Assessment Report: Developing Security Program for PPP Organization
VerifiedAdded on 2020/09/28
|16
|3932
|300
Report
AI Summary
This report provides a comprehensive assessment of a security program designed for Pampered Pet Palace (PPP), a boarding kennel. It details the development of a security policy, encompassing investigation, analysis, design, implementation, and management phases. The report emphasizes the importance of ISO security standards and discusses threat identification and risk assessment. It also outlines the current information security personnel at PPP and proposes changes to enhance security measures. The report covers the development of security policies, analysis of current security measures, risk assessment, and the roles of various security personnel. It also provides recommendations for improvements and the implementation of security standards. The report aims to help PPP secure sensitive client data and protect against cyber threats.
Assessment Report for
Developing a Security Program for Pampered Pet Palace
Developing a Security Program for Pampered Pet Palace
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
ABSTRACT
All organizations in the world used the information carefully to achieve
competitive advantages in the market. PPP is a vastly growing company
with many sensitive data of many pets bringing customers, and the
company is supposed to protect them from malicious users in all time. The
company required multiple strategies to secure critical information. The
main thing is the strategic information is being flexible and must follow
the international security and information standards. Finally, the report
expresses the information security specialist requirements and how the
specialist recognizes, mitigates, and accesses security threats.
All organizations in the world used the information carefully to achieve
competitive advantages in the market. PPP is a vastly growing company
with many sensitive data of many pets bringing customers, and the
company is supposed to protect them from malicious users in all time. The
company required multiple strategies to secure critical information. The
main thing is the strategic information is being flexible and must follow
the international security and information standards. Finally, the report
expresses the information security specialist requirements and how the
specialist recognizes, mitigates, and accesses security threats.
Contents
ABSTRACT.........................................................................................................................................2
Introduction:........................................................................................................................................4
Developing a Security Policy Program for PPP Organization:........................................................5
Investigation Phase..........................................................................................................................6
Analysis Phase..................................................................................................................................7
Design Phase....................................................................................................................................7
Implementation Phase.....................................................................................................................8
Management Phase..........................................................................................................................8
CURRENT INFORMATION SECURITY PERSONALS OF PPP................................................9
PLAN FOR THE PROPOSED CHANGES IN PPP.......................................................................10
PPP ISO SECURITY STANDARDS AND REASONING.............................................................12
SUITABILITY OF STANDARDS...............................................................................................13
THREAT IDENTIFICATION AND RISK ASSESSMENT..........................................................14
CONCLUSION..................................................................................................................................14
References:.........................................................................................................................................16
ABSTRACT.........................................................................................................................................2
Introduction:........................................................................................................................................4
Developing a Security Policy Program for PPP Organization:........................................................5
Investigation Phase..........................................................................................................................6
Analysis Phase..................................................................................................................................7
Design Phase....................................................................................................................................7
Implementation Phase.....................................................................................................................8
Management Phase..........................................................................................................................8
CURRENT INFORMATION SECURITY PERSONALS OF PPP................................................9
PLAN FOR THE PROPOSED CHANGES IN PPP.......................................................................10
PPP ISO SECURITY STANDARDS AND REASONING.............................................................12
SUITABILITY OF STANDARDS...............................................................................................13
THREAT IDENTIFICATION AND RISK ASSESSMENT..........................................................14
CONCLUSION..................................................................................................................................14
References:.........................................................................................................................................16
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Introduction:
Mr. Pavlov and Mrs. Norris established pampered Pets Palace, abbreviated as (PPP) in early
2010 as a boarding kennel for all kinds of cats and dogs like pets. Both of them developed
this boarding kennel in the Brisbane western suburbs. PPP provides a residence for all types
of cats and dogs, like pets and other services. They offer all these services free of cost.
Moreover, to reach the owners of pets' demands, the company employed a large number of
staff. All the employed staff members are professional in handlings pets like cats and dogs.
At the early stages, the organization system is running manually as per the company owners
planed. So, all the manual work includes a lot of paperwork, and it functions only in the set
working hours, and after the working hours, there are no services to take place for anyone.
