BSc Cloud Computing: ACCC4002 Internet Protocols IPv6 Report
VerifiedAdded on 2022/10/19
|13
|2479
|79
Report
AI Summary
This report provides a comprehensive overview of IPv6, the successor to IPv4, addressing its importance in modern networking. It begins with an introduction to IPv6 and its 128-bit alphanumeric address structure, contrasting it with IPv4. The report details IPv6 address types, including Global Unicast, Unique Local, and Link-Local addresses, explaining their scopes and uses. It highlights the advantages of IPv6, such as improved customer insights, enhanced security, and the ability to overcome the limitations of IPv4. The report also covers IP addressing schemes, particularly VLSM, and applies them to a network scenario with multiple schools and server configurations. The report includes the advantages of VLSM addressing scheme and also includes IPv6 addresses for servers. The report concludes by emphasizing the benefits of IPv6 and its impact on the future of the internet, including improved security and efficiency. The report includes references to academic sources.
Running Head: IPv6 0
IPv6
Report
Student name
IPv6
Report
Student name
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
IPv6 1
Table of Contents
Introduction.................................................................................................................................................2
Address Structure....................................................................................................................................2
Address Types and Scope........................................................................................................................3
Advantages of IPv6..................................................................................................................................6
Conclusion...................................................................................................................................................7
Part -2..........................................................................................................................................................7
IP addressing scheme..................................................................................................................................7
References...................................................................................................................................................9
Table of Contents
Introduction.................................................................................................................................................2
Address Structure....................................................................................................................................2
Address Types and Scope........................................................................................................................3
Advantages of IPv6..................................................................................................................................6
