Comprehensive IT Risk Management Analysis: VIC Government Security
VerifiedAdded on 2020/03/28
|15
|3652
|47
Report
AI Summary
This report provides a comprehensive analysis of IT risk management within the Victorian government. It begins with an illustration of security risks and concerns, followed by an assessment of the government's risk exposure, categorizing risks as high, medium, and low. The report then delves into the analysis of deliberate and accidental threats, ranking them based on their potential impact. It identifies and discusses the internal and external security and risk management challenges faced by the government, including the chosen strategies for risk mitigation. Furthermore, the report differentiates between risk and uncertainty, highlighting their implications for the Victorian government. The report concludes by recommending approaches for risk control and mitigation, offering valuable insights into securing the government's information systems. The report emphasizes the importance of data protection, security governance, and proactive measures to prevent data loss and theft, providing a framework for enhancing the overall security posture of the Victorian government's IT infrastructure. This detailed analysis aims to provide a clear understanding of the threats and vulnerabilities and offers strategic recommendations for effective risk management.

Running head: IT RISK MANAGEMENT
IT Risk Management
Name of the Student
Name of the University
Author Note
IT Risk Management
Name of the Student
Name of the University
Author Note
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
1
IT RISK MANAGEMENT
Table of Contents
Introduction..........................................................................................................................2
1. Illustration of Security risks and Concerns in VIC..........................................................2
2. Risk Exposure of Victorian Government........................................................................3
2.1 Risk Management and Identification of Risk Exposure: High, Medium and Low...4
3. Analysis of Deliberate and Accidental threats.................................................................5
3.1. Deliberate Threats.....................................................................................................5
3.2 Accidental Threats.....................................................................................................5
3.3. Threat ranking: High, Low.......................................................................................6
4. Security and Risk Management challenges faced by VIC government..........................6
4.1. Internal Security and Risk Management...................................................................7
4.2. External Security and Risk Management.................................................................7
4.3 The chosen Strategy of Risk Mitigation....................................................................8
5. Risk and Uncertainty.......................................................................................................8
5.1 Risk............................................................................................................................9
5.2 Uncertainty................................................................................................................9
6. Risk Control and Mitigation Approaches........................................................................9
Conclusion.........................................................................................................................10
References..........................................................................................................................12
IT RISK MANAGEMENT
Table of Contents
Introduction..........................................................................................................................2
1. Illustration of Security risks and Concerns in VIC..........................................................2
2. Risk Exposure of Victorian Government........................................................................3
2.1 Risk Management and Identification of Risk Exposure: High, Medium and Low...4
3. Analysis of Deliberate and Accidental threats.................................................................5
3.1. Deliberate Threats.....................................................................................................5
3.2 Accidental Threats.....................................................................................................5
3.3. Threat ranking: High, Low.......................................................................................6
4. Security and Risk Management challenges faced by VIC government..........................6
4.1. Internal Security and Risk Management...................................................................7
4.2. External Security and Risk Management.................................................................7
4.3 The chosen Strategy of Risk Mitigation....................................................................8
5. Risk and Uncertainty.......................................................................................................8
5.1 Risk............................................................................................................................9
5.2 Uncertainty................................................................................................................9
6. Risk Control and Mitigation Approaches........................................................................9
Conclusion.........................................................................................................................10
References..........................................................................................................................12
2
IT RISK MANAGEMENT
Introduction
Security and protection of confidentiality of data is essential for every organization.
Implementation of a proper and effective information system can help in data protection and
securing the privacy of the data. An effective information system is capable of detecting and
preventing any threats to creep into the system that may be a cause of data loss and data theft.
