7COM1012 Operating Systems and Networks: Linux Security Report
VerifiedAdded on 2022/08/27
|23
|5009
|15
Report
AI Summary
This report provides a detailed analysis of Linux network security, exploring various aspects of operating systems and networks. It begins with an introduction to Linux networks, differentiating them from other operating systems like Windows and OS, and then delves into the history and literature review of security issues in Linux networks. The report examines different types of attacks, including active and passive attacks, and discusses various security measures such as firewalls. It also explores different Linux utilities used for network monitoring and security, including vnStat, iftop, nload, NetHogs, bmon, Darkstat, IPTraf, and Iperf/Iperf3. Furthermore, the report presents experimental work and analysis, including the use of an attacker system to test the security of a network with different firewall and server configurations. Finally, the report concludes with a discussion on the evolution of network security and the importance of implementing robust security measures to protect against various threats.

ABSTRACT
Linux is referred to as an operating system which is the utilization of utilization of programming
on any PC which authorizes the administrator of PC along with several applications for accessing
various gadgets on any PC for performing the wanted capacity. Linux OS is fundamentally the
same as the Oss for example, OS and windows. The system of security in Linux OS it contains
authentication of secret key, system discretion of document security auditing and access control.
The system of Linux viewed as liberated from malware and infections. Distinctive Linux utilities
or apparatus utilized in the execution of security are investigated. Furthermore, a topology of a
system is planned utilizing the systems of Linux possess diverse configurations of firewall and
server. One of such systems is utilized in the form of the attacker system for the aim of testing
the security of the system. Outcomes are acquired when attempts are made by the attacker
system for accessing the inner system; alongside assault examination data could then be
archived. This outcomes are preferred in a situation. In this particular situation, the consequences
of system testing before the arrangement of the application of security gauges and firewall in the
configurations of the server are clarified and then contrasted and outcomes in the wake of
designing.
Linux is referred to as an operating system which is the utilization of utilization of programming
on any PC which authorizes the administrator of PC along with several applications for accessing
various gadgets on any PC for performing the wanted capacity. Linux OS is fundamentally the
same as the Oss for example, OS and windows. The system of security in Linux OS it contains
authentication of secret key, system discretion of document security auditing and access control.
The system of Linux viewed as liberated from malware and infections. Distinctive Linux utilities
or apparatus utilized in the execution of security are investigated. Furthermore, a topology of a
system is planned utilizing the systems of Linux possess diverse configurations of firewall and
server. One of such systems is utilized in the form of the attacker system for the aim of testing
the security of the system. Outcomes are acquired when attempts are made by the attacker
system for accessing the inner system; alongside assault examination data could then be
archived. This outcomes are preferred in a situation. In this particular situation, the consequences
of system testing before the arrangement of the application of security gauges and firewall in the
configurations of the server are clarified and then contrasted and outcomes in the wake of
designing.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Table of Contents
1. INTRODUCTION...................................................................................................................................3
1.1. Linux Networks............................................................................................................................3
2. HISTORY AND LITERATURE REVIEW.....................................................................................................5
2.1. Security Issue in Linux Networks..................................................................................................5
2.2. Scope...........................................................................................................................................6
2.3. Advantages of NS.........................................................................................................................6
3. METHODS............................................................................................................................................7
3.1. Active Attacks..............................................................................................................................7
3.2. Passive Attack..............................................................................................................................7
3.3. Types of hackers:.........................................................................................................................7
3.4. Attack Sources.............................................................................................................................9
3.5. Security Measures.......................................................................................................................9
3.6. Network Servers overview...........................................................................................................9
4. EXPERIMENTAL WORK AND ANALYSIS...............................................................................................10
4.1. Network Traffic Monitor (vnStat)...............................................................................................10
4.2. Bandwidth Usage Tracking (iftop)..............................................................................................11
4.3. Tracking of Network Usage (nload)............................................................................................12
4.4. Network Traffic and Bandwidth Monitoring (NetHogs).............................................................13
4.5. Bandwidth Monitor and Rate Estimator (bmon).......................................................................14
4.6. Network Traffic Capturing (Darkstat).........................................................................................15
4.7. IP Network Monitor (IPTraf)......................................................................................................16
4.8. Network Bandwidth Measurement Tool (Iperf/Iperf3).............................................................17
5. EVOLUTION OF NETWORK SECURITY.................................................................................................19
5.1. Various attack types against a system.......................................................................................19
5.2. Methods of attacking a system..................................................................................................20
5.3. Categorizing systems based on function....................................................................................21
6. CONCLUSION.....................................................................................................................................22
