CSC8419: Implementing Digital Certificates Using OpenSSL for Security
VerifiedAdded on 2024/06/04
|19
|4915
|197
Report
AI Summary
This report assesses the use of OpenSSL for generating digital certificates to enhance security. It discusses the importance of SSL certificates in securing data exchange and logins, highlighting the need for trusted Certificate Authorities. The report references related work on OpenSSL, including vulnerabilities like Heartbleed, and examines the practical aspects of creating self-signed certificates for local environments. It emphasizes the role of digital certificates in ensuring secure internet exchanges through SSL and TLS protocols, detailing the processes involved in establishing secure connections and the potential risks associated with insecure implementations. The document concludes by recommending the use of SSL-generated digital certificates to improve data and communication security within organizations and is available for study and reference on Desklib, a platform offering various AI-based study tools.
CSC8419: Cryptography and Security
Assessment 3
Topic: Using OpenSSL to generate Digital Certificates
Assessment 3
Topic: Using OpenSSL to generate Digital Certificates
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Table of Contents
Executive summary...............................................................................................................................2
Introduction...........................................................................................................................................3
Related Work (OpenSSL to generate the digital Certificate)..................................................................4
Technologies used to deal with security................................................................................................8
Cryptography technology for security.................................................................................................11
Future scope........................................................................................................................................15
Conclusion...........................................................................................................................................16
References...........................................................................................................................................17
List of figures
Figure 1 results of the attack.................................................................................................................5
Figure 2 operation of the digital certificate...........................................................................................6
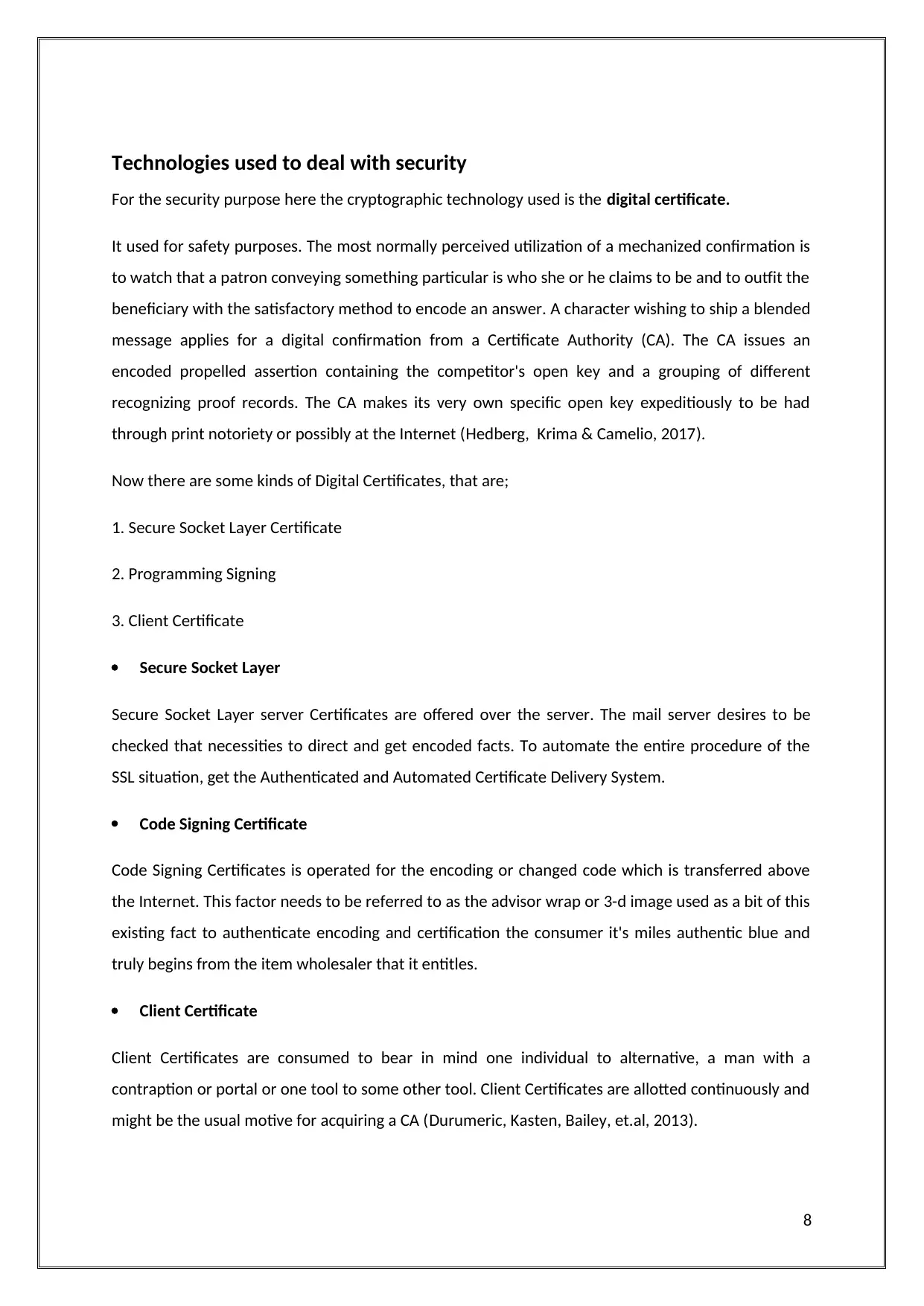
Figure 3 creation of SSL digital certificate............................................................................................10
Figure 4 proposed solution..................................................................................................................11
Figure 5 generating a digital certificate...............................................................................................12
Figure 6 use of a digital certificate.......................................................................................................13
1
Executive summary...............................................................................................................................2
Introduction...........................................................................................................................................3
Related Work (OpenSSL to generate the digital Certificate)..................................................................4
Technologies used to deal with security................................................................................................8
Cryptography technology for security.................................................................................................11
Future scope........................................................................................................................................15
Conclusion...........................................................................................................................................16
References...........................................................................................................................................17
List of figures
Figure 1 results of the attack.................................................................................................................5
Figure 2 operation of the digital certificate...........................................................................................6
Figure 3 creation of SSL digital certificate............................................................................................10
Figure 4 proposed solution..................................................................................................................11
Figure 5 generating a digital certificate...............................................................................................12
Figure 6 use of a digital certificate.......................................................................................................13
1
Executive summary
Objective: the objective at the back of doing this assessment is to apprehend the need of OpenSSL in
slicing aspect revelation age. SSL Certificates are little records statistics that deliberately connect a
cryptographic key to an affiliation's inconspicuous additives. Right while provided on an internet
server, it authorizes the lock and the https culture and licenses comfy courting from an internet
server to software. Routinely, SSL is used to comfy statistics alternate and logins, MasterCard trades
and all of the extra beginning overdue is transforming into the standard while securing scrutinizing
of internet organizing goals.
