Professional Skills for ICT Security: Challenges and Solutions
VerifiedAdded on 2020/04/07
|18
|4087
|37
Report
AI Summary
This report provides a comprehensive analysis of ICT security, focusing on the challenges faced by organizations in the current digital landscape. It begins with an introduction to the XYZ organization, a small programming company, and highlights the growing importance of information security. The report delves into network security, defining its key aspects and exploring various security applications such as firewalls and antivirus software. It emphasizes the importance of preventive measures, including system updates, strong passwords, VPN security, and data backups. The report then identifies and discusses various risks and issues, including those related to USB devices, insufficient security policies, and cloud attacks. It concludes with recommendations for mitigating these challenges and ensuring robust information security. The report covers the ethical and social challenges and provides recommendations for improvement. The report also discusses the business description, objectives and methodologies, and report outline. The report also examines the various types of security applications and their benefits. Finally, it discusses the risks and issues related to network security.

Running head: PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION
TECHNOLOGY
Professional skills for Information and Communication Technology
Name of the Student
Name of the University
Author’s Note
TECHNOLOGY
Professional skills for Information and Communication Technology
Name of the Student
Name of the University
Author’s Note
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
1
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
Executive Summary
This report focuses on the security issues in the market for the advancement of the organization
in the market. Different advances and updates in the organization have been discussed in report.
This report focuses on the Information security over the internet. The purpose behind the report
is to recognize the risks in with the online data and information of the organization. This report
focuses on the methodology used for directing the cyber-attacks in the organization. This report
deals with the good and social challenges of the relationship in the market. There are various
ethical issues discussed in the report that relates to the challenges to the organization there are
recommendations provided in the report for mitigating these challenges.
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
Executive Summary
This report focuses on the security issues in the market for the advancement of the organization
in the market. Different advances and updates in the organization have been discussed in report.
This report focuses on the Information security over the internet. The purpose behind the report
is to recognize the risks in with the online data and information of the organization. This report
focuses on the methodology used for directing the cyber-attacks in the organization. This report
deals with the good and social challenges of the relationship in the market. There are various
ethical issues discussed in the report that relates to the challenges to the organization there are
recommendations provided in the report for mitigating these challenges.
2
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
Table of Contents
1.0Introduction.................................................................................................................................4
1.1 Business Description.............................................................................................................4
1.2 Objective and methodology...................................................................................................4
1.3 Report Outline.......................................................................................................................4
2.0 Network Security.......................................................................................................................5
2.1 Defining Network Security....................................................................................................5
2.2 Types of security application.................................................................................................5
2.2.1 Firewalls.............................................................................................................................6
3.0 Preventive Measures..................................................................................................................7
3.1 Updating system....................................................................................................................7
3.2 Strong passwords...................................................................................................................7
3.3 Securing VPN........................................................................................................................8
3.4 Backing up Data....................................................................................................................8
4.0. Risks and Issues......................................................................................................................10
4.1 USB and external devices....................................................................................................10
4.2 Insufficient policies.............................................................................................................10
4.3 Cloud Attacks......................................................................................................................11
5.0 Conclusion...............................................................................................................................12
6.0 Recommendations....................................................................................................................13
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
Table of Contents
1.0Introduction.................................................................................................................................4
1.1 Business Description.............................................................................................................4
1.2 Objective and methodology...................................................................................................4
1.3 Report Outline.......................................................................................................................4
2.0 Network Security.......................................................................................................................5
2.1 Defining Network Security....................................................................................................5
2.2 Types of security application.................................................................................................5
2.2.1 Firewalls.............................................................................................................................6
3.0 Preventive Measures..................................................................................................................7
3.1 Updating system....................................................................................................................7
3.2 Strong passwords...................................................................................................................7
3.3 Securing VPN........................................................................................................................8
3.4 Backing up Data....................................................................................................................8
4.0. Risks and Issues......................................................................................................................10
4.1 USB and external devices....................................................................................................10
4.2 Insufficient policies.............................................................................................................10
4.3 Cloud Attacks......................................................................................................................11
5.0 Conclusion...............................................................................................................................12
6.0 Recommendations....................................................................................................................13
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide

3
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
7.0 References................................................................................................................................15
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
7.0 References................................................................................................................................15
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
4
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
1.0Introduction
1.1 Business Description
The ICT has been developing in the business organization in the current years. The XYZ
organization is a small programming based organization built up five years prior in Melbourne. It
used to create and redo applications in the data and systems administration field. The
organization is looking for growing its business in various parts of the nation. It is accepted that
the organization has a decent client base in the market yet at the same time not utilizing the
distributed computing administrations in their business. It is expected that the organization be not
moved up to the most recent advancements accessible in the market. There are different internet
issues incorporating the digital assaults with the assistance of infections, malwares and ransom
ware. This have been a major issue for the organization to secure their information and data from
these assaults.
