COIT 20246 Assignment Submission: Computing and Networking Concepts
VerifiedAdded on 2020/03/23
|10
|4091
|64
Homework Assignment
AI Summary
This homework assignment for COIT 20246 requires students to research and summarize various topics in computer science and networking. The assignment covers ten weeks, with each week focusing on a specific area. Week 1 involves summarizing an individual who significantly influenced modern computer architecture, such as John von Neumann. Week 2 focuses on an individual who impacted operating systems, like Bill Gates. Week 3 explores the networks that led to the internet's development, such as BITNET. Week 4 examines Layer 2 protocols, with a focus on ARP. Week 5 highlights a famous hacker, Kevin Mitnick. The assignment requires students to use literature and online resources, cite them in Harvard format, and summarize the resources in their own words, avoiding direct copying. The tasks cover a wide range of topics within the computing field, emphasizing the evolution of technologies and the individuals who shaped them. The assignment aims to assess the student's understanding of key concepts in computer science and their ability to synthesize information from various sources.
COIT 20246 ASSIGNMENT SUBMISSION
Due date: Thursday Week 11 (2PM AEST)
Part: Written Assessment
Weighting: 30% of total assessment.
Submission: Electronic (see course website for details)
Instructions
It will be necessary to use literature/online resources to complete this
assignment, please ensure you cite and reference any such materials using
the Harvard format.
DO NOT copy content directly from either the text or Internet resources: this
assignment is to be in your own words. You will lose marks if you do not
use your own words!
Please complete your assignment using this submission template file,
inserting your responses where indicated.
DO NOT delete the marking criteria page – changes are permitted to the
formatting of other pages including the headers and footers.
Please fill in the following details:
Student Name
Student Number
Due date: Thursday Week 11 (2PM AEST)
Part: Written Assessment
Weighting: 30% of total assessment.
Submission: Electronic (see course website for details)
Instructions
It will be necessary to use literature/online resources to complete this
assignment, please ensure you cite and reference any such materials using
the Harvard format.
DO NOT copy content directly from either the text or Internet resources: this
assignment is to be in your own words. You will lose marks if you do not
use your own words!
Please complete your assignment using this submission template file,
inserting your responses where indicated.
DO NOT delete the marking criteria page – changes are permitted to the
formatting of other pages including the headers and footers.
Please fill in the following details:
Student Name
Student Number
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Tasks
There are ten (10) tasks, one for each week: the tasks are detailed below. There is a
table to complete for each task. Please fill in the information required.
Note: Each resource summary should be around 200-300 words.
Week 1
The text discusses the elements of modern computing architecture however is largely silent
on the individuals who played a role in its development. Find and summarise a resource that
describes ONE such individual. The individual should have had a significant influence on the
development of computers and/or components of modern computing architecture.
Title: Mordern computer Architecture
Reference: History, T. 2017. John von Neumann - Computing History. [online]
Computinghistory.org.uk. Available at: http://www.computinghistory.org.uk/det/3665/john-von-
neumann
Link: http://www.computinghistory.org.uk/det/3665/john-von-neumann/
Summary: John von Neumann is a famous mathematician in the field of modern architecture
of the computers. This article is mainly emphasised because the complete overbiew of the
architecture of the modern computer would be incomplete without the contribution of the
author of the article. It has been stated in the article that due to the factor of John von
Neumann concept the computer with modern concept which was considered to be fast was
invented. He suggested that the modern computer could be consisting of simple structure
which is fixed which can be affective in the same period of time. The conditional control flow
transfer that mainly control the sequential flow of the program. Reinitiating and interruption in
the flow of the program can be done at any time. A model was proposed in which same
memory allocation was done in order to make it more affective by mainly utilizing the
processing unit of the system, and use the data and the instructions related to it at any time.
This concept of the system is well known as tuning machine which mainly comprised of
architecture which is sequential and based mainly upon Von Neumann Architecture. The
stored program in the digital computer is based on the theory of read and write with regards
to the digital memory which is called the RAM and these concepts are mainly based upon the
ENIAC and colossus. This architecture is mainly based upon the concept of sequential
programming switching mechanism. The main advantage that can be achieved from the
concept is that process controlling is managed in a better way and the best outcome of the
system can be achieved. When relating to the utility aspect with regards to the system is that
the software and the application can be manipulated with a better response and involve more
flexibility.
Week 2
The text discusses the components and activities of operating systems however is largely
silent on the individuals who played a role in their development. Find and summarise a
resource that describes ONE such individual. The individual should have had a significant
influence on the writing or development of operating systems.
Title: Bill gates influencing windows operating system
Reference: Influentialleadership.com. 2017. Bill Gates — Influential Leadership. [online]
Available at: http://influentialleadership.com/bill-gates/
URL: http://influentialleadership.com/bill-gates/
There are ten (10) tasks, one for each week: the tasks are detailed below. There is a
table to complete for each task. Please fill in the information required.
Note: Each resource summary should be around 200-300 words.