7. REFERENCES......................................................................................................................................23
1. INTRODUCTION...................................................................................................................................3
1.1. Linux Networks............................................................................................................................3
2. HISTORY AND LITERATURE REVIEW.....................................................................................................5
2.1. Security Issue in Linux Networks..................................................................................................5
2.2. Scope...........................................................................................................................................6
2.3. Advantages of NS.........................................................................................................................6
3. METHODS............................................................................................................................................7
3.1. Active Attacks..............................................................................................................................7
3.2. Passive Attack..............................................................................................................................7
3.3. Types of hackers:.........................................................................................................................7
3.4. Attack Sources.............................................................................................................................9
3.5. Security Measures.......................................................................................................................9
3.6. Network Servers overview...........................................................................................................9
4. EXPERIMENTAL WORK AND ANALYSIS...............................................................................................10
4.1. Network Traffic Monitor (vnStat)...............................................................................................10
4.2. Bandwidth Usage Tracking (iftop)..............................................................................................11
4.3. Tracking of Network Usage (nload)............................................................................................12
4.4. Network Traffic and Bandwidth Monitoring (NetHogs).............................................................13
4.5. Bandwidth Monitor and Rate Estimator (bmon).......................................................................14
4.6. Network Traffic Capturing (Darkstat).........................................................................................15
4.7. IP Network Monitor (IPTraf)......................................................................................................16
4.8. Network Bandwidth Measurement Tool (Iperf/Iperf3).............................................................17
5. EVOLUTION OF NETWORK SECURITY.................................................................................................19
5.1. Various attack types against a system.......................................................................................19
5.2. Methods of attacking a system..................................................................................................20
5.3. Categorizing systems based on function....................................................................................21
6. CONCLUSION.....................................................................................................................................22
7. REFERENCES......................................................................................................................................23

1. INTRODUCTION
Open source software will be a software in which the source code could be accessed by
anybody. It tends to be assumed in a form of a plan for this software, a structure which is perfect
for increasing the understanding the process of functioning of the program or adjusting to its
plan. The source code of a program is like a rule prepared by the other program which is referred
to as the compiler which makes a genuine record those sudden spikes in demand for the PC of
the end user. These records are known as article code and it is that which is received by an end-
client during their time of purchase of closed-source software such as Microsoft Word and
traditional proprietary. In contrast with the source code of it, the program code of the article is
exceptionally hard for an individual to fathom or change. Along these lines, the open source
software could be referred to welcome along with encourage change, whereas the close source
software have a tendency not to. Theses specialized attributes are likewise commonly helped via
within the going with licenses of open source licenses grant redistribution and adjustment by the
client whereas the end-client of the closed source permit understandings will in general
authoritatively tie the client to abstain from redistributing or changing the software spreaded by
them.
1.1. Linux Networks
Linux is utilized for driving of networks in strategic conditions and the administrators of
network/system which are working in these situations must possess far more profound mastery
as compared at any other time. Propelled Linux Networking gets where the traditional networks
of Linux helps the experienced network administrators and system of Linux achieve increasingly
higher tackle a big number of issues as compared to they can do it with some different book. The
profundity and broadness of it makes it to be a single-volume reference for every single
proficient of Linux which is uncommon.
The networks of Linux organized in four segments, every basic towards the working
(Nimbalkar et al. 2017) Linux director: Local Network Servers, Network Security, Low-Level
configuration, Router Functions and Internet Servers. Top to bottom inclusion incorporates:
arrangement of TCP/IP and portion, server start up scripting, elective network stacks, DHCP
Open source software will be a software in which the source code could be accessed by
anybody. It tends to be assumed in a form of a plan for this software, a structure which is perfect
for increasing the understanding the process of functioning of the program or adjusting to its
plan. The source code of a program is like a rule prepared by the other program which is referred
to as the compiler which makes a genuine record those sudden spikes in demand for the PC of
the end user. These records are known as article code and it is that which is received by an end-
client during their time of purchase of closed-source software such as Microsoft Word and
traditional proprietary. In contrast with the source code of it, the program code of the article is
exceptionally hard for an individual to fathom or change. Along these lines, the open source
software could be referred to welcome along with encourage change, whereas the close source
software have a tendency not to. Theses specialized attributes are likewise commonly helped via
within the going with licenses of open source licenses grant redistribution and adjustment by the
client whereas the end-client of the closed source permit understandings will in general
authoritatively tie the client to abstain from redistributing or changing the software spreaded by
them.