1.2 Objective and methodology
This report refers to the IT sector market for the advancement of the organization in the
market. Different types of advancements and updates in the industries have been talked about in
report. This report concentrates on the Information security over the internet. The reason for the
report is to recognize the dangers engaged with the online information and data of the
organization. This report concentrates on the techniques utilized for alleviating the digital issues
in the organization. This report manages the moral and social issues of the organization in the
market. There are moral issues in the official administration group taking part in the life cycle of
the business organization.
1.3 Report Outline
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
1.0Introduction
1.1 Business Description
The ICT has been developing in the business organization in the current years. The XYZ
organization is a small programming based organization built up five years prior in Melbourne. It
used to create and redo applications in the data and systems administration field. The
organization is looking for growing its business in various parts of the nation. It is accepted that
the organization has a decent client base in the market yet at the same time not utilizing the
distributed computing administrations in their business. It is expected that the organization be not
moved up to the most recent advancements accessible in the market. There are different internet
issues incorporating the digital assaults with the assistance of infections, malwares and ransom
ware. This have been a major issue for the organization to secure their information and data from
these assaults.
1.2 Objective and methodology
This report refers to the IT sector market for the advancement of the organization in the
market. Different types of advancements and updates in the industries have been talked about in
report. This report concentrates on the Information security over the internet. The reason for the
report is to recognize the dangers engaged with the online information and data of the
organization. This report concentrates on the techniques utilized for alleviating the digital issues
in the organization. This report manages the moral and social issues of the organization in the
market. There are moral issues in the official administration group taking part in the life cycle of
the business organization.
1.3 Report Outline
5
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
This report outlines the philosophy to be used for the advancement of the organization in
the market. This report portrays the procedures to be utilized to moderate the moral and social
issues of the organization in the market. This report give a few proposals that aide in settling the
difficulties confronted by the organization in the market. The report concentrates on the security
and their mechanical parts of the security to distinguish fitting answers for defeat the dangers
included.
2.0 Network Security
2.1 Defining Network Security
The policies and procedures implemented to protect network from unauthorized access,
modification, denial of access is termed as network security (Scott-Hayward, O'Callaghan &
Sezer, 2013). The security provided to the systems connected in the network from the malicious
behavior of the intruders has been an important topic in the market. It is the commitment of
system directors to grasp preventive measures to shield their system from potential security risks.
PC composes that are locked in with standard trades and correspondence inside the
organization, individuals, or business require security. The most broadly perceived and essential
strategy for guaranteeing a system resource is by designating it an exceptional name and a
relating mystery word (De Marco et al., 2017). The business organization have been working
over the internet to build their business in the market. Hence, the security of the information and
data over the internet is a vital part for the business association. The objectives and targets of the
business association must be satisfied with the assistance of security of data.
2.2 Types of security application
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
This report outlines the philosophy to be used for the advancement of the organization in
the market. This report portrays the procedures to be utilized to moderate the moral and social
issues of the organization in the market. This report give a few proposals that aide in settling the
difficulties confronted by the organization in the market. The report concentrates on the security
and their mechanical parts of the security to distinguish fitting answers for defeat the dangers
included.
2.0 Network Security
2.1 Defining Network Security
The policies and procedures implemented to protect network from unauthorized access,
modification, denial of access is termed as network security (Scott-Hayward, O'Callaghan &
Sezer, 2013). The security provided to the systems connected in the network from the malicious
behavior of the intruders has been an important topic in the market. It is the commitment of
system directors to grasp preventive measures to shield their system from potential security risks.
PC composes that are locked in with standard trades and correspondence inside the
organization, individuals, or business require security. The most broadly perceived and essential
strategy for guaranteeing a system resource is by designating it an exceptional name and a
relating mystery word (De Marco et al., 2017). The business organization have been working
over the internet to build their business in the market. Hence, the security of the information and
data over the internet is a vital part for the business association. The objectives and targets of the
business association must be satisfied with the assistance of security of data.
