Comprehensive Network Security Analysis with Wireshark and HTTPS
VerifiedAdded on 2021/05/30
|14
|2454
|48
Homework Assignment
AI Summary
This assignment provides a comprehensive analysis of network security using Wireshark. It begins by explaining the process of packet capture and data deciphering within Wireshark, detailing how to capture network traffic and interpret the data. The assignment then delves into the communication taking place between a machine and a web server, focusing on the TCP/IP stack and the role of protocols like HTTP. Further, the assignment provides a detailed report on the technology used to implement HTTPS, including its history, advantages, and disadvantages. The report also discusses the HTTP reaction header and its use in web servers, as well as security considerations for HTTPS and cookies. The assignment utilizes examples like 4-realestateagent.com and paypal.com to illustrate the concepts. Finally, the assignment concludes with a bibliography of relevant resources on network security and packet analysis.
Wireshark
Name
Subject
Date
Name
Subject
Date
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
2
Network Security Analysis
Question 1.
Explain how you performed the packet capture and deciphered the data.
Answer
Packet capture
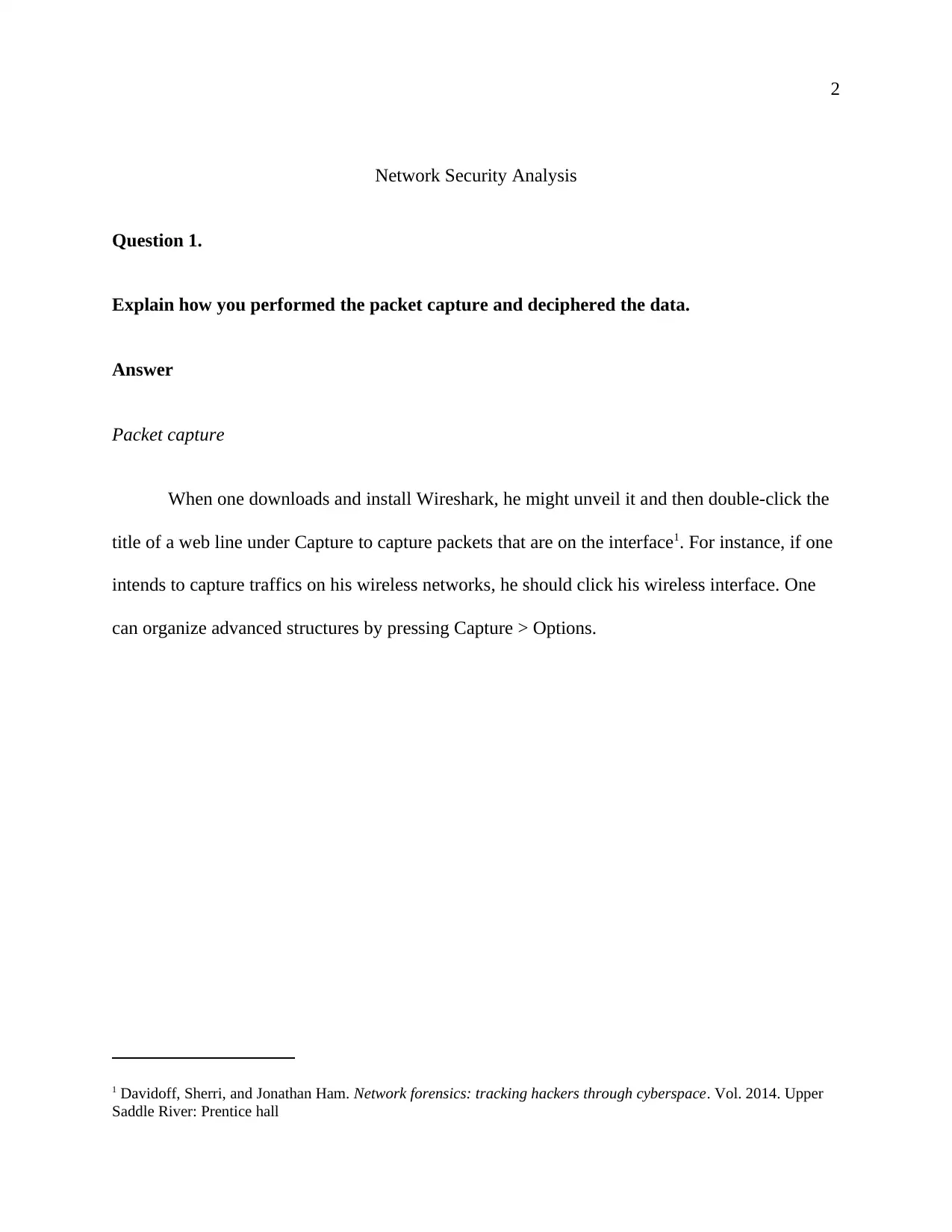
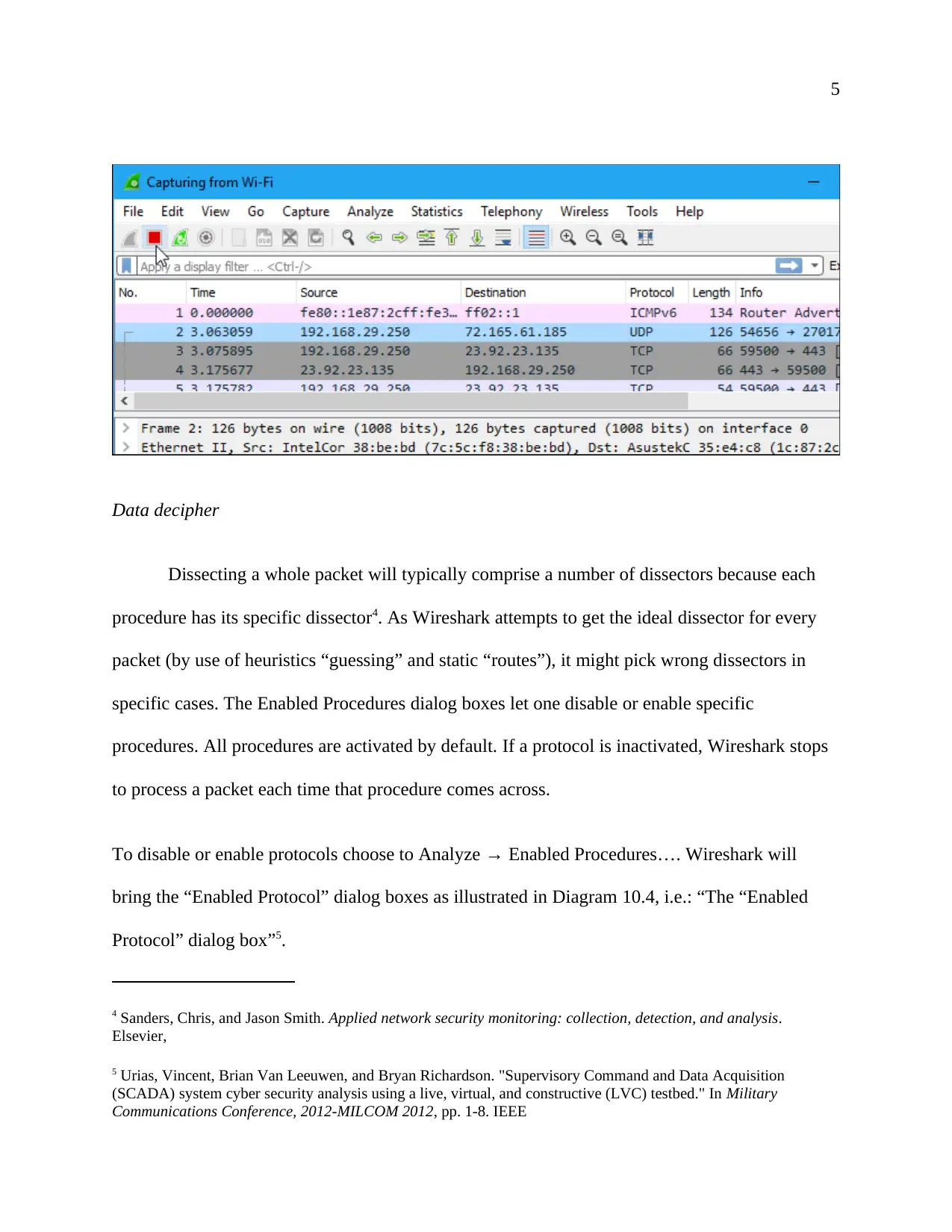
When one downloads and install Wireshark, he might unveil it and then double-click the
title of a web line under Capture to capture packets that are on the interface1. For instance, if one
intends to capture traffics on his wireless networks, he should click his wireless interface. One
can organize advanced structures by pressing Capture > Options.
1 Davidoff, Sherri, and Jonathan Ham. Network forensics: tracking hackers through cyberspace. Vol. 2014. Upper
Saddle River: Prentice hall
Network Security Analysis
Question 1.
Explain how you performed the packet capture and deciphered the data.
Answer
Packet capture
When one downloads and install Wireshark, he might unveil it and then double-click the
title of a web line under Capture to capture packets that are on the interface1. For instance, if one
intends to capture traffics on his wireless networks, he should click his wireless interface. One
can organize advanced structures by pressing Capture > Options.
