Analyzing Cybercrime Threats in Modern Digital Business Environments
VerifiedAdded on 2020/05/28
|14
|2665
|87
AI Summary
In an era where digital presence is crucial for business operations, the threat of cybercrime has significantly increased. Modern businesses face various cyber threats such as ransomware, DDoS attacks, insider threats, mobile malware, and hacktivism. High-profile companies like HBO, Yahoo, BBC, and Sony have been victims, underscoring the importance of robust cybersecurity measures. To combat these threats effectively, firms must upgrade their security policies to include data encryption, physical server protection, and secure password practices among others. The paper emphasizes the necessity for businesses to invest in comprehensive cybersecurity strategies to safeguard their operations and customer information from potential cyber attacks.

Running head: RESEARCH
Research Methodology 2
Institution Name
Student Name
Contents
Research Methodology 2
Institution Name
Student Name
Contents
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
RESEARCH 2
Contents.......................................................................................................................................................2
Introduction.................................................................................................................................................3
Project Objectives........................................................................................................................................3
Project Scope...............................................................................................................................................3
Literature Review........................................................................................................................................4
Justification.............................................................................................................................................5
Literature problems.................................................................................................................................6
Gaps........................................................................................................................................................6
Opportunities...........................................................................................................................................6
Hypothesis...............................................................................................................................................6
Research Questions.....................................................................................................................................6
Research Design and Methodology.............................................................................................................6
Time Schedule.............................................................................................................................................8
Conclusion...................................................................................................................................................9
References.................................................................................................................................................10
Appendix...................................................................................................................................................11
Introduction
The introduction of digital technology has resulted in a rise in the use of smartphones as well as
online services used by people and corporations. The use of smartphones has made it easier to
2 | P a g e
Contents.......................................................................................................................................................2
Introduction.................................................................................................................................................3
Project Objectives........................................................................................................................................3
Project Scope...............................................................................................................................................3
Literature Review........................................................................................................................................4
Justification.............................................................................................................................................5
Literature problems.................................................................................................................................6
Gaps........................................................................................................................................................6
Opportunities...........................................................................................................................................6
Hypothesis...............................................................................................................................................6
Research Questions.....................................................................................................................................6
Research Design and Methodology.............................................................................................................6
Time Schedule.............................................................................................................................................8
Conclusion...................................................................................................................................................9
References.................................................................................................................................................10
Appendix...................................................................................................................................................11
Introduction
The introduction of digital technology has resulted in a rise in the use of smartphones as well as
online services used by people and corporations. The use of smartphones has made it easier to
2 | P a g e
RESEARCH 3
access internet and online services by people. The use of internet-based services varies from
assisting in performing operations such as banking, entertainment, communication, shopping and
others not mentioned. Modern companies have developed techniques to utilize this platform to
offer their product and services directly to the consumers. With this, the use of intermediaries has
been drastically reduced resulting in lower operations cost. Despite the advantages brought by
internet and smartphones, its increasing popularity is posing a threat to individuals and
corporations. There has been an emergence of cybercriminals who attack companies and
individuals to gain an unfair advantage. The remedy to this is the need for a cybersecurity
software. In this research will concentrate on identifying and evaluating the challenges that
cybersecurity has brought to the modern companies as well as individuals relying on the use of
internet-based services. Afterwards, it will give a few recommendations that can assist minimize
the issues identified.
Project Objectives
The primary objective of the research is to evaluate the challenges that the modern companies
face regarding cybersecurity as the use of the internet as well as online-based services goes up.
Afterwards will conduct a literature review on the topic. The research will use information from
companies that have faced cybercrime to understand and expound on the problem. The
secondary target will then be to offer recommendations that can help firms enhance their
cybersecurity.
Project Scope
One of the areas the report will cover is the vulnerability of corporations to cyber-attacks as well
as the problems they face from the occurrence of cyber-attacks. The report will use various
theories that have been designed by researchers on the issue, also, will illustrate several
recommendations that canna assists fight cyber-crime.