The information system of Victorian government is not secure enough and is currently
experiencing the threat of data loss. The framework of Victorian protective data security gives
direction to the Victorian State government for data protection. The information system of VIC
is exposed to a number of risks that can be classified as deliberate and accidental threats along
with the internal and external risks. Internal risks and accidental threats can be removed easily by
undertaking proper actions. External risks and deliberate threats are however difficult to
eliminate. Proper standard of data security is to be maintained by ensuring the security
governance, information security, personal security and ICT security (Healey, 2016). Different
security management framework can help the VIC government in detecting and eliminating the
threats from the system. The report discusses the different threats associated with the information
system of VIC government and draws a line between the risk and uncertainty about VIC. The
report concludes with the recommendation of approaches, VIC government could consider in
mitigating the associated risks.
1. Illustration of Security risks and Concerns in VIC
IT RISK MANAGEMENT
Introduction
Security and protection of confidentiality of data is essential for every organization.
Implementation of a proper and effective information system can help in data protection and
securing the privacy of the data. An effective information system is capable of detecting and
preventing any threats to creep into the system that may be a cause of data loss and data theft.
The information system of Victorian government is not secure enough and is currently
experiencing the threat of data loss. The framework of Victorian protective data security gives
direction to the Victorian State government for data protection. The information system of VIC
is exposed to a number of risks that can be classified as deliberate and accidental threats along
with the internal and external risks. Internal risks and accidental threats can be removed easily by
undertaking proper actions. External risks and deliberate threats are however difficult to
eliminate. Proper standard of data security is to be maintained by ensuring the security
governance, information security, personal security and ICT security (Healey, 2016). Different
security management framework can help the VIC government in detecting and eliminating the
threats from the system. The report discusses the different threats associated with the information
system of VIC government and draws a line between the risk and uncertainty about VIC. The
report concludes with the recommendation of approaches, VIC government could consider in
mitigating the associated risks.
1. Illustration of Security risks and Concerns in VIC
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
3
IT RISK MANAGEMENT
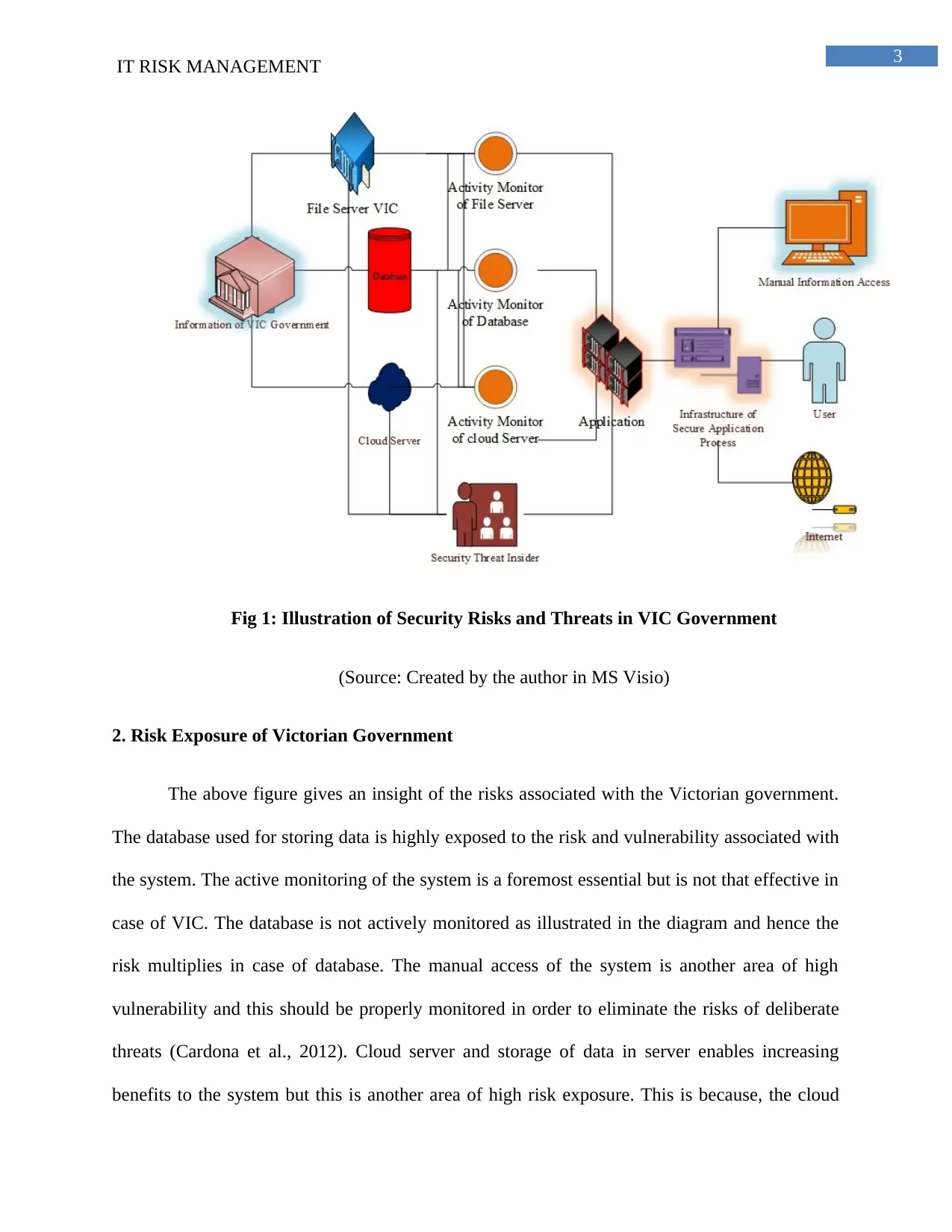
Fig 1: Illustration of Security Risks and Threats in VIC Government
(Source: Created by the author in MS Visio)
