Cybersecurity, Compliance, and Business Continuity: A Detailed Report
VerifiedAdded on 2020/04/01
|15
|3572
|214
Report
AI Summary
This report delves into the critical aspects of cybersecurity, compliance, and business continuity, examining their importance in today's rapidly evolving business environment. The report begins with an abstract highlighting the challenges faced by the real estate sector, such as data security, and introduces the role of technology in addressing these issues. It then provides a SWOT analysis of RealEstate.com.au, evaluating its strengths, weaknesses, opportunities, and threats. The core of the report focuses on IT governance, discussing the COBIT framework, acceptable IT use, IT security procedures, and the implementation of hardware and software safeguards. The report also addresses the importance of risk management in cybersecurity, including prevention, detection, and containment strategies. It emphasizes the need for a proactive approach to security, covering both technical and human factors, and highlights the significance of senior management commitment and user training. The report concludes with a summary of key findings and recommendations for RealEstate.com.au, emphasizing the need for investment in robust IT infrastructure and adherence to global standards.

CyberSecurity and Business Continuity
1
CyberSecurity, Compliance, and Business Continuity
Name
Institution
Date
1
CyberSecurity, Compliance, and Business Continuity
Name
Institution
Date
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
CyberSecurity and Business Continuity
2
Abstract
Information Technology is currently viewed as a core component that is vital for
organizations to survive and thrive in the current quickly evolving, aggressive, business
conditions. Today, the real estate sector is pondering various difficulties, for example, deficiency
of talented labor, heightening undertaking cost, delayed development period, absence of
legitimate record-keeping methodologies, rivalry, loss of documents, duplication of information,
ease back access to information and utilization of obsolete methods for breaking down and
putting away information. Technology holds the way to address some of these issues, as well as a
guarantee for the part to respond to the changing economic situations all the more successfully
and productively (Sarsby, 2016). This examination intends to look at varieties in firms' reactions,
and how expanding utilization of Information, Communication &Technology (ICT) impact on
companies' operational and exercises that incorporate profitability, staffing structure, and
prerequisites, selection of working practices, nature of client administration, and deals.
Since 2010, harming cyber-attacks focusing private information, exchange privileged
insights, and other protected information has intensified. Hacking and malware is a notorious
method used by criminals and organized gangs to cause breaches to information systems.
Cyberspies and offenders are responsible for massive financial loses around the globe ever year.
Hacktivists steal proprietory information and disrupt normal business processes. An example is
the versatile malware that was posted by cybercriminals on iTunes to bait clients into
downloading maverick applications—which at that point spread from cell phones into corporate
systems. This paper focuses on how powerless our networked infrastructure are to cyber-attacks.
How governments in partnership with other players in the global stage try to achieve cyber-
security and mitigate the impact caused by cyber-criminals.
2
Abstract
Information Technology is currently viewed as a core component that is vital for
organizations to survive and thrive in the current quickly evolving, aggressive, business
conditions. Today, the real estate sector is pondering various difficulties, for example, deficiency
of talented labor, heightening undertaking cost, delayed development period, absence of
legitimate record-keeping methodologies, rivalry, loss of documents, duplication of information,
ease back access to information and utilization of obsolete methods for breaking down and
putting away information. Technology holds the way to address some of these issues, as well as a
guarantee for the part to respond to the changing economic situations all the more successfully
and productively (Sarsby, 2016). This examination intends to look at varieties in firms' reactions,
and how expanding utilization of Information, Communication &Technology (ICT) impact on
companies' operational and exercises that incorporate profitability, staffing structure, and
prerequisites, selection of working practices, nature of client administration, and deals.
Since 2010, harming cyber-attacks focusing private information, exchange privileged
insights, and other protected information has intensified. Hacking and malware is a notorious
method used by criminals and organized gangs to cause breaches to information systems.
Cyberspies and offenders are responsible for massive financial loses around the globe ever year.
Hacktivists steal proprietory information and disrupt normal business processes. An example is
the versatile malware that was posted by cybercriminals on iTunes to bait clients into
downloading maverick applications—which at that point spread from cell phones into corporate
systems. This paper focuses on how powerless our networked infrastructure are to cyber-attacks.
How governments in partnership with other players in the global stage try to achieve cyber-
security and mitigate the impact caused by cyber-criminals.
CyberSecurity and Business Continuity
3
Introduction
This paper is about cyber security and business continuity. Cybersecurity is the sum total
of the processes, activities, and techniques put in place to ensure IT assets and information are
kept safe from unauthorized access or modification by unauthorized users. Cybersecurity
provides both logical and physical security of computer systems, networks and data. Business
continuity is putting in place mechanisms to ensure continued operation of the firm in case there
is a breach of the system. Business continuity may provide partial continuity of the critical
systems in the event of an attack or even provide full functionality from the backup system put in
place.
