Network Essentials: Network Design, Security, and Installation
VerifiedAdded on 2023/06/17
|12
|3621
|361
Report
AI Summary
This report outlines a network design solution for a small office, addressing client requirements for improved IT infrastructure. It details the current IT setup, new client demands including specific software and hardware needs, and proposes suitable network protocol services such as TCP/IP, HTTP, SSL, SFTP, SNMP, and ICMP. The design incorporates bus and ring logical topologies, an IPV4 sub netted addressing plan, and specifies appropriate IT equipment like Dell XPS laptops, Dell Vostro desktops, HP Colour LaserJet printers, and Cisco ISR routers. The solution also covers network services including Synology NAS, Lancom Systems VPN, and iDrive cloud storage. Security features are outlined, and the report concludes with installation plans and configuration procedures, aiming for minimal disruption to the client.
Network Essentials
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Table of Contents
INTRODUCTION...........................................................................................................................1
Task 1: What is the Scope of the Project?.......................................................................................1
Briefly explain what the current IT infrastructure is?............................................................1
Briefly explain what the new client requirements are for the new small office network?.....2
What network protocol services will they use, IT equipment and software needed..............2
Task 2: Identify most suitable network design to meet client requirements and Develop and
document network design. Use at least two different network mapping topologies......................3
Suggest logical topology........................................................................................................3
Task 3: Review available network technologies, devices and protocols and determine the most
appropriate to meet client requirements...........................................................................................4
Task 4: Source vendors and service suppliers to obtain specifications, availability and cost of
identified components......................................................................................................................5
Outline the specs for IT device and cost (include any laptops, desktops, printers, ISR routers,
ISPs and network services eg NAS, VPN, Cloud storage).....................................................5
Task 5: Outline the security features for this network.....................................................................6
Ensure client sign-off for proposed network design and associated components..................6
Task 6: Develop installation plans with prioritised tasks and contingency arrangements for
installation of components with minimum disruption to client. The client has identified that a
maximum of one week for the installation. You can liaise with your instructor to obtain approval
for plans, including security clearance and timing..........................................................................7
Confirm and review supplier documentation that network cables and connectors have been
installed according to industry standards, client requirements and building requirements.
(suggest wireless)...................................................................................................................7
Task 7: After feedback from your client polish your document......................................................7
Document final network design and associated hardware, software and security features....7
Document installation, boot up and configuration procedures as per client requirements....8
INTRODUCTION...........................................................................................................................1
Task 1: What is the Scope of the Project?.......................................................................................1
Briefly explain what the current IT infrastructure is?............................................................1
Briefly explain what the new client requirements are for the new small office network?.....2
What network protocol services will they use, IT equipment and software needed..............2
Task 2: Identify most suitable network design to meet client requirements and Develop and
document network design. Use at least two different network mapping topologies......................3
Suggest logical topology........................................................................................................3
Task 3: Review available network technologies, devices and protocols and determine the most
appropriate to meet client requirements...........................................................................................4
Task 4: Source vendors and service suppliers to obtain specifications, availability and cost of
identified components......................................................................................................................5
Outline the specs for IT device and cost (include any laptops, desktops, printers, ISR routers,
ISPs and network services eg NAS, VPN, Cloud storage).....................................................5
Task 5: Outline the security features for this network.....................................................................6
Ensure client sign-off for proposed network design and associated components..................6
Task 6: Develop installation plans with prioritised tasks and contingency arrangements for
installation of components with minimum disruption to client. The client has identified that a
maximum of one week for the installation. You can liaise with your instructor to obtain approval
for plans, including security clearance and timing..........................................................................7
Confirm and review supplier documentation that network cables and connectors have been
installed according to industry standards, client requirements and building requirements.
(suggest wireless)...................................................................................................................7
Task 7: After feedback from your client polish your document......................................................7
Document final network design and associated hardware, software and security features....7
Document installation, boot up and configuration procedures as per client requirements....8
CONCLUSION................................................................................................................................8
References:.......................................................................................................................................9
References:.......................................................................................................................................9
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
INTRODUCTION
Computer networking can be defined as the different sets of computers which shares the
resources that are located on the network nodes. There are some common communication
protocols which are used to share the resources over the network from one device to another.
Such as TCP/IP, UDP and many more. Internet is one of the major example of networking. It
basically the practice of exchanging the information from nodes over a network medium in an
information systems. It facilitates the telephone calls, text messaging, streaming video, internet
of things and many more (Chapman, Chinnaswamy and Garcia-Perez, 2018). The following
discussion is based on the establishment of networking topologies in the organization as per the
given scenario. The report will cover scope of the project and suitable network design to meet
the client requirements. Moreover, the report will also give the view of network technologies and
cost identification for the project. Additionally, insight of installation plans and feedback of
clients are also covered in the project report of network essentials with conclusion.
Task 1: What is the Scope of the Project?
Briefly explain what the current IT infrastructure is?