2. Risk Exposure of Victorian Government
The above figure gives an insight of the risks associated with the Victorian government.
The database used for storing data is highly exposed to the risk and vulnerability associated with
the system. The active monitoring of the system is a foremost essential but is not that effective in
case of VIC. The database is not actively monitored as illustrated in the diagram and hence the
risk multiplies in case of database. The manual access of the system is another area of high
vulnerability and this should be properly monitored in order to eliminate the risks of deliberate
threats (Cardona et al., 2012). Cloud server and storage of data in server enables increasing
benefits to the system but this is another area of high risk exposure. This is because, the cloud
IT RISK MANAGEMENT
Fig 1: Illustration of Security Risks and Threats in VIC Government
(Source: Created by the author in MS Visio)
2. Risk Exposure of Victorian Government
The above figure gives an insight of the risks associated with the Victorian government.
The database used for storing data is highly exposed to the risk and vulnerability associated with
the system. The active monitoring of the system is a foremost essential but is not that effective in
case of VIC. The database is not actively monitored as illustrated in the diagram and hence the
risk multiplies in case of database. The manual access of the system is another area of high
vulnerability and this should be properly monitored in order to eliminate the risks of deliberate
threats (Cardona et al., 2012). Cloud server and storage of data in server enables increasing
benefits to the system but this is another area of high risk exposure. This is because, the cloud
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
4
IT RISK MANAGEMENT
storage is prone to high risk and threats in form of data theft using unfair means, such as
malware infection and so on (Behl & Behl, 2012). Therefore, ensuring the data security of cloud
server is foremost essential for Victorian government.
2.1 Risk Management and Identification of Risk Exposure: High, Medium and Low
The identified risks are to be analyzed according to their negative effects in order to
manage it. The risks identified in the previous sections are further segregated into the areas of
high, medium and low risk exposure in order to prioritize them in a proper risk management
procedure (Haimes, 2015).
The area of high risk definitely includes the storage of data in cloud storage. Proper and
up to date security is essential for safeguarding the data stored in cloud storage. Cloud server is
very vulnerable to external attacks and with the concepts of data mining and big data being
prominent in today’s world, it becomes utmost important to secure the data stores in cloud
storage. Nothing is secure over internet and therefore, it is a foremost essential to secure the data
stored over cloud server. Therefore, the data storage in cloud server can be categorized as the
area of high-risk exposure.