2.2 Types of security application
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
6
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
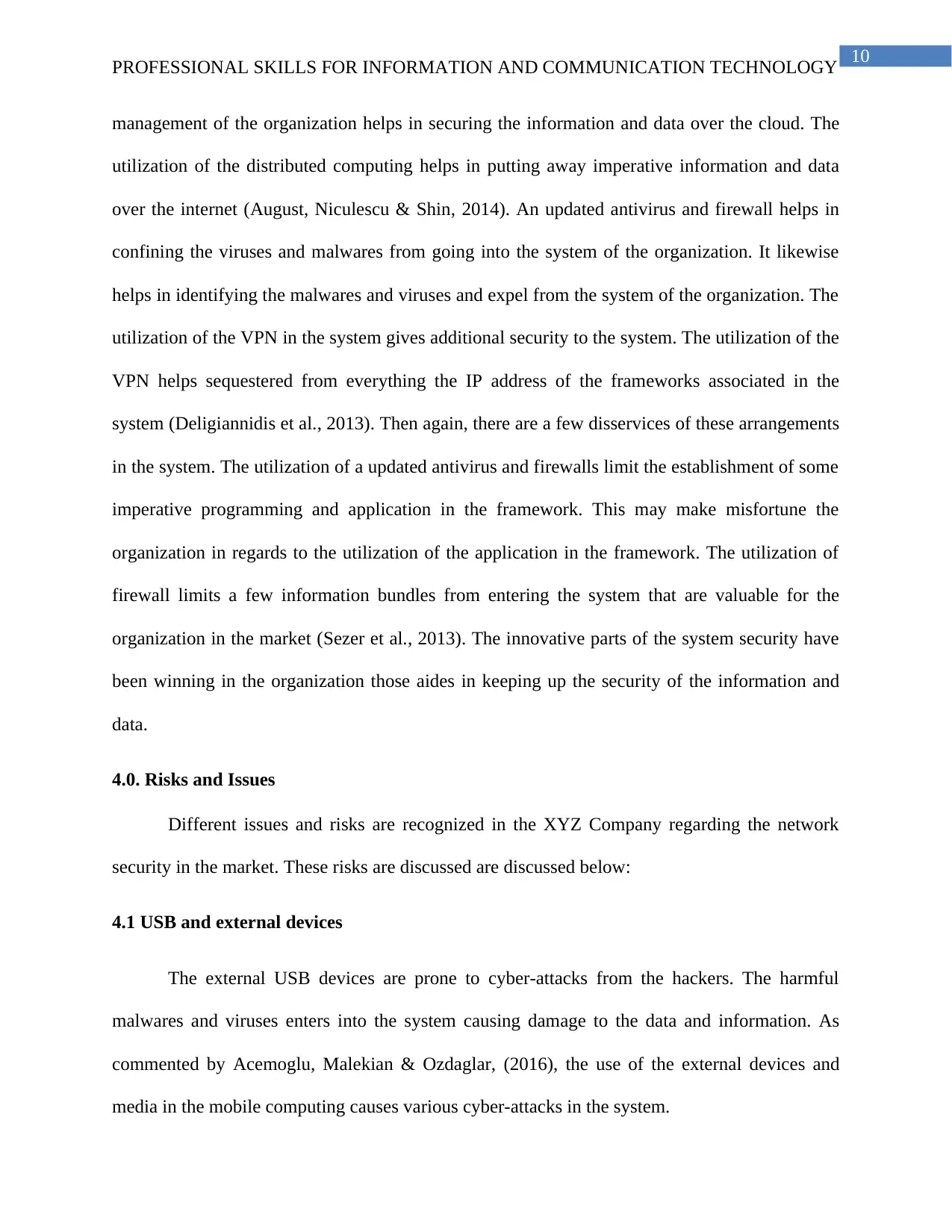
Different system security applications are at present utilized as a part of the market by the
business association including Antiviruses, Firewalls and Intrusion Detection Systems. The use
of the appropriated registering helps in securing basic data and information over the internet. The
use of an updated antivirus and firewalls keep the foundation of some basic programming and
application in the structure. These security applications help in controlling the digital assaults in
the business association. For instance, Norton Security is an antivirus programming that shield
information and data from the being broken (Fernandes et al., 2014). This application gives Anti-
Spam, Email Attachment Protection, Spyware Removal, Anti-Virus,and Internet Threat
Management to the clients (Modi et al., 2013). These highlights help in giving a secured domain
to the data over the internet. It helps in distinguishing destructive infections and malwares over
the internet.
