BSBITU305 - Marks & Spencer Online Transaction Process and Security
VerifiedAdded on 2023/06/12
|12
|1247
|483
Report
AI Summary
This report provides a detailed analysis of online transactions, using Marks & Spencer as a case study to illustrate the shopping process and security measures. It covers various aspects of online security, including browsers, cookies, e-security, firewalls, passwords, phishing, and spyware. The report also outlines methods for protecting computers and identities online, emphasizing the importance of complex passwords, secure website access, and safe online shopping practices. Furthermore, it identifies potential red flags in online advertisements that may indicate scams and offers guidance on avoiding identity theft and financial fraud. Desklib provides access to similar solved assignments and study resources for students.

Running head: ONLINE TRANSACTION
Online Transaction
Name of the student
Name of the University
Author Note:
Online Transaction
Name of the student
Name of the University
Author Note:
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
1ONLINE TRANSACTION
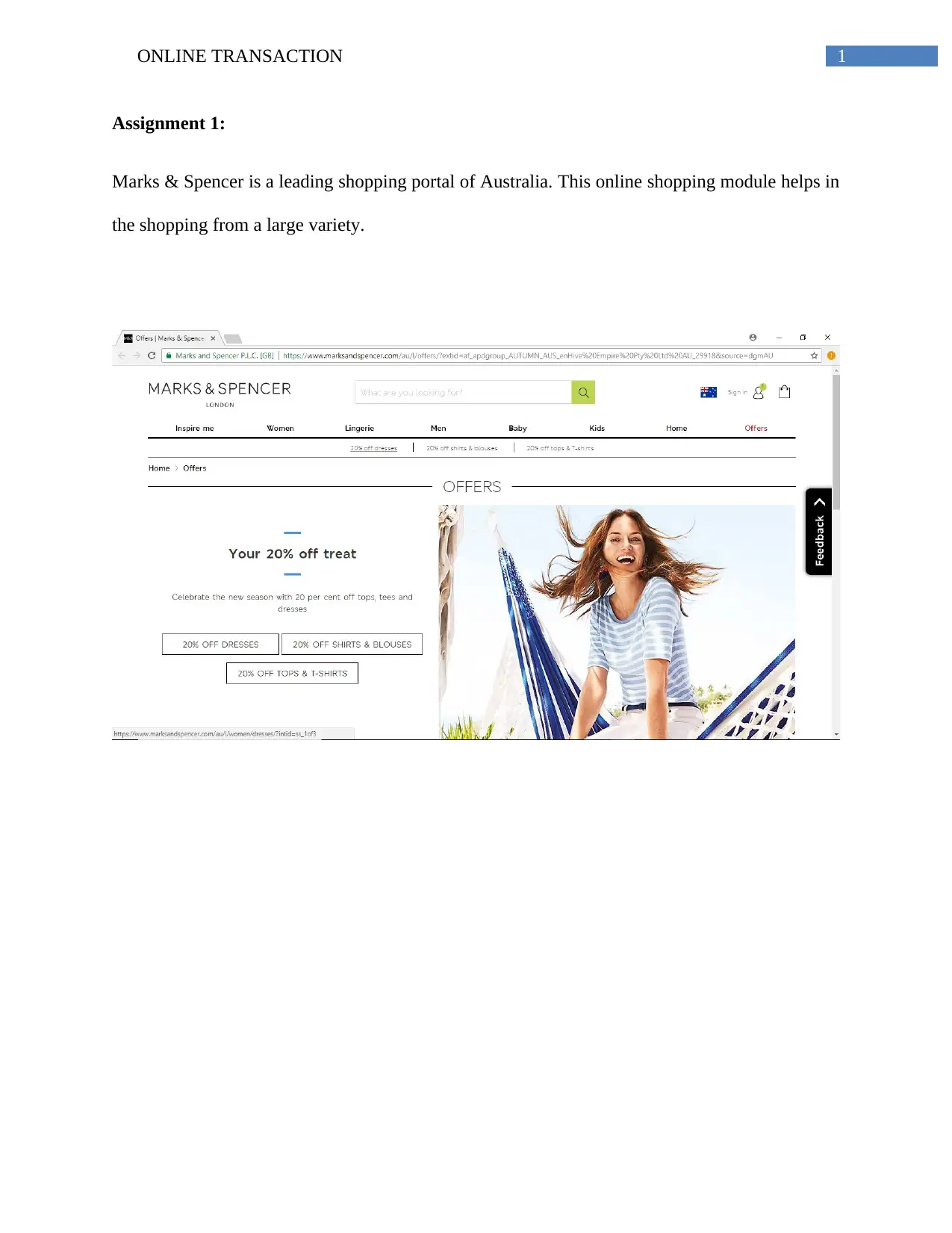
Assignment 1:
Marks & Spencer is a leading shopping portal of Australia. This online shopping module helps in
the shopping from a large variety.
