Understanding HIPAA Regulations in Healthcare Research Projects
VerifiedAdded on 2022/01/27
|18
|3571
|61
Report
AI Summary
This report comprehensively examines the Health Insurance Portability and Accountability Act (HIPAA) regulations concerning the use of protected health information (PHI) in human subjects research. It details the scope of HIPAA's protections, focusing on individually identifiable health information created or used by covered entities. The report outlines the requirements for informed consent and authorization for research uses of PHI, and it explains the circumstances under which waivers, alterations, or exemptions to these requirements are permitted, such as through de-identified data, limited data sets, and data use agreements. It also covers the responsibilities of researchers and organizations in ensuring data security and privacy, including the role of Institutional Review Boards (IRBs) and privacy officers. The report further addresses specific exceptions to authorization requirements, such as activities preparatory to research and the use of information from deceased individuals, as well as the implications of HIPAA's minimum necessary standard and the right to an accounting of disclosures. The report emphasizes the importance of understanding and adhering to these regulations to protect patient privacy and maintain compliance in healthcare research settings.
Introduction
This module discusses data protection requirements for human subjects research that creates,
obtains, uses, or discloses health data, principally the protections that derive from the Health
Insurance Portability and Accountability Act (HIPAA).
Although HIPAA is the most prominent source, other federal and state laws as well as
professional and accrediting associations also establish requirements associated with the
protection of individual health information. Individuals with access to any individually
identifiable health information for any purpose must understand these constraints. If you use
such health information for human subjects research, you need to know the specific limitations
that apply to that activity, deriving from HIPAA and other regulations like 45 CFR 46,
Subpart A (also known as the Common Rule).
HIPAA's data-focused protections, which took effect starting in 2003, work together with the
Common Rule and U.S. Food and Drug Administration (FDA) protections; they are not a
replacement. Institutional Review Board (IRB) reviews using Common Rule and FDA criteria
remain as before, including aspects related to data protection. IRBs may share responsibilities for
addressing some of HIPAA's additional requirements in their reviews when those apply; or some
responsibilities may be allocated to another kind of body that HIPAA permits (a Privacy Board)
or to an institutional official that HIPAA requires (a privacy officer). These federal rules and
regulations provide a minimum standard of practice, complemented by states’ and
accreditation bodies’ additional requirements.
Learning Objectives
By the end of this module, you should be able to:
Summarize HIPAA’s additional privacy protections for individually identifiable health data
that are used for human subjects research, including authorizations and accountings of
disclosures.
Describe situations where full HIPAA privacy protections are required, and those which
can qualify for waivers, alterations, or exemptions with more limited requirements.
Explain the responsibilities of researchers and organizations for meeting HIPAA’s privacy
requirements and for appropriate data security protections that are necessary to protect
privacy.
HIPAA's Regulatory Scope
This module discusses data protection requirements for human subjects research that creates,
obtains, uses, or discloses health data, principally the protections that derive from the Health
Insurance Portability and Accountability Act (HIPAA).
Although HIPAA is the most prominent source, other federal and state laws as well as
professional and accrediting associations also establish requirements associated with the
protection of individual health information. Individuals with access to any individually
identifiable health information for any purpose must understand these constraints. If you use
such health information for human subjects research, you need to know the specific limitations
that apply to that activity, deriving from HIPAA and other regulations like 45 CFR 46,
Subpart A (also known as the Common Rule).
HIPAA's data-focused protections, which took effect starting in 2003, work together with the
Common Rule and U.S. Food and Drug Administration (FDA) protections; they are not a
replacement. Institutional Review Board (IRB) reviews using Common Rule and FDA criteria
remain as before, including aspects related to data protection. IRBs may share responsibilities for
addressing some of HIPAA's additional requirements in their reviews when those apply; or some
responsibilities may be allocated to another kind of body that HIPAA permits (a Privacy Board)
or to an institutional official that HIPAA requires (a privacy officer). These federal rules and
regulations provide a minimum standard of practice, complemented by states’ and
accreditation bodies’ additional requirements.
Learning Objectives
By the end of this module, you should be able to:
Summarize HIPAA’s additional privacy protections for individually identifiable health data
that are used for human subjects research, including authorizations and accountings of
disclosures.
Describe situations where full HIPAA privacy protections are required, and those which
can qualify for waivers, alterations, or exemptions with more limited requirements.
Explain the responsibilities of researchers and organizations for meeting HIPAA’s privacy
requirements and for appropriate data security protections that are necessary to protect
privacy.