But after the development of an automated system for the organization, the company owners
are now looking for the development of a security program for their company. They think
that an automatic will resolve all the issues. Still, security is an essential thing next to
developing an automated system for booking, providing services, and billing services. The
proposed report contains the complete analysis of the company’s current security program,
development of new security systems, suggestions for improvements, and setting different
ISO standards for the organization. Defining Risks and possible threats also included in this
proposed report. So, the company assigned this task for developing a security program for
Pampered Pets Palace to me as a security officer of the company. In this proposed research
paper, a security program is designed for the PPP company. Through this, the company will
Mr. Pavlov and Mrs. Norris established pampered Pets Palace, abbreviated as (PPP) in early
2010 as a boarding kennel for all kinds of cats and dogs like pets. Both of them developed
this boarding kennel in the Brisbane western suburbs. PPP provides a residence for all types
of cats and dogs, like pets and other services. They offer all these services free of cost.
Moreover, to reach the owners of pets' demands, the company employed a large number of
staff. All the employed staff members are professional in handlings pets like cats and dogs.
At the early stages, the organization system is running manually as per the company owners
planed. So, all the manual work includes a lot of paperwork, and it functions only in the set
working hours, and after the working hours, there are no services to take place for anyone.
But after the development of an automated system for the organization, the company owners
are now looking for the development of a security program for their company. They think
that an automatic will resolve all the issues. Still, security is an essential thing next to
developing an automated system for booking, providing services, and billing services. The
proposed report contains the complete analysis of the company’s current security program,
development of new security systems, suggestions for improvements, and setting different
ISO standards for the organization. Defining Risks and possible threats also included in this
proposed report. So, the company assigned this task for developing a security program for
Pampered Pets Palace to me as a security officer of the company. In this proposed research
paper, a security program is designed for the PPP company. Through this, the company will
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
efficiently secure their client's sensitive information and data in a more meaningful way
without any anxiety.
Moreover, the company will protect its data and information from hackers, so; the new
security program will reduce the hacking issues in the future. Hence, we can say that PPP
would maintain the organization's security more productively and systematically in the
future. After that, the roles of different security distinctive would also be defined to achieve
the organization's goals and objectives set by top management. And finally, improvements
recommendations would also have discussed in this security program assessment report.
Developing a Security Policy Program for PPP Organization:
In the current fast-paced world, where each of the companies tries to
become more competitive in the market against their competitors,
developing a security program is not as simple as it looks like because it
needs more investment, time, money, and effort the different teams.
Pampered Pets Palace (PPP) is looking for a more generic type of security
program policy for their organization to be more suitable for its
management at all levels, from operational to highest level. It must be
developed quickly, according to the company’s requirements. Before
creating the PPP security policy, security policy developers must consider
the company’s best practices, which includes the ethics, guidelines set by
the governing bodies, different suitable methods, thoroughly review the
current system, and the most important thing to understand the abilities
of employees. So, first, the security policy team of PPP should develop the
company’s security policy into two fragments, first is to design and
develop the approach for the system, and the second thing is the
without any anxiety.
Moreover, the company will protect its data and information from hackers, so; the new
security program will reduce the hacking issues in the future. Hence, we can say that PPP
would maintain the organization's security more productively and systematically in the
future. After that, the roles of different security distinctive would also be defined to achieve
the organization's goals and objectives set by top management. And finally, improvements
recommendations would also have discussed in this security program assessment report.
Developing a Security Policy Program for PPP Organization:
In the current fast-paced world, where each of the companies tries to
become more competitive in the market against their competitors,
developing a security program is not as simple as it looks like because it
needs more investment, time, money, and effort the different teams.