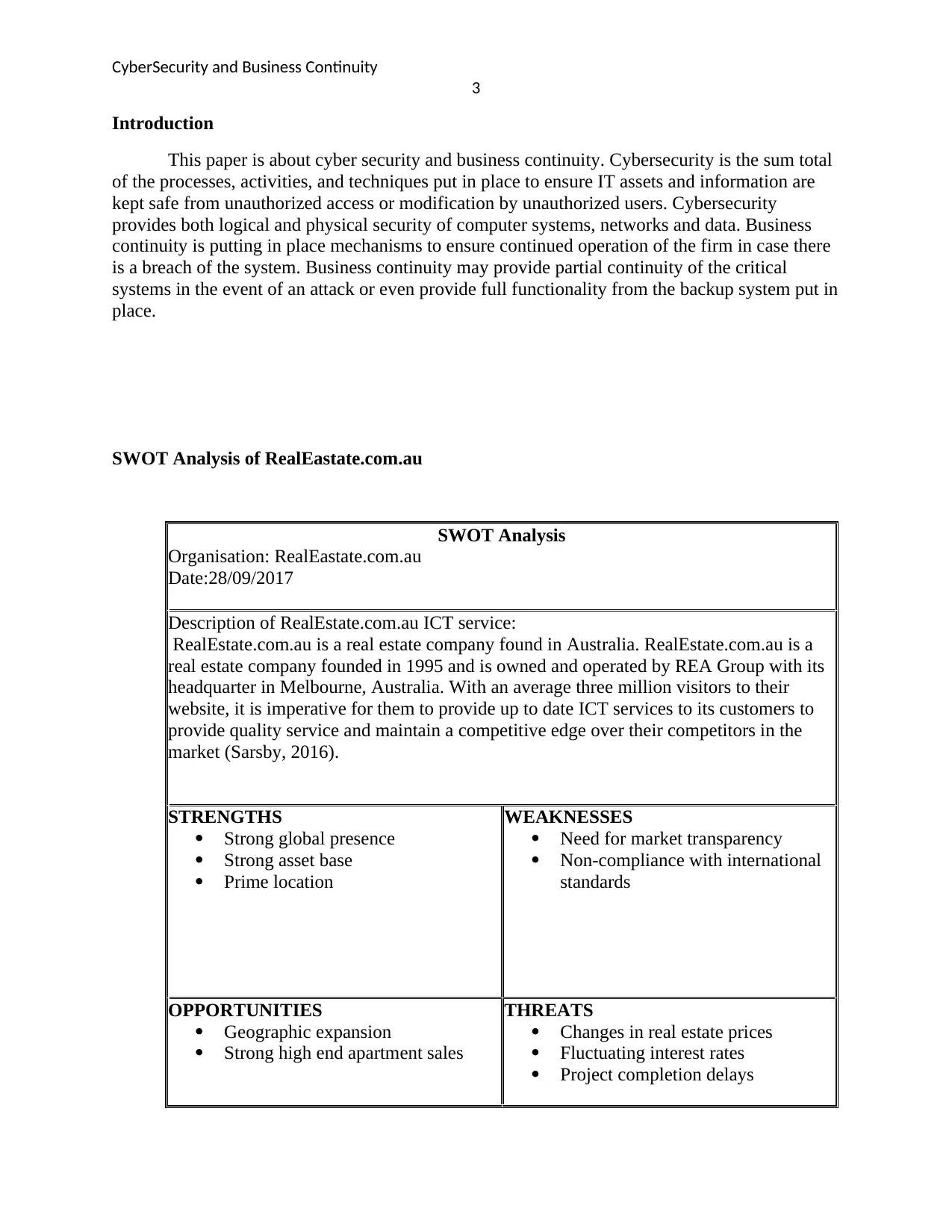
SWOT Analysis of RealEastate.com.au
SWOT Analysis
Organisation: RealEastate.com.au
Date:28/09/2017
Description of RealEstate.com.au ICT service:
RealEstate.com.au is a real estate company found in Australia. RealEstate.com.au is a
real estate company founded in 1995 and is owned and operated by REA Group with its
headquarter in Melbourne, Australia. With an average three million visitors to their
website, it is imperative for them to provide up to date ICT services to its customers to
provide quality service and maintain a competitive edge over their competitors in the
market (Sarsby, 2016).
STRENGTHS
Strong global presence
Strong asset base
Prime location
WEAKNESSES
Need for market transparency
Non-compliance with international
standards
OPPORTUNITIES
Geographic expansion
Strong high end apartment sales
THREATS
Changes in real estate prices
Fluctuating interest rates
Project completion delays
3
Introduction
This paper is about cyber security and business continuity. Cybersecurity is the sum total
of the processes, activities, and techniques put in place to ensure IT assets and information are
kept safe from unauthorized access or modification by unauthorized users. Cybersecurity
provides both logical and physical security of computer systems, networks and data. Business
continuity is putting in place mechanisms to ensure continued operation of the firm in case there
is a breach of the system. Business continuity may provide partial continuity of the critical
systems in the event of an attack or even provide full functionality from the backup system put in
place.