IT infrastructure can be defined as the sets of various components which are required for
operations and management of IT environments. Such components are hardware, software,
operating system, networking elements and data storage. All these are used to render information
technology solutions and services (Daimi, Francia, Ertaul and El-sheikh, 2018). As per the given
scenario, organizations has the following IT resources and infrastructure available currently.
The machines are connected through 10/100 MB switch.
There are three old PC tower computers with 2 GB of memory, 250 GB, hard drive and 7
USB ports.
The processor are AMD Athlon 64 x2 dual core processor and a CD/DVD read and write
drives.
Operating system used is the Windows & in every computers.
There is a low capacity, monochrome laser printer attached to each machine. These are
the machines which are not capable of running the required software for video
development.
1
Computer networking can be defined as the different sets of computers which shares the
resources that are located on the network nodes. There are some common communication
protocols which are used to share the resources over the network from one device to another.
Such as TCP/IP, UDP and many more. Internet is one of the major example of networking. It
basically the practice of exchanging the information from nodes over a network medium in an
information systems. It facilitates the telephone calls, text messaging, streaming video, internet
of things and many more (Chapman, Chinnaswamy and Garcia-Perez, 2018). The following
discussion is based on the establishment of networking topologies in the organization as per the
given scenario. The report will cover scope of the project and suitable network design to meet
the client requirements. Moreover, the report will also give the view of network technologies and
cost identification for the project. Additionally, insight of installation plans and feedback of
clients are also covered in the project report of network essentials with conclusion.
Task 1: What is the Scope of the Project?
Briefly explain what the current IT infrastructure is?
IT infrastructure can be defined as the sets of various components which are required for
operations and management of IT environments. Such components are hardware, software,
operating system, networking elements and data storage. All these are used to render information
technology solutions and services (Daimi, Francia, Ertaul and El-sheikh, 2018). As per the given
scenario, organizations has the following IT resources and infrastructure available currently.
The machines are connected through 10/100 MB switch.
There are three old PC tower computers with 2 GB of memory, 250 GB, hard drive and 7
USB ports.
The processor are AMD Athlon 64 x2 dual core processor and a CD/DVD read and write
drives.
Operating system used is the Windows & in every computers.
There is a low capacity, monochrome laser printer attached to each machine. These are
the machines which are not capable of running the required software for video
development.
1
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
These are the information technology devices used within organization. It is analysed that
this IT infrastructure is outdated and cannot be used in the video making and presentations. It
highly requires an advanced and updated resources of information technology for better
implementation and execution of the required network. This will improve the communications as
well as the functioning of the company.
Briefly explain what the new client requirements are for the new small office network?
There are various requirements asked by client for the new small office network in order
to work as per the current needs of the business. The following requirements are not only for the
networking but also to renovate the entire infrastructure of IT within organization so that safety
and security issues can be detected out and rectified accordingly (Diyeb, Saif and Al-Shaibany,
2018). The following are the requirements which are highly needed for the company.
Requirements of database and spreadsheets software along with the email facility
provided by the internet service provider.
Requirements of special editing software which uses very high resolution graphics. It
highly requires the 16 GB of memory to run such software effectively.
Requirement of Pclex 16 slot in the computer because of the requirement of interfaces
with a video capture interface board.
These are the software which only runs in the operating system of windows 10
environment. Therefore, major is a great need of windows 10.
Connection of internal network in a wireless form and plug into the data port
requirements are important so that the mobile workers can easily access to the company
resources.
Requirement of private colour laser printer because of the documents records required in
the physical form.
High resolution scanner is also needed and shared among the employees for quick
working on the customers’ demands.
What network protocol services will they use, IT equipment and software needed
There are majorly three types of network protocols which are required to use by the
organization as per the given case study.
Such as first are the network communication protocols in order to interact with the
employees who are not physically present in the office and are working remotely and also
2
this IT infrastructure is outdated and cannot be used in the video making and presentations. It
highly requires an advanced and updated resources of information technology for better
implementation and execution of the required network. This will improve the communications as
well as the functioning of the company.
Briefly explain what the new client requirements are for the new small office network?
There are various requirements asked by client for the new small office network in order
to work as per the current needs of the business. The following requirements are not only for the
networking but also to renovate the entire infrastructure of IT within organization so that safety
and security issues can be detected out and rectified accordingly (Diyeb, Saif and Al-Shaibany,
2018). The following are the requirements which are highly needed for the company.
Requirements of database and spreadsheets software along with the email facility
provided by the internet service provider.
Requirements of special editing software which uses very high resolution graphics. It
highly requires the 16 GB of memory to run such software effectively.
Requirement of Pclex 16 slot in the computer because of the requirement of interfaces
with a video capture interface board.
These are the software which only runs in the operating system of windows 10
environment. Therefore, major is a great need of windows 10.
Connection of internal network in a wireless form and plug into the data port
requirements are important so that the mobile workers can easily access to the company
resources.
Requirement of private colour laser printer because of the documents records required in
the physical form.
High resolution scanner is also needed and shared among the employees for quick
working on the customers’ demands.
What network protocol services will they use, IT equipment and software needed
There are majorly three types of network protocols which are required to use by the
organization as per the given case study.
