Enterprise Security Assignment: Stuxnet, Risk, TOGAF, and Movie
VerifiedAdded on 2023/06/03
|11
|2322
|304
Report
AI Summary
This report provides a comprehensive analysis of enterprise security, beginning with an introduction that highlights the importance of secure information management within organizations. The report then delves into the specifics of the Stuxnet virus, detailing its sophisticated structure, its impact on Programmable Logic Controllers (PLCs), and its implications for industrial systems. Following this, a qualitative risk analysis is presented, evaluating the potential threats to a nuclear program, including the use of S300 and HQ18 missiles. The report also explores the TOGAF standard, offering a brief overview and relevant questions. Finally, the report discusses a scenario from the movie "Contact", evaluating the cost-effectiveness of different security measures. The conclusion summarizes the key findings, emphasizing the importance of proactive security measures in protecting organizational assets and information. The report also includes a comprehensive bibliography of cited sources.

Running head: ENTERPRISE SECURITY ASSIGNMENT
Enterprise Security Assignment
Name of the Student:
Student ID:
Name of the University:
Author’s note:
Enterprise Security Assignment
Name of the Student:
Student ID:
Name of the University:
Author’s note:
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
1ENTERPRISE SECURITY ASSIGNMENT
Table of Contents
Introduction......................................................................................................................................2
Explanation of Stuxnet....................................................................................................................2
Qualitative Risk analysis.................................................................................................................4
TOGAF............................................................................................................................................5
Movie Contact.................................................................................................................................6
Conclusion.......................................................................................................................................7
Bibliography....................................................................................................................................8
Table of Contents
Introduction......................................................................................................................................2
Explanation of Stuxnet....................................................................................................................2
Qualitative Risk analysis.................................................................................................................4
TOGAF............................................................................................................................................5
Movie Contact.................................................................................................................................6
Conclusion.......................................................................................................................................7
Bibliography....................................................................................................................................8
2ENTERPRISE SECURITY ASSIGNMENT
Introduction
The security is a major concern for the current organization as the implication would
allow the secure information management. It has been assisting for integrating the work for
aligning with the consideration for information transfer. The alignment of the following report
would be helpful for analysis of the virus of Stuxnet and its impact on the organizational
structure. The consideration is also helpful for enduring the utilization of the quantitative risk
analysis for identifying the risk factors for the nuclear program. The calculation of the exposure
factor, single loss expectancy, annualized rate of occurrence, and annualized loss expectancy has
been considered for forming the evaluation of the program. The report would also provide a
basic information of the TOGAF and the procurement method used in the movie “Contact”.
Explanation of Stuxnet
Stuxnet can be explained as malicious computer worm having the extremely
sophisticated structure and it exploits multiple windows for forming the analysis of the improved
functional development. The malware was built jointly by the American-Israeli weapon for
targeting the influence of the effective and smart management process. The activities would be
implied with the consideration of the activities aligning the influence of the effective
management processing. The malware targets the Program Logic Controller (PLC) hindering the
process of automation of the electrochemical process. The attack source of Stuxnet was
initialized with the initial vector for the sequencing of the infection. The OS has been deigned in
a way that the external removable storages and devices can be supported. Another good feature
for the industrial absorption and USB environmental ports. The controlling of the prevention
Introduction
The security is a major concern for the current organization as the implication would
allow the secure information management. It has been assisting for integrating the work for
aligning with the consideration for information transfer. The alignment of the following report
would be helpful for analysis of the virus of Stuxnet and its impact on the organizational
structure. The consideration is also helpful for enduring the utilization of the quantitative risk
analysis for identifying the risk factors for the nuclear program. The calculation of the exposure
factor, single loss expectancy, annualized rate of occurrence, and annualized loss expectancy has
been considered for forming the evaluation of the program. The report would also provide a
basic information of the TOGAF and the procurement method used in the movie “Contact”.
Explanation of Stuxnet
Stuxnet can be explained as malicious computer worm having the extremely
sophisticated structure and it exploits multiple windows for forming the analysis of the improved
functional development. The malware was built jointly by the American-Israeli weapon for
targeting the influence of the effective and smart management process. The activities would be
implied with the consideration of the activities aligning the influence of the effective
management processing. The malware targets the Program Logic Controller (PLC) hindering the
process of automation of the electrochemical process. The attack source of Stuxnet was
initialized with the initial vector for the sequencing of the infection. The OS has been deigned in
a way that the external removable storages and devices can be supported. Another good feature
for the industrial absorption and USB environmental ports. The controlling of the prevention
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
3ENTERPRISE SECURITY ASSIGNMENT
method has been implied with the factors for developing the alignment of the endpoint access in
the system.
