Ethical Hacking Report: Case Study on System Access and Exploitation
VerifiedAdded on 2023/06/05
|11
|2131
|158
Report
AI Summary
This report provides an in-depth analysis of ethical hacking through a case study involving system access and root privilege attainment. The study focuses on five flags, each representing unique characteristics and challenges within a virtual machine environment. The flags cover aspects such as web server content examination, web shell analysis, password cracking techniques, TCP port scanning using NMAP, and Linux privilege escalation methods. The report details the methodology used to identify vulnerabilities and exploit them, including steps to deobfuscate web shells and bypass authentication checks. Ultimately, the report aims to provide a comprehensive understanding of ethical hacking principles and their practical application in identifying and mitigating security risks. Desklib provides similar solved assignments and past papers for students.
Ethical Hacking
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Executive Summary
This report sheds light on ethical hacking. To conduct this study, a case study is
provided. To carry out the study it is necessary that the user gain access to the system that is
provided and root level privileges must be attained. The observation of the study represents
that there are five flags for this project. These flags are performed with the use of the virtual
machine’s case study. All the flags and their requirements are found in this report. Each flag
contains unique characteristics which are determined in this project report.
This report sheds light on ethical hacking. To conduct this study, a case study is
provided. To carry out the study it is necessary that the user gain access to the system that is
provided and root level privileges must be attained. The observation of the study represents
that there are five flags for this project. These flags are performed with the use of the virtual
machine’s case study. All the flags and their requirements are found in this report. Each flag
contains unique characteristics which are determined in this project report.
Table of Contents
1. Description.........................................................................................................................3
2. Methodology and Testing Log.........................................................................................3
1.1 1st Flag: Web Server..................................................................................................4
1.2 2nd Flag: Web shells...................................................................................................5
1.3 3rd Flag: Password cracker.......................................................................................6
1.4 4th Flag: TCP port scanner – NMAP.......................................................................7
1.5 5th Flag: Privilege.......................................................................................................8
3. Result and Conclusion......................................................................................................9
References...............................................................................................................................10
1. Description.........................................................................................................................3
2. Methodology and Testing Log.........................................................................................3
1.1 1st Flag: Web Server..................................................................................................4
1.2 2nd Flag: Web shells...................................................................................................5
1.3 3rd Flag: Password cracker.......................................................................................6
1.4 4th Flag: TCP port scanner – NMAP.......................................................................7
1.5 5th Flag: Privilege.......................................................................................................8
3. Result and Conclusion......................................................................................................9
References...............................................................................................................................10
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1. Description
This report projects on ethical hacking. To conduct this study, a case study is provided.
To carry out the study, it is necessary that the user gain access to the system that is provided
and root level privileges must be attained. The observation of the study represents that there
are five flags for this project. These flags are performed with the use of the virtual machine’s
case study. All the flags and their requirements will be found in this report. Each flag
contains unique characteristics which will be determined in this project report.
