Analysis of VPN Types and Security Features for Starnet
VerifiedAdded on 2020/02/19
|13
|3826
|65
Report
AI Summary
This report provides a comprehensive overview of the Virtual Private Network (VPN) solution implemented for Starnet, an organization with sites in Sydney and Melbourne. It begins with an executive summary outlining the need for secure data exchange between sites. The report details the differences between internal private and external public IP interfaces and recommends the use of IPSec VPN. It then explores various VPN types, including remote access and site-to-site, highlighting their differences and advantages. The report further examines the security features of VPNs, such as traffic filtering and system connectivity, and delves into the advantages and disadvantages of VPN technology. The implementation of IPSec is also justified, along with a discussion of its security protocols. This report offers a valuable analysis of the VPN solution, including the types of VPNs, security features, and protocols implemented, and the report also covers the advantages and disadvantages of VPN technology.

Running head: VIRTUAL PRIVATE NETWORKS
Virtual Private Networks
Name of the Student
Name of the University
Author’s Note:
Virtual Private Networks
Name of the Student
Name of the University
Author’s Note:
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Executive Summary
The main aim of this report is to understand the basic concept of Virtual Private Network for the case
study of Starnet. A virtual private network or VPN is a network, which produces a secured and ciphered
connection over an unsafe network. An example of VPN is the internet. VPN is developed to enable all
the branch offices and the remote users to access all applications and resources securely. Starnet is an
organization, which has two sites located in Sydney and Melbourne. The sites are named as Site A and
Site B. These two sites require to communicate amongst each other and to exchange data securely. The
report briefly describes about the implemented VPN in Starnet and how VPN has helped Starnet in their
business.
The main aim of this report is to understand the basic concept of Virtual Private Network for the case
study of Starnet. A virtual private network or VPN is a network, which produces a secured and ciphered
connection over an unsafe network. An example of VPN is the internet. VPN is developed to enable all
the branch offices and the remote users to access all applications and resources securely. Starnet is an
organization, which has two sites located in Sydney and Melbourne. The sites are named as Site A and
Site B. These two sites require to communicate amongst each other and to exchange data securely. The
report briefly describes about the implemented VPN in Starnet and how VPN has helped Starnet in their
business.
Table of Contents
Introduction.................................................................................................................................................3
Discussion....................................................................................................................................................3
1. Internal Private IP Interface and External Public IP Interface..............................................................3
2. Type of VPN Implemented...................................................................................................................4
3. Site to Site and Remote Access VPN Difference...................................................................................6
4. Security Features of VPN.....................................................................................................................7
5. Protocols of IPSec................................................................................................................................8
6. Advantages and Disadvantages of VPN...............................................................................................8
Conclusion.................................................................................................................................................10
References.................................................................................................................................................11
Introduction.................................................................................................................................................3
Discussion....................................................................................................................................................3
1. Internal Private IP Interface and External Public IP Interface..............................................................3
2. Type of VPN Implemented...................................................................................................................4
3. Site to Site and Remote Access VPN Difference...................................................................................6
4. Security Features of VPN.....................................................................................................................7
5. Protocols of IPSec................................................................................................................................8
6. Advantages and Disadvantages of VPN...............................................................................................8
Conclusion.................................................................................................................................................10
References.................................................................................................................................................11
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
Introduction
Virtual Private Network or VPN is the type of private network, expanded over public network
that allows users to receive and send information and data over public network just like the computing
systems are directly associated to the private network. The main benefits of VPN that the application
obtains are the management, security and the functionality of private network [1]. Virtual Private
Networks even enable the staffs to access the office internet even when they are outside the office.
Starnet is an organization with two distinct sites, situated in Sydney and Melbourne. These two sites
require interfacing amongst each other and interchanging data safely. VPN is the solution for their
problem. There are various ways or several types of VPN to link the two sites for example IPsec.
The report outlines a brief description about the Virtual Private Network implemented in
Starnet. A table showing all the interfaces at each site is given here. The interfaces include Internal
private IP interface and External public IP interface [6]. The report also describes what type of VPN is
recommended for Starnet and the differences between Site to Site and Remote Access VPN. The benefit
or advantages of both the VPNs are mentioned here. The report further clarifies the security features
provided by VPN to protect and secure the data and the advantages and disadvantages of Virtual Private
Network.