Figure 1: Network Security
(Source: Modi et al., 2013, pp. 565)
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
Different system security applications are at present utilized as a part of the market by the
business association including Antiviruses, Firewalls and Intrusion Detection Systems. The use
of the appropriated registering helps in securing basic data and information over the internet. The
use of an updated antivirus and firewalls keep the foundation of some basic programming and
application in the structure. These security applications help in controlling the digital assaults in
the business association. For instance, Norton Security is an antivirus programming that shield
information and data from the being broken (Fernandes et al., 2014). This application gives Anti-
Spam, Email Attachment Protection, Spyware Removal, Anti-Virus,and Internet Threat
Management to the clients (Modi et al., 2013). These highlights help in giving a secured domain
to the data over the internet. It helps in distinguishing destructive infections and malwares over
the internet.
Figure 1: Network Security
(Source: Modi et al., 2013, pp. 565)
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
7
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
2.2.1 Firewalls
The firewalls helps in monitoring and blocking various unusual HTTP traffic in the
server of the XYZ Company. It also helps in clarifying the congestion in the network due to the
unusual data packets in the channel. The monitoring of application over the internet helps in
maintaining the security of the network in the server. The firewalls also helps in preventing the
cyber-attacks in the network by restricting harmful viruses and malwares from entering into the
network of the server. As commented by Komninos, Philippou & Pitsillides, (2014), intrusion
detection system helps in monitoring various malicious activities and help in stopping them. The
intrusion detection system acknowledges with alarm against malicious activities in the network
server.
3.0 Preventive Measures
Various factors are responsible for the implementation of the solution to the prevention of
data and information in the business organization. A properly updated antivirus and firewall
limits the entry of the viruses and malwares in the server of network.
3.1 Updating system
The applications and software utilized as a part of the PC and system requires being
updated. These aides in confining the unapproved activities in the PC and system (Jing et al.,
2014). The inventory of the applications and information must be updated for permitting
establishment of legitimate fixes and updates.
3.2 Strong passwords
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
2.2.1 Firewalls
The firewalls helps in monitoring and blocking various unusual HTTP traffic in the
server of the XYZ Company. It also helps in clarifying the congestion in the network due to the
unusual data packets in the channel. The monitoring of application over the internet helps in
maintaining the security of the network in the server. The firewalls also helps in preventing the
cyber-attacks in the network by restricting harmful viruses and malwares from entering into the
network of the server. As commented by Komninos, Philippou & Pitsillides, (2014), intrusion
detection system helps in monitoring various malicious activities and help in stopping them. The
intrusion detection system acknowledges with alarm against malicious activities in the network
server.
3.0 Preventive Measures
Various factors are responsible for the implementation of the solution to the prevention of
data and information in the business organization. A properly updated antivirus and firewall
limits the entry of the viruses and malwares in the server of network.
3.1 Updating system
The applications and software utilized as a part of the PC and system requires being
updated. These aides in confining the unapproved activities in the PC and system (Jing et al.,
2014). The inventory of the applications and information must be updated for permitting
establishment of legitimate fixes and updates.
3.2 Strong passwords
8
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
The important credentials and passwords of the XYZ Company have to be kept in safe
place that helps in securing it. The security level of the passwords have to be high by using the
combination of numbers, alphabets and symbols (Fang, Han & Li, 2014). This helps in
increasing the difficulty of the password to crack. Therefore, the security of the data and
information of the XYZ Company can be maintained.
3.3 Securing VPN
Personality verification and Information encryption are the important elements of the
VPN. An open system organization is a major weakness for the hackers can easily breach into
the system. The data and information of the company is open to all over the internet that causes
huge loss of the company in the market (Singhal et al., 2013). The use of the VPN helps in
maintaining the security of the IP address of the system and the network. Frameworks of the
VPN helps in hiding the IP address of the system for the intruder over the internet. This helps in
providing extra security to the data and information of the system.