2. Methodology and Testing Log
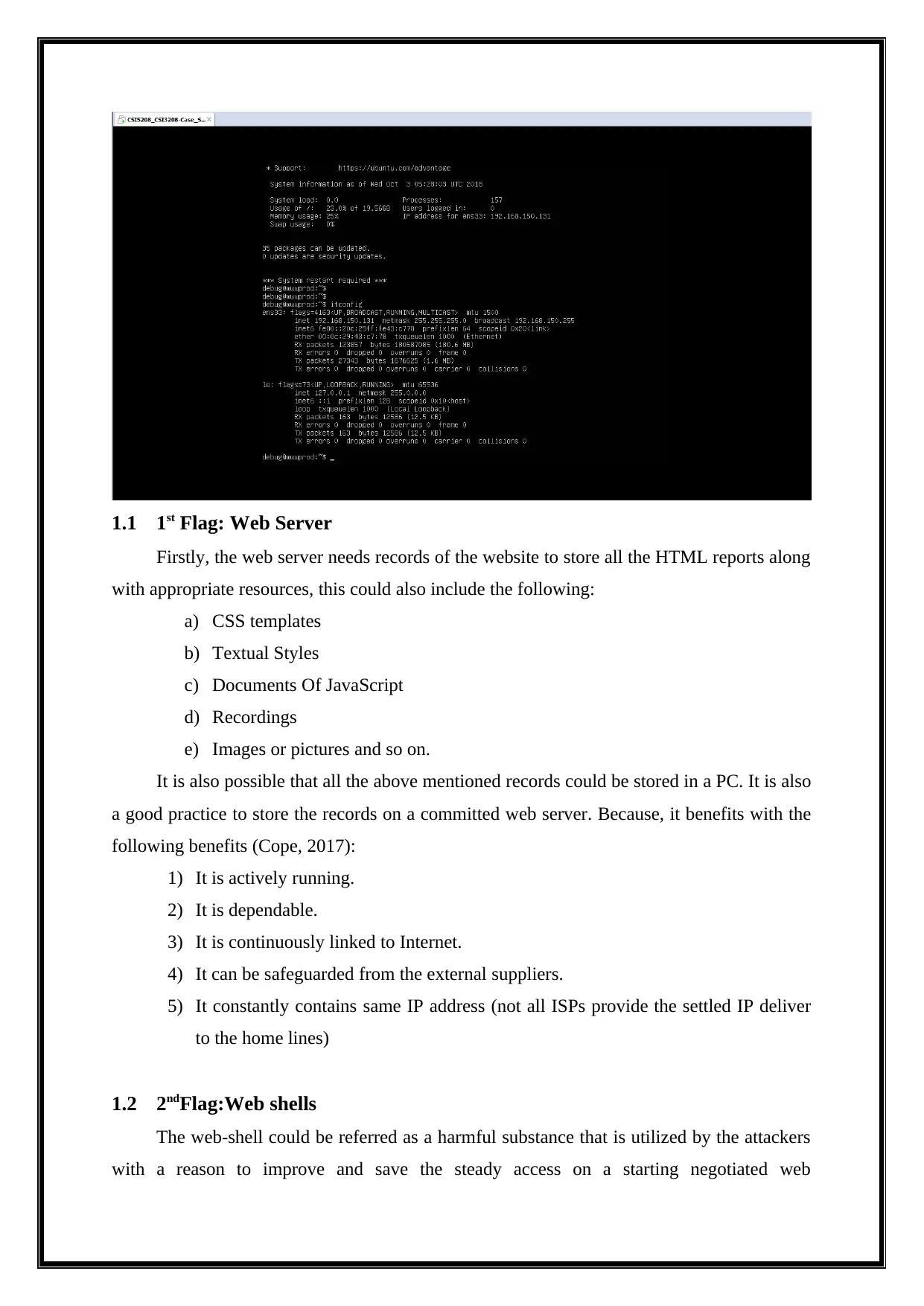
Initially, the Virtual machine must be installed, as illustrated in the above figure.
Identification of IP Address
This report projects on ethical hacking. To conduct this study, a case study is provided.
To carry out the study, it is necessary that the user gain access to the system that is provided
and root level privileges must be attained. The observation of the study represents that there
are five flags for this project. These flags are performed with the use of the virtual machine’s
case study. All the flags and their requirements will be found in this report. Each flag
contains unique characteristics which will be determined in this project report.
2. Methodology and Testing Log
Initially, the Virtual machine must be installed, as illustrated in the above figure.
Identification of IP Address
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
1.1 1st Flag: Web Server
Firstly, the web server needs records of the website to store all the HTML reports along
with appropriate resources, this could also include the following:
a) CSS templates
b) Textual Styles
c) Documents Of JavaScript
d) Recordings
e) Images or pictures and so on.
It is also possible that all the above mentioned records could be stored in a PC. It is also
a good practice to store the records on a committed web server. Because, it benefits with the
following benefits (Cope, 2017):
1) It is actively running.
2) It is dependable.
3) It is continuously linked to Internet.