Stuxnet has been designed for the harming and attacking specific areas of the system and
hence it can be considered for the evaluation of the factors for development. The Stuxnet cane be
considered for the harming the various networks and systems. The system can exploit and enter
into those systems that are unreachable for the Siemens also. The malware would infect the
system and with the help of it spreading ability would spread to the rest of the system
components. The malware has been specifically designed for the subverted industrial system as it
can reduplicate itself harming one components from other in multiple forms. The offline systems
can be reached with the help of the hardware components within the industrial computers.
Stuxnet mainly attacks the project files and devices while incorporating the different
levels of propagation in the system with single motive of infecting the project files. The PLC
devices has been continuously being harmed for allowing the informal development of the
factors for taking care of the factors for the development of the improved management process.
The worm has been targeting Windows system for listing the probable management. The
formation of the PLC windows based system influence would be effective for the listing of the
probable influence of the machine level language. The identification of the PLC model would be
effective for the development of the factors for considering the involvement of the successive
development.
The antiviruses works on system software and protects the system from being infiltrated
from software point of view. The access in the system using the programs of the software can be
protected and detected using the antiviruses. The involvement of the successful development
management for protecting from the influence of the malware from the alignment of the factorial
method has been implied with the factors for developing the alignment of the endpoint access in
the system.
Stuxnet has been designed for the harming and attacking specific areas of the system and
hence it can be considered for the evaluation of the factors for development. The Stuxnet cane be
considered for the harming the various networks and systems. The system can exploit and enter
into those systems that are unreachable for the Siemens also. The malware would infect the
system and with the help of it spreading ability would spread to the rest of the system
components. The malware has been specifically designed for the subverted industrial system as it
can reduplicate itself harming one components from other in multiple forms. The offline systems
can be reached with the help of the hardware components within the industrial computers.
Stuxnet mainly attacks the project files and devices while incorporating the different
