Data Communication: Analysis of Apple Pay and PayPal Security Features
VerifiedAdded on 2023/06/10
|6
|1172
|147
Report
AI Summary
This report provides a comparative analysis of Apple Pay and PayPal, focusing on their data communication security and application. It examines the technologies employed by each platform, including data encryption methods such as Secure Socket Layer (SSL) with 128-bit encryption for PayPal and the utilization of Secure Element for Apple Pay. The report delves into the system authentication procedures, highlighting the security measures in place to protect user data during online transactions. Furthermore, the report includes a discussion of network segments and port numbers in TCP communication. The analysis covers the evolution of card payment security, the adoption of these payment methods by major financial institutions, and their respective market shares. The report concludes with a comparison of the two payment methods, assessing their security parameters, efficiency, and overall user experience.
Data communication
Name
Institution
Professor
Course
Date
Name
Institution
Professor
Course
Date
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Security and applications
The security breach that targeted card payment was one of the severe breach that
prompted for strict measures to be taken. Despite the security issue on card payment being an
issue of concern, most of the parties in the payment sector were oblique on changing card
processing methods. Online payment discussion would be done in reference to Paypal Inc. and
Apple Pay Inc. (Ghosh et al 2017, p. 86). In this regard, it is important to note that the Apple Pay
is the payment method that has been selected by Apple Company for devices that runs on iOS.
On the same note, Paypal is an online payment method that runs on android devices. These two
online payment methods would be discussed as well as technologies used in data encryption.
Similarly, system authentication would be discussed with aim of accessing procedures provided
when access organizational data (Ogbanufe & Kim 2017, p. 142). Finally, a comparison of the
two payment methods would be done to ascertain their security parameters and efficiency of use.
There is a great assumption that Apple has developed a very good payment method
within a year and indeed come up with a very elegant payment application. By securing
integration of iOS card payment within a secured element as well as pass encrypted card
payment, the following payment issues would be resolved;
Security of card payment has greatly improved.
It has helped in keeping payment data up to date.
Card payments is be very fast than usual card swipes.
Interesting to note is that the Apple payment method has been adopted by both MasterCard and
Visa. During payment adoption by the two companies, an agreement was made on how the
The security breach that targeted card payment was one of the severe breach that
prompted for strict measures to be taken. Despite the security issue on card payment being an
issue of concern, most of the parties in the payment sector were oblique on changing card
processing methods. Online payment discussion would be done in reference to Paypal Inc. and
Apple Pay Inc. (Ghosh et al 2017, p. 86). In this regard, it is important to note that the Apple Pay
is the payment method that has been selected by Apple Company for devices that runs on iOS.
On the same note, Paypal is an online payment method that runs on android devices. These two
online payment methods would be discussed as well as technologies used in data encryption.
Similarly, system authentication would be discussed with aim of accessing procedures provided
when access organizational data (Ogbanufe & Kim 2017, p. 142). Finally, a comparison of the
two payment methods would be done to ascertain their security parameters and efficiency of use.
There is a great assumption that Apple has developed a very good payment method
within a year and indeed come up with a very elegant payment application. By securing
integration of iOS card payment within a secured element as well as pass encrypted card
payment, the following payment issues would be resolved;
Security of card payment has greatly improved.
It has helped in keeping payment data up to date.
Card payments is be very fast than usual card swipes.
Interesting to note is that the Apple payment method has been adopted by both MasterCard and
Visa. During payment adoption by the two companies, an agreement was made on how the
Secured Element would be taken over by Apple payment developed system. Generally, the two
payment methods are the basis on which Apple Payment systems have been implemented.
Card payment loading is very simple because application users can associate their card
with iTunes files or simply take a picture of the card for encryption using the Secure Element.
This has to be verified by the Apple and authorize the user to make the required payments.
Important to note is that the secure element in use by Apple is compatible to 85% of USA card
users (Plateaux et al 2014, p. 179-180). Additionally, Apple Pay interface enables merchants to
get their payment card number on timely manner. In partnership with other organization, Apple
chose Stripe as the first company to have a test of the product. In its capacity, Apple does not
issue cards, neither does it process any form of payment but just a facilitator of the payment
platform. It supports the payment process by storing the cards and making use of several security
technologies to secure the data.
Paypal Holding Inc. is an online payment system which is based in USA. To make
transaction faster and safe, Paypal both payment get way and merchant are made available to
customers (Reddy & Anusha 2015, p. 124). Through use of Pro accounts and Paypal payment
advanced, it is possible to process all transactions on the website. To enhance security
parameters on Paypal transactions, it has been secured through encryption and there is no
possibility of data leaks as it is the case with other websites. The secure Socket Layer (SSL) with
128 bit encryption key is the technology used to secure all forms of data captured on the website
(Wang, Hahn & Sutrave 2016, p. 2-3). To make sure all connections are secure, even browsers
are checked for approval before connecting to Paypal. Once information is captured on the
Paypal website, it is stored on servers which are secured through dedicated firewalls.
payment methods are the basis on which Apple Payment systems have been implemented.
