T2 2019 HS1011 Group Project: Holmes Institute Network Design
VerifiedAdded on 2022/10/04
|6
|1517
|20
Project
AI Summary
This project provides a detailed network design for the Holmes Institute, a multi-school campus in Melbourne. The design addresses the institute's need for a robust and secure network infrastructure. The project covers hardware and software requirements, including processor speed, RAM, and software like Chrome, Mozilla, and Office. Security is a major focus, with discussions on VPN security, multi-factor authentication, and regular updates. The design utilizes Cisco SAFE architecture, employing a hybrid topology for flexibility and scalability. The project also covers network testing, regression testing, methods for improving security (like 802.1X and VLANs), network management aspects, and a list of necessary equipment with associated costs. The design aims to provide a secure and efficient network for the institute's operations.
DATA COMMUNICATIONS AND NETWORKS
Name
Instructor
Institution
Course
City
Date
Name
Instructor
Institution
Course
City
Date
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
DATA COMMUNICATION AND NETWORS
Introduction
This paper identifies the resources which are needed to set-up and design a network
infrastructure for a new campus for Holmes Institute which is located in Melbourne. Holmes institute is
a five storey shop with school of information systems, school of cyber security, school of business, and
school of fashion. Each of the four school has two subnets; i.e. the student and staff subnets. In addition,
the institute has over six departments which are student services, higher education. Finance, human
resource, Exam and Accreditation. The institute has expanded to include two new schools and an IT
center. Due to this the institute has purchased one metro Ethernet connection from HLNET which
provides 10 Mbps for both download and upload.
Part 1: Holmes network design
Hardware and software requirements
Table one below lists both hardware and software requirement for the new network
Hardware requirements Software requirement
Processor speed with 2 GHz
Minimum RAM is 2 GB
Monitor resolution is 1024 by 768 or higher
Mouse and Keyboard ought to be compatible
pointing devices
Chrome 36+
Mozilla 31+
Office 2019
Kaspersky’s anti0virus
Security requirements for the new network
One of the security requirements for Holmes institute is securing its VPN. Here identity
authentication and data encryption are two major important aspects to securing VPN. According to
NIST, any open network connection is a weakness which attackers or hackers can exploit to sneak into
an organization network. One of the most vulnerable resource here will be the institute student and
office data. To secure the institute VPN, Holmes needs to use multi0factor authentication method. In
addition, remote users of the network needs to enter a password when login into the institute network.
Also, the institute needs to create and enforce user-access policies for all the remote users. Second
security requirement is keeping patches and updates current. Usually, hackers exploit weaknesses in
operating systems, web servers, and software applications. Holmes needs to verify that all its user
computers are running the current version of operating systems and keep record to make sure that each
device is updated regularly [1]
Introduction
This paper identifies the resources which are needed to set-up and design a network
infrastructure for a new campus for Holmes Institute which is located in Melbourne. Holmes institute is
a five storey shop with school of information systems, school of cyber security, school of business, and
school of fashion. Each of the four school has two subnets; i.e. the student and staff subnets. In addition,
the institute has over six departments which are student services, higher education. Finance, human
resource, Exam and Accreditation. The institute has expanded to include two new schools and an IT
center. Due to this the institute has purchased one metro Ethernet connection from HLNET which
provides 10 Mbps for both download and upload.
Part 1: Holmes network design
Hardware and software requirements
Table one below lists both hardware and software requirement for the new network
Hardware requirements Software requirement
Processor speed with 2 GHz
Minimum RAM is 2 GB
Monitor resolution is 1024 by 768 or higher
Mouse and Keyboard ought to be compatible
pointing devices
Chrome 36+
Mozilla 31+
Office 2019
Kaspersky’s anti0virus
Security requirements for the new network
One of the security requirements for Holmes institute is securing its VPN. Here identity
authentication and data encryption are two major important aspects to securing VPN. According to
NIST, any open network connection is a weakness which attackers or hackers can exploit to sneak into
an organization network. One of the most vulnerable resource here will be the institute student and
office data. To secure the institute VPN, Holmes needs to use multi0factor authentication method. In
addition, remote users of the network needs to enter a password when login into the institute network.