4) It can be safeguarded from the external suppliers.
5) It constantly contains same IP address (not all ISPs provide the settled IP deliver
to the home lines)
1.2 2ndFlag:Web shells
The web-shell could be referred as a harmful substance that is utilized by the attackers
with a reason to improve and save the steady access on a starting negotiated web
Firstly, the web server needs records of the website to store all the HTML reports along
with appropriate resources, this could also include the following:
a) CSS templates
b) Textual Styles
c) Documents Of JavaScript
d) Recordings
e) Images or pictures and so on.
It is also possible that all the above mentioned records could be stored in a PC. It is also
a good practice to store the records on a committed web server. Because, it benefits with the
following benefits (Cope, 2017):
1) It is actively running.
2) It is dependable.
3) It is continuously linked to Internet.
4) It can be safeguarded from the external suppliers.
5) It constantly contains same IP address (not all ISPs provide the settled IP deliver
to the home lines)
1.2 2ndFlag:Web shells
The web-shell could be referred as a harmful substance that is utilized by the attackers
with a reason to improve and save the steady access on a starting negotiated web
application(Prodromou, 2016). Web-shells can't strike or experience remote incapability, so it
is constantly the second step of a trap.The general vulnerabilities could be misused by the
attacker. An example could be represented as follows, The SQL implantation, RFI, FTP, or
even use XSS as a part of a social planning strike with a particular true objective for
exchanging the substance that is malicious. The fundamental usefulness rages it, but however
it isnot just limited to the execution of the web shell, record organization,database tally and
code execution ("Everything You Need To Know About Web Shells", 2017).
1. Zombie
The Web-shells another usage includes makingthe servers part of the botnet.
The botnet is defined as an arrangement of exchanged off systems which the attacker
might try to control, it can be either for using it for themselves, or to help the other
bad parties("What is a Web shell?", 2017).
2. Propelling and Pivoting Attacks
The web-shell could be utilized to revolve internally or externally area of the
framework. The attacker has to screen the framework, for development of the
structure, then test the internal framework foridentifying any unauthorized access, and
provide firewall as well as switches in the framework. This will allow to secure the
framework from the hackers (Glia, 2016).
3. Consistent Remote Access
The web-shell generally comprises an access which is probably indirect and it
gives the power for the attacker for remotely accessing and controlling the server. The
access can be allowed as and when needed by the hacker. This would save the
attacker from any kind of complex misusing a weakness each time access to the
exchanged off server is required.
1.3 3rdFlag: Password cracker
If the hacker hacks the webpage, the attacker daily leaves web shell or an auxiliary
section forachieving accomplishment to reach the website in future. This leaves the user
confused and avoids any kind of proofs which could be recognized, and the attackers require
confirmation, so that the attackers can get into the site. This post represents a process to
simplify the web shell and shows how the affirmation could be evaded, when there is
availability of source code and when the password is missing (Engebretson, 2013).
Deobfuscating the web shell
is constantly the second step of a trap.The general vulnerabilities could be misused by the
attacker. An example could be represented as follows, The SQL implantation, RFI, FTP, or
even use XSS as a part of a social planning strike with a particular true objective for
exchanging the substance that is malicious. The fundamental usefulness rages it, but however
it isnot just limited to the execution of the web shell, record organization,database tally and
code execution ("Everything You Need To Know About Web Shells", 2017).
1. Zombie
The Web-shells another usage includes makingthe servers part of the botnet.
The botnet is defined as an arrangement of exchanged off systems which the attacker
might try to control, it can be either for using it for themselves, or to help the other
bad parties("What is a Web shell?", 2017).
2. Propelling and Pivoting Attacks
The web-shell could be utilized to revolve internally or externally area of the
framework. The attacker has to screen the framework, for development of the
structure, then test the internal framework foridentifying any unauthorized access, and
provide firewall as well as switches in the framework. This will allow to secure the
framework from the hackers (Glia, 2016).