Such as first are the network communication protocols in order to interact with the
employees who are not physically present in the office and are working remotely and also
2
with staff who are present as well. TCP/IP (transmission control protocol / internet
protocol) and HTTP (hypertext transfer protocol) are the major networks which must be
implemented within company (Yadav, 2020).
Second are the network security protocols which are used to secure the IT devices and
important data from the damaging and corruption. SSL (secure socket layer) and SFTP
(secure file transfer protocol) are the security protocols must be executed in the company.
Third is the network management protocols which are used to govern and maintain the
other network protocols by managing its updates and outdates. SNMP (simple network
management protocol) and ICMP (internet control message protocol) are the management
protocols for better administration of other networks services within organization.
These are the important network protocols which are highly required by the organization
to implement in order to fulfil the needs and demands of the customers. IT equipments
and software required are discussed in the previous section.
Task 2: Identify most suitable network design to meet client requirements and
Develop and document network design. Use at least two different network
mapping topologies.
Suggest logical topology
Logical topology can be defined as the arrangement of various network devices and
nodes. It is a concept of networking which describes the architecture of the communication
framework among all the nodes in the network. There are some network equipment such as
routers and switches are used in the logical topology which is reconfigures and maintained
dynamically. It appears to the user that how the devices are connected for easy understanding of
the concept (Duffany, 2018). As per the given scenario, there are two logical network topologies
which are used as per the structure of the organization.
First is the bus logical topology, it is a type of topology in which all the switches and
nodes are connected to only one cable line. This is also know as the backbone topology.
It has various advantages to establish such as it is one of the most easiest form of network
topology. It works efficiently in a small network. Easy to connect or remove devices
without affecting any other device. It is cost effective in nature and easy to expand with
low requirements of wires. It is most effective in small business management.
3
protocol) and HTTP (hypertext transfer protocol) are the major networks which must be
implemented within company (Yadav, 2020).
Second are the network security protocols which are used to secure the IT devices and
important data from the damaging and corruption. SSL (secure socket layer) and SFTP
(secure file transfer protocol) are the security protocols must be executed in the company.
Third is the network management protocols which are used to govern and maintain the
other network protocols by managing its updates and outdates. SNMP (simple network
management protocol) and ICMP (internet control message protocol) are the management
protocols for better administration of other networks services within organization.
These are the important network protocols which are highly required by the organization
to implement in order to fulfil the needs and demands of the customers. IT equipments
and software required are discussed in the previous section.
Task 2: Identify most suitable network design to meet client requirements and
Develop and document network design. Use at least two different network
mapping topologies.
Suggest logical topology
Logical topology can be defined as the arrangement of various network devices and
nodes. It is a concept of networking which describes the architecture of the communication
framework among all the nodes in the network. There are some network equipment such as
routers and switches are used in the logical topology which is reconfigures and maintained
dynamically. It appears to the user that how the devices are connected for easy understanding of
the concept (Duffany, 2018). As per the given scenario, there are two logical network topologies
which are used as per the structure of the organization.
First is the bus logical topology, it is a type of topology in which all the switches and
nodes are connected to only one cable line. This is also know as the backbone topology.
It has various advantages to establish such as it is one of the most easiest form of network
topology. It works efficiently in a small network. Easy to connect or remove devices
without affecting any other device. It is cost effective in nature and easy to expand with
low requirements of wires. It is most effective in small business management.
3
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Second is the ring logical topology, it is a type of topology in which the devices are
connected in the form of circular connections in which network is configured as per the
data path. It is mostly used when simple work is required in the small business
organization. Its advantages include in this topology, data flows in one direction so
therefore chances of packet collusion can be minimised. It provides equal access to the
resources. It is cost efficient in installation and expansion. It renders high speed of
transfer of data in large volume. Management and organization of such topology is easy
within company.
