WLAN Design Proposal for HCP: NIT6110 Advanced Wireless Networks
VerifiedAdded on 2023/06/11
|38
|7186
|353
Report
AI Summary
This report presents a WLAN design project undertaken for HCP Corporation, an Intra Solar firm, to address the lack of network coverage on the ground floor of their building and overall workplace safety concerns. The project involves analyzing the current network capabilities, identifying limitations such as security vulnerabilities and bandwidth constraints, and proposing solutions including the implementation of a wireless Access Point on the ground floor. The report also discusses WLAN topologies, security measures like WPA, and guidelines for wireless network use. Additional capabilities required by the client, such as seamless roaming between access points, are also considered in the proposed design. The project aims to provide a reliable, secure, and scalable wireless network solution for HCP and its tenants.

Wireless Local Area Network
Name
Institution
Date
Name
Institution
Date
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Executive Summary
Wi-Fi is among the most significant progresses in the development of
internet—nobody desires to remain working with a desktop—however it is
as well among the most infuriating. This paper examines at networking
issues in an Intra Solar corporation known as HCP, which sells as well as installing Black Max
solar products. Presently, it is lacking network coverage within the ground floor of the building.
For HCP to have network coverage for the whole building, a wireless Access Point should be set
up on the ground floor through simply connecting the local area network (LAN) port to the main
router.
Wi-Fi is among the most significant progresses in the development of
internet—nobody desires to remain working with a desktop—however it is
as well among the most infuriating. This paper examines at networking
issues in an Intra Solar corporation known as HCP, which sells as well as installing Black Max
solar products. Presently, it is lacking network coverage within the ground floor of the building.
For HCP to have network coverage for the whole building, a wireless Access Point should be set
up on the ground floor through simply connecting the local area network (LAN) port to the main
router.
Contents
Wireless Local Area Network.........................................................................................................1
Executive Summary.........................................................................................................................2
Introduction......................................................................................................................................5
Client Organization and Project Background..................................................................................6
Current Network and Its Capabilities..............................................................................................7
Limitations in the Current Network.................................................................................................8
Additional Capabilities Required by Client...................................................................................11
Existing Network.......................................................................................................................12
Proposed network......................................................................................................................13
Components of Wireless Network.............................................................................................13
WLAN Topologies....................................................................................................................14
WLAN Security.........................................................................................................................16
Shared Key Authentication........................................................................................................18
Wireless Local Area Network.........................................................................................................1
Executive Summary.........................................................................................................................2
Introduction......................................................................................................................................5
Client Organization and Project Background..................................................................................6
Current Network and Its Capabilities..............................................................................................7
Limitations in the Current Network.................................................................................................8
Additional Capabilities Required by Client...................................................................................11
Existing Network.......................................................................................................................12
Proposed network......................................................................................................................13
Components of Wireless Network.............................................................................................13
WLAN Topologies....................................................................................................................14
WLAN Security.........................................................................................................................16
Shared Key Authentication........................................................................................................18
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Selection of Suitable Software and Hardware...........................................................................20
Implementation..........................................................................................................................20
Setup..........................................................................................................................................26
Guideline and Policy for Wireless Network Use.......................................................................30
Policy Scope..........................................................................................................................30
Policy Restriction...................................................................................................................30
Appropriate and Proper use...................................................................................................31
Regulatory Measures.............................................................................................................31
Acceptance of Policies and Regulations................................................................................32
Conclusion.....................................................................................................................................32
Implementation..........................................................................................................................20
Setup..........................................................................................................................................26
Guideline and Policy for Wireless Network Use.......................................................................30
Policy Scope..........................................................................................................................30
Policy Restriction...................................................................................................................30
Appropriate and Proper use...................................................................................................31
Regulatory Measures.............................................................................................................31
Acceptance of Policies and Regulations................................................................................32
Conclusion.....................................................................................................................................32
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Introduction
Being familiar with 802.11 radio indicators broadcasting from an aerial in horizontal
directions to the first floor of the building. When installing wireless networks in multi-floor
facilities, however, one should put into consideration that waves also propagate down and up
vertically to the floors (Kim, Jeon, Park, and Youn, Samsung Electronics Co Ltd, 2013). The
extent is not far in the case of vertical direction, nevertheless it is frequently enough to enter the
ceilings and floors in most constructions. The inter-floor signal transmission makes surveying of
sites become more complex, however one might be in a position to exploit the situation.