Week 1
The text discusses the elements of modern computing architecture however is largely silent
on the individuals who played a role in its development. Find and summarise a resource that
describes ONE such individual. The individual should have had a significant influence on the
development of computers and/or components of modern computing architecture.
Title: Mordern computer Architecture
Reference: History, T. 2017. John von Neumann - Computing History. [online]
Computinghistory.org.uk. Available at: http://www.computinghistory.org.uk/det/3665/john-von-
neumann
Link: http://www.computinghistory.org.uk/det/3665/john-von-neumann/
Summary: John von Neumann is a famous mathematician in the field of modern architecture
of the computers. This article is mainly emphasised because the complete overbiew of the
architecture of the modern computer would be incomplete without the contribution of the
author of the article. It has been stated in the article that due to the factor of John von
Neumann concept the computer with modern concept which was considered to be fast was
invented. He suggested that the modern computer could be consisting of simple structure
which is fixed which can be affective in the same period of time. The conditional control flow
transfer that mainly control the sequential flow of the program. Reinitiating and interruption in
the flow of the program can be done at any time. A model was proposed in which same
memory allocation was done in order to make it more affective by mainly utilizing the
processing unit of the system, and use the data and the instructions related to it at any time.
This concept of the system is well known as tuning machine which mainly comprised of
architecture which is sequential and based mainly upon Von Neumann Architecture. The
stored program in the digital computer is based on the theory of read and write with regards
to the digital memory which is called the RAM and these concepts are mainly based upon the
ENIAC and colossus. This architecture is mainly based upon the concept of sequential
programming switching mechanism. The main advantage that can be achieved from the
concept is that process controlling is managed in a better way and the best outcome of the
system can be achieved. When relating to the utility aspect with regards to the system is that
the software and the application can be manipulated with a better response and involve more
flexibility.
Week 2
The text discusses the components and activities of operating systems however is largely
silent on the individuals who played a role in their development. Find and summarise a
resource that describes ONE such individual. The individual should have had a significant
influence on the writing or development of operating systems.
Title: Bill gates influencing windows operating system
Reference: Influentialleadership.com. 2017. Bill Gates — Influential Leadership. [online]
Available at: http://influentialleadership.com/bill-gates/
URL: http://influentialleadership.com/bill-gates/

Summary: The main discussion in the above stated article is the influence of Bill Gates in the
modern advancement relating to the operating system. The main reason for choosing the
article is that the name of the author played a very vital role in the field of modern computer
with the operating system as the main field of concern. Bill gates is considered as the pioneer
in the above stated field due to the factor that the first concept of the windows was initiated
form him. The main concept of the architecture is based upon the concept of windows that
maintains an access point that expands the idea of accessing an information from a single
platform. It actually emphasis the user to use the whole processing unit of the computer
system. With the advancement related to the windows concept with it the operating system
the name bill gates became very much famous and it became the first choice of the user due
to the new features which is presents to the user. He also became the wealthiest person in
the whole world with his brand name Microsoft. In the personal life bill gates it was observed
that he was born in an upper middle class family, he graduated in the year 1973 and enrolled
into the Harvard collage. He mainly used his maximum team of his team in the computer
research than putting emphasis on the study syllabus. He was very fond of coding when
related to the computer and he initiated the Microsoft company with Paul Allen after making
an agreement with the micro instrument and telemetry system.
modern advancement relating to the operating system. The main reason for choosing the
article is that the name of the author played a very vital role in the field of modern computer
with the operating system as the main field of concern. Bill gates is considered as the pioneer
in the above stated field due to the factor that the first concept of the windows was initiated
form him. The main concept of the architecture is based upon the concept of windows that
maintains an access point that expands the idea of accessing an information from a single
platform. It actually emphasis the user to use the whole processing unit of the computer
system. With the advancement related to the windows concept with it the operating system
the name bill gates became very much famous and it became the first choice of the user due
to the new features which is presents to the user. He also became the wealthiest person in
the whole world with his brand name Microsoft. In the personal life bill gates it was observed
that he was born in an upper middle class family, he graduated in the year 1973 and enrolled
into the Harvard collage. He mainly used his maximum team of his team in the computer
research than putting emphasis on the study syllabus. He was very fond of coding when
related to the computer and he initiated the Microsoft company with Paul Allen after making
an agreement with the micro instrument and telemetry system.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide

Week 3
The Internet didn’t just appear – it was an evolution from earlier networks. Find and
summarise a resource that describes ONE of the networks that led to the development of the
modern Internet.
Title: Influence of BITNET in the advancement of modern Internet
Reference: Livinginternet.com. 2017. BITNET History - Ira Fuchs, Greydon Freeman, Mailing
Lists, Usenet. [online] Available at: https://www.livinginternet.com/u/ui_bitnet.htm
URL: https://www.livinginternet.com/u/ui_bitnet.htm
Summary: This article mainly deals with the influencing factor which is related to the BITNET
which can be directly be related to the modern internet. This article mainly related to the
features and the history of the BITNET network. The reason behind choosing the article is
that BITMAP is considered one of the most important and primary aspect of the networking
system which can be very much important in the field of advancement of the internet system.