The area of medium risk exposure includes the absence of active monitoring of the
database and risks associated with the file server of VIC government. This is categorized as the
area of medium risk exposure because proper security measures can help in eliminating the risks
associated with these risk areas (Bommer, Crowley & Pinho, 2015).
The manual access of data is although vulnerable to threat from insider, can be
categorized as the area of low risk exposure. This is because, internal risk or threat from an
IT RISK MANAGEMENT
storage is prone to high risk and threats in form of data theft using unfair means, such as
malware infection and so on (Behl & Behl, 2012). Therefore, ensuring the data security of cloud
server is foremost essential for Victorian government.
2.1 Risk Management and Identification of Risk Exposure: High, Medium and Low
The identified risks are to be analyzed according to their negative effects in order to
manage it. The risks identified in the previous sections are further segregated into the areas of
high, medium and low risk exposure in order to prioritize them in a proper risk management
procedure (Haimes, 2015).
The area of high risk definitely includes the storage of data in cloud storage. Proper and
up to date security is essential for safeguarding the data stored in cloud storage. Cloud server is
very vulnerable to external attacks and with the concepts of data mining and big data being
prominent in today’s world, it becomes utmost important to secure the data stores in cloud
storage. Nothing is secure over internet and therefore, it is a foremost essential to secure the data
stored over cloud server. Therefore, the data storage in cloud server can be categorized as the
area of high-risk exposure.
The area of medium risk exposure includes the absence of active monitoring of the
database and risks associated with the file server of VIC government. This is categorized as the
area of medium risk exposure because proper security measures can help in eliminating the risks
associated with these risk areas (Bommer, Crowley & Pinho, 2015).
The manual access of data is although vulnerable to threat from insider, can be
categorized as the area of low risk exposure. This is because, internal risk or threat from an
5
IT RISK MANAGEMENT
insider is easier to detect and eliminate. Therefore, this risk has the lowest priority and can be ac
upon in a strategic manner (Lam, 2014).
3. Analysis of Deliberate and Accidental threats
The major risks associated with the information system of Victorian government include
deliberate and accidental threats as well. These two threats have high risk exposure because of
the negative effects it may lay upon the government. Elimination of these two risks with highest
priority is essential for VIC government. The deliberate and the accidental threats associated
with VIC are elaborated in the following paragraphs.
3.1. Deliberate Threats
Deliberate threat can be termed as intentional threat as an organization is exposed to this
threat as a result of the ill intention of the attacker. The deliberate sabotaging of the information
system by acts of malware infection, viruses and Trojan horses into the system with an intention
of data theft and data modification can be termed as deliberate threats. These threats are infused
upon the system intentionally and are therefore difficult to manage (Alcorn, Good & Pain, 2013).
This type of threat is more complex than accidental threat and therefore adequate measures are
needed to be taken in order to eliminate this risk from the system. Deliberate risks are one of the
major causes of risks due to uncertainty.
3.2 Accidental Threats
The risks or threats that are not intended to or deliberately infused can be termed as
accidental threats. This risk creeps in mainly due to the activity of a threat insider. This threat is
termed as accidental threats as it is generally a result of the mistake of the employees and
IT RISK MANAGEMENT
insider is easier to detect and eliminate. Therefore, this risk has the lowest priority and can be ac
upon in a strategic manner (Lam, 2014).
3. Analysis of Deliberate and Accidental threats
The major risks associated with the information system of Victorian government include
deliberate and accidental threats as well. These two threats have high risk exposure because of
the negative effects it may lay upon the government. Elimination of these two risks with highest
priority is essential for VIC government. The deliberate and the accidental threats associated
with VIC are elaborated in the following paragraphs.
3.1. Deliberate Threats
Deliberate threat can be termed as intentional threat as an organization is exposed to this
threat as a result of the ill intention of the attacker. The deliberate sabotaging of the information
system by acts of malware infection, viruses and Trojan horses into the system with an intention
of data theft and data modification can be termed as deliberate threats. These threats are infused
upon the system intentionally and are therefore difficult to manage (Alcorn, Good & Pain, 2013).