1 Davidoff, Sherri, and Jonathan Ham. Network forensics: tracking hackers through cyberspace. Vol. 2014. Upper
Saddle River: Prentice hall
3
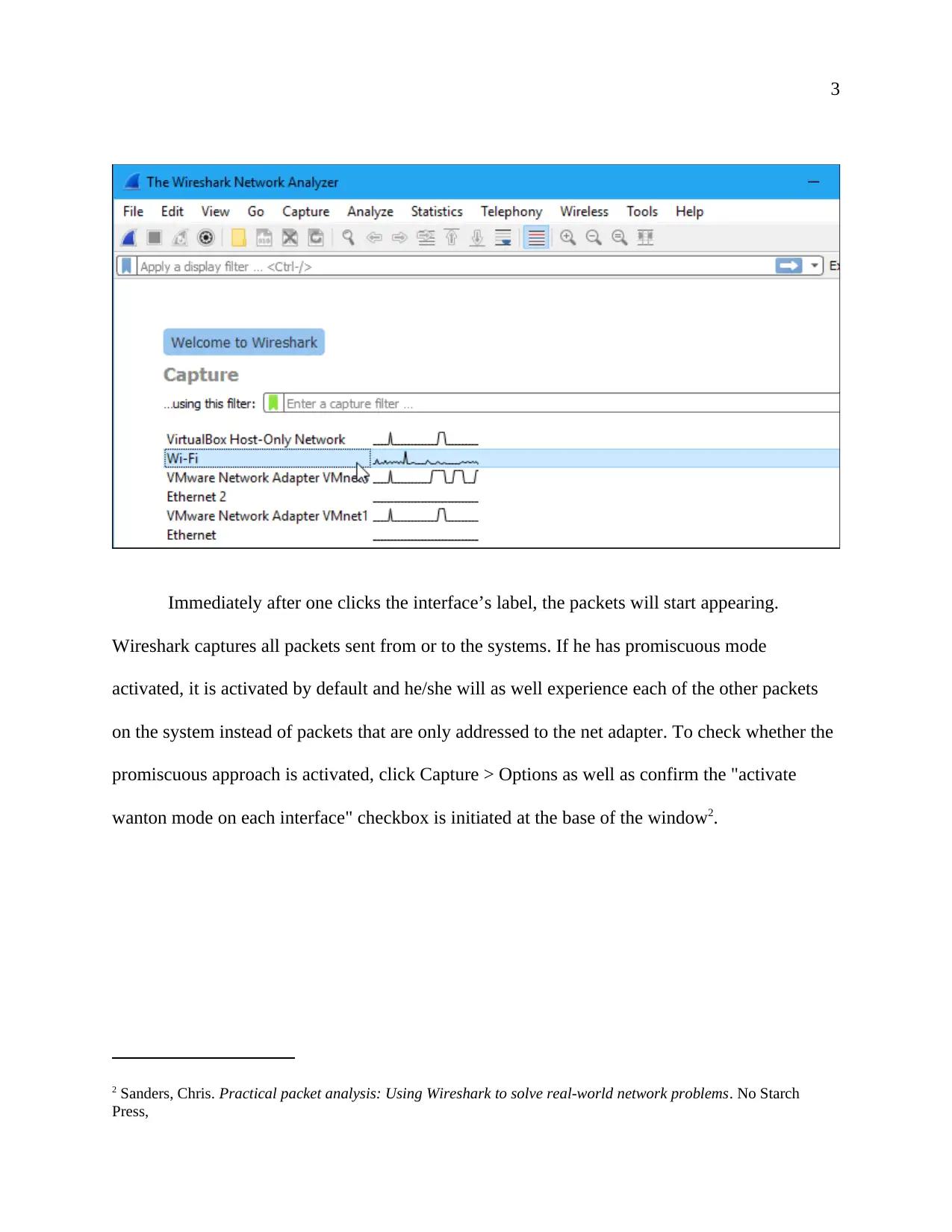
Immediately after one clicks the interface’s label, the packets will start appearing.
Wireshark captures all packets sent from or to the systems. If he has promiscuous mode
activated, it is activated by default and he/she will as well experience each of the other packets
on the system instead of packets that are only addressed to the net adapter. To check whether the
promiscuous approach is activated, click Capture > Options as well as confirm the "activate
wanton mode on each interface" checkbox is initiated at the base of the window2.
2 Sanders, Chris. Practical packet analysis: Using Wireshark to solve real-world network problems. No Starch
Press,
Immediately after one clicks the interface’s label, the packets will start appearing.
Wireshark captures all packets sent from or to the systems. If he has promiscuous mode
activated, it is activated by default and he/she will as well experience each of the other packets
on the system instead of packets that are only addressed to the net adapter. To check whether the
promiscuous approach is activated, click Capture > Options as well as confirm the "activate
wanton mode on each interface" checkbox is initiated at the base of the window2.