Conclusion...................................................................................................................................................7
Part -2..........................................................................................................................................................7
IP addressing scheme..................................................................................................................................7
References...................................................................................................................................................9

IPv6 2
Introduction
A network has configured using Internet Protocol and addresses to identify each workstation. Therefore,
IPv4 and IPv6 addresses used to provide a valid address in a network to identify the identity in a network
at a worldwide level. An IPv6 address has used to identify a node in the addressing scheme of Internet
Protocol version 6. It is a 128-bit alphanumeric number (Henderson, 2003).
It has arranged in eight groups, which have 16 bits in each group. Each group has four digits that are in
hexadecimal numbers and they are separated using colons. As an example of IPv6, address is
FE80:CD00:0000:0CDE:1257:0000:211E:729C. It can be write as FE80:CD00:0:CDE:1257:0:211E:729C
(Forouzan, 2007).
This scheme has required because of running out of IPv4 addressing scheme. IPv6 can provide trillions of
IP addresses to the computer devices as well as other things, such as Internet of Things (IoT) devices,
people, animals, objects, and many others (Rouse, 2013).
Address Structure
IPv 6 has been created to provide better IP addresses to the different devices and it will connect many
other objects as well. In addition, a number of Internet users are increasing day-by-day, which is a
critical issue in front of the whole world. Therefore, IPv6 has developed to overtake IPv4 addresses.
Moreover, tunneling has been used to manage both types of IP addresses. However, the adoption of
IPv6 is highly increased in the last two years. There is an example of the IPv6 address of a device in the
below diagram (Tanenbaum, 2014).
Source: (Steve, 2019)
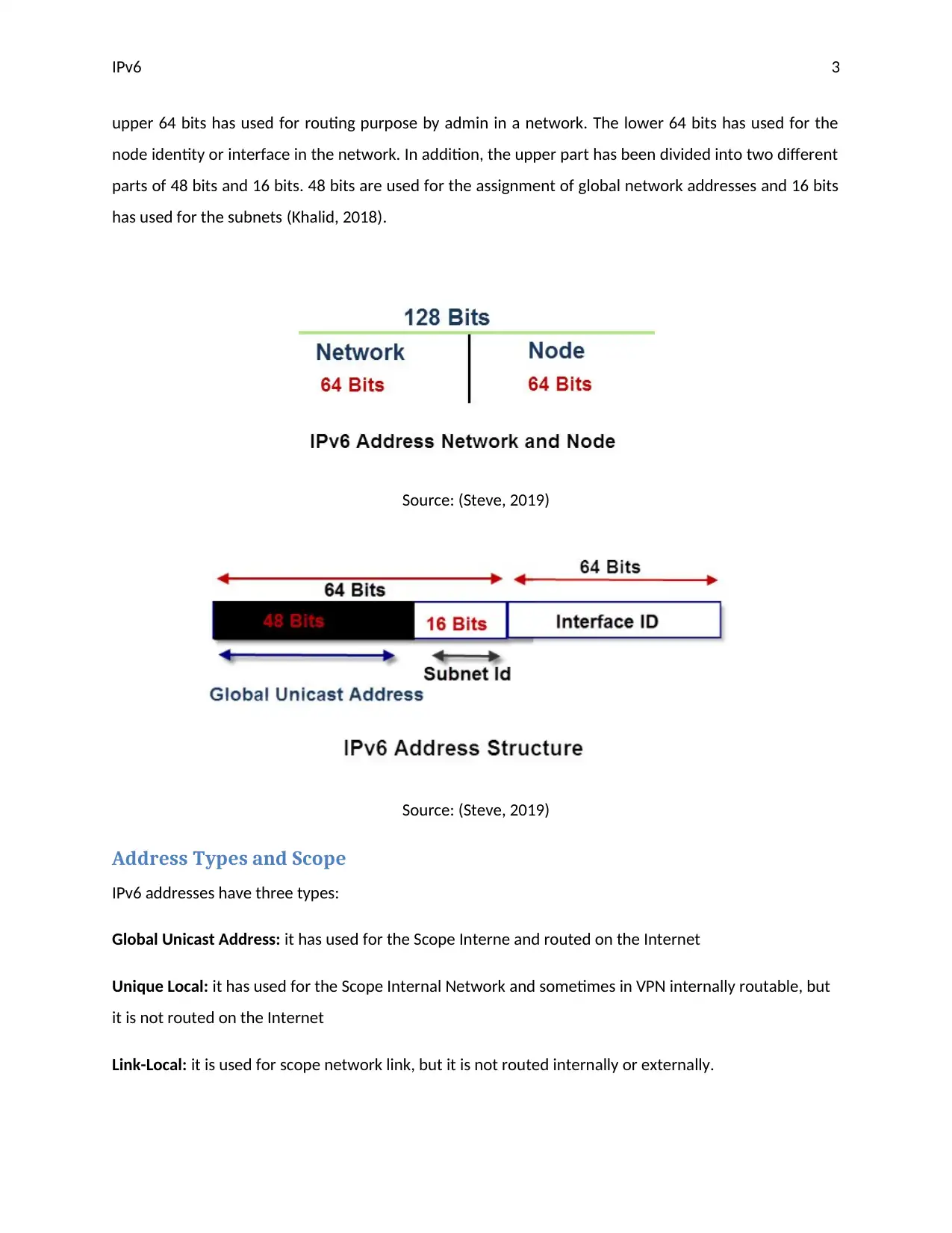
In addition, IPv4 uses two segments in their 32-bit address, which are network id and host id. Same as
IPv6 has divided 128-bit into two groups I network part and node part, both parts have 64 bits. The
Introduction
A network has configured using Internet Protocol and addresses to identify each workstation. Therefore,
IPv4 and IPv6 addresses used to provide a valid address in a network to identify the identity in a network
at a worldwide level. An IPv6 address has used to identify a node in the addressing scheme of Internet
Protocol version 6. It is a 128-bit alphanumeric number (Henderson, 2003).
It has arranged in eight groups, which have 16 bits in each group. Each group has four digits that are in
hexadecimal numbers and they are separated using colons. As an example of IPv6, address is
FE80:CD00:0000:0CDE:1257:0000:211E:729C. It can be write as FE80:CD00:0:CDE:1257:0:211E:729C