Also, the institute needs to create and enforce user-access policies for all the remote users. Second
security requirement is keeping patches and updates current. Usually, hackers exploit weaknesses in
operating systems, web servers, and software applications. Holmes needs to verify that all its user
computers are running the current version of operating systems and keep record to make sure that each
device is updated regularly [1]
Rules in the security policy for the new network
A security policy is a document which states security controls without specifying the current
technologies. A network security policy should always be applied through-out an organization in a
consistent manner. It provides references for employees to operate their typical activities. For the new
institute network, the institute needs to sign an NDA for each of the student and institute staff about
not disclosing any details about the deployed devices. This rule protects the laid network devices.
Second rule is to regularly apply patches and security updates on weekly basis, and all services needs to
be disabled if they are not in use. This ensures that all operating systems and applications are up to
date. In terms of internet access, internet access policies should include blocking of all websites which
are deemed inappropriate. Lastly, VPN is there to protect institute data meaning that it should only be
used by the institute staff not the students [2].
Network testing
Network testing is the act of qualitatively and quantitatively measuring the performance of a
computer network. The act tests for records and certain processes and behaviors of a network. The
major objective of network testing is to address network design faults and any implementation defects.
Testing in this case will include testing functionality of the network, performance, stability, and
interoperability. In addition, testing will assists in evaluating negative and false positive of network
security. It will also assists in profiling and benchmarking systems and services [3].
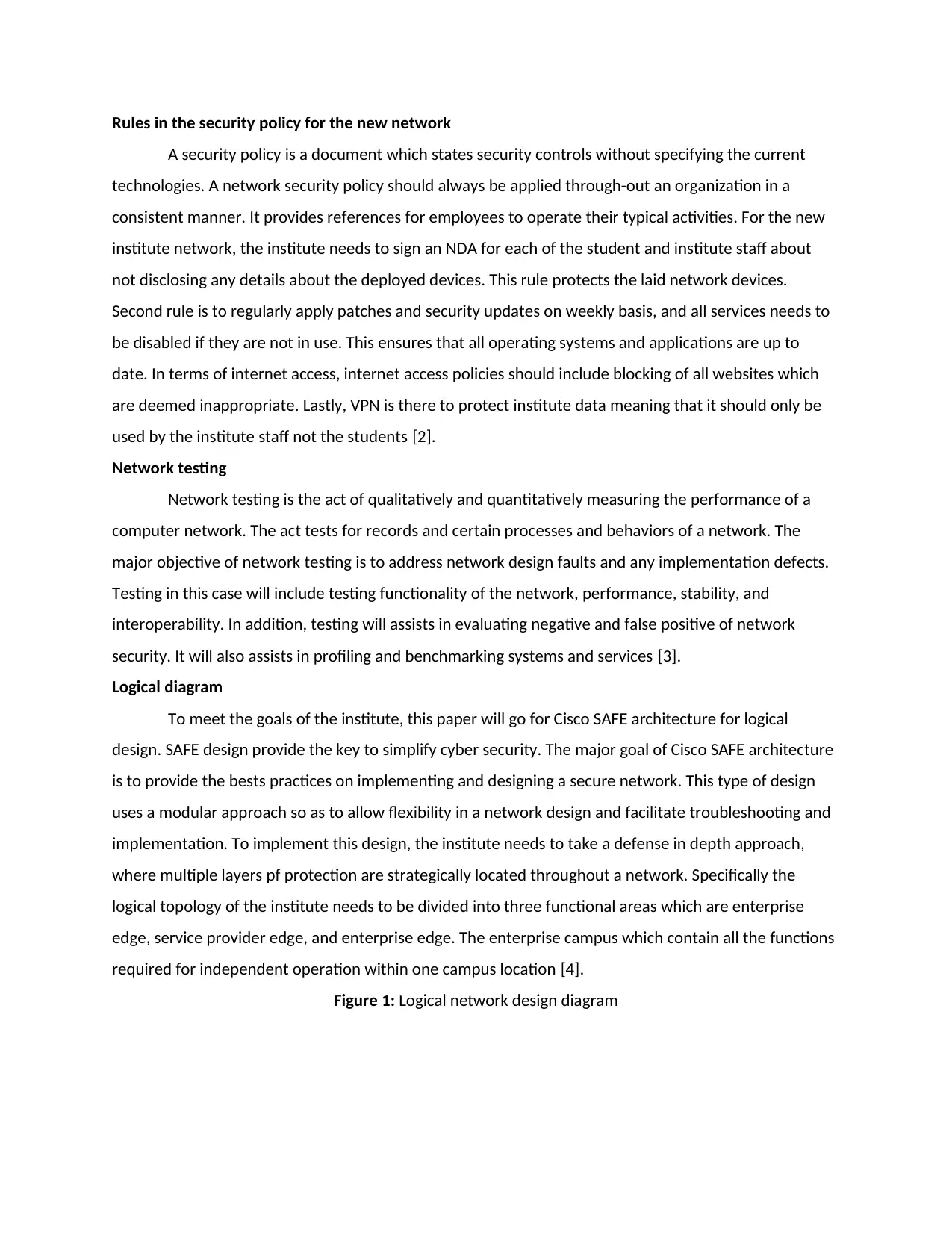
Logical diagram
To meet the goals of the institute, this paper will go for Cisco SAFE architecture for logical
design. SAFE design provide the key to simplify cyber security. The major goal of Cisco SAFE architecture
is to provide the bests practices on implementing and designing a secure network. This type of design
uses a modular approach so as to allow flexibility in a network design and facilitate troubleshooting and
implementation. To implement this design, the institute needs to take a defense in depth approach,
where multiple layers pf protection are strategically located throughout a network. Specifically the
logical topology of the institute needs to be divided into three functional areas which are enterprise
edge, service provider edge, and enterprise edge. The enterprise campus which contain all the functions
required for independent operation within one campus location [4].
Figure 1: Logical network design diagram
A security policy is a document which states security controls without specifying the current
technologies. A network security policy should always be applied through-out an organization in a
consistent manner. It provides references for employees to operate their typical activities. For the new
institute network, the institute needs to sign an NDA for each of the student and institute staff about
not disclosing any details about the deployed devices. This rule protects the laid network devices.