The multi-factor validation of the accounts over the internet helps in securing the data
and information of the company. The more strides your customers must take to exhibit their
identity, the better. For example, despite a mystery word, customers could be required to enter a
PIN (Liang & Yu, 2015). Then again, an unpredictable numerical code created by a key
authenticator predictably could be used as a piece of conjunction with a PIN or mystery word.
The usage of the VPN in the framework gives extra security to the framework.
3.4 Backing up Data
The information and data are backed up for recuperation. The system back up and
debacle recuperation helps in keeping up the reinforcement information and data (Granjal,
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
The important credentials and passwords of the XYZ Company have to be kept in safe
place that helps in securing it. The security level of the passwords have to be high by using the
combination of numbers, alphabets and symbols (Fang, Han & Li, 2014). This helps in
increasing the difficulty of the password to crack. Therefore, the security of the data and
information of the XYZ Company can be maintained.
3.3 Securing VPN
Personality verification and Information encryption are the important elements of the
VPN. An open system organization is a major weakness for the hackers can easily breach into
the system. The data and information of the company is open to all over the internet that causes
huge loss of the company in the market (Singhal et al., 2013). The use of the VPN helps in
maintaining the security of the IP address of the system and the network. Frameworks of the
VPN helps in hiding the IP address of the system for the intruder over the internet. This helps in
providing extra security to the data and information of the system.
The multi-factor validation of the accounts over the internet helps in securing the data
and information of the company. The more strides your customers must take to exhibit their
identity, the better. For example, despite a mystery word, customers could be required to enter a
PIN (Liang & Yu, 2015). Then again, an unpredictable numerical code created by a key
authenticator predictably could be used as a piece of conjunction with a PIN or mystery word.
The usage of the VPN in the framework gives extra security to the framework.
3.4 Backing up Data
The information and data are backed up for recuperation. The system back up and
debacle recuperation helps in keeping up the reinforcement information and data (Granjal,
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
9
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
Monteiro & Silva, 2015). Due to information misfortune of any digital assault and information
rupture, the lost information can be recouped effortlessly.
For this situation, the XYZ Company is looking for development in the market. Along
these lines, the information and data with respect to business must be secured. The utilization of
these applications may help in dealing with the security and insurance of the information and
data in the association (Liang & Xiao, 2013). These elements help in building up the association
in the market. The correct administration of critical information and fundamental is vital for the
accomplishment of the organization in the market. The development of the organization depends
in the security of the information and data in the market. The security of the points of interest of
workers and clients is essential to be kept up by the organization for some time later (Chen et al.,
2016). This helps in upgrading the nature of the services gave to the clients. This software
organization is at present working in an off the-shelf application.
In the current situation, the company has been operating in limited regions of Australia.
Therefore, the company is looking for the expansion of the business. The implementation of the
off-shelf application might help in connecting different customers with the company in the
market (Sgora, Vergados & Chatzimisios, 2016). This also helps in enhancing the expansion of
the company in the market. The implementation of the online business of the XYZ Company
helps in attracting a huge number of customers in the market. Online business helps in rapid
expansion of the business in the market. It also helps in creating a huge customer base in the
market by gaining the trust of the customer by its services.
There are different favorable circumstances and hindrances of the solutions of the system
security. The utilization of the firewalls and antivirus helps in securing the information and data
of the organization (Faruki et al, 2015). The utilization of the distributed computing in the
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
Monteiro & Silva, 2015). Due to information misfortune of any digital assault and information
rupture, the lost information can be recouped effortlessly.
For this situation, the XYZ Company is looking for development in the market. Along
these lines, the information and data with respect to business must be secured. The utilization of
these applications may help in dealing with the security and insurance of the information and
data in the association (Liang & Xiao, 2013). These elements help in building up the association
in the market. The correct administration of critical information and fundamental is vital for the
accomplishment of the organization in the market. The development of the organization depends
in the security of the information and data in the market. The security of the points of interest of
workers and clients is essential to be kept up by the organization for some time later (Chen et al.,
2016). This helps in upgrading the nature of the services gave to the clients. This software
organization is at present working in an off the-shelf application.
In the current situation, the company has been operating in limited regions of Australia.