2 Sanders, Chris. Practical packet analysis: Using Wireshark to solve real-world network problems. No Starch
Press,
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
4
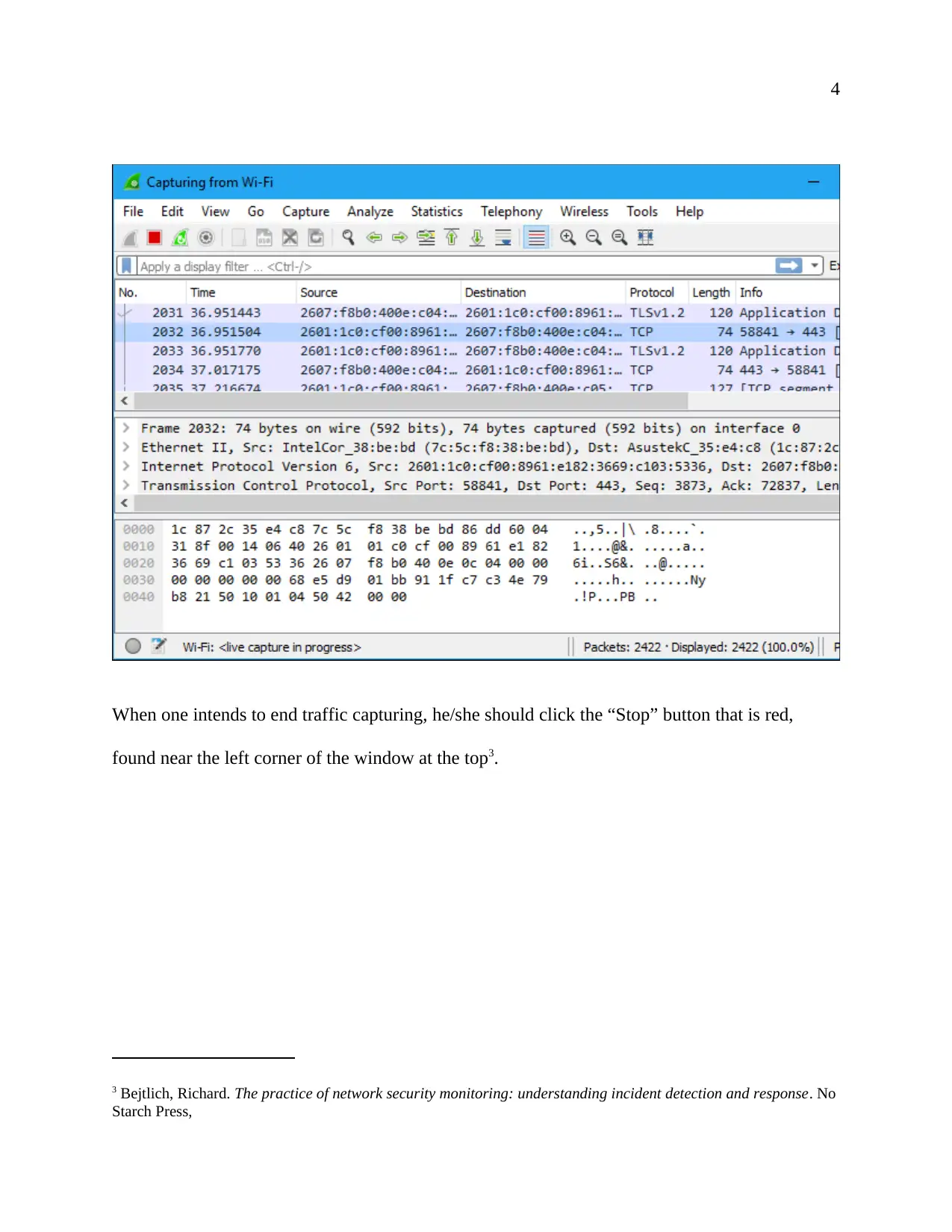
When one intends to end traffic capturing, he/she should click the “Stop” button that is red,
found near the left corner of the window at the top3.
3 Bejtlich, Richard. The practice of network security monitoring: understanding incident detection and response. No
Starch Press,
When one intends to end traffic capturing, he/she should click the “Stop” button that is red,
found near the left corner of the window at the top3.
3 Bejtlich, Richard. The practice of network security monitoring: understanding incident detection and response. No
Starch Press,
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
5
Data decipher
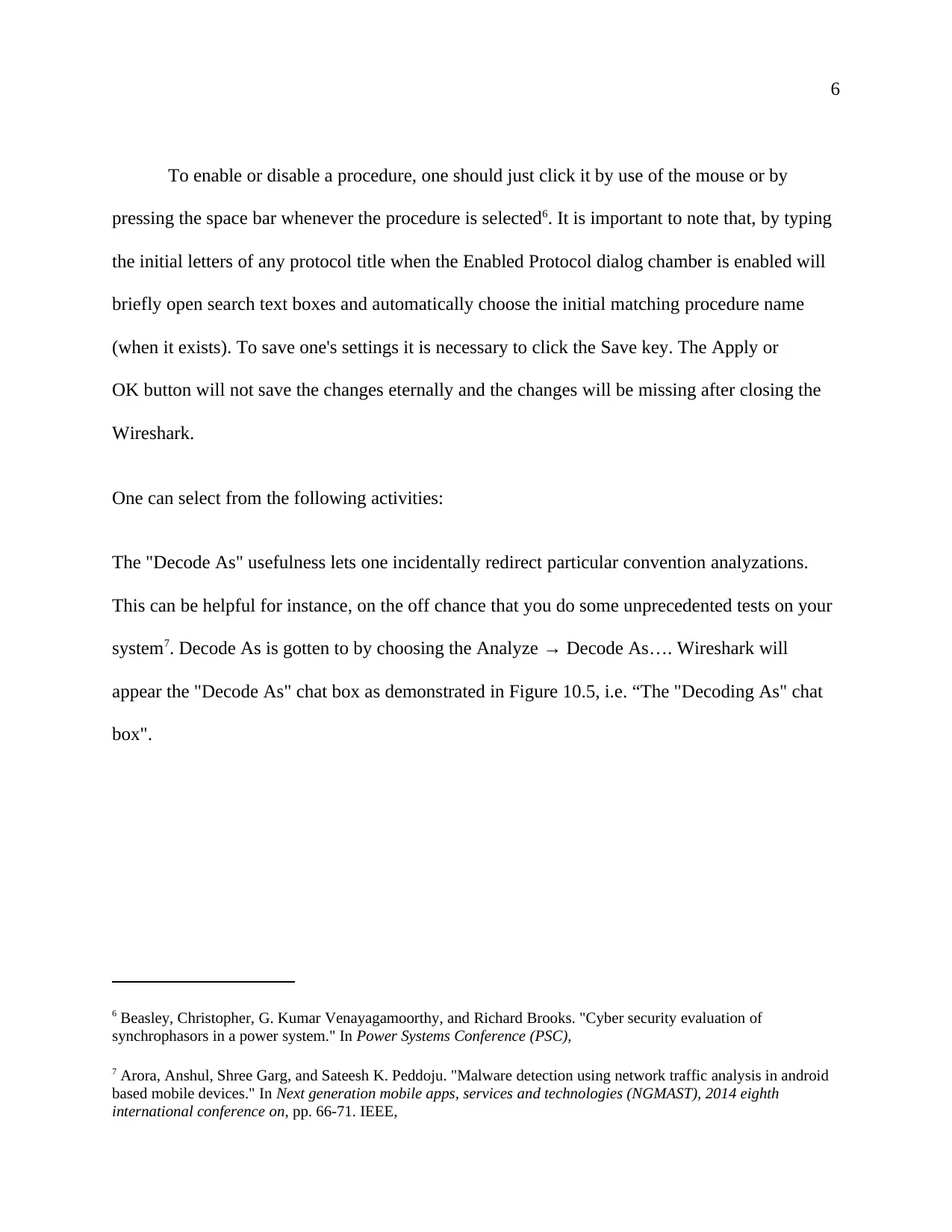
Dissecting a whole packet will typically comprise a number of dissectors because each
procedure has its specific dissector4. As Wireshark attempts to get the ideal dissector for every
packet (by use of heuristics “guessing” and static “routes”), it might pick wrong dissectors in
specific cases. The Enabled Procedures dialog boxes let one disable or enable specific
procedures. All procedures are activated by default. If a protocol is inactivated, Wireshark stops
to process a packet each time that procedure comes across.