levels of propagation in the system with single motive of infecting the project files. The PLC
devices has been continuously being harmed for allowing the informal development of the
factors for taking care of the factors for the development of the improved management process.
The worm has been targeting Windows system for listing the probable management. The
formation of the PLC windows based system influence would be effective for the listing of the
probable influence of the machine level language. The identification of the PLC model would be
effective for the development of the factors for considering the involvement of the successive
development.
The antiviruses works on system software and protects the system from being infiltrated
from software point of view. The access in the system using the programs of the software can be
protected and detected using the antiviruses. The involvement of the successful development
management for protecting from the influence of the malware from the alignment of the factorial
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
4ENTERPRISE SECURITY ASSIGNMENT
development model. The Stuxnet would work on the hardware and form the major influence on
the compilation of the work influence on the PLC. The influence of the PLC model has been
largely adopted for the consideration of the PLC model identification. The malware results in
forming the major impact on the machine level instruction and the variation on the PLC device.
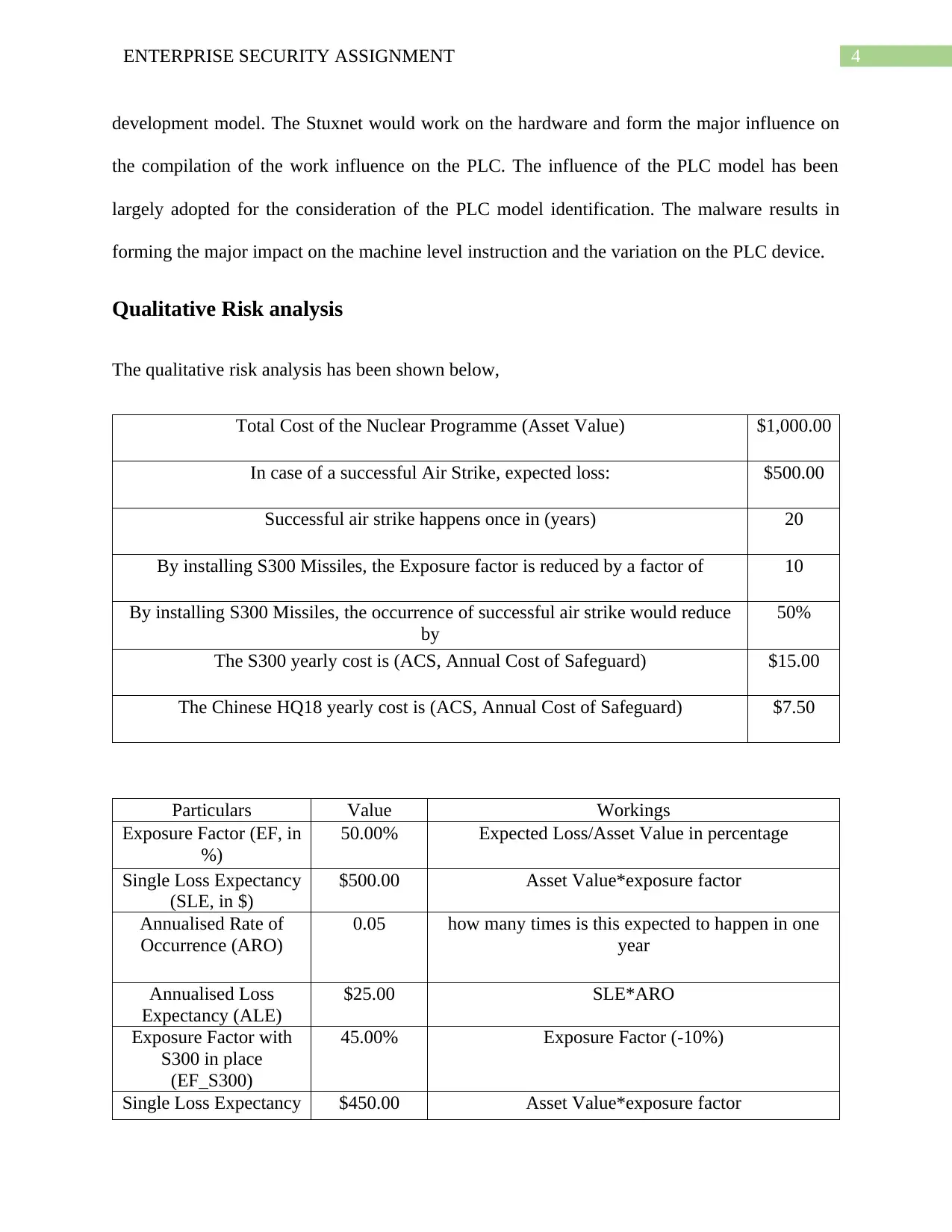
Qualitative Risk analysis
The qualitative risk analysis has been shown below,
Total Cost of the Nuclear Programme (Asset Value) $1,000.00
In case of a successful Air Strike, expected loss: $500.00
Successful air strike happens once in (years) 20
By installing S300 Missiles, the Exposure factor is reduced by a factor of 10
By installing S300 Missiles, the occurrence of successful air strike would reduce
by
50%
The S300 yearly cost is (ACS, Annual Cost of Safeguard) $15.00
The Chinese HQ18 yearly cost is (ACS, Annual Cost of Safeguard) $7.50
Particulars Value Workings
Exposure Factor (EF, in
%)
50.00% Expected Loss/Asset Value in percentage
Single Loss Expectancy
(SLE, in $)
$500.00 Asset Value*exposure factor
Annualised Rate of
Occurrence (ARO)
0.05 how many times is this expected to happen in one
year
Annualised Loss
Expectancy (ALE)
$25.00 SLE*ARO
Exposure Factor with
S300 in place
(EF_S300)
45.00% Exposure Factor (-10%)
Single Loss Expectancy $450.00 Asset Value*exposure factor
development model. The Stuxnet would work on the hardware and form the major influence on
the compilation of the work influence on the PLC. The influence of the PLC model has been
largely adopted for the consideration of the PLC model identification. The malware results in
forming the major impact on the machine level instruction and the variation on the PLC device.