Pampered Pets Palace (PPP) is looking for a more generic type of security
program policy for their organization to be more suitable for its
management at all levels, from operational to highest level. It must be
developed quickly, according to the company’s requirements. Before
creating the PPP security policy, security policy developers must consider
the company’s best practices, which includes the ethics, guidelines set by
the governing bodies, different suitable methods, thoroughly review the
current system, and the most important thing to understand the abilities
of employees. So, first, the security policy team of PPP should develop the
company’s security policy into two fragments, first is to design and
develop the approach for the system, and the second thing is the
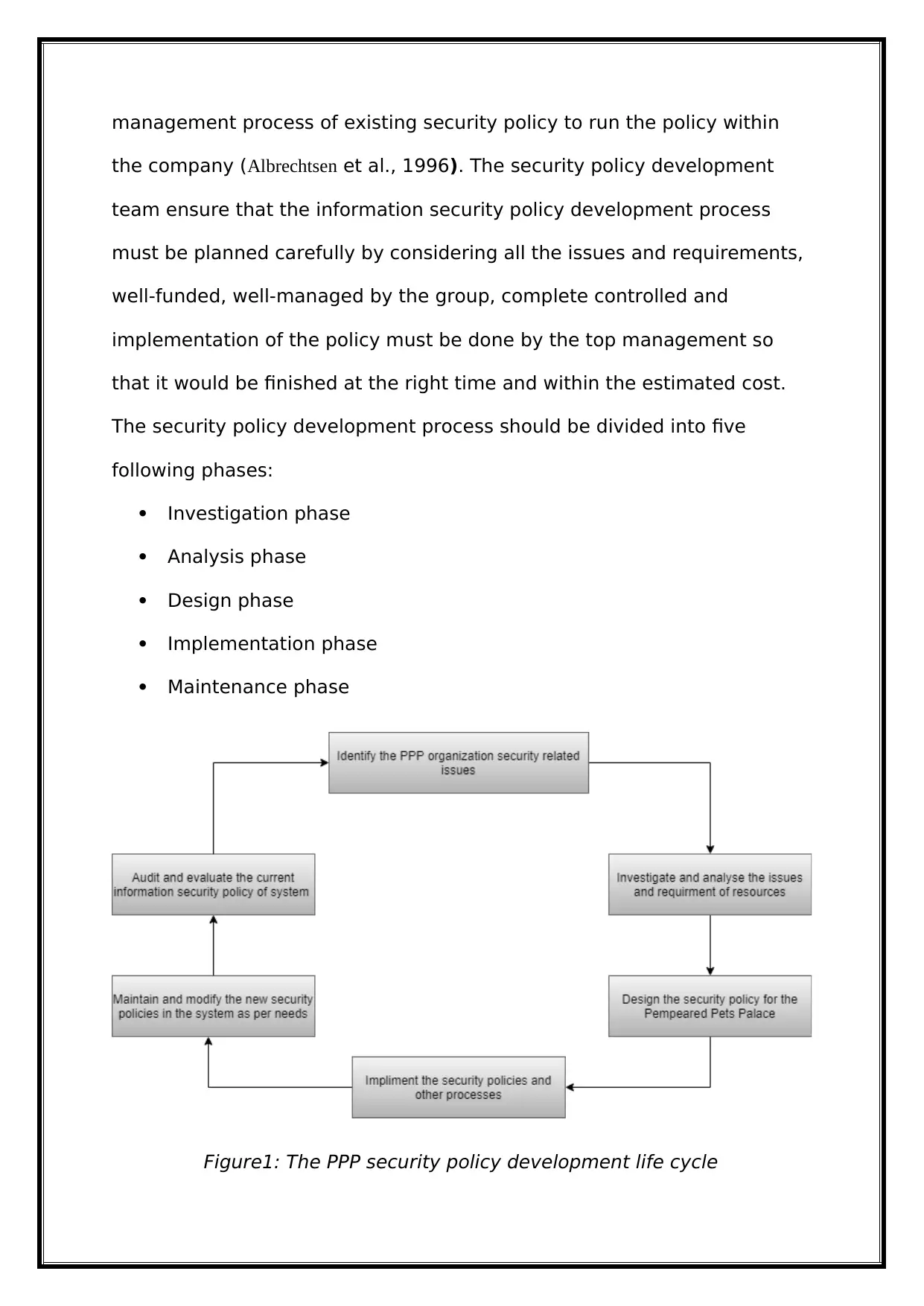
management process of existing security policy to run the policy within
the company (Albrechtsen et al., 1996). The security policy development
team ensure that the information security policy development process
must be planned carefully by considering all the issues and requirements,
well-funded, well-managed by the group, complete controlled and
implementation of the policy must be done by the top management so
that it would be finished at the right time and within the estimated cost.