Literature Review
The past decade has seen the use of internet and online services grow tremendously among
modern firms hence enabling provision of services via online platforms (Lenhart, et al., 2010).
The increasing popularity has been a significant contributor to the growth of internet use as it
also attracts companies online. Modern businesses rely on online platforms to perform several
3 | P a g e
access internet and online services by people. The use of internet-based services varies from
assisting in performing operations such as banking, entertainment, communication, shopping and
others not mentioned. Modern companies have developed techniques to utilize this platform to
offer their product and services directly to the consumers. With this, the use of intermediaries has
been drastically reduced resulting in lower operations cost. Despite the advantages brought by
internet and smartphones, its increasing popularity is posing a threat to individuals and
corporations. There has been an emergence of cybercriminals who attack companies and
individuals to gain an unfair advantage. The remedy to this is the need for a cybersecurity
software. In this research will concentrate on identifying and evaluating the challenges that
cybersecurity has brought to the modern companies as well as individuals relying on the use of
internet-based services. Afterwards, it will give a few recommendations that can assist minimize
the issues identified.
Project Objectives
The primary objective of the research is to evaluate the challenges that the modern companies
face regarding cybersecurity as the use of the internet as well as online-based services goes up.
Afterwards will conduct a literature review on the topic. The research will use information from
companies that have faced cybercrime to understand and expound on the problem. The
secondary target will then be to offer recommendations that can help firms enhance their
cybersecurity.
Project Scope
One of the areas the report will cover is the vulnerability of corporations to cyber-attacks as well
as the problems they face from the occurrence of cyber-attacks. The report will use various
theories that have been designed by researchers on the issue, also, will illustrate several
recommendations that canna assists fight cyber-crime.
Literature Review
The past decade has seen the use of internet and online services grow tremendously among
modern firms hence enabling provision of services via online platforms (Lenhart, et al., 2010).
The increasing popularity has been a significant contributor to the growth of internet use as it
also attracts companies online. Modern businesses rely on online platforms to perform several
3 | P a g e
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
RESEARCH 4
operations like recruitment, conducting surveys as well as customer interaction (Holm, et al.,
2013). The use of internet has given small-scale entrepreneurs an equal opportunity to interact
with the potential clients.
There are firms like Uber, Facebook, and others whose entire services are provided online while
others use the platform to improve the quality of their operations (Edelman & Geraldin, 2015).
The use and popularity of internet have enabled these firms to gain a competitive advantage. Due
to the rapid growth of the use of the web, there is need to increase the capital allocated to cyber
security (Howard & Mazaheri, 2009.). Cybercrimes have also increased with the increase in the
use of the internet with online servers most prone to attack as they lack security guidelines. The
attacks are directed towards gaining information regarding individuals and companies that can be
used to cause financial as well as reputational damage.
The number of glo0bal social media users have grown from 1.22 billion in 2011 to 2.26 billion in
2017 this shows the rapid increase in social media popularity a factor which has fueled
cybercrimes (Sanchex, et al., 2012.). Considering that the number is estimated to hit 3.02 billion
by 2021 and with more users acting as an attraction to companies to the online platforms then
cybersecurity is an issue of concern. Corporations like Oreo, old Spice have successfully
implemented the social media marketing strategy to gain a competitive advantage in the market.
On the other hand, several firms like HBO, Yahoo, BBC, and Sony have been hit with
cyberattack issues.
The increase in the use of mobile applications is also a contributor to cyber-attacks (Islam &
Mazumder, 2010.). As smartphones' usage increases so are the expansion of the mobile
applications industry. Smartphones usage grew from 1.57 billion in 2014 to 2.32 billion in 2017;
this number is projected to be around 2.87 billion globally by 2020, with this company like
Facebook and WhatsApp are a potential target of cybercriminals. Most of the people who use
social media have little information on cyber-crimes and end up avoiding the security features of
the applications due to their complexity (Wright & Dawson, 2012).