HIPAA's Regulatory Scope
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
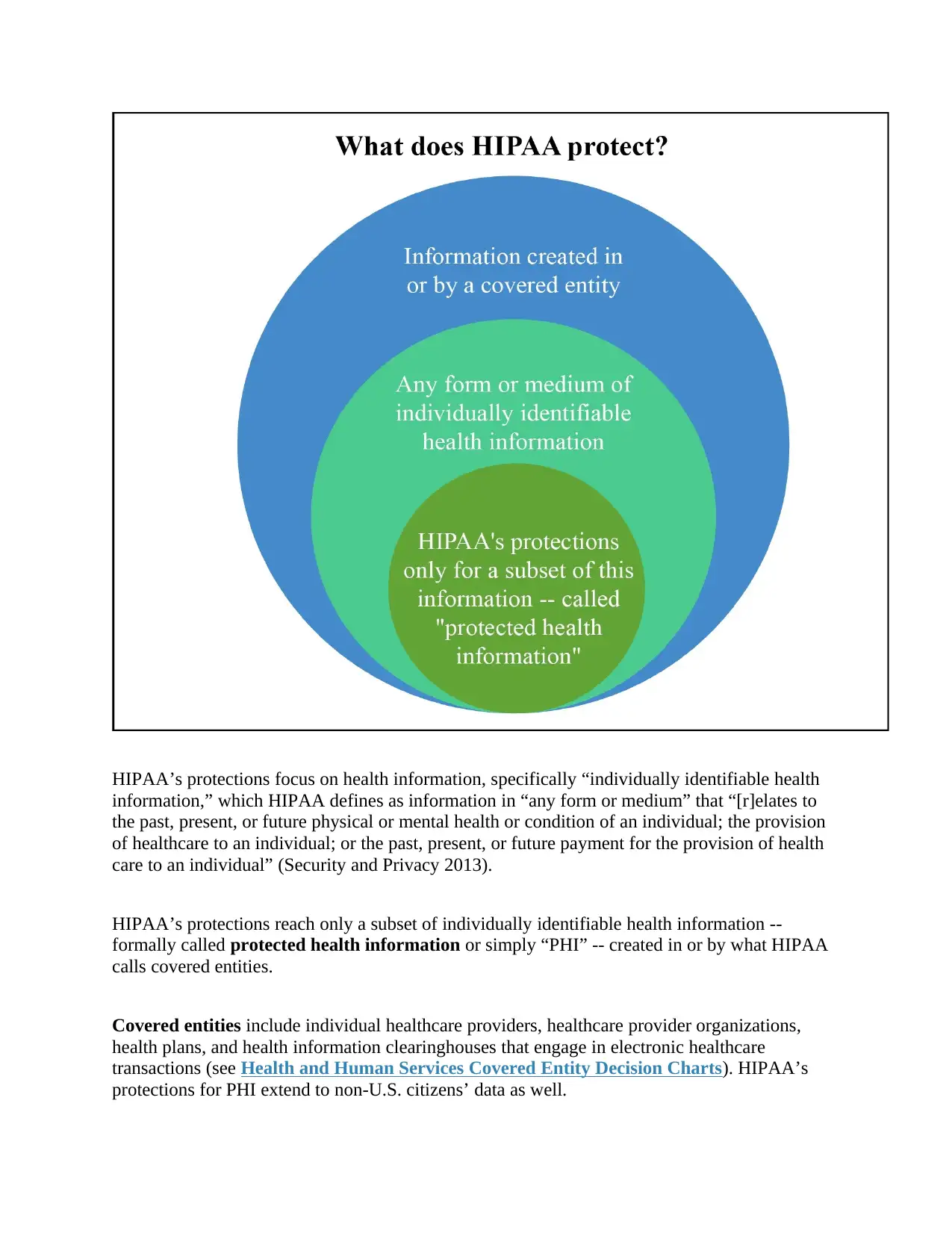
HIPAA’s protections focus on health information, specifically “individually identifiable health
information,” which HIPAA defines as information in “any form or medium” that “[r]elates to
the past, present, or future physical or mental health or condition of an individual; the provision
of healthcare to an individual; or the past, present, or future payment for the provision of health
care to an individual” (Security and Privacy 2013).
HIPAA’s protections reach only a subset of individually identifiable health information --
formally called protected health information or simply “PHI” -- created in or by what HIPAA
calls covered entities.
Covered entities include individual healthcare providers, healthcare provider organizations,
health plans, and health information clearinghouses that engage in electronic healthcare
transactions (see Health and Human Services Covered Entity Decision Charts). HIPAA’s
protections for PHI extend to non-U.S. citizens’ data as well.
information,” which HIPAA defines as information in “any form or medium” that “[r]elates to
the past, present, or future physical or mental health or condition of an individual; the provision
of healthcare to an individual; or the past, present, or future payment for the provision of health
care to an individual” (Security and Privacy 2013).
HIPAA’s protections reach only a subset of individually identifiable health information --
formally called protected health information or simply “PHI” -- created in or by what HIPAA
calls covered entities.
Covered entities include individual healthcare providers, healthcare provider organizations,
health plans, and health information clearinghouses that engage in electronic healthcare
transactions (see Health and Human Services Covered Entity Decision Charts). HIPAA’s
protections for PHI extend to non-U.S. citizens’ data as well.
Some identifiable health information used for research originates outside of covered entities, and
so may not be covered by HIPAA. However, you must check with your organization’s privacy
authorities before assuming your situation falls outside HIPAA’s scope.
What kinds of users and uses are covered?
HIPAA regulations set requirements for use and disclosure of PHI by covered entities, and by
extension on all members of a covered entity’s workforce that have contact with PHI. HIPAA’s
data protection requirements also apply “in the same manner” to business associates (and by
extension to the workforce of such business associates) that perform functions using PHI on a
covered entity’s behalf.
Researchers may be part of the workforce of a covered entity, or may be covered entities
themselves if they are also healthcare providers. If so, they are directly affected by the HIPAA’s
research rules. Researchers who meet neither of these conditions are still indirectly affected by
HIPAA rules if a covered entity is the source of their data and those data meet the definition of
PHI.
HIPAA’s rules on use and disclosure are generally “purpose-based” -- that is, the intended use
sets the rules more than the type of data itself. The research rules discussed here are different
than those for, say, treatment or treatment-related payments (relatively liberal), or for marketing
or fundraising (relatively strict). A few types of data, such as psychotherapy notes do receive
special protection under HIPAA. State laws also often have many categories of data with special
protections, with which you should be familiar (or be in contact with an organizational official
who has that knowledge).
What constitutes "research?"
Like the Common Rule, HIPAA defines research as a “systematic investigation, including
research development, testing, and evaluation, designed to develop and contribute to
generalizable knowledge” (Protection of Human Subjects 2018; Security and Privacy 2013).
Note that some kinds of investigative activities that use patient data are excluded in this
definition. For example:
so may not be covered by HIPAA. However, you must check with your organization’s privacy
authorities before assuming your situation falls outside HIPAA’s scope.
What kinds of users and uses are covered?
HIPAA regulations set requirements for use and disclosure of PHI by covered entities, and by
extension on all members of a covered entity’s workforce that have contact with PHI. HIPAA’s
data protection requirements also apply “in the same manner” to business associates (and by
extension to the workforce of such business associates) that perform functions using PHI on a
covered entity’s behalf.
Researchers may be part of the workforce of a covered entity, or may be covered entities
themselves if they are also healthcare providers. If so, they are directly affected by the HIPAA’s
research rules. Researchers who meet neither of these conditions are still indirectly affected by
HIPAA rules if a covered entity is the source of their data and those data meet the definition of
PHI.