The security policy development process should be divided into five
following phases:
Investigation phase
Analysis phase
Design phase
Implementation phase
Maintenance phase
Figure1: The PPP security policy development life cycle
the company (Albrechtsen et al., 1996). The security policy development
team ensure that the information security policy development process
must be planned carefully by considering all the issues and requirements,
well-funded, well-managed by the group, complete controlled and
implementation of the policy must be done by the top management so
that it would be finished at the right time and within the estimated cost.
The security policy development process should be divided into five
following phases:
Investigation phase
Analysis phase
Design phase
Implementation phase
Maintenance phase
Figure1: The PPP security policy development life cycle
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Investigation Phase
In the first investigation phase of developing security policy, the Pampered Pets Palace
management should contact the IT management for assistance and the IT-related employees
to initialize the security policy development process and identify or investigate the real
weaknesses related to the security system of the company. After that investigation, the
security policy management should set the goals for the security policy development process,
which provides direct assistance to other team members. During the investigation,
management should include the different levels of employees from the organization like
operational managers, receptionists, billing staff, kennel hands, and the customers or end-
users for more information about the company's current security weaknesses system
investigation. After all the inquiry and communication processes get from the different levels
of employees and customers of PPP, the security policy project management develops an
outline for the whole project. It estimates the total cost spending on the project and the time
required to complete the security policy project. In addition to this, PPP must include the
project manager capable of project investigation, analysis of the situation, design, and
implementation of security policy projects in a well-mannered way.
Analysis Phase
In the next phase of the development process, security policy management analyses the
significant requirements or needs of the different resources to secure the company's
information security system. The analysis phase includes collecting current and new risks by
the management assessment through the documenting IT audit in the company's existing
information system. After that, the management analyses the current needs of PPP. The
management should analyse the information security system's existing resources like the new
existing system must have the devices, servers, and applications for both employees and
companies' staff, which is also included in the analysis phase's resources requirements. So, all
In the first investigation phase of developing security policy, the Pampered Pets Palace
management should contact the IT management for assistance and the IT-related employees
to initialize the security policy development process and identify or investigate the real
weaknesses related to the security system of the company. After that investigation, the
security policy management should set the goals for the security policy development process,
which provides direct assistance to other team members. During the investigation,
management should include the different levels of employees from the organization like
operational managers, receptionists, billing staff, kennel hands, and the customers or end-
users for more information about the company's current security weaknesses system
investigation. After all the inquiry and communication processes get from the different levels
of employees and customers of PPP, the security policy project management develops an
outline for the whole project. It estimates the total cost spending on the project and the time
required to complete the security policy project. In addition to this, PPP must include the
project manager capable of project investigation, analysis of the situation, design, and
implementation of security policy projects in a well-mannered way.
Analysis Phase
In the next phase of the development process, security policy management analyses the
significant requirements or needs of the different resources to secure the company's
information security system. The analysis phase includes collecting current and new risks by
the management assessment through the documenting IT audit in the company's existing
information system. After that, the management analyses the current needs of PPP. The
management should analyse the information security system's existing resources like the new
existing system must have the devices, servers, and applications for both employees and
companies' staff, which is also included in the analysis phase's resources requirements. So, all
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
these already existing things are excluded from the resources requirements list in this analysis
phase.
Design Phase
In this design phase of the system's security policy, the management first considers the major
discussed and highlighted points of the investigation phase and the analysis phase. The
development process management must also decide how the policy will be distributed among
the system and express how the company will achieve its goals and objectives of the new
information security system. After that, the management team will revise the previously
discussed analysis phase to select the best design for the information security system. During
the selection of formatting, the management team should consider the fact that it would save
the organization's cost and be completed promptly. Designing the security system policy
includes technology choice, architectural design, and asset design. All the things mentioned
above must be considered during the designing phase of the information security system.
Moreover, company management describes or documenting the system's complete security
policy, which includes how the policy will be implemented.