The main aspect of the technology is that it can store and forward network which is very much
similar to the UseNet. The full form of the BITNET is that it can implement all the features of
the internet and it is stated that “because of the internet”. The system was formally based on
the IBM’s concept of VNET email system and the remote spoiling communication of the sub
systems. Later on the RSCS was emulated into the other operating system for example DEC
VMS and the UNIX to the extended portion of the BITMAP. The BITMAP introduced many
new concept and features in different fields which can be directly be implemented in the field
of computer internet and which could also be seen in this scenario. The number of services
which are provided by the concept is also very much huge. The concept actually creates a
backbone to the concept of TCP/IP protocols of the computer system with the RSCS based
applications which run above the TCP protocols. The main advantage with the
implementation fo the concept is that it is basically a multi-disciplinary network of system’s
which can be used by more than one user. It can be concluded from the above discussion
that the concept of BITMAP networking system has been highly beneficial in many ways
which the aspect of providing many new features and implementation.
Week 4
Ethernet is an example of a Layer Two (L2) data link protocol that is discussed in the text.
Find and summarise a resource that describes the features and uses of ONE other L2
protocol that is not discussed in the text (i.e. NOT Ethernet).
Title: Address Resolution Protocol (ARP)
Reference: Lifewire. 2017. What Address Resolution Protocol (ARP) does for your computer
network. [online] Available at: https://www.lifewire.com/address-resolution-protocol-817941
URL: https://www.lifewire.com/address-resolution-protocol-817941
Summary: This article puts direct emphasis on the history and the features of the most
common layer 2 protocol which is the Address Resolution protocol (ARP). This article is
mainly chosen because the Address Resolution protocol is considered as the most primary
and useful protocol which is related to the layer 2 which is mainly implemented and used in
the network system. The Address Resolution protocol main function is to convert to physical
network address from the internet protocol address. The Address Resolution protocol is an
essential part in the running of the IP networks which are used in the Ethernet and also in the
concept of Wi-Fi. Relating to the history of the Address Resolution protocol it was developed
in the year 1980 mainly with the intention of creating an address translation protocol. Address
Resolution protocol is mainly implemented in the ATM, network which are physical type and
the token rings. The main advantage that can be achieved from the implementation for the
Address Resolution protocol is that it can manage the overall connections irrespective of a
physical device in particular which are connected to one another. The Address Resolution
The Internet didn’t just appear – it was an evolution from earlier networks. Find and
summarise a resource that describes ONE of the networks that led to the development of the
modern Internet.
Title: Influence of BITNET in the advancement of modern Internet
Reference: Livinginternet.com. 2017. BITNET History - Ira Fuchs, Greydon Freeman, Mailing
Lists, Usenet. [online] Available at: https://www.livinginternet.com/u/ui_bitnet.htm
URL: https://www.livinginternet.com/u/ui_bitnet.htm
Summary: This article mainly deals with the influencing factor which is related to the BITNET
which can be directly be related to the modern internet. This article mainly related to the
features and the history of the BITNET network. The reason behind choosing the article is
that BITMAP is considered one of the most important and primary aspect of the networking
system which can be very much important in the field of advancement of the internet system.
The main aspect of the technology is that it can store and forward network which is very much
similar to the UseNet. The full form of the BITNET is that it can implement all the features of
the internet and it is stated that “because of the internet”. The system was formally based on
the IBM’s concept of VNET email system and the remote spoiling communication of the sub
systems. Later on the RSCS was emulated into the other operating system for example DEC
VMS and the UNIX to the extended portion of the BITMAP. The BITMAP introduced many
new concept and features in different fields which can be directly be implemented in the field
of computer internet and which could also be seen in this scenario. The number of services
which are provided by the concept is also very much huge. The concept actually creates a
backbone to the concept of TCP/IP protocols of the computer system with the RSCS based
applications which run above the TCP protocols. The main advantage with the
implementation fo the concept is that it is basically a multi-disciplinary network of system’s
which can be used by more than one user. It can be concluded from the above discussion
that the concept of BITMAP networking system has been highly beneficial in many ways
which the aspect of providing many new features and implementation.
Week 4
Ethernet is an example of a Layer Two (L2) data link protocol that is discussed in the text.
Find and summarise a resource that describes the features and uses of ONE other L2
protocol that is not discussed in the text (i.e. NOT Ethernet).