Therefore, the company is looking for the expansion of the business. The implementation of the
off-shelf application might help in connecting different customers with the company in the
market (Sgora, Vergados & Chatzimisios, 2016). This also helps in enhancing the expansion of
the company in the market. The implementation of the online business of the XYZ Company
helps in attracting a huge number of customers in the market. Online business helps in rapid
expansion of the business in the market. It also helps in creating a huge customer base in the
market by gaining the trust of the customer by its services.
There are different favorable circumstances and hindrances of the solutions of the system
security. The utilization of the firewalls and antivirus helps in securing the information and data
of the organization (Faruki et al, 2015). The utilization of the distributed computing in the
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
10
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
management of the organization helps in securing the information and data over the cloud. The
utilization of the distributed computing helps in putting away imperative information and data
over the internet (August, Niculescu & Shin, 2014). An updated antivirus and firewall helps in
confining the viruses and malwares from going into the system of the organization. It likewise
helps in identifying the malwares and viruses and expel from the system of the organization. The
utilization of the VPN in the system gives additional security to the system. The utilization of the
VPN helps sequestered from everything the IP address of the frameworks associated in the
system (Deligiannidis et al., 2013). Then again, there are a few disservices of these arrangements
in the system. The utilization of a updated antivirus and firewalls limit the establishment of some
imperative programming and application in the framework. This may make misfortune the
organization in regards to the utilization of the application in the framework. The utilization of
firewall limits a few information bundles from entering the system that are valuable for the
organization in the market (Sezer et al., 2013). The innovative parts of the system security have
been winning in the organization those aides in keeping up the security of the information and
data.
4.0. Risks and Issues
Different issues and risks are recognized in the XYZ Company regarding the network
security in the market. These risks are discussed are discussed below:
4.1 USB and external devices
The external USB devices are prone to cyber-attacks from the hackers. The harmful
malwares and viruses enters into the system causing damage to the data and information. As
commented by Acemoglu, Malekian & Ozdaglar, (2016), the use of the external devices and
media in the mobile computing causes various cyber-attacks in the system.
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
management of the organization helps in securing the information and data over the cloud. The
utilization of the distributed computing helps in putting away imperative information and data
over the internet (August, Niculescu & Shin, 2014). An updated antivirus and firewall helps in
confining the viruses and malwares from going into the system of the organization. It likewise
helps in identifying the malwares and viruses and expel from the system of the organization. The
utilization of the VPN in the system gives additional security to the system. The utilization of the
VPN helps sequestered from everything the IP address of the frameworks associated in the
system (Deligiannidis et al., 2013). Then again, there are a few disservices of these arrangements
in the system. The utilization of a updated antivirus and firewalls limit the establishment of some
imperative programming and application in the framework. This may make misfortune the
organization in regards to the utilization of the application in the framework. The utilization of
firewall limits a few information bundles from entering the system that are valuable for the
organization in the market (Sezer et al., 2013). The innovative parts of the system security have
been winning in the organization those aides in keeping up the security of the information and
data.
4.0. Risks and Issues
Different issues and risks are recognized in the XYZ Company regarding the network
security in the market. These risks are discussed are discussed below:
4.1 USB and external devices
The external USB devices are prone to cyber-attacks from the hackers. The harmful
malwares and viruses enters into the system causing damage to the data and information. As
commented by Acemoglu, Malekian & Ozdaglar, (2016), the use of the external devices and
media in the mobile computing causes various cyber-attacks in the system.
