Insecurities and Vulnerabilities in Mobile Devices: A Report
VerifiedAdded on 2021/04/21
|9
|1641
|120
Report
AI Summary
This report delves into the crucial topic of mobile device insecurities and vulnerabilities, examining the increasing prevalence of mobile devices and the associated cyber threats. It begins by outlining the benefits of mobile technology while highlighting the significant security risks, including data loss (both physical and application misuse) and various forms of cyber-attacks. The research aims to identify these vulnerabilities, analyze their impact on users, and propose effective mitigation strategies. The report's structure encompasses an introduction, literature review, research methodology (qualitative with thematic analysis of secondary data), data findings and analysis, and conclusions with recommendations. Key areas of focus include data encryption, wireless technology vulnerabilities, and the impact of these threats on businesses and individual users. The report emphasizes the importance of understanding and addressing these challenges to protect mobile users and organizations in an increasingly connected world. The report also includes a detailed literature review, research methodology, data findings, and conclusions with recommendations. The report also uses different figures to make the topic easier to understand.

Running head: MOBILE DEVICE INSECURITIES AND VULNERABILITIES
Mobile Device Insecurities and vulnerabilities
Name of the Student
Name of the University
Author’s Note
Mobile Device Insecurities and vulnerabilities
Name of the Student
Name of the University
Author’s Note
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
2
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
Summary
This paper will discuss the insecurities and vulnerabilities involved in the mobile devices.
Different benefits of the mobile devices will be discussed in the research. The current trend and
statistics about the use of mobile devices and cyber-attacks will be provided in the study. The
aim of the research is to identify various insecurities and vulnerabilities in the mobile devices.
The objectives and research questions will be discussed in the study. Benefits and limitations of
the mobile device technology will be provided in the research. The main problem of the
discussed in the paper is insecurities and vulnerabilities of the mobile devices. Security risks and
threats involved in the mobile devices have been identified in the research paper that might help
in mitigating the risks in the mobile devices. However, there are two types of mobile data loss
including physical loss and misuse of mobile applications. Mobile devices have been used almost
by every individual on this planet.
The use of mobile devices has been increased on a daily basis. There have been many
evolutions in the technology of the mobile phones. In the last two decades, significant
technology has been integrated into mobile phones in the market. The demand for mobile phones
has become exponential in the global market (Barcena & Wueest, 2015). These advances in the
technologies have extended the virtual limits of organizations. The literature review will focus on
the existing knowledge related to the mobile device risks and vulnerabilities. This research will
follow the qualitative methodology and data collection method. Data will be collected from
secondary sources including online journals, reports, books and government databases. Thematic
analysis will be conducted to analyze the secondary data. The expected outcomes might fulfil the
research objectives and questions initiated in the study.
Keywords: Mobile Security, Virtual Private Network (VPN) and Encryption
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
Summary
This paper will discuss the insecurities and vulnerabilities involved in the mobile devices.
Different benefits of the mobile devices will be discussed in the research. The current trend and
statistics about the use of mobile devices and cyber-attacks will be provided in the study. The
aim of the research is to identify various insecurities and vulnerabilities in the mobile devices.
The objectives and research questions will be discussed in the study. Benefits and limitations of
the mobile device technology will be provided in the research. The main problem of the
discussed in the paper is insecurities and vulnerabilities of the mobile devices. Security risks and
threats involved in the mobile devices have been identified in the research paper that might help
in mitigating the risks in the mobile devices. However, there are two types of mobile data loss
including physical loss and misuse of mobile applications. Mobile devices have been used almost
by every individual on this planet.
The use of mobile devices has been increased on a daily basis. There have been many
evolutions in the technology of the mobile phones. In the last two decades, significant
technology has been integrated into mobile phones in the market. The demand for mobile phones
has become exponential in the global market (Barcena & Wueest, 2015). These advances in the
technologies have extended the virtual limits of organizations. The literature review will focus on
the existing knowledge related to the mobile device risks and vulnerabilities. This research will
follow the qualitative methodology and data collection method. Data will be collected from
secondary sources including online journals, reports, books and government databases. Thematic
analysis will be conducted to analyze the secondary data. The expected outcomes might fulfil the
research objectives and questions initiated in the study.
