University SDN Report: Layers, Advantages, Disadvantages, and Security
VerifiedAdded on 2020/05/16
|8
|1596
|67
Report
AI Summary
This report provides a comprehensive overview of Software-Defined Networks (SDN). It begins with an introduction to SDN, highlighting its revolutionary potential in networking through control planes and data decoupling, which enables end-to-end control, flexibility, and agility. The report includes a literature review that details the layers of SDN (data forwarding, control, and application), a comparison of SDN with traditional networks, and a discussion of their respective advantages and disadvantages. A critical analysis of SDN's security issues, such as tunnel bypassing, packet encryption, DDoS attacks, and compromised controller attacks, is presented, followed by proposed mitigation and countermeasures. The report concludes that, despite certain security concerns, SDN is a superior technology for networking compared to traditional concepts and is highly applicable in real-life implementations.

Running Head: SDN (SOFTWARE-DEFINED NETWORK)
SDN (Software-Defined Network)
Name of the Student
Name of the University
Author Note
SDN (Software-Defined Network)
Name of the Student
Name of the University
Author Note
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
SDN (SOFTWARE-DEFINED NETWORK)
Table of Contents
1. Introduction............................................................................................................................... 3
2. Literature Review.......................................................................................................................3
2.1 SDN (Software-Defined Network) and its layers..................................................................3
2.2 Comparison of SDN with traditional networks.....................................................................4
2.3 Comparison of Advantages..................................................................................................4
2.4 Comparison of Disadvantages..............................................................................................4
3. Critical Analysis.......................................................................................................................... 5
3.1 Critical Security Issues in SDN..............................................................................................5
3.2 Mitigation and Countermeasures........................................................................................5
Conclusion..................................................................................................................................... 6
References..................................................................................................................................... 7
Table of Contents
1. Introduction............................................................................................................................... 3
2. Literature Review.......................................................................................................................3
2.1 SDN (Software-Defined Network) and its layers..................................................................3
2.2 Comparison of SDN with traditional networks.....................................................................4
2.3 Comparison of Advantages..................................................................................................4
2.4 Comparison of Disadvantages..............................................................................................4
3. Critical Analysis.......................................................................................................................... 5
3.1 Critical Security Issues in SDN..............................................................................................5
3.2 Mitigation and Countermeasures........................................................................................5
Conclusion..................................................................................................................................... 6
References..................................................................................................................................... 7
SDN (SOFTWARE-DEFINED NETWORK)
1. Introduction
The aim of this report is to throw light on the Software Defined Network, which is a
revolutionary technology that is capable of revolutionizing networks through Control Planes
and decoupling the data. This can be helpful in providing much end-to-end controls, flexibility,
and agility that has been necessary for the cloud computing. This report presents a literature
review on the SDN that describes about its layers, comparison with traditional networks and
advantages and disadvantages over the traditional networks. A critical analysis has also been
proposed in this report to describe the security issues and the countermeasures for these issues
associated with the application of SDN.
