Pen Testing Script Assignment: Information Gathering and Analysis
VerifiedAdded on 2022/07/28
|8
|619
|55
Practical Assignment
AI Summary
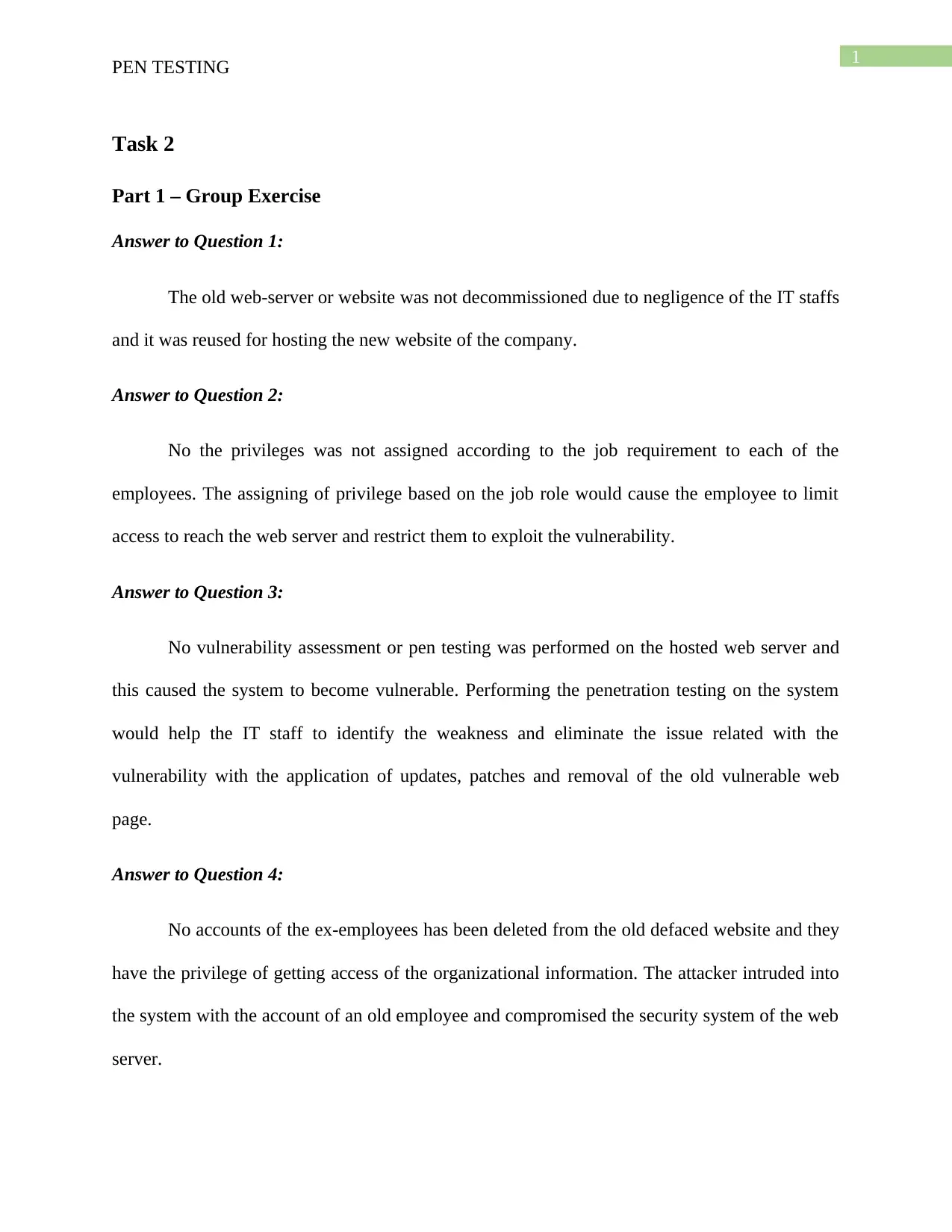
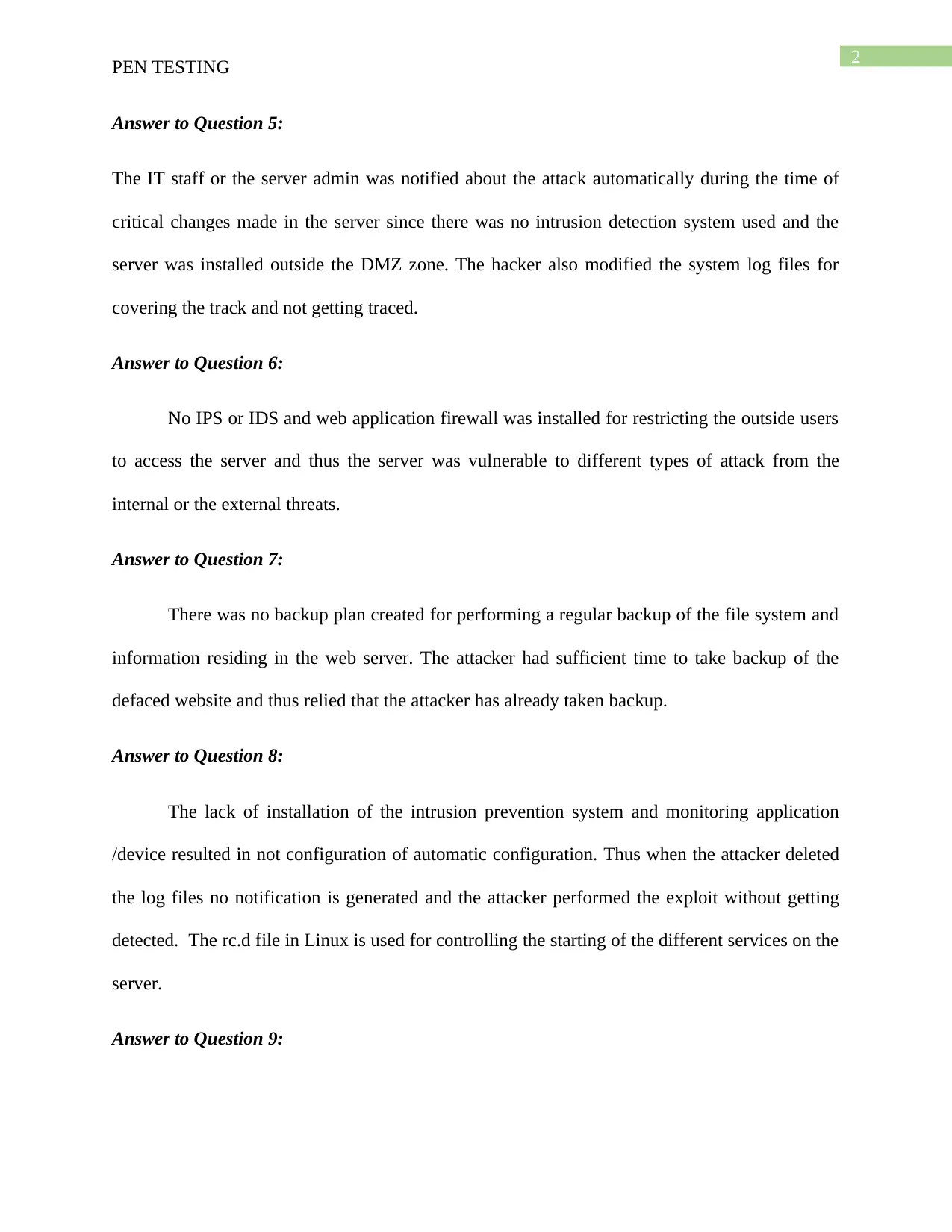
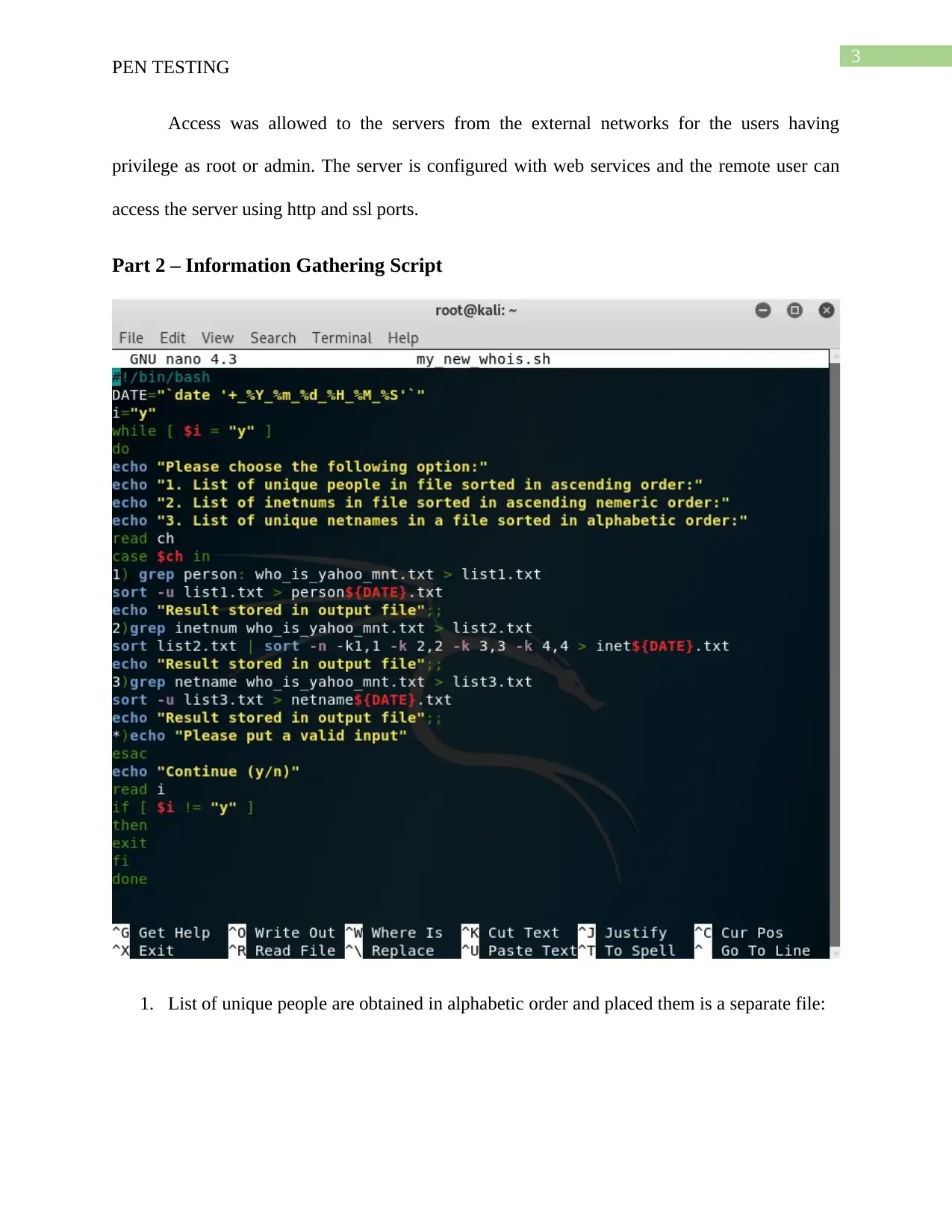
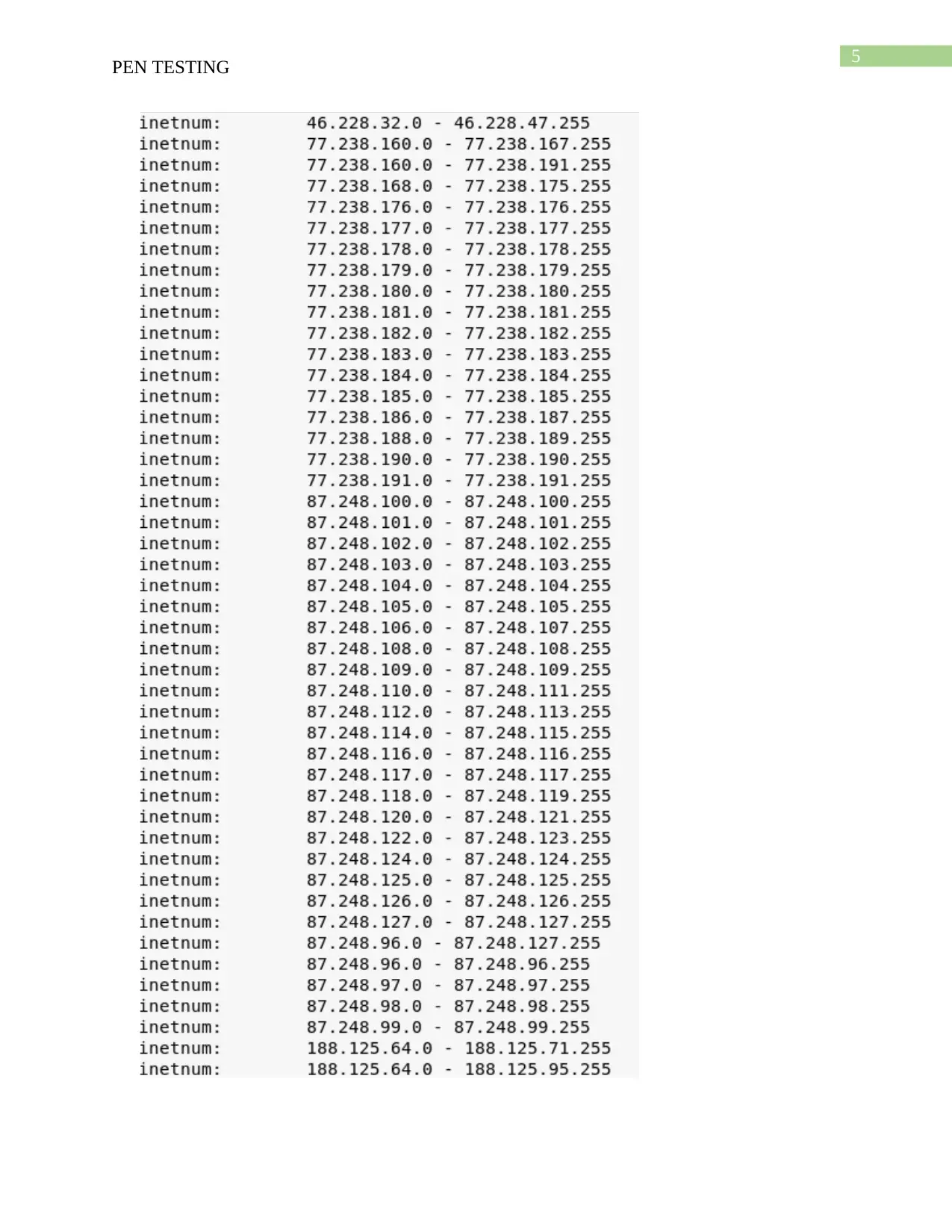