Card payment loading is very simple because application users can associate their card
with iTunes files or simply take a picture of the card for encryption using the Secure Element.
This has to be verified by the Apple and authorize the user to make the required payments.
Important to note is that the secure element in use by Apple is compatible to 85% of USA card
users (Plateaux et al 2014, p. 179-180). Additionally, Apple Pay interface enables merchants to
get their payment card number on timely manner. In partnership with other organization, Apple
chose Stripe as the first company to have a test of the product. In its capacity, Apple does not
issue cards, neither does it process any form of payment but just a facilitator of the payment
platform. It supports the payment process by storing the cards and making use of several security
technologies to secure the data.
Paypal Holding Inc. is an online payment system which is based in USA. To make
transaction faster and safe, Paypal both payment get way and merchant are made available to
customers (Reddy & Anusha 2015, p. 124). Through use of Pro accounts and Paypal payment
advanced, it is possible to process all transactions on the website. To enhance security
parameters on Paypal transactions, it has been secured through encryption and there is no
possibility of data leaks as it is the case with other websites. The secure Socket Layer (SSL) with
128 bit encryption key is the technology used to secure all forms of data captured on the website
(Wang, Hahn & Sutrave 2016, p. 2-3). To make sure all connections are secure, even browsers
are checked for approval before connecting to Paypal. Once information is captured on the
Paypal website, it is stored on servers which are secured through dedicated firewalls.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
The two payment methods presents customers with reliable and efficient means of
making payments but Apple market share is much lesser compared to Paypal Inc. Apple
Payment is trying to capture the market but it is some miles away from achieving the milestones
that Paypal has made globally (Roy & Venkateswaran 2014, p. 4). From the analysis of the
market, Apple has adopted customer relationship to gain some market share by setting some
device standards from other companies.
TCP
a. By considering the network segment Host, A to B the sequence port number in use is 207
while the network source number is 302 and packet destination port number is 80.
b. In cases where first packet set of data hits the destination address before the second
packet, the arrival acknowledgment would be done on port number 207, with source port
number being 80 and designation port number will be 302.
c. Similarly, when the second packet segment hits destination address first, to acknowledge
the arrival of first packet segment, 127 is set as the acknowledgement port numbers. This
makes it still to be ready to receive more data provided they are meant for higher port
number.
d.
making payments but Apple market share is much lesser compared to Paypal Inc. Apple
Payment is trying to capture the market but it is some miles away from achieving the milestones
that Paypal has made globally (Roy & Venkateswaran 2014, p. 4). From the analysis of the
market, Apple has adopted customer relationship to gain some market share by setting some
device standards from other companies.
TCP