To disable or enable protocols choose to Analyze → Enabled Procedures…. Wireshark will
bring the “Enabled Protocol” dialog boxes as illustrated in Diagram 10.4, i.e.: “The “Enabled
Protocol” dialog box”5.
4 Sanders, Chris, and Jason Smith. Applied network security monitoring: collection, detection, and analysis.
Elsevier,
5 Urias, Vincent, Brian Van Leeuwen, and Bryan Richardson. "Supervisory Command and Data Acquisition
(SCADA) system cyber security analysis using a live, virtual, and constructive (LVC) testbed." In Military
Communications Conference, 2012-MILCOM 2012, pp. 1-8. IEEE
Data decipher
Dissecting a whole packet will typically comprise a number of dissectors because each
procedure has its specific dissector4. As Wireshark attempts to get the ideal dissector for every
packet (by use of heuristics “guessing” and static “routes”), it might pick wrong dissectors in
specific cases. The Enabled Procedures dialog boxes let one disable or enable specific
procedures. All procedures are activated by default. If a protocol is inactivated, Wireshark stops
to process a packet each time that procedure comes across.
To disable or enable protocols choose to Analyze → Enabled Procedures…. Wireshark will
bring the “Enabled Protocol” dialog boxes as illustrated in Diagram 10.4, i.e.: “The “Enabled
Protocol” dialog box”5.
4 Sanders, Chris, and Jason Smith. Applied network security monitoring: collection, detection, and analysis.
Elsevier,
5 Urias, Vincent, Brian Van Leeuwen, and Bryan Richardson. "Supervisory Command and Data Acquisition
(SCADA) system cyber security analysis using a live, virtual, and constructive (LVC) testbed." In Military
Communications Conference, 2012-MILCOM 2012, pp. 1-8. IEEE
6
To enable or disable a procedure, one should just click it by use of the mouse or by
pressing the space bar whenever the procedure is selected6. It is important to note that, by typing
the initial letters of any protocol title when the Enabled Protocol dialog chamber is enabled will
briefly open search text boxes and automatically choose the initial matching procedure name
(when it exists). To save one's settings it is necessary to click the Save key. The Apply or
OK button will not save the changes eternally and the changes will be missing after closing the
Wireshark.
One can select from the following activities:
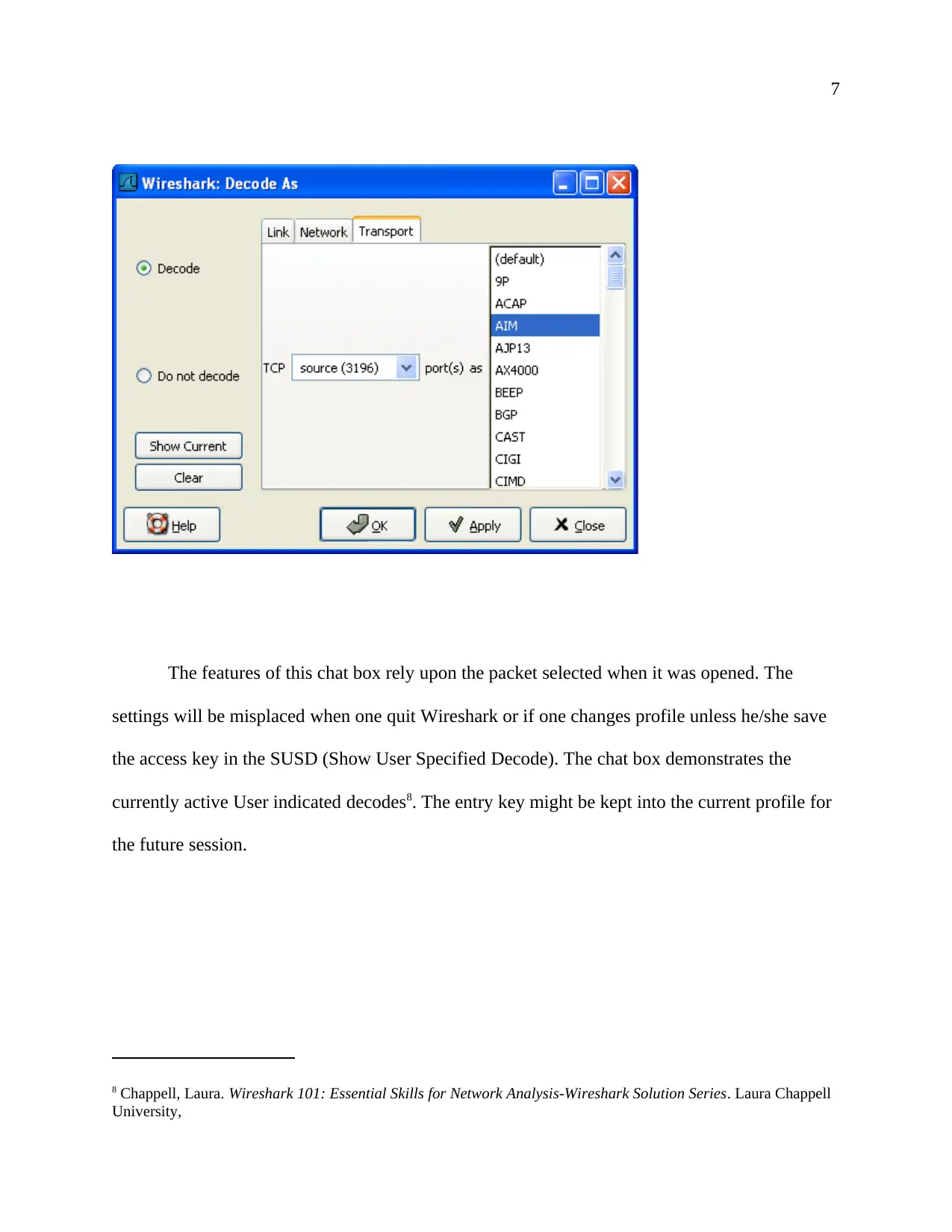
The "Decode As" usefulness lets one incidentally redirect particular convention analyzations.
This can be helpful for instance, on the off chance that you do some unprecedented tests on your
system7. Decode As is gotten to by choosing the Analyze → Decode As…. Wireshark will
appear the "Decode As" chat box as demonstrated in Figure 10.5, i.e. “The "Decoding As" chat
box".
6 Beasley, Christopher, G. Kumar Venayagamoorthy, and Richard Brooks. "Cyber security evaluation of
synchrophasors in a power system." In Power Systems Conference (PSC),
7 Arora, Anshul, Shree Garg, and Sateesh K. Peddoju. "Malware detection using network traffic analysis in android
based mobile devices." In Next generation mobile apps, services and technologies (NGMAST), 2014 eighth
international conference on, pp. 66-71. IEEE,
To enable or disable a procedure, one should just click it by use of the mouse or by
