COIT20246 Assignment: Exploring Technologies, Security, and Protocols
VerifiedAdded on 2020/05/16
|10
|3372
|125
Homework Assignment
AI Summary
This assignment, submitted for COIT20246, explores a range of computing technologies and their applications, along with associated security and privacy concerns. The assignment begins by examining mass storage technologies, specifically Direct-Attached Storage (DAS) and Network-Attached Storage (NAS), discussing their features and uses. It then delves into real-time operating systems (RTOS) and their benefits within the healthcare sector. The third task focuses on mobile cloud computing, addressing security and privacy issues in the finance sector. Next, it discusses the TCP/IP transport layer and its common standards, UDP and TCP. The assignment also explores the cyber security challenges faced by the health sector in the Internet of Things (IoT) era, and the importance of real-time data capture, data visualization, data analytics, and API protocols in IoT cloud applications. Finally, it provides solutions to deal with security threats in Social Network Services (SNS). The assignment is supported by summaries and references to relevant research papers and articles.
COIT 20246 ASSIGNMENT SUBMISSION
Due date: Thursday Week 11 (2PM AEST)
Part: Written Assessment
Weighting: 30% of total assessment.
Submission: Electronic (see course website for details)
Please fill in the following details:
Student Name
Student Number
Due date: Thursday Week 11 (2PM AEST)
Part: Written Assessment
Weighting: 30% of total assessment.
Submission: Electronic (see course website for details)
Please fill in the following details:
Student Name
Student Number
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Tasks
Week 1
Task The past decade has witnessed tremendous advances in computing,
wired and wireless communication, and storage technologies. Discuss
the main features and applications of two mass storage technologies
namely: direct-attachedstorageand network-attached storage.
Summary Title and Reference:
What is the difference between SAN, NAS and DAS?
Deen, G. 2018. NAS vs DAS vs SAN | D-Tech Consulting. [online] D-
Tech Consulting. Available at: https://dtechconsulting.com/nas-vs-
das-san/ [Accessed 22 Jan. 2018].
Summary:
DAS (Direct Attached Storage): It can be described as the computer
storage, which has been connected to the server or a computer, which
is connected to the server or computer through cable. These storage
devices could be externally to the server or the computer and it is
always connected to the server. This article presented the problem is
related to this device that states that there is limited number of disks
those could be supported by the server only. According to Deen
(2018), DAS is the most appropriate approach for the data storage for
a server or a computer.
NAS (Network Attached Storage): this storage media can be
represented as the wireless storage device for the server or the
computer that could be made available for more than one user. It
allows the users to share the same stored data and thus make it much
appropriate for the users. NAS has its own operating system, storage,
and management interface that allows it to be easily connected with
the computers through even with the existing ethernet connection.
There are many beneficial aspects of the application of NAS as it is
very easy to access and low lag time that makes it more popular.
Week 2
Task Real-time operating systems are operating systems that guarantee
a certain capability within a specified time constraint. Discuss the
main benefits of real-time operating systems for the health sector.
Summary Title and Reference:
Real time operating system architectures are important for
medical designers
Moon, J. 2018. Real time operating system architectures are
important for medical designers. [online] Newelectronics.co.uk.
Week 1
Task The past decade has witnessed tremendous advances in computing,
wired and wireless communication, and storage technologies. Discuss
the main features and applications of two mass storage technologies
namely: direct-attachedstorageand network-attached storage.
Summary Title and Reference:
What is the difference between SAN, NAS and DAS?
Deen, G. 2018. NAS vs DAS vs SAN | D-Tech Consulting. [online] D-
Tech Consulting. Available at: https://dtechconsulting.com/nas-vs-
das-san/ [Accessed 22 Jan. 2018].
Summary:
DAS (Direct Attached Storage): It can be described as the computer
storage, which has been connected to the server or a computer, which
is connected to the server or computer through cable. These storage
devices could be externally to the server or the computer and it is
always connected to the server. This article presented the problem is
related to this device that states that there is limited number of disks
those could be supported by the server only. According to Deen
(2018), DAS is the most appropriate approach for the data storage for
a server or a computer.
NAS (Network Attached Storage): this storage media can be
represented as the wireless storage device for the server or the
computer that could be made available for more than one user. It
allows the users to share the same stored data and thus make it much
appropriate for the users. NAS has its own operating system, storage,
and management interface that allows it to be easily connected with
the computers through even with the existing ethernet connection.
There are many beneficial aspects of the application of NAS as it is
very easy to access and low lag time that makes it more popular.
Week 2
Task Real-time operating systems are operating systems that guarantee
a certain capability within a specified time constraint. Discuss the
main benefits of real-time operating systems for the health sector.
Summary Title and Reference:
Real time operating system architectures are important for
medical designers
Moon, J. 2018. Real time operating system architectures are
important for medical designers. [online] Newelectronics.co.uk.
Available at: http://www.newelectronics.co.uk/electronics-
technology/real-time-operating-system-architecture-is-important-
for-medical-designers/35970/ [Accessed 29 Jan. 2018].