HIPAA’s rules on use and disclosure are generally “purpose-based” -- that is, the intended use
sets the rules more than the type of data itself. The research rules discussed here are different
than those for, say, treatment or treatment-related payments (relatively liberal), or for marketing
or fundraising (relatively strict). A few types of data, such as psychotherapy notes do receive
special protection under HIPAA. State laws also often have many categories of data with special
protections, with which you should be familiar (or be in contact with an organizational official
who has that knowledge).
What constitutes "research?"
Like the Common Rule, HIPAA defines research as a “systematic investigation, including
research development, testing, and evaluation, designed to develop and contribute to
generalizable knowledge” (Protection of Human Subjects 2018; Security and Privacy 2013).
Note that some kinds of investigative activities that use patient data are excluded in this
definition. For example:
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide

The regulations are complex. So, as with the covered entity status, a determination by an
organization’s IRB, designated privacy official(s), or legal counsel is usually required to assure
that an activity is “not research” and therefore subject to different HIPAA rules.
Who enforces the HIPAA research protections?
A covered entity may choose to rely on an IRB to assess compliance with both the FDA and
Common Rule requirements and HIPAA research requirements. Alternatively, HIPAA provides
organization’s IRB, designated privacy official(s), or legal counsel is usually required to assure
that an activity is “not research” and therefore subject to different HIPAA rules.
Who enforces the HIPAA research protections?
A covered entity may choose to rely on an IRB to assess compliance with both the FDA and
Common Rule requirements and HIPAA research requirements. Alternatively, HIPAA provides
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
that covered entities may create a Privacy Board to handle some research-related issues, notably
determinations about eligibility for waivers, alterations, and exemptions from authorization
processes. A covered entity may also leave some decisions about compliance with the research
provisions of HIPAA to its designated privacy officer. It is critical that you understand the
allocation of responsibilities at your organization.
Research subjects, like patients generally, have recourse to both your organization’s authorities
and to federal and state agencies in the event they wish to file complaints about or have questions
regarding an organization's protective efforts.
As with any other planned activity related to protected health information, research must be
mentioned in a privacy notice that HIPAA requires be provided by covered entities to their
patients/customers. The privacy notice must include the ways in which data subjects may register
complaints and report problems, either locally or with federal authorities. Every researcher
should be familiar with their organization’s privacy notice, particularly the persons or
departments it identifies as enforcement authorities for the organization.
HIPAA Research-Related Rules
If the data in question meet the definition of PHI and are being used for purposes that fall within
HIPAA’s definition of research, HIPAA generally requires explicit
written authorization (consent) from the data subject for research uses.
However, HIPAA allows for research-related access to individuals’ identifiable health data
without authorization under certain circumstances:
determinations about eligibility for waivers, alterations, and exemptions from authorization
processes. A covered entity may also leave some decisions about compliance with the research
provisions of HIPAA to its designated privacy officer. It is critical that you understand the
allocation of responsibilities at your organization.
Research subjects, like patients generally, have recourse to both your organization’s authorities
and to federal and state agencies in the event they wish to file complaints about or have questions
regarding an organization's protective efforts.
As with any other planned activity related to protected health information, research must be
mentioned in a privacy notice that HIPAA requires be provided by covered entities to their
patients/customers. The privacy notice must include the ways in which data subjects may register
complaints and report problems, either locally or with federal authorities. Every researcher
should be familiar with their organization’s privacy notice, particularly the persons or
departments it identifies as enforcement authorities for the organization.
HIPAA Research-Related Rules
If the data in question meet the definition of PHI and are being used for purposes that fall within
HIPAA’s definition of research, HIPAA generally requires explicit
written authorization (consent) from the data subject for research uses.
However, HIPAA allows for research-related access to individuals’ identifiable health data
without authorization under certain circumstances:
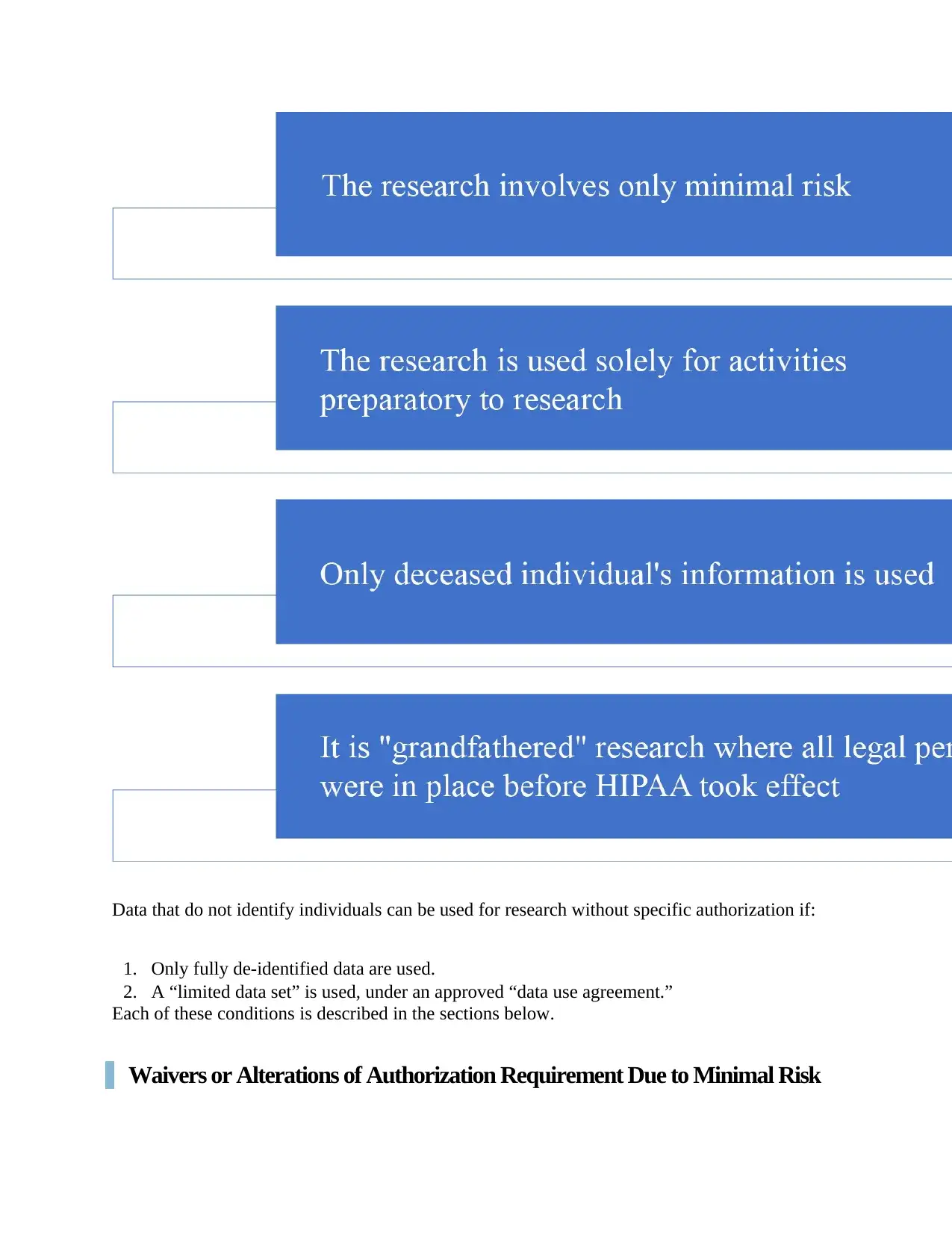
Data that do not identify individuals can be used for research without specific authorization if:
