Evaluation Study Plan: Big Data Analytics in Cyber Security
VerifiedAdded on 2019/09/23
|5
|1172
|100
Report
AI Summary
This technology evaluation study plan focuses on big data analytics and its application in cyber security. It begins with an introduction highlighting the role of big data analytics in addressing cyber security risks, emphasizing its ability to analyze data, identify vulnerabilities, and strengthen security postures. The study presents research questions, such as the maturity of big data analytics in cyber security and its comparison with other data analytics methods. It outlines a methodology involving a procedural approach to address research questions, including the analysis of information assurance pillars like confidentiality and integrity. The plan also addresses limitations, such as potential for false conclusions from large datasets, and special considerations, such as the need to focus on security and privacy-related data. The study includes a timeline for events, from technology selection to final paper development, and provides references to relevant sources. The evaluation aims to provide a comprehensive understanding of big data analytics in cyber security, its capabilities, and its limitations.
Technology Evaluation Study Plan
Introduction
Technology evaluation study plan is a documented version of detailed content that emphasize the
basic and advanced characteristics of the selected technology. This technology evaluation plan is
developed as a case study for the selected technology such as Big data analytics. The critical
infrastructure which is addressed by the solution of big data analytics is cyber security.
Big data analytics provides the platform to analyze the related data from the cyber security area
to find out the new risks and exposures. The main features of big data analytics technology are
specified as follows.
Provides accurate and properly configured platform for the risks analysis for various
categories of cyber security attacks
Provides the intelligent platform to deduce the intelligence in the definition of the
processes and procedures to prevent the attacks of cyber security.
Capable to induce the confidence to security specialist to develop the robust and powerful
solution for the cyber security.
Strengthen cyber security postures and reveals the exposures by deep analysis of the
systems involved in cyber communication
Evaluation study with big data analytics technology brings the abundant knowledge for
identification of security risks and vulnerabilities, defining the intelligent environment by
applying the heuristics through the big data analytics for the various security risks and
uncertainties. A detailed case study is prepared here for the evaluation containing the various
questions to make evaluation of the reports for the mentioned technology such as big data
analytics. The case study contains the research questions, methods and limitation of the proposed
technology as big data analytics.
Research questions
Introduction
Technology evaluation study plan is a documented version of detailed content that emphasize the
basic and advanced characteristics of the selected technology. This technology evaluation plan is
developed as a case study for the selected technology such as Big data analytics. The critical
infrastructure which is addressed by the solution of big data analytics is cyber security.
Big data analytics provides the platform to analyze the related data from the cyber security area
to find out the new risks and exposures. The main features of big data analytics technology are
specified as follows.
Provides accurate and properly configured platform for the risks analysis for various
categories of cyber security attacks
Provides the intelligent platform to deduce the intelligence in the definition of the
processes and procedures to prevent the attacks of cyber security.
Capable to induce the confidence to security specialist to develop the robust and powerful
solution for the cyber security.
Strengthen cyber security postures and reveals the exposures by deep analysis of the
systems involved in cyber communication
Evaluation study with big data analytics technology brings the abundant knowledge for
identification of security risks and vulnerabilities, defining the intelligent environment by
applying the heuristics through the big data analytics for the various security risks and
uncertainties. A detailed case study is prepared here for the evaluation containing the various
questions to make evaluation of the reports for the mentioned technology such as big data
analytics. The case study contains the research questions, methods and limitation of the proposed
technology as big data analytics.
Research questions
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
There are so many research questions associated with the big data analytics as a technology for
the cyber security. These all research questions are mentioned as follows.
Is big data analytics is mature to apply in the field of information and cyber security?
If big data analytics is the intelligent technology to derive the research and development
of the cyber defense system then what are the various steps and modalities involved with
the process of big data analytics?
What are the difference between big data analytics and other data analytics methods in
the case of research and innovations?
How big data is collected for the analytics in the field of security and information
management?