Background: An association desires to provide the SSL Certificate onto its internet server to start a
secured consultation with applications. Once a sheltered association is set up, all web development
between the internet server and the new software will be at ease.
Exactly whilst an underwriting is effectively provided for your server, the utility tradition (generally
known as HTTP) will alternate to HTTPs, in which the 'S' remains for 'security'. Dependent upon the
type of affirmation you buy and what program you are surfing the web on, an application will show
off a hook or inexperienced bar within the application when you visit a webpage that has an SSL
Certificate supplied.
Results: SSL Certificates relaxed your delicate data, as an instance, usernames, passwords, rate card
records, etc. It furthermore: Keeps records comfy between servers, Increases your Google Rankings,
Builds/Enhances patron trust what is more Improves alternate charges. SSL Certificates have to be
issued from a depended on Certificate Authority. Projects, running structures, and PDAs hold up as
soon as-over of trusted CA root helps. The digital Certificate needs to be reachable to the client's
gadget altogether. If it isn't trusted this system will reveal untrusted botch messages to the stop
customer. Because of electronic commercial enterprise, such bumble messages result in incite
nonattendance of agree with inside the website and affiliations chance dropping conviction and
enterprise from the bigger piece of customers.
Recommendations: it is recommended to all the organization to use the SSL generated digital
certificates to enhance the security of data and communication in an organization.
2
Objective: the objective at the back of doing this assessment is to apprehend the need of OpenSSL in
slicing aspect revelation age. SSL Certificates are little records statistics that deliberately connect a
cryptographic key to an affiliation's inconspicuous additives. Right while provided on an internet
server, it authorizes the lock and the https culture and licenses comfy courting from an internet
server to software. Routinely, SSL is used to comfy statistics alternate and logins, MasterCard trades
and all of the extra beginning overdue is transforming into the standard while securing scrutinizing
of internet organizing goals.
Background: An association desires to provide the SSL Certificate onto its internet server to start a
secured consultation with applications. Once a sheltered association is set up, all web development
between the internet server and the new software will be at ease.
Exactly whilst an underwriting is effectively provided for your server, the utility tradition (generally
known as HTTP) will alternate to HTTPs, in which the 'S' remains for 'security'. Dependent upon the
type of affirmation you buy and what program you are surfing the web on, an application will show
off a hook or inexperienced bar within the application when you visit a webpage that has an SSL
Certificate supplied.
Results: SSL Certificates relaxed your delicate data, as an instance, usernames, passwords, rate card
records, etc. It furthermore: Keeps records comfy between servers, Increases your Google Rankings,
Builds/Enhances patron trust what is more Improves alternate charges. SSL Certificates have to be
issued from a depended on Certificate Authority. Projects, running structures, and PDAs hold up as
soon as-over of trusted CA root helps. The digital Certificate needs to be reachable to the client's
gadget altogether. If it isn't trusted this system will reveal untrusted botch messages to the stop
customer. Because of electronic commercial enterprise, such bumble messages result in incite
nonattendance of agree with inside the website and affiliations chance dropping conviction and
enterprise from the bigger piece of customers.
Recommendations: it is recommended to all the organization to use the SSL generated digital
certificates to enhance the security of data and communication in an organization.
2
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Introduction
OpenSSL is a strong, commercial enterprise survey, and complete-blanketed tool package for the
Secure Sockets Layer (SSL) and Transport Layer Security (TLS) traditions. It is likewise an all-around
helpful cryptography library. For extra records approximately the gathering and collecting around
the enterprise, or to begin impacting your own precise responsibilities, anyways the collection page.
To get the contemporary information, download the supply, and so on, please watch the sidebar or
the gets at the most noteworthy purpose of each page. OpenSSL is permitted beneath an Apache-
style permit, which essentially infers that you are authorised to get and use it for business and non-
business functions difficulty to a few clean allow conditions. OpenSSL is an adaptable request line
device that could be utilized for the vast arrangement of endeavours associated with Public Key
Infrastructure (PKI) and HTTPS. These sheet approaches oversee offers an active reference to
OpenSSL orders which can be good sized in like manner, trendy circumstances. This fuses OpenSSL
instances of making non-public keys, affirmation stamping requesting, and support configuration
alternate. It does not cowl most of the work of OpenSSL (Armknecht, Gasmi, Sadeghi, et.al, 2008).
A propelled declaration is an electronic "visa" that lets in a man, PC or relationship to alternate facts
securely completed over the Internet using individual's all in all key establishment (PKI). A
mechanized underwriting can also in like manner be counselled as an open key confirmation. A
propelled underwriting gives spotting records, is manufacture secure and can be affirmed in light of
the manner that it becomes issued with the aid of an authority, depended on within the association.
The revelation encompasses the confirmation holder name, a serial variety, and gives up time, a
replica of a support holder's public key and the propelled signal of the authentication supplying
master that is certificate authority (CA) with the goal that a recipient can watch that the
underwriting is licensed.
To get an SSL assertion from an affirmation grasp (CA), you should make an assist stamping request
(CSR). A CSR includes commonly of the overall public key of a key match and a few extra statistics.
Both of those portions are inserted into the affirmation while it is settled upon. At anything factor
you supply a CSR, you'll be incited to offer data as for the announcement. This fact is referred to as a
Distinguished Name (DN) (Epstein, & Miller, 2014).
3
OpenSSL is a strong, commercial enterprise survey, and complete-blanketed tool package for the
Secure Sockets Layer (SSL) and Transport Layer Security (TLS) traditions. It is likewise an all-around
helpful cryptography library. For extra records approximately the gathering and collecting around
the enterprise, or to begin impacting your own precise responsibilities, anyways the collection page.
To get the contemporary information, download the supply, and so on, please watch the sidebar or
the gets at the most noteworthy purpose of each page. OpenSSL is permitted beneath an Apache-
style permit, which essentially infers that you are authorised to get and use it for business and non-
business functions difficulty to a few clean allow conditions. OpenSSL is an adaptable request line
device that could be utilized for the vast arrangement of endeavours associated with Public Key
Infrastructure (PKI) and HTTPS. These sheet approaches oversee offers an active reference to
OpenSSL orders which can be good sized in like manner, trendy circumstances. This fuses OpenSSL
instances of making non-public keys, affirmation stamping requesting, and support configuration
alternate. It does not cowl most of the work of OpenSSL (Armknecht, Gasmi, Sadeghi, et.al, 2008).
A propelled declaration is an electronic "visa" that lets in a man, PC or relationship to alternate facts
securely completed over the Internet using individual's all in all key establishment (PKI). A
mechanized underwriting can also in like manner be counselled as an open key confirmation. A
propelled underwriting gives spotting records, is manufacture secure and can be affirmed in light of
the manner that it becomes issued with the aid of an authority, depended on within the association.