The first step is gaining a good know how of the way 802.11 signals circulate thru
different floors within the building where wireless network is to be deployed. Every facility is
different from the other, therefore it is advisable to do a bit of testing to decide the number of
floors that actually can attenuate the radio signals. It is important to remember that 5GHz and
2.4GHz signals proliferate differently via the same medium, therefore testing must be performed
Being familiar with 802.11 radio indicators broadcasting from an aerial in horizontal
directions to the first floor of the building. When installing wireless networks in multi-floor
facilities, however, one should put into consideration that waves also propagate down and up
vertically to the floors (Kim, Jeon, Park, and Youn, Samsung Electronics Co Ltd, 2013). The
extent is not far in the case of vertical direction, nevertheless it is frequently enough to enter the
ceilings and floors in most constructions. The inter-floor signal transmission makes surveying of
sites become more complex, however one might be in a position to exploit the situation.
The first step is gaining a good know how of the way 802.11 signals circulate thru
different floors within the building where wireless network is to be deployed. Every facility is
different from the other, therefore it is advisable to do a bit of testing to decide the number of
floors that actually can attenuate the radio signals. It is important to remember that 5GHz and
2.4GHz signals proliferate differently via the same medium, therefore testing must be performed
using the frequency one is planning to install. When installing 802.11n, it is advisable to test
both 5GHz and 2.4GHz frequencies (Ibrahim, Brancato, and Bongiorno, Apple Inc, 2017). Do
the test at the start of RF site surveys in order to get an enhanced idea of the way to position
testing access point based on inter-floor signals propagation.
Despite the fact that, great advances have been made in terms of the ease and speed of
implementing Wi-Fi network, the simple nature of RF (radio frequency) is generally unaffected.
Increasing the users accessing the WLAN within a small physical area remains a problem
(Sorrells, Bultman, Cook, Looke, Moses Jr, Rawlins, and Rawlins, ParkerVision Inc, 2012). The
process and steps for an effective high user densities WLAN design, which can be verified,
implemented, as well as maintained through Cisco’s Unified Wireless Network design is defined.
It includes the following general stages:
Plan: Decide application as well as device required such as protocols, bandwidth, frequencies,
SLA (service level agreement), etc.
Design: Control density, antennas, cell sizing, site survey, coverage, etc.
Implement: Installation, tune, establish baseline, test, etc.
Optimize: Monitor, adjust, report, reviewing baseline for service level agreement (SLA).
Operate: Cisco WCS (Wireless Control System) checking, troubleshooting apparatuses,
reporting and capacity monitoring tools, etc.
The general ideas in the high-density Wi-Fi plan remain factual for several environments.
However it is significant to remember that the solutions and content offered will be appropriate
both 5GHz and 2.4GHz frequencies (Ibrahim, Brancato, and Bongiorno, Apple Inc, 2017). Do
the test at the start of RF site surveys in order to get an enhanced idea of the way to position
testing access point based on inter-floor signals propagation.
Despite the fact that, great advances have been made in terms of the ease and speed of
implementing Wi-Fi network, the simple nature of RF (radio frequency) is generally unaffected.
Increasing the users accessing the WLAN within a small physical area remains a problem
(Sorrells, Bultman, Cook, Looke, Moses Jr, Rawlins, and Rawlins, ParkerVision Inc, 2012). The
process and steps for an effective high user densities WLAN design, which can be verified,
implemented, as well as maintained through Cisco’s Unified Wireless Network design is defined.
It includes the following general stages:
Plan: Decide application as well as device required such as protocols, bandwidth, frequencies,
SLA (service level agreement), etc.