What are the general aspects of the cyber security where the big data analytics provides
the platform to indentify different categories of risks and vulnerabilities.
How big data analytics strengthen the confidence of researchers for finding the optimum
solution for the cyber security.
Is big data analytics addresses all the five pillars of the information and cyber security
robustly? If it addresses all five pillars of security in both cases such as information
assurance and information security.
What are characteristics of big data analytics in case of the information confidentiality
and its various risks and exposure to be assessed?
What are risks and problems associated with cyber criminal when big data analytics
technology used for breaking all the security mechanisms in the field of cyber security?
What are security risks and vulnerabilities associated with critical infrastructure and how
the cyber criminal gains the accessibility by applying the intelligent mechanisms?
These all questions related with big data analytics and cyber security must be addressed in
evaluation process. The evaluation must ensure the proper solution of the individual question
which is presented from the review paper.
Methodology
the cyber security. These all research questions are mentioned as follows.
Is big data analytics is mature to apply in the field of information and cyber security?
If big data analytics is the intelligent technology to derive the research and development
of the cyber defense system then what are the various steps and modalities involved with
the process of big data analytics?
What are the difference between big data analytics and other data analytics methods in
the case of research and innovations?
How big data is collected for the analytics in the field of security and information
management?
What are the general aspects of the cyber security where the big data analytics provides
the platform to indentify different categories of risks and vulnerabilities.
How big data analytics strengthen the confidence of researchers for finding the optimum
solution for the cyber security.
Is big data analytics addresses all the five pillars of the information and cyber security
robustly? If it addresses all five pillars of security in both cases such as information
assurance and information security.
What are characteristics of big data analytics in case of the information confidentiality
and its various risks and exposure to be assessed?
What are risks and problems associated with cyber criminal when big data analytics
technology used for breaking all the security mechanisms in the field of cyber security?
What are security risks and vulnerabilities associated with critical infrastructure and how
the cyber criminal gains the accessibility by applying the intelligent mechanisms?
These all questions related with big data analytics and cyber security must be addressed in
evaluation process. The evaluation must ensure the proper solution of the individual question
which is presented from the review paper.
Methodology
The method or methodology for the study and evaluation system is procedural aspects to extract
the functional domain of the stated technology such as big data analytics with critical
infrastructure system like cyber security.
The research questions are stated to be addressed with specific process having the suitable
procedures of the technology which is taken to deploy for the assessment of various factors
associated with cyber security. First of all a clear and stepwise procedures must be incorporated
to solve all the stated question with optimal solution on the platform of given technology of big
data analytics. The analytical framework must include the problems such as five pillars of
information assurance and information security. The individual problems such as confidentiality,
availability, non repudiation, integrity and authentication of information assurance must be taken
under the mainstream analysis to find out the proper and appropriate solution by the technology
of big data analytics.
The big data technology and its different processes involved in the analytics that is employed to
identify all the risks and vulnerabilities hidden into the cyber system or information system ("Big
Data Analytics for Security Intelligence", 2013). After identification of risks and vulnerabilities
the assessment through the big data analytics are to be taken to determine the benefits and loss.
In this case the historical data for such type of risks and vulnerabilities are taken to measure the
exposure of the prospect of the cyber security (Sivarajah, Kamal, Irani, & Weerakkody, 2016).
At final stage the intelligent defense mechanisms and techniques are developed on the basis of
exposure level of individual risk and vulnerabilities.
Limitations and Special Consideration
The limitations of big data analytics technology has certain types of limitations to deploy with
the cyber security. These limitations are as follows.
Driving the conclusion from enormous volume of big data probably outcomes bogus and
false confidence can be derived in the predictive capability of the analyst.
The special consideration is required to include only those big data that has direct relation
with the security and privacy.
the functional domain of the stated technology such as big data analytics with critical
infrastructure system like cyber security.