1.1. Linux Networks
Linux is utilized for driving of networks in strategic conditions and the administrators of
network/system which are working in these situations must possess far more profound mastery
as compared at any other time. Propelled Linux Networking gets where the traditional networks
of Linux helps the experienced network administrators and system of Linux achieve increasingly
higher tackle a big number of issues as compared to they can do it with some different book. The
profundity and broadness of it makes it to be a single-volume reference for every single
proficient of Linux which is uncommon.
The networks of Linux organized in four segments, every basic towards the working
(Nimbalkar et al. 2017) Linux director: Local Network Servers, Network Security, Low-Level
configuration, Router Functions and Internet Servers. Top to bottom inclusion incorporates:
arrangement of TCP/IP and portion, server start up scripting, elective network stacks, DHCP
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide

design, printer sharing, remote login servers, Kerberos authentication, GUI access, mail
convention, VPNs, iptables firewall, network reinforcements and remote system organizations.
The broad segment over Internet administrations tells the best way for handling secure
destinations and virtual spaces; investigate records of Apache log along with running of the
servers of FTP; and possesses nitty gritty inclusion of the systems of email based on SMTP.
Among several points canvassed in outstanding profundity: designing of Kerberos, font servers,
running of time servers and utilization of the scripting abilities of Samba for copying CDs and
making PDFs. For accomplished head of network or system of Linux, and for the power clients
of Linux with several duties related with the network.
convention, VPNs, iptables firewall, network reinforcements and remote system organizations.
The broad segment over Internet administrations tells the best way for handling secure
destinations and virtual spaces; investigate records of Apache log along with running of the
servers of FTP; and possesses nitty gritty inclusion of the systems of email based on SMTP.
Among several points canvassed in outstanding profundity: designing of Kerberos, font servers,
running of time servers and utilization of the scripting abilities of Samba for copying CDs and
making PDFs. For accomplished head of network or system of Linux, and for the power clients
of Linux with several duties related with the network.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
2. HISTORY AND LITERATURE REVIEW
2.1. Security Issue in Linux Networks
The issues of security should be preferred and possibly manage a huge counts of various
devices and provide accessible exposures of security they speak to. This kinds of issues are
depicted some of the following agent issues of security of hardware and software in the
networks of Linux. Huge numbers of this items of software could be downloaded from at
least one locales of Web recorded in. A portion of the estimates of security portrayed is clear
and commonly utilized, for example passwords are utilized in the networks of Linux.
Internet has evolved to be a risky spot over the most recent couple of years. With the
increase in the traffic and significant transactions which are significant in nature are taking
place your hazard develops as miscreants attempt to harm, capture, take or adjust your
information. On the off chance that there is something worth taking, at that point someone
will attempt to take it. An essential reason that Linux systems are so well known is on the
grounds that they are hearty and have several complex measure of security. As the director of
a system of Linux for your expertise area or independent venture, you might feel somewhat
plagued by this dangers. You have already heard that Linux remains secure. It is clichéd,
obviously, that on the off chance that you don’t utilize the Linux security apparatuses gave,
at that point you ought to be prepared for the inescapable break-in (Mishra and Goyal 2014).
Issues can likewise be brought about by seriously actualized measures of security.
Verifying a machine of Linux could get quite convoluted and whole retires of books also
have been committed towards the subject to:
Management of accounts and user authentication.
Access control on directory and file.
Process management.
Network access control.
Self-protection functioning.
Hacking of prevention functions.
2.1. Security Issue in Linux Networks
The issues of security should be preferred and possibly manage a huge counts of various
devices and provide accessible exposures of security they speak to. This kinds of issues are
depicted some of the following agent issues of security of hardware and software in the
networks of Linux. Huge numbers of this items of software could be downloaded from at
least one locales of Web recorded in. A portion of the estimates of security portrayed is clear
and commonly utilized, for example passwords are utilized in the networks of Linux.
Internet has evolved to be a risky spot over the most recent couple of years. With the
increase in the traffic and significant transactions which are significant in nature are taking
place your hazard develops as miscreants attempt to harm, capture, take or adjust your
information. On the off chance that there is something worth taking, at that point someone
will attempt to take it. An essential reason that Linux systems are so well known is on the
grounds that they are hearty and have several complex measure of security. As the director of
a system of Linux for your expertise area or independent venture, you might feel somewhat
plagued by this dangers. You have already heard that Linux remains secure. It is clichéd,
obviously, that on the off chance that you don’t utilize the Linux security apparatuses gave,
at that point you ought to be prepared for the inescapable break-in (Mishra and Goyal 2014).