Summary:
Real time operating system has many advantageous impact in the
healthcare sector that allows better and effective data collection
and data execution in manner to accomplish the objectives and
activities within the health care. This operating system is much
more reliable and consistent than operating systems being
practiced traditionally and thus make it an appropriate option for
enhancing the efficiency and effectiveness of the healthcare
sector. It allows the user to collect very sensitive and personal
information related to the patient along with a very less response
time in manner to execute the objective. It has become much
more popular after the integration of IoT and RTOS within the
healthcare sector and is also being applicable in the crucial
sectors of the health care including ICU, risky wards and many
more. There are many other advantages such as: cots could be
decreased, treatments could be enhanced, disease management
system could become much effective and efficient through the
collection of data using the Real time operating systems. This
could be helpful measure in eliminating the human error as it
could affect severely to the medical condition of the patient and
thus enhance the way of medical care in the health sector.
Week 3
Tas
k
Mobile Cloud computing has gained a wide acceptance for organisations as
well as individuals by introducing computation, storage and software based
services. Explain the security and privacy issues in relation to the use of the
mobile Cloud computing in the finance sector.
Sum
mar
y
Title and Reference:
Security, Privacy and Challenges in Mobile Cloud Computing (MCC):- A
Critical Study and Comparison
Chaubey, N. and Tank, D. 2018. [online] Available at:
https://www.researchgate.net/profile/Nirbhay_Chaubey/publication/305307
099_Security_Privacy_and_Challenges_in_Mobile_Cloud_Computing_MC
C-
Summary:
Mobile cloud computing has become one of the most innovative and popular
technology that is generally being used by almost the whole world.
Technology advancement has no doubt change the face of the world,
however, there are certain security and privacy issues related to the
application of this technology that can hamper the individual in many ways.
This article stated that data being stored or exchanged using the network of
technology/real-time-operating-system-architecture-is-important-
for-medical-designers/35970/ [Accessed 29 Jan. 2018].
Summary:
Real time operating system has many advantageous impact in the
healthcare sector that allows better and effective data collection
and data execution in manner to accomplish the objectives and
activities within the health care. This operating system is much
more reliable and consistent than operating systems being
practiced traditionally and thus make it an appropriate option for
enhancing the efficiency and effectiveness of the healthcare
sector. It allows the user to collect very sensitive and personal
information related to the patient along with a very less response
time in manner to execute the objective. It has become much
more popular after the integration of IoT and RTOS within the
healthcare sector and is also being applicable in the crucial
sectors of the health care including ICU, risky wards and many
more. There are many other advantages such as: cots could be
decreased, treatments could be enhanced, disease management
system could become much effective and efficient through the
collection of data using the Real time operating systems. This
could be helpful measure in eliminating the human error as it
could affect severely to the medical condition of the patient and
thus enhance the way of medical care in the health sector.
Week 3
Tas
k
Mobile Cloud computing has gained a wide acceptance for organisations as
well as individuals by introducing computation, storage and software based
services. Explain the security and privacy issues in relation to the use of the
mobile Cloud computing in the finance sector.
Sum
mar
y
Title and Reference:
Security, Privacy and Challenges in Mobile Cloud Computing (MCC):- A
Critical Study and Comparison
Chaubey, N. and Tank, D. 2018. [online] Available at:
https://www.researchgate.net/profile/Nirbhay_Chaubey/publication/305307
099_Security_Privacy_and_Challenges_in_Mobile_Cloud_Computing_MC
C-
Summary:
Mobile cloud computing has become one of the most innovative and popular
technology that is generally being used by almost the whole world.
Technology advancement has no doubt change the face of the world,
however, there are certain security and privacy issues related to the
application of this technology that can hamper the individual in many ways.
This article stated that data being stored or exchanged using the network of
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
the mobile cloud computing is vulnerable to data breach or intrusion that
could allow an unauthorized user to access the data or information saved or
exchanged using the network. Chaubey and Tank (2018) stated that
malwares are the most affective malicious code that could lead to the
manipulation, deletion or exposing of the data or information by an
unauthorized person. Software vulnerabilities is another concern that could
lead to privacy and security issues to the individual using mobile cloud
computing. Mobile network security was never provided high concern while
developing mobile devices or using the network that makes it less reliable
for the individuals as it could be a window for the intruders to access the
network and thus affect the privacy and security of the individual utilizing
Mobile Cloud Computing.
Week 4
Task TCP/IPis consists of communication protocols used to transfer
packets between computer hosts within the network. In TCP/IP,
the transport layer is responsible for providing the application
layer with session and datagram communication services.
Discuss the common standards at the transport layer.
Summary Title and Reference:
TCP/IP Protocol Fundamentals Explained with a Diagram
ARORA, H. 2018. [online] Available at:
https://www.thegeekstuff.com/2011/11/tcp-ip-fundamentals/
[Accessed 29 Jan. 2018].