The research questions are stated to be addressed with specific process having the suitable
procedures of the technology which is taken to deploy for the assessment of various factors
associated with cyber security. First of all a clear and stepwise procedures must be incorporated
to solve all the stated question with optimal solution on the platform of given technology of big
data analytics. The analytical framework must include the problems such as five pillars of
information assurance and information security. The individual problems such as confidentiality,
availability, non repudiation, integrity and authentication of information assurance must be taken
under the mainstream analysis to find out the proper and appropriate solution by the technology
of big data analytics.
The big data technology and its different processes involved in the analytics that is employed to
identify all the risks and vulnerabilities hidden into the cyber system or information system ("Big
Data Analytics for Security Intelligence", 2013). After identification of risks and vulnerabilities
the assessment through the big data analytics are to be taken to determine the benefits and loss.
In this case the historical data for such type of risks and vulnerabilities are taken to measure the
exposure of the prospect of the cyber security (Sivarajah, Kamal, Irani, & Weerakkody, 2016).
At final stage the intelligent defense mechanisms and techniques are developed on the basis of
exposure level of individual risk and vulnerabilities.
Limitations and Special Consideration
The limitations of big data analytics technology has certain types of limitations to deploy with
the cyber security. These limitations are as follows.
Driving the conclusion from enormous volume of big data probably outcomes bogus and
false confidence can be derived in the predictive capability of the analyst.
The special consideration is required to include only those big data that has direct relation
with the security and privacy.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Big data analytics poses much reliance on data not on the behavior, so that cyber security
attacker behavior pattern identification is not possible correctly (Jain, Gyanchandani, &
Khare, 2016).
The special consideration is required to make scope for the behavior pattern of attacker
analysis to find out the probabilistic future behavior to enhance security scope by big data