Issues can likewise be brought about by seriously actualized measures of security.
Verifying a machine of Linux could get quite convoluted and whole retires of books also
have been committed towards the subject to:
Management of accounts and user authentication.
Access control on directory and file.
Process management.
Network access control.
Self-protection functioning.
Hacking of prevention functions.
Performance and installation.
2.2. Scope
According to the present business framework situation, all sort of organization initially
focusing to set one up great network security system for guaranteeing of loss of any protected
information. And in this particular spot estimation of a network specialist will naturally pick up
according to organization necessity. Those specialists basically play one of the indispensable
jobs for operating handling any sort of Security Bridge and execute a few machines like
Firewalls, presenting a few IPS for verifying some significant information of any sort of
organization.
2.3. Advantages of NS
Security of network helps in ensuring of customer’s personal information present over the
network.
NS promotes protection of information which is shred among the PCs over the network.
Spyware/infection assaults or hacking endeavours from internet would not contain the
option of hurting physical PCs. Avoidance of outer potential assaults.
NS provides various access levels. There are various PCs in the events connected to any
network, there could be fewer PCs which might contain prominent information access
than others.
Private networks could be provided protection from outer assaults by deterring them from
the internet. The security of networks makes them safer from the assaults of infection and
so on.
2.2. Scope
According to the present business framework situation, all sort of organization initially
focusing to set one up great network security system for guaranteeing of loss of any protected
information. And in this particular spot estimation of a network specialist will naturally pick up
according to organization necessity. Those specialists basically play one of the indispensable
jobs for operating handling any sort of Security Bridge and execute a few machines like
Firewalls, presenting a few IPS for verifying some significant information of any sort of
organization.
2.3. Advantages of NS
Security of network helps in ensuring of customer’s personal information present over the
network.
NS promotes protection of information which is shred among the PCs over the network.
Spyware/infection assaults or hacking endeavours from internet would not contain the
option of hurting physical PCs. Avoidance of outer potential assaults.
NS provides various access levels. There are various PCs in the events connected to any
network, there could be fewer PCs which might contain prominent information access
than others.
Private networks could be provided protection from outer assaults by deterring them from
the internet. The security of networks makes them safer from the assaults of infection and
so on.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
3. METHODS
Organization is not secured for the hackers. They may attack from inside of the outside of the
organization. All of their actions may be situated as active or passive attacks (Deng 2011).
Operations and the system resources are disrupted by the active attacks. So the availability along
with the integrity will decrease. The passive attacks will affect indirectly to utilize the main
system. So system resources should be attacked by the secondary attacks.
3.1. Active Attacks
Various kind of attacks can be situated in the active attack formation, those are:
3.1.1. Denial-Service
A large amount of solicitation with the flooding technology is the main reason for denial-
service attacks. The customer's misconfiguration is one of the main reasons for this kind of
attack.
3.1.2. Spoofing attacks
The IP address manipulation is one of the vital causes of these attacks. The service cannot
have detected this one as the unauthorized entry; IP, DNS and ARP are the main defenseless
against these attacks.
3.2. Passive Attack
Another name of this kind of attack is wiretapping attacks. Wireshark or Tcpdump may
create a huge problem in network trafficking. The network will be hampered with the
indiscriminate code; on the other hand, all packets are delivered to the tcpdump application. The
packet will be not identified, and the host will not configure. This kind of attack can be effaced
in the communicational path like Ethernet, Wi-Fi, USB, Cellular networks.
Organization is not secured for the hackers. They may attack from inside of the outside of the
organization. All of their actions may be situated as active or passive attacks (Deng 2011).
Operations and the system resources are disrupted by the active attacks. So the availability along
with the integrity will decrease. The passive attacks will affect indirectly to utilize the main
system. So system resources should be attacked by the secondary attacks.
3.1. Active Attacks
Various kind of attacks can be situated in the active attack formation, those are:
3.1.1. Denial-Service
A large amount of solicitation with the flooding technology is the main reason for denial-
service attacks. The customer's misconfiguration is one of the main reasons for this kind of
attack.