(Forouzan, 2007).
This scheme has required because of running out of IPv4 addressing scheme. IPv6 can provide trillions of
IP addresses to the computer devices as well as other things, such as Internet of Things (IoT) devices,
people, animals, objects, and many others (Rouse, 2013).
Address Structure
IPv 6 has been created to provide better IP addresses to the different devices and it will connect many
other objects as well. In addition, a number of Internet users are increasing day-by-day, which is a
critical issue in front of the whole world. Therefore, IPv6 has developed to overtake IPv4 addresses.
Moreover, tunneling has been used to manage both types of IP addresses. However, the adoption of
IPv6 is highly increased in the last two years. There is an example of the IPv6 address of a device in the
below diagram (Tanenbaum, 2014).
Source: (Steve, 2019)
In addition, IPv4 uses two segments in their 32-bit address, which are network id and host id. Same as
IPv6 has divided 128-bit into two groups I network part and node part, both parts have 64 bits. The
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
IPv6 3
upper 64 bits has used for routing purpose by admin in a network. The lower 64 bits has used for the
node identity or interface in the network. In addition, the upper part has been divided into two different
parts of 48 bits and 16 bits. 48 bits are used for the assignment of global network addresses and 16 bits
has used for the subnets (Khalid, 2018).
Source: (Steve, 2019)
Source: (Steve, 2019)
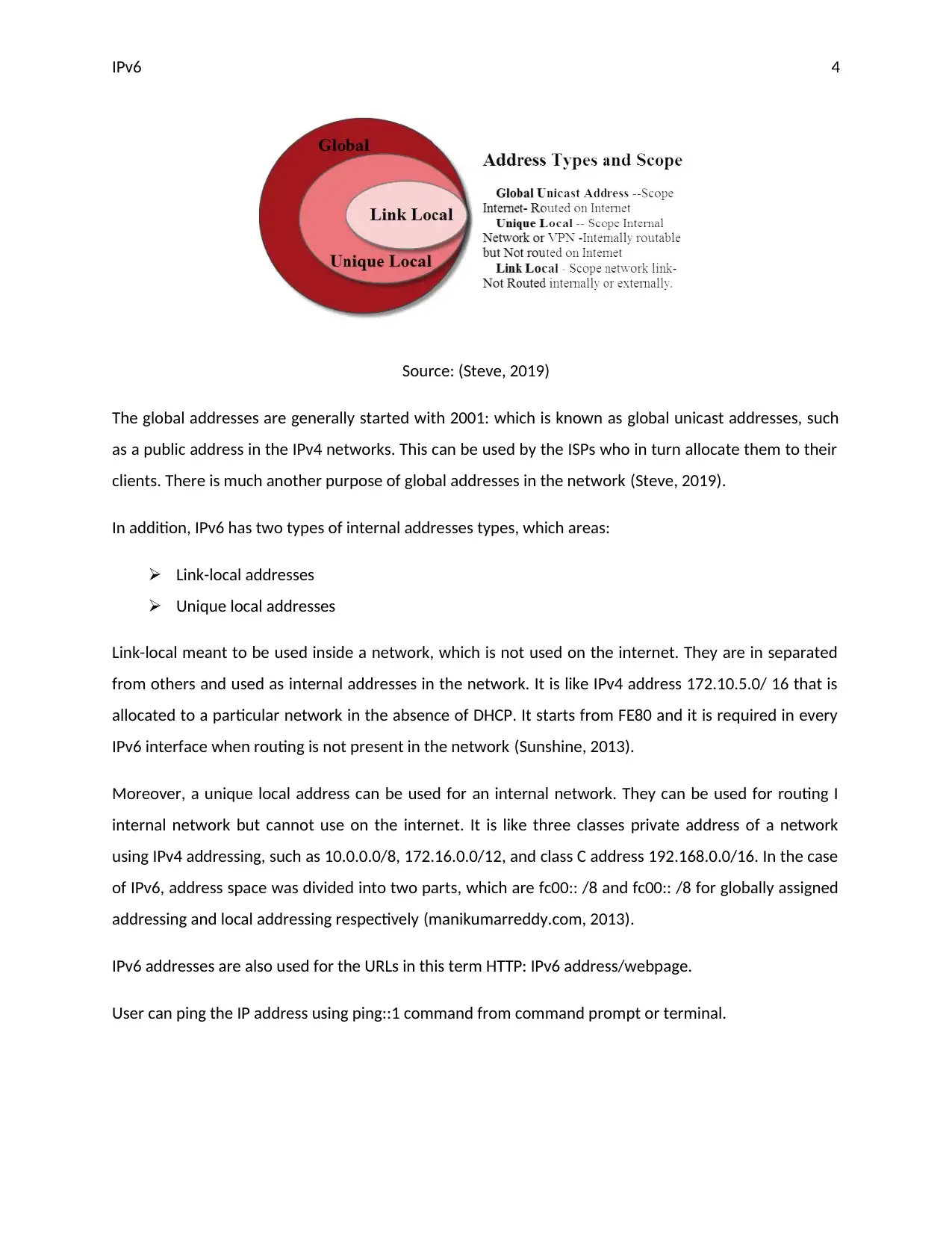
Address Types and Scope
IPv6 addresses have three types:
Global Unicast Address: it has used for the Scope Interne and routed on the Internet
Unique Local: it has used for the Scope Internal Network and sometimes in VPN internally routable, but
it is not routed on the Internet
Link-Local: it is used for scope network link, but it is not routed internally or externally.
upper 64 bits has used for routing purpose by admin in a network. The lower 64 bits has used for the
node identity or interface in the network. In addition, the upper part has been divided into two different
parts of 48 bits and 16 bits. 48 bits are used for the assignment of global network addresses and 16 bits
has used for the subnets (Khalid, 2018).
Source: (Steve, 2019)
Source: (Steve, 2019)
Address Types and Scope
IPv6 addresses have three types:
Global Unicast Address: it has used for the Scope Interne and routed on the Internet
Unique Local: it has used for the Scope Internal Network and sometimes in VPN internally routable, but
it is not routed on the Internet
Link-Local: it is used for scope network link, but it is not routed internally or externally.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
IPv6 4
Source: (Steve, 2019)
The global addresses are generally started with 2001: which is known as global unicast addresses, such
as a public address in the IPv4 networks. This can be used by the ISPs who in turn allocate them to their
clients. There is much another purpose of global addresses in the network (Steve, 2019).