Summary:
User Data Protocol (UDP) and Transmission Control Protocol
(TCP) are the common standards for data transport layer those
have been being utilized mostly in the current world. Arora
(2018) stated that TCP can be categorized in reliable source
however, UDP is not much reliable as compared to that of TCP
and thus being widely used in the networks for the exchange of
data or information. TCP provides error control and extensive
data flow control for ensuring that the data or information being
travelled using the network is capable of ensuring its safety and
thus enhance the security and possibility of data delivery. Packets
of data are generally used in the UDP for the exchange of
information and integrity could be evaluated after the delivery of
the message. TCP is capable of handling the data streaming by
the bytes stream and do not differentiate between the
transmission and indication of the signal message. The packets
created in the UDP transport layer those does not have any
definite boundary and thus after collaborating the messages it
yields the original message. This helps in ensuring that the
could allow an unauthorized user to access the data or information saved or
exchanged using the network. Chaubey and Tank (2018) stated that
malwares are the most affective malicious code that could lead to the
manipulation, deletion or exposing of the data or information by an
unauthorized person. Software vulnerabilities is another concern that could
lead to privacy and security issues to the individual using mobile cloud
computing. Mobile network security was never provided high concern while
developing mobile devices or using the network that makes it less reliable
for the individuals as it could be a window for the intruders to access the
network and thus affect the privacy and security of the individual utilizing
Mobile Cloud Computing.
Week 4
Task TCP/IPis consists of communication protocols used to transfer
packets between computer hosts within the network. In TCP/IP,
the transport layer is responsible for providing the application
layer with session and datagram communication services.
Discuss the common standards at the transport layer.
Summary Title and Reference:
TCP/IP Protocol Fundamentals Explained with a Diagram
ARORA, H. 2018. [online] Available at:
https://www.thegeekstuff.com/2011/11/tcp-ip-fundamentals/
[Accessed 29 Jan. 2018].
Summary:
User Data Protocol (UDP) and Transmission Control Protocol
(TCP) are the common standards for data transport layer those
have been being utilized mostly in the current world. Arora
(2018) stated that TCP can be categorized in reliable source
however, UDP is not much reliable as compared to that of TCP
and thus being widely used in the networks for the exchange of
data or information. TCP provides error control and extensive
data flow control for ensuring that the data or information being
travelled using the network is capable of ensuring its safety and
thus enhance the security and possibility of data delivery. Packets
of data are generally used in the UDP for the exchange of
information and integrity could be evaluated after the delivery of
the message. TCP is capable of handling the data streaming by
the bytes stream and do not differentiate between the
transmission and indication of the signal message. The packets
created in the UDP transport layer those does not have any
definite boundary and thus after collaborating the messages it
yields the original message. This helps in ensuring that the
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
message sent is received to the desired individual and actual
message has been delivered to the user accepting message.
Week 5
Task The Internet of Things (IoT) is a system of interrelated
computing devices that are provided with unique identifiers and
the ability to transfer data over a network without requiring
human-to-human or human-to-computer interaction. Discuss the
cyber security challenges faced by the health sector in this IoT
era.
Summary Title and Reference:
Security of the Internet of Things (IoT) in healthcare
Nccgroup.trust. 2018. Cite a Website -. [online] Available at:
www.nccgroup.trust.
https://www.nccgroup.trust/uk/about-us/newsroom-and-events/bl
ogs/2017/february/security-of-the-internet-of-things-iot-in-
healthcare/ [Accessed 29 Jan. 2018].
Summary:
IoT has been no doubt became the integral part for the
technologies and thus enhancing the experience or every sector
with the help of real data collection and execution. It has been
widely spread in the healthcare sector however, it is also
vulnerable to security issues such as intrusion, DDoD attacks,
malwares, viruses and many other malicious coding those could
affect the data or information saved in the database in many
ways. Most of the recent activities of intrusion and breaches have
remind the world that the data or information being transferred or
saved in the internet are vulnerable to breaches and intrusion that
could result in the unauthorized access of the individual. Medical
sector always collects very personal and sensitive information
and expose of this information could affect the user in many
ways including financially and physically. IoT is generally
comprised of sensors those could be hacked in very easy manner
through proper coding that could allow the access of the devices
based on the IoT to use it according to their purpose. Proper
awareness and training is needed to utilize the devices or
technology in secured manner as not utilizing efficiently could
allow the intruders to access the data or information saved in the
network.
Week 6
Task Internet of Things (IoT) Cloud is a model designed to facilitate
the information society, enabling advanced services by
interconnecting physical and virtual things based on, existing and
message has been delivered to the user accepting message.
Week 5
Task The Internet of Things (IoT) is a system of interrelated
computing devices that are provided with unique identifiers and
the ability to transfer data over a network without requiring
human-to-human or human-to-computer interaction. Discuss the
cyber security challenges faced by the health sector in this IoT
era.
Summary Title and Reference:
Security of the Internet of Things (IoT) in healthcare
Nccgroup.trust. 2018. Cite a Website -. [online] Available at:
www.nccgroup.trust.
https://www.nccgroup.trust/uk/about-us/newsroom-and-events/bl
ogs/2017/february/security-of-the-internet-of-things-iot-in-
healthcare/ [Accessed 29 Jan. 2018].