Second rule is to regularly apply patches and security updates on weekly basis, and all services needs to
be disabled if they are not in use. This ensures that all operating systems and applications are up to
date. In terms of internet access, internet access policies should include blocking of all websites which
are deemed inappropriate. Lastly, VPN is there to protect institute data meaning that it should only be
used by the institute staff not the students [2].
Network testing
Network testing is the act of qualitatively and quantitatively measuring the performance of a
computer network. The act tests for records and certain processes and behaviors of a network. The
major objective of network testing is to address network design faults and any implementation defects.
Testing in this case will include testing functionality of the network, performance, stability, and
interoperability. In addition, testing will assists in evaluating negative and false positive of network
security. It will also assists in profiling and benchmarking systems and services [3].
Logical diagram
To meet the goals of the institute, this paper will go for Cisco SAFE architecture for logical
design. SAFE design provide the key to simplify cyber security. The major goal of Cisco SAFE architecture
is to provide the bests practices on implementing and designing a secure network. This type of design
uses a modular approach so as to allow flexibility in a network design and facilitate troubleshooting and
implementation. To implement this design, the institute needs to take a defense in depth approach,
where multiple layers pf protection are strategically located throughout a network. Specifically the
logical topology of the institute needs to be divided into three functional areas which are enterprise
edge, service provider edge, and enterprise edge. The enterprise campus which contain all the functions
required for independent operation within one campus location [4].
Figure 1: Logical network design diagram
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Regression testing
Regression testing in networking is defines as a type of test which intended to confirm that a
recent network design or upgrade has not adversely affected the existing network features. This type of
testing is there to make sure that new changes in an organization network ought not to have side effects
on the existing network functionalities. One example of regression testing is required when there is a
change of requirements such as in this case study. In here a new feature has been added; example
Holmes has just purchased one Metro Ethernet connection and added two new schools. These new
features needs to be modified to include the existing network features. Here regression testing is
needed to fix any performance issue, and to fix defect
Method of improving security of the new network
There are various methods employed to improve security for a new network. The commonly
used method and the recommended in this case is the use of 802.1X for authentication. This method is
commonly used to protect wireless network but by deploying 802.1X authentication an organization is
able unnecessary access of the institute network by unauthorized personnel. In addition, this method
has that ability of dynamically assigning users to VLANs. Also the institute needs to implement VLANs to
segregate traffic. Here VLANs will be used to separate institute network by traffic type i.e. by general
access, DMZ, VoIP, and SAN. To use VLANs, the institute routers and switches must support it; here one
looks for the IEE 802.1Q support in the product specs.