In addition, IPv6 has two types of internal addresses types, which areas:
Link-local addresses
Unique local addresses
Link-local meant to be used inside a network, which is not used on the internet. They are in separated
from others and used as internal addresses in the network. It is like IPv4 address 172.10.5.0/ 16 that is
allocated to a particular network in the absence of DHCP. It starts from FE80 and it is required in every
IPv6 interface when routing is not present in the network (Sunshine, 2013).
Moreover, a unique local address can be used for an internal network. They can be used for routing I
internal network but cannot use on the internet. It is like three classes private address of a network
using IPv4 addressing, such as 10.0.0.0/8, 172.16.0.0/12, and class C address 192.168.0.0/16. In the case
of IPv6, address space was divided into two parts, which are fc00:: /8 and fc00:: /8 for globally assigned
addressing and local addressing respectively (manikumarreddy.com, 2013).
IPv6 addresses are also used for the URLs in this term HTTP: IPv6 address/webpage.
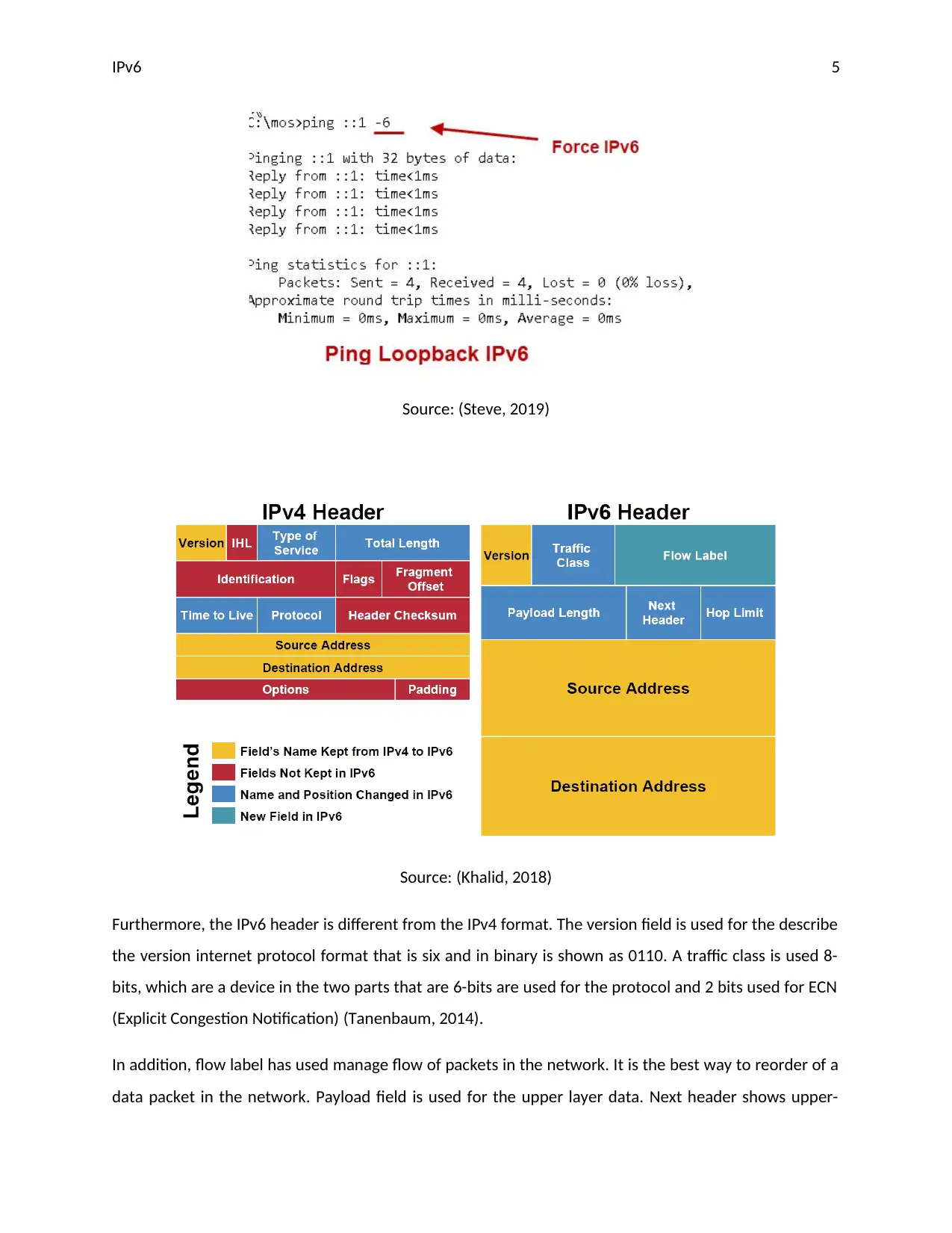
User can ping the IP address using ping::1 command from command prompt or terminal.
Source: (Steve, 2019)
The global addresses are generally started with 2001: which is known as global unicast addresses, such
as a public address in the IPv4 networks. This can be used by the ISPs who in turn allocate them to their
clients. There is much another purpose of global addresses in the network (Steve, 2019).
In addition, IPv6 has two types of internal addresses types, which areas:
Link-local addresses
Unique local addresses
Link-local meant to be used inside a network, which is not used on the internet. They are in separated
from others and used as internal addresses in the network. It is like IPv4 address 172.10.5.0/ 16 that is
allocated to a particular network in the absence of DHCP. It starts from FE80 and it is required in every
IPv6 interface when routing is not present in the network (Sunshine, 2013).
Moreover, a unique local address can be used for an internal network. They can be used for routing I
internal network but cannot use on the internet. It is like three classes private address of a network
using IPv4 addressing, such as 10.0.0.0/8, 172.16.0.0/12, and class C address 192.168.0.0/16. In the case
of IPv6, address space was divided into two parts, which are fc00:: /8 and fc00:: /8 for globally assigned
addressing and local addressing respectively (manikumarreddy.com, 2013).
IPv6 addresses are also used for the URLs in this term HTTP: IPv6 address/webpage.
User can ping the IP address using ping::1 command from command prompt or terminal.
IPv6 5
Source: (Steve, 2019)
Source: (Khalid, 2018)
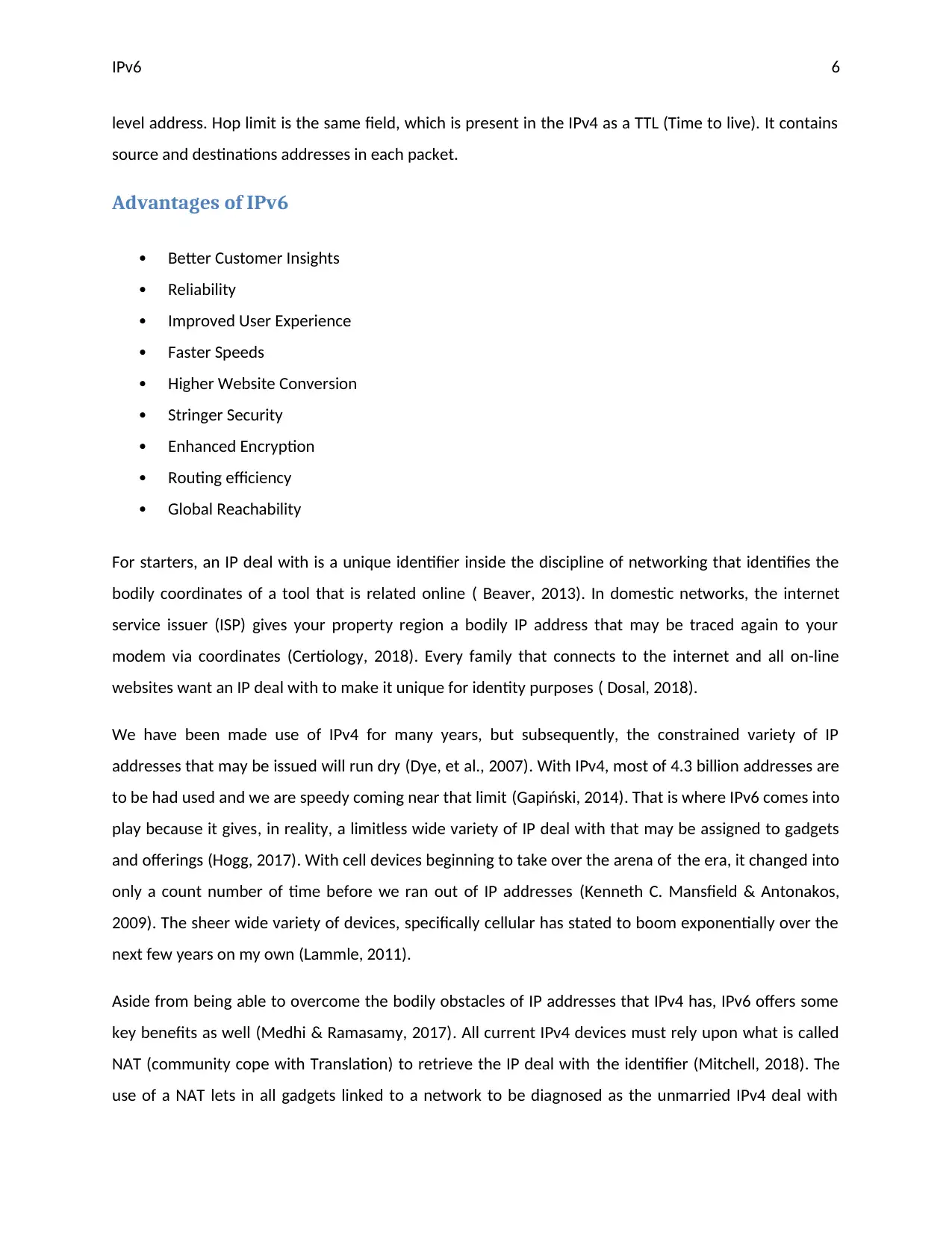
Furthermore, the IPv6 header is different from the IPv4 format. The version field is used for the describe
the version internet protocol format that is six and in binary is shown as 0110. A traffic class is used 8-
bits, which are a device in the two parts that are 6-bits are used for the protocol and 2 bits used for ECN
(Explicit Congestion Notification) (Tanenbaum, 2014).