2. Literature Review
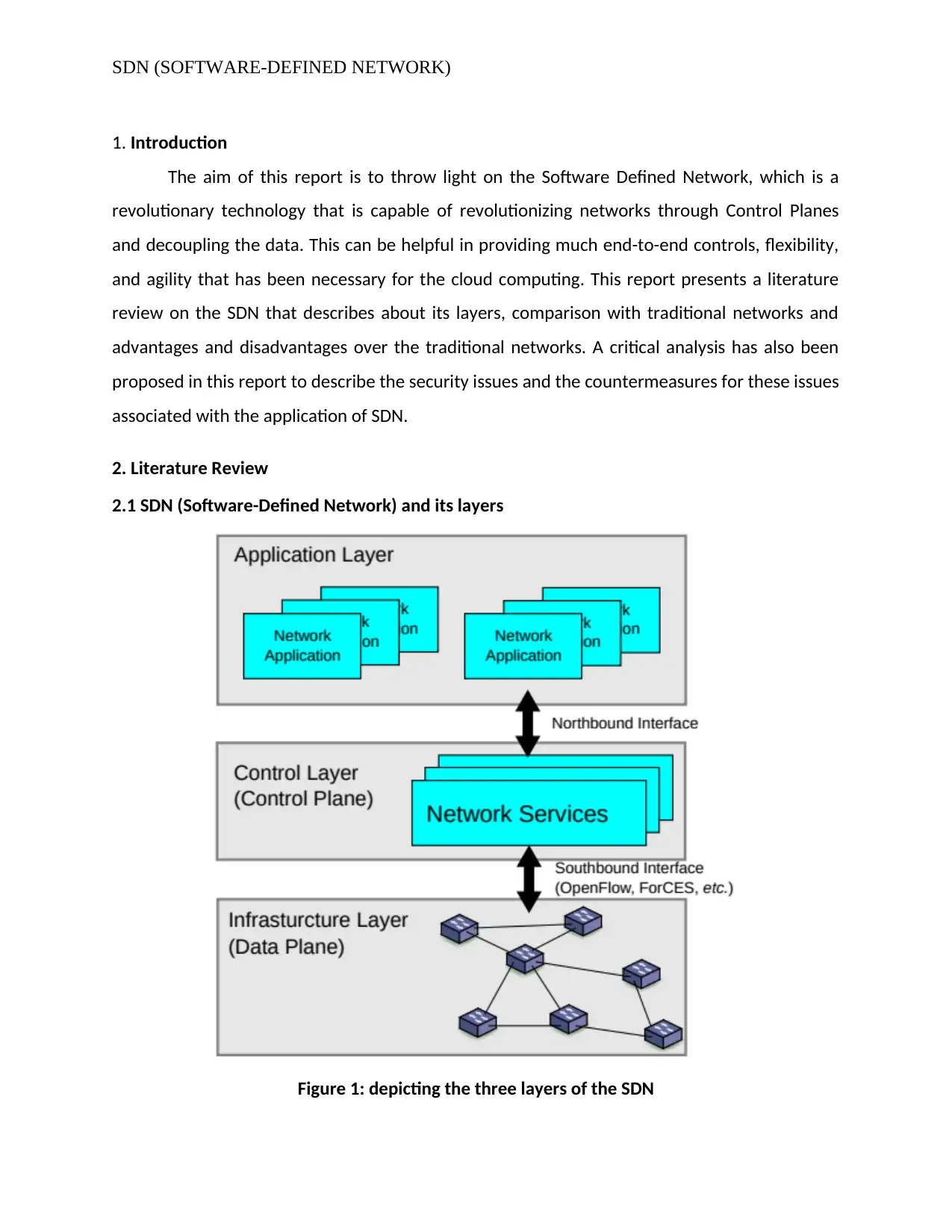
2.1 SDN (Software-Defined Network) and its layers
Figure 1: depicting the three layers of the SDN
1. Introduction
The aim of this report is to throw light on the Software Defined Network, which is a
revolutionary technology that is capable of revolutionizing networks through Control Planes
and decoupling the data. This can be helpful in providing much end-to-end controls, flexibility,
and agility that has been necessary for the cloud computing. This report presents a literature
review on the SDN that describes about its layers, comparison with traditional networks and
advantages and disadvantages over the traditional networks. A critical analysis has also been
proposed in this report to describe the security issues and the countermeasures for these issues
associated with the application of SDN.
2. Literature Review
2.1 SDN (Software-Defined Network) and its layers
Figure 1: depicting the three layers of the SDN
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
SDN (SOFTWARE-DEFINED NETWORK)
(Source: [3])
As described in the above picture, SDN consist of three layers including “data forwarding layer,
control layer and application” as infrastructure layer, control layer and application layer. The
lower layer is also described as data plane that is comprised of forwarding the network
elements [7]. It is responsible for forwarding the data, gathering statistics, and monitoring the
local information. Above this layer, there is control layer (control plane) that is responsible for
the management and programming of the forwarding plane and thus defines the network
routing and operations at the other end. It might comprise more than one or one software
controllers “that communicate with the forwarding network elements through standardized
interfaces, which are referred to as southbound interfaces [2].” Thereafter, the top most layer
is the application layer, which is helpful in introducing additional network features for example
manageability and security, assisting control layer or forwarding schemed and many more. [1]
stated “it can receive global and abstracted view of the same network.