Keywords: Mobile Security, Virtual Private Network (VPN) and Encryption
3
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
Structure of the Study
Mobile securities have been the essential topic for research in present days. Various
studies have been done on the insecurities and vulnerabilities of the mobile devices. Major
vulnerabilities in the mobile devices include encrypting of data and information stored in the
mobile device. Wireless technology used in the mobile device for transmission of data and
signals have been creating major vulnerabilities to the mobile device.
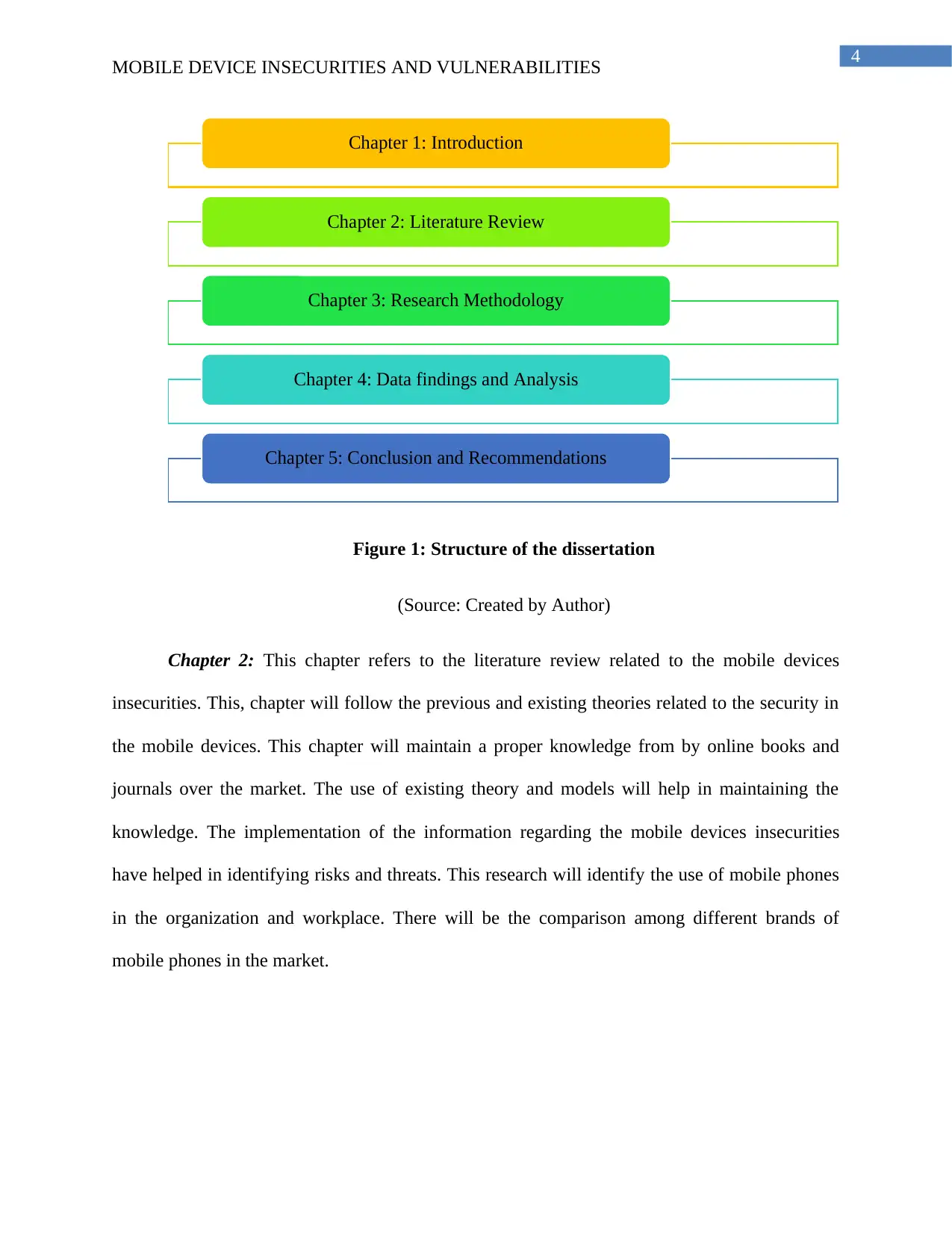
The paper will be structured in five different chapters including Introduction, Literature
Review, Research Methodology, Data Findings and Analysis and Conclusion and
Recommendations.