Discussion
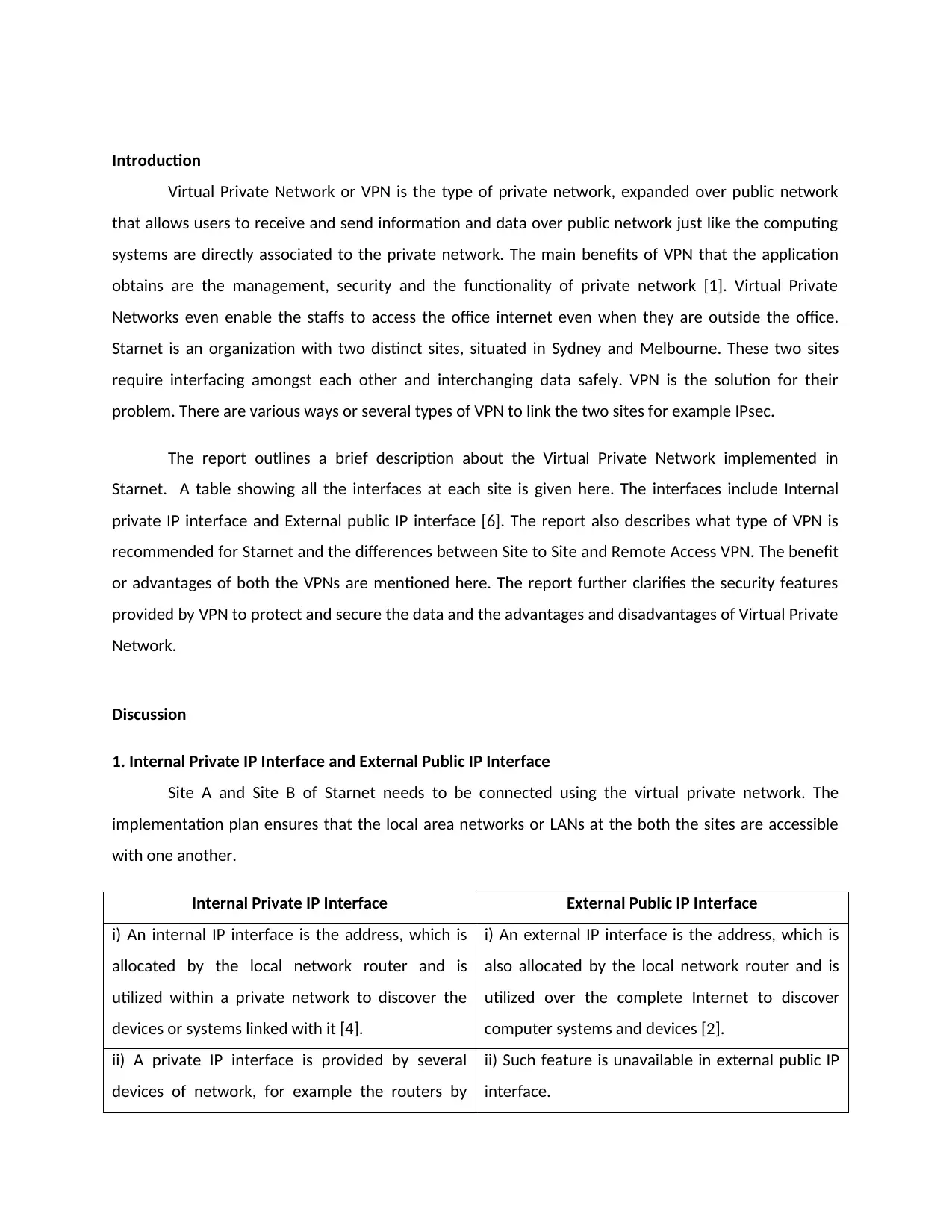
1. Internal Private IP Interface and External Public IP Interface
Site A and Site B of Starnet needs to be connected using the virtual private network. The
implementation plan ensures that the local area networks or LANs at the both the sites are accessible
with one another.