Below are several examples of online security problems faced by modern companies.
DDoS
4 | P a g e
operations like recruitment, conducting surveys as well as customer interaction (Holm, et al.,
2013). The use of internet has given small-scale entrepreneurs an equal opportunity to interact
with the potential clients.
There are firms like Uber, Facebook, and others whose entire services are provided online while
others use the platform to improve the quality of their operations (Edelman & Geraldin, 2015).
The use and popularity of internet have enabled these firms to gain a competitive advantage. Due
to the rapid growth of the use of the web, there is need to increase the capital allocated to cyber
security (Howard & Mazaheri, 2009.). Cybercrimes have also increased with the increase in the
use of the internet with online servers most prone to attack as they lack security guidelines. The
attacks are directed towards gaining information regarding individuals and companies that can be
used to cause financial as well as reputational damage.
The number of glo0bal social media users have grown from 1.22 billion in 2011 to 2.26 billion in
2017 this shows the rapid increase in social media popularity a factor which has fueled
cybercrimes (Sanchex, et al., 2012.). Considering that the number is estimated to hit 3.02 billion
by 2021 and with more users acting as an attraction to companies to the online platforms then
cybersecurity is an issue of concern. Corporations like Oreo, old Spice have successfully
implemented the social media marketing strategy to gain a competitive advantage in the market.
On the other hand, several firms like HBO, Yahoo, BBC, and Sony have been hit with
cyberattack issues.
The increase in the use of mobile applications is also a contributor to cyber-attacks (Islam &
Mazumder, 2010.). As smartphones' usage increases so are the expansion of the mobile
applications industry. Smartphones usage grew from 1.57 billion in 2014 to 2.32 billion in 2017;
this number is projected to be around 2.87 billion globally by 2020, with this company like
Facebook and WhatsApp are a potential target of cybercriminals. Most of the people who use
social media have little information on cyber-crimes and end up avoiding the security features of
the applications due to their complexity (Wright & Dawson, 2012).
Below are several examples of online security problems faced by modern companies.
DDoS
4 | P a g e
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
RESEARCH 5
As the increase in online users increases internet traffic for firms' cybercriminals take advantage
of this to send Distributed Denial of Service (DDoS) with this, the criminals can cause the failure
of the company servers and then gain access to the company system to collect confidential
information (Zargar & Tipper, 2013).
Internet of things
The internet popularity has increased the number of gadgets connected to the internet. These
gadgets are called internet of things. They pose a security challenge as hackers can gain access to
one and use it to collect sensitive information to the other connected systems (Covington, 2013).
Smartphone Malware
Cybercriminals sometimes attack peoples' phones directly as they contain personal information
which can be used to blackmail companies and gain access to sensitive data like the case of
Plankton and Drone KungFu (Covington, 2009).
Hacktivism
According to Kelly (Kelly, 2012), the emergence of Hacktivism which involves hacking
organizations systems to protest their political agendas is a risk firm face. The aim is to destroy
the firm's reputation hence a dangerous trend.
Other harmful cybercrime trends involve Ransomware, Machine Learning, Insider threats,
Malware as well as Phishing.
Justification
More and more firms are entering the internet-based service provision, with social media also
seeing individuals uploading their personal information online. The enormous number of people
and companies in the online platform need information security to guarantee their
confidentiality. The rise of cybercrime is a direct threat to this which makes it a threat to the
growth of online businesses the research is, therefore, Vitol as it aims to come up with means
which will assist minimize cybercrimes.
5 | P a g e
As the increase in online users increases internet traffic for firms' cybercriminals take advantage
of this to send Distributed Denial of Service (DDoS) with this, the criminals can cause the failure
of the company servers and then gain access to the company system to collect confidential
information (Zargar & Tipper, 2013).
Internet of things
The internet popularity has increased the number of gadgets connected to the internet. These
gadgets are called internet of things. They pose a security challenge as hackers can gain access to
one and use it to collect sensitive information to the other connected systems (Covington, 2013).