3. Consistent Remote Access
The web-shell generally comprises an access which is probably indirect and it
gives the power for the attacker for remotely accessing and controlling the server. The
access can be allowed as and when needed by the hacker. This would save the
attacker from any kind of complex misusing a weakness each time access to the
exchanged off server is required.
1.3 3rdFlag: Password cracker
If the hacker hacks the webpage, the attacker daily leaves web shell or an auxiliary
section forachieving accomplishment to reach the website in future. This leaves the user
confused and avoids any kind of proofs which could be recognized, and the attackers require
confirmation, so that the attackers can get into the site. This post represents a process to
simplify the web shell and shows how the affirmation could be evaded, when there is
availability of source code and when the password is missing (Engebretson, 2013).
Deobfuscating the web shell
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
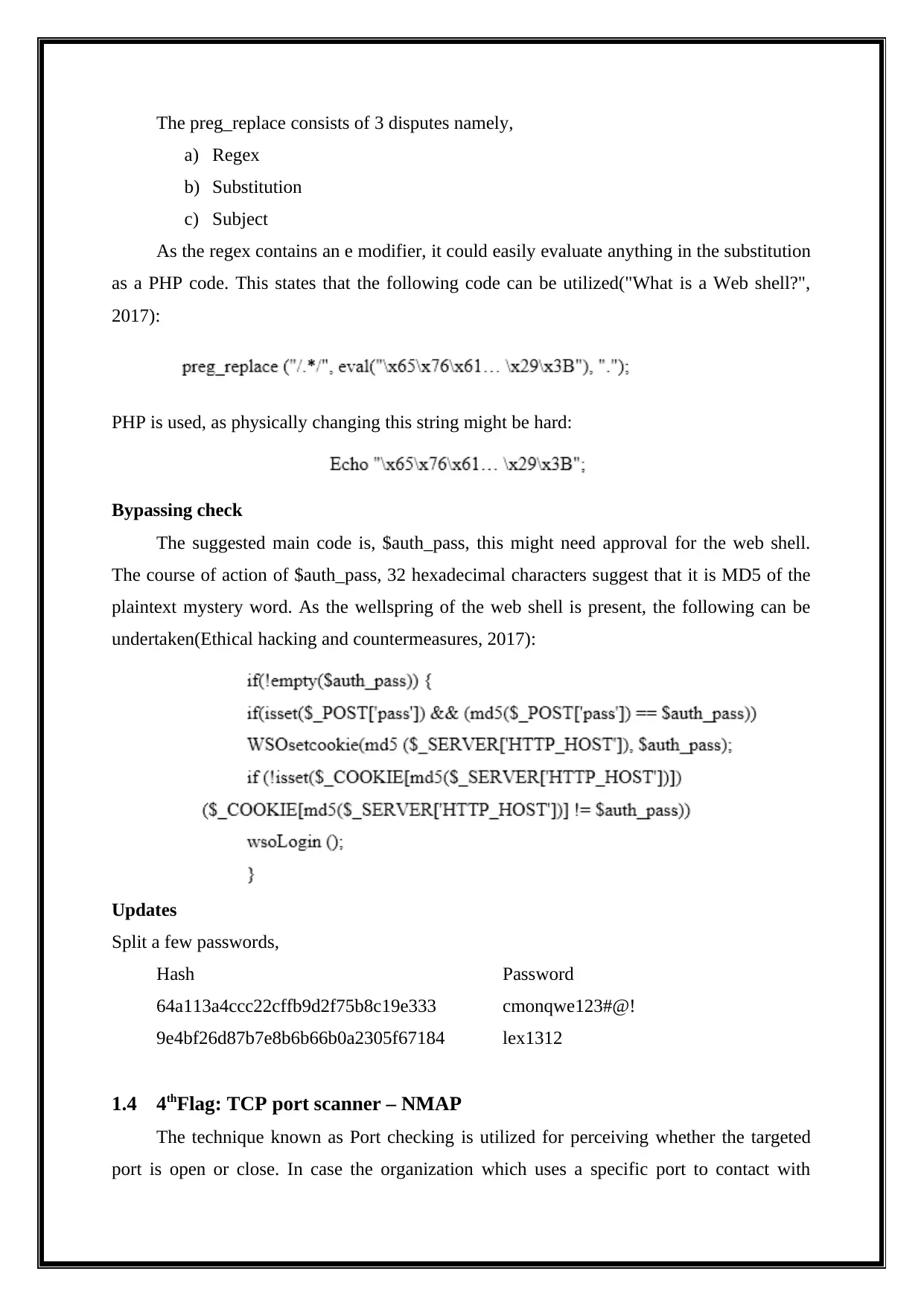
The preg_replace consists of 3 disputes namely,
a) Regex
b) Substitution
c) Subject
As the regex contains an e modifier, it could easily evaluate anything in the substitution
as a PHP code. This states that the following code can be utilized("What is a Web shell?",
2017):
PHP is used, as physically changing this string might be hard:
Bypassing check
The suggested main code is, $auth_pass, this might need approval for the web shell.
