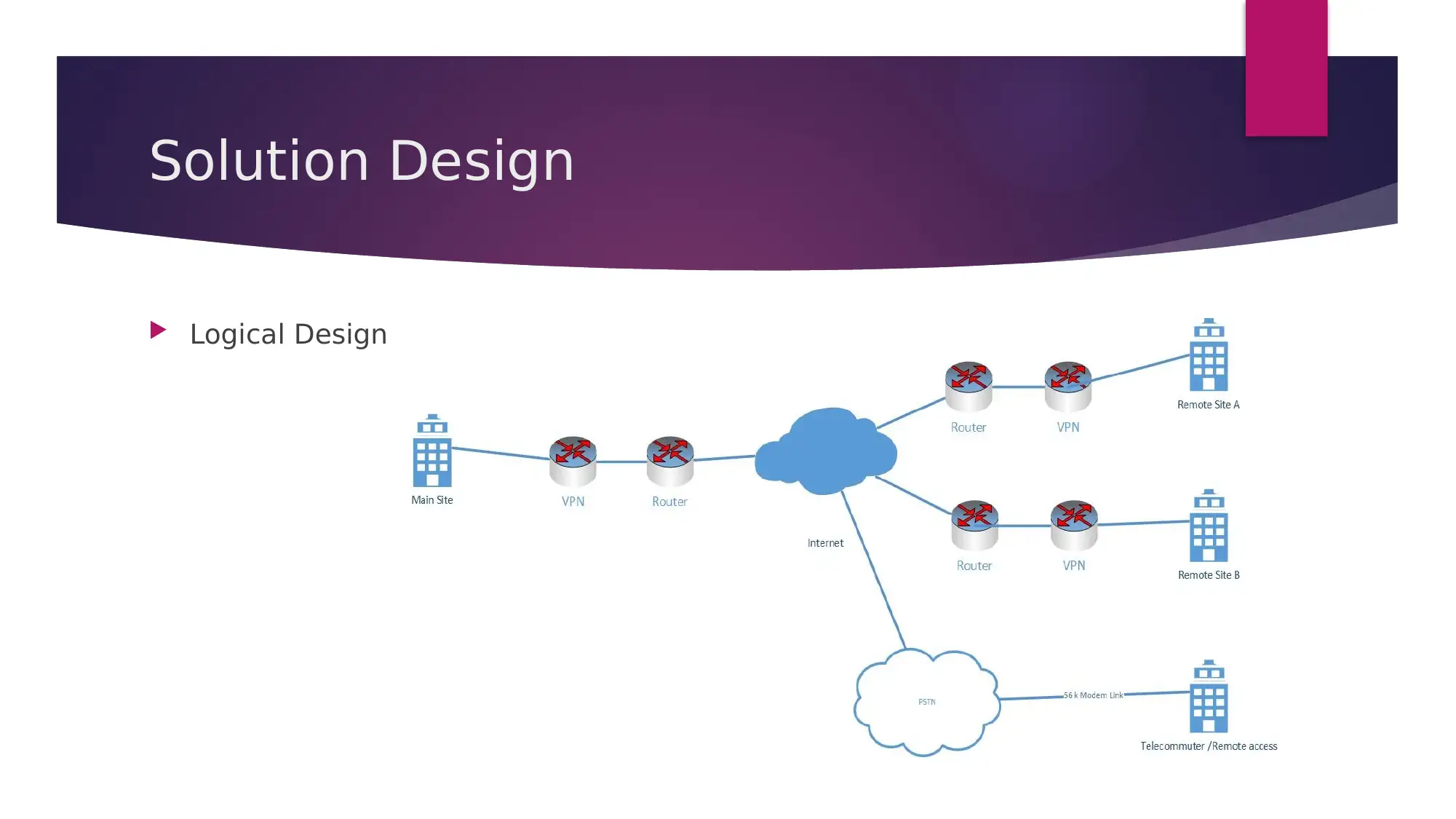
Logical Design
Logical Design
Solution Design
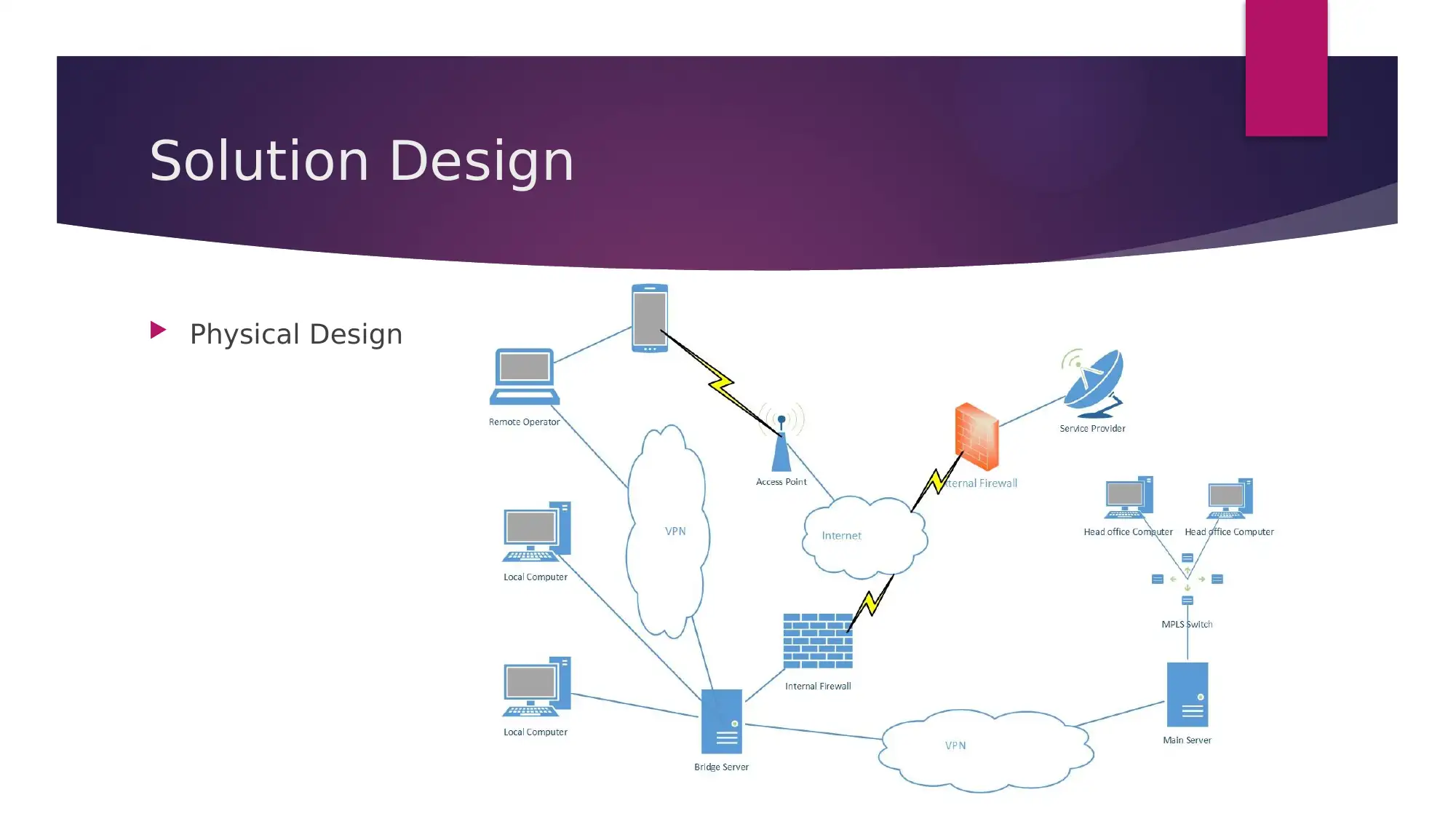
Physical Design
Physical Design
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Network Topologies
The network topology of the VPN network infrastructure is developed
with the use of public telecommunication network and the WAN is
extended from the core site to reach the branches of the network.
Proper encryption technique is applied and security procedure is
applied for keeping the data private. The implementation of VPN helps
in enabling the company to share distributed data and application
without much expense. Dedicated leased lines are not needed for
transmitting the data packets and internet can be used for serving the
needs of the users and improve the performance of the organization.
There are different network monitoring tools that can be applied for the
identification of flow of data packet and the selection of the topology.