analytics.
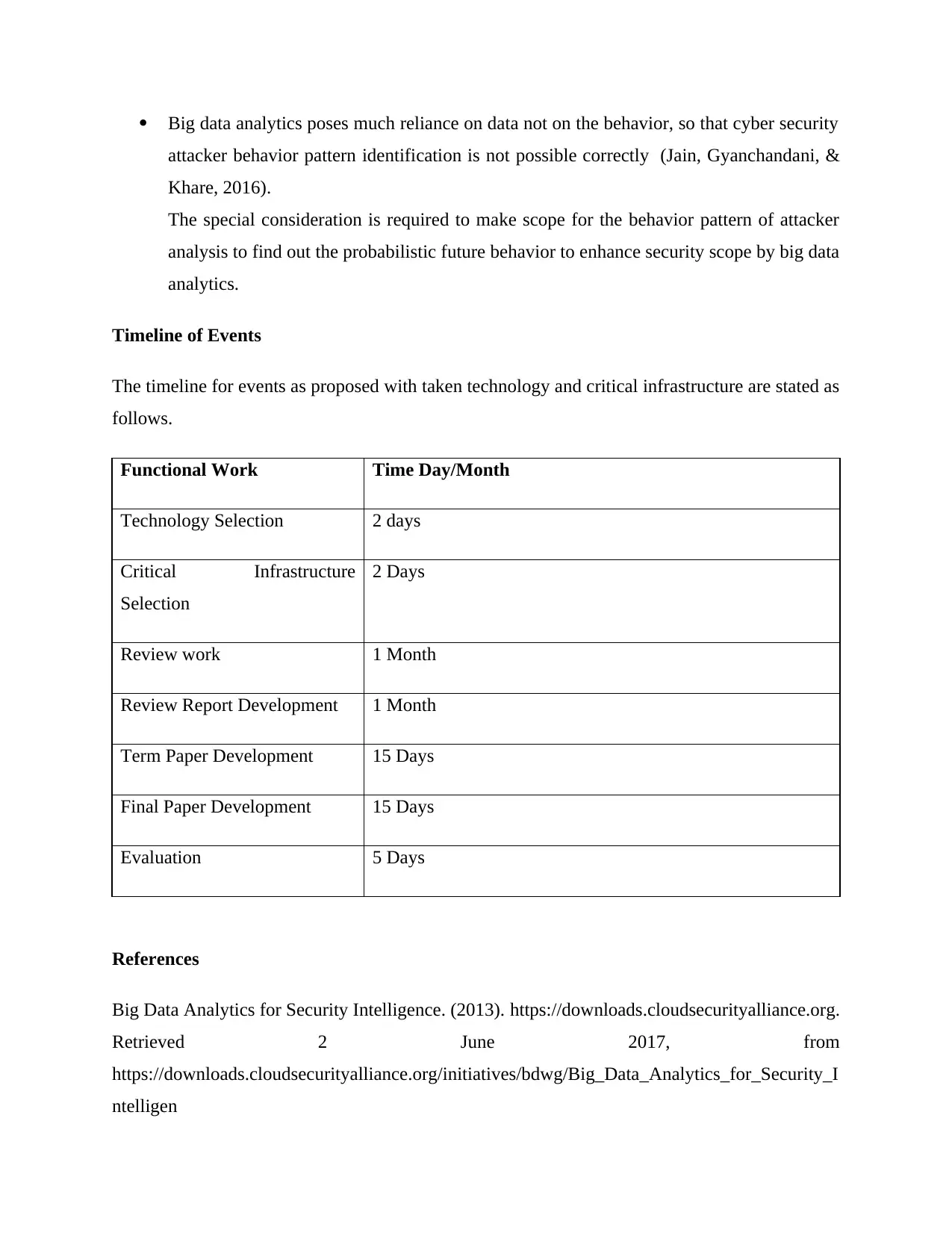
Timeline of Events
The timeline for events as proposed with taken technology and critical infrastructure are stated as
follows.
Functional Work Time Day/Month
Technology Selection 2 days
Critical Infrastructure
Selection
2 Days
Review work 1 Month
Review Report Development 1 Month
Term Paper Development 15 Days
Final Paper Development 15 Days
Evaluation 5 Days
References
Big Data Analytics for Security Intelligence. (2013). https://downloads.cloudsecurityalliance.org.
Retrieved 2 June 2017, from
https://downloads.cloudsecurityalliance.org/initiatives/bdwg/Big_Data_Analytics_for_Security_I
ntelligen
attacker behavior pattern identification is not possible correctly (Jain, Gyanchandani, &
Khare, 2016).
The special consideration is required to make scope for the behavior pattern of attacker
analysis to find out the probabilistic future behavior to enhance security scope by big data
analytics.
Timeline of Events
The timeline for events as proposed with taken technology and critical infrastructure are stated as
follows.
Functional Work Time Day/Month
Technology Selection 2 days
Critical Infrastructure
Selection
2 Days
Review work 1 Month
Review Report Development 1 Month
Term Paper Development 15 Days
Final Paper Development 15 Days
Evaluation 5 Days
References
Big Data Analytics for Security Intelligence. (2013). https://downloads.cloudsecurityalliance.org.
Retrieved 2 June 2017, from
https://downloads.cloudsecurityalliance.org/initiatives/bdwg/Big_Data_Analytics_for_Security_I
ntelligen
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Sivarajah, U., Kamal, M., Irani, Z., & Weerakkody, V. (2016). Critical analysis of Big Data
challenges and analytical methods. Sciencedirect.com. Retrieved 2 June 2017, from
http://www.sciencedirect.com/science/article/pii/S014829631630488X
Jain, P., Gyanchandani, M., & Khare, N. (2016). Big data privacy: a technological perspective
and review. Retrieved 2 June 2017, from
challenges and analytical methods. Sciencedirect.com. Retrieved 2 June 2017, from
http://www.sciencedirect.com/science/article/pii/S014829631630488X
Jain, P., Gyanchandani, M., & Khare, N. (2016). Big data privacy: a technological perspective
and review. Retrieved 2 June 2017, from
1 out of 5
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