3.1.2. Spoofing attacks
The IP address manipulation is one of the vital causes of these attacks. The service cannot
have detected this one as the unauthorized entry; IP, DNS and ARP are the main defenseless
against these attacks.
3.2. Passive Attack
Another name of this kind of attack is wiretapping attacks. Wireshark or Tcpdump may
create a huge problem in network trafficking. The network will be hampered with the
indiscriminate code; on the other hand, all packets are delivered to the tcpdump application. The
packet will be not identified, and the host will not configure. This kind of attack can be effaced
in the communicational path like Ethernet, Wi-Fi, USB, Cellular networks.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
3.3. Types of hackers:
There are several types of hackers, those are:
3.3.1. A white hat hacker
The mainly ethical hackers are named as this name. They actually try to do some test in his
own company’s system to check the toughness of own security system. A contractual agreement
has been situated with these hackers, also the hacking will be done for good reason or make own
system strong.
3.3.2. A black hat hacker
If the hacking will be done with the bad impact and for personal gain this one named the
black hat hackers. They will hamper the data hugely, or make the system unstable for their
personal gain.
3.3.3. A script kiddie
The small understanding concept with the pre-packaged auto-generated contraption attacks
will be named as the script kiddie attacks. The attacker should have to be a non-master user or
outsider.
3.3.4. Hacktivist
Denial service attacks have been used in this kind of attack. Ideology, script, social, political
data should be hacked in this procedure.
3.3.5. Nation state
Digital operatives and agencies of the national state are included in this kind of activity.
3.3.6. Organized crime
Out of profit attacks are named as organized crime.
3.3.7. Bots
There are several types of hackers, those are:
3.3.1. A white hat hacker
The mainly ethical hackers are named as this name. They actually try to do some test in his
own company’s system to check the toughness of own security system. A contractual agreement
has been situated with these hackers, also the hacking will be done for good reason or make own
system strong.
3.3.2. A black hat hacker
If the hacking will be done with the bad impact and for personal gain this one named the
black hat hackers. They will hamper the data hugely, or make the system unstable for their
personal gain.
3.3.3. A script kiddie
The small understanding concept with the pre-packaged auto-generated contraption attacks
will be named as the script kiddie attacks. The attacker should have to be a non-master user or
outsider.
3.3.4. Hacktivist
Denial service attacks have been used in this kind of attack. Ideology, script, social, political
data should be hacked in this procedure.
3.3.5. Nation state
Digital operatives and agencies of the national state are included in this kind of activity.
3.3.6. Organized crime
Out of profit attacks are named as organized crime.
3.3.7. Bots
Automated software is used to do this kind of attack. The artificial intelligence is one of the
updated version of this kind of thought.
3.4. Attack Sources
Attacks can be happening outside or inside of the organization. If the attacks will be done
internally with unauthorized access, den it will break confidentiality and honesty. Outside attacks
can be happened by the client and providers or other people who will damage hugely.
The resource is one of the main assets of the company, which can be hampered by them. So it
can be said that the target amount of job can be situated according to their work to complete their
task. That is why the internal employee will also have needed to be honest to make the system
and organization protected. Also the after the attacks the system reaction should be perfect to
complete the system process with proper anti-virus and backup planning.
3.5. Security Measures
3.5.1. Firewalls
It is one of the strong barriers between the system and the unauthorized access to protect the
system. Inside with the outside, both are protected hugely via firewall, because the network has
to be passed through this firewall. There are several types of firewall that are used with various
thoughts to make the system better day by day. The local approaches can be used to make the
system better hugely. The firewall itself is one of the secure methods to complete the process of
the work. It will help to protect the system with the hardware and the software hugely. There is
mainly two types of firewalls that are used to protect the system, those are App-level firewalls,
and Circuit-level firewalls.
3.6. Network Servers overview
There are mainly two types of network that are used in the situation:
3.6.1. Apache web
The multi-threading concepts are used in the apache web server. This one is the worldwide
huge familiar web service. The HTTPS and HTTP both server are handled in the Apache server.
The customer and server communication can be maintained through the HTTP. A normal
connection procedure is used in this section. On the other hand, the port 443c will be always
updated version of this kind of thought.
3.4. Attack Sources
Attacks can be happening outside or inside of the organization. If the attacks will be done
internally with unauthorized access, den it will break confidentiality and honesty. Outside attacks
can be happened by the client and providers or other people who will damage hugely.