pressing the space bar whenever the procedure is selected6. It is important to note that, by typing
the initial letters of any protocol title when the Enabled Protocol dialog chamber is enabled will
briefly open search text boxes and automatically choose the initial matching procedure name
(when it exists). To save one's settings it is necessary to click the Save key. The Apply or
OK button will not save the changes eternally and the changes will be missing after closing the
Wireshark.
One can select from the following activities:
The "Decode As" usefulness lets one incidentally redirect particular convention analyzations.
This can be helpful for instance, on the off chance that you do some unprecedented tests on your
system7. Decode As is gotten to by choosing the Analyze → Decode As…. Wireshark will
appear the "Decode As" chat box as demonstrated in Figure 10.5, i.e. “The "Decoding As" chat
box".
6 Beasley, Christopher, G. Kumar Venayagamoorthy, and Richard Brooks. "Cyber security evaluation of
synchrophasors in a power system." In Power Systems Conference (PSC),
7 Arora, Anshul, Shree Garg, and Sateesh K. Peddoju. "Malware detection using network traffic analysis in android
based mobile devices." In Next generation mobile apps, services and technologies (NGMAST), 2014 eighth
international conference on, pp. 66-71. IEEE,
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
7
The features of this chat box rely upon the packet selected when it was opened. The
settings will be misplaced when one quit Wireshark or if one changes profile unless he/she save
the access key in the SUSD (Show User Specified Decode). The chat box demonstrates the
currently active User indicated decodes8. The entry key might be kept into the current profile for
the future session.
8 Chappell, Laura. Wireshark 101: Essential Skills for Network Analysis-Wireshark Solution Series. Laura Chappell
University,
The features of this chat box rely upon the packet selected when it was opened. The
settings will be misplaced when one quit Wireshark or if one changes profile unless he/she save
the access key in the SUSD (Show User Specified Decode). The chat box demonstrates the
currently active User indicated decodes8. The entry key might be kept into the current profile for
the future session.
8 Chappell, Laura. Wireshark 101: Essential Skills for Network Analysis-Wireshark Solution Series. Laura Chappell
University,
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

8
Question 2
Explain the communication-taking place between your machine and the web server.
Answer:
Several links between the webserver and machine occur at Transmission Control
Protocols/Internet Protocols (TCP/IP) pile. Hyper Text Transfer Protocol (HTTP), applied for
transporting website pages9. TCP/IP stack is made up of four layers which are: Network,
Internet, Transport, and Application. There are diverse protocols that are utilized to regulate the
movement of data at each layer, and all are computer programs (running on the PC) that are
applied to arrange the data into a packet when moving down the Transmission Control
9 Hunt, Ray, and Sherali Zeadally. "Network forensics: an analysis of techniques, tools, and trends." Computer 45,
no. 12
Question 2
Explain the communication-taking place between your machine and the web server.