Summary:
IoT has been no doubt became the integral part for the
technologies and thus enhancing the experience or every sector
with the help of real data collection and execution. It has been
widely spread in the healthcare sector however, it is also
vulnerable to security issues such as intrusion, DDoD attacks,
malwares, viruses and many other malicious coding those could
affect the data or information saved in the database in many
ways. Most of the recent activities of intrusion and breaches have
remind the world that the data or information being transferred or
saved in the internet are vulnerable to breaches and intrusion that
could result in the unauthorized access of the individual. Medical
sector always collects very personal and sensitive information
and expose of this information could affect the user in many
ways including financially and physically. IoT is generally
comprised of sensors those could be hacked in very easy manner
through proper coding that could allow the access of the devices
based on the IoT to use it according to their purpose. Proper
awareness and training is needed to utilize the devices or
technology in secured manner as not utilizing efficiently could
allow the intruders to access the data or information saved in the
network.
Week 6
Task Internet of Things (IoT) Cloud is a model designed to facilitate
the information society, enabling advanced services by
interconnecting physical and virtual things based on, existing and
evolving, interoperable information and communication
technologies through ennoblement of ubiquitous, convenient, on-
demand network access to a shared pool of configurable
computing resources. Explain the importance of real time data
capture capability, data visualisation, data analytics, and API
protocols in the application of IoT Cloud.
Summary Title and Reference:
Big IoT Data Analytics: Architecture, Opportunities, and Open
Research Challenges
Marjani, M., Nasaruddin, F., Gani, A., Karim, A., Abaker Targio
Hashem, I., Siddiqa, A. and Yaqoob, I. 2018. Big IoT Data
Analytics: Architecture, Opportunities, and Open Research
Challenges - IEEE Journals & Magazine. [online]
Ieeexplore.ieee.org. Available at:
http://ieeexplore.ieee.org/document/7888916/?part=1 [Accessed
29 Jan. 2018].
Summary:
Health sector is one of the sensitive sector in the current situation
as very personal information are being collected for the medical
care and thus the databases of the health sector is the most
targeted place in the present time. This article was a survey on
twenty-five different cloud companies who provides cloud
services to the health sector and it was found that most crucial
aspect that does not meet the medical requirement is interaction
with the HER system. This is the most lacking aspect of the IoT
cloud services despite of allowing real time data collection and
execution and thus, important data or information are not being
collected in the right time. Interoperability is the other factor that
lacks in this technology as this technology leads to the locking of
the data or information to the single computer that could lead to
loss in the patient care system. Other challenging factor in the
application of IoT is that the data has been meaningless if the
collected real time data has not been in the context with the full
patient record. Data breaches or intrusion are some of other
challenging factors those are drawing back the effective
implementation of the IoT cloud.
Week 7
Task A Social Network Service (SNS) is a kind of web service for
establishing a virtual connection between people with similar
interests, backgrounds, and activities. However, there are
different security and privacy threats that target every user of
social networking sites. Provide five solutions to deal with these
security threats.
Summary Title and Reference:
A Survey on Privacy and Security Issues in Social Networking
technologies through ennoblement of ubiquitous, convenient, on-
demand network access to a shared pool of configurable
computing resources. Explain the importance of real time data
capture capability, data visualisation, data analytics, and API
protocols in the application of IoT Cloud.
Summary Title and Reference:
Big IoT Data Analytics: Architecture, Opportunities, and Open
Research Challenges
Marjani, M., Nasaruddin, F., Gani, A., Karim, A., Abaker Targio
Hashem, I., Siddiqa, A. and Yaqoob, I. 2018. Big IoT Data
Analytics: Architecture, Opportunities, and Open Research
Challenges - IEEE Journals & Magazine. [online]
Ieeexplore.ieee.org. Available at:
http://ieeexplore.ieee.org/document/7888916/?part=1 [Accessed
29 Jan. 2018].
Summary:
Health sector is one of the sensitive sector in the current situation
as very personal information are being collected for the medical
care and thus the databases of the health sector is the most
targeted place in the present time. This article was a survey on
twenty-five different cloud companies who provides cloud
services to the health sector and it was found that most crucial
aspect that does not meet the medical requirement is interaction
with the HER system. This is the most lacking aspect of the IoT
cloud services despite of allowing real time data collection and
execution and thus, important data or information are not being
collected in the right time. Interoperability is the other factor that
lacks in this technology as this technology leads to the locking of
the data or information to the single computer that could lead to
loss in the patient care system. Other challenging factor in the
application of IoT is that the data has been meaningless if the
collected real time data has not been in the context with the full
patient record. Data breaches or intrusion are some of other
challenging factors those are drawing back the effective
implementation of the IoT cloud.
Week 7
Task A Social Network Service (SNS) is a kind of web service for
establishing a virtual connection between people with similar
interests, backgrounds, and activities. However, there are
different security and privacy threats that target every user of
social networking sites. Provide five solutions to deal with these
security threats.
Summary Title and Reference:
A Survey on Privacy and Security Issues in Social Networking
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Services
Gunatilaka, D. 2018. www.cse.wustl.edu.[online] Cse.wustl.edu.