2.2 Comparison of SDN with traditional networks
2.2.1 Comparison of Advantages
The biggest drawback of the traditional network was that there was not any availability of the
resource visibility at the network layer however, SDN is capable of providing network resource
visibility. This allows the centralized controller to monitor the resource requirement. In
traditional networks decision-making and intelligence are spread within the network and in
SDN, it has been a centralized controller that can be helpful in reducing complexities [3]. Thus,
SDN provides a simplified network hardware and eliminates the complexity with the layers of
protocols. Traditional network deployment was much complex as even troubleshooting
includes the archaic tools whereas, SDN’s centralized controller has the characteristic to be
programmed.
2.2.2 Comparison of Disadvantages
It has been much time consuming as compared to that of the traditional networks and
that could be a major concern for the implementation of SDM network. Other drawback of
SDM is that it is more expensive as compared to the traditional ones as the prototype has been
made using the same material that has been used in the final product [6]. Because of the
(Source: [3])
As described in the above picture, SDN consist of three layers including “data forwarding layer,
control layer and application” as infrastructure layer, control layer and application layer. The
lower layer is also described as data plane that is comprised of forwarding the network
elements [7]. It is responsible for forwarding the data, gathering statistics, and monitoring the
local information. Above this layer, there is control layer (control plane) that is responsible for
the management and programming of the forwarding plane and thus defines the network
routing and operations at the other end. It might comprise more than one or one software
controllers “that communicate with the forwarding network elements through standardized
interfaces, which are referred to as southbound interfaces [2].” Thereafter, the top most layer
is the application layer, which is helpful in introducing additional network features for example
manageability and security, assisting control layer or forwarding schemed and many more. [1]
stated “it can receive global and abstracted view of the same network.
2.2 Comparison of SDN with traditional networks
2.2.1 Comparison of Advantages
The biggest drawback of the traditional network was that there was not any availability of the
resource visibility at the network layer however, SDN is capable of providing network resource
visibility. This allows the centralized controller to monitor the resource requirement. In
traditional networks decision-making and intelligence are spread within the network and in
SDN, it has been a centralized controller that can be helpful in reducing complexities [3]. Thus,
SDN provides a simplified network hardware and eliminates the complexity with the layers of
protocols. Traditional network deployment was much complex as even troubleshooting
includes the archaic tools whereas, SDN’s centralized controller has the characteristic to be
programmed.
2.2.2 Comparison of Disadvantages
It has been much time consuming as compared to that of the traditional networks and
that could be a major concern for the implementation of SDM network. Other drawback of
SDM is that it is more expensive as compared to the traditional ones as the prototype has been
made using the same material that has been used in the final product [6]. Because of the
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
SDN (SOFTWARE-DEFINED NETWORK)
internal stresses passed through the layering process, the SDM prototype is weaker than that of
the final product.
3. Critical Analysis
3.1 Critical Security Issues in SDN
Tunnel Bypassing and Packet Encryption: It is easy to treat the different payloads in the SDN
because it has adopted the “flow-based forwarding scheme” that certainly allows the intruder
to customize the packets in this network [4]. After the packets travelled to the other end, the
inner packets automatically gets routed, decapsulated, and decrypted as it is based on the new
network policy. Malicious users could use this window to skip the networking border and thus
enters the control policy of the network.
DDoS Attacks: the control layer of the SDN is vulnerable to DDoS (Distributed Denial of Service)
attacks as more than one compromised hosts distributing in the same network would might
flood with packets to the network. [8] explains “Since not all rules will already be available in
the switches’ tables, many queries will be generated and sent to the controller which ends up
utilizing the controller’s processing power causing legitimate queries to be delayed or
dropped.”
Compromised Controller Attacks: the intruders might be able to gain access to the controller
through keeping the switches controlled through compromising or programming the controller.
This compromised controller could be used to as a platform for the execution of the malicious
code or drop each and every incoming traffics.
