Wireless Networking Concepts Report: Analysis of Wireless Technologies
VerifiedAdded on 2020/05/28

Wireless Networking Concepts
Name of the Student
Name of the University
Author’s note
Paraphrase This Document
WIRELESS NETWORKING CONCEPTS
Table of Contents
Answer 1..........................................................................................................................................2
Answer 2..........................................................................................................................................4
Answer 3..........................................................................................................................................6
Answer 4..........................................................................................................................................9
References......................................................................................................................................26
WIRELESS NETWORKING CONCEPTS
Answer 1
Channel reuse in WLAN
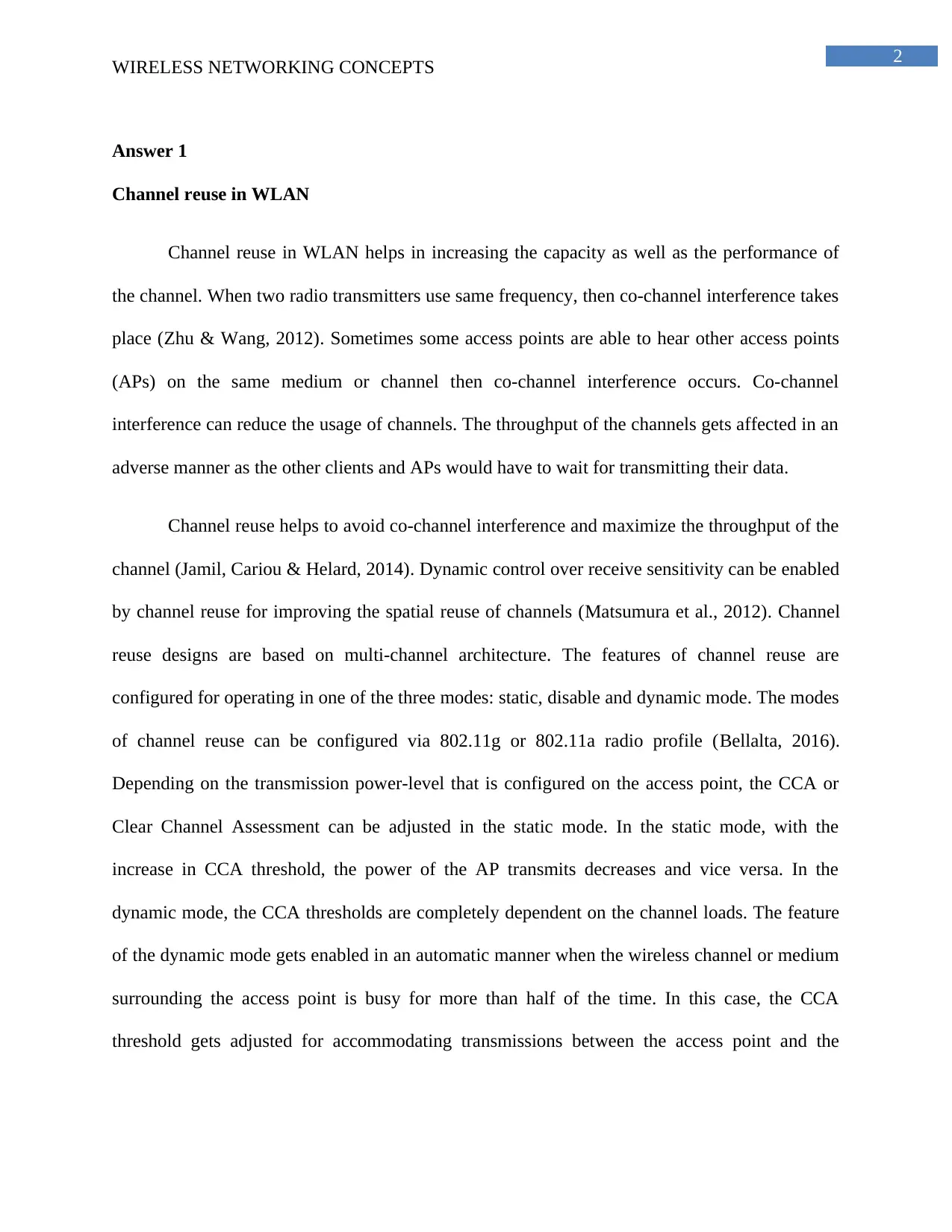
Channel reuse in WLAN helps in increasing the capacity as well as the performance of
the channel. When two radio transmitters use same frequency, then co-channel interference takes
place (Zhu & Wang, 2012). Sometimes some access points are able to hear other access points
(APs) on the same medium or channel then co-channel interference occurs. Co-channel
interference can reduce the usage of channels. The throughput of the channels gets affected in an
adverse manner as the other clients and APs would have to wait for transmitting their data.
Channel reuse helps to avoid co-channel interference and maximize the throughput of the
channel (Jamil, Cariou & Helard, 2014). Dynamic control over receive sensitivity can be enabled
by channel reuse for improving the spatial reuse of channels (Matsumura et al., 2012). Channel