Title: Address Resolution Protocol (ARP)
Reference: Lifewire. 2017. What Address Resolution Protocol (ARP) does for your computer
network. [online] Available at: https://www.lifewire.com/address-resolution-protocol-817941
URL: https://www.lifewire.com/address-resolution-protocol-817941
Summary: This article puts direct emphasis on the history and the features of the most
common layer 2 protocol which is the Address Resolution protocol (ARP). This article is
mainly chosen because the Address Resolution protocol is considered as the most primary
and useful protocol which is related to the layer 2 which is mainly implemented and used in
the network system. The Address Resolution protocol main function is to convert to physical
network address from the internet protocol address. The Address Resolution protocol is an
essential part in the running of the IP networks which are used in the Ethernet and also in the
concept of Wi-Fi. Relating to the history of the Address Resolution protocol it was developed
in the year 1980 mainly with the intention of creating an address translation protocol. Address
Resolution protocol is mainly implemented in the ATM, network which are physical type and
the token rings. The main advantage that can be achieved from the implementation for the
Address Resolution protocol is that it can manage the overall connections irrespective of a
physical device in particular which are connected to one another. The Address Resolution
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
protocol operates at the layer 2 of the OSI model. The Address Resolution protocol which is
maintained in every device helps in mapping of the IP too MAC address mapping. A scenario
can arise that when the IP address does not appear in the device then the Address
Resolution protocol is used to send a broadcasting message on the local subset. The host
replies with the help of the corresponding Address Resolution protocol request in order to
create a reply to the broadcasting message. Based on the concept of the Address Resolution
protocol a reverse Address Resolution protocol and an inverse Address Resolution protocol is
also developed which is considered as an important internet protocol.
Week 5
The text mentions the role of hackers in attacks on networked infrastructure. Find and
summarise a resource that describes ONE famous or well-known hacker.
Title: Famous hacker Kevin Mitnick
Reference: Knowbe4.com. 2017. Kevin Mitnick | KnowBe4. [online] Available at:
https://www.knowbe4.com/products/who-is-kevin-mitnick/
URL : https://www.knowbe4.com/products/who-is-kevin-mitnick/
Summary: The above stated article puts direct emphasis on the role of hacker putting
emphasis on a hacker in the real world. The first name which usually comes into mind
regarding the concept is Kevin Mitnick. The article also puts emphasis on the characteristics
of a hacker. Kevin Mitnick is most of the famous hackers who have also participated as a
security consultant. In the nineties the person was announced as the most wanted hacker in
this field. He was also writer of many books. The bypassing of the punch card system was
initiated by him which took place in the city of new York. The attempt which he made to get
the unauthorised access to a network was done in the year 1976, when he was only 16 years
of age. Keven was also arrested ones for his activities which was considered as illegal. He
had intercepted a computer system by stealing the password and had also changed the
network system of a full computer network server. The role of the hacker can be divided into
two parts one being an ethical hacking part and on the other hand is the non-ethical part. It
can be further de divided into two parts that is passive and active. In passive the hacker
would not alter the data and would use it for their own benefit, due to this factor passive
hackers where very difficult to detect. On the other hand an active hacker would alter the data
and make them according to their requirement, the active hackers can be detected quite
easily. Keven was involved in both the styles of hacking. From the above discussion it can be
concluded that kelvin was one of the biggest wanted hackers of all times who was involved in
various activity and ones was also punished for the activity he conducted.
maintained in every device helps in mapping of the IP too MAC address mapping. A scenario
can arise that when the IP address does not appear in the device then the Address
Resolution protocol is used to send a broadcasting message on the local subset. The host
replies with the help of the corresponding Address Resolution protocol request in order to
create a reply to the broadcasting message. Based on the concept of the Address Resolution
protocol a reverse Address Resolution protocol and an inverse Address Resolution protocol is
also developed which is considered as an important internet protocol.
Week 5
The text mentions the role of hackers in attacks on networked infrastructure. Find and
summarise a resource that describes ONE famous or well-known hacker.
Title: Famous hacker Kevin Mitnick
Reference: Knowbe4.com. 2017. Kevin Mitnick | KnowBe4. [online] Available at:
https://www.knowbe4.com/products/who-is-kevin-mitnick/
URL : https://www.knowbe4.com/products/who-is-kevin-mitnick/
Summary: The above stated article puts direct emphasis on the role of hacker putting
emphasis on a hacker in the real world. The first name which usually comes into mind
regarding the concept is Kevin Mitnick. The article also puts emphasis on the characteristics
of a hacker. Kevin Mitnick is most of the famous hackers who have also participated as a
security consultant. In the nineties the person was announced as the most wanted hacker in
this field. He was also writer of many books. The bypassing of the punch card system was
initiated by him which took place in the city of new York. The attempt which he made to get
the unauthorised access to a network was done in the year 1976, when he was only 16 years
of age. Keven was also arrested ones for his activities which was considered as illegal. He
had intercepted a computer system by stealing the password and had also changed the
network system of a full computer network server. The role of the hacker can be divided into
two parts one being an ethical hacking part and on the other hand is the non-ethical part. It
can be further de divided into two parts that is passive and active. In passive the hacker
would not alter the data and would use it for their own benefit, due to this factor passive
hackers where very difficult to detect. On the other hand an active hacker would alter the data
and make them according to their requirement, the active hackers can be detected quite
easily. Keven was involved in both the styles of hacking. From the above discussion it can be
concluded that kelvin was one of the biggest wanted hackers of all times who was involved in
various activity and ones was also punished for the activity he conducted.
Week 6
Society is increasingly reliant on networks and network technologies but they are evolving at
a rapid pace. Find and summarise a resource that describes ONE example of a future
networking technology or trend that will impact society.
