INFS 5115: Security Principal Report - Cyber Attack Analysis
VerifiedAdded on 2023/06/07
|6
|1072
|191
Report
AI Summary
This report analyzes a social engineering attack targeting Cheese Movers International (CMI), detailing the attack's ontological components as defined by Mouton et al. (2016). The attackers used social engineering to target executives, leveraging the company's business model and global vulnerabilities to phish customers. The report proposes mitigation strategies considering people, process, and technology factors, including staying off the radar, implementing security systems, protecting social media accounts, and securing third-party services. Furthermore, the report outlines key elements of an incident response plan, emphasizing preparation, incident definition, and documentation. The analysis aims to provide a comprehensive understanding of the attack and effective countermeasures.

Running head: SECURITY PRINCIPAL
Security Principal
Name of the Student
Name of the University
Author Note
Security Principal
Name of the Student
Name of the University
Author Note
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
1SECURITY PRINCIPAL
1. Describe the attack that occurred according to the ontological components specified in
Mouton et al. (2016).
As per Mouton et al. (2016), it has been specified that according to an ontological model,
the social engineering attacks can be specified with respect to the direct as well as indirect
communication. The attacker targets any organization or an individual for the attack with the
help of a social engineer, a target through a medium and uses compliance principles as well as
various techniques. As per this case study, the attackers have obtained a social engineering
procedure to perform their malicious cyber attacks towards the organization of the Cheese
Movers International or CMI.
The ontological components that were followed in the attacks by the hackers using social
engineering procedure can be listed as follows:
Target: The attackers had successfully targeted two of the chief executives of the
company to hack into the systems of the organization of CMI including the
organization’s personal process as well as the social website. They chose these
people to be the medium through which the attacks were initiated.
Medium: The attackers had successfully impersonated the identities of the
executives that have been targeted and chose the diversified business model of the
organization and the vulnerabilities of the global business units that the
organization had.
Goal: The attackers had the goal of unauthorized accessing of the business
website and social networks handled by the company to phish the organization’s
customers into visiting their hacking website.
1. Describe the attack that occurred according to the ontological components specified in
Mouton et al. (2016).
As per Mouton et al. (2016), it has been specified that according to an ontological model,
the social engineering attacks can be specified with respect to the direct as well as indirect
communication. The attacker targets any organization or an individual for the attack with the
help of a social engineer, a target through a medium and uses compliance principles as well as
various techniques. As per this case study, the attackers have obtained a social engineering
procedure to perform their malicious cyber attacks towards the organization of the Cheese
Movers International or CMI.
The ontological components that were followed in the attacks by the hackers using social
engineering procedure can be listed as follows:
Target: The attackers had successfully targeted two of the chief executives of the
company to hack into the systems of the organization of CMI including the
organization’s personal process as well as the social website. They chose these
people to be the medium through which the attacks were initiated.
Medium: The attackers had successfully impersonated the identities of the
executives that have been targeted and chose the diversified business model of the
organization and the vulnerabilities of the global business units that the
organization had.
Goal: The attackers had the goal of unauthorized accessing of the business
website and social networks handled by the company to phish the organization’s
customers into visiting their hacking website.
2SECURITY PRINCIPAL
Techniques: The techniques used by the attackers had been the baiting technique
that was used to impersonate the executives as well as using the company website
and making them being redirected to their website for accessing their personal
information.
Compliance Principle: The hacktivists had used the methodology of social
validation of the organization to perform their malevolent activities and in turn,
derogating the reputation of the company.
2. Propose and justify potential mitigations for this type of attack, with consideration of
people, process and technology factors.
As per the case study, there were mitigation techniques available to eliminate these kinds
of attacks in the organization. However, after the attacks have been performed, the Verizon
RISK Team was contacted to investigate on the hacking incident of the organization.