Assignment 1:
Marks & Spencer is a leading shopping portal of Australia. This online shopping module helps in
the shopping from a large variety.
2ONLINE TRANSACTION
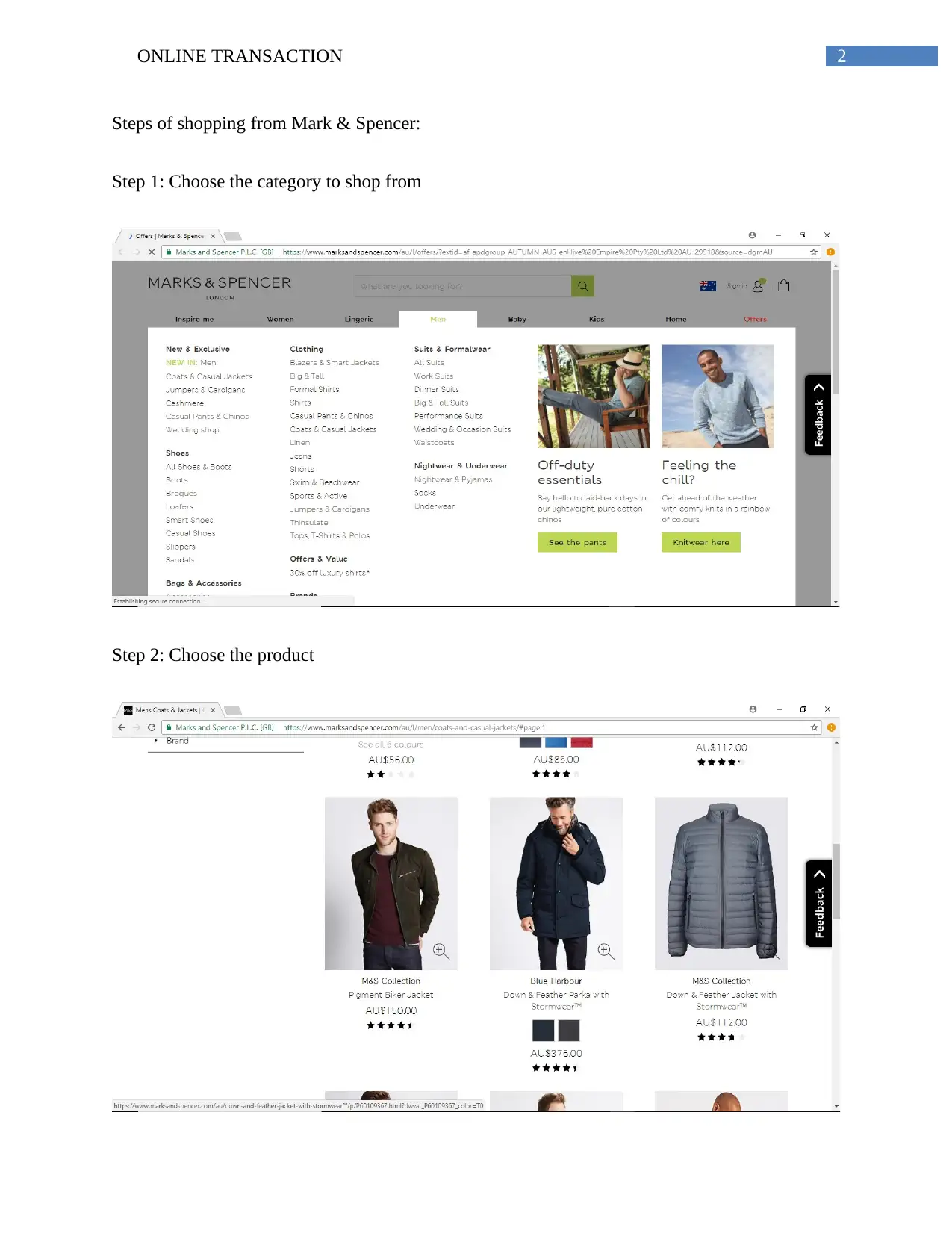
Steps of shopping from Mark & Spencer:
Step 1: Choose the category to shop from
Step 2: Choose the product
Steps of shopping from Mark & Spencer:
Step 1: Choose the category to shop from
Step 2: Choose the product
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
3ONLINE TRANSACTION
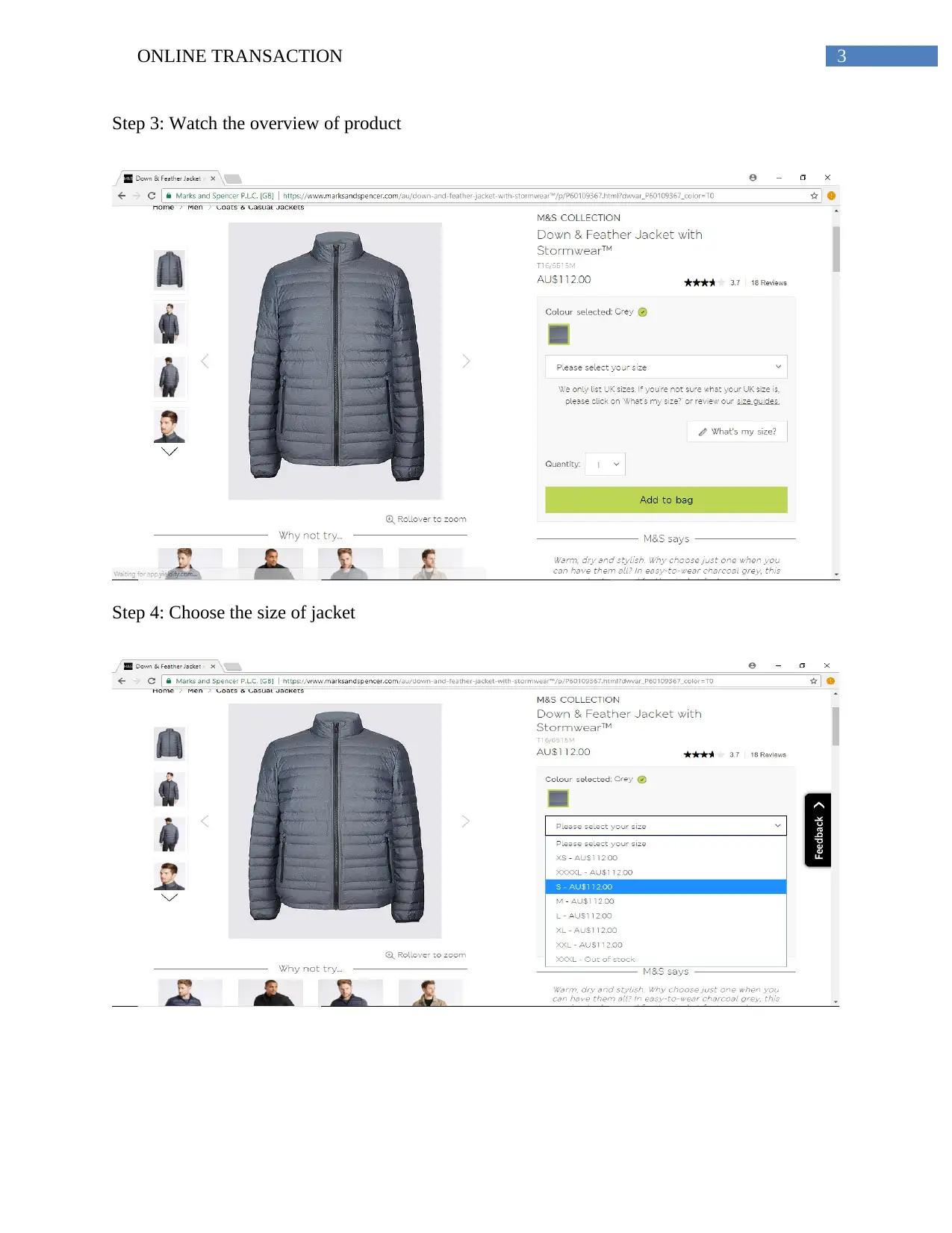