SWOT Analysis of RealEastate.com.au
SWOT Analysis
Organisation: RealEastate.com.au
Date:28/09/2017
Description of RealEstate.com.au ICT service:
RealEstate.com.au is a real estate company found in Australia. RealEstate.com.au is a
real estate company founded in 1995 and is owned and operated by REA Group with its
headquarter in Melbourne, Australia. With an average three million visitors to their
website, it is imperative for them to provide up to date ICT services to its customers to
provide quality service and maintain a competitive edge over their competitors in the
market (Sarsby, 2016).
STRENGTHS
Strong global presence
Strong asset base
Prime location
WEAKNESSES
Need for market transparency
Non-compliance with international
standards
OPPORTUNITIES
Geographic expansion
Strong high end apartment sales
THREATS
Changes in real estate prices
Fluctuating interest rates
Project completion delays
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
CyberSecurity and Business Continuity
4
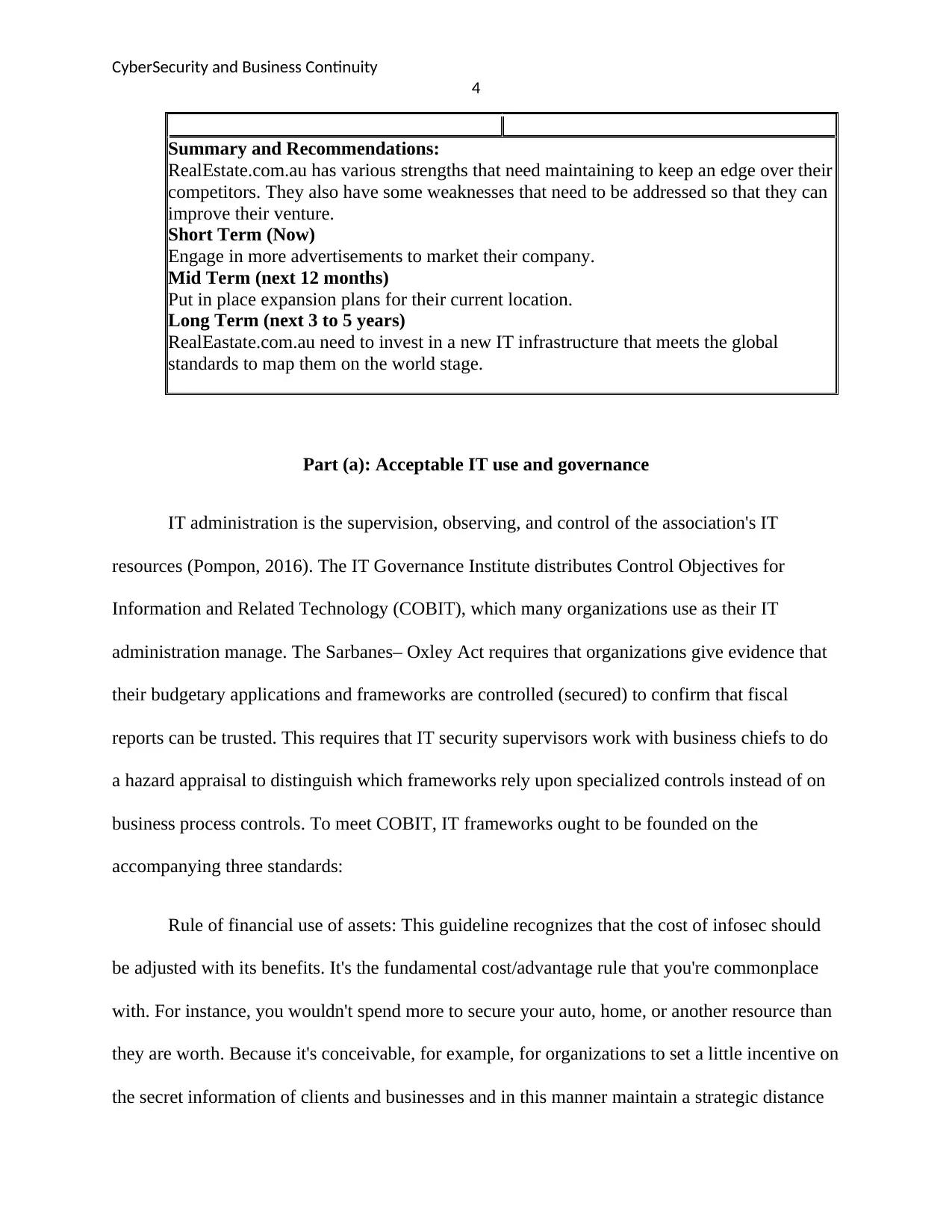
Summary and Recommendations:
RealEstate.com.au has various strengths that need maintaining to keep an edge over their
competitors. They also have some weaknesses that need to be addressed so that they can
improve their venture.