The resource is one of the main assets of the company, which can be hampered by them. So it
can be said that the target amount of job can be situated according to their work to complete their
task. That is why the internal employee will also have needed to be honest to make the system
and organization protected. Also the after the attacks the system reaction should be perfect to
complete the system process with proper anti-virus and backup planning.
3.5. Security Measures
3.5.1. Firewalls
It is one of the strong barriers between the system and the unauthorized access to protect the
system. Inside with the outside, both are protected hugely via firewall, because the network has
to be passed through this firewall. There are several types of firewall that are used with various
thoughts to make the system better day by day. The local approaches can be used to make the
system better hugely. The firewall itself is one of the secure methods to complete the process of
the work. It will help to protect the system with the hardware and the software hugely. There is
mainly two types of firewalls that are used to protect the system, those are App-level firewalls,
and Circuit-level firewalls.
3.6. Network Servers overview
There are mainly two types of network that are used in the situation:
3.6.1. Apache web
The multi-threading concepts are used in the apache web server. This one is the worldwide
huge familiar web service. The HTTPS and HTTP both server are handled in the Apache server.
The customer and server communication can be maintained through the HTTP. A normal
connection procedure is used in this section. On the other hand, the port 443c will be always
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
handled by the HTTPS. It is one of the verified connections. The encryption procedure will have
happened when the server will try to use this process. The customer end connection will be better
always. The authentication of the customer will be verified with the help of exchanging the
personal info and certificated. The same key will be utilizing to maintained the situation
appropriately. The login pages the hugely used in the HTTPS.
3.6.2. OpenSSH
It is one of the main versions of the SSH. The communication process is encoded as per the
requirement. The other devices like RSH, telnet will have delivered the password in unprotected
format. On the other hand, the Open SSH will give upper security to make the transfer more
projected. The customer connection should be managed with the SSDH components. On the
other hand, the Open SSH will use the open keys procedure to protect the password. The ELOG,
RSH and Telnet are undependable networking procedures. That is why each and every company
should like to manage the SSH in their system to make the protection stronger.
4. EXPERIMENTAL WORK AND ANALYSIS
4.1. Network Traffic Monitor (vnStat)