This type of threat is more complex than accidental threat and therefore adequate measures are
needed to be taken in order to eliminate this risk from the system. Deliberate risks are one of the
major causes of risks due to uncertainty.
3.2 Accidental Threats
The risks or threats that are not intended to or deliberately infused can be termed as
accidental threats. This risk creeps in mainly due to the activity of a threat insider. This threat is
termed as accidental threats as it is generally a result of the mistake of the employees and
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
6
IT RISK MANAGEMENT
untrained staffs. Lack of knowledge about the information system and its management is one of
the major causes of this risk and the risk is widespread in VIC government as well. The primary
reason being the presence of untrained employees into the system (Man et al., 2013). The risk
has however, has a very low priority as it can be effectively managed by the intervention of the
organization and responding appropriately in culminating the threat.
3.3. Threat ranking: High, Low
The two threats identified in the information system of VIC government includes
deliberate and the accidental threats. On basis of the ill effect it may lay upon the system, these
two risk are ranked as rank one and rank two.
The deliberate risk is ranked in number one position as it includes the deliberate
sabotaging of the information security by means of unfair practices such as hacking, malware
infection, and phishing and so on. This risk is severe and therefore should be act upon as soon as
possible. Since the priority of this risk is high, it allotted the number one rank, which suggests
that this risk is needed to be eliminated from the system in no time.
The accidental risk has a lower priority and therefore, is allotted the rank two. This is
because, the ill effect of this risk is low. The main cause of this risk or threats includes lack of
knowledge or negligence of the employees. Example of accidental threats includes erroneous
data entry or not keeping the information system up to date. The severity of this risk is medium
to low and hence can be act upon in due time. This risk can be identified or mitigated easily and
therefore it is allocated the rank two.
4. Security and Risk Management challenges faced by VIC government
IT RISK MANAGEMENT
untrained staffs. Lack of knowledge about the information system and its management is one of
the major causes of this risk and the risk is widespread in VIC government as well. The primary
reason being the presence of untrained employees into the system (Man et al., 2013). The risk
has however, has a very low priority as it can be effectively managed by the intervention of the
organization and responding appropriately in culminating the threat.
3.3. Threat ranking: High, Low
The two threats identified in the information system of VIC government includes
deliberate and the accidental threats. On basis of the ill effect it may lay upon the system, these
two risk are ranked as rank one and rank two.
The deliberate risk is ranked in number one position as it includes the deliberate
sabotaging of the information security by means of unfair practices such as hacking, malware
infection, and phishing and so on. This risk is severe and therefore should be act upon as soon as
possible. Since the priority of this risk is high, it allotted the number one rank, which suggests
that this risk is needed to be eliminated from the system in no time.
The accidental risk has a lower priority and therefore, is allotted the rank two. This is
because, the ill effect of this risk is low. The main cause of this risk or threats includes lack of
knowledge or negligence of the employees. Example of accidental threats includes erroneous
data entry or not keeping the information system up to date. The severity of this risk is medium
to low and hence can be act upon in due time. This risk can be identified or mitigated easily and
therefore it is allocated the rank two.
4. Security and Risk Management challenges faced by VIC government
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
7
IT RISK MANAGEMENT
Risk is a result of uncertainty about a particular issue. There are different risks associated
with the information system of Victorian government and therefore proper risk management
strategy is essential for identifying and eliminating the risks from the system. two risk
management methodologies are discussed in the following paragraphs, which are internal
security risk management and external security risk management (Jouini, Rabai & Aissa, 2014).
4.1. Internal Security and Risk Management
Internal security risk management is one of the easiest risk management and mitigation
approach that VIC government can make use of. The method of internal security risk
management deals with the identification and elimination of risk by the organization. Generally,
the higher level authorities with a proper discussion with the employees suggest an approach to
mitigate or eliminate the risk after identifying it. This method of risk management is effective for
less severe risks and is a cost effective solution for the organization as well. This is an effective
method of the risk mitigation as well. This is because the employees and higher level authorities
are engaged in this risk mitigation approach, who have a proper knowledge about the working of
the organization and it’s every minute details (Poolsappasit, Dewri & Ray, 2012). Therefore, this
solution is time effective as well. However, the act of dishonest employees may result in yielding
an improper result in risk mitigation and can result in failure of the entire process.