The course of action of $auth_pass, 32 hexadecimal characters suggest that it is MD5 of the
plaintext mystery word. As the wellspring of the web shell is present, the following can be
undertaken(Ethical hacking and countermeasures, 2017):
Updates
Split a few passwords,
Hash Password
64a113a4ccc22cffb9d2f75b8c19e333 cmonqwe123#@!
9e4bf26d87b7e8b6b66b0a2305f67184 lex1312
1.4 4thFlag: TCP port scanner – NMAP
The technique known as Port checking is utilized for perceiving whether the targeted
port is open or close. In case the organization which uses a specific port to contact with
a) Regex
b) Substitution
c) Subject
As the regex contains an e modifier, it could easily evaluate anything in the substitution
as a PHP code. This states that the following code can be utilized("What is a Web shell?",
2017):
PHP is used, as physically changing this string might be hard:
Bypassing check
The suggested main code is, $auth_pass, this might need approval for the web shell.
The course of action of $auth_pass, 32 hexadecimal characters suggest that it is MD5 of the
plaintext mystery word. As the wellspring of the web shell is present, the following can be
undertaken(Ethical hacking and countermeasures, 2017):
Updates
Split a few passwords,
Hash Password
64a113a4ccc22cffb9d2f75b8c19e333 cmonqwe123#@!
9e4bf26d87b7e8b6b66b0a2305f67184 lex1312
1.4 4thFlag: TCP port scanner – NMAP
The technique known as Port checking is utilized for perceiving whether the targeted
port is open or close. In case the organization which uses a specific port to contact with
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
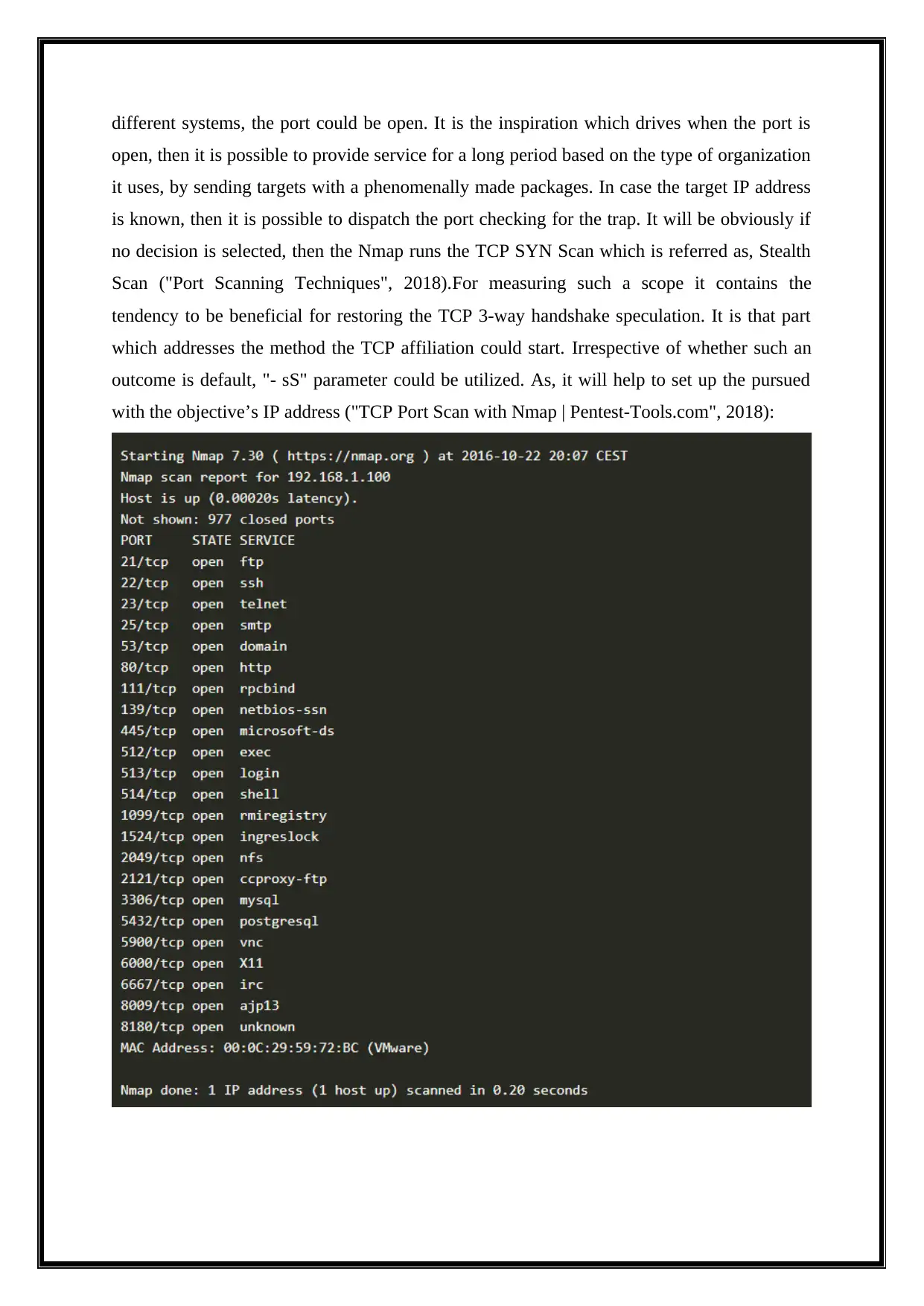
different systems, the port could be open. It is the inspiration which drives when the port is
open, then it is possible to provide service for a long period based on the type of organization
it uses, by sending targets with a phenomenally made packages. In case the target IP address
is known, then it is possible to dispatch the port checking for the trap. It will be obviously if