Implementation Phase
In this phase of implementation, the security policy management ensures that the
implementation of the security policy of PPP organization in a significant way, and it must be
going in the right direction. Also, control ensures that the policy distribution is not going to
be straight forward because it was traditionally not in favour of the company. All the
employees included in the team must effectively contribute to the implementation of the
security policy. Moreover, Pampered Pets Palace company management must strive to
decrease the technical jargon and accommodated different terminologies for the successful
execution of selected design policy in the organization. Furthermore, the security policy
management of the PPP company will continuously monitor or evaluate the underdeveloped
phase.
Design Phase
In this design phase of the system's security policy, the management first considers the major
discussed and highlighted points of the investigation phase and the analysis phase. The
development process management must also decide how the policy will be distributed among
the system and express how the company will achieve its goals and objectives of the new
information security system. After that, the management team will revise the previously
discussed analysis phase to select the best design for the information security system. During
the selection of formatting, the management team should consider the fact that it would save
the organization's cost and be completed promptly. Designing the security system policy
includes technology choice, architectural design, and asset design. All the things mentioned
above must be considered during the designing phase of the information security system.
Moreover, company management describes or documenting the system's complete security
policy, which includes how the policy will be implemented.
Implementation Phase
In this phase of implementation, the security policy management ensures that the
implementation of the security policy of PPP organization in a significant way, and it must be
going in the right direction. Also, control ensures that the policy distribution is not going to
be straight forward because it was traditionally not in favour of the company. All the
employees included in the team must effectively contribute to the implementation of the
security policy. Moreover, Pampered Pets Palace company management must strive to
decrease the technical jargon and accommodated different terminologies for the successful
execution of selected design policy in the organization. Furthermore, the security policy
management of the PPP company will continuously monitor or evaluate the underdeveloped
system to determine that it will go in the right direction. It also considers how PPP will
achieve the goals and objectives in the future with this security program.
Management Phase
In the last management phase of the security policy development, Pampered Pets Palace
company management continuously maintains and modifies the security policy according to
its requirements. PPP will define some mechanism to monitor the company's daily activities
that ensure that the current security policy will be implemented among all parts of the
organization. Different steps will have included preparing result reports depending on
customer's behaviour, implementing audits, getting reviews, and carrying out intrusion
detection. Maintenance consists of the following efforts: analyses the technology and security
infrastructure, evaluate the different reports related to security incidents, analyse the legal
requirements, and revise the security policy development life cycle. Evaluation of security
infrastructure is necessary to identify the major threats which could be possible due to the
addition of the new technology in the organization like PPP company owners add a biometric
system for customers or staff attendance so, these type of changes might be a threat for
security policy in the company.
CURRENT INFORMATION SECURITY PERSONALS OF PPP
Pampered Pets Palace (PPP) has a security officer for the security of management, staff, pets,
and coming customers. The information security officers working under the Chief
information officer. The IS officer work with other individuals to provide full proof security
to the PPP organization. They help the organization in securing information. All the officers
should follow the cybersecurity laws and rules vary across the organization. The company
also has legal experts who understand all security laws and regulations. These experts
achieve the goals and objectives in the future with this security program.
Management Phase
In the last management phase of the security policy development, Pampered Pets Palace
company management continuously maintains and modifies the security policy according to
its requirements. PPP will define some mechanism to monitor the company's daily activities
that ensure that the current security policy will be implemented among all parts of the
organization. Different steps will have included preparing result reports depending on
customer's behaviour, implementing audits, getting reviews, and carrying out intrusion
detection. Maintenance consists of the following efforts: analyses the technology and security
infrastructure, evaluate the different reports related to security incidents, analyse the legal
requirements, and revise the security policy development life cycle. Evaluation of security
infrastructure is necessary to identify the major threats which could be possible due to the
addition of the new technology in the organization like PPP company owners add a biometric
system for customers or staff attendance so, these type of changes might be a threat for
security policy in the company.