4.2. External Security and Risk Management
This is another effective strategy of risk management and risk mitigation. In this
approach, help of experienced security consultants are fetched in order to identify the problems
associated with the system and its root cause. Different effective risk management tools and
techniques are used by these external consultants in mitigation and elimination of the risk
IT RISK MANAGEMENT
Risk is a result of uncertainty about a particular issue. There are different risks associated
with the information system of Victorian government and therefore proper risk management
strategy is essential for identifying and eliminating the risks from the system. two risk
management methodologies are discussed in the following paragraphs, which are internal
security risk management and external security risk management (Jouini, Rabai & Aissa, 2014).
4.1. Internal Security and Risk Management
Internal security risk management is one of the easiest risk management and mitigation
approach that VIC government can make use of. The method of internal security risk
management deals with the identification and elimination of risk by the organization. Generally,
the higher level authorities with a proper discussion with the employees suggest an approach to
mitigate or eliminate the risk after identifying it. This method of risk management is effective for
less severe risks and is a cost effective solution for the organization as well. This is an effective
method of the risk mitigation as well. This is because the employees and higher level authorities
are engaged in this risk mitigation approach, who have a proper knowledge about the working of
the organization and it’s every minute details (Poolsappasit, Dewri & Ray, 2012). Therefore, this
solution is time effective as well. However, the act of dishonest employees may result in yielding
an improper result in risk mitigation and can result in failure of the entire process.
4.2. External Security and Risk Management
This is another effective strategy of risk management and risk mitigation. In this
approach, help of experienced security consultants are fetched in order to identify the problems
associated with the system and its root cause. Different effective risk management tools and
techniques are used by these external consultants in mitigation and elimination of the risk
8
IT RISK MANAGEMENT
associated with the system. This generally provides a guaranteed risk mitigation solution for the
organization and therefore can be effectively used by the Victorian government in identification
and elimination of severe risks. This however involves a huge sum of capital investments.
Furthermore, a proper communication channel and means of communication is needed to be
established between the external consultant and the Victorian government in order to fetch
effective solutions to the problem (Rakow, Heard & Newell, 2015). Therefore, this an effective
risk mitigation approach that Victorian government can consider.
4.3 The chosen Strategy of Risk Mitigation
Both the internal and external risk mitigation strategy will be helpful for the Victorian
government in elimination of the risks associated with the system. The internal risk mitigation
approach can help in eliminating the internal risks associated with the system. This is because the
employees of the system generally have a detailed knowledge about the problems associated
with the system and therefore can help in mitigating them. The major security risks, which
include the deliberate threats and threat from an outsider, would however need the involvement
of a security expert in identifying the root cause of the problems and in suggestion of the
solutions in mitigating them. Therefore, Victorian government needs to run both internal and
external risk management strategies and approaches in eliminating the associated risks in the
system.
5. Risk and Uncertainty
There is a thin line between the concept of risk and uncertainty, which is needed to be
identified in order to strategically act upon them. The detailed description of the risk and
IT RISK MANAGEMENT
associated with the system. This generally provides a guaranteed risk mitigation solution for the
organization and therefore can be effectively used by the Victorian government in identification
and elimination of severe risks. This however involves a huge sum of capital investments.
Furthermore, a proper communication channel and means of communication is needed to be
established between the external consultant and the Victorian government in order to fetch
effective solutions to the problem (Rakow, Heard & Newell, 2015). Therefore, this an effective
risk mitigation approach that Victorian government can consider.