Chapter 1: This chapter discusses about the basic information about the insecurities and
vulnerabilities in the mobile devices. This chapter will discusses about various information
related ti the mobile devices vulnerabilities. Therefore, the aims and objectives of the research
will be initiated in this chapter. The use of different knowledge about the mobile device
insecurities will be discussed in this chapter. This chapter introduces the mobile devices
insecurities and vulnerabilities in the market. This paper will focus on the cyber-attacks and
other threats to mobile devices. This research will explain the impact of the threats and risks on
the business organizations and mobile users in the market. There will be proper strategies
recommended for mitigating these challenges in the context.
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
Structure of the Study
Mobile securities have been the essential topic for research in present days. Various
studies have been done on the insecurities and vulnerabilities of the mobile devices. Major
vulnerabilities in the mobile devices include encrypting of data and information stored in the
mobile device. Wireless technology used in the mobile device for transmission of data and
signals have been creating major vulnerabilities to the mobile device.
The paper will be structured in five different chapters including Introduction, Literature
Review, Research Methodology, Data Findings and Analysis and Conclusion and
Recommendations.
Chapter 1: This chapter discusses about the basic information about the insecurities and
vulnerabilities in the mobile devices. This chapter will discusses about various information
related ti the mobile devices vulnerabilities. Therefore, the aims and objectives of the research
will be initiated in this chapter. The use of different knowledge about the mobile device
insecurities will be discussed in this chapter. This chapter introduces the mobile devices
insecurities and vulnerabilities in the market. This paper will focus on the cyber-attacks and
other threats to mobile devices. This research will explain the impact of the threats and risks on
the business organizations and mobile users in the market. There will be proper strategies
recommended for mitigating these challenges in the context.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
4
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
Figure 1: Structure of the dissertation
(Source: Created by Author)
Chapter 2: This chapter refers to the literature review related to the mobile devices
insecurities. This, chapter will follow the previous and existing theories related to the security in
the mobile devices. This chapter will maintain a proper knowledge from by online books and
journals over the market. The use of existing theory and models will help in maintaining the
knowledge. The implementation of the information regarding the mobile devices insecurities
have helped in identifying risks and threats. This research will identify the use of mobile phones
in the organization and workplace. There will be the comparison among different brands of
mobile phones in the market.
Chapter 1: Introduction
Chapter 2: Literature Review
Chapter 3: Research Methodology
Chapter 4: Data findings and Analysis
Chapter 5: Conclusion and Recommendations
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
Figure 1: Structure of the dissertation
(Source: Created by Author)
Chapter 2: This chapter refers to the literature review related to the mobile devices
insecurities. This, chapter will follow the previous and existing theories related to the security in
the mobile devices. This chapter will maintain a proper knowledge from by online books and
journals over the market. The use of existing theory and models will help in maintaining the
knowledge. The implementation of the information regarding the mobile devices insecurities
have helped in identifying risks and threats. This research will identify the use of mobile phones
in the organization and workplace. There will be the comparison among different brands of
mobile phones in the market.