reuse designs are based on multi-channel architecture. The features of channel reuse are
configured for operating in one of the three modes: static, disable and dynamic mode. The modes
of channel reuse can be configured via 802.11g or 802.11a radio profile (Bellalta, 2016).
Depending on the transmission power-level that is configured on the access point, the CCA or
Clear Channel Assessment can be adjusted in the static mode. In the static mode, with the
increase in CCA threshold, the power of the AP transmits decreases and vice versa. In the
dynamic mode, the CCA thresholds are completely dependent on the channel loads. The feature
of the dynamic mode gets enabled in an automatic manner when the wireless channel or medium
surrounding the access point is busy for more than half of the time. In this case, the CCA
threshold gets adjusted for accommodating transmissions between the access point and the
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
WIRELESS NETWORKING CONCEPTS
distant client. The CCA detect threshold does not get tuned in the disable mode of the channel
reuse.
Fig 1: Channel Reuse in WLAN
(Source: Jamil, Cariou & Helard, 2014, p. 305 )
Frequency reuse in Mobile Phone networks
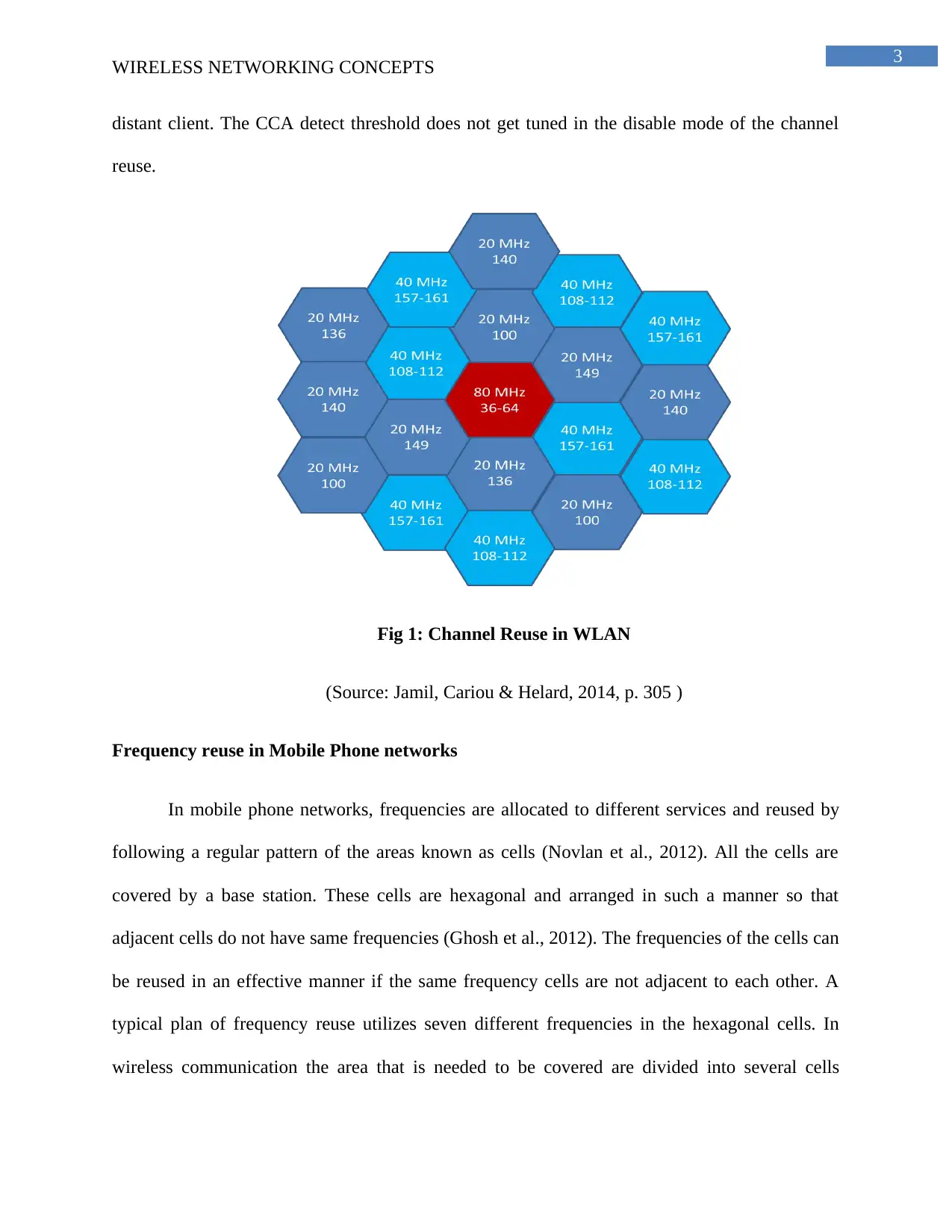
In mobile phone networks, frequencies are allocated to different services and reused by
following a regular pattern of the areas known as cells (Novlan et al., 2012). All the cells are
covered by a base station. These cells are hexagonal and arranged in such a manner so that
adjacent cells do not have same frequencies (Ghosh et al., 2012). The frequencies of the cells can
be reused in an effective manner if the same frequency cells are not adjacent to each other. A
typical plan of frequency reuse utilizes seven different frequencies in the hexagonal cells. In
wireless communication the area that is needed to be covered are divided into several cells
Paraphrase This Document