3.2 Mitigation and Countermeasures
For the above security issues, following are the countermeasures respectively:
Tunnel Bypassing and Packet Encryption can be addressed through the construction of models
that is capable of identifying the type of encrypted packet’s load type on the basis of the traffic
statistics analysis for example arrival timing of the interpacket or analyzing the message length
and many more [5].
internal stresses passed through the layering process, the SDM prototype is weaker than that of
the final product.
3. Critical Analysis
3.1 Critical Security Issues in SDN
Tunnel Bypassing and Packet Encryption: It is easy to treat the different payloads in the SDN
because it has adopted the “flow-based forwarding scheme” that certainly allows the intruder
to customize the packets in this network [4]. After the packets travelled to the other end, the
inner packets automatically gets routed, decapsulated, and decrypted as it is based on the new
network policy. Malicious users could use this window to skip the networking border and thus
enters the control policy of the network.
DDoS Attacks: the control layer of the SDN is vulnerable to DDoS (Distributed Denial of Service)
attacks as more than one compromised hosts distributing in the same network would might
flood with packets to the network. [8] explains “Since not all rules will already be available in
the switches’ tables, many queries will be generated and sent to the controller which ends up
utilizing the controller’s processing power causing legitimate queries to be delayed or
dropped.”
Compromised Controller Attacks: the intruders might be able to gain access to the controller
through keeping the switches controlled through compromising or programming the controller.
This compromised controller could be used to as a platform for the execution of the malicious
code or drop each and every incoming traffics.
3.2 Mitigation and Countermeasures
For the above security issues, following are the countermeasures respectively:
Tunnel Bypassing and Packet Encryption can be addressed through the construction of models
that is capable of identifying the type of encrypted packet’s load type on the basis of the traffic
statistics analysis for example arrival timing of the interpacket or analyzing the message length
and many more [5].
SDN (SOFTWARE-DEFINED NETWORK)
The solution for the second issue can be described as the replication that could be helpful in
managing the network through multiple physical controller’s manager despite of the single user
or controller. Whereas, the forwarding plane should be operating while the single programmer
is involved in the configuration of the whole network.
There is the need of the resiliency against the third type of attack mentioned above and this
type of attack could be fought with control replication [4]. Although, this solution will only be
applicable if every controller has been installed within a single platform in manner to share and
transfer the same threat or vulnerability and force the intruder to enter every one network
once it enters the network of the single controller.
Conclusion
Based on the above report it can be concluded that SDN has been an innovative and emerging
technology that could revolutionized the networking business. Through the embracement of
the network automation, the organization would be able to significantly enhance the flexibility
of the network and save a very large time. This paper discusses the three layers of the SDN and
explained about the advantages and disadvantages of the SDN. It can be concluded that despite
of have certain security issues the SDN is a far better technology for the networking as
compared to those of traditional networking concepts and it could be much applicable and
secure in the real-life implementation.
The solution for the second issue can be described as the replication that could be helpful in
managing the network through multiple physical controller’s manager despite of the single user
or controller. Whereas, the forwarding plane should be operating while the single programmer
is involved in the configuration of the whole network.
There is the need of the resiliency against the third type of attack mentioned above and this
type of attack could be fought with control replication [4]. Although, this solution will only be
applicable if every controller has been installed within a single platform in manner to share and
transfer the same threat or vulnerability and force the intruder to enter every one network
once it enters the network of the single controller.
Conclusion
Based on the above report it can be concluded that SDN has been an innovative and emerging
technology that could revolutionized the networking business. Through the embracement of
the network automation, the organization would be able to significantly enhance the flexibility
of the network and save a very large time. This paper discusses the three layers of the SDN and
explained about the advantages and disadvantages of the SDN. It can be concluded that despite
of have certain security issues the SDN is a far better technology for the networking as
compared to those of traditional networking concepts and it could be much applicable and
secure in the real-life implementation.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
SDN (SOFTWARE-DEFINED NETWORK)
References
[1] Alvizu, R., Maier, G., Kukreja, N., Pattavina, A., Morro, R., Capello, A. and Cavazzoni, C.,
2017. Comprehensive survey on T-SDN: Software-defined networking for transport
networks. IEEE Communications Surveys & Tutorials, 19(4), pp.2232-2283.