Step 3: Watch the overview of product
Step 4: Choose the size of jacket
Step 3: Watch the overview of product
Step 4: Choose the size of jacket
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
4ONLINE TRANSACTION
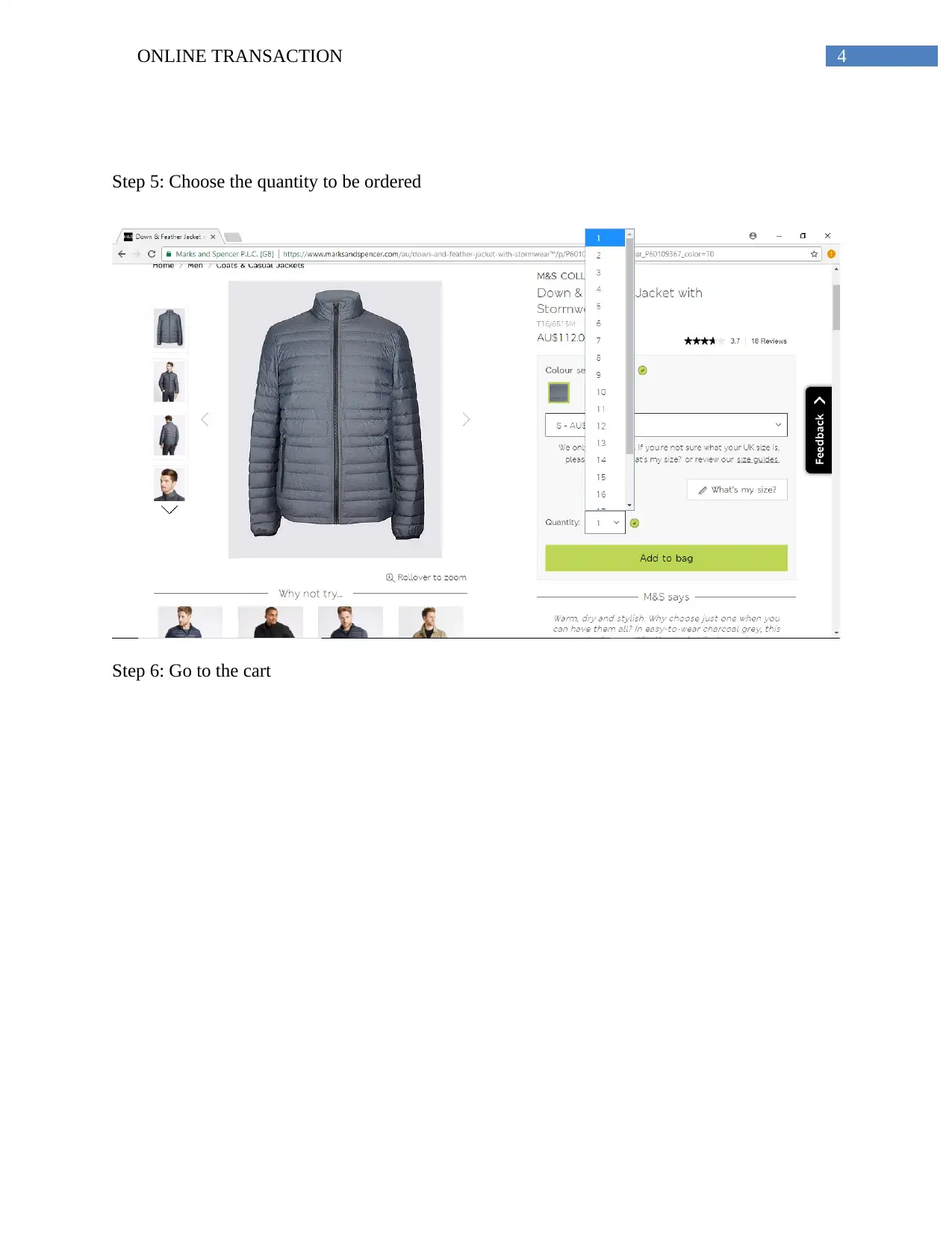
Step 5: Choose the quantity to be ordered
Step 6: Go to the cart
Step 5: Choose the quantity to be ordered
Step 6: Go to the cart

5ONLINE TRANSACTION
Step 7: Finally give the details to make the online payment
Step 7: Finally give the details to make the online payment
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide

6ONLINE TRANSACTION
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
7ONLINE TRANSACTION
Assignment 2:
1. a. Browser: The browser is a software that is used to search and find solutions to the
different questions
b. Cookies: The cookies are responsible for the identification of the users and the
preparation of the customized web pages. The access of the websites using cookies
require the user to entering of the details.