An entirely command line based platform, vnStat is used to keep a track on the bandwidth
utilization and network traffic network traffic in real-time basis. It is mainly used BSD and Linux
based systems.
happened when the server will try to use this process. The customer end connection will be better
always. The authentication of the customer will be verified with the help of exchanging the
personal info and certificated. The same key will be utilizing to maintained the situation
appropriately. The login pages the hugely used in the HTTPS.
3.6.2. OpenSSH
It is one of the main versions of the SSH. The communication process is encoded as per the
requirement. The other devices like RSH, telnet will have delivered the password in unprotected
format. On the other hand, the Open SSH will give upper security to make the transfer more
projected. The customer connection should be managed with the SSDH components. On the
other hand, the Open SSH will use the open keys procedure to protect the password. The ELOG,
RSH and Telnet are undependable networking procedures. That is why each and every company
should like to manage the SSH in their system to make the protection stronger.
4. EXPERIMENTAL WORK AND ANALYSIS
4.1. Network Traffic Monitor (vnStat)
An entirely command line based platform, vnStat is used to keep a track on the bandwidth
utilization and network traffic network traffic in real-time basis. It is mainly used BSD and Linux
based systems.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
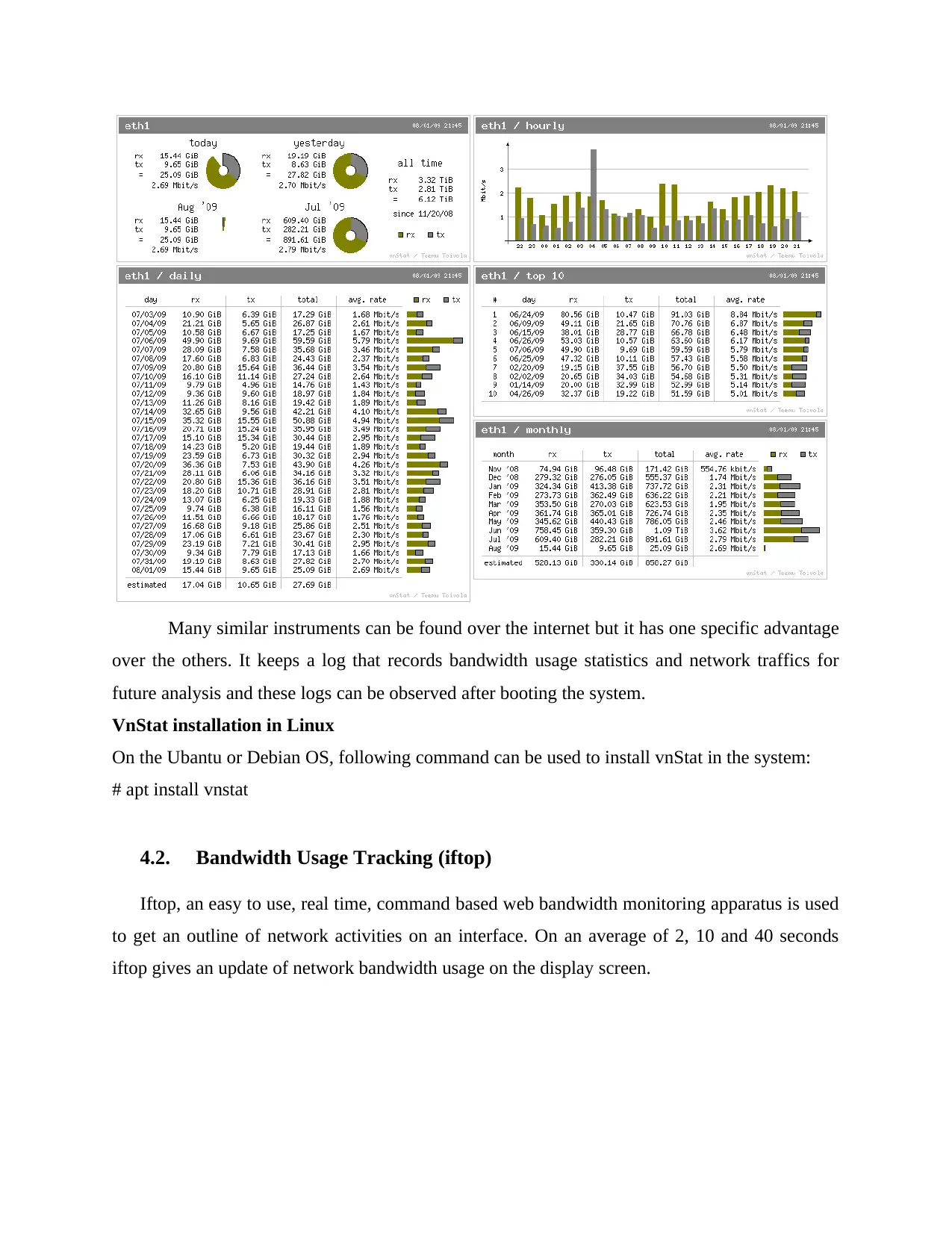
Many similar instruments can be found over the internet but it has one specific advantage
over the others. It keeps a log that records bandwidth usage statistics and network traffics for
future analysis and these logs can be observed after booting the system.
VnStat installation in Linux
On the Ubantu or Debian OS, following command can be used to install vnStat in the system:
# apt install vnstat
4.2. Bandwidth Usage Tracking (iftop)
Iftop, an easy to use, real time, command based web bandwidth monitoring apparatus is used
to get an outline of network activities on an interface. On an average of 2, 10 and 40 seconds
iftop gives an update of network bandwidth usage on the display screen.
over the others. It keeps a log that records bandwidth usage statistics and network traffics for
future analysis and these logs can be observed after booting the system.
VnStat installation in Linux
On the Ubantu or Debian OS, following command can be used to install vnStat in the system:
# apt install vnstat
4.2. Bandwidth Usage Tracking (iftop)
Iftop, an easy to use, real time, command based web bandwidth monitoring apparatus is used
to get an outline of network activities on an interface. On an average of 2, 10 and 40 seconds
iftop gives an update of network bandwidth usage on the display screen.