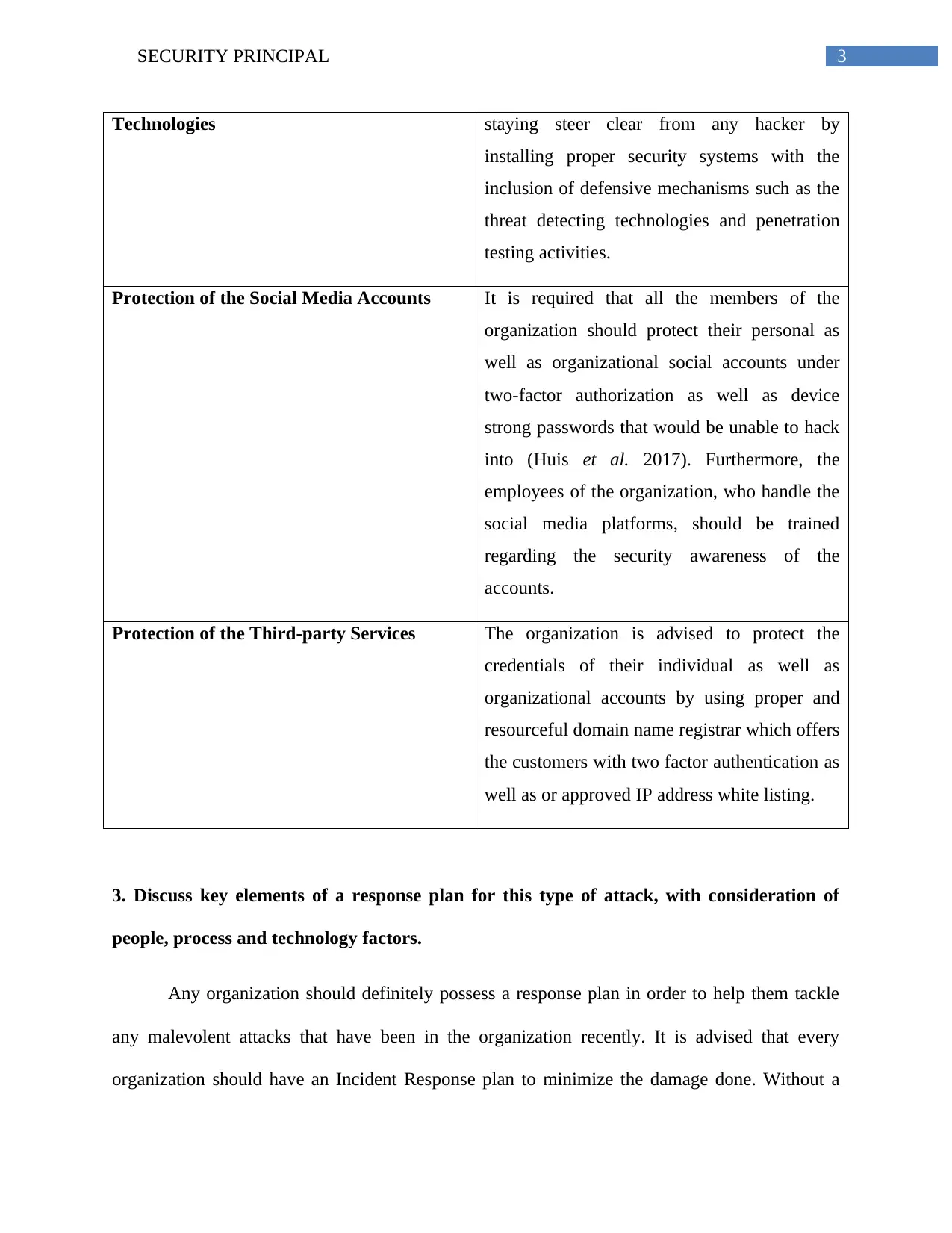
Further, to mitigate the social attacks like this, a justified mitigation plan can be proposed
considering the people, process and technology factors of the organization. These mitigation
methodologies can be described in details as follows:
Mitigation Technique Justification
Staying off the radar It is to be kept in mind that any activities that
may attract the interest of an attacker must be
avoided. This would include staying away
from phishing attacks, installing unauthorized
malwares and even staying away from sharing
any business details over unsecured emails,
texts and phones.
Installing Security Systems and Detection The organization should prepare itself for
Techniques: The techniques used by the attackers had been the baiting technique
that was used to impersonate the executives as well as using the company website
and making them being redirected to their website for accessing their personal
information.
Compliance Principle: The hacktivists had used the methodology of social
validation of the organization to perform their malevolent activities and in turn,
derogating the reputation of the company.
2. Propose and justify potential mitigations for this type of attack, with consideration of
people, process and technology factors.
As per the case study, there were mitigation techniques available to eliminate these kinds
of attacks in the organization. However, after the attacks have been performed, the Verizon
RISK Team was contacted to investigate on the hacking incident of the organization.
Further, to mitigate the social attacks like this, a justified mitigation plan can be proposed
considering the people, process and technology factors of the organization. These mitigation
methodologies can be described in details as follows:
Mitigation Technique Justification
Staying off the radar It is to be kept in mind that any activities that
may attract the interest of an attacker must be
avoided. This would include staying away
from phishing attacks, installing unauthorized
malwares and even staying away from sharing
any business details over unsecured emails,
texts and phones.