Title: Quantum networking system
Reference: Ieeexplore.ieee.org. 2017. Quantum networking and internetworking - IEEE
Journals & Magazine. [online] Available at: http://ieeexplore.ieee.org/document/6246754/
URL : http://ieeexplore.ieee.org/document/6246754/
Summary: The article puts direct limelight on the prospective of the quantum network
computing phenomenon and its direct implementation of the quantum technology which can
be applied to the future which related to network system. It can be stated that the future of the
networking system is directly dependent on the implementation of the quantum technology.
There are mainly three advantages that can be related to the topic. One of the most important
advantage that can be related to the implementation of the technology is directly making te
system more secured. In any system the security of the system plays a very vital role in every
aspect. The main theory of the quantum lies on the concept of qubits. The quantum physical
is mainly used as method in order to detect the eavesdropping. It can make the system more
and more advanced with making the system well isochronized with the technology of the
quantum. It also helps in creating a distributed data system which can be used in order to
make the numerical quantum computation possible which can achieve a much faster
response in the networking system. The teleportation method which is involved in the process
can create a revolution with regards to the communication system. From the above
discussion it can be concluded that the quantum technology can be a successful
implementation in the future related to the network system.
Week 7
The text mentions social business and the impact of the use of social networking platforms.
Find and summarise a resource that describes the history of the development of ONE such
social media platform.
Title: Brief history of Facebook
Reference: Phillips, S. 2017. A brief history of Facebook. [online] the Guardian. Available at:
https://www.theguardian.com/technology/2007/jul/25/media.newmedia
URL : https://www.theguardian.com/technology/2007/jul/25/media.newmedia
Summary: In this article the social networking site which has renovated the world, is taken
into account. Facebook comes among the biggest name in the field of social media. This
article is chosen due to the fact that the Facebook have altered the life of the people in many
aspects. Mark Zuckerberg is the founder and the owner of the Facebook, and he initiated the
social media site from a dormitory of the Harvard university. There are many expansion
technique that are related the Facebook history from its origin in the year 2004.it is one of the
fastest growing social networking site that exist in the recent times. Mark first created a social
networking site with the help of the website of the Harvard university and created a fashmash
of the site and later on the site was named as Facebook. In the recent update Facebook have
implemented many new technological aspect into it which includes haring of video, pictures
post or text. People with the text and the post can revert with their liking and comment on
them if they have any option regarding it. People can also chat and share their current
location with the aspect. Zuckerberg refuses to sell his company to google and to other giants
in the initial stage of the development of the company and on the other hand he refused to
post any advertisement in this regard.
Week 8
With the advent of mass data collection and storage has come data mining. Find and
summarise a resource that describes ONE example where data mining has been used
successfully by a business. You should not use any examples covered in the textbook.
Society is increasingly reliant on networks and network technologies but they are evolving at
a rapid pace. Find and summarise a resource that describes ONE example of a future
networking technology or trend that will impact society.
Title: Quantum networking system
Reference: Ieeexplore.ieee.org. 2017. Quantum networking and internetworking - IEEE
Journals & Magazine. [online] Available at: http://ieeexplore.ieee.org/document/6246754/
URL : http://ieeexplore.ieee.org/document/6246754/
Summary: The article puts direct limelight on the prospective of the quantum network
computing phenomenon and its direct implementation of the quantum technology which can
be applied to the future which related to network system. It can be stated that the future of the
networking system is directly dependent on the implementation of the quantum technology.
There are mainly three advantages that can be related to the topic. One of the most important
advantage that can be related to the implementation of the technology is directly making te
system more secured. In any system the security of the system plays a very vital role in every
aspect. The main theory of the quantum lies on the concept of qubits. The quantum physical
is mainly used as method in order to detect the eavesdropping. It can make the system more
and more advanced with making the system well isochronized with the technology of the
quantum. It also helps in creating a distributed data system which can be used in order to
make the numerical quantum computation possible which can achieve a much faster
response in the networking system. The teleportation method which is involved in the process
can create a revolution with regards to the communication system. From the above
discussion it can be concluded that the quantum technology can be a successful
implementation in the future related to the network system.
Week 7
The text mentions social business and the impact of the use of social networking platforms.
Find and summarise a resource that describes the history of the development of ONE such
social media platform.
Title: Brief history of Facebook
Reference: Phillips, S. 2017. A brief history of Facebook. [online] the Guardian. Available at:
https://www.theguardian.com/technology/2007/jul/25/media.newmedia
URL : https://www.theguardian.com/technology/2007/jul/25/media.newmedia
Summary: In this article the social networking site which has renovated the world, is taken
into account. Facebook comes among the biggest name in the field of social media. This
article is chosen due to the fact that the Facebook have altered the life of the people in many
aspects. Mark Zuckerberg is the founder and the owner of the Facebook, and he initiated the
social media site from a dormitory of the Harvard university. There are many expansion
technique that are related the Facebook history from its origin in the year 2004.it is one of the
fastest growing social networking site that exist in the recent times. Mark first created a social
networking site with the help of the website of the Harvard university and created a fashmash
of the site and later on the site was named as Facebook. In the recent update Facebook have
implemented many new technological aspect into it which includes haring of video, pictures
post or text. People with the text and the post can revert with their liking and comment on
them if they have any option regarding it. People can also chat and share their current
location with the aspect. Zuckerberg refuses to sell his company to google and to other giants
in the initial stage of the development of the company and on the other hand he refused to
post any advertisement in this regard.