The network topology of the VPN network infrastructure is developed
with the use of public telecommunication network and the WAN is
extended from the core site to reach the branches of the network.
Proper encryption technique is applied and security procedure is
applied for keeping the data private. The implementation of VPN helps
in enabling the company to share distributed data and application
without much expense. Dedicated leased lines are not needed for
transmitting the data packets and internet can be used for serving the
needs of the users and improve the performance of the organization.
There are different network monitoring tools that can be applied for the
identification of flow of data packet and the selection of the topology.
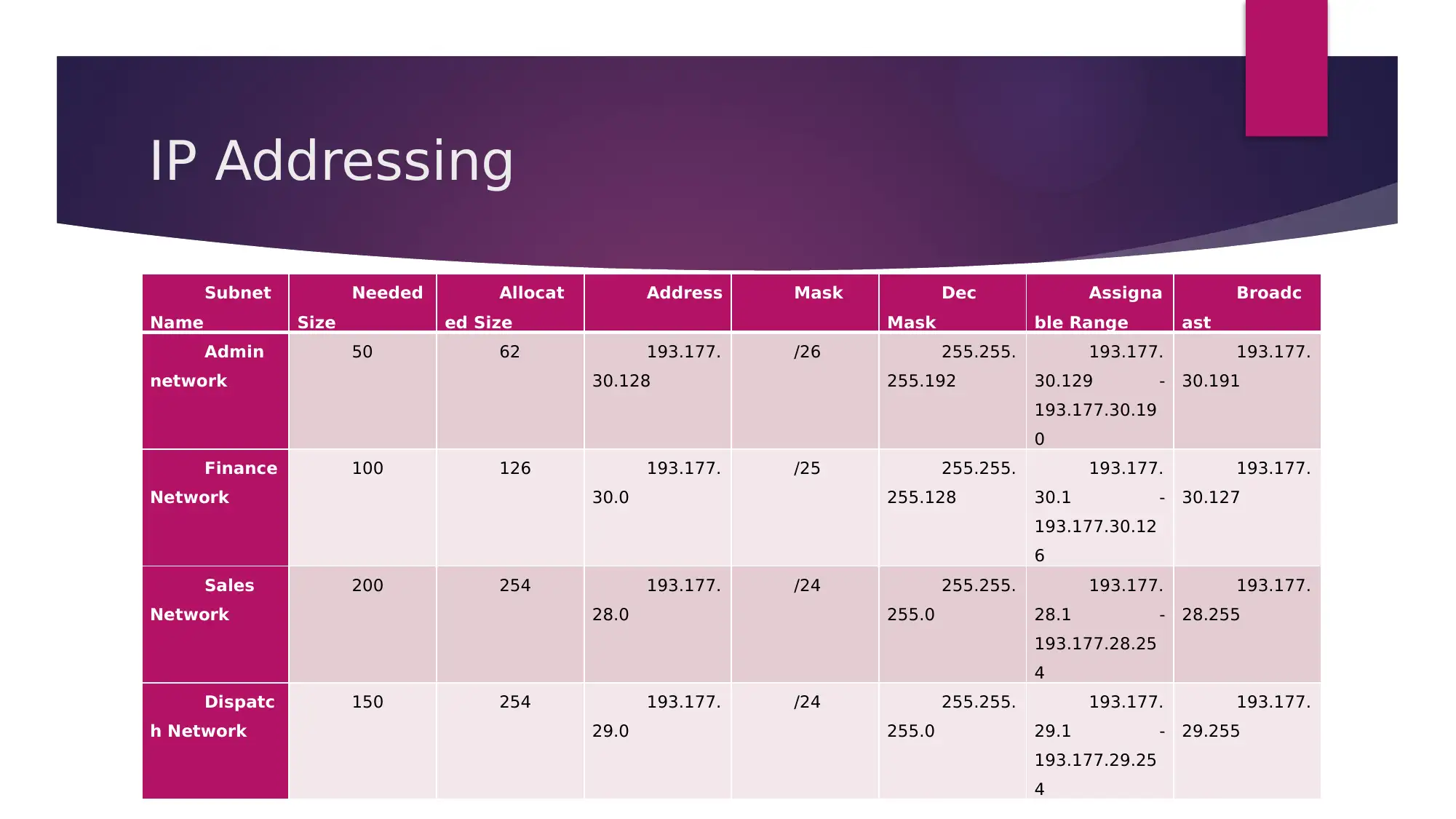
IP Addressing
Subnet
Name
Needed
Size
Allocat
ed Size
Address Mask Dec
Mask
Assigna
ble Range
Broadc
ast
Admin
network
50 62 193.177.