Smartphone Malware
Cybercriminals sometimes attack peoples' phones directly as they contain personal information
which can be used to blackmail companies and gain access to sensitive data like the case of
Plankton and Drone KungFu (Covington, 2009).
Hacktivism
According to Kelly (Kelly, 2012), the emergence of Hacktivism which involves hacking
organizations systems to protest their political agendas is a risk firm face. The aim is to destroy
the firm's reputation hence a dangerous trend.
Other harmful cybercrime trends involve Ransomware, Machine Learning, Insider threats,
Malware as well as Phishing.
Justification
More and more firms are entering the internet-based service provision, with social media also
seeing individuals uploading their personal information online. The enormous number of people
and companies in the online platform need information security to guarantee their
confidentiality. The rise of cybercrime is a direct threat to this which makes it a threat to the
growth of online businesses the research is, therefore, Vitol as it aims to come up with means
which will assist minimize cybercrimes.
5 | P a g e
RESEARCH 6
Literature problems
The information composing of the literature review is generated from diverse sources; it's,
therefore, hard to identify the relevant information without getting buried and to lose focus on
the research scope.
Gaps
The gap in the research is the actual economic damage caused by cyber-crimes as most of the
data regarding that is treated as confidential by confirmed firms.
Opportunities
The literature review has availed a chance to see the impact of the use of internet on social
interaction and business operations. Also, it has highlighted some of the most commonly used
paths by cybercriminals
Hypothesis
Cybercrime is limiting the growth of online business
Cybercrimes can be contained by appropriate security policies by firms operating online.
Research Questions
Primary
Highlight Cybersecurity challenges facing modern organizations and internet users?
Secondary
i. What's the reason behind the increased usage of internet?
ii. Reasons why more firms are implementing online marketing strategies/
iii. What's are some of the techniques cybercriminals employ to commit cybercrimes?
iv. Illustrate ways of minimizing cybercrimes
Research Design and Methodology
The research will include both the qualitative and quantitative design.
Qualitative design
6 | P a g e
Literature problems
The information composing of the literature review is generated from diverse sources; it's,
therefore, hard to identify the relevant information without getting buried and to lose focus on
the research scope.
Gaps
The gap in the research is the actual economic damage caused by cyber-crimes as most of the
data regarding that is treated as confidential by confirmed firms.
Opportunities
The literature review has availed a chance to see the impact of the use of internet on social
interaction and business operations. Also, it has highlighted some of the most commonly used
paths by cybercriminals
Hypothesis
Cybercrime is limiting the growth of online business
Cybercrimes can be contained by appropriate security policies by firms operating online.
Research Questions
Primary
Highlight Cybersecurity challenges facing modern organizations and internet users?
Secondary
i. What's the reason behind the increased usage of internet?
ii. Reasons why more firms are implementing online marketing strategies/
iii. What's are some of the techniques cybercriminals employ to commit cybercrimes?
iv. Illustrate ways of minimizing cybercrimes
Research Design and Methodology
The research will include both the qualitative and quantitative design.
Qualitative design
6 | P a g e
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
RESEARCH 7
This design will be employed to gain an insight of some of the underlying opinions, reasons, and
motivations concerning the research. This will give an insight into the issues and generate the
research hypothesis as well as pave the way for the quantitative analysis.
To enhance reliability and validity of the information, the data will be collected in a structured
manner mainly from interviewing employees concerned with internet security in organizations.
In addition, the research will take into consideration the previous reports of agencies on
cybercrime issues.
The data will be collected from a randomly selected sample of three companies. Apart from the
interviews with the concerned company employees, the data collection will be concentrated on
articles and reports availed in the company websites and other platforms used for public
communication.
The variable of concern will be the prevalence of cyber-crimes as well as financial impacts to the
firms.