The revelation encompasses the confirmation holder name, a serial variety, and gives up time, a
replica of a support holder's public key and the propelled signal of the authentication supplying
master that is certificate authority (CA) with the goal that a recipient can watch that the
underwriting is licensed.
To get an SSL assertion from an affirmation grasp (CA), you should make an assist stamping request
(CSR). A CSR includes commonly of the overall public key of a key match and a few extra statistics.
Both of those portions are inserted into the affirmation while it is settled upon. At anything factor
you supply a CSR, you'll be incited to offer data as for the announcement. This fact is referred to as a
Distinguished Name (DN) (Epstein, & Miller, 2014).
3
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Related Work (OpenSSL to generate the digital Certificate)
According to (Anwar & Kaur, 2016) the security on the Internet is a crucial ordeal. Despite the way
that the considerable majority of the assaults depend upon a wrong setup it'd manifest that it isn't
patron's imperfection. Programming may additionally arise quickly. The OpenSSL library executes a
brilliant measure of determining suites used by special programs. The Heart use up shortcoming
astounded the Internet in April 2014. The weak spot, a champion most of the maximum big since the
nearness of the enterprise Internet, enabled aggressors to remotely examine shielded reminiscence
from an everyday 24– fifty-five % of sincerely comprehended HTTPS regions. In any case, inspectors
have uncovered an ensured defencelessness in this general Web encryption programming, the
Trojan horse can give programming engineers get right of entry to particular information like fee
card numbers, usernames, passwords, and, maybe especially, cryptographic keys which could allow
designers to reflect or display screen a server.
These traditions are cryptographic traditions. At first, the tradition becomes named SSL (comfortable
connection layer) and the trendy form is called TLS (transport layer protection). This way of life is
utilized by numerous others, as an instance, HTTPS, POP3S, STAMPS, SMTPS, and IMPAS. It passes on
to the customer of the library more than one discerns suites. A make sense of suite is manufactured
from a key change figuring (for instance Diffie Hellman), a mass encryption computation to exchange
information as soon as the association is mounted (for outline AES), a message affirmation code (for
case SHA) and a pseudo sporadic capacity to make the consultation key. It offers affirmation by way
of the distinctive feature of cryptography with the utilization of confirmations, a characterization
with the symmetric cryptographic key, and uprightness with message check code (MAC). To permit
each the sort of homes, a presentation of the association is required. To installation, a tried and true
association which authorized the safety portrayed more than, more than one degrees are
imperative. We need to diagram it with a relationship between a purchaser which has no affirmation
and a server which prompted one to renowned a TCP association has been opened. This is the
normal condition whilst a purchaser relates to a website with HTTPS. To begin with, the customer
sends a Client Hello message with 5 handles: the higher type of SSL which may be used, a self-
assertive number, a consultation ID, a discern suite and a weighting methodology. The self-assertive
range is used as a test to check the server and besides as decoded salt. The consultation ID is used to
exchange the parameters of a gift affiliation. The determine suite incorporates an orchestrated once-
over of the parent suites needed by the consumer. The weight gadget consists of in addition an
orchestrated once-over with the slant strategies. This ultimate summary may be unfilled. Data are
not for the most elements compacted.
4
According to (Anwar & Kaur, 2016) the security on the Internet is a crucial ordeal. Despite the way
that the considerable majority of the assaults depend upon a wrong setup it'd manifest that it isn't
patron's imperfection. Programming may additionally arise quickly. The OpenSSL library executes a
brilliant measure of determining suites used by special programs. The Heart use up shortcoming
astounded the Internet in April 2014. The weak spot, a champion most of the maximum big since the
nearness of the enterprise Internet, enabled aggressors to remotely examine shielded reminiscence
from an everyday 24– fifty-five % of sincerely comprehended HTTPS regions. In any case, inspectors
have uncovered an ensured defencelessness in this general Web encryption programming, the
Trojan horse can give programming engineers get right of entry to particular information like fee
card numbers, usernames, passwords, and, maybe especially, cryptographic keys which could allow
designers to reflect or display screen a server.
These traditions are cryptographic traditions. At first, the tradition becomes named SSL (comfortable
connection layer) and the trendy form is called TLS (transport layer protection). This way of life is
utilized by numerous others, as an instance, HTTPS, POP3S, STAMPS, SMTPS, and IMPAS. It passes on
to the customer of the library more than one discerns suites. A make sense of suite is manufactured
from a key change figuring (for instance Diffie Hellman), a mass encryption computation to exchange
information as soon as the association is mounted (for outline AES), a message affirmation code (for
case SHA) and a pseudo sporadic capacity to make the consultation key. It offers affirmation by way
of the distinctive feature of cryptography with the utilization of confirmations, a characterization
with the symmetric cryptographic key, and uprightness with message check code (MAC). To permit
each the sort of homes, a presentation of the association is required. To installation, a tried and true
association which authorized the safety portrayed more than, more than one degrees are
imperative. We need to diagram it with a relationship between a purchaser which has no affirmation
and a server which prompted one to renowned a TCP association has been opened. This is the
normal condition whilst a purchaser relates to a website with HTTPS. To begin with, the customer
sends a Client Hello message with 5 handles: the higher type of SSL which may be used, a self-
assertive number, a consultation ID, a discern suite and a weighting methodology. The self-assertive
range is used as a test to check the server and besides as decoded salt. The consultation ID is used to
exchange the parameters of a gift affiliation. The determine suite incorporates an orchestrated once-
over of the parent suites needed by the consumer. The weight gadget consists of in addition an
orchestrated once-over with the slant strategies. This ultimate summary may be unfilled. Data are
not for the most elements compacted.