WIRELESS NETWORKING CONCEPTS
having different frequencies for avoiding interference and facilitating reuse of the radio
frequencies (Zhang et al., 2013). Frequency reuse facilitates effective communication within a
single cell and enables the re-use of frequencies in the nearby cells. Frequency reuse enables the
use of same frequencies for carrying out multiple conversations (Feng et al., 2014). Consider a
situation where N number of cells use same number of frequencies and K is the total number of
frequencies. Then the cell frequency of each cell is given by K/N. Suppose K=397, N= 7. Then
each cell frequencies will be 395/7=56. Frequency reuse helps in utilizing radio frequencies that
are same within an area and separated by a certain distance. It helps in the increase of capacity.
Fig 2: Frequency Reuse
(Source: Novlan et al., 2012, p. 2033)
Answer 2
WMAN or Wireless Metropolitan Area Network helps in establishing wireless
connections between various locations in a metropolitan area. Its area coverage is more than that
WIRELESS NETWORKING CONCEPTS
of WLAN but less than that of WWAN (Jia, Cao & Liang, 2015). One of the best known
WMAN technologies is WiMAX. It has several benefits that can be utilized for improving the
WMAN. Security challenges of WiMAX are:
1) Authentication related threats: Masquerading attacks can take place where one system
masquerades its identity by reprogramming its hardware address with another device’s hardware
address (Sari & Rahnama, 2013). Attacks can also take place on PKM protocol where the
attacker saves the messages received from a legal subscriber station and performs replay attacks
against the base station (Dubey & Kumar, 2013). The process of authorization has several
vulnerabilities as it does not have any mechanism for ensuring message integrity.
2) Jamming attacks: In this type of attack a strong source of noise is introduced for
reducing the capacity of the channel (Dubey & Kumar, 2013). This can take place
unintentionally as well as intentionally. Jamming attacks can be easily performed by an attacker.
This security challenge takes place in the physical layer.
3) Denial of Service attack: Several types of DoS attacks such as unencrypted
management of communication and unprotected entry in the network can take place in WiMAX
technologies (Dadhich, Narang & Yadav, 2012). When a subscriber station sends several false
requests of authorization to a base station, then the base station uses all the resources by carrying
out calculations for checking the validity of the certificate (Sari & Rahnama, 2013). This will
lead to a DoS attack as the base stations will be unable to serve the subscriber stations any
further. In DoS attack, an attacker forges the RNG-RSP or Ranging Request/Response message
for minimizing the power of the subscriber stations or SS and does not allow the SS to transmit
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
WIRELESS NETWORKING CONCEPTS
to the base stations. DoS attacks can also be based on FPC or Fast Power Control, Authorization-
invalid and Reset Command or RES-CMD message.
WMAN can use Wi-Fi technology. Wi-Fi technology has several security challenges.
Data interception can take place when the eavesdroppers capture data over the Wi-Fi network
(Banerji & Chowdhury, 2013). DoS attacks are the most common type of attack where the
resources of the base stations are overused and it is unable to serve to the subscriber stations
(Dondyk, Rivera & Zou, 2013). Wireless intruders and misconfigured access points are some of
the major security challenges of the Wi-Fi challenges. Man-in-the-middle is a type of wireless
phishing attack that can harm the Wi-Fi network.
Answer 3
Paper 1: Design and Simulation of State-of-Art ZigBee Transmitter for IoT Wireless
Devices
This research paper discusses about the designing and simulation of ZigBee
transmitter for the wireless devices of Internet of Things. Over the past few years, wireless
networks have developed by providing extreme speed and higher range of applications (Elarabi,
Deep & Rai, 2015). The demand for high speed has increased everyday and this demand has led
to the technology of ZigBee. This particular technology is an important standard of WPAN or
Wireless Personal Area Networks.