c. e- security: The e- security is the phenomenon, which can be used for the protection of
the confidential information by the use of electronic method or through online mode.
d. Firewall: The installation of the firewall helps in the detection and prevention of the
attacks that may take place on the systems of an organization
e. Password: The password is a code that is used to gain access of a portal or confidential
information.
f. Phishing: Phishing involves the online malicious attacks that take place on the systems
that carry out the online transactions or online payment methods.
g. Spyware: The use of the spyware helps the user to obtain the information that is
coveted. This coveted information is obtained by the transmission of the coveted data
directly from the hard drive. The use of spyware can be made for the obtaining of the
information about another computer.
Assignment 2:
1. a. Browser: The browser is a software that is used to search and find solutions to the
different questions
b. Cookies: The cookies are responsible for the identification of the users and the
preparation of the customized web pages. The access of the websites using cookies
require the user to entering of the details.
c. e- security: The e- security is the phenomenon, which can be used for the protection of
the confidential information by the use of electronic method or through online mode.
d. Firewall: The installation of the firewall helps in the detection and prevention of the
attacks that may take place on the systems of an organization
e. Password: The password is a code that is used to gain access of a portal or confidential
information.
f. Phishing: Phishing involves the online malicious attacks that take place on the systems
that carry out the online transactions or online payment methods.
g. Spyware: The use of the spyware helps the user to obtain the information that is
coveted. This coveted information is obtained by the transmission of the coveted data
directly from the hard drive. The use of spyware can be made for the obtaining of the
information about another computer.
8ONLINE TRANSACTION
2. The ways in which the computer may be protected are:
Use of firewall: The use of firewall contributes in keeping the system secure from the
malicious outside attacks. The use of the firewall helps in the prevention of the cyber
crimes. Installation of firewall contribute in detection of any form of suspicious activity
in the system or the network of an individual or an organization.
Installation of anti- virus software: The installation of anti- virus helps in the prevention
of any form of attack that may occur from the virus. The virus may attack through
visiting of the various websites.
Encryption of information: All the information and the other confidential information
such as the passwords and personal details should be encrypted. This helps in the
protection of the important and confidential information of the user.
3. The ways in which one can stay smart online are:
Use of complex passwords: The use of complex passwords helps in the keeping the
system safe. The use of the complex passwords prevents the hackers from cracking the
password easily. The passwords should also be changed from time to time. This will
restrict the hackers from accessing the systems.
Accessing sites efficiently: There should be a check on the websites that one visits and
the links that one visits as the visiting of these websites may lead to the attack from the
various viruses. There are links that one visits unknowingly and due to the presence of
the keyloggers in the different sites there may be attack on the system of the individual.
4. The ways in which one can stay smart while shopping online:
2. The ways in which the computer may be protected are:
Use of firewall: The use of firewall contributes in keeping the system secure from the
malicious outside attacks. The use of the firewall helps in the prevention of the cyber
crimes. Installation of firewall contribute in detection of any form of suspicious activity
in the system or the network of an individual or an organization.
Installation of anti- virus software: The installation of anti- virus helps in the prevention
of any form of attack that may occur from the virus. The virus may attack through
visiting of the various websites.
Encryption of information: All the information and the other confidential information
such as the passwords and personal details should be encrypted. This helps in the
protection of the important and confidential information of the user.
3. The ways in which one can stay smart online are:
Use of complex passwords: The use of complex passwords helps in the keeping the
system safe. The use of the complex passwords prevents the hackers from cracking the
password easily. The passwords should also be changed from time to time. This will
restrict the hackers from accessing the systems.
Accessing sites efficiently: There should be a check on the websites that one visits and
the links that one visits as the visiting of these websites may lead to the attack from the
various viruses. There are links that one visits unknowingly and due to the presence of
the keyloggers in the different sites there may be attack on the system of the individual.
4. The ways in which one can stay smart while shopping online:
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
9ONLINE TRANSACTION
Be safe while making payment: Only those websites should be used for the online
shopping which are certified and while making the payments the details should be give
carefully. If any of suspicious activities is detected then one should not proceed with the
payment. There are large numbers of fraud that occur in the name of online shopping.
