Analysis of Face Recognition System: Strengths and Weaknesses
VerifiedAdded on 2022/08/17
|6
|1275
|18
Report
AI Summary
This report provides a comprehensive analysis of face recognition systems, a prominent application of image analysis with roots in the 1960s and significant evolution in recent years. It explores the growing interest in these systems due to increasing security concerns and their use in identification and verification. The report delves into the strengths of face recognition, including enhanced security, easy integration with existing systems, high accuracy rates, full automation, and attendance tracking. Conversely, it also examines weaknesses such as processing and storage demands, image quality dependence, surveillance angle limitations, and high costs. The report concludes by highlighting the system's potential for future innovation while acknowledging its limitations and vulnerability to hacking and technical errors. It references key research and real-world applications by companies like Google and Facebook, illustrating the ongoing advancements in this field.

Running head: FACIAL RECOGNITION SYSTEM
FACIAL RECOGNITION SYSTEM
Name of the Student
Name of the university
Author note
FACIAL RECOGNITION SYSTEM
Name of the Student
Name of the university
Author note
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
1FACIAL RECOGNITION SYSTEM
Introduction
Face recognition system is considered as one amongst the most popular as well as
successful applications of image analysis. The research on this system started as early as in
the year 1960s and in the past few years this has shown drastic evolution. People are taking a
lot of interest in these face recognition systems as there has been an increase in the security
issues. The system is one of the popular systems used for identifying verification in this
digital world. The benefit the system is laced with is the reason for its growing use. There are
many existing solutions of this face recognition system and these solutions make use of
different software as well as different algorithms (Zhou, Cao and Yin 2015). Some of this
software extracts the features of the face from the input image for the purpose of identifying
the face while other algorithms normalize sets of face images after which the face data is
compressed then saving this in one image for using it to recognize users’ face. In this paper,
the strength and various weakness of this face recognition system will be considered.
Insights into face recognition system
Popular companies such as Google, Facebook and Amazon are coming up with
theoretical discoveries so that they can stay a step ahead in this race of biometric innovations.
For instance, Facebok launched DeepFace program which helps in determining whether two
photographed faces are of the same person (Sarkar, Patel and Chellappa 2016). These are
software and considering devices there are outdoor and vandal resistant facial recognition
terminal like ProFace, Bio-metric smart identification time attendance and access control
terminal like G3 H.
Introduction
Face recognition system is considered as one amongst the most popular as well as
successful applications of image analysis. The research on this system started as early as in
the year 1960s and in the past few years this has shown drastic evolution. People are taking a
lot of interest in these face recognition systems as there has been an increase in the security
issues. The system is one of the popular systems used for identifying verification in this
digital world. The benefit the system is laced with is the reason for its growing use. There are
many existing solutions of this face recognition system and these solutions make use of
different software as well as different algorithms (Zhou, Cao and Yin 2015). Some of this
software extracts the features of the face from the input image for the purpose of identifying
the face while other algorithms normalize sets of face images after which the face data is
compressed then saving this in one image for using it to recognize users’ face. In this paper,
the strength and various weakness of this face recognition system will be considered.
Insights into face recognition system
Popular companies such as Google, Facebook and Amazon are coming up with
theoretical discoveries so that they can stay a step ahead in this race of biometric innovations.
For instance, Facebok launched DeepFace program which helps in determining whether two
photographed faces are of the same person (Sarkar, Patel and Chellappa 2016). These are
software and considering devices there are outdoor and vandal resistant facial recognition
terminal like ProFace, Bio-metric smart identification time attendance and access control
terminal like G3 H.