CURRENT INFORMATION SECURITY PERSONALS OF PPP
Pampered Pets Palace (PPP) has a security officer for the security of management, staff, pets,
and coming customers. The information security officers working under the Chief
information officer. The IS officer work with other individuals to provide full proof security
to the PPP organization. They help the organization in securing information. All the officers
should follow the cybersecurity laws and rules vary across the organization. The company
also has legal experts who understand all security laws and regulations. These experts
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
individually work together to ensure that all the organization's sensitive information must be
protected from competitors. Several rules are used in the organization that prohibits the other
companies from accessing the PPP information security system. A grand scheme called
strategy in any organization, and through this strategy, ensures that all its assets and
procedures are safe from evils or other competitors. So, we can say that all organizations like
PPP ensure that all their information and assets are secure from others
(Liu et al., 2009, p. 204).
At PPP, all the operational managers, receptionists, billing managers, and kennel hands must
have security access cards. Security access cards are used to open various doors in the PPP
organization. When any of the employees decide to leave the company for some reason, the
company's security officer gives back the security cards from him. If any employee from the
information security department leaves the company, all the passwords and protocols
changed due to security reasons. He/she signed the document that they do not share the
company's sensitive information outside.
Moreover, there are multiple security technician's in the PPP who worked with the security
officers. They all are well trained and have enough experience for configurations of firewalls.
They implement multiple software in the company, plus they troubleshoot many problems
that occur in the company and make sure that all information security technology is executed
well mannered. Security technicians have a vital role, so they are thoroughly interviewed
before hiring.
Security staffers and watchstanders also work hand-in-hand with the security officer. They
are carefully observing the company's email accounts, billing information, amounts,
customer's security, sensitive information, and in general, they are keeping everything in the
organization. And in terms of the physical safety of the PPP organization, some multiple
investigators and officers provide security at any time. They make sure that any unauthorized
protected from competitors. Several rules are used in the organization that prohibits the other
companies from accessing the PPP information security system. A grand scheme called
strategy in any organization, and through this strategy, ensures that all its assets and
procedures are safe from evils or other competitors. So, we can say that all organizations like
PPP ensure that all their information and assets are secure from others
(Liu et al., 2009, p. 204).
At PPP, all the operational managers, receptionists, billing managers, and kennel hands must
have security access cards. Security access cards are used to open various doors in the PPP
organization. When any of the employees decide to leave the company for some reason, the
company's security officer gives back the security cards from him. If any employee from the
information security department leaves the company, all the passwords and protocols
changed due to security reasons. He/she signed the document that they do not share the
company's sensitive information outside.
Moreover, there are multiple security technician's in the PPP who worked with the security
officers. They all are well trained and have enough experience for configurations of firewalls.
They implement multiple software in the company, plus they troubleshoot many problems
that occur in the company and make sure that all information security technology is executed
well mannered. Security technicians have a vital role, so they are thoroughly interviewed
before hiring.
Security staffers and watchstanders also work hand-in-hand with the security officer. They
are carefully observing the company's email accounts, billing information, amounts,
customer's security, sensitive information, and in general, they are keeping everything in the
organization. And in terms of the physical safety of the PPP organization, some multiple
investigators and officers provide security at any time. They make sure that any unauthorized
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
person will not interfere with the company. Guards and gates are also providing within the
company. Surveillance cameras are placed in a well-mannered way for the surveillance of the
company and its surroundings. All the systems mentioned above and staff are part of the
information security program of PPP.
PLAN FOR THE PROPOSED CHANGES IN PPP
Organizations follow multiple procedures to become more competitive in the market against
their competitors (Cooper et al., 1964). In the implementation plan for proposed changes,
PPP must have to be flexible at all times. PPP organization will build relationships and strong
teams to become more competitive and relaxed in the market. Everyone in the company,
includes operational managers, kennel hands; the receptionist has to think that it is not just
the chief information officer's responsibility to secure the information, but everyone has the
responsibility to secure the data. Everyone in the company, from top-level management to
billing staff, should understand the importance of keeping all the information safe. After that,
the main issue is training and evaluation.
The second thing is that PPP now becomes a substantial growing organization in these ten
years, and mostly its processes become very complicated, and all these things increase the
risks of security violations. Manage many kennel hands, operational staff, complex
procedures, and workloads are very tough now. Flexibility is an essential thing because it will
come up with the plans and courses of acceptable actions and help the company alleviate
information insecurity. Everyone in the organization must have a sense of what to do and not
do to keep the all-important data safe. Chief information officer also responsible for all the
things mentioned above. PPP company will have to understand that all the demands that
occur with threats of security, information governance, and markets evolvement. The
organization's information security department will have to discover and carry out more ways
company. Surveillance cameras are placed in a well-mannered way for the surveillance of the
company and its surroundings. All the systems mentioned above and staff are part of the
information security program of PPP.