Short Term (Now)
Engage in more advertisements to market their company.
Mid Term (next 12 months)
Put in place expansion plans for their current location.
Long Term (next 3 to 5 years)
RealEastate.com.au need to invest in a new IT infrastructure that meets the global
standards to map them on the world stage.
Part (a): Acceptable IT use and governance
IT administration is the supervision, observing, and control of the association's IT
resources (Pompon, 2016). The IT Governance Institute distributes Control Objectives for
Information and Related Technology (COBIT), which many organizations use as their IT
administration manage. The Sarbanes– Oxley Act requires that organizations give evidence that
their budgetary applications and frameworks are controlled (secured) to confirm that fiscal
reports can be trusted. This requires that IT security supervisors work with business chiefs to do
a hazard appraisal to distinguish which frameworks rely upon specialized controls instead of on
business process controls. To meet COBIT, IT frameworks ought to be founded on the
accompanying three standards:
Rule of financial use of assets: This guideline recognizes that the cost of infosec should
be adjusted with its benefits. It's the fundamental cost/advantage rule that you're commonplace
with. For instance, you wouldn't spend more to secure your auto, home, or another resource than
they are worth. Because it's conceivable, for example, for organizations to set a little incentive on
the secret information of clients and businesses and in this manner maintain a strategic distance
4
Summary and Recommendations:
RealEstate.com.au has various strengths that need maintaining to keep an edge over their
competitors. They also have some weaknesses that need to be addressed so that they can
improve their venture.
Short Term (Now)
Engage in more advertisements to market their company.
Mid Term (next 12 months)
Put in place expansion plans for their current location.
Long Term (next 3 to 5 years)
RealEastate.com.au need to invest in a new IT infrastructure that meets the global
standards to map them on the world stage.
Part (a): Acceptable IT use and governance
IT administration is the supervision, observing, and control of the association's IT
resources (Pompon, 2016). The IT Governance Institute distributes Control Objectives for
Information and Related Technology (COBIT), which many organizations use as their IT
administration manage. The Sarbanes– Oxley Act requires that organizations give evidence that
their budgetary applications and frameworks are controlled (secured) to confirm that fiscal
reports can be trusted. This requires that IT security supervisors work with business chiefs to do
a hazard appraisal to distinguish which frameworks rely upon specialized controls instead of on
business process controls. To meet COBIT, IT frameworks ought to be founded on the
accompanying three standards:
Rule of financial use of assets: This guideline recognizes that the cost of infosec should
be adjusted with its benefits. It's the fundamental cost/advantage rule that you're commonplace
with. For instance, you wouldn't spend more to secure your auto, home, or another resource than
they are worth. Because it's conceivable, for example, for organizations to set a little incentive on
the secret information of clients and businesses and in this manner maintain a strategic distance
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
CyberSecurity and Business Continuity
5
from essential infosec safeguards, the following two standards endeavor to ensure that doesn't
occur.
Standard of lawfulness: This rule requires that organizations contribute in infosec to meet
least lawful necessities. This is a fundamental security standard, much the same as having hand
railings on stairways, fire quenchers, and caution frameworks.
Bookkeeping standards: These standards require that the uprightness, accessibility, and
dependability of information and data frameworks be kept up.
COBIT and IT Governance Best Practices.
COBIT framework is a top to bottom multi-layered way to deal with infosec. The
fundamental rule is that when one resistance layer comes up short, another layer gives assurance.
For instance, if a remote system's security were traded off, at that point having encrypted
information would, in any case, secure the information gave that the criminals couldn't decode it.
The achievement of an IT threat relies upon the dedication and association of official
administration and control strategies.
The same is valid for IT security. When senior administration demonstrates its sense of
duty regarding IT security, it moves toward becoming essential to others too. This infosec tone
makes users mindful that shaky practices and oversights won't go on without serious
consequences. Hence, an IT security and interior control display starts with senior administration
responsibility and support (Pompon, 2016).
Stage 1: Senior administration duty and support. Senior supervisors are expected to effect
and look after security. This can be effected by implementing internal and external controls.
5
from essential infosec safeguards, the following two standards endeavor to ensure that doesn't
occur.
Standard of lawfulness: This rule requires that organizations contribute in infosec to meet
least lawful necessities. This is a fundamental security standard, much the same as having hand
railings on stairways, fire quenchers, and caution frameworks.
Bookkeeping standards: These standards require that the uprightness, accessibility, and
dependability of information and data frameworks be kept up.
COBIT and IT Governance Best Practices.
COBIT framework is a top to bottom multi-layered way to deal with infosec. The
fundamental rule is that when one resistance layer comes up short, another layer gives assurance.