Qualitative Risk analysis
The qualitative risk analysis has been shown below,
Total Cost of the Nuclear Programme (Asset Value) $1,000.00
In case of a successful Air Strike, expected loss: $500.00
Successful air strike happens once in (years) 20
By installing S300 Missiles, the Exposure factor is reduced by a factor of 10
By installing S300 Missiles, the occurrence of successful air strike would reduce
by
50%
The S300 yearly cost is (ACS, Annual Cost of Safeguard) $15.00
The Chinese HQ18 yearly cost is (ACS, Annual Cost of Safeguard) $7.50
Particulars Value Workings
Exposure Factor (EF, in
%)
50.00% Expected Loss/Asset Value in percentage
Single Loss Expectancy
(SLE, in $)
$500.00 Asset Value*exposure factor
Annualised Rate of
Occurrence (ARO)
0.05 how many times is this expected to happen in one
year
Annualised Loss
Expectancy (ALE)
$25.00 SLE*ARO
Exposure Factor with
S300 in place
(EF_S300)
45.00% Exposure Factor (-10%)
Single Loss Expectancy $450.00 Asset Value*exposure factor
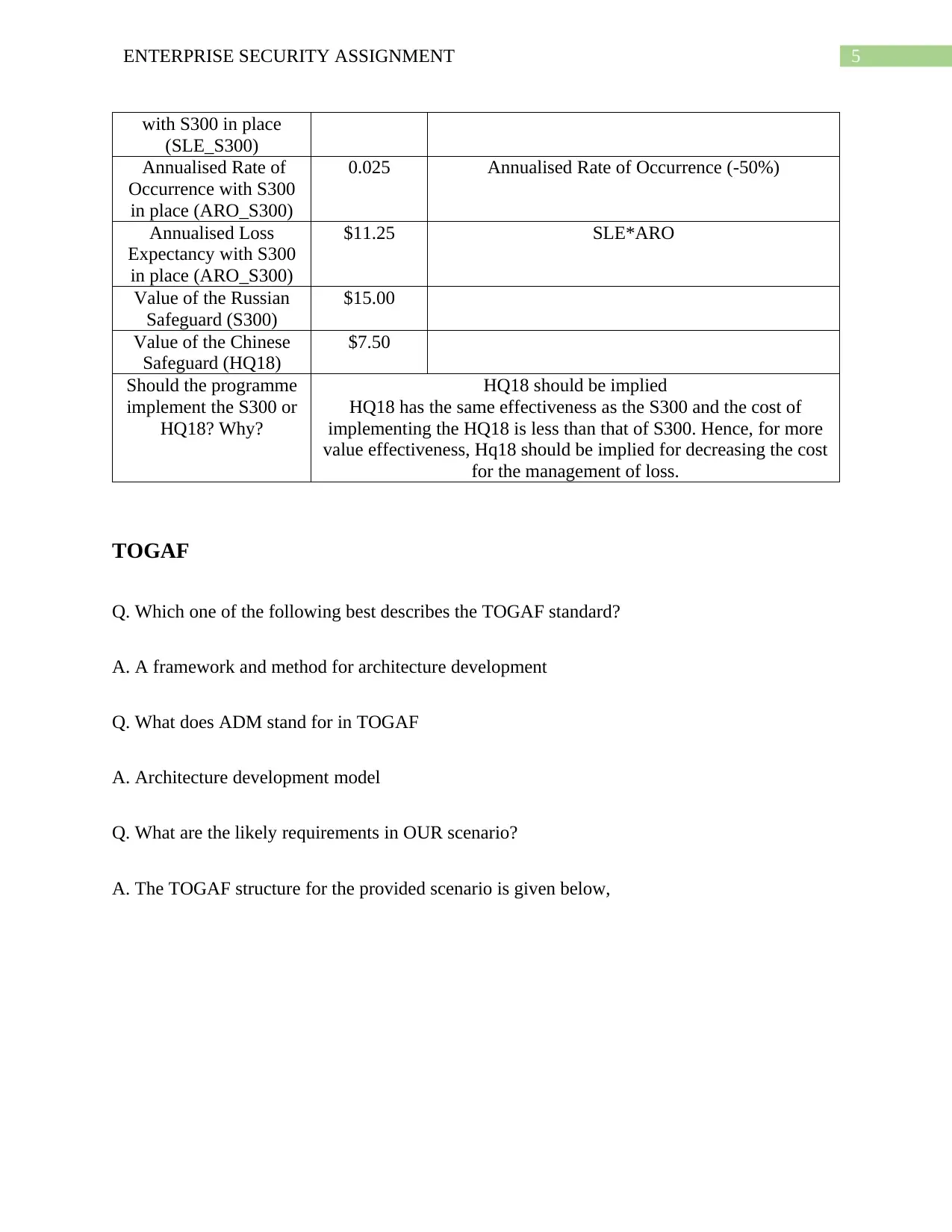
5ENTERPRISE SECURITY ASSIGNMENT
with S300 in place
(SLE_S300)
Annualised Rate of
Occurrence with S300
in place (ARO_S300)
0.025 Annualised Rate of Occurrence (-50%)
Annualised Loss
Expectancy with S300
in place (ARO_S300)
$11.25 SLE*ARO
Value of the Russian
Safeguard (S300)
$15.00
Value of the Chinese
Safeguard (HQ18)
$7.50
Should the programme
implement the S300 or
HQ18? Why?