4
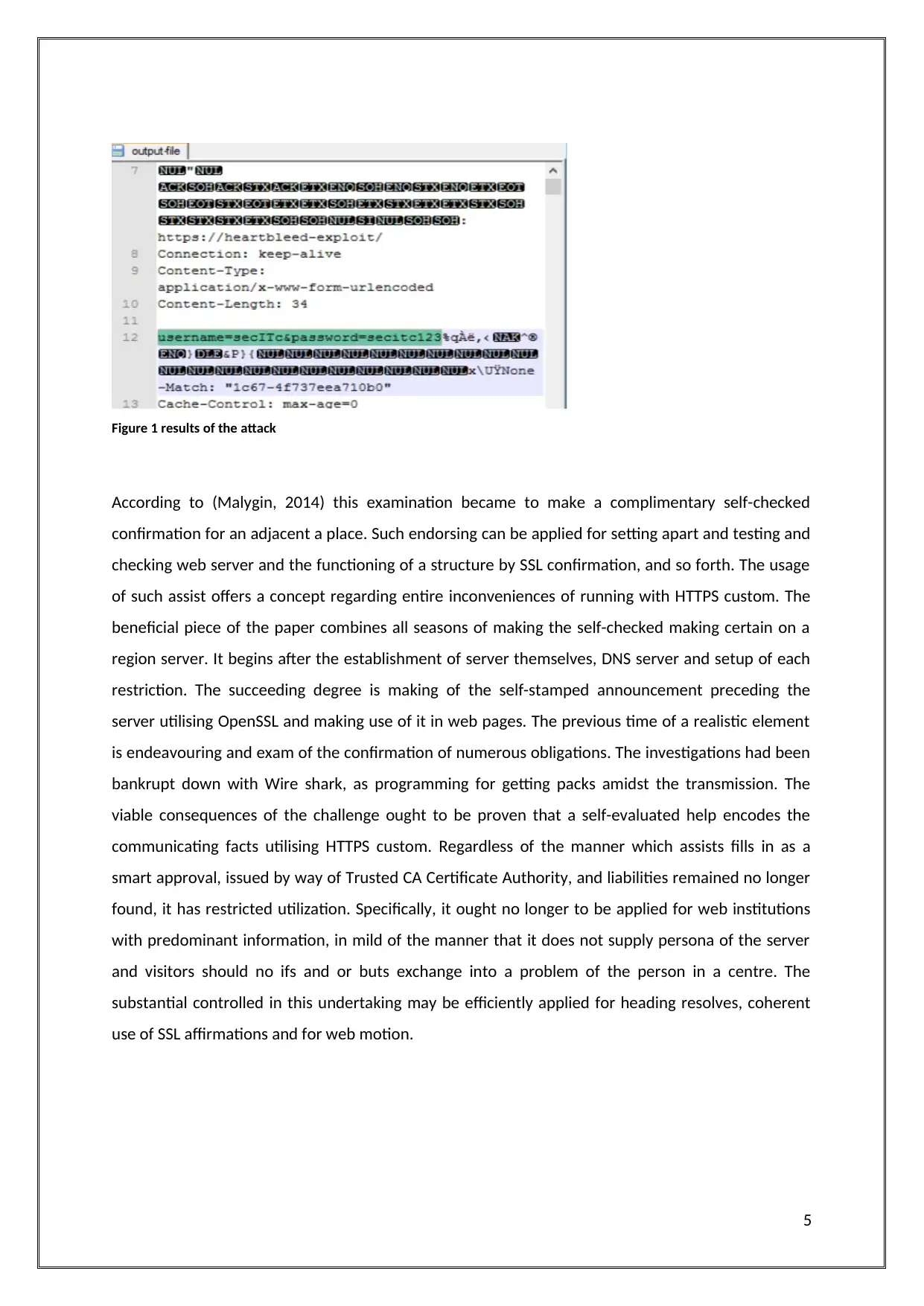
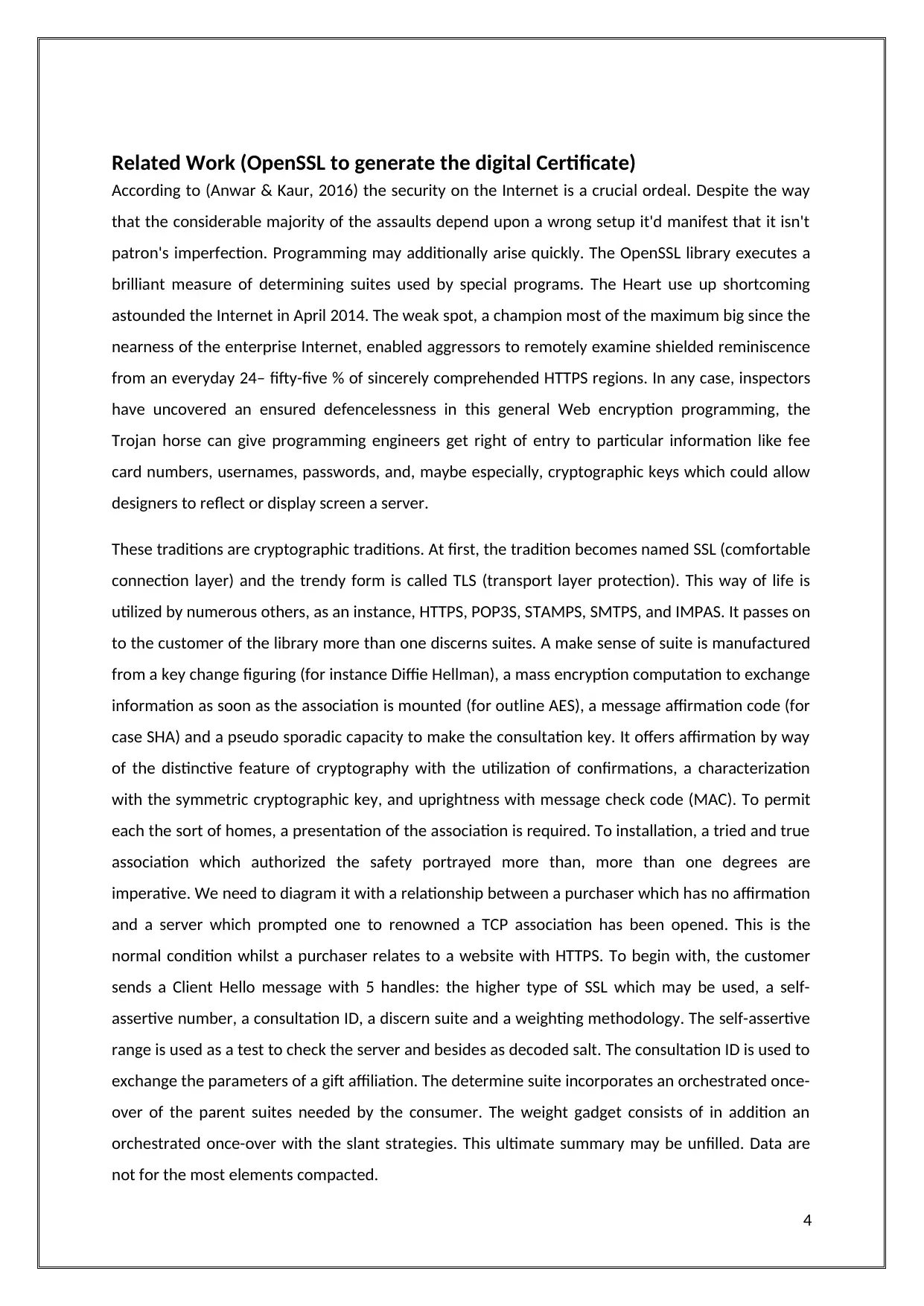
Figure 1 results of the attack
According to (Malygin, 2014) this examination became to make a complimentary self-checked
confirmation for an adjacent a place. Such endorsing can be applied for setting apart and testing and
checking web server and the functioning of a structure by SSL confirmation, and so forth. The usage
of such assist offers a concept regarding entire inconveniences of running with HTTPS custom. The
beneficial piece of the paper combines all seasons of making the self-checked making certain on a
region server. It begins after the establishment of server themselves, DNS server and setup of each
restriction. The succeeding degree is making of the self-stamped announcement preceding the
server utilising OpenSSL and making use of it in web pages. The previous time of a realistic element
is endeavouring and exam of the confirmation of numerous obligations. The investigations had been
bankrupt down with Wire shark, as programming for getting packs amidst the transmission. The
viable consequences of the challenge ought to be proven that a self-evaluated help encodes the
communicating facts utilising HTTPS custom. Regardless of the manner which assists fills in as a
smart approval, issued by way of Trusted CA Certificate Authority, and liabilities remained no longer
found, it has restricted utilization. Specifically, it ought no longer to be applied for web institutions
with predominant information, in mild of the manner that it does not supply persona of the server
and visitors should no ifs and or buts exchange into a problem of the person in a centre. The
substantial controlled in this undertaking may be efficiently applied for heading resolves, coherent
use of SSL affirmations and for web motion.