Available at:
http://www.cse.wustl.edu/~jain/cse571-11/ftp/social.pdf
[Accessed 29 Jan. 2018].
Summary:
Social Networking Services are the most popular technology
nowadays that is having a tail of security issues with it. Through
proper implementation and protective measures, these networks
could be highly secured and could result in enhancing the
security of the network. Watermarking is a method that could be
used as a signature on the digital media files that will allow the
owner to retain his or her ownership. Co-ownership, and
steganalysis are some of the other security measures that could
be applied to the files containing digital media in manner to
manage the ownership between more than on e user based on the
policies. There are many technical ways to make it happen and
thus, distribute the ownership of the same file. Encryption is one
of the most secured and advanced technology for the current
digital world that allows user to encrypt the file using a unique
code and receiver will have to use the unique decryption key to
access the file. Digital oblivion is another advanced technology
that allows the user to set expiry date or time on the digital media
file in manner to remove the data access of the file after a certain
time and thus secure the file.
Week 8
Task Big data has been considered to be a breakthrough technological
development over recent year. Big data is based on large volumes
of extensively varied data that are generated, captured, and
processed at high velocity. Discuss the main challenges as well as
the social and economic values for organizations in adopting big
data.
Summary Title and Reference:
Big Data: Challenges, Opportunities and Realities
Bhadani, A. and Jothimani, D. 2018.arxiv.org. [online] Arxiv.org.
Available at:
https://arxiv.org/ftp/arxiv/papers/1705/1705.04928.pdf [Accessed
29 Jan. 2018].
Summary:
Bhadani and Jothimani (2018) stated that big data has more than
expected advantages however, current world is not entirely ready
for the implementation of big data in each sector. They stated that
flexibility, Handoop management, and less knowledge about the
Gunatilaka, D. 2018. www.cse.wustl.edu.[online] Cse.wustl.edu.
Available at:
http://www.cse.wustl.edu/~jain/cse571-11/ftp/social.pdf
[Accessed 29 Jan. 2018].
Summary:
Social Networking Services are the most popular technology
nowadays that is having a tail of security issues with it. Through
proper implementation and protective measures, these networks
could be highly secured and could result in enhancing the
security of the network. Watermarking is a method that could be
used as a signature on the digital media files that will allow the
owner to retain his or her ownership. Co-ownership, and
steganalysis are some of the other security measures that could
be applied to the files containing digital media in manner to
manage the ownership between more than on e user based on the
policies. There are many technical ways to make it happen and
thus, distribute the ownership of the same file. Encryption is one
of the most secured and advanced technology for the current
digital world that allows user to encrypt the file using a unique
code and receiver will have to use the unique decryption key to
access the file. Digital oblivion is another advanced technology
that allows the user to set expiry date or time on the digital media
file in manner to remove the data access of the file after a certain
time and thus secure the file.
Week 8
Task Big data has been considered to be a breakthrough technological
development over recent year. Big data is based on large volumes
of extensively varied data that are generated, captured, and
processed at high velocity. Discuss the main challenges as well as
the social and economic values for organizations in adopting big
data.
Summary Title and Reference:
Big Data: Challenges, Opportunities and Realities
Bhadani, A. and Jothimani, D. 2018.arxiv.org. [online] Arxiv.org.
Available at:
https://arxiv.org/ftp/arxiv/papers/1705/1705.04928.pdf [Accessed
29 Jan. 2018].
Summary:
Bhadani and Jothimani (2018) stated that big data has more than
expected advantages however, current world is not entirely ready
for the implementation of big data in each sector. They stated that
flexibility, Handoop management, and less knowledge about the
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
technology are the most vital challenges that is being faced for
the complete implementation of the Big Data analytics. Data is
being stored in the cloud and physical databases and more than
expectations, data are being collected in manner to bring out the
maximum efficiency of the technology that could lead to the
shortage of the space after some time. Technologies based on the
big data analytics need learned people and people with
knowledge only could utilize this technology in an efficient
manner and assigning individuals with less talent and knowledge
would not might be able to execute the objectives in an effective
and efficient manner. Privacy issues can be categorized in the
challenges being faced by the organization while utilizing the big
data analytics. Big Data analytics generally collects the data or
information related to the choices and interest of the individuals
connected to the network and thus could affect the privacy of the
individual of this data reaches to an unauthorized person.
Week 9
Task There has been a growing interest in the application of agile and lean
practices for software development. Discuss the benefits of agile and lean
practices and their impacts on project constraints.
Summ
ary
Title and Reference:
The Impacts of Agile and Lean Practices on Project Constraints: A
Tertiary Study
Nurdiania, I., Börstlera, J. and Frickera, S. 2018. www.bth.se. [online]
Bth.se. Available at:
http://www.bth.se/com/inu.nsf/attachments/AgileTertiaryStudy_pdf/$file/
AgileTertiaryStudy.pdf [Accessed 29 Jan. 2018].