Quantitative research
The quantitative design will be applicable in quantifying the issues and generating numerical
data which can be analyzed to obtain useful statistics. This way the patterns of the problems will
be developed.
The research will involve a collection of numerical data online from company websites, reports,
and journals. To hence obtain a reliable trend the data collection will be restricted to companies
which operate globally and have clients all over the globe. Five companies will be selected at
random and the numerical data obtained analyzed using statistical instruments; charts, diagrams,
and graphs will then be applied in presenting the data. The analysis that will be done is t-test,
descriptive analysis, and variance test. Microsoft Excel will be the primary analytical software
applied.
Research Limitations
One of the biggest challenge that the research faces are the availability of too much information
on the online platforms. Since time is always a limited resource, it is not possible to access, vary
7 | P a g e
This design will be employed to gain an insight of some of the underlying opinions, reasons, and
motivations concerning the research. This will give an insight into the issues and generate the
research hypothesis as well as pave the way for the quantitative analysis.
To enhance reliability and validity of the information, the data will be collected in a structured
manner mainly from interviewing employees concerned with internet security in organizations.
In addition, the research will take into consideration the previous reports of agencies on
cybercrime issues.
The data will be collected from a randomly selected sample of three companies. Apart from the
interviews with the concerned company employees, the data collection will be concentrated on
articles and reports availed in the company websites and other platforms used for public
communication.
The variable of concern will be the prevalence of cyber-crimes as well as financial impacts to the
firms.
Quantitative research
The quantitative design will be applicable in quantifying the issues and generating numerical
data which can be analyzed to obtain useful statistics. This way the patterns of the problems will
be developed.
The research will involve a collection of numerical data online from company websites, reports,
and journals. To hence obtain a reliable trend the data collection will be restricted to companies
which operate globally and have clients all over the globe. Five companies will be selected at
random and the numerical data obtained analyzed using statistical instruments; charts, diagrams,