PLAN FOR THE PROPOSED CHANGES IN PPP
Organizations follow multiple procedures to become more competitive in the market against
their competitors (Cooper et al., 1964). In the implementation plan for proposed changes,
PPP must have to be flexible at all times. PPP organization will build relationships and strong
teams to become more competitive and relaxed in the market. Everyone in the company,
includes operational managers, kennel hands; the receptionist has to think that it is not just
the chief information officer's responsibility to secure the information, but everyone has the
responsibility to secure the data. Everyone in the company, from top-level management to
billing staff, should understand the importance of keeping all the information safe. After that,
the main issue is training and evaluation.
The second thing is that PPP now becomes a substantial growing organization in these ten
years, and mostly its processes become very complicated, and all these things increase the
risks of security violations. Manage many kennel hands, operational staff, complex
procedures, and workloads are very tough now. Flexibility is an essential thing because it will
come up with the plans and courses of acceptable actions and help the company alleviate
information insecurity. Everyone in the organization must have a sense of what to do and not
do to keep the all-important data safe. Chief information officer also responsible for all the
things mentioned above. PPP company will have to understand that all the demands that
occur with threats of security, information governance, and markets evolvement. The
organization's information security department will have to discover and carry out more ways
to adapt to all these changes. This includes the technologies and data storage for
modification.
Additionally, PPP top management decides to implement multiple methodologies for security
awareness within the company. The organization's security awareness program includes the
different training sessions, and all the staff members should have to come in these sessions,
which will help them realize the importance of security programs and the distinctive vastness
of its failures in the company. Different security letters might be used in the organization to
disseminate other plans, processes, and existing information security of the company. Emails,
messages, and hard copies require in these processes. PPP needs to become flexible for the
implementation of providing information security.
PPP ISO SECURITY STANDARDS AND REASONING
International Organization for Standards (ISO) certification expresses that the thorough
documentation, management, services, or process meets the quality assurance requirements
and defined standards. This organization of standards aims to develop measures to ensure the
quality, security, and efficiency of the products and services. PPP uses the following ISO
standards during their working processes:
Pampered Pets Palace uses the ISO 27001 standards. This standard includes the different
applications related to the management of information security and protocols in the
organization. This standard provides the procedures and strategies necessary for technical and
physical controls included in the organization's risks management of information. This
standard also provides the methods to operate, implement, monitor the management of
information security in the company (Biermann et al.,1996).
PPP organization also uses the ISO 14000 standards. This standard provides the guideline to
perform the company's procedures and strategies that do not humiliate the company
modification.
Additionally, PPP top management decides to implement multiple methodologies for security
awareness within the company. The organization's security awareness program includes the
different training sessions, and all the staff members should have to come in these sessions,
which will help them realize the importance of security programs and the distinctive vastness
of its failures in the company. Different security letters might be used in the organization to
disseminate other plans, processes, and existing information security of the company. Emails,
messages, and hard copies require in these processes. PPP needs to become flexible for the
implementation of providing information security.
PPP ISO SECURITY STANDARDS AND REASONING
International Organization for Standards (ISO) certification expresses that the thorough
documentation, management, services, or process meets the quality assurance requirements
and defined standards. This organization of standards aims to develop measures to ensure the
quality, security, and efficiency of the products and services. PPP uses the following ISO
standards during their working processes:
Pampered Pets Palace uses the ISO 27001 standards. This standard includes the different
applications related to the management of information security and protocols in the
organization. This standard provides the procedures and strategies necessary for technical and
physical controls included in the organization's risks management of information. This
standard also provides the methods to operate, implement, monitor the management of
information security in the company (Biermann et al.,1996).
PPP organization also uses the ISO 14000 standards. This standard provides the guideline to
perform the company's procedures and strategies that do not humiliate the company
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 16
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.