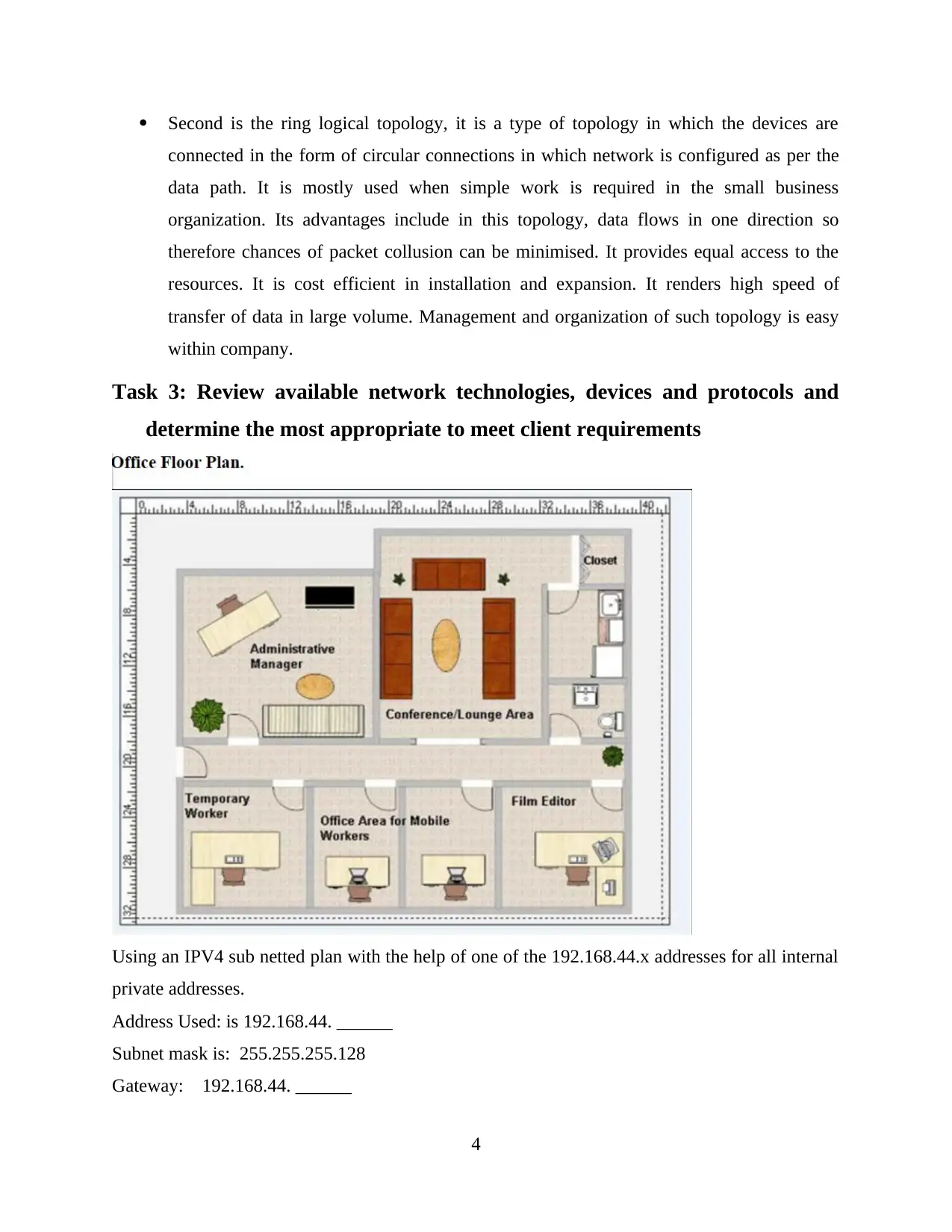
Task 3: Review available network technologies, devices and protocols and
determine the most appropriate to meet client requirements
Using an IPV4 sub netted plan with the help of one of the 192.168.44.x addresses for all internal
private addresses.
Address Used: is 192.168.44. ______
Subnet mask is: 255.255.255.128
Gateway: 192.168.44. ______
4
connected in the form of circular connections in which network is configured as per the
data path. It is mostly used when simple work is required in the small business
organization. Its advantages include in this topology, data flows in one direction so
therefore chances of packet collusion can be minimised. It provides equal access to the
resources. It is cost efficient in installation and expansion. It renders high speed of
transfer of data in large volume. Management and organization of such topology is easy
within company.
Task 3: Review available network technologies, devices and protocols and
determine the most appropriate to meet client requirements
Using an IPV4 sub netted plan with the help of one of the 192.168.44.x addresses for all internal
private addresses.
Address Used: is 192.168.44. ______
Subnet mask is: 255.255.255.128
Gateway: 192.168.44. ______
4
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
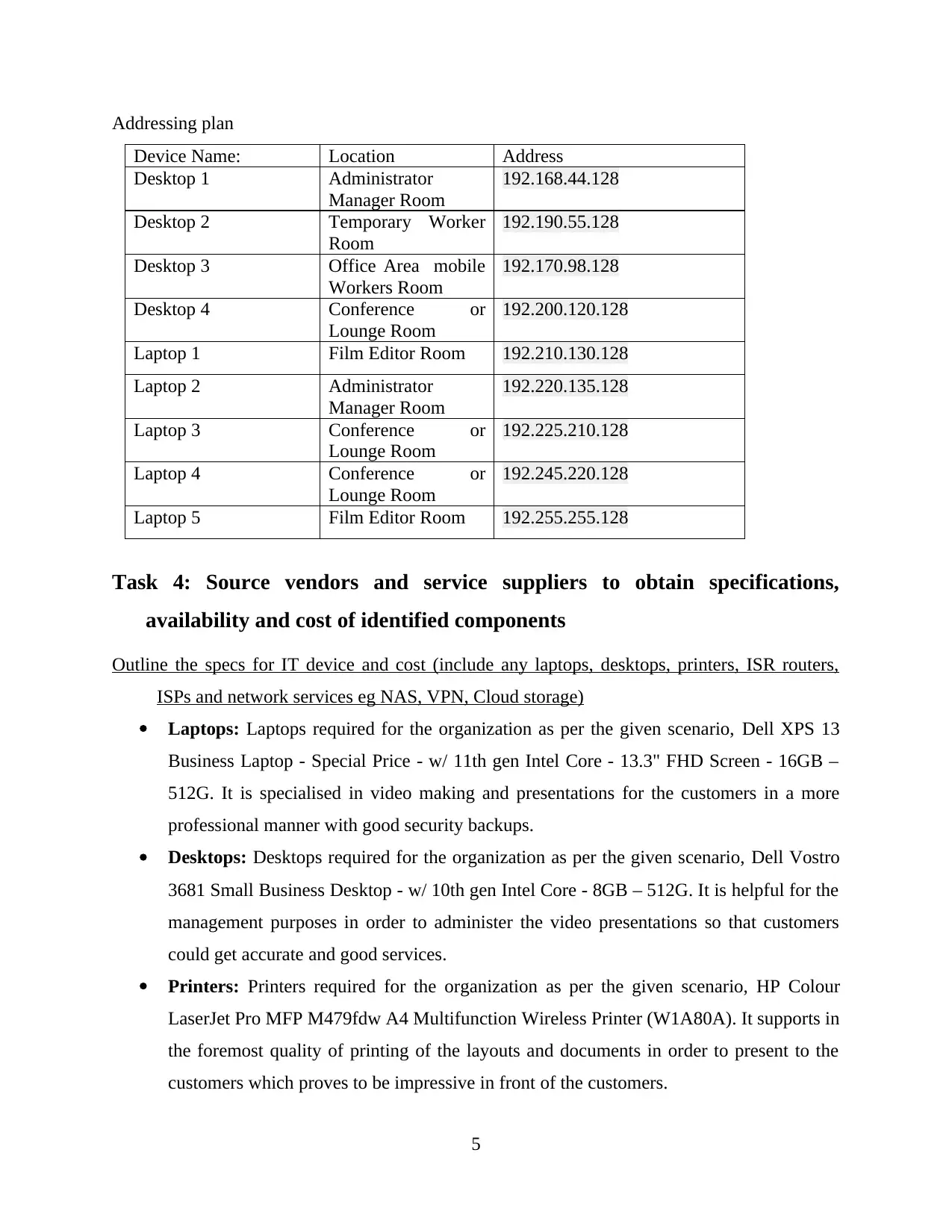
Addressing plan
Device Name: Location Address
Desktop 1 Administrator
Manager Room
192.168.44.128
Desktop 2 Temporary Worker
Room
192.190.55.128
Desktop 3 Office Area mobile
Workers Room
192.170.98.128
Desktop 4 Conference or
Lounge Room
192.200.120.128
Laptop 1 Film Editor Room 192.210.130.128
Laptop 2 Administrator
Manager Room
192.220.135.128
Laptop 3 Conference or
Lounge Room
192.225.210.128
Laptop 4 Conference or
Lounge Room
192.245.220.128
Laptop 5 Film Editor Room 192.255.255.128
Task 4: Source vendors and service suppliers to obtain specifications,
availability and cost of identified components
Outline the specs for IT device and cost (include any laptops, desktops, printers, ISR routers,