For instance, if a remote system's security were traded off, at that point having encrypted
information would, in any case, secure the information gave that the criminals couldn't decode it.
The achievement of an IT threat relies upon the dedication and association of official
administration and control strategies.
The same is valid for IT security. When senior administration demonstrates its sense of
duty regarding IT security, it moves toward becoming essential to others too. This infosec tone
makes users mindful that shaky practices and oversights won't go on without serious
consequences. Hence, an IT security and interior control display starts with senior administration
responsibility and support (Pompon, 2016).
Stage 1: Senior administration duty and support. Senior supervisors are expected to effect
and look after security. This can be effected by implementing internal and external controls.
CyberSecurity and Business Continuity
6
Inward control is a procedure intended at giving sensible confirmation of robust internal
operations whereas external controls protect the organization from external threats.
Stage 2: Acceptable use approaches and IT security preparing. Building a feasible IT
security program is a preparation to guaranteeing that all players know about and comprehend
them. The more noteworthy the comprehension of how security influences generation levels,
client and provider connections, income streams, and administration's risk, the greater security
will be fused into business ventures and proposition. Most basic is an acceptable use policy
(AUP) that advises users of their obligations. An AUP is required for two reasons: (1) to
counteract misuse of data and hardware assets; and (2) to lessen introduction to fines, sanctions,
and legitimate risks. To be powerful, the AUP needs to characterize users' duties, acceptable and
unacceptable activities, and outcomes of rebelliousness.
Email, Internet, and hardware AUPs ought to be thought of as an augmentation of other
corporate arrangements, for example, those that address physical wellbeing, approach
opportunity, badgering, and segregation.
Stage 3: IT Security Procedures and Enforcement. If users' exercises are not observed for
consistence, the AUP is useless. Therefore, the following stage is meant to check whether AUP
techniques are prepared and implemented. Poor implementation of security can expose a
business to huge financial loses in case their defenses are breached. Security depends on the
advanced resources' hazard introduction. The hazard introduction demonstrate for advanced
resources is contained the five components.
Another hazard evaluation technique is the business impact examination (BIA). BIA is an
activity that decides the impact of losing the help or accessibility of an asset. For instance, for the
6
Inward control is a procedure intended at giving sensible confirmation of robust internal
operations whereas external controls protect the organization from external threats.
Stage 2: Acceptable use approaches and IT security preparing. Building a feasible IT
security program is a preparation to guaranteeing that all players know about and comprehend
them. The more noteworthy the comprehension of how security influences generation levels,
client and provider connections, income streams, and administration's risk, the greater security
will be fused into business ventures and proposition. Most basic is an acceptable use policy
(AUP) that advises users of their obligations. An AUP is required for two reasons: (1) to
counteract misuse of data and hardware assets; and (2) to lessen introduction to fines, sanctions,
and legitimate risks. To be powerful, the AUP needs to characterize users' duties, acceptable and
unacceptable activities, and outcomes of rebelliousness.
Email, Internet, and hardware AUPs ought to be thought of as an augmentation of other
corporate arrangements, for example, those that address physical wellbeing, approach
opportunity, badgering, and segregation.
Stage 3: IT Security Procedures and Enforcement. If users' exercises are not observed for
consistence, the AUP is useless. Therefore, the following stage is meant to check whether AUP
techniques are prepared and implemented. Poor implementation of security can expose a
business to huge financial loses in case their defenses are breached. Security depends on the
advanced resources' hazard introduction. The hazard introduction demonstrate for advanced
resources is contained the five components.
Another hazard evaluation technique is the business impact examination (BIA). BIA is an
activity that decides the impact of losing the help or accessibility of an asset. For instance, for the
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
CyberSecurity and Business Continuity
7
vast majority, the passing of a cell phone would have a more prominent impact than the loss of
an advanced camera. BIA distinguishes the primary assets projected to recover, and organizes
the recovery of procedures and auxiliary structures.
A BIA should be refreshed as new dangers to IT rise. After the hazard presentation of
computerized resources has been assessed, at that point educated choices about interests in
infosec can be made.
Stage 4: Hardware and Software. Usage of programming and hardware equipment is expected
to help and authorize the AUP and secure practices. Remember that security is a continous
process and not a one-time affair that can be settled with hardware or software. Equipment and
programming security guards cannot however protect against human errors. One of the greatest
oversights chiefs make is thinking little of IT vulnerabilities also, dangers. Most specialists use
their portable PCs and mobiles for both work and relaxation, and in a period of multitasking,
they regularly do both at the same time. Off time or, then again the off-site use of gadgets stays
hazardous because, in spite of arrangements, workers proceed to participate in perilous on the
web and correspondence propensities. Those propensities make them a powerless connection in
an association's strong security efforts. These dangers can be named inadvertent or deliberate.
