Exploring IOT Technologies: Applications and Security Concerns
VerifiedAdded on 2020/02/24
|12
|2244
|42
Homework Assignment
AI Summary
This IOT assignment provides a comprehensive overview of various aspects related to the Internet of Things. It starts with the fundamental concept of a user interface-less system and its realization through IOT technology, using examples like Mercedes-Benz's keyless entry. The assignment explores different types of cables, including twisted pair, coaxial, and fiber optic cables, detailing their characteristics, bandwidths, and applications. It then delves into the advantages and disadvantages of RFID technology, comparing it to other tracking methods like video tracking, and sensor technologies. The assignment also discusses the potential of IOT in various sectors, such as transportation, energy, and healthcare, while addressing critical security and privacy issues, including hacking vulnerabilities, data protection, and consumer confidence concerns. Furthermore, the assignment includes calculations related to application trigger requests, round-trip propagation delays, and sensor consumption. Finally, it touches upon Nielsen's Law of Internet Bandwidth and its implications for IOT, along with the impact of IOT on intelligent cities and business networks. The document provides references to relevant sources.
IOT
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Table of Contents
Q1 ans:........................................................................................................................................................3
Q2) ans:-......................................................................................................................................................3
Q3) ans:-......................................................................................................................................................7
Q4)ans:-.......................................................................................................................................................8
Q5)ans:-.....................................................................................................................................................10
Q6)ans:-.....................................................................................................................................................10
References.................................................................................................................................................12
Q1 ans:........................................................................................................................................................3
Q2) ans:-......................................................................................................................................................3
Q3) ans:-......................................................................................................................................................7
Q4)ans:-.......................................................................................................................................................8
Q5)ans:-.....................................................................................................................................................10
Q6)ans:-.....................................................................................................................................................10
References.................................................................................................................................................12
Q1 ans: - “The best interface for a system is no users interface” is mainly referred as the
process in which data or information is input directly from the source computer to the destination
systems without users interface or communication. In computer system users mainly serves two
objectives (excluding entertainment application) and they are - 1) inserting the input data into
computer, and 2) offering information for human decisions (Shneiderman, 2010). No interface is
the best interface concept in computer world is achieved with the help of IOT (internet of things
technology). In this concept, client may only get involved when they are needed.
KEYLESS-GO (LOCK/UNLOCK) - Mercedes-Benz USA uses this concept and with this
concept the organisation (automaker) has eliminated the user interface. A few organizations
such as Google also implement this concept in their Smartphone applications that permits
customers to pay merchants with use of NFC.
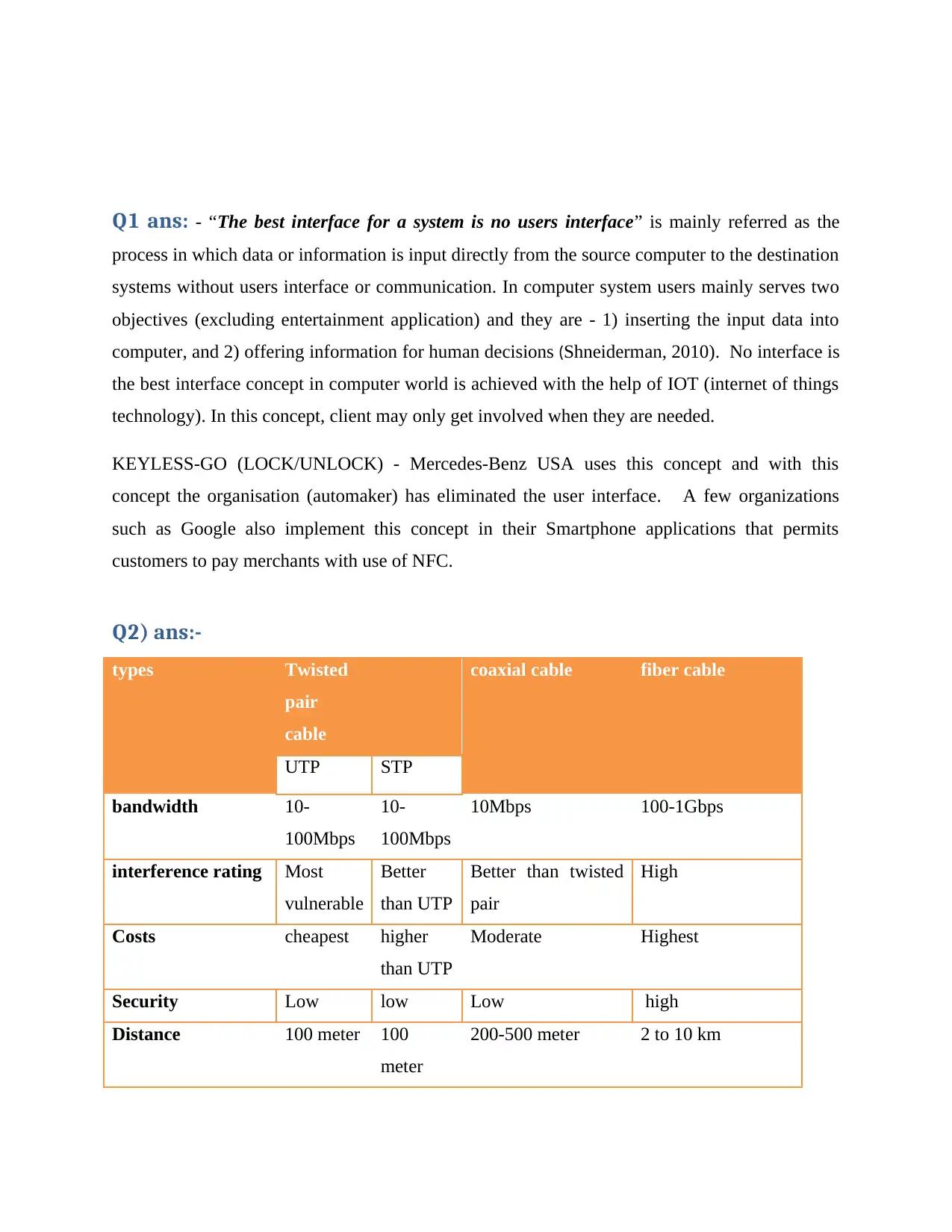
Q2) ans:-
types Twisted
pair
cable
coaxial cable fiber cable
UTP STP
bandwidth 10-
100Mbps
10-
100Mbps
10Mbps 100-1Gbps
interference rating Most
vulnerable
Better
than UTP
Better than twisted
pair
High
Costs cheapest higher
than UTP
Moderate Highest
Security Low low Low high
Distance 100 meter 100
meter
200-500 meter 2 to 10 km
process in which data or information is input directly from the source computer to the destination
systems without users interface or communication. In computer system users mainly serves two
objectives (excluding entertainment application) and they are - 1) inserting the input data into
computer, and 2) offering information for human decisions (Shneiderman, 2010). No interface is
the best interface concept in computer world is achieved with the help of IOT (internet of things
technology). In this concept, client may only get involved when they are needed.