ISPs and network services eg NAS, VPN, Cloud storage)
Laptops: Laptops required for the organization as per the given scenario, Dell XPS 13
Business Laptop - Special Price - w/ 11th gen Intel Core - 13.3" FHD Screen - 16GB –
512G. It is specialised in video making and presentations for the customers in a more
professional manner with good security backups.
Desktops: Desktops required for the organization as per the given scenario, Dell Vostro
3681 Small Business Desktop - w/ 10th gen Intel Core - 8GB – 512G. It is helpful for the
management purposes in order to administer the video presentations so that customers
could get accurate and good services.
Printers: Printers required for the organization as per the given scenario, HP Colour
LaserJet Pro MFP M479fdw A4 Multifunction Wireless Printer (W1A80A). It supports in
the foremost quality of printing of the layouts and documents in order to present to the
customers which proves to be impressive in front of the customers.
5
Device Name: Location Address
Desktop 1 Administrator
Manager Room
192.168.44.128
Desktop 2 Temporary Worker
Room
192.190.55.128
Desktop 3 Office Area mobile
Workers Room
192.170.98.128
Desktop 4 Conference or
Lounge Room
192.200.120.128
Laptop 1 Film Editor Room 192.210.130.128
Laptop 2 Administrator
Manager Room
192.220.135.128
Laptop 3 Conference or
Lounge Room
192.225.210.128
Laptop 4 Conference or
Lounge Room
192.245.220.128
Laptop 5 Film Editor Room 192.255.255.128
Task 4: Source vendors and service suppliers to obtain specifications,
availability and cost of identified components
Outline the specs for IT device and cost (include any laptops, desktops, printers, ISR routers,
ISPs and network services eg NAS, VPN, Cloud storage)
Laptops: Laptops required for the organization as per the given scenario, Dell XPS 13
Business Laptop - Special Price - w/ 11th gen Intel Core - 13.3" FHD Screen - 16GB –
512G. It is specialised in video making and presentations for the customers in a more
professional manner with good security backups.