Design: Control density, antennas, cell sizing, site survey, coverage, etc.
Implement: Installation, tune, establish baseline, test, etc.
Optimize: Monitor, adjust, report, reviewing baseline for service level agreement (SLA).
Operate: Cisco WCS (Wireless Control System) checking, troubleshooting apparatuses,
reporting and capacity monitoring tools, etc.
The general ideas in the high-density Wi-Fi plan remain factual for several environments.
However it is significant to remember that the solutions and content offered will be appropriate
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
for WLAN plan of HCP Company. The intention of the leader is to elucidate the problems in
WLAN plan for high-density user HCP as well as offering successful approaches so that
administrators and engineers know them as well as are in a position to tell the effect design
choices will have (Rudolf, Zuniga, Rahman, and Kwak, InterDigital Technology Corp, 2012).
Client Organization and Project Background
HCP, an Intra Solar firm that sells as well as installing Black Max solar items. The
company owns a construction situated at Footscay. Inside the organization head office, they have
rent out some office space to other firms such as Web Donate site, which is a company dealing in
real estates, and a furniture selling firm (Kholaif, Mendahawi, Barbu, and Bakthavathsalu,
BlackBerry Ltd, 2014). All the four firms are currently operating from the 2nd floor of that
building. All business operates from different offices and they have company-based single
network.
HCP realized that the whole establishment had serious factory safety challenging without
a central control as well as management system. The administration decided to reorganize the
structure to offer network connection as well as Internet access via HCP controlled
establishments (Gopi, Bidichandani, and Mohan, Marvell International Ltd, 2012). The other
firms who have rent the working space can utilize the services and devices offered by HCP.
HCP is arranging to rent out the ground floor that is at this time used as stores only and
does not have access to network. HCP intends to outspread the network service to the ground
WLAN plan for high-density user HCP as well as offering successful approaches so that
administrators and engineers know them as well as are in a position to tell the effect design
choices will have (Rudolf, Zuniga, Rahman, and Kwak, InterDigital Technology Corp, 2012).
Client Organization and Project Background
HCP, an Intra Solar firm that sells as well as installing Black Max solar items. The
company owns a construction situated at Footscay. Inside the organization head office, they have
rent out some office space to other firms such as Web Donate site, which is a company dealing in
real estates, and a furniture selling firm (Kholaif, Mendahawi, Barbu, and Bakthavathsalu,
BlackBerry Ltd, 2014). All the four firms are currently operating from the 2nd floor of that
building. All business operates from different offices and they have company-based single
network.
HCP realized that the whole establishment had serious factory safety challenging without
a central control as well as management system. The administration decided to reorganize the
structure to offer network connection as well as Internet access via HCP controlled
establishments (Gopi, Bidichandani, and Mohan, Marvell International Ltd, 2012). The other
firms who have rent the working space can utilize the services and devices offered by HCP.
HCP is arranging to rent out the ground floor that is at this time used as stores only and
does not have access to network. HCP intends to outspread the network service to the ground
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
floor as well from the 2nd floor. In addition, the Wi-Fi must be accessible from all corners of the
building.
Current Network and Its Capabilities
The HCP Corporation is currently using a network that only covers their individual
offices that are within second floor. Wireless is a limitless medium, which is not affected by
restrictions like wiring. In addition it is robust as well as flexible and not a must it be
safeguarded or routed among specific physical areas. For engineers, it might be appealing to
purely follow the outline of a prevailing wired network, then do "cut and paste" in case of
wireless networks (Roy, and Gupta, Empire Technology Development LLC, 2012). While this
procedure may seem convenient, it will as well replicate the wired system's shortcomings as well
as mistakes and end up being more expensive at the end. Generally, less installation talent and
equipment are needed to implement WLAN (wireless local area network) than in the case of a
wired system. With wireless network, less often means more. WLAN plan is a different exit from
wired plan, and the constituents, which make-up the whole outline will be focused in the
following several articles.