HQ18 should be implied
HQ18 has the same effectiveness as the S300 and the cost of
implementing the HQ18 is less than that of S300. Hence, for more
value effectiveness, Hq18 should be implied for decreasing the cost
for the management of loss.
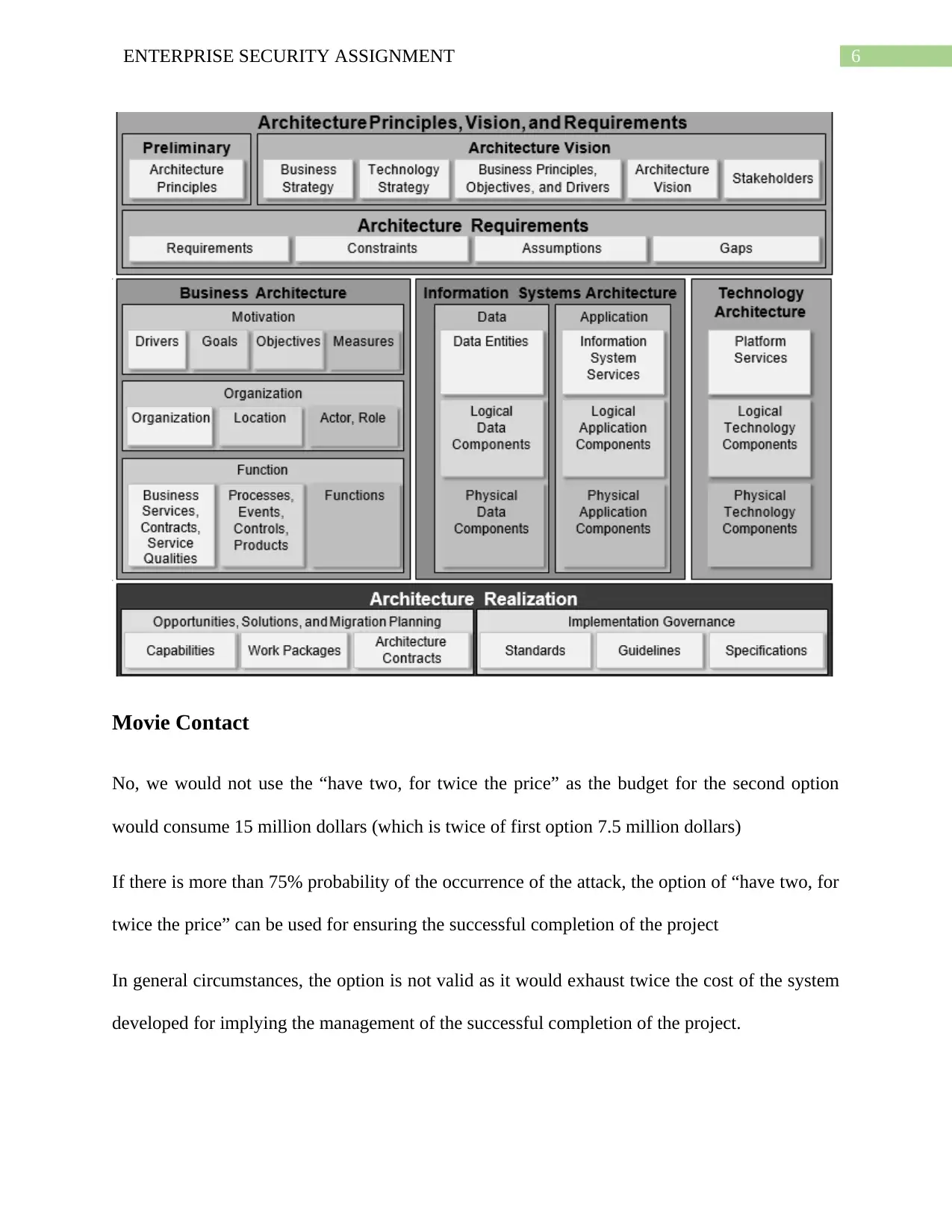
TOGAF
Q. Which one of the following best describes the TOGAF standard?
A. A framework and method for architecture development
Q. What does ADM stand for in TOGAF
A. Architecture development model
Q. What are the likely requirements in OUR scenario?
A. The TOGAF structure for the provided scenario is given below,
with S300 in place
(SLE_S300)
Annualised Rate of
Occurrence with S300
in place (ARO_S300)
0.025 Annualised Rate of Occurrence (-50%)
Annualised Loss
Expectancy with S300
in place (ARO_S300)
$11.25 SLE*ARO
Value of the Russian
Safeguard (S300)
$15.00
Value of the Chinese
Safeguard (HQ18)
$7.50
Should the programme
implement the S300 or
HQ18? Why?