no decision is selected, then the Nmap runs the TCP SYN Scan which is referred as, Stealth
Scan ("Port Scanning Techniques", 2018).For measuring such a scope it contains the
tendency to be beneficial for restoring the TCP 3-way handshake speculation. It is that part
which addresses the method the TCP affiliation could start. Irrespective of whether such an
outcome is default, "- sS" parameter could be utilized. As, it will help to set up the pursued
with the objective’s IP address ("TCP Port Scan with Nmap | Pentest-Tools.com", 2018):
open, then it is possible to provide service for a long period based on the type of organization
it uses, by sending targets with a phenomenally made packages. In case the target IP address
is known, then it is possible to dispatch the port checking for the trap. It will be obviously if
no decision is selected, then the Nmap runs the TCP SYN Scan which is referred as, Stealth
Scan ("Port Scanning Techniques", 2018).For measuring such a scope it contains the
tendency to be beneficial for restoring the TCP 3-way handshake speculation. It is that part
which addresses the method the TCP affiliation could start. Irrespective of whether such an
outcome is default, "- sS" parameter could be utilized. As, it will help to set up the pursued
with the objective’s IP address ("TCP Port Scan with Nmap | Pentest-Tools.com", 2018):
Due to each reason, the users contains least need for runningNmap from the limited shared
shell accounts and it is fortunate enough because the privileged options lets Nmapto becomes
highly flexible and powerful. As Nmaptries to generate accurate results, it must be
remembered that each ofits insights depend on the returned packets which the target
machines send (due to firewalls). Similar hosts cannot be trusted and it transfers the
responses that can confuse the Nmap. non-RFC-compliant hosts are the most common ones
which probesNmap. The following scans can be susceptible are FIN, NULL, and Xmas
scans.Similar problems are particular for certain type of scans.