11
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
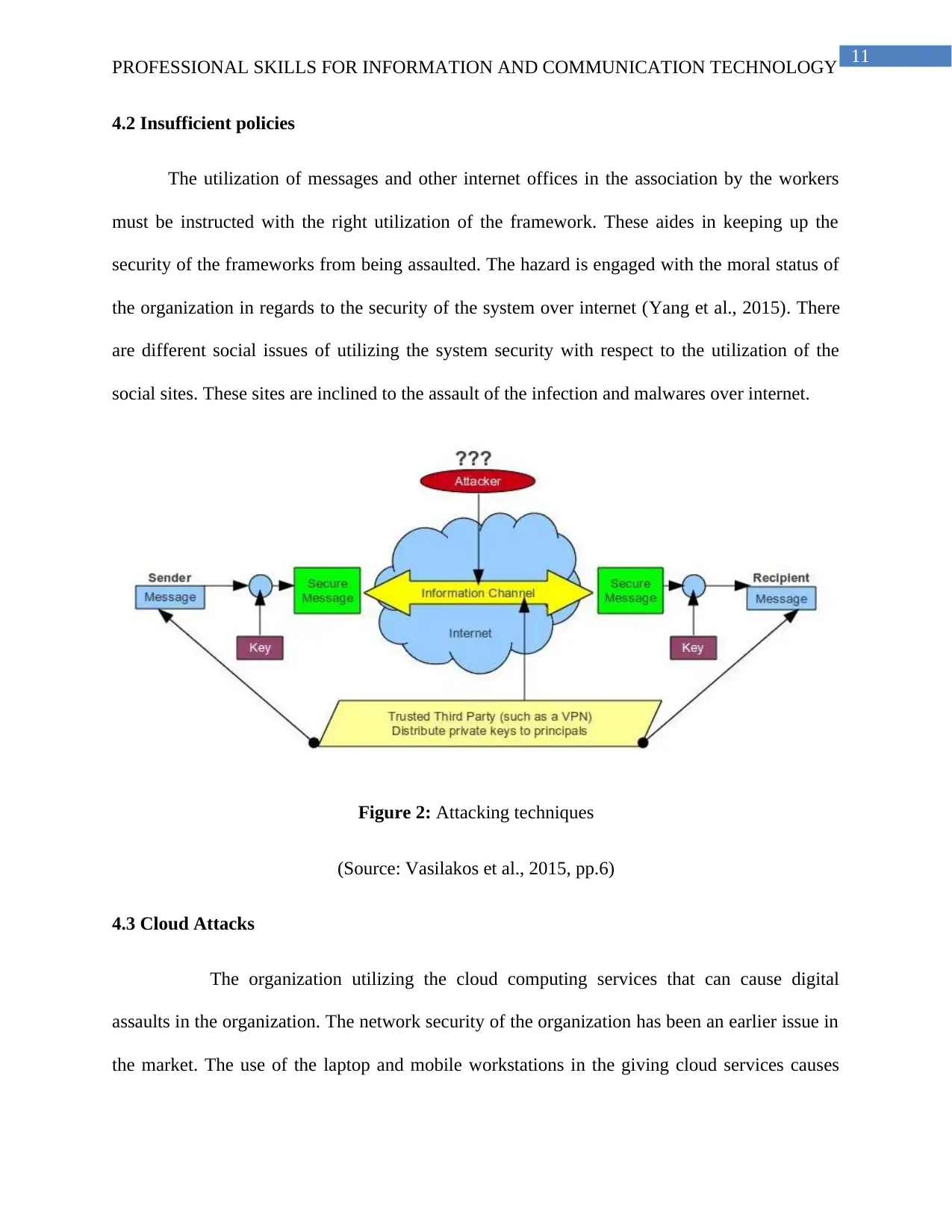
4.2 Insufficient policies
The utilization of messages and other internet offices in the association by the workers
must be instructed with the right utilization of the framework. These aides in keeping up the
security of the frameworks from being assaulted. The hazard is engaged with the moral status of
the organization in regards to the security of the system over internet (Yang et al., 2015). There
are different social issues of utilizing the system security with respect to the utilization of the
social sites. These sites are inclined to the assault of the infection and malwares over internet.
Figure 2: Attacking techniques
(Source: Vasilakos et al., 2015, pp.6)
4.3 Cloud Attacks
The organization utilizing the cloud computing services that can cause digital
assaults in the organization. The network security of the organization has been an earlier issue in
the market. The use of the laptop and mobile workstations in the giving cloud services causes
PROFESSIONAL SKILLS FOR INFORMATION AND COMMUNICATION TECHNOLOGY
4.2 Insufficient policies
The utilization of messages and other internet offices in the association by the workers
must be instructed with the right utilization of the framework. These aides in keeping up the
security of the frameworks from being assaulted. The hazard is engaged with the moral status of
the organization in regards to the security of the system over internet (Yang et al., 2015). There
are different social issues of utilizing the system security with respect to the utilization of the
social sites. These sites are inclined to the assault of the infection and malwares over internet.
Figure 2: Attacking techniques
(Source: Vasilakos et al., 2015, pp.6)
4.3 Cloud Attacks
The organization utilizing the cloud computing services that can cause digital
assaults in the organization. The network security of the organization has been an earlier issue in
the market. The use of the laptop and mobile workstations in the giving cloud services causes
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 18
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.