30.128
/26 255.255.
255.192
193.177.
30.129 -
193.177.30.19
0
193.177.
30.191
Finance
Network
100 126 193.177.
30.0
/25 255.255.
255.128
193.177.
30.1 -
193.177.30.12
6
193.177.
30.127
Sales
Network
200 254 193.177.
28.0
/24 255.255.
255.0
193.177.
28.1 -
193.177.28.25
4
193.177.
28.255
Dispatc
h Network
150 254 193.177.
29.0
/24 255.255.
255.0
193.177.
29.1 -
193.177.29.25
4
193.177.
29.255
Subnet
Name
Needed
Size
Allocat
ed Size
Address Mask Dec
Mask
Assigna
ble Range
Broadc
ast
Admin
network
50 62 193.177.
30.128
/26 255.255.
255.192
193.177.
30.129 -
193.177.30.19
0
193.177.
30.191
Finance
Network
100 126 193.177.
30.0
/25 255.255.
255.128
193.177.
30.1 -
193.177.30.12
6
193.177.
30.127
Sales
Network
200 254 193.177.
28.0
/24 255.255.
255.0
193.177.
28.1 -
193.177.28.25
4
193.177.
28.255
Dispatc
h Network
150 254 193.177.
29.0
/24 255.255.
255.0
193.177.
29.1 -
193.177.29.25
4
193.177.
29.255
Security features and policies
The following are the security implication that can be applied for
increasing the security of the VPN network.
The connection of VPN can be strengthened with the deployment of
firewall
An IDP or IPS system can be deployed for monitoring the attack and
increasing the efficiency of the system
The remote client should be installed with Antivirus software for
prevention of spread of virus in the network
The logging of the user into the server should be managed and auditing
function should be implemented for recording the unauthorized
attempts and reviewing the vulnerability of the network.
The following are the security implication that can be applied for
increasing the security of the VPN network.
The connection of VPN can be strengthened with the deployment of
firewall
An IDP or IPS system can be deployed for monitoring the attack and
increasing the efficiency of the system
The remote client should be installed with Antivirus software for
prevention of spread of virus in the network
The logging of the user into the server should be managed and auditing
function should be implemented for recording the unauthorized
attempts and reviewing the vulnerability of the network.
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
Redundancy and failover plans
The servers should be connected via redundant link for the
management of the network loads and reduce the risk of
unavailability due to failure of link. The data traffic in the network is
needed to be managed and the servers should have support for
virtualization such that it can be used for serving more number of
users [2]. A regular backup of the network should be performed and
stored in remote location such that it can be used for restoring the
network in case of disaster and no data is lost. A power backup plan
should also be created such that the situation of power outrages can
be handled and the uptime of the network is increased.
The servers should be connected via redundant link for the
management of the network loads and reduce the risk of
unavailability due to failure of link. The data traffic in the network is
needed to be managed and the servers should have support for
virtualization such that it can be used for serving more number of
users [2]. A regular backup of the network should be performed and
stored in remote location such that it can be used for restoring the
network in case of disaster and no data is lost. A power backup plan
should also be created such that the situation of power outrages can
be handled and the uptime of the network is increased.
VPN service implementation
Remote access VPN – This is used for connecting a remote user using mobile or home
network to connect with the private network of the organization. The VPN is used for permitting
secured, encrypted connectivity between the private network and remote users.
Intranet VPN – This type of VPN is created for establishing connection between two fixed
location and it can be branch to branch, head office to branch, etc. This protocol is used for
joining multiple remote location and work as a single private network.
Extranet VPN – It is used for connecting the business partner of the organization for example
customer, supplier and allow the user to work with other parties and securely share data in the
shared environment.