Being a limitless medium, the network design should facilitate efficient proliferation of
RF, wireless (radio frequency) signals. This enables capacity and coverage, which are main
WLAN system strictures (Abramov, Kirdin, and Sukharnikov, Airgain Inc, 2013). Where does
radio frequencies energy reach as well as how many users might effectively utilize the network
before it is over used to become slow? Several factors that are involved when designing a
dependable, available, and secure wireless system are there. Rational design and planning, based
building.
Current Network and Its Capabilities
The HCP Corporation is currently using a network that only covers their individual
offices that are within second floor. Wireless is a limitless medium, which is not affected by
restrictions like wiring. In addition it is robust as well as flexible and not a must it be
safeguarded or routed among specific physical areas. For engineers, it might be appealing to
purely follow the outline of a prevailing wired network, then do "cut and paste" in case of
wireless networks (Roy, and Gupta, Empire Technology Development LLC, 2012). While this
procedure may seem convenient, it will as well replicate the wired system's shortcomings as well
as mistakes and end up being more expensive at the end. Generally, less installation talent and
equipment are needed to implement WLAN (wireless local area network) than in the case of a
wired system. With wireless network, less often means more. WLAN plan is a different exit from
wired plan, and the constituents, which make-up the whole outline will be focused in the
following several articles.
Being a limitless medium, the network design should facilitate efficient proliferation of
RF, wireless (radio frequency) signals. This enables capacity and coverage, which are main
WLAN system strictures (Abramov, Kirdin, and Sukharnikov, Airgain Inc, 2013). Where does
radio frequencies energy reach as well as how many users might effectively utilize the network
before it is over used to become slow? Several factors that are involved when designing a
dependable, available, and secure wireless system are there. Rational design and planning, based
on thorough initial evaluations, can make sure that a wireless local area network will function the
first round and enable ease of extension without disruption.
Limitations in the Current Network
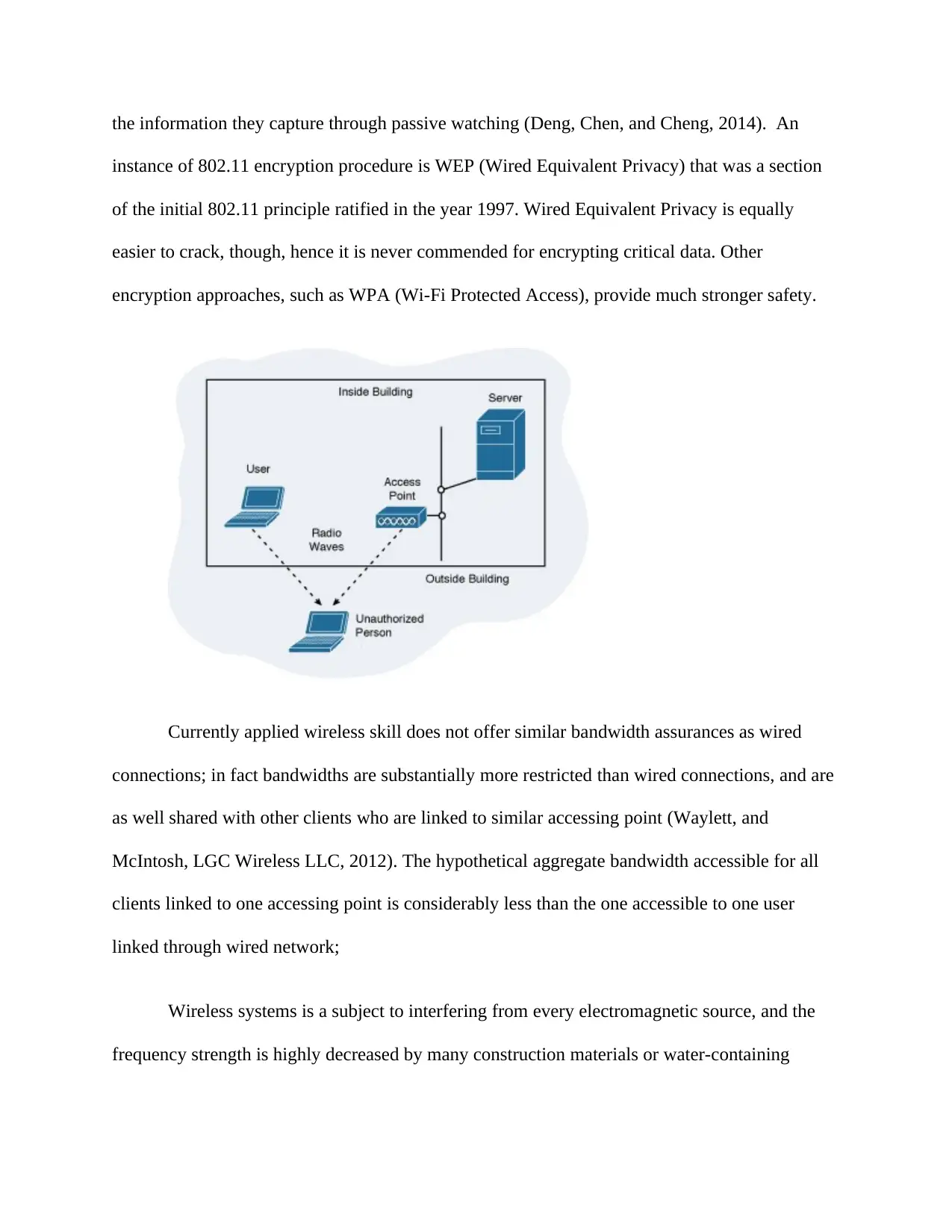
Wireless LANs purposely propagate data all over buildings, campuses, as well as towns.
As a consequence, the radio frequencies regularly go outside the limited area that a company
controls. For example, radio waves simply penetrate construction walls and might be gotten from
the establishment’s parking bay and perhaps a few meters away, as demonstrated in the Figure