Internal Private IP Interface External Public IP Interface
i) An internal IP interface is the address, which is
allocated by the local network router and is
utilized within a private network to discover the
devices or systems linked with it [4].
i) An external IP interface is the address, which is
also allocated by the local network router and is
utilized over the complete Internet to discover
computer systems and devices [2].
ii) A private IP interface is provided by several
devices of network, for example the routers by
ii) Such feature is unavailable in external public IP
interface.
Virtual Private Network or VPN is the type of private network, expanded over public network
that allows users to receive and send information and data over public network just like the computing
systems are directly associated to the private network. The main benefits of VPN that the application
obtains are the management, security and the functionality of private network [1]. Virtual Private
Networks even enable the staffs to access the office internet even when they are outside the office.
Starnet is an organization with two distinct sites, situated in Sydney and Melbourne. These two sites
require interfacing amongst each other and interchanging data safely. VPN is the solution for their
problem. There are various ways or several types of VPN to link the two sites for example IPsec.
The report outlines a brief description about the Virtual Private Network implemented in
Starnet. A table showing all the interfaces at each site is given here. The interfaces include Internal
private IP interface and External public IP interface [6]. The report also describes what type of VPN is
recommended for Starnet and the differences between Site to Site and Remote Access VPN. The benefit
or advantages of both the VPNs are mentioned here. The report further clarifies the security features
provided by VPN to protect and secure the data and the advantages and disadvantages of Virtual Private
Network.
Discussion
1. Internal Private IP Interface and External Public IP Interface
Site A and Site B of Starnet needs to be connected using the virtual private network. The
implementation plan ensures that the local area networks or LANs at the both the sites are accessible
with one another.
Internal Private IP Interface External Public IP Interface
i) An internal IP interface is the address, which is
allocated by the local network router and is
utilized within a private network to discover the
devices or systems linked with it [4].
i) An external IP interface is the address, which is
also allocated by the local network router and is
utilized over the complete Internet to discover
computer systems and devices [2].
ii) A private IP interface is provided by several
devices of network, for example the routers by
ii) Such feature is unavailable in external public IP
interface.
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
utilizing Network Address Translation or NAT
iii) These types of IP interfaces cannot be
contacted directly over the network.
iii) Public IP interfaces can be contacted over the
network [7].
iv) The main advantage of this interface is that it
has the ability to switch servers quickly [13].
iv) The main advantage of external public IP
interface is that it can be connected to the system
from any machine anywhere.
v) Another advantage of this IP interface is its
security. It is extremely secured.
v) External IP interface is not as safe as the internal
IP interface [16].
vi) Private interfaces do not lose internet
connectivity [18].
vi) External public interfaces has the tendency to
lose internet connectivity very often.
The above differences describe the differences between the Internal private IP interface and
External public IP interface. For the case study of Starnet, two suitable IP addresses are assumed as A
and B. the routers are R1 and R2.
2. Type of VPN Implemented
There are several types of Virtual Private Network or VPN. The basic types of VPN are as follows:
i) Remote Access VPN: This connection enables an individual to link from an unlikely situation to
a private organization network with the help of a desktop computer or laptop that are connected to the
Internet [2].
ii) Site to Site VPN: This is the kind of Virtual Private Network, which is generated between the
two different locations [7]. Site to site VPN helps to link two completely discrete geographical networks
or locations.
iii) Internet Protocol Security or IPSec: This is a set of protocols, which gives security to the
internet protocol [19]. It normally utilizes cryptography to obtain security.
iv) Layer 2 Tunneling Protocol or L2TP: It is a tunneling protocol, utilized to reinforce the Virtual
Private Networks [11]. The main disadvantage of this protocol is that it does not give any security by
itself.
iii) These types of IP interfaces cannot be
contacted directly over the network.
iii) Public IP interfaces can be contacted over the
network [7].
iv) The main advantage of this interface is that it
has the ability to switch servers quickly [13].
iv) The main advantage of external public IP
interface is that it can be connected to the system
from any machine anywhere.
v) Another advantage of this IP interface is its
security. It is extremely secured.
v) External IP interface is not as safe as the internal
IP interface [16].
vi) Private interfaces do not lose internet
connectivity [18].
vi) External public interfaces has the tendency to
lose internet connectivity very often.