Chapter 1: Introduction
Chapter 2: Literature Review
Chapter 3: Research Methodology
Chapter 4: Data findings and Analysis
Chapter 5: Conclusion and Recommendations
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
5
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
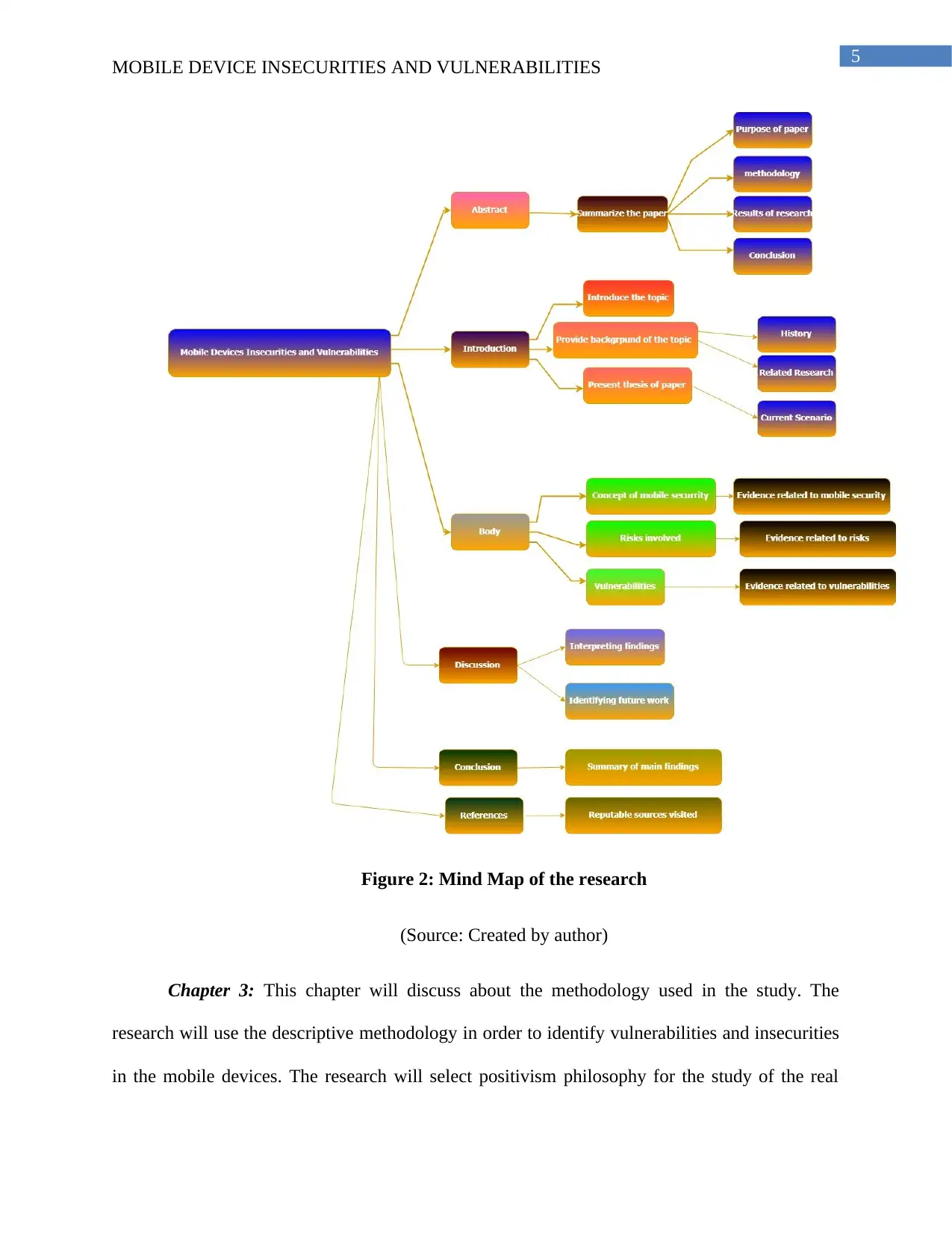
Figure 2: Mind Map of the research
(Source: Created by author)
Chapter 3: This chapter will discuss about the methodology used in the study. The
research will use the descriptive methodology in order to identify vulnerabilities and insecurities
in the mobile devices. The research will select positivism philosophy for the study of the real
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
Figure 2: Mind Map of the research
(Source: Created by author)
Chapter 3: This chapter will discuss about the methodology used in the study. The
research will use the descriptive methodology in order to identify vulnerabilities and insecurities
in the mobile devices. The research will select positivism philosophy for the study of the real
6
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
facts of the mobile securities. There will be some limitations in the collection data from
secondary sources. Different journals might be of a paid version that will not be accessed.