Desktops: Desktops required for the organization as per the given scenario, Dell Vostro
3681 Small Business Desktop - w/ 10th gen Intel Core - 8GB – 512G. It is helpful for the
management purposes in order to administer the video presentations so that customers
could get accurate and good services.
Printers: Printers required for the organization as per the given scenario, HP Colour
LaserJet Pro MFP M479fdw A4 Multifunction Wireless Printer (W1A80A). It supports in
the foremost quality of printing of the layouts and documents in order to present to the
customers which proves to be impressive in front of the customers.
5
ISR Routers: ISR Routers required for the organization as per the given scenario, Cisco
ISR 4331 Integrated Services Router, Connector Ethernet/RJ 45, 10/100/1000Mbps, Ports
3, 110 120vac 220 240vac B&H Photo-Video-Audio. It highly supports the sharing of
high quality video, audio and photo content across the network without any complicated
issues in networking.
Network services – NAS: NAS required for the organization as per the given scenario,
Synology RackStation RS1221+ 8bay Network Attached Storage Drive. Network
attached storage is used professionally within organization with enhanced experience for
storing of the large quantity of files without any corrupting element.
Network services – VPN: VPN required for the organization as per the given scenario,
Lancom Systems 1780EW-4G+ VPN router 1000 Mbit/s. Virtual private network is
established to share the information within the organization without going out of the
company. Moreover, it is secure in nature so therefore, it is highly essential to introduce
in the firm.
Network services – Cloud Storage: Cloud storage required for the organization as per
the given scenario, iDrive is chosen to use by the organization because it has the
capability of multiple device backup, online file sync, snapshots and versioning,
management of computers, clone or computer backup, security and privacy and a veru
high rich speed (Kabir, Basak, Tanim and Islam, 2019).
Task 5: Outline the security features for this network
Ensure client sign-off for proposed network design and associated components
Client sign off for proposed network design and associated components are carrying the
process. The first step is to organise the project documents so that the preparation of the final
report can be done. Second step is to distribute the sign off sheet so that the transition of
remaining items to a do list can be performed. Third step is to review the lessons learnt so that
improvement can be made for the development of a network. It is basically the method in order
to verify the supplier's quality planning process that has been successfully executed. It is a
process for asking the confirmation to the client so that a document can be written and signed off
after clearing out doubts on the networking part which is regarded as the proof for the acceptance
of the project (Kao, Wang, Tsai and Chen, 2018).
6
ISR 4331 Integrated Services Router, Connector Ethernet/RJ 45, 10/100/1000Mbps, Ports
3, 110 120vac 220 240vac B&H Photo-Video-Audio. It highly supports the sharing of
high quality video, audio and photo content across the network without any complicated
issues in networking.
Network services – NAS: NAS required for the organization as per the given scenario,
Synology RackStation RS1221+ 8bay Network Attached Storage Drive. Network
attached storage is used professionally within organization with enhanced experience for
storing of the large quantity of files without any corrupting element.
Network services – VPN: VPN required for the organization as per the given scenario,
Lancom Systems 1780EW-4G+ VPN router 1000 Mbit/s. Virtual private network is
established to share the information within the organization without going out of the
company. Moreover, it is secure in nature so therefore, it is highly essential to introduce
in the firm.
Network services – Cloud Storage: Cloud storage required for the organization as per
the given scenario, iDrive is chosen to use by the organization because it has the
capability of multiple device backup, online file sync, snapshots and versioning,
management of computers, clone or computer backup, security and privacy and a veru
high rich speed (Kabir, Basak, Tanim and Islam, 2019).
Task 5: Outline the security features for this network
Ensure client sign-off for proposed network design and associated components
Client sign off for proposed network design and associated components are carrying the
process. The first step is to organise the project documents so that the preparation of the final
report can be done. Second step is to distribute the sign off sheet so that the transition of
remaining items to a do list can be performed. Third step is to review the lessons learnt so that
improvement can be made for the development of a network. It is basically the method in order
to verify the supplier's quality planning process that has been successfully executed. It is a
process for asking the confirmation to the client so that a document can be written and signed off
after clearing out doubts on the networking part which is regarded as the proof for the acceptance
of the project (Kao, Wang, Tsai and Chen, 2018).
6
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Task 6: Develop installation plans with prioritised tasks and contingency
arrangements for installation of components with minimum disruption to
client. The client has identified that a maximum of one week for the
installation. You can liaise with your instructor to obtain approval for
plans, including security clearance and timing.
Confirm and review supplier documentation that network cables and connectors have been
installed according to industry standards, client requirements and building requirements.
(suggest wireless)
According to the industry standards and client requirements along with the building
requirements, the chosen network cables and connectors which have to be installed is the
wireless local area network. It is chosen because it is efficient in small business organisations. It
is not complicated in nature and enhances the business operations with the comfort in networking
in the organisation. A wireless local area network is defined as the computer network which
connects more than one device using wireless communication in order to form the local area
network. It is connected within a limited area for example a small business organisation, School,
office building, campus and computer laboratory (Komeda, Handa, Matsui and Kudo, 2019).