KEYLESS-GO (LOCK/UNLOCK) - Mercedes-Benz USA uses this concept and with this
concept the organisation (automaker) has eliminated the user interface. A few organizations
such as Google also implement this concept in their Smartphone applications that permits
customers to pay merchants with use of NFC.
Q2) ans:-
types Twisted
pair
cable
coaxial cable fiber cable
UTP STP
bandwidth 10-
100Mbps
10-
100Mbps
10Mbps 100-1Gbps
interference rating Most
vulnerable
Better
than UTP
Better than twisted
pair
High
Costs cheapest higher
than UTP
Moderate Highest
Security Low low Low high
Distance 100 meter 100
meter
200-500 meter 2 to 10 km
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
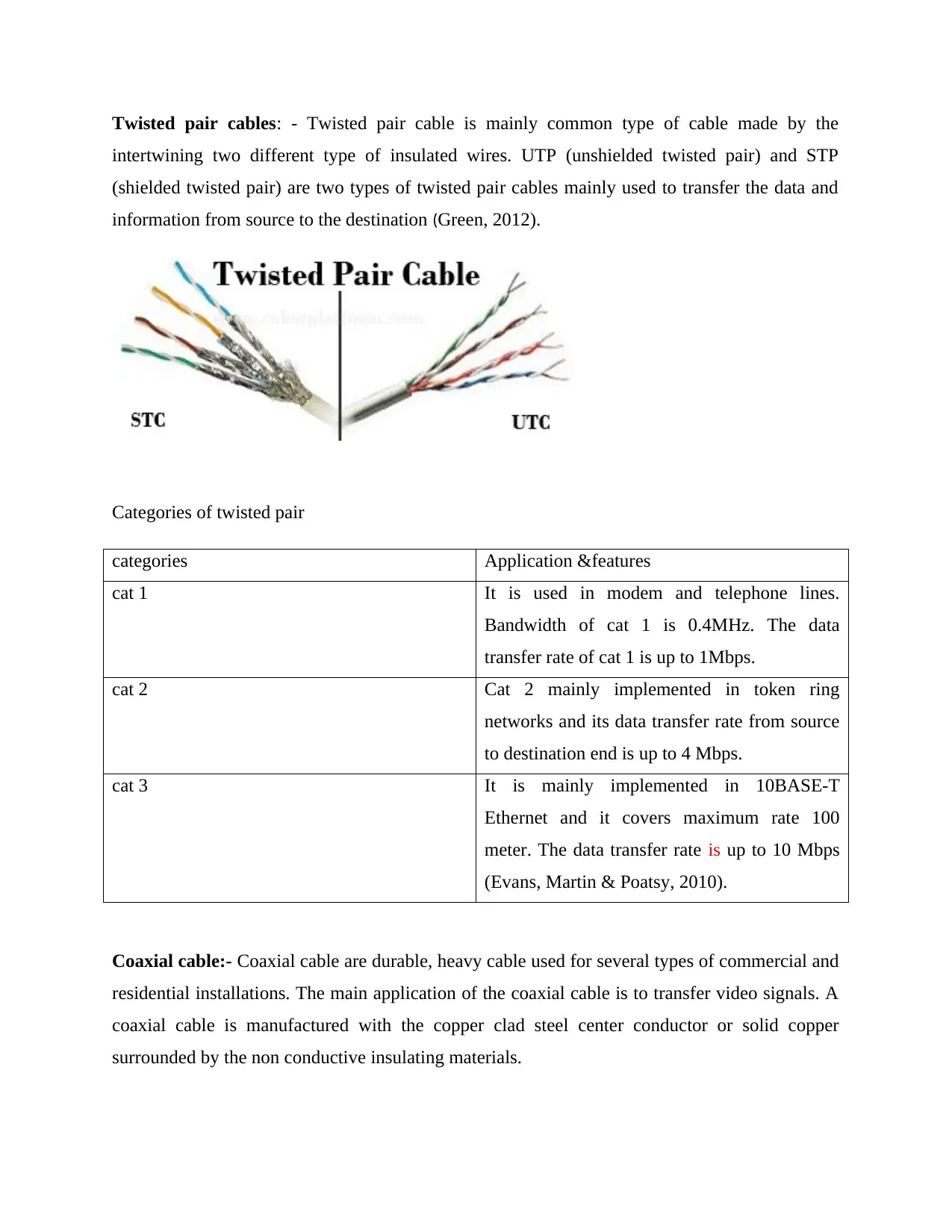
Twisted pair cables: - Twisted pair cable is mainly common type of cable made by the
intertwining two different type of insulated wires. UTP (unshielded twisted pair) and STP
(shielded twisted pair) are two types of twisted pair cables mainly used to transfer the data and
information from source to the destination (Green, 2012).
Categories of twisted pair
categories Application &features
cat 1 It is used in modem and telephone lines.