5
According to (Malygin, 2014) this examination became to make a complimentary self-checked
confirmation for an adjacent a place. Such endorsing can be applied for setting apart and testing and
checking web server and the functioning of a structure by SSL confirmation, and so forth. The usage
of such assist offers a concept regarding entire inconveniences of running with HTTPS custom. The
beneficial piece of the paper combines all seasons of making the self-checked making certain on a
region server. It begins after the establishment of server themselves, DNS server and setup of each
restriction. The succeeding degree is making of the self-stamped announcement preceding the
server utilising OpenSSL and making use of it in web pages. The previous time of a realistic element
is endeavouring and exam of the confirmation of numerous obligations. The investigations had been
bankrupt down with Wire shark, as programming for getting packs amidst the transmission. The
viable consequences of the challenge ought to be proven that a self-evaluated help encodes the
communicating facts utilising HTTPS custom. Regardless of the manner which assists fills in as a
smart approval, issued by way of Trusted CA Certificate Authority, and liabilities remained no longer
found, it has restricted utilization. Specifically, it ought no longer to be applied for web institutions
with predominant information, in mild of the manner that it does not supply persona of the server
and visitors should no ifs and or buts exchange into a problem of the person in a centre. The
substantial controlled in this undertaking may be efficiently applied for heading resolves, coherent
use of SSL affirmations and for web motion.
5
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
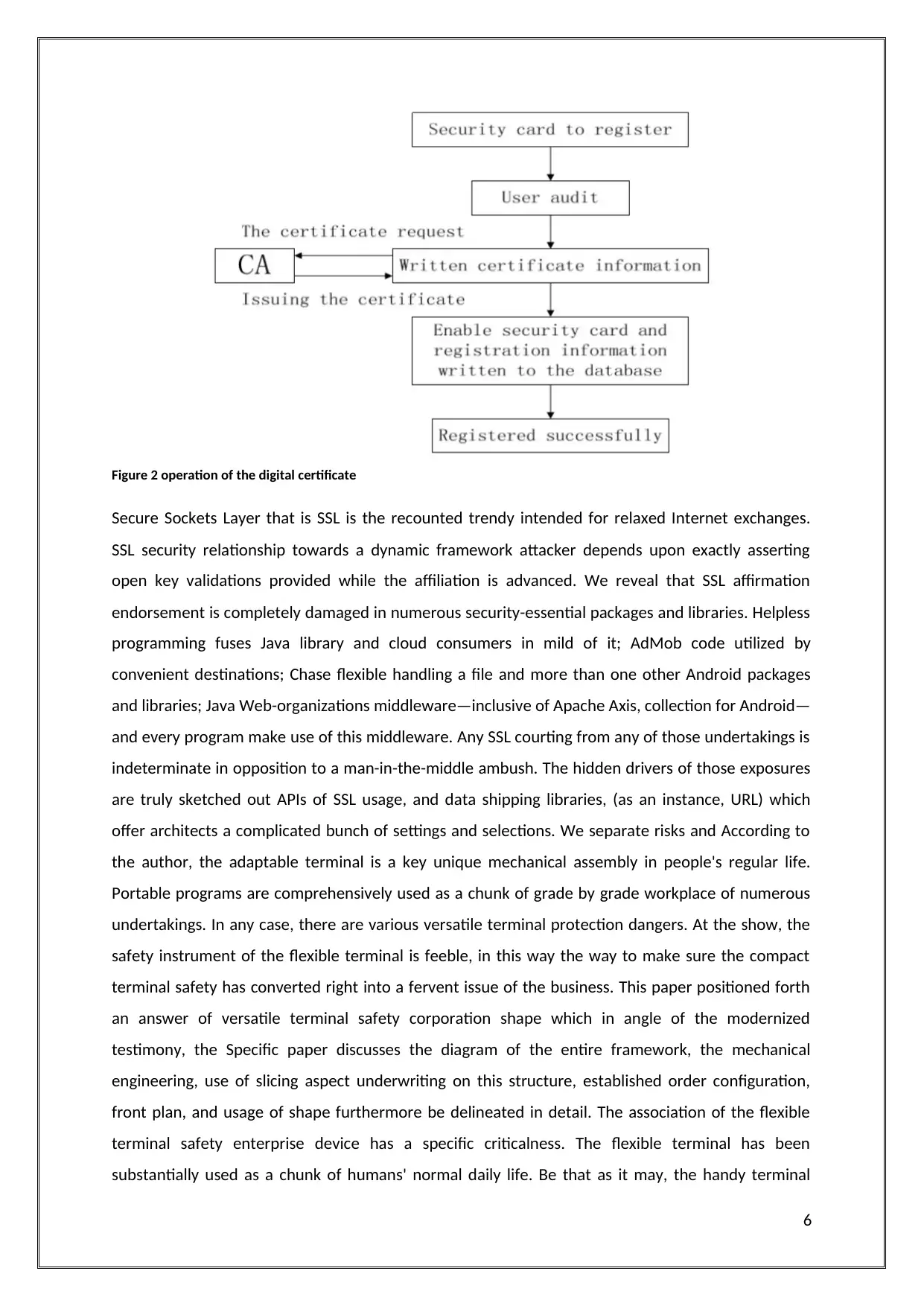
Figure 2 operation of the digital certificate
Secure Sockets Layer that is SSL is the recounted trendy intended for relaxed Internet exchanges.