The above differences describe the differences between the Internal private IP interface and
External public IP interface. For the case study of Starnet, two suitable IP addresses are assumed as A
and B. the routers are R1 and R2.
2. Type of VPN Implemented
There are several types of Virtual Private Network or VPN. The basic types of VPN are as follows:
i) Remote Access VPN: This connection enables an individual to link from an unlikely situation to
a private organization network with the help of a desktop computer or laptop that are connected to the
Internet [2].
ii) Site to Site VPN: This is the kind of Virtual Private Network, which is generated between the
two different locations [7]. Site to site VPN helps to link two completely discrete geographical networks
or locations.
iii) Internet Protocol Security or IPSec: This is a set of protocols, which gives security to the
internet protocol [19]. It normally utilizes cryptography to obtain security.
iv) Layer 2 Tunneling Protocol or L2TP: It is a tunneling protocol, utilized to reinforce the Virtual
Private Networks [11]. The main disadvantage of this protocol is that it does not give any security by
itself.
v) Point to Point Tunneling Protocol or PPTP: It is an obsolete method for the implantation of
VPNs [10]. It utilizes a channel of control of TCP to encrypt the point-to-point packets.
vi) Secure Sockets Layer or SSL: This is a type of VPN that is utilized with the help of a norm Web
browser [1]. The main advantage of this secure sockets layer is that it never requires any kind of
installation of the exclusive client software on the computer of the end user.
vii) Transport Layer Security or TLS: The successor of SSL is known as the Transport Layer
Security protocol or the TLS.
viii) Open VPN: This is the open source software application, which executes the virtual private
network techniques for generating the secured site-to-site or point-to-point connections in bridged
configurations [20].
ix) Secure Shell or SSH: It is ciphered network protocol used for functioning the services of
network safely over the unsafe network.
The type of virtual private network implemented in Starnet is the Internet Protocol Security
VPN. IPSec is a protocol suite of network, which validates and ciphers the data packets sent over the
network [9]. It includes protocols for initiating mutual authentication within the agents at the starting of
the session and negotiating the cryptographic keys to utilize within the session. Starnet would get the
advantages of IPSec. The benefits of Internet Protocol Security are as follows:
a) Origin of Data Authentication: This feature helps to identify who has sent the data to whom
and thus hacking can be mitigated [8].
b) Encryption: This characteristic ensures that data is not read during the time of sending or
within the route.
c) Connectionless Integrity: This feature ensures that data is not altered during the time of
sending or within the route [12].
d) Protection: IPSec helps to detect the packets and to protect them against the attacks of DoS
or denial of service [19].
IPSec should be selected, as it is the most secured virtual private network. It is implemented in a
router or firewall and it gives high security, whose application is to cross the perimeter. IPSec comes
VPNs [10]. It utilizes a channel of control of TCP to encrypt the point-to-point packets.
vi) Secure Sockets Layer or SSL: This is a type of VPN that is utilized with the help of a norm Web
browser [1]. The main advantage of this secure sockets layer is that it never requires any kind of
installation of the exclusive client software on the computer of the end user.
vii) Transport Layer Security or TLS: The successor of SSL is known as the Transport Layer
Security protocol or the TLS.
viii) Open VPN: This is the open source software application, which executes the virtual private
network techniques for generating the secured site-to-site or point-to-point connections in bridged
configurations [20].
ix) Secure Shell or SSH: It is ciphered network protocol used for functioning the services of
network safely over the unsafe network.
The type of virtual private network implemented in Starnet is the Internet Protocol Security
VPN. IPSec is a protocol suite of network, which validates and ciphers the data packets sent over the
network [9]. It includes protocols for initiating mutual authentication within the agents at the starting of
the session and negotiating the cryptographic keys to utilize within the session. Starnet would get the
advantages of IPSec. The benefits of Internet Protocol Security are as follows:
a) Origin of Data Authentication: This feature helps to identify who has sent the data to whom
and thus hacking can be mitigated [8].
b) Encryption: This characteristic ensures that data is not read during the time of sending or
within the route.
c) Connectionless Integrity: This feature ensures that data is not altered during the time of
sending or within the route [12].
d) Protection: IPSec helps to detect the packets and to protect them against the attacks of DoS
or denial of service [19].