Bandwidth of cat 1 is 0.4MHz. The data
transfer rate of cat 1 is up to 1Mbps.
cat 2 Cat 2 mainly implemented in token ring
networks and its data transfer rate from source
to destination end is up to 4 Mbps.
cat 3 It is mainly implemented in 10BASE-T
Ethernet and it covers maximum rate 100
meter. The data transfer rate is up to 10 Mbps
(Evans, Martin & Poatsy, 2010).
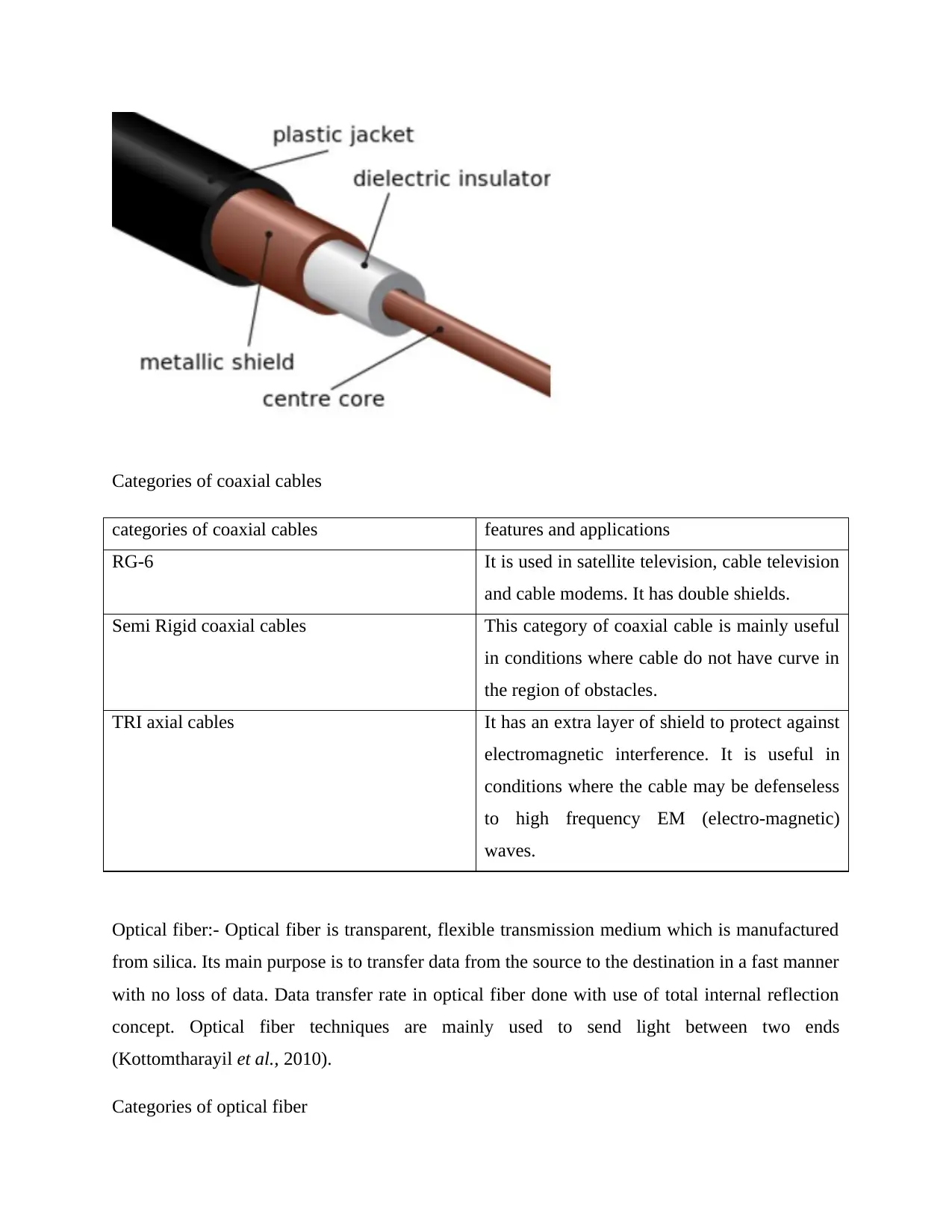
Coaxial cable:- Coaxial cable are durable, heavy cable used for several types of commercial and
residential installations. The main application of the coaxial cable is to transfer video signals. A
coaxial cable is manufactured with the copper clad steel center conductor or solid copper
surrounded by the non conductive insulating materials.
intertwining two different type of insulated wires. UTP (unshielded twisted pair) and STP
(shielded twisted pair) are two types of twisted pair cables mainly used to transfer the data and
information from source to the destination (Green, 2012).
Categories of twisted pair
categories Application &features
cat 1 It is used in modem and telephone lines.
Bandwidth of cat 1 is 0.4MHz. The data
transfer rate of cat 1 is up to 1Mbps.
cat 2 Cat 2 mainly implemented in token ring
networks and its data transfer rate from source
to destination end is up to 4 Mbps.
cat 3 It is mainly implemented in 10BASE-T
Ethernet and it covers maximum rate 100
meter. The data transfer rate is up to 10 Mbps
(Evans, Martin & Poatsy, 2010).
Coaxial cable:- Coaxial cable are durable, heavy cable used for several types of commercial and
residential installations. The main application of the coaxial cable is to transfer video signals. A
coaxial cable is manufactured with the copper clad steel center conductor or solid copper
surrounded by the non conductive insulating materials.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Categories of coaxial cables
categories of coaxial cables features and applications
RG-6 It is used in satellite television, cable television
and cable modems. It has double shields.
Semi Rigid coaxial cables This category of coaxial cable is mainly useful
in conditions where cable do not have curve in
the region of obstacles.
TRI axial cables It has an extra layer of shield to protect against
electromagnetic interference. It is useful in
conditions where the cable may be defenseless
to high frequency EM (electro-magnetic)
waves.
Optical fiber:- Optical fiber is transparent, flexible transmission medium which is manufactured
from silica. Its main purpose is to transfer data from the source to the destination in a fast manner
with no loss of data. Data transfer rate in optical fiber done with use of total internal reflection
concept. Optical fiber techniques are mainly used to send light between two ends
(Kottomtharayil et al., 2010).