Aspects of network management
Regression testing in networking is defines as a type of test which intended to confirm that a
recent network design or upgrade has not adversely affected the existing network features. This type of
testing is there to make sure that new changes in an organization network ought not to have side effects
on the existing network functionalities. One example of regression testing is required when there is a
change of requirements such as in this case study. In here a new feature has been added; example
Holmes has just purchased one Metro Ethernet connection and added two new schools. These new
features needs to be modified to include the existing network features. Here regression testing is
needed to fix any performance issue, and to fix defect
Method of improving security of the new network
There are various methods employed to improve security for a new network. The commonly
used method and the recommended in this case is the use of 802.1X for authentication. This method is
commonly used to protect wireless network but by deploying 802.1X authentication an organization is
able unnecessary access of the institute network by unauthorized personnel. In addition, this method
has that ability of dynamically assigning users to VLANs. Also the institute needs to implement VLANs to
segregate traffic. Here VLANs will be used to separate institute network by traffic type i.e. by general
access, DMZ, VoIP, and SAN. To use VLANs, the institute routers and switches must support it; here one
looks for the IEE 802.1Q support in the product specs.
Aspects of network management
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
The ISO network management has five functional areas which are fault management,
performance management, security management, and accounting management. Fault management is
used to detect, notify, and isolate faults which are encountered in a network. One aspect of network
management which the institute can use for fault management is Simple Network Management
protocol. The SNMP protocol will be used to directly share data with the CiscoWorks server.
Network topology design
When designing a network topology, a designer must focus on network security and
interoperability. Interoperability is the ability of network devices to effectively communicate thus
creating a homogenous environment. The best topology design in this case is hybrid topology; this
topology integrates two or more topologies together. This needs to be done in all the departments.
Even though the topology can be costly, this paper goes for this topology since is flexible, scalable one is
able to easily add or remove a component or a node, suitable for large networks such as this one, and
easily to manage as compared to other topologies
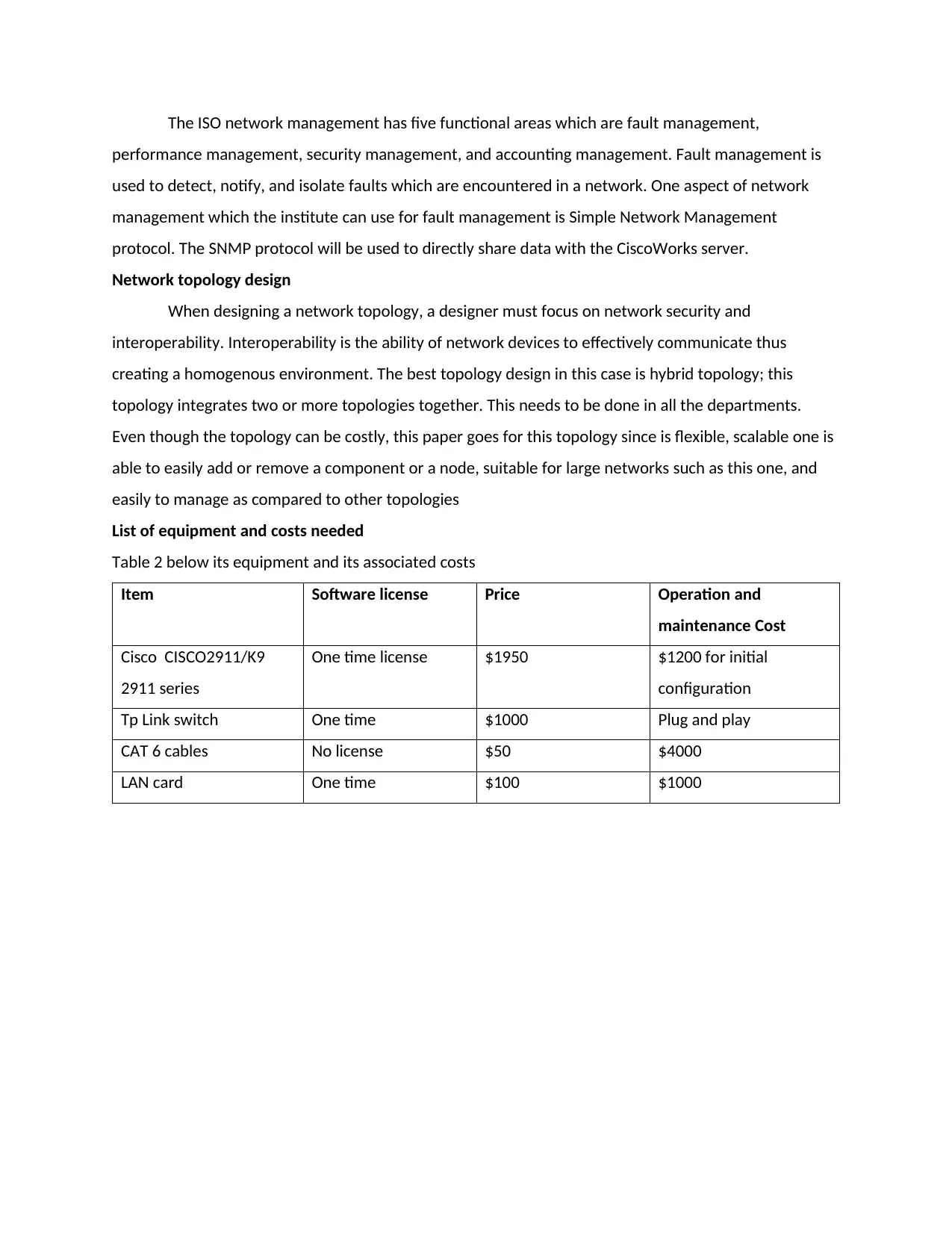
List of equipment and costs needed
Table 2 below its equipment and its associated costs
Item Software license Price Operation and
maintenance Cost
Cisco CISCO2911/K9
2911 series