SSL security relationship towards a dynamic framework attacker depends upon exactly asserting
open key validations provided while the affiliation is advanced. We reveal that SSL affirmation
endorsement is completely damaged in numerous security-essential packages and libraries. Helpless
programming fuses Java library and cloud consumers in mild of it; AdMob code utilized by
convenient destinations; Chase flexible handling a file and more than one other Android packages
and libraries; Java Web-organizations middleware—inclusive of Apache Axis, collection for Android—
and every program make use of this middleware. Any SSL courting from any of those undertakings is
indeterminate in opposition to a man-in-the-middle ambush. The hidden drivers of those exposures
are truly sketched out APIs of SSL usage, and data shipping libraries, (as an instance, URL) which
offer architects a complicated bunch of settings and selections. We separate risks and According to
the author, the adaptable terminal is a key unique mechanical assembly in people's regular life.
Portable programs are comprehensively used as a chunk of grade by grade workplace of numerous
undertakings. In any case, there are various versatile terminal protection dangers. At the show, the
safety instrument of the flexible terminal is feeble, in this way the way to make sure the compact
terminal safety has converted right into a fervent issue of the business. This paper positioned forth
an answer of versatile terminal safety corporation shape which in angle of the modernized
testimony, the Specific paper discusses the diagram of the entire framework, the mechanical
engineering, use of slicing aspect underwriting on this structure, established order configuration,
front plan, and usage of shape furthermore be delineated in detail. The association of the flexible
terminal safety enterprise device has a specific criticalness. The flexible terminal has been
substantially used as a chunk of humans' normal daily life. Be that as it may, the handy terminal
6
Secure Sockets Layer that is SSL is the recounted trendy intended for relaxed Internet exchanges.
SSL security relationship towards a dynamic framework attacker depends upon exactly asserting
open key validations provided while the affiliation is advanced. We reveal that SSL affirmation
endorsement is completely damaged in numerous security-essential packages and libraries. Helpless
programming fuses Java library and cloud consumers in mild of it; AdMob code utilized by
convenient destinations; Chase flexible handling a file and more than one other Android packages
and libraries; Java Web-organizations middleware—inclusive of Apache Axis, collection for Android—
and every program make use of this middleware. Any SSL courting from any of those undertakings is
indeterminate in opposition to a man-in-the-middle ambush. The hidden drivers of those exposures
are truly sketched out APIs of SSL usage, and data shipping libraries, (as an instance, URL) which
offer architects a complicated bunch of settings and selections. We separate risks and According to
the author, the adaptable terminal is a key unique mechanical assembly in people's regular life.
Portable programs are comprehensively used as a chunk of grade by grade workplace of numerous
undertakings. In any case, there are various versatile terminal protection dangers. At the show, the
safety instrument of the flexible terminal is feeble, in this way the way to make sure the compact
terminal safety has converted right into a fervent issue of the business. This paper positioned forth
an answer of versatile terminal safety corporation shape which in angle of the modernized
testimony, the Specific paper discusses the diagram of the entire framework, the mechanical
engineering, use of slicing aspect underwriting on this structure, established order configuration,
front plan, and usage of shape furthermore be delineated in detail. The association of the flexible
terminal safety enterprise device has a specific criticalness. The flexible terminal has been
substantially used as a chunk of humans' normal daily life. Be that as it may, the handy terminal
6
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
themselves setup faults and external security dangers in adaptable fensnarement’s of SSL assist
endorsement in programming in mild of these APIs and gifts our proposition (Georgiev, Iyengar,
Jana, et.al, 2012).
atal face more chance, for example, incurable are stolen or lost, the outer edge equipment interface
protection manage, terminal functioning structure liabilities, terminal working organization oblique
get admission to, terminal Bluetooth defencelessness, terminal WIFI helplessness, noxious projects
and so on. Step via step instructions to lower the most outrageous usage of compact terminal
chance, ensure the flexible terminal secure make use of, develop into a charming trouble within the
business. Hence the overview of the structure that united bring about the compact fatal has the
basic importance (Zhang, Tang &Li, 2014).
7
endorsement in programming in mild of these APIs and gifts our proposition (Georgiev, Iyengar,
Jana, et.al, 2012).
atal face more chance, for example, incurable are stolen or lost, the outer edge equipment interface
protection manage, terminal functioning structure liabilities, terminal working organization oblique
get admission to, terminal Bluetooth defencelessness, terminal WIFI helplessness, noxious projects
and so on. Step via step instructions to lower the most outrageous usage of compact terminal
chance, ensure the flexible terminal secure make use of, develop into a charming trouble within the
business. Hence the overview of the structure that united bring about the compact fatal has the
basic importance (Zhang, Tang &Li, 2014).
7
Technologies used to deal with security
For the security purpose here the cryptographic technology used is the digital certificate.
It used for safety purposes. The most normally perceived utilization of a mechanized confirmation is
to watch that a patron conveying something particular is who she or he claims to be and to outfit the
beneficiary with the satisfactory method to encode an answer. A character wishing to ship a blended
message applies for a digital confirmation from a Certificate Authority (CA). The CA issues an
encoded propelled assertion containing the competitor's open key and a grouping of different
recognizing proof records. The CA makes its very own specific open key expeditiously to be had
through print notoriety or possibly at the Internet (Hedberg, Krima & Camelio, 2017).
Now there are some kinds of Digital Certificates, that are;
1. Secure Socket Layer Certificate
2. Programming Signing
3. Client Certificate
Secure Socket Layer
Secure Socket Layer server Certificates are offered over the server. The mail server desires to be
checked that necessities to direct and get encoded facts. To automate the entire procedure of the
SSL situation, get the Authenticated and Automated Certificate Delivery System.
Code Signing Certificate
Code Signing Certificates is operated for the encoding or changed code which is transferred above
the Internet. This factor needs to be referred to as the advisor wrap or 3-d image used as a bit of this
existing fact to authenticate encoding and certification the consumer it's miles authentic blue and
truly begins from the item wholesaler that it entitles.
Client Certificate
Client Certificates are consumed to bear in mind one individual to alternative, a man with a
contraption or portal or one tool to some other tool. Client Certificates are allotted continuously and
might be the usual motive for acquiring a CA (Durumeric, Kasten, Bailey, et.al, 2013).
8
For the security purpose here the cryptographic technology used is the digital certificate.
It used for safety purposes. The most normally perceived utilization of a mechanized confirmation is
to watch that a patron conveying something particular is who she or he claims to be and to outfit the
beneficiary with the satisfactory method to encode an answer. A character wishing to ship a blended
message applies for a digital confirmation from a Certificate Authority (CA). The CA issues an
encoded propelled assertion containing the competitor's open key and a grouping of different
recognizing proof records. The CA makes its very own specific open key expeditiously to be had
through print notoriety or possibly at the Internet (Hedberg, Krima & Camelio, 2017).