Answer:
Several links between the webserver and machine occur at Transmission Control
Protocols/Internet Protocols (TCP/IP) pile. Hyper Text Transfer Protocol (HTTP), applied for
transporting website pages9. TCP/IP stack is made up of four layers which are: Network,
Internet, Transport, and Application. There are diverse protocols that are utilized to regulate the
movement of data at each layer, and all are computer programs (running on the PC) that are
applied to arrange the data into a packet when moving down the Transmission Control
9 Hunt, Ray, and Sherali Zeadally. "Network forensics: an analysis of techniques, tools, and trends." Computer 45,
no. 12
9
Protocol/Internet Protocol stacks. Packets are made by a combination of the TCP or UDP
(Transport Layer title), the Application Layer information, as well as the IP layer title (the Layer
take the packets and then turn it into frames)
The Transport Layer is in charge of relegating source as well as goal port numbers to
applications. The Transport Layer for tending to use port numbers where they run from 1 to
65,535. Port numbers from 0 to 1023 are known as "well-known ports10. The port numbers
underneath 256 are saved for open (standard) benefits that keep running at the Application
Layer. Here are two or three: 80 for HTTP, 53 for DNS (UDP for area determination and TCP
for zone exchanges), and 25 for SMTP. Ports numbering from 1024 to 65,535 are utilized for
customer-side applications - the website program being used by the machine to peruse this page.
The Application Layer comprises of all applications that utilize the system to transport
information. Applications transfer information to the subsequent layer in the TCP/IP stack and
after that keep on performing different capacities until the point when an answer is gotten. The
Application Layer utilizes host terms (such as www.dalantech.com) for tending to11. Cases of
application layer conventions: SMTP - electronic mail, HTTP - web perusing, DNS - settling
hostnames to the IP addresses. The primary reason for the Application Layer is to give a request
as well as language structure among applications which, are running on various operating
frameworks - like a translator. The information that is sent by an application that uses the system
10 Asrodia, Pallavi, and Hemlata Patel. "Network traffic analysis using packet sniffer." International journal of
engineering research and applications 2, no
11 Hunt, Ray, and Sherali Zeadally. "Network forensics: an analysis of techniques, tools, and trends." Computer 45,
no. 12
Protocol/Internet Protocol stacks. Packets are made by a combination of the TCP or UDP
(Transport Layer title), the Application Layer information, as well as the IP layer title (the Layer
take the packets and then turn it into frames)
The Transport Layer is in charge of relegating source as well as goal port numbers to
applications. The Transport Layer for tending to use port numbers where they run from 1 to
65,535. Port numbers from 0 to 1023 are known as "well-known ports10. The port numbers
underneath 256 are saved for open (standard) benefits that keep running at the Application
Layer. Here are two or three: 80 for HTTP, 53 for DNS (UDP for area determination and TCP
for zone exchanges), and 25 for SMTP. Ports numbering from 1024 to 65,535 are utilized for
customer-side applications - the website program being used by the machine to peruse this page.
The Application Layer comprises of all applications that utilize the system to transport
information. Applications transfer information to the subsequent layer in the TCP/IP stack and
after that keep on performing different capacities until the point when an answer is gotten. The
Application Layer utilizes host terms (such as www.dalantech.com) for tending to11. Cases of
application layer conventions: SMTP - electronic mail, HTTP - web perusing, DNS - settling
hostnames to the IP addresses. The primary reason for the Application Layer is to give a request
as well as language structure among applications which, are running on various operating
frameworks - like a translator. The information that is sent by an application that uses the system
10 Asrodia, Pallavi, and Hemlata Patel. "Network traffic analysis using packet sniffer." International journal of
engineering research and applications 2, no
11 Hunt, Ray, and Sherali Zeadally. "Network forensics: an analysis of techniques, tools, and trends." Computer 45,
no. 12
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
10
is designed to fit in with one of a few set principles. The accepting PC can comprehend the
information that is being sent regardless of whether it is running an unexpected operating
framework in comparison to the sender because of the measures that all system applications
adjust to.
The Internet Layer acts like the "adhesive" that clamps networking together where it allows the
transfer, receiving, as well as routing of information.
The Network Layer comprises of one’s NIC (Network Interface Card) as well as the cable linked
to it. Data is transmitted and received by the physical medium. The Network Layer utilizes MAC
(Media Access Control) addresses, talked about prior, for an address. The Media Access Control
address is settled at the time an interface was made and cannot be altered12. There are a couple of
special cases, such as DSL switches that enable ones to clone the Media Access Control address
of the Network Interface Card in the computer.
Question 3
Write a report on the technology used to implement this https site giving an overview of
how it works history of the technology & advantages/disadvantages of the security methods
adopted.
Solution
12 Hunt, Ray, and Sherali Zeadally. "Network forensics: an analysis of techniques, tools, and trends." Computer 45,
no. 12
is designed to fit in with one of a few set principles. The accepting PC can comprehend the
information that is being sent regardless of whether it is running an unexpected operating
framework in comparison to the sender because of the measures that all system applications
adjust to.
The Internet Layer acts like the "adhesive" that clamps networking together where it allows the
transfer, receiving, as well as routing of information.
The Network Layer comprises of one’s NIC (Network Interface Card) as well as the cable linked
to it. Data is transmitted and received by the physical medium. The Network Layer utilizes MAC
(Media Access Control) addresses, talked about prior, for an address. The Media Access Control
address is settled at the time an interface was made and cannot be altered12. There are a couple of
special cases, such as DSL switches that enable ones to clone the Media Access Control address
of the Network Interface Card in the computer.