Accidental dangers fall into three noteworthy classifications: human blunders, ecological
hazards, and computer system failures.
Human errors can arise from the use of assets. They can also occur amid programming,
testing, or information section. Failure to change default passwords on a firewalls or neglecting
to patch software create loopholes. Human mistakes are usually as a result of poor training or
7
vast majority, the passing of a cell phone would have a more prominent impact than the loss of
an advanced camera. BIA distinguishes the primary assets projected to recover, and organizes
the recovery of procedures and auxiliary structures.
A BIA should be refreshed as new dangers to IT rise. After the hazard presentation of
computerized resources has been assessed, at that point educated choices about interests in
infosec can be made.
Stage 4: Hardware and Software. Usage of programming and hardware equipment is expected
to help and authorize the AUP and secure practices. Remember that security is a continous
process and not a one-time affair that can be settled with hardware or software. Equipment and
programming security guards cannot however protect against human errors. One of the greatest
oversights chiefs make is thinking little of IT vulnerabilities also, dangers. Most specialists use
their portable PCs and mobiles for both work and relaxation, and in a period of multitasking,
they regularly do both at the same time. Off time or, then again the off-site use of gadgets stays
hazardous because, in spite of arrangements, workers proceed to participate in perilous on the
web and correspondence propensities. Those propensities make them a powerless connection in
an association's strong security efforts. These dangers can be named inadvertent or deliberate.
Accidental dangers fall into three noteworthy classifications: human blunders, ecological
hazards, and computer system failures.
Human errors can arise from the use of assets. They can also occur amid programming,
testing, or information section. Failure to change default passwords on a firewalls or neglecting
to patch software create loopholes. Human mistakes are usually as a result of poor training or
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
CyberSecurity and Business Continuity
8
unconscious users reacting to phishing or overlooking security strategies. Human mistakes
constitute the largest part of an inner control and infosec issues.
Ecological dangers incorporate volcanoes, tremors, snow squalls, surges, control
disappointments or, then again solid changes, fires (the most well-known peril), damaged
aerating and cooling, blasts, radioactive aftermath, and water-cooling-framework
disappointments. Notwithstanding the essential harm, PC assets can be harmed by reactions, for
example, smoke and water. Such risks may disturb typical PC operations and result in long
holding up periods and over the top expenses while PC projects and information records are
reproduced.
Computer system failures can happen as the aftereffect of poor assembling, flawed
materials, and obsolete or ineffectively looked after systems (Pompon, 2016). Unexpected
glitches can likewise occur for other reasons, running from the absence of experience to lacking
testing. Cases of purposeful dangers incorporate burglary of information; wrong use of
information (e.g., controlling data sources); breach of centralized server PC time; robbery of gear
or potentially programs; consider control in taking care of, entering, preparing, exchanging, or
programming information; work strikes, mobs, or harm; pernicious harm to PC assets;
demolition from viruses and comparable assaults; and different PC abuses and Internet
misrepresentation.
Part (b): Information Communication Technology Risk Management
Its target security administration rehearses to guard the greater part of the segments of a
data framework, particularly information, programming applications, equipment, and systems.
Before they settle on any choices concerning barriers, individuals in charge of security must
8
unconscious users reacting to phishing or overlooking security strategies. Human mistakes
constitute the largest part of an inner control and infosec issues.
Ecological dangers incorporate volcanoes, tremors, snow squalls, surges, control
disappointments or, then again solid changes, fires (the most well-known peril), damaged
aerating and cooling, blasts, radioactive aftermath, and water-cooling-framework
disappointments. Notwithstanding the essential harm, PC assets can be harmed by reactions, for
example, smoke and water. Such risks may disturb typical PC operations and result in long
holding up periods and over the top expenses while PC projects and information records are
reproduced.
Computer system failures can happen as the aftereffect of poor assembling, flawed
materials, and obsolete or ineffectively looked after systems (Pompon, 2016). Unexpected
glitches can likewise occur for other reasons, running from the absence of experience to lacking
testing. Cases of purposeful dangers incorporate burglary of information; wrong use of
information (e.g., controlling data sources); breach of centralized server PC time; robbery of gear
or potentially programs; consider control in taking care of, entering, preparing, exchanging, or
programming information; work strikes, mobs, or harm; pernicious harm to PC assets;
demolition from viruses and comparable assaults; and different PC abuses and Internet
misrepresentation.
Part (b): Information Communication Technology Risk Management
Its target security administration rehearses to guard the greater part of the segments of a
data framework, particularly information, programming applications, equipment, and systems.
Before they settle on any choices concerning barriers, individuals in charge of security must
CyberSecurity and Business Continuity
9
comprehend the necessities and operations of the business, which frame the reason for a tweaked
protection procedure. In the following segment, we portray the real resistance methodologies.