The main advantages of ZigBee technology include lower rate of data and cost
effectiveness. Moreover, the battery life is much more than the rest of the wireless networks. It
defines a significant set of protocols related to communication. The range of frequency bands
within which ZigBee normally operates is 868 MegaHz, 915 MegaHz and 2.4 GigaHz. The
Paraphrase This Document
WIRELESS NETWORKING CONCEPTS
highest rate of data for the ZigBee technology is 250KB per second (Elarabi, Deep & Rai, 2015).
There are various blocks of architecture in one digital ZigBee transmitter. This technology was
developed due to the advancement of VLSI technology. ZigBee transmitter is extremely
efficient, rapid and accurate. It never gives inaccurate data. Furthermore, ZigBee transmitter is
smaller in size, which reduces the bulkiness of a device.
IoT or Internet of Things is the networking of various physical devices or any other item
that is implanted with sensors, software and even connectivity of various networks. The Internet
of Things allows each and every object to link and exchange information within each other
(Elarabi, Deep & Rai, 2015). Every device or item that is connected or linked to the IoT can be
identified uniquely with the help of the implanted system of computing. However, they have the
ability to internally operate in the infrastructure of Internet that already exists. There is an
immense connection between Internet of Things and ZigBee technology. This technology is an
application of Internet of Things or IoT as it allows lower rate of data and lesser power. The
ZigBee transmitter can be easily designed with the help of Verilog for the applications of
Internet of Things (Elarabi, Deep & Rai, 2015). A typical ZigBee transmitter comprises of a
modulator, blocks of bit to symbol and symbol to chip and CRC or cyclic redundancy check.
Paper 2: From Today’s Intranet of Things to a Future Internet of Things: A Wireless and
Mobility Related View
This research paper discusses about the evolution of Intranet of Things to Internet
of Things. Intranet of Things is a specific element of all the encompassing IoT or Internet of
Things (Zorzi et al., 2010). It utilizes same technologies or systems, however restricts to the
access of all the connected or linked things to any corporate network.
WIRELESS NETWORKING CONCEPTS
The concept of Intranet of Things mainly comprises of every corporate asset that are
accessible in any particular organization. However, these things can be accessed directly on the
public Internet. Intranet of Things is somewhat too similar to the Internet of Things (Zorzi et al.,
2010). IoT mainly harnesses sensor data, incorporates technology of big data and even machine
learning. The machine to machine or M2M communication technology is also harnessed with the
help of Internet of Things.
There are various technological challenges that are related to the wireless and mobility
related view of the evolution. Moreover, there are various methods for solving the procedure of
challenges, faced while the Internet of Things is developed.
The architectural framework of the evolution of Intranet of Things to Internet of Things
completely makes it possible for overcoming the present fragmentation and even the restriction
of all the solutions (Zorzi et al., 2010). These restrictions occur where several Intranets of Things
are present, in the direction of a real Internet of Things, where each and every device would be a
specific part of a universally integrated system.
Internet of Things first came into account ten years ago. Prior to it, Intranet of Things was
ruling the market of wireless networking (Zorzi et al., 2010). The development was done with
the help of RFID or Radio Frequency Identification and sensor networks. The sensor networks,
which are considered to be an important pillar of the Internet of Things, have experienced
various developments in recent years. A number of researches have been done on this
development in the past couple of years, not only within the main area of the networking
protocols, involving the routing and MAC, but also within the area of technologies like nano and
micro, as well as on the problems in higher layer, like the applications, middleware and security
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide

WIRELESS NETWORKING CONCEPTS
(Zorzi et al., 2010). In future, the integration of RFID and sensor networks is supposed to bring
exclusive development in the evolution of Intranet of Things to Internet of Things.
Paraphrase This Document
WIRELESS NETWORKING CONCEPTS
Answer 4

WIRELESS NETWORKING CONCEPTS
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
WIRELESS NETWORKING CONCEPTS
Paraphrase This Document

WIRELESS NETWORKING CONCEPTS
WIRELESS NETWORKING CONCEPTS
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
WIRELESS NETWORKING CONCEPTS
Paraphrase This Document
WIRELESS NETWORKING CONCEPTS
WIRELESS NETWORKING CONCEPTS
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide

WIRELESS NETWORKING CONCEPTS
Paraphrase This Document
WIRELESS NETWORKING CONCEPTS
WIRELESS NETWORKING CONCEPTS
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide

WIRELESS NETWORKING CONCEPTS
Paraphrase This Document
WIRELESS NETWORKING CONCEPTS

WIRELESS NETWORKING CONCEPTS
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
WIRELESS NETWORKING CONCEPTS
Paraphrase This Document

WIRELESS NETWORKING CONCEPTS
WIRELESS NETWORKING CONCEPTS
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
WIRELESS NETWORKING CONCEPTS
References
Banerji, S., & Chowdhury, R. S. (2013). Wi-Fi & WiMAX: A Comparative Study. arXiv
preprint arXiv:1302.2247.
Bellalta, B. (2016). IEEE 802.11 ax: High-efficiency WLANs. IEEE Wireless
Communications, 23(1), 38-46.
Dadhich, R., Narang, G., & Yadav, D. M. (2012). Analysis and Literature Review of IEEE
802.16 e (Mobile WiMAX) Security. International Journal of Engineering and
Advanced Technology, 1, 167-173.
Dondyk, E., Rivera, L., & Zou, C. C. (2013). Wi–Fi access denial of service attack to
smartphones. International Journal of Security and Networks, 8(3), 117-129.
Dubey, S., & Kumar, S. (2013). Security Issues in WiMAX: A Critical Review. International
Journal of Information and Computation Technology, 3(3), 189-194.
Elarabi, T., Deep, V., & Rai, C. K. (2015, December). Design and simulation of state-of-art
ZigBee transmitter for IoT wireless devices. In Signal Processing and Information
Technology (ISSPIT), 2015 IEEE International Symposium on(pp. 297-300). IEEE.
Feng, D., Lu, L., Yuan-Wu, Y., Li, G., Li, S., & Feng, G. (2014). Device-to-device
communications in cellular networks. IEEE Communications Magazine, 52(4), 49-55.
Ghosh, A., Mangalvedhe, N., Ratasuk, R., Mondal, B., Cudak, M., Visotsky, E., ... & Dhillon,
H. S. (2012). Heterogeneous cellular networks: From theory to practice. IEEE
communications magazine, 50(6).
Paraphrase This Document
WIRELESS NETWORKING CONCEPTS
Jamil, I., Cariou, L., & Helard, J. F. (2014, May). Improving the capacity of future IEEE
802.11 high efficiency WLANs. In Telecommunications (ICT), 2014 21st International
Conference on (pp. 303-307). IEEE.
Jia, M., Cao, J., & Liang, W. (2015). Optimal cloudlet placement and user to cloudlet allocation
in wireless metropolitan area networks. IEEE Transactions on Cloud Computing.
Matsumura, Y., Kumagai, S., Obara, T., Yamamoto, T., & Adachi, F. (2012, November).
Channel segregation based dynamic channel assignment for WLAN. In Communication
Systems (ICCS), 2012 IEEE International Conference on (pp. 463-467). IEEE.
Novlan, T. D., Ganti, R. K., Ghosh, A., & Andrews, J. G. (2012). Analytical evaluation of
fractional frequency reuse for heterogeneous cellular networks. IEEE Transactions on
Communications, 60(7), 2029-2039.
Sari, A., & Rahnama, B. (2013, November). Addressing security challenges in WiMAX
environment. In Proceedings of the 6th International Conference on Security of
Information and Networks (pp. 454-456). ACM.
Zhang, J., Zhang, R., Li, G., & Hanzo, L. (2013). Distributed antenna systems in fractional-
frequency-reuse-aided cellular networks. IEEE Transactions on vehicular
technology, 62(3), 1340-1349.
Zhu, R., & Wang, J. (2012). Power-efficient spatial reusable channel assignment scheme in
WLAN mesh networks. Mobile Networks and Applications, 17(1), 53-63.

WIRELESS NETWORKING CONCEPTS
Zorzi, M., Gluhak, A., Lange, S., & Bassi, A. (2010). From today's intranet of things to a future
internet of things: a wireless-and mobility-related view. IEEE Wireless
Communications, 17(6)
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
© 2024 | Zucol Services PVT LTD | All rights reserved.