1. Only fully de-identified data are used.
2. A “limited data set” is used, under an approved “data use agreement.”
Each of these conditions is described in the sections below.
Waivers or Alterations of Authorization Requirement Due to Minimal Risk
1. Only fully de-identified data are used.
2. A “limited data set” is used, under an approved “data use agreement.”
Each of these conditions is described in the sections below.
Waivers or Alterations of Authorization Requirement Due to Minimal Risk
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
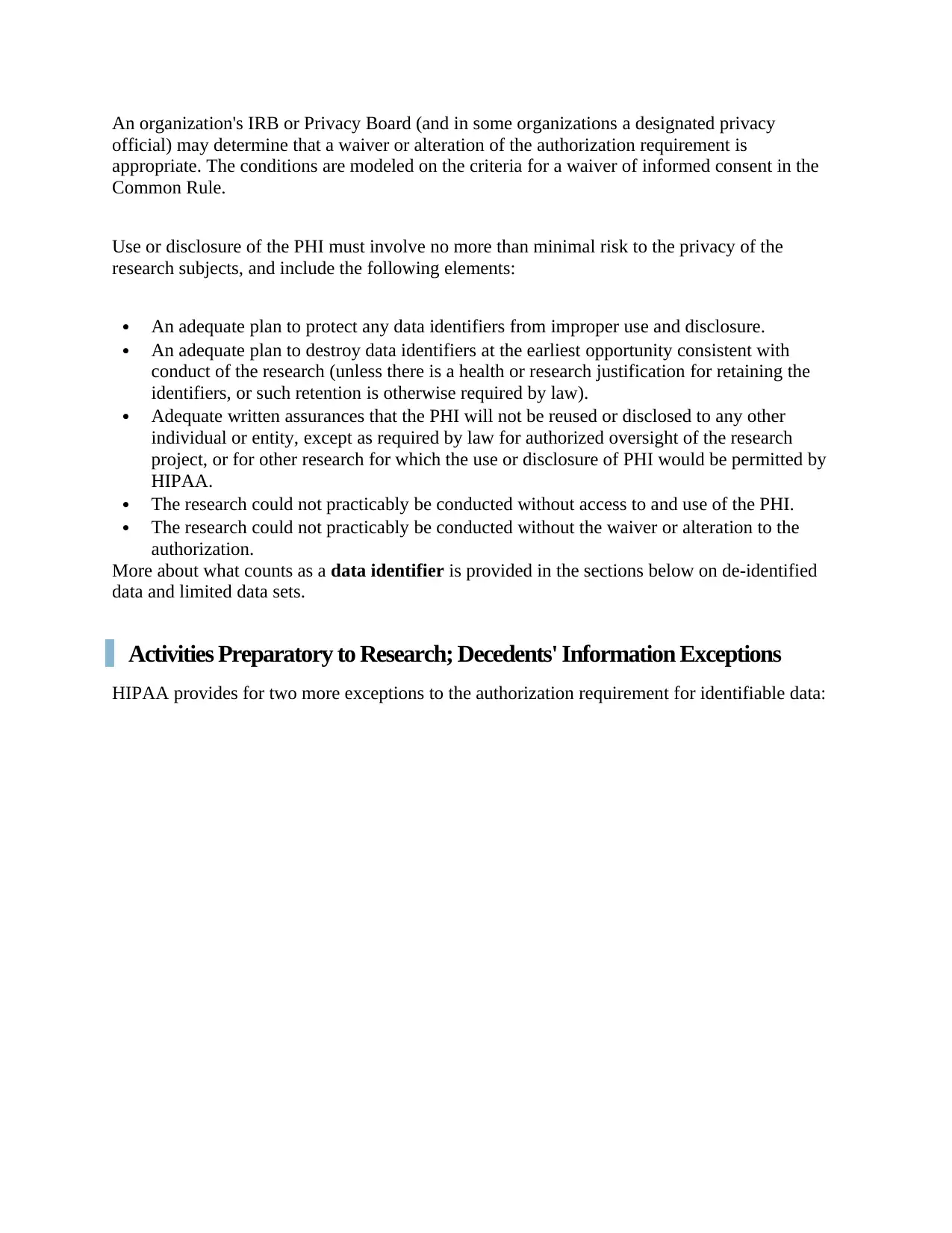
An organization's IRB or Privacy Board (and in some organizations a designated privacy
official) may determine that a waiver or alteration of the authorization requirement is
appropriate. The conditions are modeled on the criteria for a waiver of informed consent in the
Common Rule.
Use or disclosure of the PHI must involve no more than minimal risk to the privacy of the
research subjects, and include the following elements:
An adequate plan to protect any data identifiers from improper use and disclosure.