Categories of optical fiber
categories of coaxial cables features and applications
RG-6 It is used in satellite television, cable television
and cable modems. It has double shields.
Semi Rigid coaxial cables This category of coaxial cable is mainly useful
in conditions where cable do not have curve in
the region of obstacles.
TRI axial cables It has an extra layer of shield to protect against
electromagnetic interference. It is useful in
conditions where the cable may be defenseless
to high frequency EM (electro-magnetic)
waves.
Optical fiber:- Optical fiber is transparent, flexible transmission medium which is manufactured
from silica. Its main purpose is to transfer data from the source to the destination in a fast manner
with no loss of data. Data transfer rate in optical fiber done with use of total internal reflection
concept. Optical fiber techniques are mainly used to send light between two ends
(Kottomtharayil et al., 2010).
Categories of optical fiber
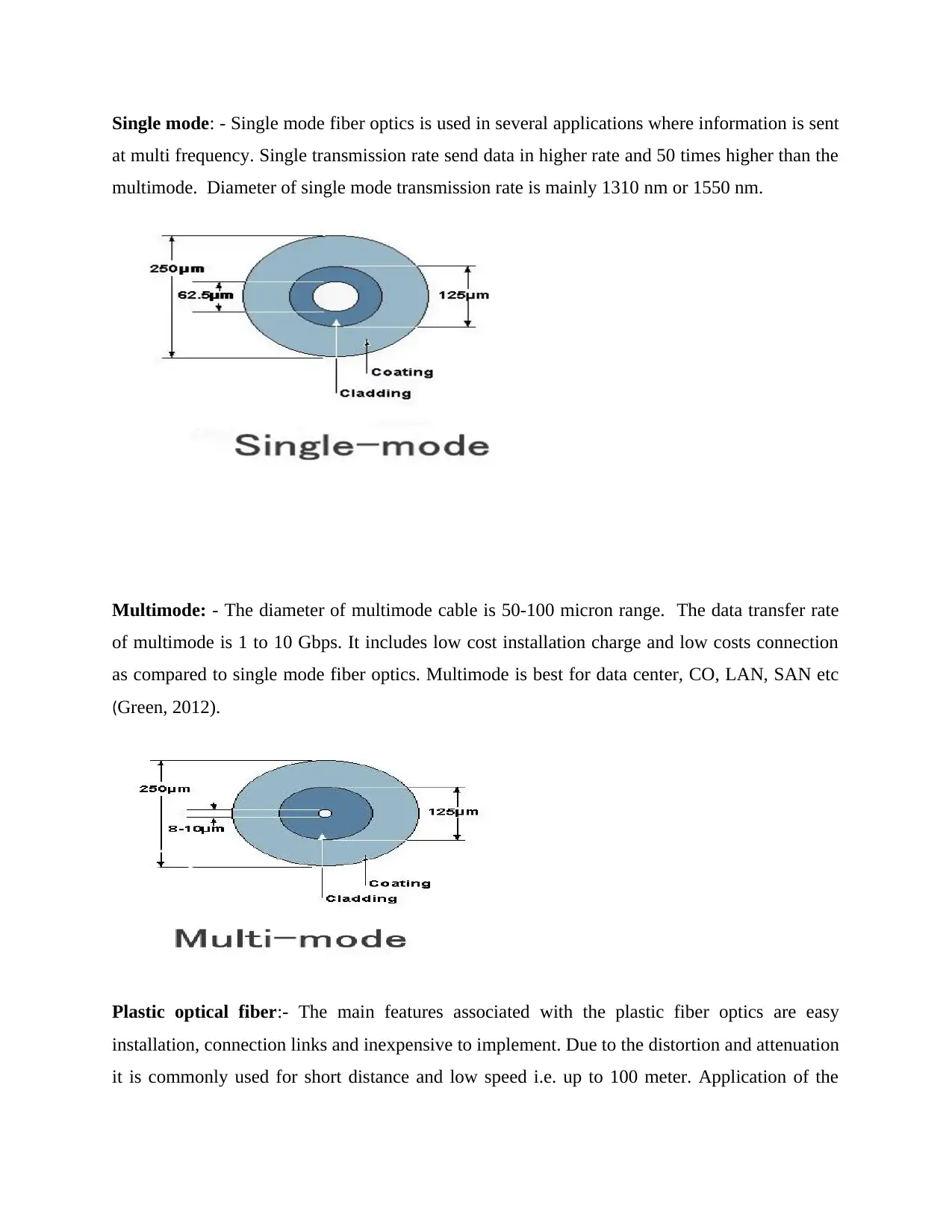
Single mode: - Single mode fiber optics is used in several applications where information is sent
at multi frequency. Single transmission rate send data in higher rate and 50 times higher than the
multimode. Diameter of single mode transmission rate is mainly 1310 nm or 1550 nm.