In addition, flow label has used manage flow of packets in the network. It is the best way to reorder of a
data packet in the network. Payload field is used for the upper layer data. Next header shows upper-
Source: (Steve, 2019)
Source: (Khalid, 2018)
Furthermore, the IPv6 header is different from the IPv4 format. The version field is used for the describe
the version internet protocol format that is six and in binary is shown as 0110. A traffic class is used 8-
bits, which are a device in the two parts that are 6-bits are used for the protocol and 2 bits used for ECN
(Explicit Congestion Notification) (Tanenbaum, 2014).
In addition, flow label has used manage flow of packets in the network. It is the best way to reorder of a
data packet in the network. Payload field is used for the upper layer data. Next header shows upper-
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
IPv6 6
level address. Hop limit is the same field, which is present in the IPv4 as a TTL (Time to live). It contains
source and destinations addresses in each packet.
Advantages of IPv6
Better Customer Insights
Reliability
Improved User Experience
Faster Speeds
Higher Website Conversion
Stringer Security
Enhanced Encryption
Routing efficiency
Global Reachability
For starters, an IP deal with is a unique identifier inside the discipline of networking that identifies the
bodily coordinates of a tool that is related online ( Beaver, 2013). In domestic networks, the internet
service issuer (ISP) gives your property region a bodily IP address that may be traced again to your
modem via coordinates (Certiology, 2018). Every family that connects to the internet and all on-line
websites want an IP deal with to make it unique for identity purposes ( Dosal, 2018).
We have been made use of IPv4 for many years, but subsequently, the constrained variety of IP
addresses that may be issued will run dry (Dye, et al., 2007). With IPv4, most of 4.3 billion addresses are
to be had used and we are speedy coming near that limit (Gapiński, 2014). That is where IPv6 comes into
play because it gives, in reality, a limitless wide variety of IP deal with that may be assigned to gadgets
and offerings (Hogg, 2017). With cell devices beginning to take over the arena of the era, it changed into
only a count number of time before we ran out of IP addresses (Kenneth C. Mansfield & Antonakos,
2009). The sheer wide variety of devices, specifically cellular has stated to boom exponentially over the
next few years on my own (Lammle, 2011).
Aside from being able to overcome the bodily obstacles of IP addresses that IPv4 has, IPv6 offers some
key benefits as well (Medhi & Ramasamy, 2017). All current IPv4 devices must rely upon what is called
NAT (community cope with Translation) to retrieve the IP deal with the identifier (Mitchell, 2018). The
use of a NAT lets in all gadgets linked to a network to be diagnosed as the unmarried IPv4 deal with
level address. Hop limit is the same field, which is present in the IPv4 as a TTL (Time to live). It contains
source and destinations addresses in each packet.
Advantages of IPv6
Better Customer Insights
Reliability
Improved User Experience
Faster Speeds
Higher Website Conversion
Stringer Security
Enhanced Encryption
Routing efficiency
Global Reachability
For starters, an IP deal with is a unique identifier inside the discipline of networking that identifies the
bodily coordinates of a tool that is related online ( Beaver, 2013). In domestic networks, the internet
service issuer (ISP) gives your property region a bodily IP address that may be traced again to your
modem via coordinates (Certiology, 2018). Every family that connects to the internet and all on-line
websites want an IP deal with to make it unique for identity purposes ( Dosal, 2018).
We have been made use of IPv4 for many years, but subsequently, the constrained variety of IP
addresses that may be issued will run dry (Dye, et al., 2007). With IPv4, most of 4.3 billion addresses are
to be had used and we are speedy coming near that limit (Gapiński, 2014). That is where IPv6 comes into
play because it gives, in reality, a limitless wide variety of IP deal with that may be assigned to gadgets
and offerings (Hogg, 2017). With cell devices beginning to take over the arena of the era, it changed into
only a count number of time before we ran out of IP addresses (Kenneth C. Mansfield & Antonakos,
2009). The sheer wide variety of devices, specifically cellular has stated to boom exponentially over the
next few years on my own (Lammle, 2011).