An adequate plan to destroy data identifiers at the earliest opportunity consistent with
conduct of the research (unless there is a health or research justification for retaining the
identifiers, or such retention is otherwise required by law).
Adequate written assurances that the PHI will not be reused or disclosed to any other
individual or entity, except as required by law for authorized oversight of the research
project, or for other research for which the use or disclosure of PHI would be permitted by
HIPAA.
The research could not practicably be conducted without access to and use of the PHI.
The research could not practicably be conducted without the waiver or alteration to the
authorization.
More about what counts as a data identifier is provided in the sections below on de-identified
data and limited data sets.
Activities Preparatory to Research; Decedents' Information Exceptions
HIPAA provides for two more exceptions to the authorization requirement for identifiable data:
official) may determine that a waiver or alteration of the authorization requirement is
appropriate. The conditions are modeled on the criteria for a waiver of informed consent in the
Common Rule.
Use or disclosure of the PHI must involve no more than minimal risk to the privacy of the
research subjects, and include the following elements:
An adequate plan to protect any data identifiers from improper use and disclosure.
An adequate plan to destroy data identifiers at the earliest opportunity consistent with
conduct of the research (unless there is a health or research justification for retaining the
identifiers, or such retention is otherwise required by law).
Adequate written assurances that the PHI will not be reused or disclosed to any other
individual or entity, except as required by law for authorized oversight of the research
project, or for other research for which the use or disclosure of PHI would be permitted by
HIPAA.
The research could not practicably be conducted without access to and use of the PHI.
The research could not practicably be conducted without the waiver or alteration to the
authorization.
More about what counts as a data identifier is provided in the sections below on de-identified
data and limited data sets.
Activities Preparatory to Research; Decedents' Information Exceptions
HIPAA provides for two more exceptions to the authorization requirement for identifiable data:
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
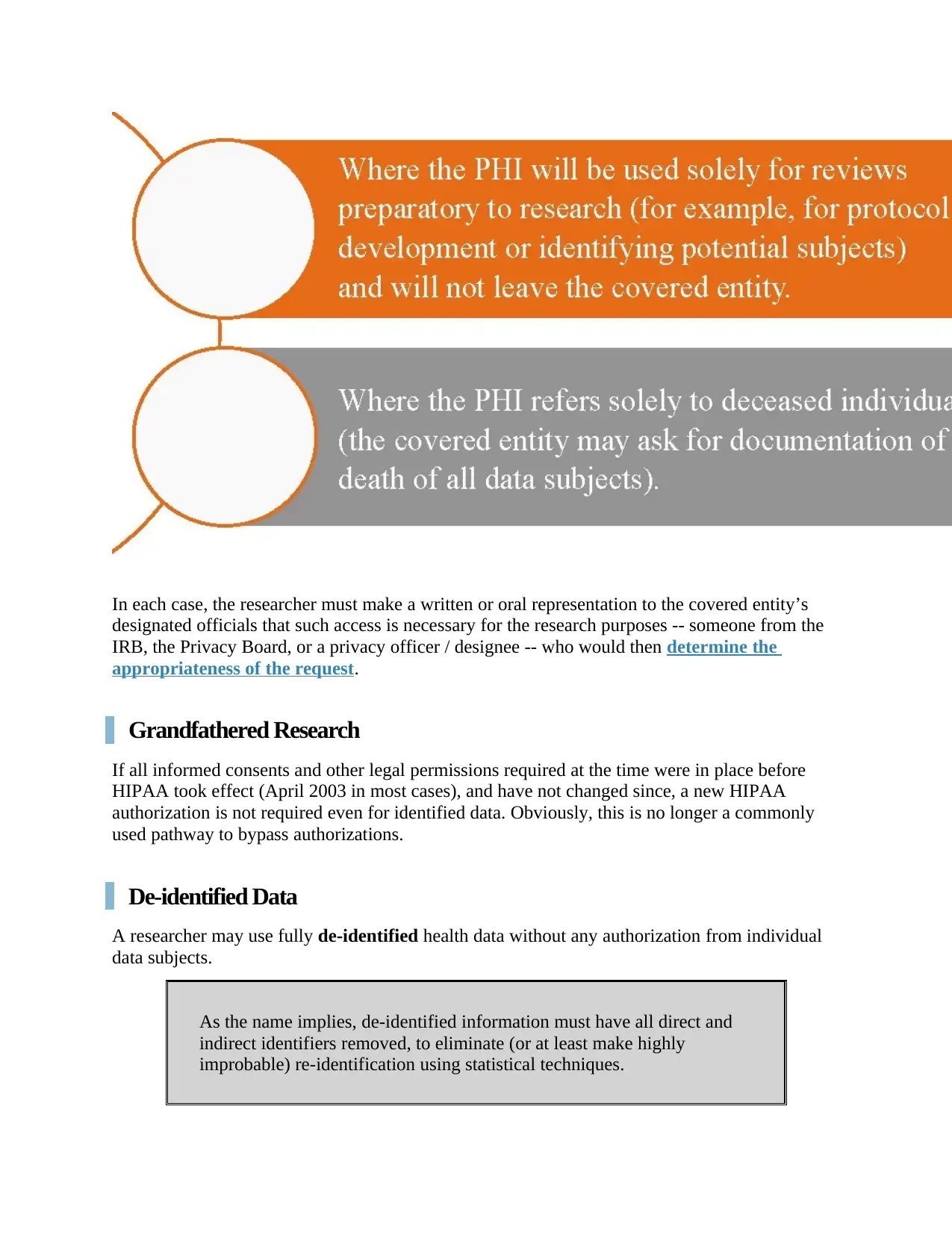
In each case, the researcher must make a written or oral representation to the covered entity’s
designated officials that such access is necessary for the research purposes -- someone from the
IRB, the Privacy Board, or a privacy officer / designee -- who would then determine the
appropriateness of the request.
Grandfathered Research
If all informed consents and other legal permissions required at the time were in place before
HIPAA took effect (April 2003 in most cases), and have not changed since, a new HIPAA
authorization is not required even for identified data. Obviously, this is no longer a commonly
used pathway to bypass authorizations.
De-identified Data
A researcher may use fully de-identified health data without any authorization from individual
data subjects.