HQ18 should be implied
HQ18 has the same effectiveness as the S300 and the cost of
implementing the HQ18 is less than that of S300. Hence, for more
value effectiveness, Hq18 should be implied for decreasing the cost
for the management of loss.
TOGAF
Q. Which one of the following best describes the TOGAF standard?
A. A framework and method for architecture development
Q. What does ADM stand for in TOGAF
A. Architecture development model
Q. What are the likely requirements in OUR scenario?
A. The TOGAF structure for the provided scenario is given below,
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
6ENTERPRISE SECURITY ASSIGNMENT
Movie Contact
No, we would not use the “have two, for twice the price” as the budget for the second option
would consume 15 million dollars (which is twice of first option 7.5 million dollars)
If there is more than 75% probability of the occurrence of the attack, the option of “have two, for
twice the price” can be used for ensuring the successful completion of the project
In general circumstances, the option is not valid as it would exhaust twice the cost of the system
developed for implying the management of the successful completion of the project.
Movie Contact
No, we would not use the “have two, for twice the price” as the budget for the second option
would consume 15 million dollars (which is twice of first option 7.5 million dollars)
If there is more than 75% probability of the occurrence of the attack, the option of “have two, for
twice the price” can be used for ensuring the successful completion of the project
In general circumstances, the option is not valid as it would exhaust twice the cost of the system
developed for implying the management of the successful completion of the project.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
7ENTERPRISE SECURITY ASSIGNMENT
The option (S300) is hot site as it would allow the continuation of the protection of the nuclear
program even after the failure of the HQ18. The facility would allow the significant management
of the successful completion of the project.
Conclusion
It can be concluded from the assignment that the implication would be helpful for taking
care of the factors for aligning the management. The alignment of the following report had been
helpful for analysis of the virus of Stuxnet and its impact on the organizational structure. The
nuclear sector had been implied with the consideration for the factors and management of the
improved factors. The successful implication management for the listing the analysis for the
formation of the factors. The analysis had been implied with the formation development for
project intuition.
The option (S300) is hot site as it would allow the continuation of the protection of the nuclear
program even after the failure of the HQ18. The facility would allow the significant management
of the successful completion of the project.
Conclusion
It can be concluded from the assignment that the implication would be helpful for taking
care of the factors for aligning the management. The alignment of the following report had been
helpful for analysis of the virus of Stuxnet and its impact on the organizational structure. The
nuclear sector had been implied with the consideration for the factors and management of the
improved factors. The successful implication management for the listing the analysis for the
formation of the factors. The analysis had been implied with the formation development for
project intuition.
8ENTERPRISE SECURITY ASSIGNMENT
Bibliography
Army, U.S., 2017. Cyberterrorism After Stuxnet-Terrorist Cyberattacks, Distributed Denial of
Service (DDoS), Motives, Critical US Infrastructure Vulnerabilities, al-Qaeda Computer
Capability, PC Attacks.
Cabrera, A., Abad, M., Jaramillo, D., Gómez, J. and Verdum, J.C., 2016. Definition and
implementation of the enterprise business layer through a business reference model, using the
architecture development method ADM-TOGAF. In Trends and Applications in Software
Engineering (pp. 111-121). Springer, Cham.
Darmanto, D., Suyanto, M. and Al Fatta, H., 2018. PEMODELAN ARSITEKTUR SISTEM
INFORMASI PERIZINAN MENGGUNAKAN KERANGKA KERJA TOGAF
ADM. Informasi Interaktif, 3(1), pp.16-26.
Du, J., Zhang, J., He, T., Li, Y., Su, Y., Tie, F., Liu, M., Harte, P.J. and Zhu, A.J., 2016. Stuxnet
Facilitates the Degradation of Polycomb Protein during Development. Developmental cell, 37(6),
pp.507-519.
Farooq, M.U., Waseem, M., Khairi, A. and Mazhar, S., 2015. A critical analysis on the security
concerns of internet of things (IoT). International Journal of Computer Applications, 111(7).