Week 8
With the advent of mass data collection and storage has come data mining. Find and
summarise a resource that describes ONE example where data mining has been used
successfully by a business. You should not use any examples covered in the textbook.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide

Title: Implementation of data mining in retailing business
Reference: Saravanan, G. 2017. [online] Available at:
http://www.coolavenues.com/marketing-zone/role-of-data-mining-in-retail-sector
URL : http://www.coolavenues.com/marketing-zone/role-of-data-mining-in-retail-sector
Summary: The article puts direct emphasis on the aspect of the role of the data mining in the
field of business related to mining. There are many advantages that can be related to the
topic. Data mining can be considered as a method which is related to the information system,
by this mean the processor can take action regarding a particular style or type of useful data
from a database or large amount of data. Data mining can be implemented in order to detect
the requirement of the user from the previously stored data ij the database. It can also act as
a mean of detecting the behaviour of the customer, trends that the customer are following and
the customer satisfaction level or different ways of improving the standard of the work that is
expected from the user. The information which is extracted from the process can be used to
strategically implement different processes related to the concept. It is very much important to
take into account the different production techniques which is related to the company. The
best implementation of the data mining concept is in the CR as CRM deals with the customer
relationship management. It can directly help in improving the loyalty which is related to the
customer, gaining the very important aspect which is the customer insight, retaining the
customer and also in implementing focused strategies which is related to the customer.
Reference: Saravanan, G. 2017. [online] Available at:
http://www.coolavenues.com/marketing-zone/role-of-data-mining-in-retail-sector
URL : http://www.coolavenues.com/marketing-zone/role-of-data-mining-in-retail-sector
Summary: The article puts direct emphasis on the aspect of the role of the data mining in the
field of business related to mining. There are many advantages that can be related to the
topic. Data mining can be considered as a method which is related to the information system,
by this mean the processor can take action regarding a particular style or type of useful data
from a database or large amount of data. Data mining can be implemented in order to detect
the requirement of the user from the previously stored data ij the database. It can also act as
a mean of detecting the behaviour of the customer, trends that the customer are following and
the customer satisfaction level or different ways of improving the standard of the work that is
expected from the user. The information which is extracted from the process can be used to
strategically implement different processes related to the concept. It is very much important to
take into account the different production techniques which is related to the company. The
best implementation of the data mining concept is in the CR as CRM deals with the customer
relationship management. It can directly help in improving the loyalty which is related to the
customer, gaining the very important aspect which is the customer insight, retaining the
customer and also in implementing focused strategies which is related to the customer.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Week 9
One of the greatest success stories in application development in recent times has been the
popularity of mobile apps. Find and summarise a resource that describes the story of ONE
successful mobile app developer.
Title: Successful young app developer Robert Nay
Reference: Sutter, J. 2017. 14-year-old creates 'Bubble Ball,' iTunes' most popular free app.
[online] Edition.cnn.com. Available at:
http://edition.cnn.com/2011/TECH/mobile/01/21/bubble.ball.app/
URL : http://edition.cnn.com/2011/TECH/mobile/01/21/bubble.ball.app/
Summary: The main topic which is emphasized is the development of successful application.
This article mainly draws a point on the young and famous developer of application Robert
Nay, he has developed the most important free application ITunes. This article is mainly
chosen due to the factor of the person’s brilliant innovative ideas and its direct implementation
which would make the application field cross a certain level of boundary. On the other and the
developer also developed a famous app named bubble ball which was selected as the most
commonly used free application in the iTunes store and this application was invented by him
at the age of 14 only. This game was considered to be very much simple yet it was very much
attractive for the small kids. In the game there was series of puzzle that the player had to
guide the ball through in order to reach the goal of the game. Then most important aspect
which is very much needed for a game developer is that the person should have immense
knowledge of the programming language which is being used for the game and must have
creative thinking ideas in order to make the game look more realistic. On the other hand the
market need should be taken into account and the choice of the customers. From the above
discussion it can be concluded that the field of the development of a new application is
increasing on a day to day basis and knowledge and the creativity are very much required for
the development of the application.
Week 10
While information systems and technology deliver many benefits to society, they can also
result in (sometimes inadvertent) negative effects and outcomes. Find and summarise a
resource that describes ONE example of where the use of an information system or
technology has led to negative consequences for humans.
Title: Negative consequences of data warehousing
Reference: Burnside, K. 2017. The Disadvantages of a Data Warehouse. [online]
Smallbusiness.chron.com. Available at: http://smallbusiness.chron.com/disadvantages-data-
warehouse-73584.html
URL : http://smallbusiness.chron.com/disadvantages-data-warehouse-73584.html
Summary: In this article direct emphasis is gathered for the concept of data warehousing and
its negative impact. This article is mainly chosen due to the factor that the warehouse
technique is considered as the most important aspect in the information system. This conceit
is implemented in several information system and businesses. Data warehousing is mainly
used in order to find out in particular, the types of useful data from a huge amount of data.