Aside from being able to overcome the bodily obstacles of IP addresses that IPv4 has, IPv6 offers some
key benefits as well (Medhi & Ramasamy, 2017). All current IPv4 devices must rely upon what is called
NAT (community cope with Translation) to retrieve the IP deal with the identifier (Mitchell, 2018). The
use of a NAT lets in all gadgets linked to a network to be diagnosed as the unmarried IPv4 deal with
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

IPv6 7
given to you via your ISP (Mitchell, 2018). Irrespective of which device you operate in your own home
community, they will all show the same place because of the number one IP address with the aid of
default (Paquet, 2013).
With IPv6, there will be no need to use a NAT, because of this all gadgets will be capable of being
recognized with a completely unique IP address in their very own (RIPE, 2018). IPv6 additionally lets in
for an extra exceptional-tuned manage over individual devices seeing that every device can be assigned
with a unique IP deal with network (Yadav, 2018) (Masucci, 2016). This permits for the router or modem
to engage with those devices especially, making manner for greater accurate communique between
them. Protection is likewise an awful lot higher with IPv6 since the authenticity of each network packet
is encrypted. Encrypting the packets being sent and acquired over the community ensures that packet
spoofing will be tougher to accomplish by using a capacity attacker (Prospects, 2018).
Conclusion
It has concluded from above parts of this report that IPv6 has provided many facilities in the field of
networking. It has contained a unique address style and types with a different structure. It can provide
trillions of IP addresses to various computer devices and other things, such as IoT devices, animals and
other objects. It can be used for identification of various objects. It will provide better addressing and
management of nodes in proper way.
Finally, IPv6 has implemented in various devices. It used for networking and other purposes. It will
provide better monitoring and controlling facility to the administrator.
Part -2
IP addressing scheme
I choose VLSM addressing scheme for this network because of various advantages of it instead of
particular fixed addresses. There are some extra requirements of addresses but it will be in limit.
Therefore, VLSM is used for the address scheme, as it is good for best-fit scheme. There are three school
given to you via your ISP (Mitchell, 2018). Irrespective of which device you operate in your own home
community, they will all show the same place because of the number one IP address with the aid of
default (Paquet, 2013).
With IPv6, there will be no need to use a NAT, because of this all gadgets will be capable of being
recognized with a completely unique IP address in their very own (RIPE, 2018). IPv6 additionally lets in
for an extra exceptional-tuned manage over individual devices seeing that every device can be assigned
with a unique IP deal with network (Yadav, 2018) (Masucci, 2016). This permits for the router or modem
to engage with those devices especially, making manner for greater accurate communique between
them. Protection is likewise an awful lot higher with IPv6 since the authenticity of each network packet
is encrypted. Encrypting the packets being sent and acquired over the community ensures that packet
spoofing will be tougher to accomplish by using a capacity attacker (Prospects, 2018).
Conclusion
It has concluded from above parts of this report that IPv6 has provided many facilities in the field of
networking. It has contained a unique address style and types with a different structure. It can provide
trillions of IP addresses to various computer devices and other things, such as IoT devices, animals and
other objects. It can be used for identification of various objects. It will provide better addressing and