The most famous and default option for scan includes, SYN scan, which could be conducted
instantly, to scan ports which are thousands in number per second on a fast network not
hampered by the firewalls which are restrictive. It is linked with unobtrusive and stealthy,
because it never finishes the TCP connections. Against any kind of compliant, SYN scan
works. It even lets the reliable and clear differentiation among the open, closed, and filtered
states.
Such a technique could be referred as the half-open scanning, as the complete TCP
connection is not opened. It is possible to send the SYN packet, due to opening the real
connection and next it waits for the response. The SYN/ACK denotes the listening of the port
(open), when RST (reset) is indicative of non-listener. When no response arrives once various
retransmissions, the port will be marked as filtered. The port is also marked filtered if an
ICMP unreachable error (type 3, code 0, 1, 2, 3, 9, 10, or 13) is received. When the SYN
packet (without the ACK flag) receives the response it is considered that the port is opened.
This is because of the feature of TCP which is rare and is called to be simultaneous open
/split handshake connection
-sT (TCP connect scan).
The TCP connect scan refers to the default the TCP scan type, in case where the SYN scan
isn’t the option. This is the case when a user does not have raw packet privileges. Rather
thannwriting the raw packets like how various types of scan perform, the Nmap asks for
underlying operating system, for establishing the connection with the target machine and port
by issuing the connect system call. TheNmap utilizes API for obtaining the information status
on every single try of the connection.
shell accounts and it is fortunate enough because the privileged options lets Nmapto becomes
highly flexible and powerful. As Nmaptries to generate accurate results, it must be
remembered that each ofits insights depend on the returned packets which the target
machines send (due to firewalls). Similar hosts cannot be trusted and it transfers the
responses that can confuse the Nmap. non-RFC-compliant hosts are the most common ones
which probesNmap. The following scans can be susceptible are FIN, NULL, and Xmas
scans.Similar problems are particular for certain type of scans.
The most famous and default option for scan includes, SYN scan, which could be conducted
instantly, to scan ports which are thousands in number per second on a fast network not
hampered by the firewalls which are restrictive. It is linked with unobtrusive and stealthy,
because it never finishes the TCP connections. Against any kind of compliant, SYN scan
works. It even lets the reliable and clear differentiation among the open, closed, and filtered
states.
Such a technique could be referred as the half-open scanning, as the complete TCP
connection is not opened. It is possible to send the SYN packet, due to opening the real
connection and next it waits for the response. The SYN/ACK denotes the listening of the port
(open), when RST (reset) is indicative of non-listener. When no response arrives once various
retransmissions, the port will be marked as filtered. The port is also marked filtered if an
ICMP unreachable error (type 3, code 0, 1, 2, 3, 9, 10, or 13) is received. When the SYN
packet (without the ACK flag) receives the response it is considered that the port is opened.
This is because of the feature of TCP which is rare and is called to be simultaneous open
/split handshake connection
-sT (TCP connect scan).