As the name implies, de-identified information must have all direct and
indirect identifiers removed, to eliminate (or at least make highly
improbable) re-identification using statistical techniques.
designated officials that such access is necessary for the research purposes -- someone from the
IRB, the Privacy Board, or a privacy officer / designee -- who would then determine the
appropriateness of the request.
Grandfathered Research
If all informed consents and other legal permissions required at the time were in place before
HIPAA took effect (April 2003 in most cases), and have not changed since, a new HIPAA
authorization is not required even for identified data. Obviously, this is no longer a commonly
used pathway to bypass authorizations.
De-identified Data
A researcher may use fully de-identified health data without any authorization from individual
data subjects.
As the name implies, de-identified information must have all direct and
indirect identifiers removed, to eliminate (or at least make highly
improbable) re-identification using statistical techniques.
De-identified information is no longer considered PHI, because by definition it is no longer
individually identifiable.
HHS issued its Guidance Regarding Methods for De-identification of Protected Health
Information in 2012. This guidance provides a detailed description of alternative methods, and
should be considered required reading for anyone contemplating a de-identification strategy.
Under the HIPAA regulations, successful de-identification may be based on an "Expert
Determination" by an “individual with appropriate knowledge” of statistical techniques who has
analyzed the data set and can attest that the risk of re-identification is “very small.” (Very small
is not defined in the regulations.) Alternatively, covered entities may use the “Safe Harbor”
method of removing 18 types of identifying elements specified in the HIPAA regulations. In
either case, the covered entity must have no actual knowledge that re-identification is possible or
likely, for example by linking to other known data sets.
Limited Data Sets and Data Use Agreements
De-identification trades privacy protection for research productivity. Sometimes the trade-off is
too steep, and a fully de-identified data set will not meet a research need. As an alternative, a
covered entity may disclose PHI in a limited data set (LDS) to a researcher who has entered
into an appropriate data use agreement.
A LDS must have all direct identifiers removed; however, it may still
include information that could “indirectly” identify the subject using
statistical methods.
That is, the disclosure risk is greater than “very small.”
The data use agreement for an LDS must:
Delineate the permitted uses and disclosures of such information by the
recipient, consistent with the purposes of research;
Limit the individuals that can use or receive the data; and
Require the recipient to agree not to re-identify the data or contact the
individuals.
Minimum Necessary Uses and Disclosures
Uses and disclosures of data for research that are allowed to bypass the
authorization requirement are still subject to the minimum necessary
individually identifiable.
HHS issued its Guidance Regarding Methods for De-identification of Protected Health
Information in 2012. This guidance provides a detailed description of alternative methods, and
should be considered required reading for anyone contemplating a de-identification strategy.
Under the HIPAA regulations, successful de-identification may be based on an "Expert
Determination" by an “individual with appropriate knowledge” of statistical techniques who has
analyzed the data set and can attest that the risk of re-identification is “very small.” (Very small
is not defined in the regulations.) Alternatively, covered entities may use the “Safe Harbor”
method of removing 18 types of identifying elements specified in the HIPAA regulations. In
either case, the covered entity must have no actual knowledge that re-identification is possible or
likely, for example by linking to other known data sets.
Limited Data Sets and Data Use Agreements
De-identification trades privacy protection for research productivity. Sometimes the trade-off is
too steep, and a fully de-identified data set will not meet a research need. As an alternative, a
covered entity may disclose PHI in a limited data set (LDS) to a researcher who has entered
into an appropriate data use agreement.
A LDS must have all direct identifiers removed; however, it may still
include information that could “indirectly” identify the subject using
statistical methods.
That is, the disclosure risk is greater than “very small.”
The data use agreement for an LDS must:
Delineate the permitted uses and disclosures of such information by the
recipient, consistent with the purposes of research;
Limit the individuals that can use or receive the data; and
Require the recipient to agree not to re-identify the data or contact the
individuals.
Minimum Necessary Uses and Disclosures
Uses and disclosures of data for research that are allowed to bypass the
authorization requirement are still subject to the minimum necessary
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
standard -- that is, the uses/disclosures must be no more than the minimum
required for the described research purpose. A covered entity may rely on a
researcher's documentation -- or the assessment of an IRB or Privacy Board --
that the information requested is the minimum necessary for the research
purpose.
By contrast, research information obtained using an authorization is not bound by
the minimum necessary standard -- on the theory that the data subject has given
explicit permission in accordance with the signed authorization. However, be
aware that while HIPAA may not require a minimum necessary justification at all
times, an IRB's evaluation of risks and burdens on human research subjects
arguably does.