Several journals will not be in the context of the mobile insecurities and vulnerabilities (Lewis,
2015). Therefore, these journals will not be taken for data collection technique. This research
will follow all the ethical norms and values. Data and information used in the research will not
be shared with anyone. This research will follow the Data Protection Act 1998 and personal
information will not be shared with anyone (Flick, 2015).
Chapter 4: This chapter will discuss about the findings of data and its analysis. The
research will collect data from secondary data sources including online journals, books, reports,
articles and government databases. Various journals after the year 2012 will be taken for data
collection, which will provide the latest information related to the mobile device insecurities and
vulnerabilities (Mackey & Gass, 2015). Data will be analyzed by using qualitative data analysis
method. Three themes will be created based on the research objectives and research questions.
Thematic analysis will help in analyzing the data collected from the online journals and
government databases.
Chapter 5: This chapter will help in concluding the whole study. This chapter will focus on the
findings of the research and help in linking with the objectives of the research. The use of
various theories and models in the research will be analyzed. The data findings and outcomes
will be thematically analyzed and the findings will be analyzed. There will be recommendations
provided in the chapter that might help in mitigating the mobile devices insecurities and
vulnerabilities. The future work in this research topic will be provided in the chapter.
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
facts of the mobile securities. There will be some limitations in the collection data from
secondary sources. Different journals might be of a paid version that will not be accessed.
Several journals will not be in the context of the mobile insecurities and vulnerabilities (Lewis,
2015). Therefore, these journals will not be taken for data collection technique. This research
will follow all the ethical norms and values. Data and information used in the research will not
be shared with anyone. This research will follow the Data Protection Act 1998 and personal
information will not be shared with anyone (Flick, 2015).
Chapter 4: This chapter will discuss about the findings of data and its analysis. The
research will collect data from secondary data sources including online journals, books, reports,
articles and government databases. Various journals after the year 2012 will be taken for data
collection, which will provide the latest information related to the mobile device insecurities and
vulnerabilities (Mackey & Gass, 2015). Data will be analyzed by using qualitative data analysis
method. Three themes will be created based on the research objectives and research questions.
Thematic analysis will help in analyzing the data collected from the online journals and
government databases.
Chapter 5: This chapter will help in concluding the whole study. This chapter will focus on the
findings of the research and help in linking with the objectives of the research. The use of
various theories and models in the research will be analyzed. The data findings and outcomes
will be thematically analyzed and the findings will be analyzed. There will be recommendations
provided in the chapter that might help in mitigating the mobile devices insecurities and
vulnerabilities. The future work in this research topic will be provided in the chapter.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
7
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
1.3 Research Aim, Objectives and Questions
The aim of the research is to identify the insecurities and vulnerabilities in mobile
devices.
The objectives of the research are as follows:
To identify the insecurities and vulnerabilities in mobile devices
To analyze the impact of these vulnerabilities and insecurities on mobile users
To recommend strategies for mitigating these challenges and vulnerabilities in mobile
users
The research questions are as follows:
What are the insecurities and vulnerabilities in mobile devices?
What is the impact of these vulnerabilities and insecurities on mobile users?
How to mitigate these challenges and vulnerabilities in mobile users?
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
1.3 Research Aim, Objectives and Questions
The aim of the research is to identify the insecurities and vulnerabilities in mobile
devices.
The objectives of the research are as follows:
To identify the insecurities and vulnerabilities in mobile devices
To analyze the impact of these vulnerabilities and insecurities on mobile users
To recommend strategies for mitigating these challenges and vulnerabilities in mobile
users
The research questions are as follows:
What are the insecurities and vulnerabilities in mobile devices?
What is the impact of these vulnerabilities and insecurities on mobile users?
How to mitigate these challenges and vulnerabilities in mobile users?