and graphs will then be applied in presenting the data. The analysis that will be done is t-test,
descriptive analysis, and variance test. Microsoft Excel will be the primary analytical software
applied.
Research Limitations
One of the biggest challenge that the research faces are the availability of too much information
on the online platforms. Since time is always a limited resource, it is not possible to access, vary
7 | P a g e
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
RESEARCH 8
and use all the information available online hence the report may end up ignoring some vital
aspects.
Also, the availability of too much information means validity and reliability may not be
accurately assessed as some information are not easily vetted.
The over-reliance on secondary data may mean the research conclusion may end up being
backed by information on whose reporter was biased when presenting. The situation is like data
obtained from interviews as they are tough to verify.
Finally accessing some of the people whose responses might assist make vital judgments may be
difficult as highly skilled IT professionals are busy people with minimal time to allocate to
surveys and interviews.
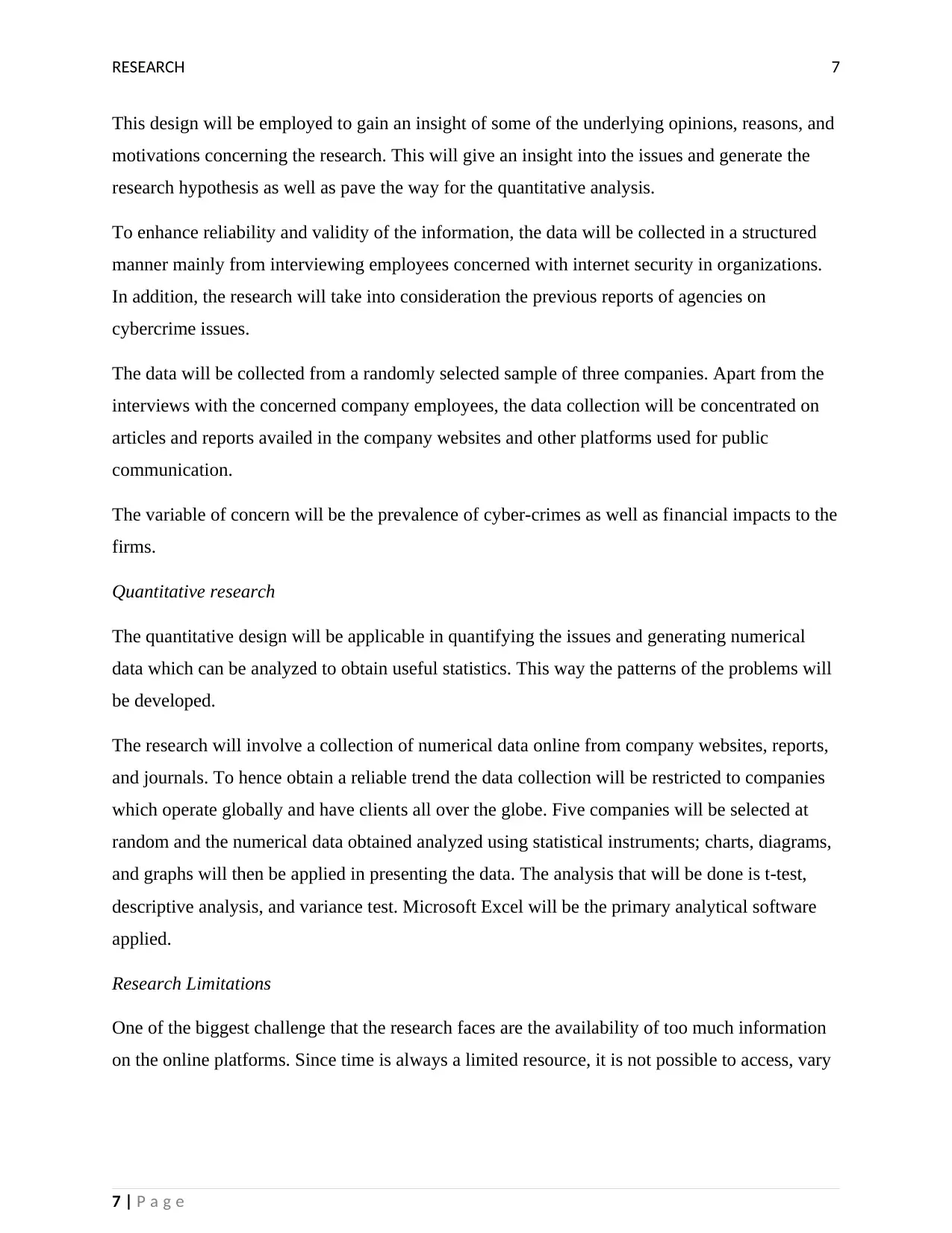
Time Schedule
Month Research goal Task Projected completion
date
Responsible
individuals
January
2017
Illustrate and
expound on the
need for internet
security on
individuals and
companies using
internet-based
services.
Assess the
internet usage
trend
In progress Project assistant
manager
January
2017
Book time and
location for
expected
interviews
In progress Project assistant
manager
April
2017
Expand on the
extent to which
companies have
suffered cyber
View company
reports
regarding
experience
May 2017 Project assistant
manager
8 | P a g e
and use all the information available online hence the report may end up ignoring some vital
aspects.
Also, the availability of too much information means validity and reliability may not be
accurately assessed as some information are not easily vetted.
The over-reliance on secondary data may mean the research conclusion may end up being
backed by information on whose reporter was biased when presenting. The situation is like data
obtained from interviews as they are tough to verify.
Finally accessing some of the people whose responses might assist make vital judgments may be
difficult as highly skilled IT professionals are busy people with minimal time to allocate to
surveys and interviews.
Time Schedule
Month Research goal Task Projected completion
date
Responsible
individuals
January
2017
Illustrate and
expound on the
need for internet
security on
individuals and
companies using
internet-based
services.