IPSec should be selected, as it is the most secured virtual private network. It is implemented in a
router or firewall and it gives high security, whose application is to cross the perimeter. IPSec comes
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
under the transport layer and the translucent applications [2]. The main advantage of this protocol is its
high security. The applications of Starnet will be extremely secured with the help of this protocol.
3. Site to Site and Remote Access VPN Difference
Site to site and Remote Access Virtual Private Networks are the two best types of VPNs.
However, they differ a lot in their applications and networking. A site-to-site virtual private network
enables organizations located in various fixed locations to reinforce safe connections amongst each
other over the public network [3]. An example of site-to-site VPN is the internet. It extends the network
of the organization so that the employees get the network from other locations as well. There are
mainly two types of site-to-site VPNS. They are as follows:
a) Extranet: When a particular company is related to another company like the supplier, partner
or customer, it builds an extranet VPN, which can connect to the LANs of those companies [13]. The
advantage of this extranet is that it enables all the organizations to do the job in a shared and safe
network by preventing any kind of utilization to the different intranets.
b) Intranet: When an organization has more than one remote location that is needed to connect
in one private network, the organization constructs an intranet VPN to attach every different LAN to one
WAN.
A remote access VPN enables all users to reinforce safe connections with the help of a network
of remote computer. These users usually access the network to obtain secured resources just like the
networks are directly connected to the servers of the network. There are two elements requires for a
remote access VPN [14]. The first component is a network access server or NAS. This is also known as
the media gateway or a remote access server or RAS. A NAS is a committed server and it can be claimed
as one of the multiple software applications that are running on the shared server. A NAS is something
that links the Internet with a user to give authenticated credentials to register in to the virtual private
network. To validate the credentials of the user, the network access server utilizes its own process of
authentication or a different server of authentication running on the network [17]. The other element
of VPN is the client software. The staffs, who wish to utilize the virtual private network from their own
systems need software on the systems, which can reinforce and maintain a link with the VPN. Most of
the operating systems have software automatically installed in them which links to remote access VPNs,
since some of the VPNs may need users to establish a distinct application. This second element sets a
tunneled linkage to the NAS that the end user demonstrates by the internet address [5]. This client
high security. The applications of Starnet will be extremely secured with the help of this protocol.
3. Site to Site and Remote Access VPN Difference
Site to site and Remote Access Virtual Private Networks are the two best types of VPNs.
However, they differ a lot in their applications and networking. A site-to-site virtual private network
enables organizations located in various fixed locations to reinforce safe connections amongst each
other over the public network [3]. An example of site-to-site VPN is the internet. It extends the network
of the organization so that the employees get the network from other locations as well. There are
mainly two types of site-to-site VPNS. They are as follows:
a) Extranet: When a particular company is related to another company like the supplier, partner
or customer, it builds an extranet VPN, which can connect to the LANs of those companies [13]. The
advantage of this extranet is that it enables all the organizations to do the job in a shared and safe
network by preventing any kind of utilization to the different intranets.
b) Intranet: When an organization has more than one remote location that is needed to connect
in one private network, the organization constructs an intranet VPN to attach every different LAN to one
WAN.
A remote access VPN enables all users to reinforce safe connections with the help of a network
of remote computer. These users usually access the network to obtain secured resources just like the
networks are directly connected to the servers of the network. There are two elements requires for a
remote access VPN [14]. The first component is a network access server or NAS. This is also known as
the media gateway or a remote access server or RAS. A NAS is a committed server and it can be claimed
as one of the multiple software applications that are running on the shared server. A NAS is something
that links the Internet with a user to give authenticated credentials to register in to the virtual private
network. To validate the credentials of the user, the network access server utilizes its own process of
authentication or a different server of authentication running on the network [17]. The other element
of VPN is the client software. The staffs, who wish to utilize the virtual private network from their own
systems need software on the systems, which can reinforce and maintain a link with the VPN. Most of
the operating systems have software automatically installed in them which links to remote access VPNs,
since some of the VPNs may need users to establish a distinct application. This second element sets a
tunneled linkage to the NAS that the end user demonstrates by the internet address [5]. This client
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
software further controls the encryption to secure the connection. The main difference between site-to-
site and remote access VPNs is that site to site VPN is server-to-server connection, whereas remote
access VPN is a client to server. The site-to-site VPN is an ASA to ASA connection but remote access VPN
example is PC to ASA [11]. Another difference is that in site-to-site the keys and networks should match
for the link to reinforce. However, in remote access VPN, the server validates the client and informs the
client which is the route towards tunnels and which one are not.