The TCP connect scan refers to the default the TCP scan type, in case where the SYN scan
isn’t the option. This is the case when a user does not have raw packet privileges. Rather
thannwriting the raw packets like how various types of scan perform, the Nmap asks for
underlying operating system, for establishing the connection with the target machine and port
by issuing the connect system call. TheNmap utilizes API for obtaining the information status
on every single try of the connection.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1.5 5thFlag: Privilege
The things learnt related to fundamentals of the Linux privilege escalation are listed
below (Feroze, 2018):
a) Applications and Services
b) Operating System
c) Confidential Information
d) Preparation
e) Finding Exploit Code
f) File Systems
g) Networking communication
3. Result and Conclusion
The topic ethical hacking is covered effectively, with the help of a provided case study. It
is noted that the study can be carried out,when the user gainssystem access along with root
level privileges. The cases study’s observation displays five flags for this project. These flags
were worked with the use of virtual machine.The First flag is utilized for checking the
content of the web server,where the admin’s username and password is identified. The
second flag is utilized for learning web shells, then the third flag is utilized for cracking the
password and the fourth flag is utilized for finding the user entering the incorrect password
intothe system. This process is supported by a tool named, TCP port scanner. At last, the final
flag is utilized to gain knowledge of the general Linux privilege escalations.
Therefore, all the flags and their requirements are identified, where each flag represents
different characteristics.
The things learnt related to fundamentals of the Linux privilege escalation are listed
below (Feroze, 2018):
a) Applications and Services
b) Operating System
c) Confidential Information
d) Preparation
e) Finding Exploit Code
f) File Systems
g) Networking communication
3. Result and Conclusion
The topic ethical hacking is covered effectively, with the help of a provided case study. It
is noted that the study can be carried out,when the user gainssystem access along with root
level privileges. The cases study’s observation displays five flags for this project. These flags
were worked with the use of virtual machine.The First flag is utilized for checking the
content of the web server,where the admin’s username and password is identified. The
second flag is utilized for learning web shells, then the third flag is utilized for cracking the
password and the fourth flag is utilized for finding the user entering the incorrect password
intothe system. This process is supported by a tool named, TCP port scanner. At last, the final
flag is utilized to gain knowledge of the general Linux privilege escalations.
Therefore, all the flags and their requirements are identified, where each flag represents
different characteristics.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
References
Cope, S. (2017). Introduction to HTTP : Understanding HTTP Basics. Retrieved from
http://www.steves-internet-guide.com/http-basics/
Everything You Need To Know About Web Shells. (2017). Retrieved from
https://www.darknet.org.uk/2016/07/everything-need-know-web-shells/
Feroze, R. (2018). A guide to Linux Privilege Escalation. Retrieved from
https://payatu.com/guide-linux-privilege-escalation/
Glia. (2016). Web Shells and Backdoors. Retrieved from https://no-sec.net/web-shells-and-
backdoors/
Port Scanning Techniques. (2018). Retrieved from https://nmap.org/book/man-port-scanning-
techniques.html
Prodromou, A. (2016). Detection and Prevention - An Introduction to Web-Shells - Final
Part. Retrieved from https://www.acunetix.com/blog/articles/detection-prevention-
introduction-web-shells-part-5/
What is a Web shell?. (2017). Retrieved from https://malware.expert/general/what-is-a-web-
shell/
Cope, S. (2017). Introduction to HTTP : Understanding HTTP Basics. Retrieved from
http://www.steves-internet-guide.com/http-basics/
Everything You Need To Know About Web Shells. (2017). Retrieved from
https://www.darknet.org.uk/2016/07/everything-need-know-web-shells/
Feroze, R. (2018). A guide to Linux Privilege Escalation. Retrieved from
https://payatu.com/guide-linux-privilege-escalation/
Glia. (2016). Web Shells and Backdoors. Retrieved from https://no-sec.net/web-shells-and-
backdoors/
Port Scanning Techniques. (2018). Retrieved from https://nmap.org/book/man-port-scanning-
techniques.html
Prodromou, A. (2016). Detection and Prevention - An Introduction to Web-Shells - Final
Part. Retrieved from https://www.acunetix.com/blog/articles/detection-prevention-
introduction-web-shells-part-5/
What is a Web shell?. (2017). Retrieved from https://malware.expert/general/what-is-a-web-
shell/
1 out of 11
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