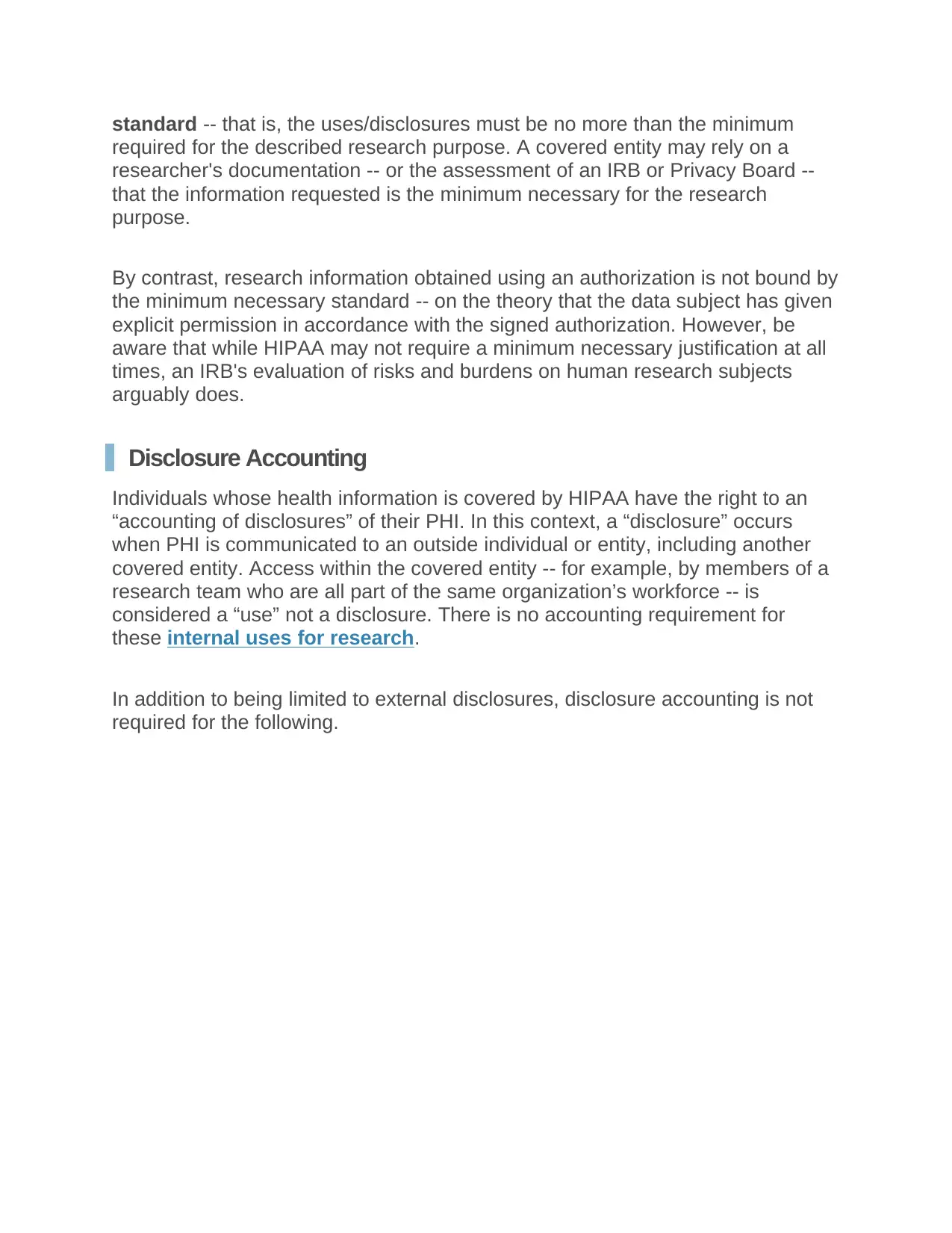
Disclosure Accounting
Individuals whose health information is covered by HIPAA have the right to an
“accounting of disclosures” of their PHI. In this context, a “disclosure” occurs
when PHI is communicated to an outside individual or entity, including another
covered entity. Access within the covered entity -- for example, by members of a
research team who are all part of the same organization’s workforce -- is
considered a “use” not a disclosure. There is no accounting requirement for
these internal uses for research.
In addition to being limited to external disclosures, disclosure accounting is not
required for the following.
required for the described research purpose. A covered entity may rely on a
researcher's documentation -- or the assessment of an IRB or Privacy Board --
that the information requested is the minimum necessary for the research
purpose.
By contrast, research information obtained using an authorization is not bound by
the minimum necessary standard -- on the theory that the data subject has given
explicit permission in accordance with the signed authorization. However, be
aware that while HIPAA may not require a minimum necessary justification at all
times, an IRB's evaluation of risks and burdens on human research subjects
arguably does.
Disclosure Accounting
Individuals whose health information is covered by HIPAA have the right to an
“accounting of disclosures” of their PHI. In this context, a “disclosure” occurs
when PHI is communicated to an outside individual or entity, including another
covered entity. Access within the covered entity -- for example, by members of a
research team who are all part of the same organization’s workforce -- is
considered a “use” not a disclosure. There is no accounting requirement for
these internal uses for research.
In addition to being limited to external disclosures, disclosure accounting is not
required for the following.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
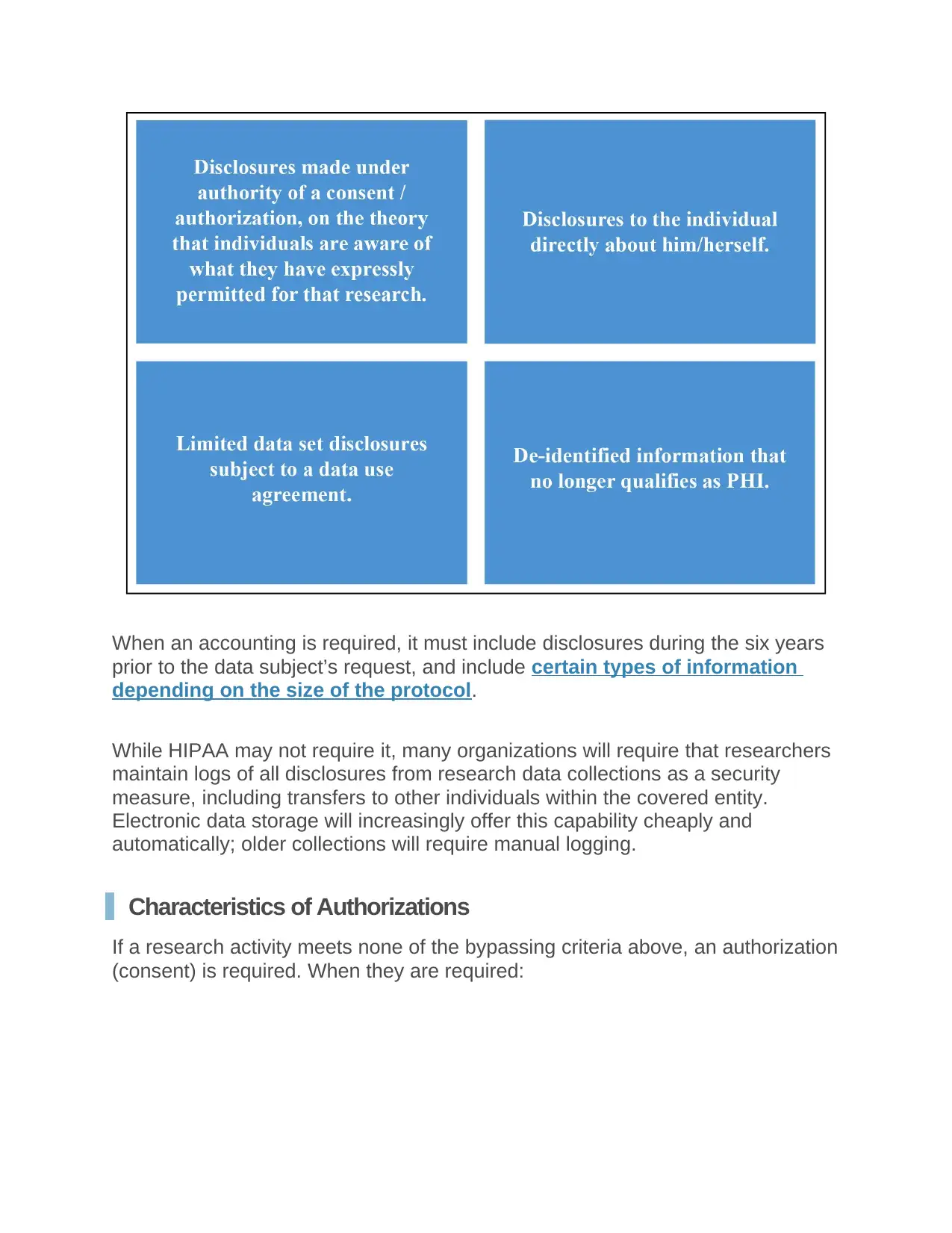
When an accounting is required, it must include disclosures during the six years
prior to the data subject’s request, and include certain types of information
depending on the size of the protocol.