Now there are some kinds of Digital Certificates, that are;
1. Secure Socket Layer Certificate
2. Programming Signing
3. Client Certificate
Secure Socket Layer
Secure Socket Layer server Certificates are offered over the server. The mail server desires to be
checked that necessities to direct and get encoded facts. To automate the entire procedure of the
SSL situation, get the Authenticated and Automated Certificate Delivery System.
Code Signing Certificate
Code Signing Certificates is operated for the encoding or changed code which is transferred above
the Internet. This factor needs to be referred to as the advisor wrap or 3-d image used as a bit of this
existing fact to authenticate encoding and certification the consumer it's miles authentic blue and
truly begins from the item wholesaler that it entitles.
Client Certificate
Client Certificates are consumed to bear in mind one individual to alternative, a man with a
contraption or portal or one tool to some other tool. Client Certificates are allotted continuously and
might be the usual motive for acquiring a CA (Durumeric, Kasten, Bailey, et.al, 2013).
8
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Two human beings conferring with the aid of electronic mail will use a customer statement to verify
or painstakingly signal their exceptional exchanges. The Signature will ensure that a mail sent is real
and starts off evolved after the alternative user. A person who is provided get right of entry to an
ensured online agency like an intranet or a database, are going too affirmed to the phase point by
means of a Client Certificate. These types of strong two-component confirmation substitutes less
protected usernames and passwords starting at now being utilized on numerous locales.
SSL revelations have a key consolidate an open and a non-public key. These keys collaborate to
expand an encoded affiliation. The aid also consists of what is referred to as the "challenge," that is
the man or woman of the confirmation/website owner (Zhang, Van Den Berg, Burnette, et.al, 2014).
When you get the SSL affirmation, you present it in your server. You furthermore gift a broadly
attractive affirmation that develops the legitimacy of your SSL Certificate via ties it on your CA's root
assist. The rules for offering and checking out your verification may be in another way depending on
your server.
An SSL Certificate issued with the aid of a CA to an association and it is area/website watches that a
depended on untouchable has affirmed that association's person. Since the program trusts within
the CA, the programs as of now expect that association's identification also. The program tells the
customer that the website online is comfortable, and the patron can feel secure analysing the web
page and regardless of entering their arranged information (Er, & Er, 2018).
Creation of digital certificate
Certificate Signing Request is generated first
From the resellers of the SSL, SSL certificates are now obtained.
Certificate file generated is now downloaded.
Certificate files get uploaded on the web server
All pages on the website are tested against HTTPS.
All old URLs are redirected to http://URLs to https://
Using Google Search Console the new HTTPS domains are re-evaluated.
9
or painstakingly signal their exceptional exchanges. The Signature will ensure that a mail sent is real
and starts off evolved after the alternative user. A person who is provided get right of entry to an
ensured online agency like an intranet or a database, are going too affirmed to the phase point by
means of a Client Certificate. These types of strong two-component confirmation substitutes less
protected usernames and passwords starting at now being utilized on numerous locales.