The advantages of site-to-site VPN are as follows:
a) High Security: It permits high security
b) Managed Service: It can be installed by a particular enterprise or can be offered as the
managed service.
c) Enables network in Multi locations: It enables network in multiple locations at a single time
even after locating outside the internet premises [12].
The main advantages of remote access VPN are as follows:
a) The moment a firewall is acquired, it involves many licenses for the remote access VPN
connections [4].
b) It is extremely cost effective.
c) An established and recognized technology and at the same time is extremely simple.
4. Security Features of VPN
A virtual private network is a private network that is utilized to access the network virtually over
the public network [14]. It has several features. The characteristics of VPN are as follows:
i) VPN filters the traffic in network and it helps to understand which traffic should be allowed.
ii) VPN configures the traffic filters. Configuration is extremely important for any network.
iii) VPN keeps the systems connected [20].
iv) VPN helps in strong encryption.
v) VPN helps to forward the secrecy.
site and remote access VPNs is that site to site VPN is server-to-server connection, whereas remote
access VPN is a client to server. The site-to-site VPN is an ASA to ASA connection but remote access VPN
example is PC to ASA [11]. Another difference is that in site-to-site the keys and networks should match
for the link to reinforce. However, in remote access VPN, the server validates the client and informs the
client which is the route towards tunnels and which one are not.
The advantages of site-to-site VPN are as follows:
a) High Security: It permits high security
b) Managed Service: It can be installed by a particular enterprise or can be offered as the
managed service.
c) Enables network in Multi locations: It enables network in multiple locations at a single time
even after locating outside the internet premises [12].
The main advantages of remote access VPN are as follows:
a) The moment a firewall is acquired, it involves many licenses for the remote access VPN
connections [4].
b) It is extremely cost effective.
c) An established and recognized technology and at the same time is extremely simple.
4. Security Features of VPN
A virtual private network is a private network that is utilized to access the network virtually over
the public network [14]. It has several features. The characteristics of VPN are as follows:
i) VPN filters the traffic in network and it helps to understand which traffic should be allowed.
ii) VPN configures the traffic filters. Configuration is extremely important for any network.
iii) VPN keeps the systems connected [20].
iv) VPN helps in strong encryption.
v) VPN helps to forward the secrecy.
vi) VPN helps to secure the protocols strongly.
The above mentioned statements clearly describe the security features of virtual private
network.
5. Protocols of IPSec
IPSec is a protocol suite of network, which validates and ciphers the data packets sent over the
network. It includes protocols for initiating mutual authentication within the agents at the starting of the
session and negotiating the cryptographic keys to utilize within the session [13]. IPSec protects the flow
of data within the pair of hosts that means the host-to-host between the host and the security gateway
that means the network to host. It utilizes various cryptographic security services to secure the
communications over the networks of Internet Protocols. IPSec reinforces the replay protection, data
integrity. It also helps in data origin authentication, network level peer authentication, and data
confidentiality (encryption). It is an end-to-end scheme of security that is operating in the Internet Layer
of the Internet Protocol Suite, whereas some of the other security systems of internet are also in use,
such as the Secure Shell or SSH and Transport Layer Security (TLS) [7]. These function in the top layers at
the Application Layer or SSH and the Transport Layer or TLS. IPSec can secure the applications in the
Internet Protocol layer automatically.
The three protocols used in the case of IPSec are as follows:
a) Authentication Header: The Authentication Header or AH is a component of the protocol
suite of Internet Protocol Security [5]. This Authentication Header guarantees the data origin
authentication and connectionless integrity of all the IP packets.
b) Encapsulating Security: The Encapsulation Security Payload or ESP gives confidentiality,
integrity and authentication that protect against the data tampering and provide protection to the
content of the message [16]. It even gives a framework for the implementation of standard algorithms
like the SHA and MD5.
c) Internet Key Exchange: the Internet Key Exchange is a protocol in the IPSec protocol suite
that is utilized to put up a SA or security association. Internet Key Exchange constructs on the ISAKMP
and the protocol of Oakley [6].