The guard technique and controls that ought to be utilized rely upon what should be secured and
the money-saving advantage analysis. That is, organizations should neither under-contribute nor
over-contribute when implementing security techniques.
Avoidance and discouragement. Legitimately composed controls may keep blunders from
happening, stop offenders from assaulting the framework, and, even better, deny access to
unapproved people. These are the most alluring controls.
Identification. Like a fire, the prior an assault is distinguished, the less demanding it is to
battle, what's more, the less harm is finished. Discovery can be performed much of the time by
utilizing exceptional analytic programming, at a negligible cost.
Contain the harm. This goal is to limit the impact of misfortunes once a breakdown has
happened. This procedure is likewise called mitigation. This can be proficient, for instance, by
including a fault tolerant system that grants operation in a corrupted mode until the point that full
recovery is made. In the event a fault tolerant system does not exist, a fast and perhaps expensive
recovery process must occur. Clients need their systems back in operation as quickly as possible.
Recuperation. A recuperation design discloses how to settle a breached information
system as rapidly as could reasonably be expected. Supplanting as opposed to restoring segments
is one course to swift restoration.
Revision. Adjusting the reasons for harmed frameworks can keep the issue from
happening once more.
9
comprehend the necessities and operations of the business, which frame the reason for a tweaked
protection procedure. In the following segment, we portray the real resistance methodologies.
The guard technique and controls that ought to be utilized rely upon what should be secured and
the money-saving advantage analysis. That is, organizations should neither under-contribute nor
over-contribute when implementing security techniques.
Avoidance and discouragement. Legitimately composed controls may keep blunders from
happening, stop offenders from assaulting the framework, and, even better, deny access to
unapproved people. These are the most alluring controls.
Identification. Like a fire, the prior an assault is distinguished, the less demanding it is to
battle, what's more, the less harm is finished. Discovery can be performed much of the time by
utilizing exceptional analytic programming, at a negligible cost.
Contain the harm. This goal is to limit the impact of misfortunes once a breakdown has
happened. This procedure is likewise called mitigation. This can be proficient, for instance, by
including a fault tolerant system that grants operation in a corrupted mode until the point that full
recovery is made. In the event a fault tolerant system does not exist, a fast and perhaps expensive
recovery process must occur. Clients need their systems back in operation as quickly as possible.
Recuperation. A recuperation design discloses how to settle a breached information
system as rapidly as could reasonably be expected. Supplanting as opposed to restoring segments
is one course to swift restoration.
Revision. Adjusting the reasons for harmed frameworks can keep the issue from
happening once more.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
CyberSecurity and Business Continuity
10
Mindfulness and consistence. All players must be instructed about the risks to
information systems assets and should follow the security tenets and controls.
A safeguard methodology is likewise going to require a few controls. General controls
are built up to ensure the framework paying little heed to the particular application. For instance,
securing equipment and controlling access to the server farm are autonomous of the particular
application. Application controls are shields that are proposed to secure particular applications.
General controls are physical controls, access controls, information security controls,
correspondence arrange controls and administrative controls.
Physical controls. Physical security alludes to the protection of hardware resources. This
incorporates ensuring physical property, for example, PCs, server farms, programming, manuals,
and systems. It gives assurance against most regular perils and additionally against some human
dangers. Proper physical security may incorporate a few controls, for example, the
accompanying:
• Appropriate outline of the server farm. For instance, the server farm ought to be
noncombustible also, waterproof.
• Shielding against electromagnetic fields
• Good fire avoidance, location, and smothering frameworks, including sprinkler
frameworks, water pumps, and satisfactory waste offices
• Emergency control shutoff and reinforcement batteries, which must be kept up in
operational condition
• Properly composed and kept up aerating and cooling frameworks
10
Mindfulness and consistence. All players must be instructed about the risks to
information systems assets and should follow the security tenets and controls.
A safeguard methodology is likewise going to require a few controls. General controls
are built up to ensure the framework paying little heed to the particular application. For instance,
securing equipment and controlling access to the server farm are autonomous of the particular
application. Application controls are shields that are proposed to secure particular applications.
General controls are physical controls, access controls, information security controls,
correspondence arrange controls and administrative controls.
Physical controls. Physical security alludes to the protection of hardware resources. This
incorporates ensuring physical property, for example, PCs, server farms, programming, manuals,
and systems. It gives assurance against most regular perils and additionally against some human
dangers. Proper physical security may incorporate a few controls, for example, the
accompanying:
• Appropriate outline of the server farm. For instance, the server farm ought to be
noncombustible also, waterproof.