Assess the
internet usage
trend
In progress Project assistant
manager
January
2017
Book time and
location for
expected
interviews
In progress Project assistant
manager
April
2017
Expand on the
extent to which
companies have
suffered cyber
View company
reports
regarding
experience
May 2017 Project assistant
manager
8 | P a g e
RESEARCH 9
attack with
cybercriminals
May
2017
Understand the
economic
consequence of
cybercrimes
-conduct the
research
interviews
-compile the
information
obtained from
online reports
June 2017 Research manager
June
2017
Understand the
actual and verify
the pre-generated
hypothesis
Data analysis
Report writing
August 2017 Project manager
Conclusion
In conclusion, the increasing popularity of the internet has attracted millions of people to the
platform. This in return is making social media marketing as one of the best strategies companies
apply to edge out their competitors in the market. The use of the internet has made it possible for
firms to avail their products online an activity which minimizes intermediaries hence reducing
the final cost of the products to the consumers. Despite the numerous advantages brought by the
introduction of internet in doing business and social interaction, cyber-crime threats have
emerged. The increasing number of people and firms turning to the internet have in turn
increased the need to enhance cyber-security policies due to the increase in cyber-crime attacks.
Modern companies now must face emerging cybercrime issues like Ransomware, DDoS, mobile
malware, insider threat, hacktivism and many others. Inadequate security has seen several firms
fall victims of cyber criminals HBO, Yahoo, BBC and Sony being some of the examples. For
firms to tackle the issues they must upgrade their security policies and accommodate factors like;
data encryption, physical security of the servers, secure passwords and others that might be
relevant. It’s mandatory for firms to understand the importance of cybersecurity and invest
inadequate measures to protect the organizations and its clients in case of an attack (IBM., 2016)
9 | P a g e
attack with
cybercriminals
May
2017
Understand the
economic
consequence of
cybercrimes
-conduct the
research
interviews
-compile the
information
obtained from
online reports
June 2017 Research manager
June
2017
Understand the
actual and verify
the pre-generated
hypothesis
Data analysis
Report writing
August 2017 Project manager
Conclusion
In conclusion, the increasing popularity of the internet has attracted millions of people to the
platform. This in return is making social media marketing as one of the best strategies companies
apply to edge out their competitors in the market. The use of the internet has made it possible for
firms to avail their products online an activity which minimizes intermediaries hence reducing
the final cost of the products to the consumers. Despite the numerous advantages brought by the
introduction of internet in doing business and social interaction, cyber-crime threats have
emerged. The increasing number of people and firms turning to the internet have in turn
increased the need to enhance cyber-security policies due to the increase in cyber-crime attacks.
Modern companies now must face emerging cybercrime issues like Ransomware, DDoS, mobile
malware, insider threat, hacktivism and many others. Inadequate security has seen several firms
fall victims of cyber criminals HBO, Yahoo, BBC and Sony being some of the examples. For
firms to tackle the issues they must upgrade their security policies and accommodate factors like;
data encryption, physical security of the servers, secure passwords and others that might be
relevant. It’s mandatory for firms to understand the importance of cybersecurity and invest
inadequate measures to protect the organizations and its clients in case of an attack (IBM., 2016)
9 | P a g e
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide

RESEARCH 10
References
Covington, P., 2009. The growing phenomenon of crime and the internet: A cybercrim execution
and analysis model. Computer Law & Security Review, 25(6), pp. 528-535.
Edelman, G. & Geraldin, D., 2015. Efficiencies and regulatory shortcuts: How should we
regulate companies like Airbnb and Uber. Stan. Tech. L., Volume 19, p. 293.
Holm, H., Flores, W. & Ericsson, G., 2013. Cyber security for a smart grid-what about
phishing?. In Innovative Smart Grid Technologies Europe (ISGT EUROPE), 2013 4th IEEE/PES
(pp. 1-5). IEEE., 3(1),pp.15.
Howard, P. & Mazaheri, N., 2009.. Telecommunications reform, Internet use and mobile phone
adoption in the developing world.. World Development, 37(7), pp. 1159-1169.