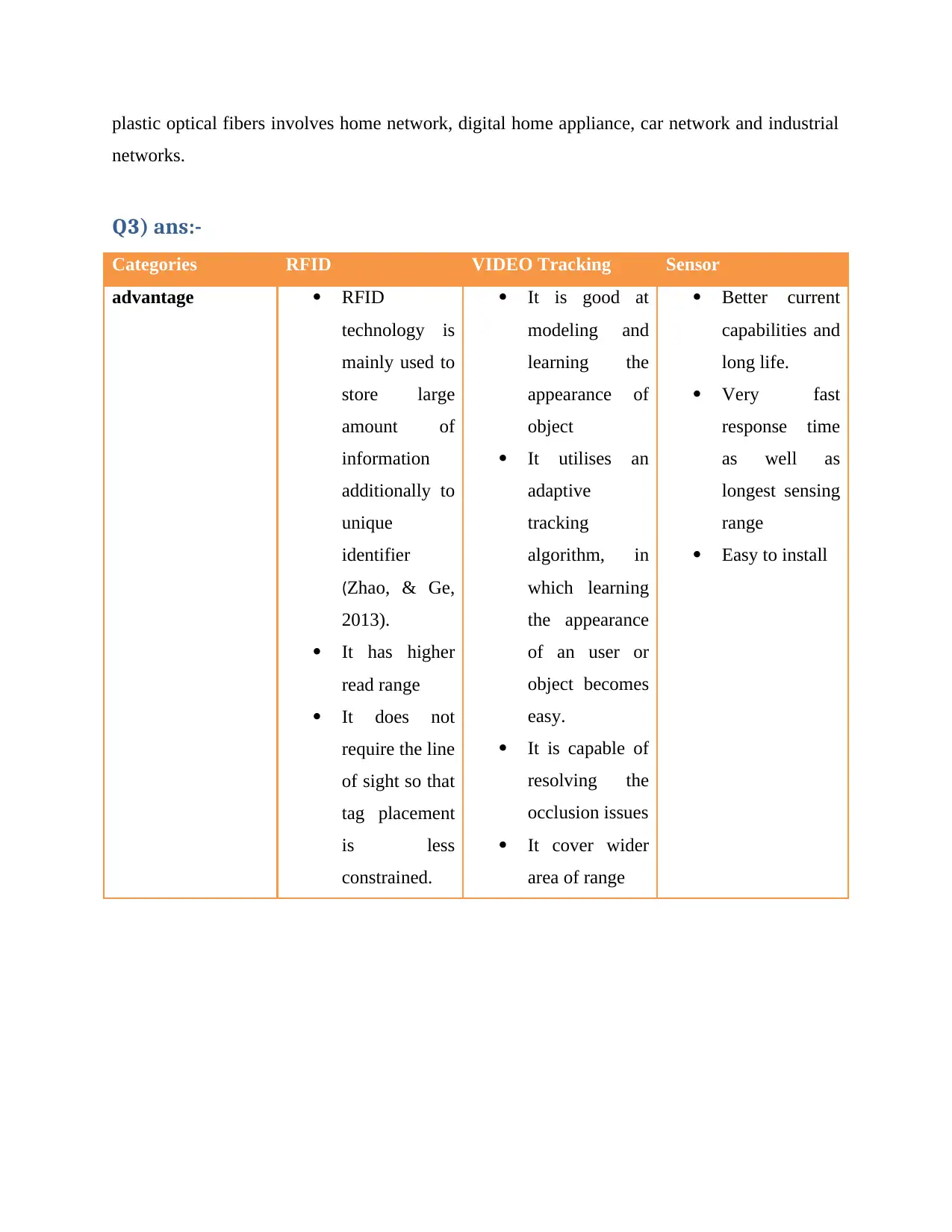
Multimode: - The diameter of multimode cable is 50-100 micron range. The data transfer rate
of multimode is 1 to 10 Gbps. It includes low cost installation charge and low costs connection
as compared to single mode fiber optics. Multimode is best for data center, CO, LAN, SAN etc
(Green, 2012).
Plastic optical fiber:- The main features associated with the plastic fiber optics are easy
installation, connection links and inexpensive to implement. Due to the distortion and attenuation
it is commonly used for short distance and low speed i.e. up to 100 meter. Application of the
at multi frequency. Single transmission rate send data in higher rate and 50 times higher than the
multimode. Diameter of single mode transmission rate is mainly 1310 nm or 1550 nm.
Multimode: - The diameter of multimode cable is 50-100 micron range. The data transfer rate
of multimode is 1 to 10 Gbps. It includes low cost installation charge and low costs connection
as compared to single mode fiber optics. Multimode is best for data center, CO, LAN, SAN etc
(Green, 2012).
Plastic optical fiber:- The main features associated with the plastic fiber optics are easy
installation, connection links and inexpensive to implement. Due to the distortion and attenuation
it is commonly used for short distance and low speed i.e. up to 100 meter. Application of the
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
plastic optical fibers involves home network, digital home appliance, car network and industrial
networks.
Q3) ans:-
Categories RFID VIDEO Tracking Sensor
advantage RFID
technology is
mainly used to
store large
amount of
information
additionally to
unique
identifier
(Zhao, & Ge,
2013).
It has higher
read range
It does not
require the line
of sight so that
tag placement
is less
constrained.
It is good at
modeling and
learning the
appearance of
object
It utilises an
adaptive
tracking
algorithm, in
which learning
the appearance
of an user or
object becomes
easy.
It is capable of
resolving the
occlusion issues
It cover wider
area of range
Better current
capabilities and
long life.
Very fast
response time
as well as
longest sensing
range
Easy to install
networks.
Q3) ans:-
Categories RFID VIDEO Tracking Sensor
advantage RFID
technology is
mainly used to
store large
amount of
information
additionally to
unique
identifier
(Zhao, & Ge,
2013).
It has higher
read range
It does not
require the line
of sight so that
tag placement
is less
constrained.
It is good at
modeling and
learning the
appearance of
object
It utilises an
adaptive
tracking
algorithm, in
which learning
the appearance
of an user or
object becomes
easy.
It is capable of
resolving the
occlusion issues
It cover wider
area of range
Better current
capabilities and
long life.