below. Unauthorized people can passively retrieve an enterprise’s sensitive data by use of
laptops armed with radio cards from this range without being identified by network safety
workers. Hackers, for instance, might be waiting in a car outside a company, capturing every
802.11 transmission through easily accessible packet sniffers, like WireShark. When he captures
the information, the hacker can be in a position to retrieve details of e-mails as well as user secret
codes to enterprise servers. Obviously, the hacker might use this data to cause a security threat to
the business. This challenge as well is experienced in wired Ethernet systems, however to a
smaller extent. Flow of current via the metallic cables emits electromagnetic signals that could
be received by using critical listening apparatus (Doyle, Yuen, and Girardeau Jr, ViXS Systems
Inc, 2012). However the person should be nearby the cable to get the signals. Therefore, for
passive watching, wireless local area networks are never as safe as the way wired networks are.
The approach for undertaking the concerns of passive checking is by implementing
encryption among all user devices as well as the accessing points. Encryption modifies the data
bits in all frames, based on encryption keys, so that hackers cannot make anything sensible from
first round and enable ease of extension without disruption.
Limitations in the Current Network
Wireless LANs purposely propagate data all over buildings, campuses, as well as towns.
As a consequence, the radio frequencies regularly go outside the limited area that a company
controls. For example, radio waves simply penetrate construction walls and might be gotten from
the establishment’s parking bay and perhaps a few meters away, as demonstrated in the Figure
below. Unauthorized people can passively retrieve an enterprise’s sensitive data by use of
laptops armed with radio cards from this range without being identified by network safety
workers. Hackers, for instance, might be waiting in a car outside a company, capturing every
802.11 transmission through easily accessible packet sniffers, like WireShark. When he captures
the information, the hacker can be in a position to retrieve details of e-mails as well as user secret
codes to enterprise servers. Obviously, the hacker might use this data to cause a security threat to
the business. This challenge as well is experienced in wired Ethernet systems, however to a
smaller extent. Flow of current via the metallic cables emits electromagnetic signals that could
be received by using critical listening apparatus (Doyle, Yuen, and Girardeau Jr, ViXS Systems
Inc, 2012). However the person should be nearby the cable to get the signals. Therefore, for
passive watching, wireless local area networks are never as safe as the way wired networks are.