management of nodes in proper way.
Finally, IPv6 has implemented in various devices. It used for networking and other purposes. It will
provide better monitoring and controlling facility to the administrator.
Part -2
IP addressing scheme
I choose VLSM addressing scheme for this network because of various advantages of it instead of
particular fixed addresses. There are some extra requirements of addresses but it will be in limit.
Therefore, VLSM is used for the address scheme, as it is good for best-fit scheme. There are three school
IPv6 8
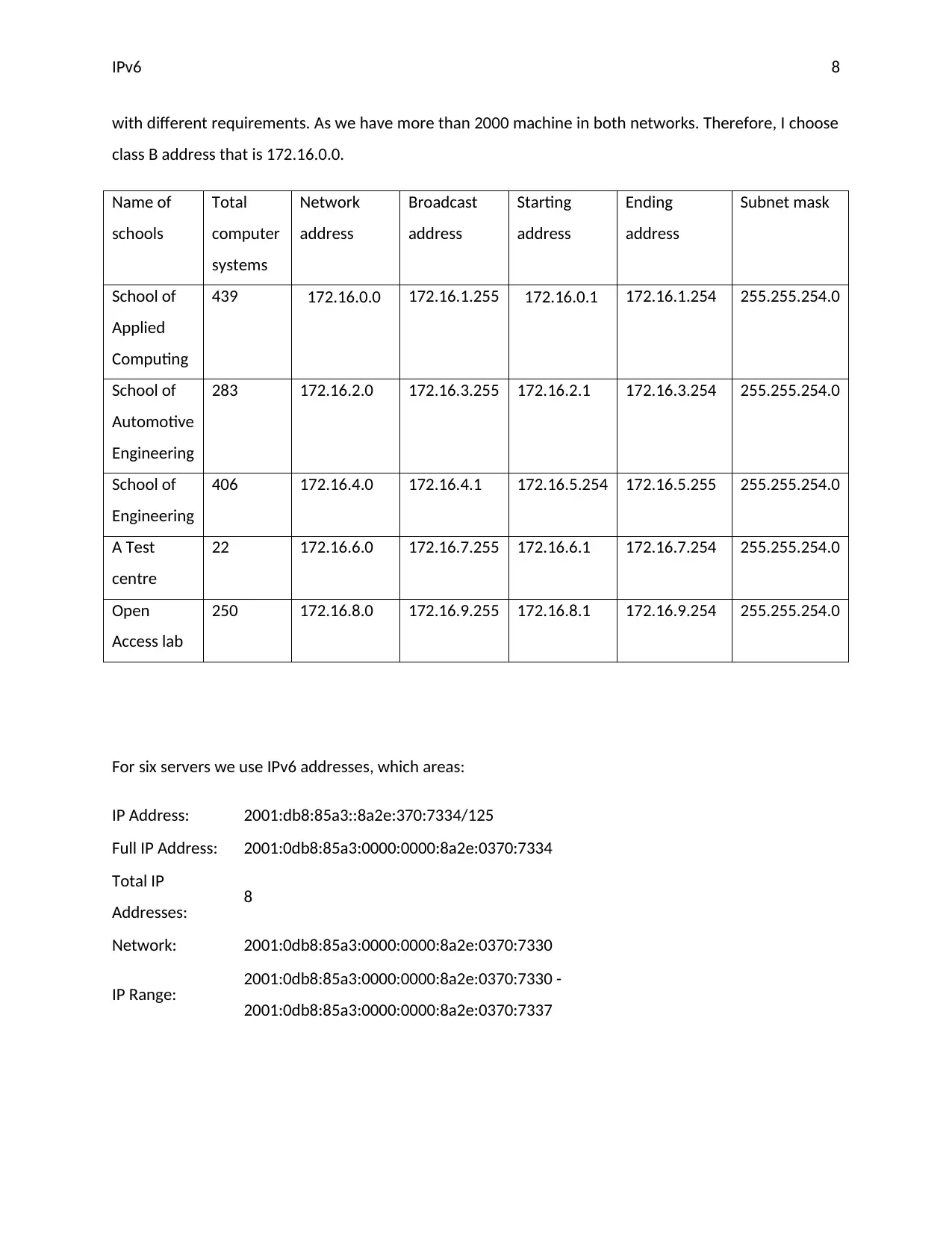
with different requirements. As we have more than 2000 machine in both networks. Therefore, I choose
class B address that is 172.16.0.0.
Name of
schools
Total
computer
systems
Network
address
Broadcast
address
Starting
address
Ending
address
Subnet mask
School of
Applied
Computing
439 172.16.0.0 172.16.1.255 172.16.0.1 172.16.1.254 255.255.254.0
School of
Automotive
Engineering
283 172.16.2.0 172.16.3.255 172.16.2.1 172.16.3.254 255.255.254.0
School of
Engineering
406 172.16.4.0 172.16.4.1 172.16.5.254 172.16.5.255 255.255.254.0
A Test
centre
22 172.16.6.0 172.16.7.255 172.16.6.1 172.16.7.254 255.255.254.0
Open
Access lab
250 172.16.8.0 172.16.9.255 172.16.8.1 172.16.9.254 255.255.254.0
For six servers we use IPv6 addresses, which areas:
IP Address: 2001:db8:85a3::8a2e:370:7334/125
Full IP Address: 2001:0db8:85a3:0000:0000:8a2e:0370:7334
Total IP
Addresses: 8
Network: 2001:0db8:85a3:0000:0000:8a2e:0370:7330
IP Range: 2001:0db8:85a3:0000:0000:8a2e:0370:7330 -
2001:0db8:85a3:0000:0000:8a2e:0370:7337
with different requirements. As we have more than 2000 machine in both networks. Therefore, I choose
class B address that is 172.16.0.0.
Name of
schools
Total
computer
systems
Network
address
Broadcast
address
Starting
address
Ending
address
Subnet mask
School of
Applied
Computing
439 172.16.0.0 172.16.1.255 172.16.0.1 172.16.1.254 255.255.254.0
School of
Automotive
Engineering
283 172.16.2.0 172.16.3.255 172.16.2.1 172.16.3.254 255.255.254.0
School of
Engineering
406 172.16.4.0 172.16.4.1 172.16.5.254 172.16.5.255 255.255.254.0
A Test
centre
22 172.16.6.0 172.16.7.255 172.16.6.1 172.16.7.254 255.255.254.0
Open
Access lab
250 172.16.8.0 172.16.9.255 172.16.8.1 172.16.9.254 255.255.254.0
For six servers we use IPv6 addresses, which areas:
IP Address: 2001:db8:85a3::8a2e:370:7334/125
Full IP Address: 2001:0db8:85a3:0000:0000:8a2e:0370:7334
Total IP
Addresses: 8
Network: 2001:0db8:85a3:0000:0000:8a2e:0370:7330
IP Range: 2001:0db8:85a3:0000:0000:8a2e:0370:7330 -
2001:0db8:85a3:0000:0000:8a2e:0370:7337
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
IPv6 9
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
IPv6 10
References
Beaver, K., 2013. Top 5 Common Network Security Vulnerabilities that Are Often Overlooked. [Online]
Available at: https://www.acunetix.com/blog/articles/the-top-5-network-security-vulnerabilities/
Dosal, E., 2018. 5 Common Network Security Problems and Solutions. [Online]
Available at: https://www.compuquip.com/blog/5-common-network-security-problems-and-solutions
[Accessed 12 March 2019].
Certiology, 2018. Network Devices:. [Online]
Available at: http://www.certiology.com/computing/computer-networking/network-devices.html
[Accessed 29 08 2018].
Dye, M., McDonald, R. & Rufi, A., 2007. Network Fundamentals, CCNA Exploration Companion Guide.
Indianapolis: Cisco press..
Forouzan, A. B., 2007. Data communications & networking. 8th ed. New Delhi: Tata McGraw-Hill
Education.
Gapiński, A., 2014. Strategies for Computer Networks Security. Kwartalnik Nauk o Przedsiębiorstwie,
Volume 3, pp. 59-65.
Henderson, T. R., 2003. Host mobility for IP networks: a comparison. IEEE network, 17(6), pp. 18-26.
Hogg, S., 2017. IPv6 Addressing for Enterprises. [Online]
Available at: https://www.networkworld.com/article/3235384/ipv6-address-enterprises-how-to-easier-
than-ipv4.html
[Accessed 5 August 2019].