Very fast
response time
as well as
longest sensing
range
Easy to install
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
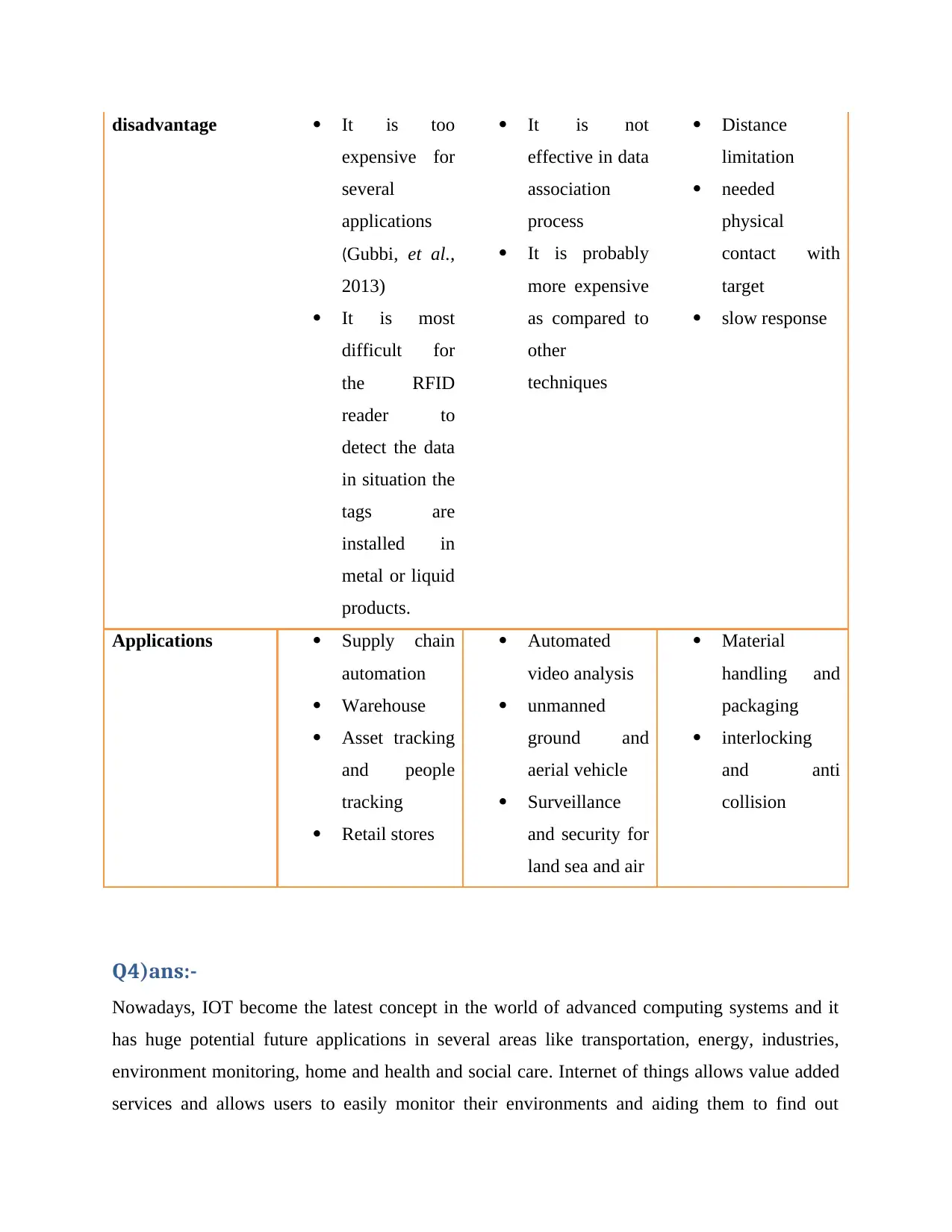
disadvantage It is too
expensive for
several
applications
(Gubbi, et al.,
2013)
It is most
difficult for
the RFID
reader to
detect the data
in situation the
tags are
installed in
metal or liquid
products.
It is not
effective in data
association
process
It is probably
more expensive
as compared to
other
techniques
Distance
limitation
needed
physical
contact with
target
slow response
Applications Supply chain
automation
Warehouse
Asset tracking
and people
tracking
Retail stores
Automated
video analysis
unmanned
ground and
aerial vehicle
Surveillance
and security for
land sea and air
Material
handling and
packaging
interlocking
and anti
collision
Q4)ans:-
Nowadays, IOT become the latest concept in the world of advanced computing systems and it
has huge potential future applications in several areas like transportation, energy, industries,
environment monitoring, home and health and social care. Internet of things allows value added
services and allows users to easily monitor their environments and aiding them to find out
expensive for
several
applications
(Gubbi, et al.,
2013)
It is most
difficult for
the RFID
reader to
detect the data
in situation the
tags are
installed in
metal or liquid
products.
It is not
effective in data
association
process
It is probably
more expensive
as compared to
other
techniques
Distance
limitation
needed
physical
contact with
target
slow response
Applications Supply chain
automation
Warehouse
Asset tracking
and people
tracking
Retail stores
Automated
video analysis
unmanned
ground and
aerial vehicle
Surveillance
and security for
land sea and air
Material
handling and
packaging
interlocking
and anti
collision
Q4)ans:-
Nowadays, IOT become the latest concept in the world of advanced computing systems and it
has huge potential future applications in several areas like transportation, energy, industries,
environment monitoring, home and health and social care. Internet of things allows value added
services and allows users to easily monitor their environments and aiding them to find out
effective solutions to the everyday problems which are being faced in the present times.
According to the (Kelly, Suryadevara, & Mukhopadhyay, 2013), the internet of things is an
emerging international internet based technology and architecture which facilitates the exchange
of services and goods in worldwide network thereby having an effective impact on primary and
security. The security and privacy issues of IOT are illustrated below;
Security issues
Vulnerability of hacking:-The main security issues of IOT are that it raises the number of the
divides behind the computer network system. Therefore to functions in an optimum manner IOT
requires that data and information (Kottomtharayil et al., 2010). With the available of huge
amount of data and information, hackers can easily access information of the organizations.
Data protection: - Data protection is the main issue associated with the IOT technology. In
order to protect the data and information SSL is implemented in the website, but it protects only
half part of the data i.e. while data is transferred through wireless technology then they require
the extra protection. This can be solved in an organization by incorporating better or complex
encryption technique on data.
Data authentication and access problems: - Data authentication procedures help the
organizations to secure their information and data from unauthorised users. Sometime it is seen
that due to lack of the security issues, hackers easily authenticate with the organisation’s data and
access them. As organisation perspective data is more vital and helps them to sustain in the
market in a long time. Thus in such manner access issues and data authentication issues are also
considered to be the vital security issues of IOT.
Privacy issues
Huge amount of data: - IOT technology works with the data and execute its operations with the
help of the past information and data (QIAN & WANG, 2012). Therefore huge amount of data is
considered one of the vital privacy issues. As per the report published by the federal trade
commission, less than 10000 households generate above than 150 million discrete data each day.