Question 3
Write a report on the technology used to implement this https site giving an overview of
how it works history of the technology & advantages/disadvantages of the security methods
adopted.
Solution
12 Hunt, Ray, and Sherali Zeadally. "Network forensics: an analysis of techniques, tools, and trends." Computer 45,
no. 12
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
11
Being extensively utilized on the HTTPS (Hypertext transfer protocol secure) or HTTP
(internet hypertext transfer protocol) is an allowance for safe communications over a PC
network. The communication protocol is encoded by TLS (Transport Layer Security) in the
Hypertext transfer protocol secure or its precursor SSL (Secure Sockets Layer).This protocol can
likewise be denoted to a HTTP over SSL, or HTTP over TLS13. It is the administrator obligation
to generate a public key license for the website server to make a website server receive HTTPS
links. For a web browser to consent to it deprived of warning the certificate must be signed by a
dependable certificate authority.
Consequently, the protocol is as well often known as hypertext transfer protocol over
SSL or hypertext transfer protocol over TLS. To make website servers to take HTTPS links, the
administrator should generate public key certificates for the website servers. This license should
be approved by a trusted licensing body for the website browser to take it without any warning.
The certificate owner is certified by the authority as the regulator of the website server that
grants it. In the year 1994 Netscape Communication produced HTTPS aimed at its Netscape
Navigator website browser. HTTPS was formerly utilized with SSL procedure. HTTPS was
officially detailed by a tool known as RFC 2818 in the year 2000 as SSL advancd into TLS
(Transport Layer Security).HTTPS connections historically were mainly utilized for
disbursement dealings on the email, World and for delicate transactions in corporate information
systems
13 Chappell, Laura. Wireshark 101: Essential Skills for Network Analysis-Wireshark Solution Series. Laura Chappell
University
Being extensively utilized on the HTTPS (Hypertext transfer protocol secure) or HTTP
(internet hypertext transfer protocol) is an allowance for safe communications over a PC
network. The communication protocol is encoded by TLS (Transport Layer Security) in the
Hypertext transfer protocol secure or its precursor SSL (Secure Sockets Layer).This protocol can
likewise be denoted to a HTTP over SSL, or HTTP over TLS13. It is the administrator obligation
to generate a public key license for the website server to make a website server receive HTTPS
links. For a web browser to consent to it deprived of warning the certificate must be signed by a
dependable certificate authority.
Consequently, the protocol is as well often known as hypertext transfer protocol over
SSL or hypertext transfer protocol over TLS. To make website servers to take HTTPS links, the
administrator should generate public key certificates for the website servers. This license should
be approved by a trusted licensing body for the website browser to take it without any warning.
The certificate owner is certified by the authority as the regulator of the website server that
grants it. In the year 1994 Netscape Communication produced HTTPS aimed at its Netscape
Navigator website browser. HTTPS was formerly utilized with SSL procedure. HTTPS was
officially detailed by a tool known as RFC 2818 in the year 2000 as SSL advancd into TLS
(Transport Layer Security).HTTPS connections historically were mainly utilized for
disbursement dealings on the email, World and for delicate transactions in corporate information
systems
13 Chappell, Laura. Wireshark 101: Essential Skills for Network Analysis-Wireshark Solution Series. Laura Chappell
University
12
Originally, hypertext transfer protocol links were basically utilized for installment
exchanges on the email, World Wide Website and for delicate businesses in corporate data
frameworks. Since 2018, hypertext transfer protocol (HTTPS) is utilized more frequently by
website users than the first non-secure hypertext transfer protocol, essentially to ensure page
credibility on a wider range of sites; secure records; and keeping client communication,
personality, as well as website perusing private14.
Benefits of HTTPS
o Data Honesty: When information is sent free, it is feasible for an outsider to get in
between the browser and the server and access everything, however, much more terrible,
when they access it, they may transform it.
o Identity Confirmation: A certificate ensures the data a program is getting begins in the
normal space. It is a certification that when a client sends delicate information, it's being
sent to the intended place, and not to a malevolent outsider
o SEO: Google desires to transfer its clients to safe sites hence making HTTPS links a rank
signal.
o Trust: Lastly, the green padlock shows that when one takes safety seriously, it helps to
give clients assurance.
Disadvantage
14 Sanders, Chris, and Jason Smith. Applied network security monitoring: collection, detection, and analysis.
Elsevier
Originally, hypertext transfer protocol links were basically utilized for installment
exchanges on the email, World Wide Website and for delicate businesses in corporate data
frameworks. Since 2018, hypertext transfer protocol (HTTPS) is utilized more frequently by
website users than the first non-secure hypertext transfer protocol, essentially to ensure page
credibility on a wider range of sites; secure records; and keeping client communication,
personality, as well as website perusing private14.
Benefits of HTTPS
o Data Honesty: When information is sent free, it is feasible for an outsider to get in
between the browser and the server and access everything, however, much more terrible,
when they access it, they may transform it.
o Identity Confirmation: A certificate ensures the data a program is getting begins in the
normal space. It is a certification that when a client sends delicate information, it's being
sent to the intended place, and not to a malevolent outsider
o SEO: Google desires to transfer its clients to safe sites hence making HTTPS links a rank
signal.
o Trust: Lastly, the green padlock shows that when one takes safety seriously, it helps to
give clients assurance.
Disadvantage
14 Sanders, Chris, and Jason Smith. Applied network security monitoring: collection, detection, and analysis.
Elsevier
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 14
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.