[2] Baktir, A.C., Ozgovde, A. and Ersoy, C., 2017. How Can Edge Computing Benefit From
Software-Defined Networking: A Survey, Use Cases, and Future Directions. IEEE
Communications Surveys & Tutorials, 19(4), pp.2359-2391.
[3] Karakus, M. and Durresi, A., 2017. A survey: Control plane scalability issues and
approaches in Software-Defined Networking (SDN). Computer Networks, 112, pp.279-
293.
[4] Karakus, M. and Durresi, A., 2017. Quality of service (qos) in software defined
networking (sdn): A survey. Journal of Network and Computer Applications, 80, pp.200-
218.
[5] Khan, S., Gani, A., Wahab, A.W.A., Guizani, M. and Khan, M.K., 2017. Topology discovery
in software defined networks: Threats, taxonomy, and state-of-the-art. IEEE
Communications Surveys & Tutorials, 19(1), pp.303-324.
[6] Lee, S., Kim, J., Shin, S., Porras, P. and Yegneswaran, V., 2017, June. Athena: A
framework for scalable anomaly detection in software-defined networks. In Dependable
Systems and Networks (DSN), 2017 47th Annual IEEE/IFIP International Conference
on (pp. 249-260). IEEE.
[7] Rawat, D.B. and Reddy, S.R., 2017. Software defined networking architecture, security
and energy efficiency: A survey. IEEE Communications Surveys & Tutorials, 19(1), pp.325-
346.
[8] Tsai, S.C., Liu, I.H., Lu, C.T., Chang, C.H. and Li, J.S., 2017. Defending cloud computing
environment against the challenge of DDoS attacks based on software defined network.
References
[1] Alvizu, R., Maier, G., Kukreja, N., Pattavina, A., Morro, R., Capello, A. and Cavazzoni, C.,
2017. Comprehensive survey on T-SDN: Software-defined networking for transport
networks. IEEE Communications Surveys & Tutorials, 19(4), pp.2232-2283.
[2] Baktir, A.C., Ozgovde, A. and Ersoy, C., 2017. How Can Edge Computing Benefit From
Software-Defined Networking: A Survey, Use Cases, and Future Directions. IEEE
Communications Surveys & Tutorials, 19(4), pp.2359-2391.
[3] Karakus, M. and Durresi, A., 2017. A survey: Control plane scalability issues and
approaches in Software-Defined Networking (SDN). Computer Networks, 112, pp.279-
293.
[4] Karakus, M. and Durresi, A., 2017. Quality of service (qos) in software defined
networking (sdn): A survey. Journal of Network and Computer Applications, 80, pp.200-
218.
[5] Khan, S., Gani, A., Wahab, A.W.A., Guizani, M. and Khan, M.K., 2017. Topology discovery
in software defined networks: Threats, taxonomy, and state-of-the-art. IEEE
Communications Surveys & Tutorials, 19(1), pp.303-324.
[6] Lee, S., Kim, J., Shin, S., Porras, P. and Yegneswaran, V., 2017, June. Athena: A
framework for scalable anomaly detection in software-defined networks. In Dependable
Systems and Networks (DSN), 2017 47th Annual IEEE/IFIP International Conference
on (pp. 249-260). IEEE.
[7] Rawat, D.B. and Reddy, S.R., 2017. Software defined networking architecture, security
and energy efficiency: A survey. IEEE Communications Surveys & Tutorials, 19(1), pp.325-
346.
[8] Tsai, S.C., Liu, I.H., Lu, C.T., Chang, C.H. and Li, J.S., 2017. Defending cloud computing
environment against the challenge of DDoS attacks based on software defined network.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser

SDN (SOFTWARE-DEFINED NETWORK)
In Advances in Intelligent Information Hiding and Multimedia Signal Processing (pp. 285-
292). Springer, Cham.
In Advances in Intelligent Information Hiding and Multimedia Signal Processing (pp. 285-
292). Springer, Cham.
1 out of 8
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.