2FACIAL RECOGNITION SYSTEM
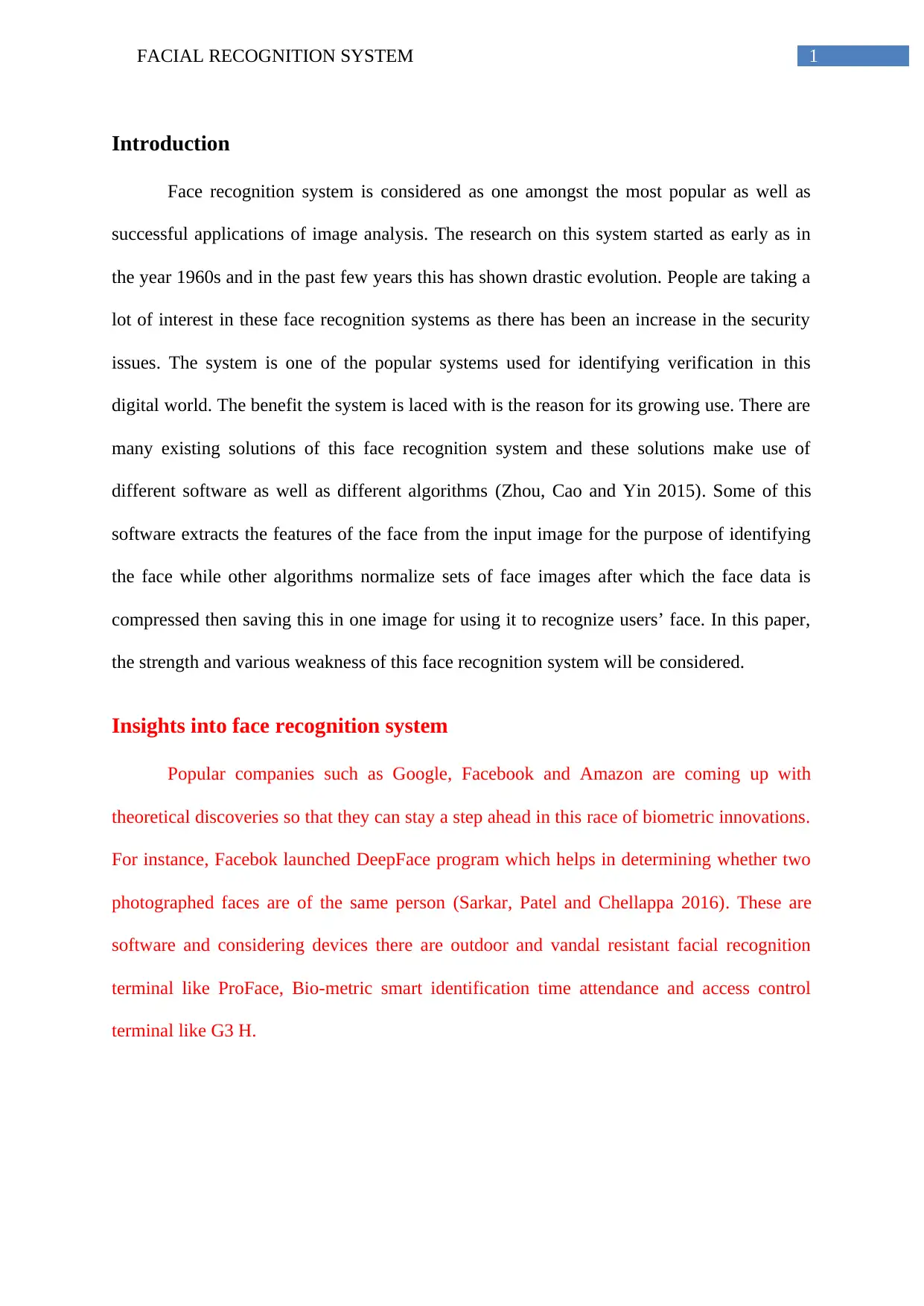
Picture 1: Working of facial recognition system (Team 2020)
Strengths of the face recognition system
1. Improvisations in the level of security- This system greatly enhance the security of any
premise where it is used. The visitors or the employees of the premise can be kept a track of
thus checking on unauthorized access.
2. Easy to integrate- The face recognition systems can be easily integrated to the existing
security software that are installed in the companies (Ding and Tao 2015). These systems can
be programmed easily as well to make them compatible with the computer system of the
company.
3. High rates of accuracy- These systems have been modified and new innovation have been
made since their inception and at present almost all of these systems have infrared cameras
which provide the users with accurate results.
4. Full automation- The system brings in automation in the identification process thereby
ensuring its flawlessness without any hindrance (Schroff, Kalenichenko and Philbin 2015).