Taking into account the practical aspect of the implementation there are many disadvantages
that can be taken in regards to the implementation. Data warehouse can be considered as a
technique which can be used to extract information which is mainly collected from different
department which can be directly be implemented for the betterment of the different services
that can improve the productivity of the organisation. The bad effect of the data warehouse is
the risk associated with the extra work which need to be done with the aspect. As the data
warehouse can be directly be related to the data collection from a wide range of customers in
some cases it is seen that the organisations database have the same time of data or content
thus as a result of which the data can be copied. Data warehouse can also affect the
flexibility aspect in any organisation. From the above discussion it can be stated that data
One of the greatest success stories in application development in recent times has been the
popularity of mobile apps. Find and summarise a resource that describes the story of ONE
successful mobile app developer.
Title: Successful young app developer Robert Nay
Reference: Sutter, J. 2017. 14-year-old creates 'Bubble Ball,' iTunes' most popular free app.
[online] Edition.cnn.com. Available at:
http://edition.cnn.com/2011/TECH/mobile/01/21/bubble.ball.app/
URL : http://edition.cnn.com/2011/TECH/mobile/01/21/bubble.ball.app/
Summary: The main topic which is emphasized is the development of successful application.
This article mainly draws a point on the young and famous developer of application Robert
Nay, he has developed the most important free application ITunes. This article is mainly
chosen due to the factor of the person’s brilliant innovative ideas and its direct implementation
which would make the application field cross a certain level of boundary. On the other and the
developer also developed a famous app named bubble ball which was selected as the most
commonly used free application in the iTunes store and this application was invented by him
at the age of 14 only. This game was considered to be very much simple yet it was very much
attractive for the small kids. In the game there was series of puzzle that the player had to
guide the ball through in order to reach the goal of the game. Then most important aspect
which is very much needed for a game developer is that the person should have immense
knowledge of the programming language which is being used for the game and must have
creative thinking ideas in order to make the game look more realistic. On the other hand the
market need should be taken into account and the choice of the customers. From the above
discussion it can be concluded that the field of the development of a new application is
increasing on a day to day basis and knowledge and the creativity are very much required for
the development of the application.
Week 10
While information systems and technology deliver many benefits to society, they can also
result in (sometimes inadvertent) negative effects and outcomes. Find and summarise a
resource that describes ONE example of where the use of an information system or
technology has led to negative consequences for humans.
Title: Negative consequences of data warehousing
Reference: Burnside, K. 2017. The Disadvantages of a Data Warehouse. [online]
Smallbusiness.chron.com. Available at: http://smallbusiness.chron.com/disadvantages-data-
warehouse-73584.html
URL : http://smallbusiness.chron.com/disadvantages-data-warehouse-73584.html
Summary: In this article direct emphasis is gathered for the concept of data warehousing and
its negative impact. This article is mainly chosen due to the factor that the warehouse
technique is considered as the most important aspect in the information system. This conceit
is implemented in several information system and businesses. Data warehousing is mainly
used in order to find out in particular, the types of useful data from a huge amount of data.
Taking into account the practical aspect of the implementation there are many disadvantages
that can be taken in regards to the implementation. Data warehouse can be considered as a
technique which can be used to extract information which is mainly collected from different
department which can be directly be implemented for the betterment of the different services
that can improve the productivity of the organisation. The bad effect of the data warehouse is
the risk associated with the extra work which need to be done with the aspect. As the data
warehouse can be directly be related to the data collection from a wide range of customers in
some cases it is seen that the organisations database have the same time of data or content
thus as a result of which the data can be copied. Data warehouse can also affect the
flexibility aspect in any organisation. From the above discussion it can be stated that data

warehouse has a lot in hand with the advantages with it many disadvantage related to the
aspect.