4.3 The chosen Strategy of Risk Mitigation
Both the internal and external risk mitigation strategy will be helpful for the Victorian
government in elimination of the risks associated with the system. The internal risk mitigation
approach can help in eliminating the internal risks associated with the system. This is because the
employees of the system generally have a detailed knowledge about the problems associated
with the system and therefore can help in mitigating them. The major security risks, which
include the deliberate threats and threat from an outsider, would however need the involvement
of a security expert in identifying the root cause of the problems and in suggestion of the
solutions in mitigating them. Therefore, Victorian government needs to run both internal and
external risk management strategies and approaches in eliminating the associated risks in the
system.
5. Risk and Uncertainty
There is a thin line between the concept of risk and uncertainty, which is needed to be
identified in order to strategically act upon them. The detailed description of the risk and
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
9
IT RISK MANAGEMENT
uncertainty associated with the VIC government are elaborated in the following paragraphs
(Guerron-Quintana, 2012).
5.1 Risk
Risk is a situation that involves a probable danger. It can be defined as the probability of
the damage an organization might face due to the involvement of certain threats and
vulnerabilities. An organization is generally exposed to a risk due to the act or involvement of
certain internal as well as external threats and vulnerabilities (Silbey, 2013). The major risk
associated with VIC is related to the information system of the government. It is not strong
enough to eliminate the data theft and security attacks that might be a cause of different threats
and vulnerabilities. The Victorian government is severely exposed to both internal and external
attacks. Risks can however be managed with the involvement of proper risk mitigation
approaches. Risk can be managed by proper strategic means (Rasmussen, 2013).
5.2 Uncertainty
Uncertainty is more severe than risk as it cannot be determined or managed. The
unmanageable risks or outcomes can be termed as uncertainty. This is more severe than risk as
the its effect is not certain. The uncertainties linked with the VIC government are the lack of
proper and effective decision-making (Covello et al., 2013). The insufficient knowledge of the
employees regarding the information system of the VIC government gives rise to the uncertainty
associated with the VIC. Uncertainty cannot be controlled or mitigated an therefore it is more
dangerous than risk (Toma, Chiriţă & Şarpe, 2012).
6. Risk Control and Mitigation Approaches
IT RISK MANAGEMENT
uncertainty associated with the VIC government are elaborated in the following paragraphs
(Guerron-Quintana, 2012).
5.1 Risk
Risk is a situation that involves a probable danger. It can be defined as the probability of
the damage an organization might face due to the involvement of certain threats and
vulnerabilities. An organization is generally exposed to a risk due to the act or involvement of
certain internal as well as external threats and vulnerabilities (Silbey, 2013). The major risk
associated with VIC is related to the information system of the government. It is not strong
enough to eliminate the data theft and security attacks that might be a cause of different threats
and vulnerabilities. The Victorian government is severely exposed to both internal and external
attacks. Risks can however be managed with the involvement of proper risk mitigation
approaches. Risk can be managed by proper strategic means (Rasmussen, 2013).
5.2 Uncertainty
Uncertainty is more severe than risk as it cannot be determined or managed. The
unmanageable risks or outcomes can be termed as uncertainty. This is more severe than risk as
the its effect is not certain. The uncertainties linked with the VIC government are the lack of
proper and effective decision-making (Covello et al., 2013). The insufficient knowledge of the
employees regarding the information system of the VIC government gives rise to the uncertainty
associated with the VIC. Uncertainty cannot be controlled or mitigated an therefore it is more
dangerous than risk (Toma, Chiriţă & Şarpe, 2012).
6. Risk Control and Mitigation Approaches
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
10
IT RISK MANAGEMENT
Proper risk mitigation approaches are necessary to eliminate the different risks associated
with the system. Proper risk mitigation strategies can help in eliminating all the internal and
external risks associated with the Victorian government. Quantitative risk mitigation approach
can help in estimating the probable causes and effect of the risks, which may ultimately help in
risk mitigation (Creswell, 2013). Furthermore, dealing with the risk strategically is more
important to estimate the probable damage it may lay upon the information system. The
probability and the impact of the risk should be evaluated of basis of the identified risks before
the application of risk mitigation strategies (Maxwell, 2012). The different risk mitigation
approaches are elaborated below-
1) Risk Avoidance: This is an effective and an expensive risk mitigation approach. This
avoids any type of risk in creeping into the system and therefore requires active monitoring of
the system
2) Risk limitation is another strategy that can be undertaken by the Victorian government
in eliminating the possibility of new risk creeping into the system. This is the most common
strategy employed by different organization as an effective means of risk mitigation (McNeil,
Frey & Embrechts, 2015). Proper intrusion detection system and the use of firewalls in the
information system can help in Risk limitation.