• Shielding against electromagnetic fields
• Good fire avoidance, location, and smothering frameworks, including sprinkler
frameworks, water pumps, and satisfactory waste offices
• Emergency control shutoff and reinforcement batteries, which must be kept up in
operational condition
• Properly composed and kept up aerating and cooling frameworks
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
CyberSecurity and Business Continuity
11
• Motion-locator alerts that distinguish physical interruption
Access Control is the administration of who is and is not approved to utilize an
organization's equipment and software. Access control techniques, for example, firewalls also,
get to control records, limit access to a system, database, document, or information. It is the real
barrier line against unapproved insiders and additionally outsiders. Access control includes
approval (having the privilege to access) and verification, which is additionally called client
distinguishing proof (demonstrating that the client is who he claims to be).
Verification strategies include:
• Something just the client knows, for example, a secret word
• Something just the client has, for instance, a brilliant card or a token
• Something just the client is, for example, a mark, voice, unique finger impression, or
retinal (eye) examine; actualized employing biometric controls, which can be physical or
behavioral
Biometric Control is a digital strategy for confirming the personality of a man, in light of
physical or behavioral attributes. For instance, different mark scanners are utilized for ID. Most
biometric frameworks are checked against a stored profile. The most regular biometrics are:
• Thumbprint or unique mark.
• Retinal output.
Authoritative Controls. While the beforehand examined general controls are specialized
in nature, administrative controls manage to issue rules and observing consistence with the rules.
11
• Motion-locator alerts that distinguish physical interruption
Access Control is the administration of who is and is not approved to utilize an
organization's equipment and software. Access control techniques, for example, firewalls also,
get to control records, limit access to a system, database, document, or information. It is the real
barrier line against unapproved insiders and additionally outsiders. Access control includes
approval (having the privilege to access) and verification, which is additionally called client
distinguishing proof (demonstrating that the client is who he claims to be).
Verification strategies include:
• Something just the client knows, for example, a secret word
• Something just the client has, for instance, a brilliant card or a token
• Something just the client is, for example, a mark, voice, unique finger impression, or
retinal (eye) examine; actualized employing biometric controls, which can be physical or
behavioral
Biometric Control is a digital strategy for confirming the personality of a man, in light of
physical or behavioral attributes. For instance, different mark scanners are utilized for ID. Most
biometric frameworks are checked against a stored profile. The most regular biometrics are:
• Thumbprint or unique mark.
• Retinal output.
Authoritative Controls. While the beforehand examined general controls are specialized
in nature, administrative controls manage to issue rules and observing consistence with the rules.
CyberSecurity and Business Continuity
12
Endpoint Security and Control. Numerous chiefs think little of business hazard postured
by decoded versatile capacity gadgets—which are cases of endpoints.
Business information is frequently carried on thumb drives, cell phones, and removable
media without consent, oversight, or adequate assurance against misfortune or burglary.
Handhelds and convenient stockpiling gadgets put touchy information in danger. According to
the statistical surveying firm Applied Research-West, three out of four specialists’ spare
corporate information on thumb drives. As per their examination, 25 percent spare client records,
17 percent store money related information, and 15 percent store strategies for success on thumb
drives, however under 50 percent of organizations routinely scramble those drives and even less
reliably secure information replicated onto cell phones.
Convenient gadgets that store secret client or money related information must be ensured
regardless of who possesses them- workers or the organization. If there are no security measures
to secure handhelds or other versatile/convenient capacity, information must not be put away on
them since it opens the organization to obligation, claims, and fines. For little organizations, a
solitary information rupture could bankrupt the organization.
Part (c): Business Continuity
Disaster recuperation is the chain of occasions connecting the business coherence want to
assurance what's more, to recovery. The following are some critical contemplation about the
procedure:
• The reason for business progression design is to keep the company continuity incase a
breach happens. Each capacity in the business ought to have a legitimate recovery plan
layout.
12
Endpoint Security and Control. Numerous chiefs think little of business hazard postured
by decoded versatile capacity gadgets—which are cases of endpoints.
Business information is frequently carried on thumb drives, cell phones, and removable
media without consent, oversight, or adequate assurance against misfortune or burglary.
Handhelds and convenient stockpiling gadgets put touchy information in danger. According to
the statistical surveying firm Applied Research-West, three out of four specialists’ spare
corporate information on thumb drives. As per their examination, 25 percent spare client records,
17 percent store money related information, and 15 percent store strategies for success on thumb
drives, however under 50 percent of organizations routinely scramble those drives and even less
reliably secure information replicated onto cell phones.
Convenient gadgets that store secret client or money related information must be ensured
regardless of who possesses them- workers or the organization. If there are no security measures
to secure handhelds or other versatile/convenient capacity, information must not be put away on
them since it opens the organization to obligation, claims, and fines. For little organizations, a
solitary information rupture could bankrupt the organization.
Part (c): Business Continuity
Disaster recuperation is the chain of occasions connecting the business coherence want to
assurance what's more, to recovery. The following are some critical contemplation about the
procedure:
• The reason for business progression design is to keep the company continuity incase a
breach happens. Each capacity in the business ought to have a legitimate recovery plan
layout.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 15
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