The approach for undertaking the concerns of passive checking is by implementing
encryption among all user devices as well as the accessing points. Encryption modifies the data
bits in all frames, based on encryption keys, so that hackers cannot make anything sensible from
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
the information they capture through passive watching (Deng, Chen, and Cheng, 2014). An
instance of 802.11 encryption procedure is WEP (Wired Equivalent Privacy) that was a section
of the initial 802.11 principle ratified in the year 1997. Wired Equivalent Privacy is equally
easier to crack, though, hence it is never commended for encrypting critical data. Other
encryption approaches, such as WPA (Wi-Fi Protected Access), provide much stronger safety.
Currently applied wireless skill does not offer similar bandwidth assurances as wired
connections; in fact bandwidths are substantially more restricted than wired connections, and are
as well shared with other clients who are linked to similar accessing point (Waylett, and
McIntosh, LGC Wireless LLC, 2012). The hypothetical aggregate bandwidth accessible for all
clients linked to one accessing point is considerably less than the one accessible to one user
linked through wired network;
Wireless systems is a subject to interfering from every electromagnetic source, and the
frequency strength is highly decreased by many construction materials or water-containing
instance of 802.11 encryption procedure is WEP (Wired Equivalent Privacy) that was a section
of the initial 802.11 principle ratified in the year 1997. Wired Equivalent Privacy is equally
easier to crack, though, hence it is never commended for encrypting critical data. Other
encryption approaches, such as WPA (Wi-Fi Protected Access), provide much stronger safety.
Currently applied wireless skill does not offer similar bandwidth assurances as wired
connections; in fact bandwidths are substantially more restricted than wired connections, and are
as well shared with other clients who are linked to similar accessing point (Waylett, and
McIntosh, LGC Wireless LLC, 2012). The hypothetical aggregate bandwidth accessible for all
clients linked to one accessing point is considerably less than the one accessible to one user
linked through wired network;
Wireless systems is a subject to interfering from every electromagnetic source, and the
frequency strength is highly decreased by many construction materials or water-containing
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
objects (e.g. Students in a class). The availability of items within the vicinity such as DECT
phones, microwave ovens, machinery, wire-framed door glasses, people, and several other things
within the local surroundings will dramatically decrease the reliability and throughput of the
fitting; such interference might go and come following the movement and operation of objects,
as well as an extent of intrusion at some moment says nothing concerning the extent of intrusion
at another moment (Abramov, Kirdin, and Sukharnikov, Airgain Inc, 2013);
For authentication purpose, wireless system traffic goes thru one of some of gateway
gadgets, and these might bring about problems of congestion or even failing under error
circumstances or malicious or high traffic; the activities that few can possibly influence the
network connection of many (Boyd, ZIH Corp, 2016);
Traffic from wireless networks is firewalled, however not every service might be
accessible to wireless clients. This is essential because for instance, bandwidth-hungry apps such
as video streaming are tightly regulated, to make sure that no single user can unintentionally
flood the shared system, to harm other users within the vicinity (Yeh, and Chang, MediaTek Inc,
2012).
Regarding application of wireless networks for bulk training purpose, it must be recalled
that through its nature, one access point can never be projected to provide reliable and sustained
services for huge amounts of traffics (Yeh, and Chang, MediaTek Inc, 2012). Typically, access
points can reasonably provide to about 25 users having 'bursty' traffic profiles (like reading
email, opening a typical web page). Effectiveness of wireless networks in certain areas will
reduce dramatically when the number of clients escalates, or when the users maintain constant
phones, microwave ovens, machinery, wire-framed door glasses, people, and several other things
within the local surroundings will dramatically decrease the reliability and throughput of the
fitting; such interference might go and come following the movement and operation of objects,
as well as an extent of intrusion at some moment says nothing concerning the extent of intrusion
at another moment (Abramov, Kirdin, and Sukharnikov, Airgain Inc, 2013);
For authentication purpose, wireless system traffic goes thru one of some of gateway
gadgets, and these might bring about problems of congestion or even failing under error
circumstances or malicious or high traffic; the activities that few can possibly influence the
network connection of many (Boyd, ZIH Corp, 2016);
Traffic from wireless networks is firewalled, however not every service might be
accessible to wireless clients. This is essential because for instance, bandwidth-hungry apps such
as video streaming are tightly regulated, to make sure that no single user can unintentionally
flood the shared system, to harm other users within the vicinity (Yeh, and Chang, MediaTek Inc,
2012).