According to the (Kelly, Suryadevara, & Mukhopadhyay, 2013), the internet of things is an
emerging international internet based technology and architecture which facilitates the exchange
of services and goods in worldwide network thereby having an effective impact on primary and
security. The security and privacy issues of IOT are illustrated below;
Security issues
Vulnerability of hacking:-The main security issues of IOT are that it raises the number of the
divides behind the computer network system. Therefore to functions in an optimum manner IOT
requires that data and information (Kottomtharayil et al., 2010). With the available of huge
amount of data and information, hackers can easily access information of the organizations.
Data protection: - Data protection is the main issue associated with the IOT technology. In
order to protect the data and information SSL is implemented in the website, but it protects only
half part of the data i.e. while data is transferred through wireless technology then they require
the extra protection. This can be solved in an organization by incorporating better or complex
encryption technique on data.
Data authentication and access problems: - Data authentication procedures help the
organizations to secure their information and data from unauthorised users. Sometime it is seen
that due to lack of the security issues, hackers easily authenticate with the organisation’s data and
access them. As organisation perspective data is more vital and helps them to sustain in the
market in a long time. Thus in such manner access issues and data authentication issues are also
considered to be the vital security issues of IOT.
Privacy issues
Huge amount of data: - IOT technology works with the data and execute its operations with the
help of the past information and data (QIAN & WANG, 2012). Therefore huge amount of data is
considered one of the vital privacy issues. As per the report published by the federal trade
commission, less than 10000 households generate above than 150 million discrete data each day.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide

Consumer confidence: - Now a day’s most of the consumers purchase its goods and services
through internet that would prevent the internet of things from fulfilling its true potential.
Therefore those hackers can easily access the user’s personal information and data from internet.
Accessing data without customer’s information: - Organisations make use of customer’s
information including credit and insurance information for the purpose of generating higher
profits. But this may be problematic, if the organization uses data without customer’s consent
and without ensuring the accuracy of information.
Q5)ans:-
According to the questions
Application trigger request= 1s
Round trip propagation delays:- 12 ms
Average sensor consume=3ms
Application consumes=2ms
Time budget can be saved=12+2+3+1=18ms
Q6)ans:-
Nielsen’s law: - According to the Nielsen’s law of internet bandwidth, bandwidth connectively
has increased by 50% per years from 1983 to 2016 (Nielsen, 2014).
through internet that would prevent the internet of things from fulfilling its true potential.
Therefore those hackers can easily access the user’s personal information and data from internet.
Accessing data without customer’s information: - Organisations make use of customer’s
information including credit and insurance information for the purpose of generating higher
profits. But this may be problematic, if the organization uses data without customer’s consent
and without ensuring the accuracy of information.
Q5)ans:-
According to the questions
Application trigger request= 1s
Round trip propagation delays:- 12 ms
Average sensor consume=3ms
Application consumes=2ms
Time budget can be saved=12+2+3+1=18ms
Q6)ans:-
Nielsen’s law: - According to the Nielsen’s law of internet bandwidth, bandwidth connectively
has increased by 50% per years from 1983 to 2016 (Nielsen, 2014).
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
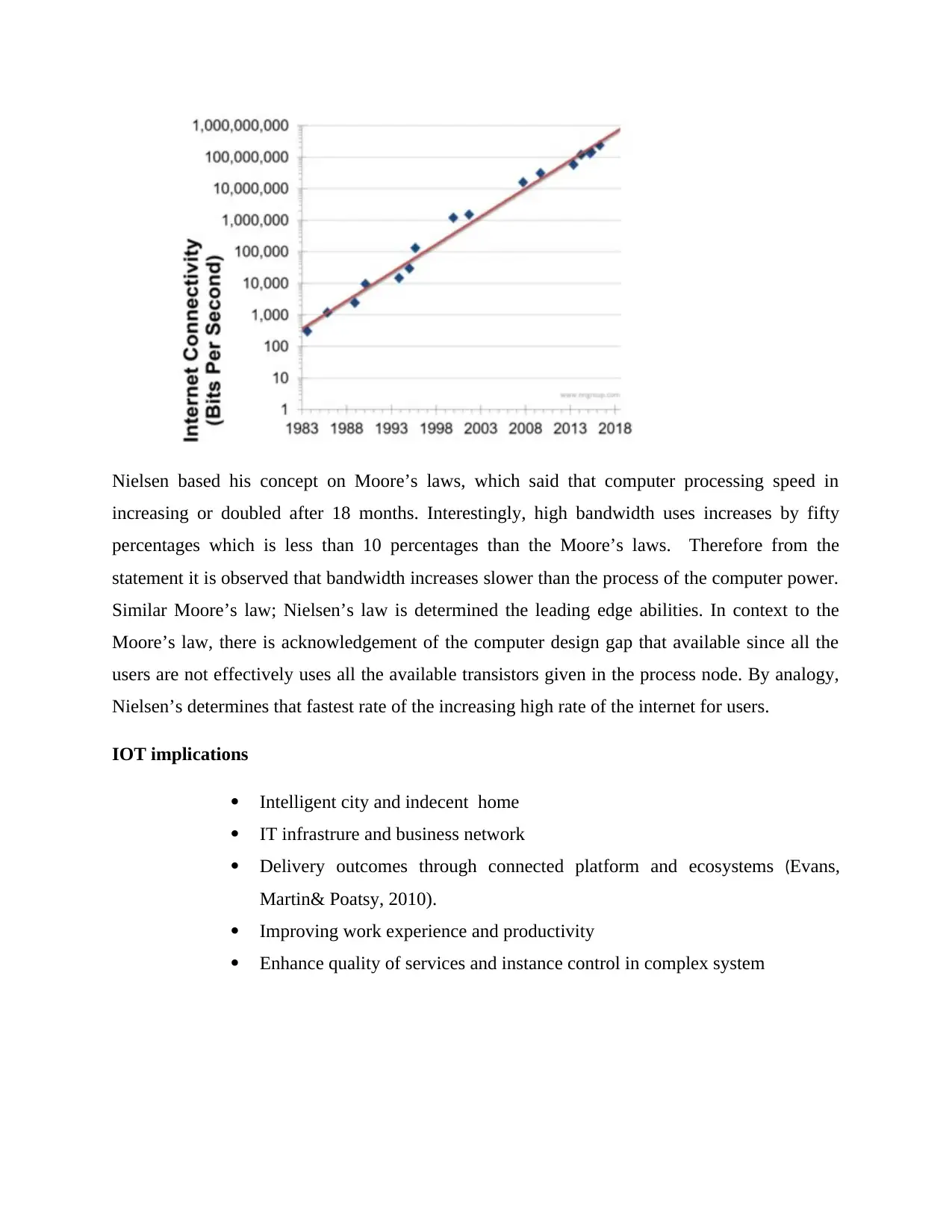
Nielsen based his concept on Moore’s laws, which said that computer processing speed in
increasing or doubled after 18 months. Interestingly, high bandwidth uses increases by fifty
percentages which is less than 10 percentages than the Moore’s laws. Therefore from the
statement it is observed that bandwidth increases slower than the process of the computer power.