The above mentioned statements clearly describe the security features of virtual private
network.
5. Protocols of IPSec
IPSec is a protocol suite of network, which validates and ciphers the data packets sent over the
network. It includes protocols for initiating mutual authentication within the agents at the starting of the
session and negotiating the cryptographic keys to utilize within the session [13]. IPSec protects the flow
of data within the pair of hosts that means the host-to-host between the host and the security gateway
that means the network to host. It utilizes various cryptographic security services to secure the
communications over the networks of Internet Protocols. IPSec reinforces the replay protection, data
integrity. It also helps in data origin authentication, network level peer authentication, and data
confidentiality (encryption). It is an end-to-end scheme of security that is operating in the Internet Layer
of the Internet Protocol Suite, whereas some of the other security systems of internet are also in use,
such as the Secure Shell or SSH and Transport Layer Security (TLS) [7]. These function in the top layers at
the Application Layer or SSH and the Transport Layer or TLS. IPSec can secure the applications in the
Internet Protocol layer automatically.
The three protocols used in the case of IPSec are as follows:
a) Authentication Header: The Authentication Header or AH is a component of the protocol
suite of Internet Protocol Security [5]. This Authentication Header guarantees the data origin
authentication and connectionless integrity of all the IP packets.
b) Encapsulating Security: The Encapsulation Security Payload or ESP gives confidentiality,
integrity and authentication that protect against the data tampering and provide protection to the
content of the message [16]. It even gives a framework for the implementation of standard algorithms
like the SHA and MD5.
c) Internet Key Exchange: the Internet Key Exchange is a protocol in the IPSec protocol suite
that is utilized to put up a SA or security association. Internet Key Exchange constructs on the ISAKMP
and the protocol of Oakley [6].
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
6. Advantages and Disadvantages of VPN
A VPN or Virtual Private Network is a private network over the public network and allows the
users to receive and send data over the public and shared networks as if their systems are directly linked
to the private network [14]. The main benefits that the applications get from VPN are the security,
management and functionality of the private network. VPN even enables the staffs of an organization to
access the intranet safely even when they are present outside the office [1]. There are various
advantages and disadvantages of VPN. The advantages of VPN are as follows:
i) With the help of a VPN, the users are able to access a network or a computer system from any
place, which has any type of internet connection.
ii) VPN is extremely secured and it provides high security to the network [18].
iii) VPN is extremely cost effective and it makes it very popular for all organizations.
iv) VPN has the advantage to work within the public network such as a private network or a WiFi
hotspot.
v) VPN is extremely flexible and scalable.
vi) It can open the blocked sites and can encapsulate the IP address with the replacement of
public IP VPN [12].
vii) It uses cryptography and thus can be claimed as secured.
In spite of having so many advantages, VPN do have various disadvantages. The disadvantages
of VPN are as follows:
i) Data sometimes get lost during the journey.
ii) VPN needs extra attention to set up the security system completely to mitigate the cyber
crime acts [3].
iii) Public access is prohibited in virtual private network.
iv) Most of the connections are long distanced in VPN.
v) Sharing of files sometimes creates problem for VPN [6].
A VPN or Virtual Private Network is a private network over the public network and allows the
users to receive and send data over the public and shared networks as if their systems are directly linked
to the private network [14]. The main benefits that the applications get from VPN are the security,
management and functionality of the private network. VPN even enables the staffs of an organization to
access the intranet safely even when they are present outside the office [1]. There are various
advantages and disadvantages of VPN. The advantages of VPN are as follows:
i) With the help of a VPN, the users are able to access a network or a computer system from any
place, which has any type of internet connection.
ii) VPN is extremely secured and it provides high security to the network [18].
iii) VPN is extremely cost effective and it makes it very popular for all organizations.
iv) VPN has the advantage to work within the public network such as a private network or a WiFi
hotspot.
v) VPN is extremely flexible and scalable.
vi) It can open the blocked sites and can encapsulate the IP address with the replacement of
public IP VPN [12].
vii) It uses cryptography and thus can be claimed as secured.