3) Risk transfer is another risk mitigation approach that can be undertaken by the VIC
government. It deals with the transfer of risk to a third party who is willing to take the charge of
the risk. This needs a lot of capital investment and is an expensive risk mitigation approaches.
IT RISK MANAGEMENT
Proper risk mitigation approaches are necessary to eliminate the different risks associated
with the system. Proper risk mitigation strategies can help in eliminating all the internal and
external risks associated with the Victorian government. Quantitative risk mitigation approach
can help in estimating the probable causes and effect of the risks, which may ultimately help in
risk mitigation (Creswell, 2013). Furthermore, dealing with the risk strategically is more
important to estimate the probable damage it may lay upon the information system. The
probability and the impact of the risk should be evaluated of basis of the identified risks before
the application of risk mitigation strategies (Maxwell, 2012). The different risk mitigation
approaches are elaborated below-
1) Risk Avoidance: This is an effective and an expensive risk mitigation approach. This
avoids any type of risk in creeping into the system and therefore requires active monitoring of
the system
2) Risk limitation is another strategy that can be undertaken by the Victorian government
in eliminating the possibility of new risk creeping into the system. This is the most common
strategy employed by different organization as an effective means of risk mitigation (McNeil,
Frey & Embrechts, 2015). Proper intrusion detection system and the use of firewalls in the
information system can help in Risk limitation.
3) Risk transfer is another risk mitigation approach that can be undertaken by the VIC
government. It deals with the transfer of risk to a third party who is willing to take the charge of
the risk. This needs a lot of capital investment and is an expensive risk mitigation approaches.
11
IT RISK MANAGEMENT
The above discussed risk mitigation approaches can be undertaken by the Victorian
government in order to eliminate all the possible risks associated with the information system of
the government.
Conclusion
Therefore, from the above discussion, it can be concluded that the information system of
the Victorian government is exposed to a number of security risks and concerns that should be
considered by the organization with a highest priority. The report identifies the different risks
associated with the information system of the Victorian government and classifies them on basis
of high, medium and low risk areas. The report further distinguishes between the risk and
uncertainty according to the severity of their effect in the organization. Risk is less severe than
uncertainty as it can be easily controlled and mitigated. The different threats associated with the
system are further classified as threat from insider and outsider. Deliberate threat or threat from
outsider is more severe as it is difficult to detect and eliminate. The report further discusses the
different strategies that VIC can undertake in controlling the risk. The report concludes with the
different recommended risk mitigation strategies and approaches that Victorian government can
consider.
IT RISK MANAGEMENT
The above discussed risk mitigation approaches can be undertaken by the Victorian
government in order to eliminate all the possible risks associated with the information system of
the government.
Conclusion
Therefore, from the above discussion, it can be concluded that the information system of
the Victorian government is exposed to a number of security risks and concerns that should be
considered by the organization with a highest priority. The report identifies the different risks
associated with the information system of the Victorian government and classifies them on basis
of high, medium and low risk areas. The report further distinguishes between the risk and
uncertainty according to the severity of their effect in the organization. Risk is less severe than
uncertainty as it can be easily controlled and mitigated. The different threats associated with the
system are further classified as threat from insider and outsider. Deliberate threat or threat from
outsider is more severe as it is difficult to detect and eliminate. The report further discusses the
different strategies that VIC can undertake in controlling the risk. The report concludes with the
different recommended risk mitigation strategies and approaches that Victorian government can
consider.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 15
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