Accessing of right form of information: While the checking of the various products one
should be careful with the links that one visits. There are a number of advertisements that
are associated in the e shop applications, clicking of which can lead to the attack of the
virus and other form of attacks.
5. The ways to protect identity online:
In order to protect the loss of identity, there are certain steps that needs to be taken. People using
the range of online portals should limit the data and information that can be shared. Many of the
hackers may use this information in the wrong for the accessing of the confidential information.
Enough protection should be given to the details that is shared. There are various online portals
such as that of online shopping models, which ask for the various personal details of the
customer. While entering these details one should check if the sites where the details are being
entered are certified and can be trusted.
6. In this website advertisement, the red flags that are present are that there may be identity loss
as the website asks for the various details regarding the user. The website advertisement is
intended to attracting the different people towards this advertisement. Many people would be
filling the form with the expectation of winning the reward. The organization is not certified and
the advertisement is just given in order to attract the customers. The other red flag may occur
while making the payment. There may be stealing of the personal information in the process of
Be safe while making payment: Only those websites should be used for the online
shopping which are certified and while making the payments the details should be give
carefully. If any of suspicious activities is detected then one should not proceed with the
payment. There are large numbers of fraud that occur in the name of online shopping.
Accessing of right form of information: While the checking of the various products one
should be careful with the links that one visits. There are a number of advertisements that
are associated in the e shop applications, clicking of which can lead to the attack of the
virus and other form of attacks.
5. The ways to protect identity online:
In order to protect the loss of identity, there are certain steps that needs to be taken. People using
the range of online portals should limit the data and information that can be shared. Many of the
hackers may use this information in the wrong for the accessing of the confidential information.
Enough protection should be given to the details that is shared. There are various online portals
such as that of online shopping models, which ask for the various personal details of the
customer. While entering these details one should check if the sites where the details are being
entered are certified and can be trusted.
6. In this website advertisement, the red flags that are present are that there may be identity loss
as the website asks for the various details regarding the user. The website advertisement is
intended to attracting the different people towards this advertisement. Many people would be
filling the form with the expectation of winning the reward. The organization is not certified and
the advertisement is just given in order to attract the customers. The other red flag may occur
while making the payment. There may be stealing of the personal information in the process of
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
10ONLINE TRANSACTION
taking the payment of the customer. The organization asks for making a one- time payment and
in this process there may be the stealing of the bank details of the customer.
7. Three red flags indicating scam:
If any of the advertisements asks for the entering of the personal details in order to access
the portal. This is a hoax at times as the sites do not generally ask for these details in
order to access the portal.
Any of the organizations or the bank staff asking for the bank details of the customers for
the purchase of the products. No bank officials ask for personal details such as pin
numbers or CVV.
Hoax may be said to be present in the link or advertisement that provide attractive offers.
taking the payment of the customer. The organization asks for making a one- time payment and
in this process there may be the stealing of the bank details of the customer.
7. Three red flags indicating scam:
If any of the advertisements asks for the entering of the personal details in order to access
the portal. This is a hoax at times as the sites do not generally ask for these details in
order to access the portal.
Any of the organizations or the bank staff asking for the bank details of the customers for
the purchase of the products. No bank officials ask for personal details such as pin
numbers or CVV.
Hoax may be said to be present in the link or advertisement that provide attractive offers.
11ONLINE TRANSACTION
References:
Lambert, S.L., 2017. Auto Accessories, Inc.: An Educational Case on Online Transaction
Processing (OLTP) and Controls as Compared to Batch Processing and Controls. Journal of
Emerging Technologies in Accounting, 14(2), pp.59-81.
Zhong, S. and Zhang, M., 2015, April. Research on the personal privacy information protection
problem based on computer security technology. In 2015 International Conference on
Automation, Mechanical Control and Computational Engineering. Atlantis Press.
References:
Lambert, S.L., 2017. Auto Accessories, Inc.: An Educational Case on Online Transaction
Processing (OLTP) and Controls as Compared to Batch Processing and Controls. Journal of
Emerging Technologies in Accounting, 14(2), pp.59-81.
Zhong, S. and Zhang, M., 2015, April. Research on the personal privacy information protection
problem based on computer security technology. In 2015 International Conference on
Automation, Mechanical Control and Computational Engineering. Atlantis Press.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 12
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