Summary:
Not many studies have been performed yet for the calculation of the
impact of lean and agile practices on the project constraints whereas,
Nurdiani, Borstler, and Fricker (2018) had executed this study that
implies that these practices could result in either positive or negative both
impacts on the constraints of the project. It can be stated that such
practices do not always have negative impact mostly these practices could
be helpful in accomplishing the constraints of the project in an effective
manner and in easy way. There are many advantages on the application of
these practices that include the team management, better communication,
accomplishment of tasks before the deadline and thus it could affect the
project in positive manner. Adoption is another beneficial aspect of these
practices including the identification of candidates with capability, correct
resources pool and many more. Thus, it can be stated that utilizing these
practices in an efficient manner could allow the team leader to manage
the team and the objectives of the project within the scheduled time and
budget set during the project planning. These practices could be a boon
the complete implementation of the Big Data analytics. Data is
being stored in the cloud and physical databases and more than
expectations, data are being collected in manner to bring out the
maximum efficiency of the technology that could lead to the
shortage of the space after some time. Technologies based on the
big data analytics need learned people and people with
knowledge only could utilize this technology in an efficient
manner and assigning individuals with less talent and knowledge
would not might be able to execute the objectives in an effective
and efficient manner. Privacy issues can be categorized in the
challenges being faced by the organization while utilizing the big
data analytics. Big Data analytics generally collects the data or
information related to the choices and interest of the individuals
connected to the network and thus could affect the privacy of the
individual of this data reaches to an unauthorized person.
Week 9
Task There has been a growing interest in the application of agile and lean
practices for software development. Discuss the benefits of agile and lean
practices and their impacts on project constraints.
Summ
ary
Title and Reference:
The Impacts of Agile and Lean Practices on Project Constraints: A
Tertiary Study
Nurdiania, I., Börstlera, J. and Frickera, S. 2018. www.bth.se. [online]
Bth.se. Available at:
http://www.bth.se/com/inu.nsf/attachments/AgileTertiaryStudy_pdf/$file/
AgileTertiaryStudy.pdf [Accessed 29 Jan. 2018].
Summary:
Not many studies have been performed yet for the calculation of the
impact of lean and agile practices on the project constraints whereas,
Nurdiani, Borstler, and Fricker (2018) had executed this study that
implies that these practices could result in either positive or negative both
impacts on the constraints of the project. It can be stated that such
practices do not always have negative impact mostly these practices could
be helpful in accomplishing the constraints of the project in an effective
manner and in easy way. There are many advantages on the application of
these practices that include the team management, better communication,
accomplishment of tasks before the deadline and thus it could affect the
project in positive manner. Adoption is another beneficial aspect of these
practices including the identification of candidates with capability, correct
resources pool and many more. Thus, it can be stated that utilizing these