Picture 1: Working of facial recognition system (Team 2020)
Strengths of the face recognition system
1. Improvisations in the level of security- This system greatly enhance the security of any
premise where it is used. The visitors or the employees of the premise can be kept a track of
thus checking on unauthorized access.
2. Easy to integrate- The face recognition systems can be easily integrated to the existing
security software that are installed in the companies (Ding and Tao 2015). These systems can
be programmed easily as well to make them compatible with the computer system of the
company.
3. High rates of accuracy- These systems have been modified and new innovation have been
made since their inception and at present almost all of these systems have infrared cameras
which provide the users with accurate results.
4. Full automation- The system brings in automation in the identification process thereby
ensuring its flawlessness without any hindrance (Schroff, Kalenichenko and Philbin 2015).
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
3FACIAL RECOGNITION SYSTEM
These also save the company or organizations or big buildings from deploying security
personnel.
5. Attendance tracking- This is considered one of the major advantages of the facial
recognition system as when an employee logs in to the system his or her attendance gets
marked and is updated to the same. The organization can thus keep a record of the entry as
well as the exit timings of its employees.
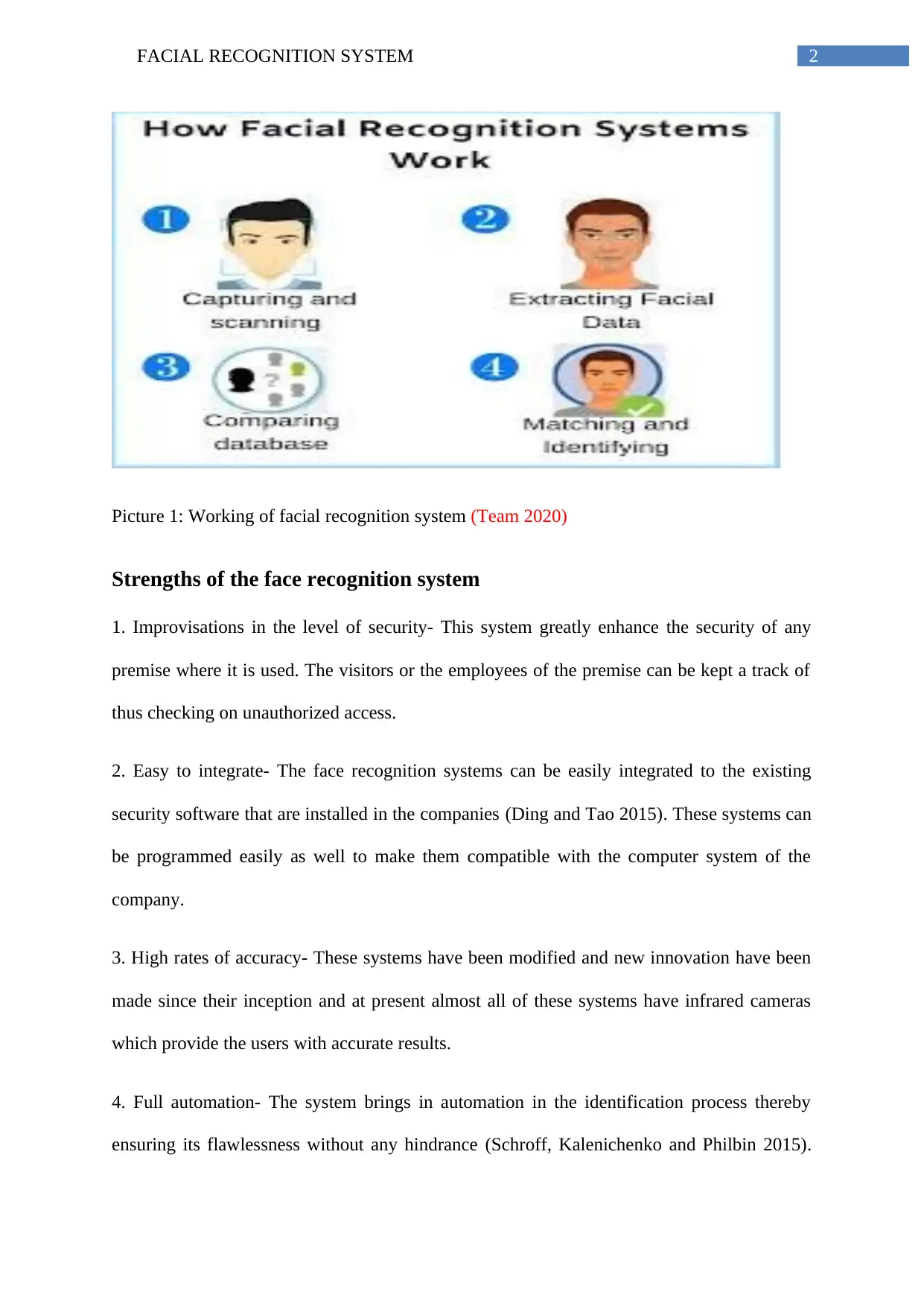
Picture 2: Different biometric system and main strengths and weakness (Biometrics set
smartphones apart, 2020)
Weaknesses of the face recognition system
1. Processing and storing- With volumes of data to be handled, the system compromises with
the storage capacity and burdens the firms with huge sets of data. Though it can be said that
HD-video can be got with quiet a less resolution still it requires a significant amount of space.
2. Size of the image and its quality- These systems are advanced software requiring HQ
digital cameras so that the algorithms can operate accurately (Khade, Gaikwad, Aher and
These also save the company or organizations or big buildings from deploying security
personnel.
5. Attendance tracking- This is considered one of the major advantages of the facial
recognition system as when an employee logs in to the system his or her attendance gets
marked and is updated to the same. The organization can thus keep a record of the entry as
well as the exit timings of its employees.
Picture 2: Different biometric system and main strengths and weakness (Biometrics set
smartphones apart, 2020)
Weaknesses of the face recognition system
1. Processing and storing- With volumes of data to be handled, the system compromises with
the storage capacity and burdens the firms with huge sets of data. Though it can be said that