Harrison, R., 2018. Togaf (r) 9 Foundation Study Guide. Van Haren.
Hu, Z., Wang, M., Yan, X., Yin, Y. and Luo, Z., 2015, February. A comprehensive security
architecture for SDN. In Intelligence in Next Generation Networks (ICIN), 2015 18th
International Conference on (pp. 30-37). IEEE.
Bibliography
Army, U.S., 2017. Cyberterrorism After Stuxnet-Terrorist Cyberattacks, Distributed Denial of
Service (DDoS), Motives, Critical US Infrastructure Vulnerabilities, al-Qaeda Computer
Capability, PC Attacks.
Cabrera, A., Abad, M., Jaramillo, D., Gómez, J. and Verdum, J.C., 2016. Definition and
implementation of the enterprise business layer through a business reference model, using the
architecture development method ADM-TOGAF. In Trends and Applications in Software
Engineering (pp. 111-121). Springer, Cham.
Darmanto, D., Suyanto, M. and Al Fatta, H., 2018. PEMODELAN ARSITEKTUR SISTEM
INFORMASI PERIZINAN MENGGUNAKAN KERANGKA KERJA TOGAF
ADM. Informasi Interaktif, 3(1), pp.16-26.
Du, J., Zhang, J., He, T., Li, Y., Su, Y., Tie, F., Liu, M., Harte, P.J. and Zhu, A.J., 2016. Stuxnet
Facilitates the Degradation of Polycomb Protein during Development. Developmental cell, 37(6),
pp.507-519.
Farooq, M.U., Waseem, M., Khairi, A. and Mazhar, S., 2015. A critical analysis on the security
concerns of internet of things (IoT). International Journal of Computer Applications, 111(7).
Harrison, R., 2018. Togaf (r) 9 Foundation Study Guide. Van Haren.
Hu, Z., Wang, M., Yan, X., Yin, Y. and Luo, Z., 2015, February. A comprehensive security
architecture for SDN. In Intelligence in Next Generation Networks (ICIN), 2015 18th
International Conference on (pp. 30-37). IEEE.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
9ENTERPRISE SECURITY ASSIGNMENT
Karch, F., 2016. Stuxnet Recruits the Proteasome to Take Down Polycomb. Developmental
cell, 37(6), pp.485-486.
Kenney, M., 2015. Cyber-terrorism in a post-stuxnet world. Orbis, 59(1), pp.111-128.
Koeberl, P., Schulz, S., Sadeghi, A.R. and Varadharajan, V., 2014, April. TrustLite: A security
architecture for tiny embedded devices. In Proceedings of the Ninth European Conference on
Computer Systems (p. 10). ACM.
Liger, V.V., Mironenko, V.R., Kuritsyn, Y.A. and Bolshov, M.A., 2018. Determination of the
Maximum Temperature in a Non-Uniform Hot Zone by Line-of-Site Absorption Spectroscopy
with a Single Diode Laser. Sensors, 18(5), p.1608.
Mayer, N., Aubert, J., Grandry, E. and Feltus, C., 2016, November. An Integrated Conceptual
Model for Information System Security Risk Management and Enterprise Architecture
Management Based on TOGAF. In IFIP Working Conference on The Practice of Enterprise
Modeling (pp. 353-361). Springer, Cham.
Nourian, A. and Madnick, S., 2018. A systems theoretic approach to the security threats in cyber
physical systems applied to stuxnet. IEEE Transactions on Dependable and Secure
Computing, 15(1), pp.2-13.
Ntuli, N. and Abu-Mahfouz, A., 2016. A simple security architecture for smart water
management system. Procedia Computer Science, 83, pp.1164-1169.
Olivier, F., Carlos, G. and Florent, N., 2015. New security architecture for IoT
network. Procedia Computer Science, 52, pp.1028-1033.
Karch, F., 2016. Stuxnet Recruits the Proteasome to Take Down Polycomb. Developmental
cell, 37(6), pp.485-486.
Kenney, M., 2015. Cyber-terrorism in a post-stuxnet world. Orbis, 59(1), pp.111-128.
Koeberl, P., Schulz, S., Sadeghi, A.R. and Varadharajan, V., 2014, April. TrustLite: A security
architecture for tiny embedded devices. In Proceedings of the Ninth European Conference on
Computer Systems (p. 10). ACM.