Installing Security Systems and Detection The organization should prepare itself for
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
3SECURITY PRINCIPAL
Technologies staying steer clear from any hacker by
installing proper security systems with the
inclusion of defensive mechanisms such as the
threat detecting technologies and penetration
testing activities.
Protection of the Social Media Accounts It is required that all the members of the
organization should protect their personal as
well as organizational social accounts under
two-factor authorization as well as device
strong passwords that would be unable to hack
into (Huis et al. 2017). Furthermore, the
employees of the organization, who handle the
social media platforms, should be trained
regarding the security awareness of the
accounts.
Protection of the Third-party Services The organization is advised to protect the
credentials of their individual as well as
organizational accounts by using proper and
resourceful domain name registrar which offers
the customers with two factor authentication as
well as or approved IP address white listing.
3. Discuss key elements of a response plan for this type of attack, with consideration of
people, process and technology factors.
Any organization should definitely possess a response plan in order to help them tackle
any malevolent attacks that have been in the organization recently. It is advised that every
organization should have an Incident Response plan to minimize the damage done. Without a
Technologies staying steer clear from any hacker by
installing proper security systems with the
inclusion of defensive mechanisms such as the
threat detecting technologies and penetration
testing activities.
Protection of the Social Media Accounts It is required that all the members of the
organization should protect their personal as
well as organizational social accounts under
two-factor authorization as well as device
strong passwords that would be unable to hack
into (Huis et al. 2017). Furthermore, the
employees of the organization, who handle the
social media platforms, should be trained
regarding the security awareness of the
accounts.
Protection of the Third-party Services The organization is advised to protect the
credentials of their individual as well as
organizational accounts by using proper and
resourceful domain name registrar which offers
the customers with two factor authentication as
well as or approved IP address white listing.
3. Discuss key elements of a response plan for this type of attack, with consideration of
people, process and technology factors.
Any organization should definitely possess a response plan in order to help them tackle
any malevolent attacks that have been in the organization recently. It is advised that every
organization should have an Incident Response plan to minimize the damage done. Without a
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
4SECURITY PRINCIPAL
response plan, it would be difficult to specify the severity of the attacks and thus the mitigating
plans would not be able to specify how to implement. Thus, key elements of a response plan that
should be enlisted are explained as follows:
Preparation and initiation of the Incident Response plan: It is necessary that a
proper preparation and initiation should be planned before the response plan
begins. Initiation and preparation are the key factors before analyzing the severity
of an attack.
Definition of the security incidents: The response plan must clearly define what
the incident holds. This would also hold the information about the prioritizing of
the different types of incidences that had previously occurred in the organization.
Documentation and communication: The effectiveness of a response plan
becomes limited if not documented properly (Huis et al. 2017). This means that
the employees should document every single process, action and procedure of the
IR plan. Furthermore, the entire knowledge of the plan should be properly spread
amongst the entire workforce and especially the team members handling the
incident response.
response plan, it would be difficult to specify the severity of the attacks and thus the mitigating
plans would not be able to specify how to implement. Thus, key elements of a response plan that
should be enlisted are explained as follows:
Preparation and initiation of the Incident Response plan: It is necessary that a
proper preparation and initiation should be planned before the response plan
begins. Initiation and preparation are the key factors before analyzing the severity
of an attack.
Definition of the security incidents: The response plan must clearly define what
the incident holds. This would also hold the information about the prioritizing of
the different types of incidences that had previously occurred in the organization.
Documentation and communication: The effectiveness of a response plan
becomes limited if not documented properly (Huis et al. 2017). This means that
the employees should document every single process, action and procedure of the
IR plan. Furthermore, the entire knowledge of the plan should be properly spread
amongst the entire workforce and especially the team members handling the
incident response.
5SECURITY PRINCIPAL
References
Huis, M.A.A., van der Kleij, R., Kleinhuis, I.G., de Koning, L., Kort, J., Meiler, I.P., van
Schendel MSc, J.A., Schultz, S. and Young, H.J., 2017. Human Factors in Cyber Incident
Response: Needs, collaboration and The Reporter.
Mouton, F., Leenen, L. and Venter, H.S., 2016. Social engineering attack examples, templates
and scenarios. Computers & Security, 59, pp.186-209.
References
Huis, M.A.A., van der Kleij, R., Kleinhuis, I.G., de Koning, L., Kort, J., Meiler, I.P., van
Schendel MSc, J.A., Schultz, S. and Young, H.J., 2017. Human Factors in Cyber Incident
Response: Needs, collaboration and The Reporter.
Mouton, F., Leenen, L. and Venter, H.S., 2016. Social engineering attack examples, templates
and scenarios. Computers & Security, 59, pp.186-209.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 6
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.