HD-video can be got with quiet a less resolution still it requires a significant amount of space.
2. Size of the image and its quality- These systems are advanced software requiring HQ
digital cameras so that the algorithms can operate accurately (Khade, Gaikwad, Aher and
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
4FACIAL RECOGNITION SYSTEM
Patil 2016). There are systems that speed up image processing but are costly and not
recommended for small and medium scale industries.
3. Surveillance angle- The process involved in identification is also dependent on the angle of
surveillance that is an important parameter for capturing the face properly. Multiple angels
are in use but a frontal view is required to capture a face properly. The capture is dependent
on factors such as higher resolution and direct angle. It also has trouble with things such as
facial hair or sunglasses.
4. Cost- The cost of these face recognition systems are high and thus many companies cannot
afford such a security system and they prefer going for the finger print recognition system
instead (Agrawal and Singh 2015). The face recognition system is mostly used by bigger
firms that too studies suggest there usage is less as compared to the finger print recognition
system.
Conclusion
Summing up the discussion it can be said that, this face recognition system represents
lot of perspectives as well as promise for evolution in the days to come. It is desired of these
systems that in near future many new innovations will be integrated with this such as
processing gestures, palm patterns, expressions, scent signatures and many more. It cannot be
denied that though these systems are well programmed and technology laden they cannot
replace human force. These systems are vulnerable to hacking which can result in data
breach. The loss of data can also happen due to technical faults and errors thus it can be said
these systems have both pros and cons as any other system in the world.
Patil 2016). There are systems that speed up image processing but are costly and not
recommended for small and medium scale industries.
3. Surveillance angle- The process involved in identification is also dependent on the angle of
surveillance that is an important parameter for capturing the face properly. Multiple angels
are in use but a frontal view is required to capture a face properly. The capture is dependent
on factors such as higher resolution and direct angle. It also has trouble with things such as
facial hair or sunglasses.
4. Cost- The cost of these face recognition systems are high and thus many companies cannot
afford such a security system and they prefer going for the finger print recognition system
instead (Agrawal and Singh 2015). The face recognition system is mostly used by bigger
firms that too studies suggest there usage is less as compared to the finger print recognition
system.