Task 7: After feedback from your client polish your document.
Document final network design and associated hardware, software and security features
Wireless local area network is used within the organisation in order to set up the different
networking topology such as bus logical topology and ring logical topology. These networks are
used to establish hypertext transfer protocol and transmission control protocol for the network
communication protocol. Secure socket layer and secure file transfer protocol for the network
security protocol. Simple network management protocol and internet control message protocol
are used for the network management protocols. Software and hardware requirements summed
up in the form of database and spreadsheet software and special editing software. These are the
software which performs the video interfaces and captures presentations. Windows 10 is a major
use and wireless networking as a whole. Private colour laser printers and high-resolution
scanners are also essential (Kumar and Kumar, 2021).
7
arrangements for installation of components with minimum disruption to
client. The client has identified that a maximum of one week for the
installation. You can liaise with your instructor to obtain approval for
plans, including security clearance and timing.
Confirm and review supplier documentation that network cables and connectors have been
installed according to industry standards, client requirements and building requirements.
(suggest wireless)
According to the industry standards and client requirements along with the building
requirements, the chosen network cables and connectors which have to be installed is the
wireless local area network. It is chosen because it is efficient in small business organisations. It
is not complicated in nature and enhances the business operations with the comfort in networking
in the organisation. A wireless local area network is defined as the computer network which
connects more than one device using wireless communication in order to form the local area
network. It is connected within a limited area for example a small business organisation, School,
office building, campus and computer laboratory (Komeda, Handa, Matsui and Kudo, 2019).
Task 7: After feedback from your client polish your document.
Document final network design and associated hardware, software and security features
Wireless local area network is used within the organisation in order to set up the different
networking topology such as bus logical topology and ring logical topology. These networks are
used to establish hypertext transfer protocol and transmission control protocol for the network
communication protocol. Secure socket layer and secure file transfer protocol for the network
security protocol. Simple network management protocol and internet control message protocol
are used for the network management protocols. Software and hardware requirements summed
up in the form of database and spreadsheet software and special editing software. These are the
software which performs the video interfaces and captures presentations. Windows 10 is a major
use and wireless networking as a whole. Private colour laser printers and high-resolution
scanners are also essential (Kumar and Kumar, 2021).
7
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

Document installation, boot up and configuration procedures as per client requirements
There are different parameters which are supplied at the time of network configuration.
The IP address of each network interface must be installed in every machine along with the
hostname of each machine on the network. What's name is typed in a local file or in a name
service database. There are different domain names which are used in the machine as per the
requirements of the networking system. The basic steps include the configuration of the host for
local files mode which includes the setting up of a network configuration server. Configuration
of a host for network client mode is done so that the specification of a router for the client
network can be performed (Wang, Cheng and Deng, 2018).
CONCLUSION
It is concluded that computer networking is an important concept to learn and study so
that its applications can be applied in the real world organizations. This is because without
establishing an appropriate networking within organization as per the needs and requirements, it
can result in the error and disruption in the normal functioning of the company. The reason being
is that networking provides the digital communication among employees which is a very
effective and efficient manner. Therefore, current IT infrastructure is analysed in the above
report so that the new client requirements and protocols can be examined. Logical topologies and
network technologies are established for better implementation of the networks. Information
technology resources and cost are identified within the organization so that proposed network
design and supplier documentation can be formulated in a conceptual manner. Final network
design and network installation are also executed for better structure of the entire project. Hence,
this report covers all such areas in order to better understand the conception of computer
networking.
References:
Books and Journals
Chapman, J., Chinnaswamy, A. and Garcia-Perez, A., 2018, January. The severity of cyber
attacks on education and research institutions: a function of their security posture.
8
There are different parameters which are supplied at the time of network configuration.
The IP address of each network interface must be installed in every machine along with the
hostname of each machine on the network. What's name is typed in a local file or in a name
service database. There are different domain names which are used in the machine as per the
requirements of the networking system. The basic steps include the configuration of the host for
local files mode which includes the setting up of a network configuration server. Configuration
of a host for network client mode is done so that the specification of a router for the client
network can be performed (Wang, Cheng and Deng, 2018).
CONCLUSION
It is concluded that computer networking is an important concept to learn and study so
that its applications can be applied in the real world organizations. This is because without
establishing an appropriate networking within organization as per the needs and requirements, it
can result in the error and disruption in the normal functioning of the company. The reason being
is that networking provides the digital communication among employees which is a very
effective and efficient manner. Therefore, current IT infrastructure is analysed in the above
report so that the new client requirements and protocols can be examined. Logical topologies and
network technologies are established for better implementation of the networks. Information
technology resources and cost are identified within the organization so that proposed network
design and supplier documentation can be formulated in a conceptual manner. Final network
design and network installation are also executed for better structure of the entire project. Hence,
this report covers all such areas in order to better understand the conception of computer
networking.