Kenneth C. Mansfield, J. & Antonakos, J. L., 2009. Computer Networking for LANS to WANS: Hardware,
Software and Security. 1 ed. Bostan(MA): Cengage Learning.
Khalid, B., 2018. What Is IPv6 Address & Why Should I Know About It?. [Online]
Available at: https://www.purevpn.com/blog/what-is-ipv6-address-scty/
[Accessed 5 August 2019].
References
Beaver, K., 2013. Top 5 Common Network Security Vulnerabilities that Are Often Overlooked. [Online]
Available at: https://www.acunetix.com/blog/articles/the-top-5-network-security-vulnerabilities/
Dosal, E., 2018. 5 Common Network Security Problems and Solutions. [Online]
Available at: https://www.compuquip.com/blog/5-common-network-security-problems-and-solutions
[Accessed 12 March 2019].
Certiology, 2018. Network Devices:. [Online]
Available at: http://www.certiology.com/computing/computer-networking/network-devices.html
[Accessed 29 08 2018].
Dye, M., McDonald, R. & Rufi, A., 2007. Network Fundamentals, CCNA Exploration Companion Guide.
Indianapolis: Cisco press..
Forouzan, A. B., 2007. Data communications & networking. 8th ed. New Delhi: Tata McGraw-Hill
Education.
Gapiński, A., 2014. Strategies for Computer Networks Security. Kwartalnik Nauk o Przedsiębiorstwie,
Volume 3, pp. 59-65.
Henderson, T. R., 2003. Host mobility for IP networks: a comparison. IEEE network, 17(6), pp. 18-26.
Hogg, S., 2017. IPv6 Addressing for Enterprises. [Online]
Available at: https://www.networkworld.com/article/3235384/ipv6-address-enterprises-how-to-easier-
than-ipv4.html
[Accessed 5 August 2019].
Kenneth C. Mansfield, J. & Antonakos, J. L., 2009. Computer Networking for LANS to WANS: Hardware,
Software and Security. 1 ed. Bostan(MA): Cengage Learning.
Khalid, B., 2018. What Is IPv6 Address & Why Should I Know About It?. [Online]
Available at: https://www.purevpn.com/blog/what-is-ipv6-address-scty/
[Accessed 5 August 2019].
IPv6 11
Lammle, T., 2011. CCNA Cisco Certified Network Associate Deluxe Study Guide. indiana: John Wiley &
Sons.
manikumarreddy.com, 2013. Introduction to Network Fault Management. [Online]
Available at: https://manikumarreddy.com/2013/10/15/introduction-to-network-fault-management/
Masucci, M., 2016. 4 Ways to Ensure Network Physical Security. [Online]
Available at: https://www.belden.com/blog/smart-building/4-ways-to-ensure-network-physical-security
Medhi, D. & Ramasamy, K., 2017. Network routing: algorithms, protocols, and architectures. s.l.:Morgan
Kaufmann.
Mitchell, B., 2018. What Is Computer Networking?. [Online]
Available at: https://www.lifewire.com/what-is-computer-networking-816249
[Accessed 16 January 2019].
Paquet, C., 2013. Network Security Concepts and Policies. [Online]
Available at: http://www.ciscopress.com/articles/article.asp?p=1998559&seqNum=3
[Accessed 4 June 2019].
Prospects, 2018. Network engineer. [Online]
Available at: https://www.prospects.ac.uk/job-profiles/network-engineer
[Accessed 22 08 2018].
RIPE, 2018. IPv6 Address Allocation and Assignment Policy. [Online]
Available at: https://www.ripe.net/publications/docs/ripe-707
[Accessed 5 August 2019].
Rouse, M., 2013. IPv6 address. [Online]
Available at: https://internetofthingsagenda.techtarget.com/definition/IPv6-address
[Accessed 5 August 2019].
Steve, 2019. IPv6 Explained for Beginners. [Online]
Available at: http://www.steves-internet-guide.com/ipv6-guide/
[Accessed 5 August 2019].
Lammle, T., 2011. CCNA Cisco Certified Network Associate Deluxe Study Guide. indiana: John Wiley &
Sons.
manikumarreddy.com, 2013. Introduction to Network Fault Management. [Online]
Available at: https://manikumarreddy.com/2013/10/15/introduction-to-network-fault-management/
Masucci, M., 2016. 4 Ways to Ensure Network Physical Security. [Online]
Available at: https://www.belden.com/blog/smart-building/4-ways-to-ensure-network-physical-security
Medhi, D. & Ramasamy, K., 2017. Network routing: algorithms, protocols, and architectures. s.l.:Morgan
Kaufmann.
Mitchell, B., 2018. What Is Computer Networking?. [Online]
Available at: https://www.lifewire.com/what-is-computer-networking-816249
[Accessed 16 January 2019].
Paquet, C., 2013. Network Security Concepts and Policies. [Online]
Available at: http://www.ciscopress.com/articles/article.asp?p=1998559&seqNum=3
[Accessed 4 June 2019].
Prospects, 2018. Network engineer. [Online]
Available at: https://www.prospects.ac.uk/job-profiles/network-engineer
[Accessed 22 08 2018].
RIPE, 2018. IPv6 Address Allocation and Assignment Policy. [Online]
Available at: https://www.ripe.net/publications/docs/ripe-707
[Accessed 5 August 2019].
Rouse, M., 2013. IPv6 address. [Online]
Available at: https://internetofthingsagenda.techtarget.com/definition/IPv6-address
[Accessed 5 August 2019].
Steve, 2019. IPv6 Explained for Beginners. [Online]
Available at: http://www.steves-internet-guide.com/ipv6-guide/
[Accessed 5 August 2019].
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 13
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.