IBM., 2016. An integrated approach to insider threat protection. [Online]
Available at: https://www-05.ibm.com/services/europe/digital-whitepaper/security/
growing_threats.html
[Accessed 12 January 2017].
Islam, R. & Mazumder, T., 2010.. Mobile application and its global impact. International
Journal of Engineering & Technology (IJEST), 10(6), pp. 72-78.
Kelly, B., 2012. Investing in a centralized cybersecurity infrastructure: Why hacktivism can and
should influence cybersecurity reform. BUL Rev, Volume 92, p. 1663.
Lenhart, A., Purcell, K. & Zickuhr, K., 2010. Social Media & Mobile Internet Use among Teens
and Young Adult, New York: Pew internet & American life project.
Sanchex, A., Levin, A. & Del Riego, A., 2012.. Blurred boundaries: Social media privacy and
the twenty‐first‐century employee. American Business Law Journal, 49(1), pp. 63-124..
Wright, J. & Dawson, M., 2012. Journal of Information Systems. Technology and Planning,
5(14), pp. 40-60.
Zargar, S. & Tipper, D., 2013. A survey of defense mechanisms agains distributed denial of
service (DDoS) flooding attacks. IEEE communications surveys & tutorials, 15(4), pp. 2046-
2069.
10 | P a g e
References
Covington, P., 2009. The growing phenomenon of crime and the internet: A cybercrim execution
and analysis model. Computer Law & Security Review, 25(6), pp. 528-535.
Edelman, G. & Geraldin, D., 2015. Efficiencies and regulatory shortcuts: How should we
regulate companies like Airbnb and Uber. Stan. Tech. L., Volume 19, p. 293.
Holm, H., Flores, W. & Ericsson, G., 2013. Cyber security for a smart grid-what about
phishing?. In Innovative Smart Grid Technologies Europe (ISGT EUROPE), 2013 4th IEEE/PES
(pp. 1-5). IEEE., 3(1),pp.15.
Howard, P. & Mazaheri, N., 2009.. Telecommunications reform, Internet use and mobile phone
adoption in the developing world.. World Development, 37(7), pp. 1159-1169.
IBM., 2016. An integrated approach to insider threat protection. [Online]
Available at: https://www-05.ibm.com/services/europe/digital-whitepaper/security/
growing_threats.html
[Accessed 12 January 2017].
Islam, R. & Mazumder, T., 2010.. Mobile application and its global impact. International
Journal of Engineering & Technology (IJEST), 10(6), pp. 72-78.
Kelly, B., 2012. Investing in a centralized cybersecurity infrastructure: Why hacktivism can and
should influence cybersecurity reform. BUL Rev, Volume 92, p. 1663.
Lenhart, A., Purcell, K. & Zickuhr, K., 2010. Social Media & Mobile Internet Use among Teens
and Young Adult, New York: Pew internet & American life project.
Sanchex, A., Levin, A. & Del Riego, A., 2012.. Blurred boundaries: Social media privacy and
the twenty‐first‐century employee. American Business Law Journal, 49(1), pp. 63-124..
Wright, J. & Dawson, M., 2012. Journal of Information Systems. Technology and Planning,
5(14), pp. 40-60.
Zargar, S. & Tipper, D., 2013. A survey of defense mechanisms agains distributed denial of
service (DDoS) flooding attacks. IEEE communications surveys & tutorials, 15(4), pp. 2046-
2069.
10 | P a g e
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

RESEARCH 11
Appendix
Figure 1: the number of smartphone users globally between 2014 and 2020 (Statista, 2018).
11 | P a g e
Appendix
Figure 1: the number of smartphone users globally between 2014 and 2020 (Statista, 2018).
11 | P a g e

RESEARCH 12
Figure 2: The insider threat (SecurityIntelligence, 2016).
12 | P a g e
Figure 2: The insider threat (SecurityIntelligence, 2016).
12 | P a g e
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 14
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