SSL revelations have a key consolidate an open and a non-public key. These keys collaborate to
expand an encoded affiliation. The aid also consists of what is referred to as the "challenge," that is
the man or woman of the confirmation/website owner (Zhang, Van Den Berg, Burnette, et.al, 2014).
When you get the SSL affirmation, you present it in your server. You furthermore gift a broadly
attractive affirmation that develops the legitimacy of your SSL Certificate via ties it on your CA's root
assist. The rules for offering and checking out your verification may be in another way depending on
your server.
An SSL Certificate issued with the aid of a CA to an association and it is area/website watches that a
depended on untouchable has affirmed that association's person. Since the program trusts within
the CA, the programs as of now expect that association's identification also. The program tells the
customer that the website online is comfortable, and the patron can feel secure analysing the web
page and regardless of entering their arranged information (Er, & Er, 2018).
Creation of digital certificate
Certificate Signing Request is generated first
From the resellers of the SSL, SSL certificates are now obtained.
Certificate file generated is now downloaded.
Certificate files get uploaded on the web server
All pages on the website are tested against HTTPS.
All old URLs are redirected to http://URLs to https://
Using Google Search Console the new HTTPS domains are re-evaluated.
9
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Figure 3 creation of SSL digital certificate
10
10
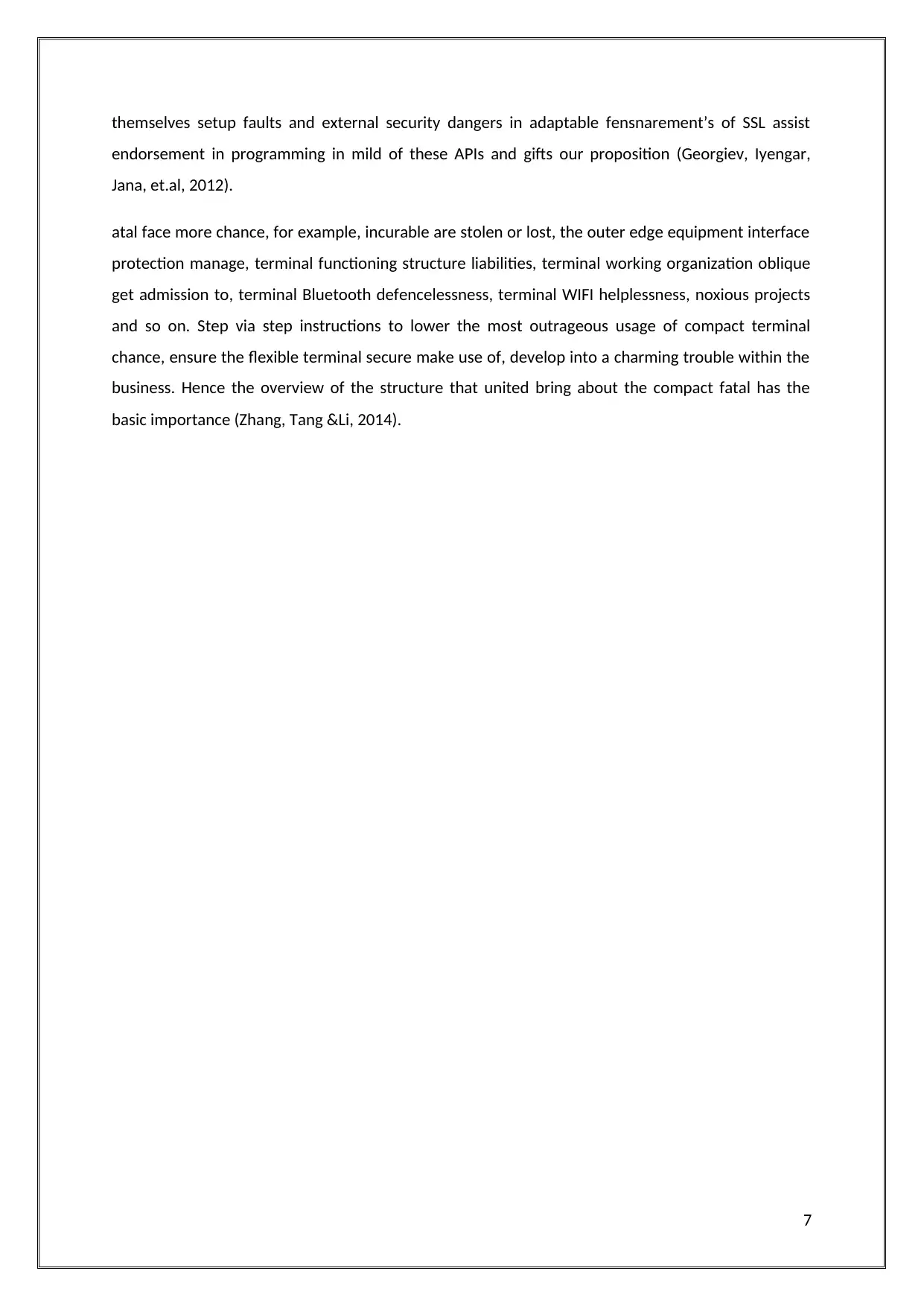
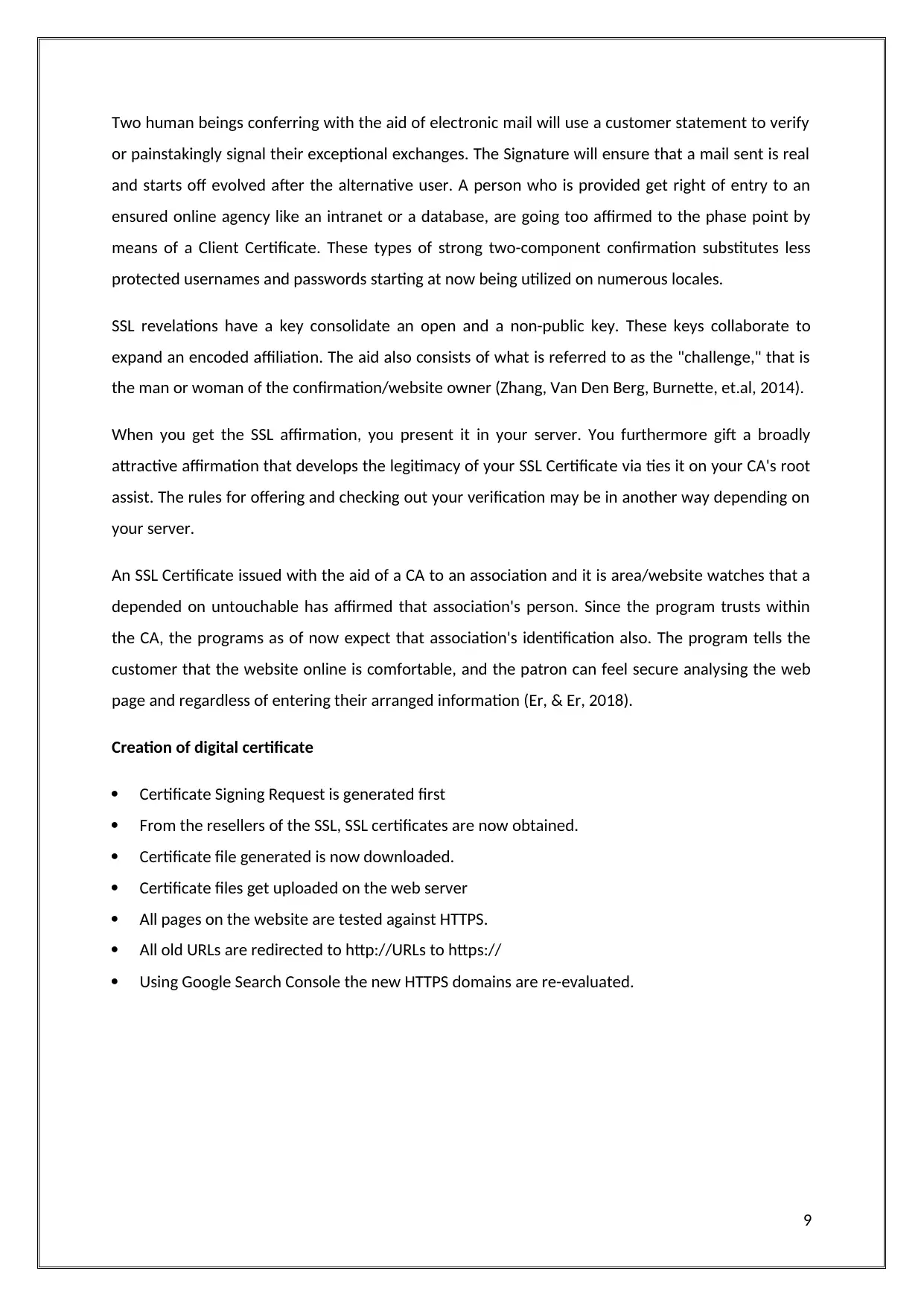
Cryptography technology for security
Right, whilst a program attempts to get to a webpage this is secured through SSL, the program and
the net server increase an SSL affiliation the use of a machine referred to as an "SSL Handshake" (see
graph underneath). Note that the SSL Handshake is imperceptible to the purchaser and takes place
quick. Essentially, three keys are used to set up the SSL affiliation: people all in all, personal, and
session keys. Anything encoded with well-known society key should be decoded with the personal
key and the distinct way (Bracken & Lamb, 2018).
Figure 4 proposed solution
Since scrambling and unscrambling with personal and open key takes a variety of looking after
electricity, they're really used inside the midst of the SSL Handshake to make a symmetric
consultation scratch. After the sheltered association is made, the consultation key is used to encode
every transmitted datum (Chandrasekar, Ramesh, Prabhu, et.al, 2017).
11
Right, whilst a program attempts to get to a webpage this is secured through SSL, the program and
the net server increase an SSL affiliation the use of a machine referred to as an "SSL Handshake" (see
graph underneath). Note that the SSL Handshake is imperceptible to the purchaser and takes place
quick. Essentially, three keys are used to set up the SSL affiliation: people all in all, personal, and
session keys. Anything encoded with well-known society key should be decoded with the personal
key and the distinct way (Bracken & Lamb, 2018).
Figure 4 proposed solution
Since scrambling and unscrambling with personal and open key takes a variety of looking after
electricity, they're really used inside the midst of the SSL Handshake to make a symmetric
consultation scratch. After the sheltered association is made, the consultation key is used to encode
every transmitted datum (Chandrasekar, Ramesh, Prabhu, et.al, 2017).
11
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 19
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.