Liger, V.V., Mironenko, V.R., Kuritsyn, Y.A. and Bolshov, M.A., 2018. Determination of the
Maximum Temperature in a Non-Uniform Hot Zone by Line-of-Site Absorption Spectroscopy
with a Single Diode Laser. Sensors, 18(5), p.1608.
Mayer, N., Aubert, J., Grandry, E. and Feltus, C., 2016, November. An Integrated Conceptual
Model for Information System Security Risk Management and Enterprise Architecture
Management Based on TOGAF. In IFIP Working Conference on The Practice of Enterprise
Modeling (pp. 353-361). Springer, Cham.
Nourian, A. and Madnick, S., 2018. A systems theoretic approach to the security threats in cyber
physical systems applied to stuxnet. IEEE Transactions on Dependable and Secure
Computing, 15(1), pp.2-13.
Ntuli, N. and Abu-Mahfouz, A., 2016. A simple security architecture for smart water
management system. Procedia Computer Science, 83, pp.1164-1169.
Olivier, F., Carlos, G. and Florent, N., 2015. New security architecture for IoT
network. Procedia Computer Science, 52, pp.1028-1033.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
10ENTERPRISE SECURITY ASSIGNMENT
Segal, A., Pitts, H. and Grindal, K., 2016. Cyber Conflict After Stuxnet: Essays from the Other
Bank of the Rubicon. Cyber Conflict Studies Association.
Siddiqui, M.S., Escalona, E., Trouva, E., Kourtis, M.A., Kritharidis, D., Katsaros, K., Spirou, S.,
Canales, C. and Lorenzo, M., 2016, November. Policy based virtualised security architecture for
SDN/NFV enabled 5G access networks. In 2016 IEEE Conference on Network Function
Virtualization and Software Defined Networks (NFV-SDN) (pp. 44-49). IEEE.
Singer, P.W., 2015. Stuxnet and its hidden lessons on the ethics of cyberweapons. Case W. Res.
J. Int'l L., 47, p.79.
Souissi, S., Sliman, L. and Charroux, B., 2016, November. A novel security architecture based
on multi-level rule expression language. In International Conference on Hybrid Intelligent
Systems (pp. 259-269). Springer, Cham.
Tian, Y., Shuai, Z., Shen, J., Zhang, L., Chen, S., Song, C., Zhao, B., Fan, Q. and Wang, L.,
2018. Plasmonic Heterodimers with Binding Site‐Dependent Hot Spot for Surface‐Enhanced
Raman Scattering. Small, 14(24), p.1800669.
Vučinić, M., Tourancheau, B., Rousseau, F., Duda, A., Damon, L. and Guizzetti, R., 2015.
OSCAR: Object security architecture for the Internet of Things. Ad Hoc Networks, 32, pp.3-16.
Wu, X., 2016. Stuxnet detected, Pc breaks down. Science China. Life Sciences, 59(11), p.1202.
Segal, A., Pitts, H. and Grindal, K., 2016. Cyber Conflict After Stuxnet: Essays from the Other
Bank of the Rubicon. Cyber Conflict Studies Association.
Siddiqui, M.S., Escalona, E., Trouva, E., Kourtis, M.A., Kritharidis, D., Katsaros, K., Spirou, S.,
Canales, C. and Lorenzo, M., 2016, November. Policy based virtualised security architecture for
SDN/NFV enabled 5G access networks. In 2016 IEEE Conference on Network Function
Virtualization and Software Defined Networks (NFV-SDN) (pp. 44-49). IEEE.
Singer, P.W., 2015. Stuxnet and its hidden lessons on the ethics of cyberweapons. Case W. Res.
J. Int'l L., 47, p.79.
Souissi, S., Sliman, L. and Charroux, B., 2016, November. A novel security architecture based
on multi-level rule expression language. In International Conference on Hybrid Intelligent
Systems (pp. 259-269). Springer, Cham.
Tian, Y., Shuai, Z., Shen, J., Zhang, L., Chen, S., Song, C., Zhao, B., Fan, Q. and Wang, L.,
2018. Plasmonic Heterodimers with Binding Site‐Dependent Hot Spot for Surface‐Enhanced
Raman Scattering. Small, 14(24), p.1800669.
Vučinić, M., Tourancheau, B., Rousseau, F., Duda, A., Damon, L. and Guizzetti, R., 2015.
OSCAR: Object security architecture for the Internet of Things. Ad Hoc Networks, 32, pp.3-16.
Wu, X., 2016. Stuxnet detected, Pc breaks down. Science China. Life Sciences, 59(11), p.1202.
1 out of 11
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.