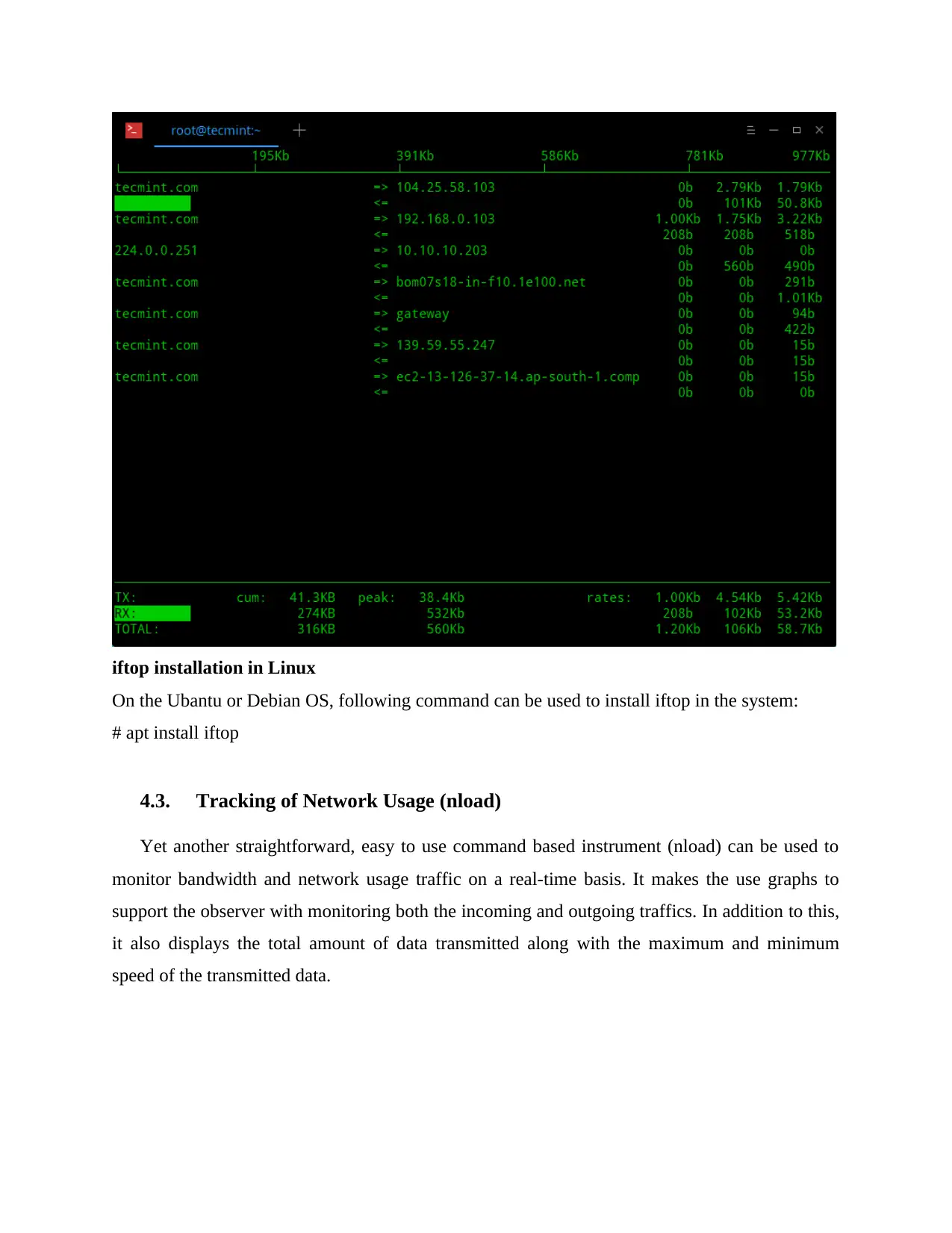
iftop installation in Linux
On the Ubantu or Debian OS, following command can be used to install iftop in the system:
# apt install iftop
4.3. Tracking of Network Usage (nload)
Yet another straightforward, easy to use command based instrument (nload) can be used to
monitor bandwidth and network usage traffic on a real-time basis. It makes the use graphs to
support the observer with monitoring both the incoming and outgoing traffics. In addition to this,
it also displays the total amount of data transmitted along with the maximum and minimum
speed of the transmitted data.
On the Ubantu or Debian OS, following command can be used to install iftop in the system:
# apt install iftop
4.3. Tracking of Network Usage (nload)
Yet another straightforward, easy to use command based instrument (nload) can be used to
monitor bandwidth and network usage traffic on a real-time basis. It makes the use graphs to
support the observer with monitoring both the incoming and outgoing traffics. In addition to this,
it also displays the total amount of data transmitted along with the maximum and minimum
speed of the transmitted data.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 23
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.
![Server Installation and Management Project - [Course Name] [Semester]](/_next/image/?url=https%3A%2F%2Fdesklib.com%2Fmedia%2Fimages%2Fkl%2F1a2c109da7e14c78a6b2e8ca6dd132c5.jpg&w=256&q=75)