While HIPAA may not require it, many organizations will require that researchers
maintain logs of all disclosures from research data collections as a security
measure, including transfers to other individuals within the covered entity.
Electronic data storage will increasingly offer this capability cheaply and
automatically; older collections will require manual logging.
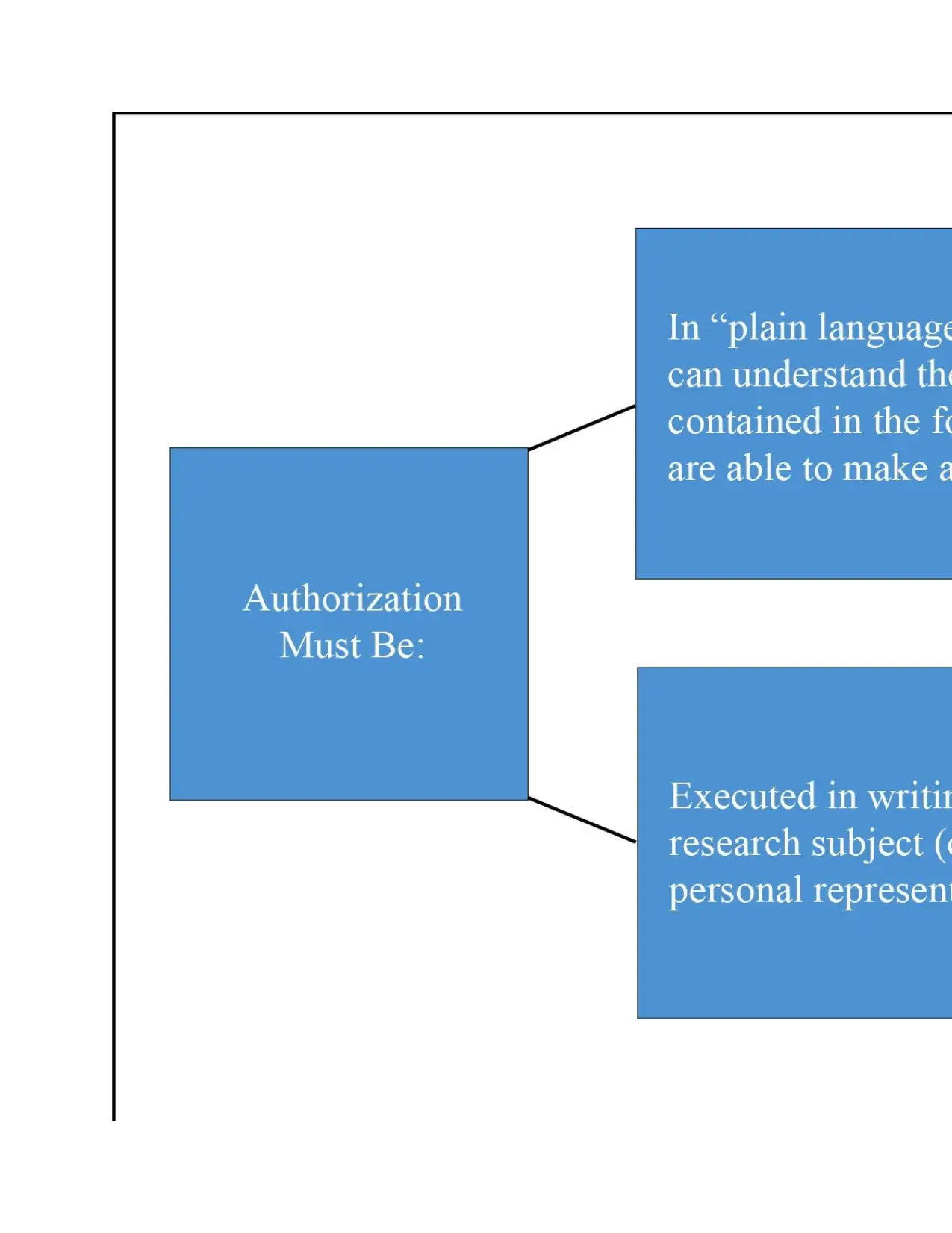
Characteristics of Authorizations
If a research activity meets none of the bypassing criteria above, an authorization
(consent) is required. When they are required:
prior to the data subject’s request, and include certain types of information
depending on the size of the protocol.
While HIPAA may not require it, many organizations will require that researchers
maintain logs of all disclosures from research data collections as a security
measure, including transfers to other individuals within the covered entity.
Electronic data storage will increasingly offer this capability cheaply and
automatically; older collections will require manual logging.
Characteristics of Authorizations
If a research activity meets none of the bypassing criteria above, an authorization
(consent) is required. When they are required:
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 18
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