Regarding application of wireless networks for bulk training purpose, it must be recalled
that through its nature, one access point can never be projected to provide reliable and sustained
services for huge amounts of traffics (Yeh, and Chang, MediaTek Inc, 2012). Typically, access
points can reasonably provide to about 25 users having 'bursty' traffic profiles (like reading
email, opening a typical web page). Effectiveness of wireless networks in certain areas will
reduce dramatically when the number of clients escalates, or when the users maintain constant
traffic flows for a duration of time (like, at initial system logon, when transferring large
documents or website pages containing large imageries, or streaming video or audio content).
Additional Capabilities Required by Client
At an elementary stage, roaming within a company IEEE 802.11 system happens when
an IEEE 802.11 users changes their AP (access point) connection from one access point to the
other in the same wireless local area network. Based on client abilities, an 802.11 wireless local
area network client can roam all over the same wireless local area network between access points
in the same signal band or among the 5 GHz and 2.4 GHz frequency bands (Yeh, and Chang,
MediaTek Inc, 2012). Tablets and smartphones, which have simultaneous Wi-Fi as well as
cellular connections might seamlessly roam through networks if there is appropriate
infrastructure network designs. When users roam from a wireless local area network with single
SSID (service set identifier) to a wireless local area network with the next SSID, the roaming
will never be smooth. The Wi-Fi user logic upholds only a single Wi-Fi Wireless LAN
verification at a particular time.
WLAN clients might roam based exclusively on the software abilities or they might
depend on supported roaming abilities offered by the wireless local area network infrastructure
access points. When there is client regulated roaming, the user is responsible for determining if it
should roam, and therefore detects, evaluates, as well as roam to another access point (Rudolf,
Zuniga, Rahman, and Kwak, InterDigital Technology Corp, 2012). The software residing in the
user assesses the quality of available Wi-Fi links, and implements the connection as well as
roaming logic to link an alternate access point to have an improved quality connection.
documents or website pages containing large imageries, or streaming video or audio content).
Additional Capabilities Required by Client
At an elementary stage, roaming within a company IEEE 802.11 system happens when
an IEEE 802.11 users changes their AP (access point) connection from one access point to the
other in the same wireless local area network. Based on client abilities, an 802.11 wireless local
area network client can roam all over the same wireless local area network between access points
in the same signal band or among the 5 GHz and 2.4 GHz frequency bands (Yeh, and Chang,
MediaTek Inc, 2012). Tablets and smartphones, which have simultaneous Wi-Fi as well as
cellular connections might seamlessly roam through networks if there is appropriate
infrastructure network designs. When users roam from a wireless local area network with single
SSID (service set identifier) to a wireless local area network with the next SSID, the roaming
will never be smooth. The Wi-Fi user logic upholds only a single Wi-Fi Wireless LAN
verification at a particular time.
WLAN clients might roam based exclusively on the software abilities or they might
depend on supported roaming abilities offered by the wireless local area network infrastructure
access points. When there is client regulated roaming, the user is responsible for determining if it
should roam, and therefore detects, evaluates, as well as roam to another access point (Rudolf,
Zuniga, Rahman, and Kwak, InterDigital Technology Corp, 2012). The software residing in the
user assesses the quality of available Wi-Fi links, and implements the connection as well as
roaming logic to link an alternate access point to have an improved quality connection.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 38
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.