One time license $1950 $1200 for initial
configuration
Tp Link switch One time $1000 Plug and play
CAT 6 cables No license $50 $4000
LAN card One time $100 $1000
performance management, security management, and accounting management. Fault management is
used to detect, notify, and isolate faults which are encountered in a network. One aspect of network
management which the institute can use for fault management is Simple Network Management
protocol. The SNMP protocol will be used to directly share data with the CiscoWorks server.
Network topology design
When designing a network topology, a designer must focus on network security and
interoperability. Interoperability is the ability of network devices to effectively communicate thus
creating a homogenous environment. The best topology design in this case is hybrid topology; this
topology integrates two or more topologies together. This needs to be done in all the departments.
Even though the topology can be costly, this paper goes for this topology since is flexible, scalable one is
able to easily add or remove a component or a node, suitable for large networks such as this one, and
easily to manage as compared to other topologies
List of equipment and costs needed
Table 2 below its equipment and its associated costs
Item Software license Price Operation and
maintenance Cost
Cisco CISCO2911/K9
2911 series
One time license $1950 $1200 for initial
configuration
Tp Link switch One time $1000 Plug and play
CAT 6 cables No license $50 $4000
LAN card One time $100 $1000
References
[1] M. Berry, "Network Security: Top 5 Fundamentals," IT Manager Daily, n.d. [Online]. Available:
http://www.itmanagerdaily.com/network-security-fundamentals/. [Accessed 29th September 2019].
[2] InfoSec, "Network Security Policy," Infosec, n.d. [Online]. Available:
https://resources.infosecinstitute.com/network-security-policy-part-3/#gref. [Accessed 29th
September 2019].
[3] P. Byrne, Computer networking, New York: Larsen and Keller Education Press, 2017.
[4] J. F. Kurose and K. W. Ross, Computer networking : a top-down approach, Chicago: John & Wiley
Press, 2018.
[5] I. Kotenko and V. A. Skormin, Computer network security : 5th International., New York: Springer
Press, 2017.
[1] M. Berry, "Network Security: Top 5 Fundamentals," IT Manager Daily, n.d. [Online]. Available:
http://www.itmanagerdaily.com/network-security-fundamentals/. [Accessed 29th September 2019].
[2] InfoSec, "Network Security Policy," Infosec, n.d. [Online]. Available:
https://resources.infosecinstitute.com/network-security-policy-part-3/#gref. [Accessed 29th
September 2019].
[3] P. Byrne, Computer networking, New York: Larsen and Keller Education Press, 2017.
[4] J. F. Kurose and K. W. Ross, Computer networking : a top-down approach, Chicago: John & Wiley
Press, 2018.
[5] I. Kotenko and V. A. Skormin, Computer network security : 5th International., New York: Springer
Press, 2017.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 6
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