Conclusion
Summing up the discussion it can be said that, this face recognition system represents
lot of perspectives as well as promise for evolution in the days to come. It is desired of these
systems that in near future many new innovations will be integrated with this such as
processing gestures, palm patterns, expressions, scent signatures and many more. It cannot be
denied that though these systems are well programmed and technology laden they cannot
replace human force. These systems are vulnerable to hacking which can result in data
breach. The loss of data can also happen due to technical faults and errors thus it can be said
these systems have both pros and cons as any other system in the world.
5FACIAL RECOGNITION SYSTEM
References
Agrawal, A.K. and Singh, Y.N., 2015. Evaluation of face recognition methods in
unconstrained environments. Procedia Computer Science, 48, pp.644-651.
Ding, C. and Tao, D., 2015. Robust face recognition via multimodal deep face
representation. IEEE Transactions on Multimedia, 17(11), pp.2049-2058.
Khade, B.S., Gaikwad, H.M., Aher, A.S. and Patil, K.K., 2016. Face recognition techniques:
a survey. International Journal of Computer Science and Mobile Computing, 5(11), pp.65-72.
Korea JoongAng Daily. 2020. Biometrics Set Smartphones Apart. [online] Available at:
<http://mengnews.joins.com/view.aspx?aid=3039229> [Accessed 7 April 2020].
Sarkar, S., Patel, V.M. and Chellappa, R., 2016, February. Deep feature-based face detection
on mobile devices. In 2016 IEEE International Conference on Identity, Security and
Behavior Analysis (ISBA) (pp. 1-8). IEEE.
Schroff, F., Kalenichenko, D. and Philbin, J., 2015. Facenet: A unified embedding for face
recognition and clustering. In Proceedings of the IEEE conference on computer vision and
pattern recognition (pp. 815-823).
Team, A., 2020. Improving Business Operations With Facial Recognition Technology |
Artificial Intelligence Services. [online] AI Oodles. Available at:
<https://artificialintelligence.oodles.io/blogs/improving-business-operations-facial-
recognition-artificial-intelligence-services/> [Accessed 7 April 2020].
Zhou, E., Cao, Z. and Yin, Q., 2015. Naive-deep face recognition: Touching the limit of LFW
benchmark or not?. arXiv preprint arXiv:1501.04690.
References
Agrawal, A.K. and Singh, Y.N., 2015. Evaluation of face recognition methods in
unconstrained environments. Procedia Computer Science, 48, pp.644-651.
Ding, C. and Tao, D., 2015. Robust face recognition via multimodal deep face
representation. IEEE Transactions on Multimedia, 17(11), pp.2049-2058.
Khade, B.S., Gaikwad, H.M., Aher, A.S. and Patil, K.K., 2016. Face recognition techniques:
a survey. International Journal of Computer Science and Mobile Computing, 5(11), pp.65-72.
Korea JoongAng Daily. 2020. Biometrics Set Smartphones Apart. [online] Available at:
<http://mengnews.joins.com/view.aspx?aid=3039229> [Accessed 7 April 2020].
Sarkar, S., Patel, V.M. and Chellappa, R., 2016, February. Deep feature-based face detection
on mobile devices. In 2016 IEEE International Conference on Identity, Security and
Behavior Analysis (ISBA) (pp. 1-8). IEEE.
Schroff, F., Kalenichenko, D. and Philbin, J., 2015. Facenet: A unified embedding for face
recognition and clustering. In Proceedings of the IEEE conference on computer vision and
pattern recognition (pp. 815-823).
Team, A., 2020. Improving Business Operations With Facial Recognition Technology |
Artificial Intelligence Services. [online] AI Oodles. Available at:
<https://artificialintelligence.oodles.io/blogs/improving-business-operations-facial-
recognition-artificial-intelligence-services/> [Accessed 7 April 2020].
Zhou, E., Cao, Z. and Yin, Q., 2015. Naive-deep face recognition: Touching the limit of LFW
benchmark or not?. arXiv preprint arXiv:1501.04690.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 6
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