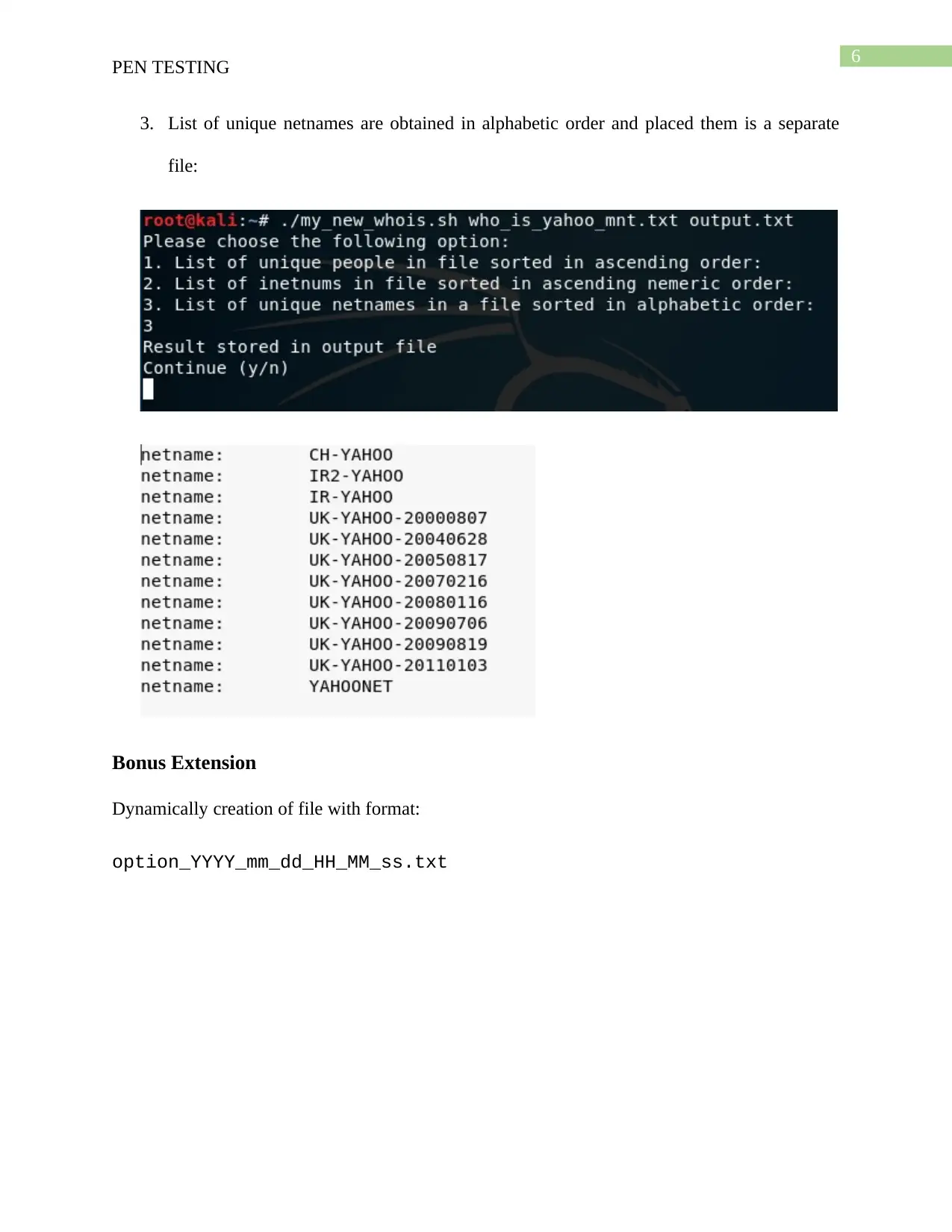
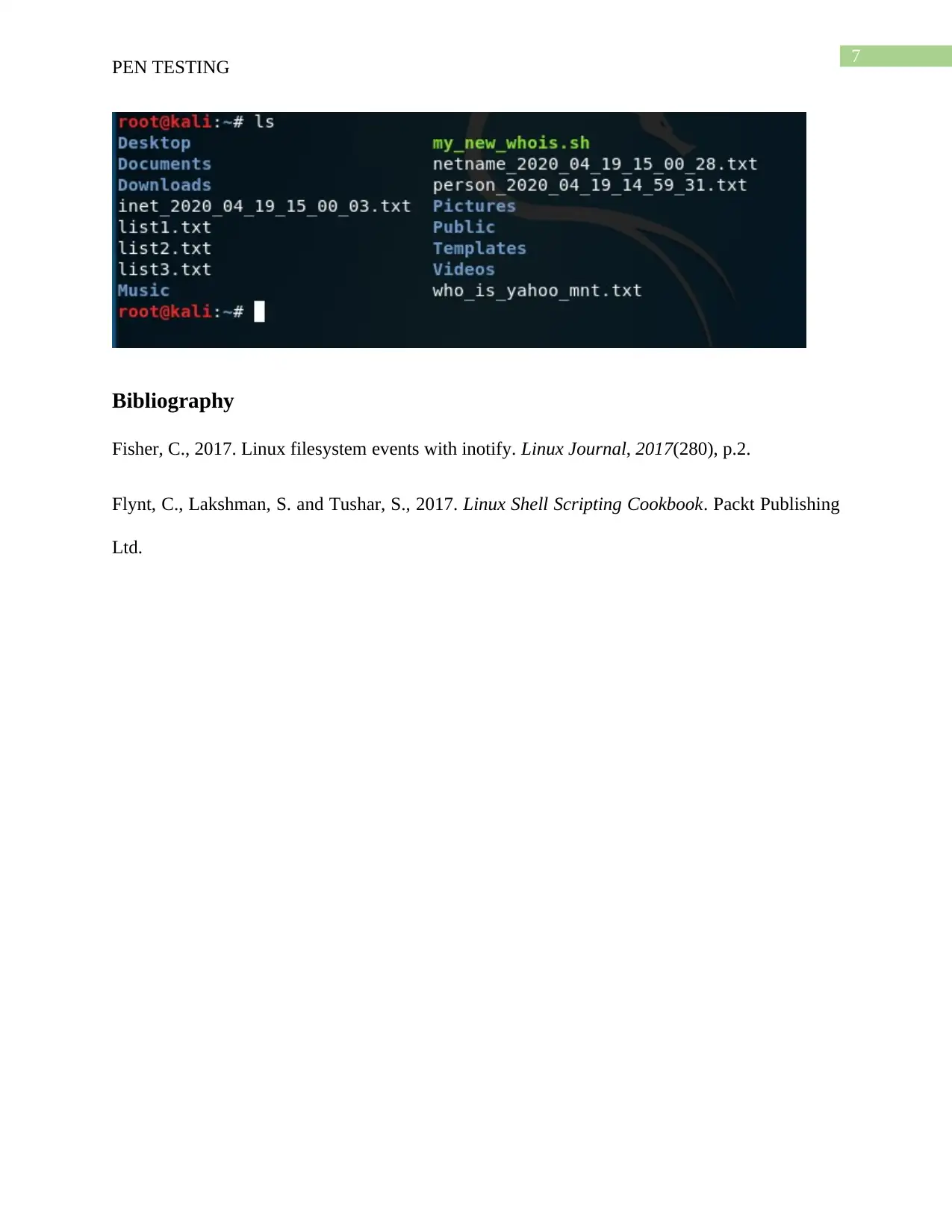
This assignment presents a pen testing exercise involving a fictitious case study of a web server attack and a script writing task. The first part requires a group reflection on a penetration test scoping activity, discussing the team's approach in a high-pressure scenario. The second part involves creating a shell script named 'my_new_whois.sh' that utilizes a provided 'whois' file. The script must prompt the user to perform specific tasks: obtaining unique people, inetnums, and netnames from the file, sorting them according to specified criteria, and placing the results into designated files. The script also needs to implement input validation, remove leading whitespace, and append the date and time to the output file. A bonus extension is included to dynamically create output files with specific filenames based on the user's search criteria and the current date and time. The assignment emphasizes practical application of penetration testing techniques and scripting skills, with marks allocated based on the script's functionality, input validation, and adherence to the provided requirements. The assignment aims to assess the student's ability to conduct a full-scale penetration test, and demonstrate an insight into the implications of the problem introduced in each task by using clear and concise arguments.
1 out of 8








![[object Object]](/_next/static/media/star-bottom.7253800d.svg)