practices in an efficient manner could allow the team leader to manage
the team and the objectives of the project within the scheduled time and
budget set during the project planning. These practices could be a boon
for the organization or the heads involved in the project for the
accomplishment of the project constraints and meeting the requirements
of the project.
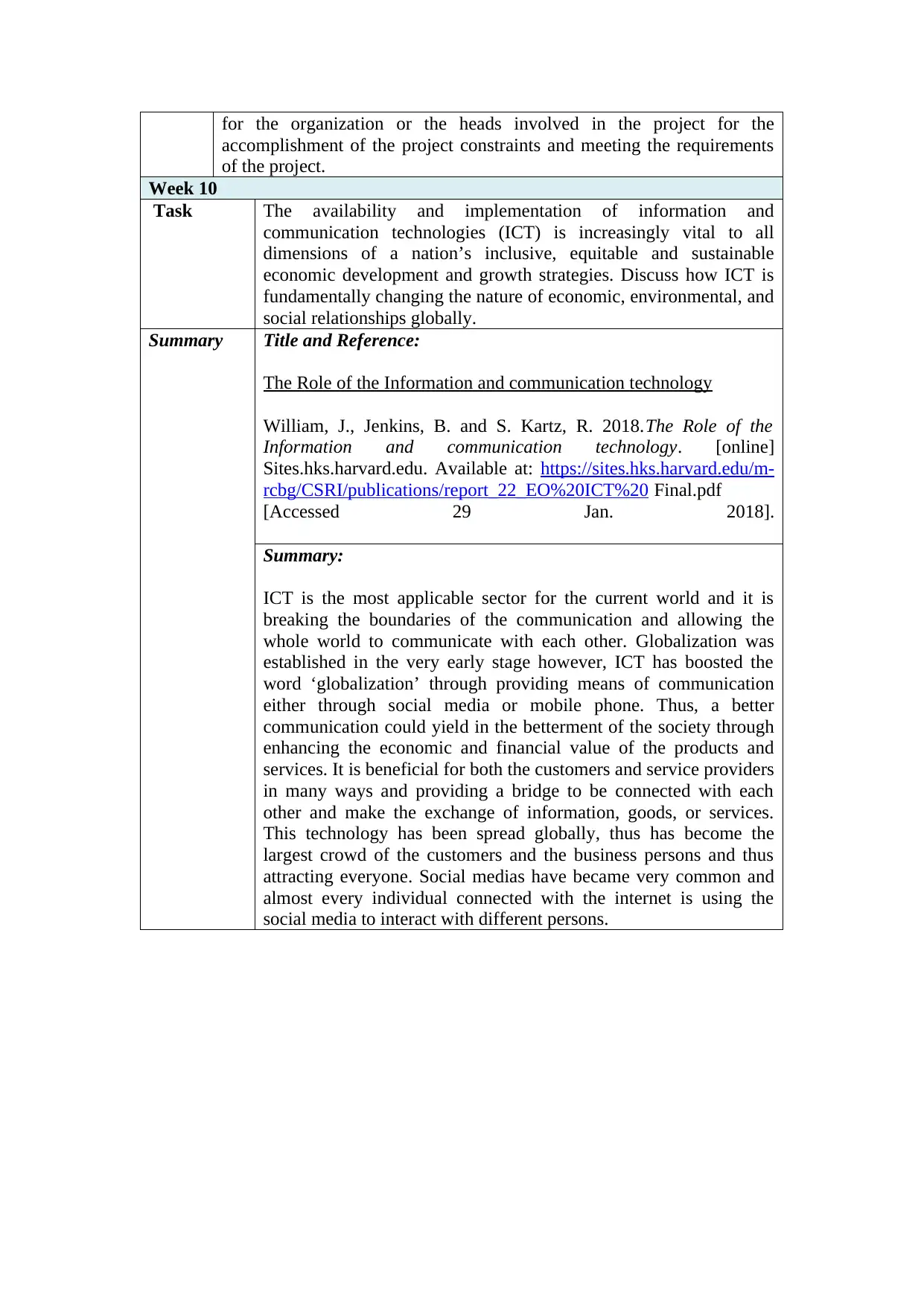
Week 10
Task The availability and implementation of information and
communication technologies (ICT) is increasingly vital to all
dimensions of a nation’s inclusive, equitable and sustainable
economic development and growth strategies. Discuss how ICT is
fundamentally changing the nature of economic, environmental, and
social relationships globally.
Summary Title and Reference:
The Role of the Information and communication technology
William, J., Jenkins, B. and S. Kartz, R. 2018.The Role of the
Information and communication technology. [online]
Sites.hks.harvard.edu. Available at: https://sites.hks.harvard.edu/m-
rcbg/CSRI/publications/report_22_EO%20ICT%20 Final.pdf
[Accessed 29 Jan. 2018].
Summary:
ICT is the most applicable sector for the current world and it is
breaking the boundaries of the communication and allowing the
whole world to communicate with each other. Globalization was
established in the very early stage however, ICT has boosted the
word ‘globalization’ through providing means of communication
either through social media or mobile phone. Thus, a better
communication could yield in the betterment of the society through
enhancing the economic and financial value of the products and
services. It is beneficial for both the customers and service providers
in many ways and providing a bridge to be connected with each
other and make the exchange of information, goods, or services.
This technology has been spread globally, thus has become the
largest crowd of the customers and the business persons and thus
attracting everyone. Social medias have became very common and
almost every individual connected with the internet is using the
social media to interact with different persons.
accomplishment of the project constraints and meeting the requirements
of the project.
Week 10
Task The availability and implementation of information and
communication technologies (ICT) is increasingly vital to all
dimensions of a nation’s inclusive, equitable and sustainable
economic development and growth strategies. Discuss how ICT is
fundamentally changing the nature of economic, environmental, and
social relationships globally.
Summary Title and Reference:
The Role of the Information and communication technology
William, J., Jenkins, B. and S. Kartz, R. 2018.The Role of the
Information and communication technology. [online]
Sites.hks.harvard.edu. Available at: https://sites.hks.harvard.edu/m-
rcbg/CSRI/publications/report_22_EO%20ICT%20 Final.pdf
[Accessed 29 Jan. 2018].
Summary:
ICT is the most applicable sector for the current world and it is
breaking the boundaries of the communication and allowing the
whole world to communicate with each other. Globalization was
established in the very early stage however, ICT has boosted the
word ‘globalization’ through providing means of communication
either through social media or mobile phone. Thus, a better
communication could yield in the betterment of the society through
enhancing the economic and financial value of the products and
services. It is beneficial for both the customers and service providers
in many ways and providing a bridge to be connected with each
other and make the exchange of information, goods, or services.