a. By considering the network segment Host, A to B the sequence port number in use is 207
while the network source number is 302 and packet destination port number is 80.
b. In cases where first packet set of data hits the destination address before the second
packet, the arrival acknowledgment would be done on port number 207, with source port
number being 80 and designation port number will be 302.
c. Similarly, when the second packet segment hits destination address first, to acknowledge
the arrival of first packet segment, 127 is set as the acknowledgement port numbers. This
makes it still to be ready to receive more data provided they are meant for higher port
number.
d.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
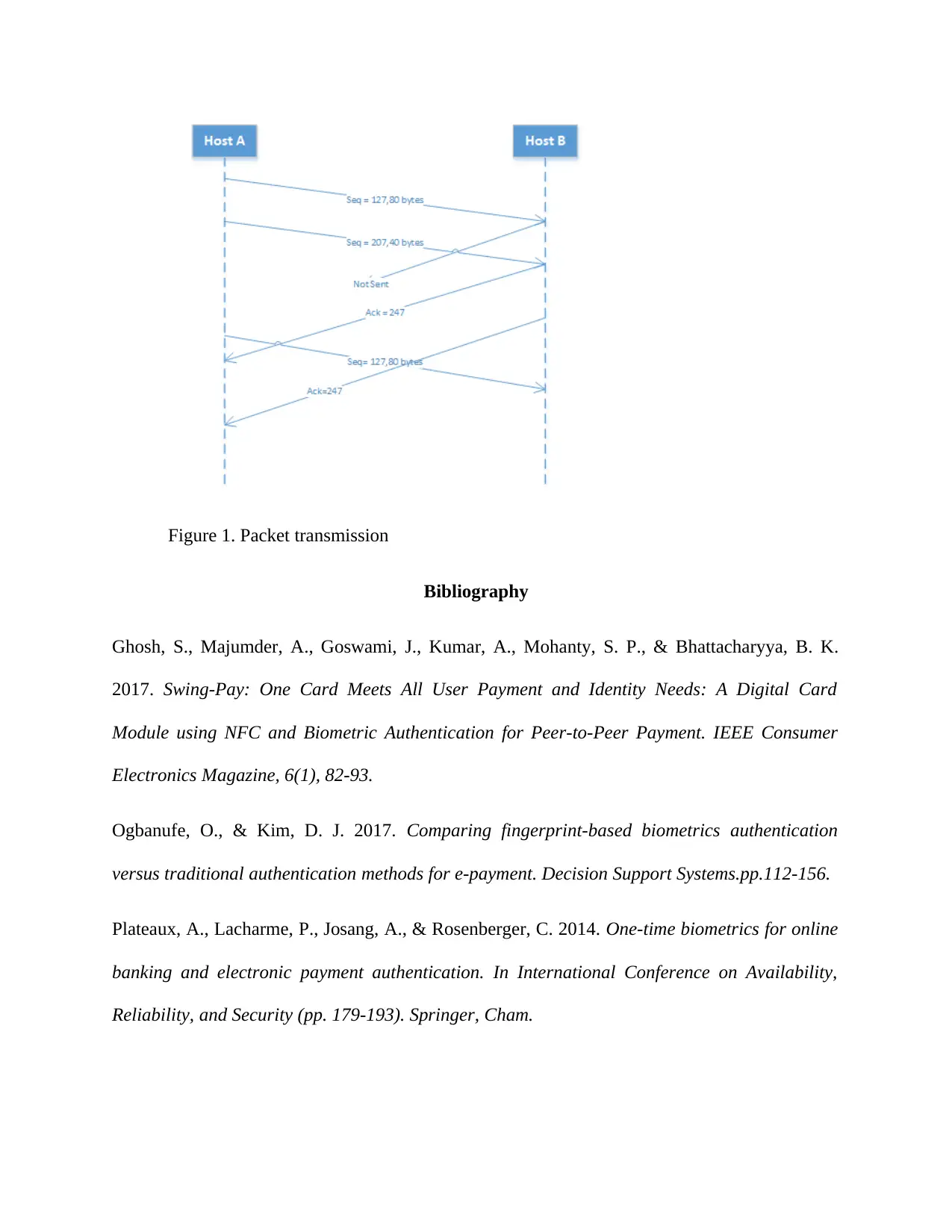
Figure 1. Packet transmission
Bibliography
Ghosh, S., Majumder, A., Goswami, J., Kumar, A., Mohanty, S. P., & Bhattacharyya, B. K.
2017. Swing-Pay: One Card Meets All User Payment and Identity Needs: A Digital Card
Module using NFC and Biometric Authentication for Peer-to-Peer Payment. IEEE Consumer
Electronics Magazine, 6(1), 82-93.
Ogbanufe, O., & Kim, D. J. 2017. Comparing fingerprint-based biometrics authentication
versus traditional authentication methods for e-payment. Decision Support Systems.pp.112-156.
Plateaux, A., Lacharme, P., Josang, A., & Rosenberger, C. 2014. One-time biometrics for online
banking and electronic payment authentication. In International Conference on Availability,
Reliability, and Security (pp. 179-193). Springer, Cham.
Bibliography
Ghosh, S., Majumder, A., Goswami, J., Kumar, A., Mohanty, S. P., & Bhattacharyya, B. K.
2017. Swing-Pay: One Card Meets All User Payment and Identity Needs: A Digital Card
Module using NFC and Biometric Authentication for Peer-to-Peer Payment. IEEE Consumer
Electronics Magazine, 6(1), 82-93.
Ogbanufe, O., & Kim, D. J. 2017. Comparing fingerprint-based biometrics authentication
versus traditional authentication methods for e-payment. Decision Support Systems.pp.112-156.
Plateaux, A., Lacharme, P., Josang, A., & Rosenberger, C. 2014. One-time biometrics for online
banking and electronic payment authentication. In International Conference on Availability,
Reliability, and Security (pp. 179-193). Springer, Cham.
Reddy, V. L., & Anusha, T. 2015. Combine use of steganography and visual cryptography for
online payment system. International Journal of Computer Applications, 124(6).
Roy, S., & Venkateswaran, P. 2014. Online payment system using steganography and visual
cryptography. In Electrical, Electronics and Computer Science (SCEECS), 2014 IEEE Students'
Conference on (pp. 1-5). IEEE.
Wang, Y., Hahn, C., & Sutrave, K. 2016. Mobile payment security, threats, and challenges. In
Mobile and Secure Services (MobiSecServ), 2016 Second International Conference on (pp. 1-5).
IEEE.
online payment system. International Journal of Computer Applications, 124(6).
Roy, S., & Venkateswaran, P. 2014. Online payment system using steganography and visual
cryptography. In Electrical, Electronics and Computer Science (SCEECS), 2014 IEEE Students'
Conference on (pp. 1-5). IEEE.
Wang, Y., Hahn, C., & Sutrave, K. 2016. Mobile payment security, threats, and challenges. In
Mobile and Secure Services (MobiSecServ), 2016 Second International Conference on (pp. 1-5).
IEEE.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 6
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.