WAN replacement – VPN can be used as an alternative to WAN because the maintenance cost
of WAN is much higher specially in case of network dispersed over a larger geographical area. A
less cost is required for VPN because the overhead cost for management of WAN is higher and
the scalability is higher. The reliability and performance of the network can be improved with
the implementation of VPN and creating a tunnel for communication via the internet.
Remote access VPN – This is used for connecting a remote user using mobile or home
network to connect with the private network of the organization. The VPN is used for permitting
secured, encrypted connectivity between the private network and remote users.
Intranet VPN – This type of VPN is created for establishing connection between two fixed
location and it can be branch to branch, head office to branch, etc. This protocol is used for
joining multiple remote location and work as a single private network.
Extranet VPN – It is used for connecting the business partner of the organization for example
customer, supplier and allow the user to work with other parties and securely share data in the
shared environment.
WAN replacement – VPN can be used as an alternative to WAN because the maintenance cost
of WAN is much higher specially in case of network dispersed over a larger geographical area. A
less cost is required for VPN because the overhead cost for management of WAN is higher and
the scalability is higher. The reliability and performance of the network can be improved with
the implementation of VPN and creating a tunnel for communication via the internet.
Conclusion
It can be concluded that it is essential to identify the scope and limitation of
the project for identification of errors and resolving it before deployment of
the network framework. The requirement of the organization is needed to be
analyzed such that it helps in analyzing the VPN parts and service essential
for the development of the project. The network topology that should be
followed for the development of the network is needed to be identified and an
IP addressing plan is created for the configuration of the network interface of
the hardware device essential for the development of the network framework.
AN analysis is made on the security requirement of the organization and a
security feature and policy is applied to the network for increasing the
security of the network. A redundancy and failover plan is created for
increasing the availability of the network and provide service to the users.
It can be concluded that it is essential to identify the scope and limitation of
the project for identification of errors and resolving it before deployment of
the network framework. The requirement of the organization is needed to be
analyzed such that it helps in analyzing the VPN parts and service essential
for the development of the project. The network topology that should be
followed for the development of the network is needed to be identified and an
IP addressing plan is created for the configuration of the network interface of
the hardware device essential for the development of the network framework.
AN analysis is made on the security requirement of the organization and a
security feature and policy is applied to the network for increasing the
security of the network. A redundancy and failover plan is created for
increasing the availability of the network and provide service to the users.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Bibliography
[1]. Aguado, Alejandro, et al. "VPN Service Provisioning via Virtual Router Deployment and
Quantum Key Distribution." 2018 Optical Fiber Communications Conference and Exposition (OFC).
IEEE, 2018.
[2]. Aznar, José, et al. "CNSMO: A Network Services Manager/Orchestrator tool for cloud
federated environments." Ad Hoc Networking Workshop (Med-Hoc-Net), 2016 Mediterranean. IEEE,
2016.
[3]. Baranda, Jorge, et al. "Orchestration of end-to-end network services in the 5G-Crosshaul
multi-domain multi-technology transport network." IEEE Communications Magazine 56.7 (2018):
184-191.
[4]. Baucke, Stephan, et al. "Cloud API support for self-service Virtual Network Function (VNF)
deployment." Network Function Virtualization and Software Defined Network (NFV-SDN), 2015 IEEE
Conference on. IEEE, 2015.
[1]. Aguado, Alejandro, et al. "VPN Service Provisioning via Virtual Router Deployment and
Quantum Key Distribution." 2018 Optical Fiber Communications Conference and Exposition (OFC).
IEEE, 2018.
[2]. Aznar, José, et al. "CNSMO: A Network Services Manager/Orchestrator tool for cloud
federated environments." Ad Hoc Networking Workshop (Med-Hoc-Net), 2016 Mediterranean. IEEE,
2016.
[3]. Baranda, Jorge, et al. "Orchestration of end-to-end network services in the 5G-Crosshaul
multi-domain multi-technology transport network." IEEE Communications Magazine 56.7 (2018):
184-191.
[4]. Baucke, Stephan, et al. "Cloud API support for self-service Virtual Network Function (VNF)
deployment." Network Function Virtualization and Software Defined Network (NFV-SDN), 2015 IEEE
Conference on. IEEE, 2015.

1 out of 15
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
© 2024 | Zucol Services PVT LTD | All rights reserved.