References:
Books and Journals
Chapman, J., Chinnaswamy, A. and Garcia-Perez, A., 2018, January. The severity of cyber
attacks on education and research institutions: a function of their security posture.
8
In Proceedings of ICCWS 2018 13th International Conference on Cyber Warfare and
Security. Academic Conferences and Publishing Limited (pp. 111-9).
Daimi, K., Francia, G., Ertaul, L. and El-sheikh, E. eds., 2018. Computer and network security
essentials. Springer.
Diyeb, I.A.I., Saif, A. and Al-Shaibany, N.A., 2018. Ethical network surveillance using packet
sniffing tools: A comparative study. International Journal of Computer Network and
Information Security, 11(7), p.12.
Duffany, J.L., 2018. Computer Security. In Computer and Network Security Essentials (pp. 3-
20). Springer, Cham.
Kabir, A.I., Basak, S., Tanim, M.H. and Islam, A., 2019. Smart university network module
implementation by using Cisco CCNA with packet tracer. Journal of Network
Communications and Emerging Technologies (JNCET) www. jncet. Org, 9(12).
Kao, D.Y., Wang, Y.S., Tsai, F.C. and Chen, C.H., 2018, February. Forensic analysis of network
packets from penetration test toolkits. In 2018 20th International Conference on Advanced
Communication Technology (ICACT) (pp. 363-368). IEEE.
Komeda, Y., Handa, H., Matsui, R. and Kudo, M., 2019. Computer-aided diagnosis (CAD) based
on convolutional neural network (CNN) system using artificial intelligence (AI) for
colorectal polyp classification. Endoscopy, 51(04), p.OP2.
Kumar, N. and Kumar, U., 2021. Diverse Analysis of Data Mining and Machine Learning
Algorithms to Secure Computer Network.
Wang, C.H., Cheng, H.Y. and Deng, Y.T., 2018. Using Bayesian belief network and time-series
model to conduct prescriptive and predictive analytics for computer industries. Computers
& Industrial Engineering, 115, pp.486-494.
Yadav, B., 2020. Problem-Based Learning as an Effective Tool for Teaching Computer Network
Design.
(Chapman, Chinnaswamy and Garcia-Perez, 2018)(Daimi, Francia, Ertaul and El-sheikh, 2018)
(Diyeb, Saif and Al-Shaibany, 2018)(Duffany, 2018)(Kabir, Basak, Tanim and Islam,
2019)(Kao, Wang, Tsai and Chen, 2018)(Komeda, Handa, Matsui and Kudo, 2019)(Kumar
and Kumar, 2021)(Wang, Cheng and Deng, 2018)(Yadav, 2020)
9
Security. Academic Conferences and Publishing Limited (pp. 111-9).
Daimi, K., Francia, G., Ertaul, L. and El-sheikh, E. eds., 2018. Computer and network security
essentials. Springer.
Diyeb, I.A.I., Saif, A. and Al-Shaibany, N.A., 2018. Ethical network surveillance using packet
sniffing tools: A comparative study. International Journal of Computer Network and
Information Security, 11(7), p.12.
Duffany, J.L., 2018. Computer Security. In Computer and Network Security Essentials (pp. 3-
20). Springer, Cham.
Kabir, A.I., Basak, S., Tanim, M.H. and Islam, A., 2019. Smart university network module
implementation by using Cisco CCNA with packet tracer. Journal of Network
Communications and Emerging Technologies (JNCET) www. jncet. Org, 9(12).
Kao, D.Y., Wang, Y.S., Tsai, F.C. and Chen, C.H., 2018, February. Forensic analysis of network
packets from penetration test toolkits. In 2018 20th International Conference on Advanced
Communication Technology (ICACT) (pp. 363-368). IEEE.
Komeda, Y., Handa, H., Matsui, R. and Kudo, M., 2019. Computer-aided diagnosis (CAD) based
on convolutional neural network (CNN) system using artificial intelligence (AI) for
colorectal polyp classification. Endoscopy, 51(04), p.OP2.
Kumar, N. and Kumar, U., 2021. Diverse Analysis of Data Mining and Machine Learning
Algorithms to Secure Computer Network.
Wang, C.H., Cheng, H.Y. and Deng, Y.T., 2018. Using Bayesian belief network and time-series
model to conduct prescriptive and predictive analytics for computer industries. Computers
& Industrial Engineering, 115, pp.486-494.
Yadav, B., 2020. Problem-Based Learning as an Effective Tool for Teaching Computer Network
Design.
(Chapman, Chinnaswamy and Garcia-Perez, 2018)(Daimi, Francia, Ertaul and El-sheikh, 2018)
(Diyeb, Saif and Al-Shaibany, 2018)(Duffany, 2018)(Kabir, Basak, Tanim and Islam,
2019)(Kao, Wang, Tsai and Chen, 2018)(Komeda, Handa, Matsui and Kudo, 2019)(Kumar
and Kumar, 2021)(Wang, Cheng and Deng, 2018)(Yadav, 2020)
9
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 12
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