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
8
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
References
Ahmad, S., Haamid, A. L., Qazi, Z. A., Zhou, Z., Benson, T., & Qazi, I. A. (2016, November). A
view from the other side: Understanding mobile phone characteristics in the developing
world. In Proceedings of the 2016 Internet Measurement Conference (pp. 319-325).
ACM.
Barcena, M. B., & Wueest, C. (2015). Insecurity in the Internet of Things. Security Response,
Symantec.
Do, Q., Martini, B., & Choo, K. K. R. (2017). Is the data on your wearable device secure? An
Android Wear smartwatch case study. Software: Practice and Experience, 47(3), 391-
403.
Flick, U. (2015). Introducing research methodology: A beginner's guide to doing a research
project. Sage.
Jadhav, S., Oh, T., Kim, Y. H., & Kim, J. N. (2015, July). Mobile device penetration testing
framework and platform for the mobile device security course. In Advanced
Communication Technology (ICACT), 2015 17th International Conference on(pp. 675-
680). IEEE.
Khan, J., Abbas, H., & Al-Muhtadi, J. (2015). Survey on Mobile User's Data Privacy Threats and
Defense Mechanisms. Procedia Computer Science, 56, 376-383.
Lewis, S. (2015). Qualitative inquiry and research design: Choosing among five
approaches. Health promotion practice, 16(4), 473-475.
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
References
Ahmad, S., Haamid, A. L., Qazi, Z. A., Zhou, Z., Benson, T., & Qazi, I. A. (2016, November). A
view from the other side: Understanding mobile phone characteristics in the developing
world. In Proceedings of the 2016 Internet Measurement Conference (pp. 319-325).
ACM.
Barcena, M. B., & Wueest, C. (2015). Insecurity in the Internet of Things. Security Response,
Symantec.
Do, Q., Martini, B., & Choo, K. K. R. (2017). Is the data on your wearable device secure? An
Android Wear smartwatch case study. Software: Practice and Experience, 47(3), 391-
403.
Flick, U. (2015). Introducing research methodology: A beginner's guide to doing a research
project. Sage.
Jadhav, S., Oh, T., Kim, Y. H., & Kim, J. N. (2015, July). Mobile device penetration testing
framework and platform for the mobile device security course. In Advanced
Communication Technology (ICACT), 2015 17th International Conference on(pp. 675-
680). IEEE.
Khan, J., Abbas, H., & Al-Muhtadi, J. (2015). Survey on Mobile User's Data Privacy Threats and
Defense Mechanisms. Procedia Computer Science, 56, 376-383.
Lewis, S. (2015). Qualitative inquiry and research design: Choosing among five
approaches. Health promotion practice, 16(4), 473-475.
9
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
Mackey, A., & Gass, S. M. (2015). Second language research: Methodology and design.
Routledge.
Raj, N., Bharti, P., & Thakur, S. (2015, April). Vulnerabilities, challenges and threats in securing
mobile ad-hoc network. In Communication Systems and Network Technologies (CSNT),
2015 Fifth International Conference on (pp. 771-775). IEEE.
Sinha, A. (2015). U.S. Patent No. 9,119,017. Washington, DC: U.S. Patent and Trademark
Office.\
Taylor, S. J., Bogdan, R., & DeVault, M. (2015). Introduction to qualitative research methods: A
guidebook and resource. John Wiley & Sons.
MOBILE DEVICE INSECURITIES AND VULNERABILITIES
Mackey, A., & Gass, S. M. (2015). Second language research: Methodology and design.
Routledge.
Raj, N., Bharti, P., & Thakur, S. (2015, April). Vulnerabilities, challenges and threats in securing
mobile ad-hoc network. In Communication Systems and Network Technologies (CSNT),
2015 Fifth International Conference on (pp. 771-775). IEEE.
Sinha, A. (2015). U.S. Patent No. 9,119,017. Washington, DC: U.S. Patent and Trademark
Office.\
Taylor, S. J., Bogdan, R., & DeVault, M. (2015). Introduction to qualitative research methods: A
guidebook and resource. John Wiley & Sons.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 9
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.