This technology has been spread globally, thus has become the
largest crowd of the customers and the business persons and thus
attracting everyone. Social medias have became very common and
almost every individual connected with the internet is using the
social media to interact with different persons.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
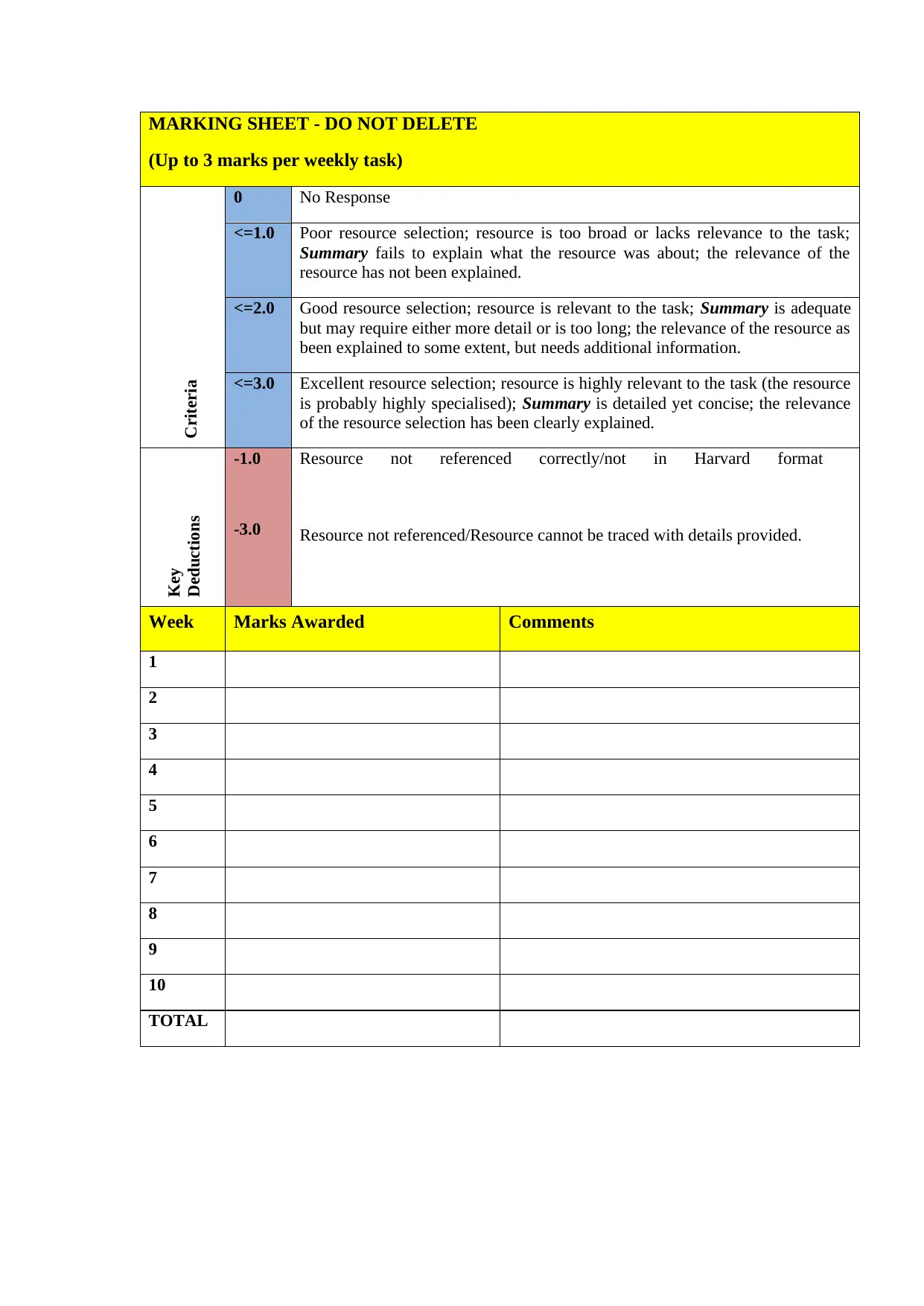
MARKING SHEET - DO NOT DELETE
(Up to 3 marks per weekly task)
Criteria
0 No Response
<=1.0 Poor resource selection; resource is too broad or lacks relevance to the task;
Summary fails to explain what the resource was about; the relevance of the
resource has not been explained.
<=2.0 Good resource selection; resource is relevant to the task; Summary is adequate
but may require either more detail or is too long; the relevance of the resource as
been explained to some extent, but needs additional information.
<=3.0 Excellent resource selection; resource is highly relevant to the task (the resource
is probably highly specialised); Summary is detailed yet concise; the relevance
of the resource selection has been clearly explained.
Key
Deductions
-1.0
-3.0
Resource not referenced correctly/not in Harvard format
Resource not referenced/Resource cannot be traced with details provided.
Week Marks Awarded Comments
1
2
3
4
5
6
7
8
9
10
TOTAL
(Up to 3 marks per weekly task)
Criteria
0 No Response
<=1.0 Poor resource selection; resource is too broad or lacks relevance to the task;
Summary fails to explain what the resource was about; the relevance of the
resource has not been explained.
<=2.0 Good resource selection; resource is relevant to the task; Summary is adequate
but may require either more detail or is too long; the relevance of the resource as
been explained to some extent, but needs additional information.
<=3.0 Excellent resource selection; resource is highly relevant to the task (the resource
is probably highly specialised); Summary is detailed yet concise; the relevance
of the resource selection has been clearly explained.
Key
Deductions
-1.0
-3.0
Resource not referenced correctly/not in Harvard format
Resource not referenced/Resource cannot be traced with details provided.
Week Marks Awarded Comments
1
2
3
4
5
6
7
8
9
10
TOTAL
1 out of 10
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.