aspect.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
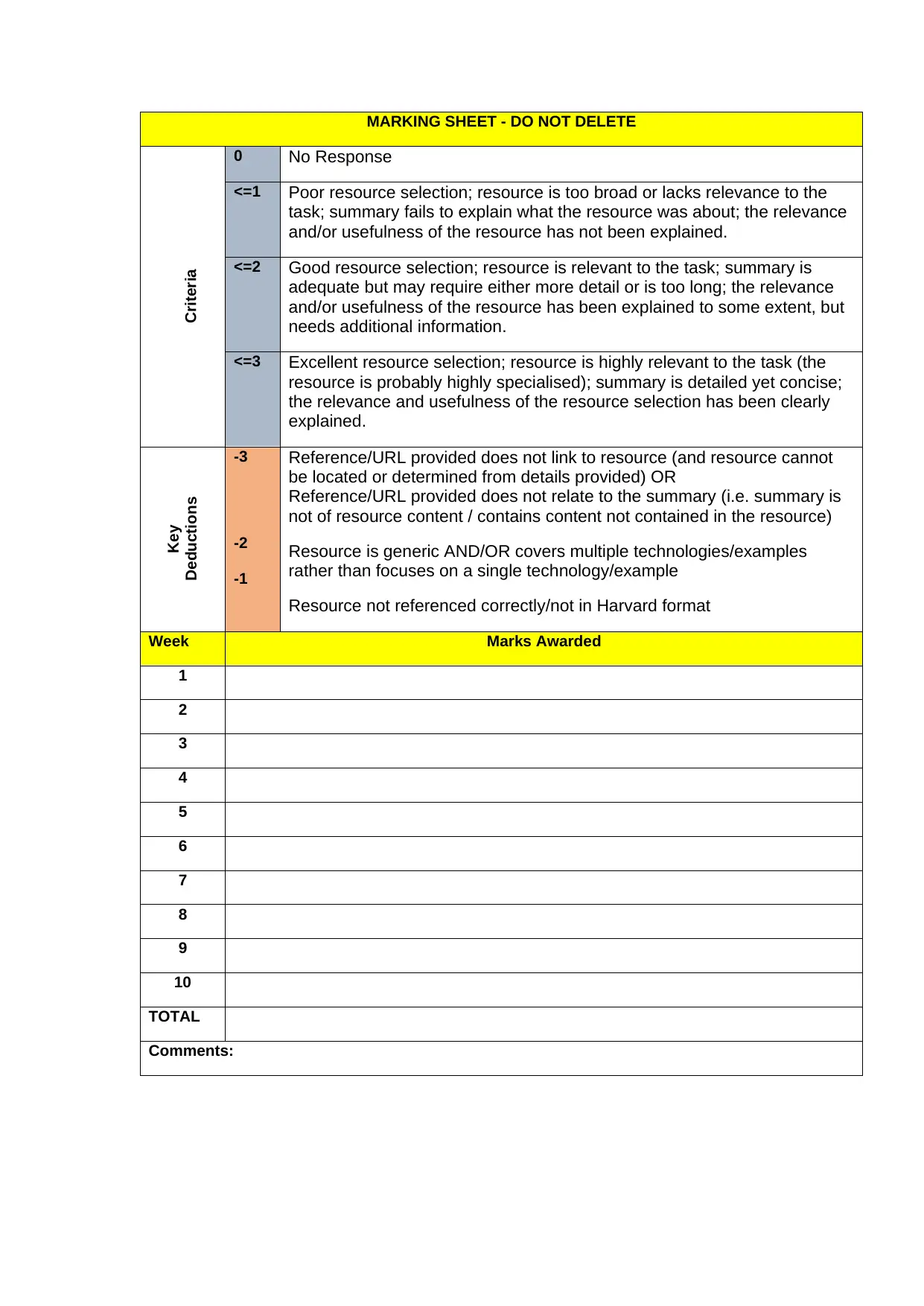
MARKING SHEET - DO NOT DELETE
Criteria
0 No Response
<=1 Poor resource selection; resource is too broad or lacks relevance to the
task; summary fails to explain what the resource was about; the relevance
and/or usefulness of the resource has not been explained.
<=2 Good resource selection; resource is relevant to the task; summary is
adequate but may require either more detail or is too long; the relevance
and/or usefulness of the resource has been explained to some extent, but
needs additional information.
<=3 Excellent resource selection; resource is highly relevant to the task (the
resource is probably highly specialised); summary is detailed yet concise;
the relevance and usefulness of the resource selection has been clearly
explained.
Key
Deductions
-3
-2
-1
Reference/URL provided does not link to resource (and resource cannot
be located or determined from details provided) OR
Reference/URL provided does not relate to the summary (i.e. summary is
not of resource content / contains content not contained in the resource)
Resource is generic AND/OR covers multiple technologies/examples
rather than focuses on a single technology/example
Resource not referenced correctly/not in Harvard format
Week Marks Awarded
1
2
3
4
5
6
7
8
9
10
TOTAL
Comments:
Criteria
0 No Response
<=1 Poor resource selection; resource is too broad or lacks relevance to the
task; summary fails to explain what the resource was about; the relevance
and/or usefulness of the resource has not been explained.
<=2 Good resource selection; resource is relevant to the task; summary is
adequate but may require either more detail or is too long; the relevance
and/or usefulness of the resource has been explained to some extent, but
needs additional information.
<=3 Excellent resource selection; resource is highly relevant to the task (the
resource is probably highly specialised); summary is detailed yet concise;
the relevance and usefulness of the resource selection has been clearly
explained.
Key
Deductions
-3
-2
-1
Reference/URL provided does not link to resource (and resource cannot
be located or determined from details provided) OR
Reference/URL provided does not relate to the summary (i.e. summary is
not of resource content / contains content not contained in the resource)
Resource is generic AND/OR covers multiple technologies/examples
rather than focuses on a single technology/example
Resource not referenced correctly/not in Harvard format
Week Marks Awarded
1
2
3
4
5
6
7
8
9
10
TOTAL
Comments:
1 out of 10
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.