Similar Moore’s law; Nielsen’s law is determined the leading edge abilities. In context to the
Moore’s law, there is acknowledgement of the computer design gap that available since all the
users are not effectively uses all the available transistors given in the process node. By analogy,
Nielsen’s determines that fastest rate of the increasing high rate of the internet for users.
IOT implications
Intelligent city and indecent home
IT infrastrure and business network
Delivery outcomes through connected platform and ecosystems (Evans,
Martin& Poatsy, 2010).
Improving work experience and productivity
Enhance quality of services and instance control in complex system
increasing or doubled after 18 months. Interestingly, high bandwidth uses increases by fifty
percentages which is less than 10 percentages than the Moore’s laws. Therefore from the
statement it is observed that bandwidth increases slower than the process of the computer power.
Similar Moore’s law; Nielsen’s law is determined the leading edge abilities. In context to the
Moore’s law, there is acknowledgement of the computer design gap that available since all the
users are not effectively uses all the available transistors given in the process node. By analogy,
Nielsen’s determines that fastest rate of the increasing high rate of the internet for users.
IOT implications
Intelligent city and indecent home
IT infrastrure and business network
Delivery outcomes through connected platform and ecosystems (Evans,
Martin& Poatsy, 2010).
Improving work experience and productivity
Enhance quality of services and instance control in complex system
References
Gubbi, J., Buyya, R., Marusic, S., & Palaniswami, M. (2013). Internet of Things (IoT): A vision,
architectural elements, and future directions. Future generation computer
systems, 29(7), 1645-1660.
Kelly, S. D. T., Suryadevara, N. K., & Mukhopadhyay, S. C. (2013). Towards the implementation of IoT for
environmental condition monitoring in homes.IEEE Sensors Journal, 13(10), 3846-3853.
Shneiderman, B. (2010). Designing the user interface: strategies for effective human-computer
interaction. Pearson Education India.
Kottomtharayil, R., Gokhale, P., Prahlad, A., Retnamma, M. K. V., Ngo, D., & Devassy, V.
(2010). U.S. Patent No. 7,769,961. Washington, DC: U.S. Patent and Trademark Office.
Evans, A., Martin, K., & Poatsy, M. A. (2010). Technology in action. Prentice Hall.
Green, P. (Ed.). (2012). Computer network architectures and protocols. Springer Science &
Business Media.
QIAN, Z. H., & WANG, Y. J. (2012). IoT technology and application. Acta Electronica Sinica, 5,
026.
Zhao, K., & Ge, L. (2013, December). A survey on the internet of things security.
In Computational Intelligence and Security (CIS), 2013 9th International Conference
on (pp. 663-667). IEEE.
Nielsen, J. (2014). Nielsen’s Law of Internet Bandwidth, 1998.
Sanders, T. (2015). The Moore's Law of Moore's Laws. MRS Bulletin, 40(11), 991.
Kottomtharayil, R., Gokhale, P., Prahlad, A., Retnamma, M. K. V., Ngo, D., & Devassy, V.
(2010). U.S. Patent No. 7,769,961. Washington, DC: U.S. Patent and Trademark Office.
Gubbi, J., Buyya, R., Marusic, S., & Palaniswami, M. (2013). Internet of Things (IoT): A vision,
architectural elements, and future directions. Future generation computer
systems, 29(7), 1645-1660.
Kelly, S. D. T., Suryadevara, N. K., & Mukhopadhyay, S. C. (2013). Towards the implementation of IoT for
environmental condition monitoring in homes.IEEE Sensors Journal, 13(10), 3846-3853.
Shneiderman, B. (2010). Designing the user interface: strategies for effective human-computer
interaction. Pearson Education India.
Kottomtharayil, R., Gokhale, P., Prahlad, A., Retnamma, M. K. V., Ngo, D., & Devassy, V.
(2010). U.S. Patent No. 7,769,961. Washington, DC: U.S. Patent and Trademark Office.
Evans, A., Martin, K., & Poatsy, M. A. (2010). Technology in action. Prentice Hall.
Green, P. (Ed.). (2012). Computer network architectures and protocols. Springer Science &
Business Media.
QIAN, Z. H., & WANG, Y. J. (2012). IoT technology and application. Acta Electronica Sinica, 5,
026.
Zhao, K., & Ge, L. (2013, December). A survey on the internet of things security.
In Computational Intelligence and Security (CIS), 2013 9th International Conference
on (pp. 663-667). IEEE.
Nielsen, J. (2014). Nielsen’s Law of Internet Bandwidth, 1998.
Sanders, T. (2015). The Moore's Law of Moore's Laws. MRS Bulletin, 40(11), 991.
Kottomtharayil, R., Gokhale, P., Prahlad, A., Retnamma, M. K. V., Ngo, D., & Devassy, V.
(2010). U.S. Patent No. 7,769,961. Washington, DC: U.S. Patent and Trademark Office.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 12
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.