In spite of having so many advantages, VPN do have various disadvantages. The disadvantages
of VPN are as follows:
i) Data sometimes get lost during the journey.
ii) VPN needs extra attention to set up the security system completely to mitigate the cyber
crime acts [3].
iii) Public access is prohibited in virtual private network.
iv) Most of the connections are long distanced in VPN.
v) Sharing of files sometimes creates problem for VPN [6].
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
These are the advantages and the disadvantages of Virtual Private Network.
Conclusion
Therefore, from the above discussion it can be concluded that, Virtual Private Network is a
secured network that provides a highly secured virtual network. The above report clearly describes the
difference between the interfaces and what type of virtual private network should be implemented for
the case study of Starnet. The report also explains the differences between the Site to Site VPN and the
Remote Access VPN and also the advantages of both of them. The security features of VPN are also
explained in this report. The report also covers the three important protocols of IPSec and also the
advantages and disadvantages of VPN to the network.
Conclusion
Therefore, from the above discussion it can be concluded that, Virtual Private Network is a
secured network that provides a highly secured virtual network. The above report clearly describes the
difference between the interfaces and what type of virtual private network should be implemented for
the case study of Starnet. The report also explains the differences between the Site to Site VPN and the
Remote Access VPN and also the advantages of both of them. The security features of VPN are also
explained in this report. The report also covers the three important protocols of IPSec and also the
advantages and disadvantages of VPN to the network.
References
[1]L. Qu, X. Cui and X. Liu, "IPv6 in IPv4 Virtual Private Network Based on Virtual Devices in Vehicle
Information System", Applied Mechanics and Materials, vol. 321-324, pp. 2910-2913, 2013.
[2]F. Gharehchopogh, R. Aliverdiloo and V. Banayi, "A New Communication Platform for Data
Transmission in Virtual Private Network", International Journal of Mobile Network Communications &
Telematics, vol. 3, no. 2, pp. 1-9, 2013.
[3]M. Liyanage and A. Gurtov, "Securing virtual private LAN service by efficient key
management", Security and Communication Networks, vol. 7, no. 1, pp. 1-13, 2013.
[4]M. Sathyan.K, "Security Enhancement of Firewall Policies in Virtual Private Network", IOSR Journal of
Engineering, vol. 02, no. 02, pp. 197-202, 2012.
[5]H. Lian and A. Faragó, "Optimizing Virtual Private Network Design Using a New Heuristic Optimization
Method", ISRN Communications and Networking, vol. 2012, pp. 1-9, 2012.
[6]F. Ibikunle, S. Oloja and E. Philip O., "Campus Network Virtualization using Multiprotocol Label
Switching Virtual Private Networks (MPLS-VPNs)", International Journal of Applied Information Systems,
vol. 5, no. 8, pp. 1-9, 2013.
[7]J. Guichard, MPLS and VPN architectures. Cisco Press, 2012.
[8]H. Hooper, CCNP security VPN 642-647 official cert guide. Indianapolis, Ind.: Cisco Press, 2012.
[9]K. Grewal and R. Dangi, "Comparative Analysis of QoS VPN Provisioning Algorithm on Traditional IP
based VPN and MPLS VPN using NS-2", International Journal of Computer Applications, vol. 48, no. 1, pp.
43-46, 2012.
[10]V. Perta, M. Barbera, G. Tyson, H. Haddadi and A. Mei, "A Glance through the VPN Looking Glass:
IPv6 Leakage and DNS Hijacking in Commercial VPN clients", Proceedings on Privacy Enhancing
Technologies, vol. 2015, no. 1, 2015.
[11]B. BĂNUȚĂ, "Security Technologies Implemented in MPLS VPN Networks", International Journal of
Information Security and Cybercrime, vol. 1, no. 2, pp. 9-16, 2012.
[1]L. Qu, X. Cui and X. Liu, "IPv6 in IPv4 Virtual Private Network Based on Virtual Devices in Vehicle
Information System", Applied Mechanics and Materials, vol. 321-324, pp. 2910-2913, 2013.
[2]F. Gharehchopogh, R. Aliverdiloo and V. Banayi, "A New Communication Platform for Data
Transmission in Virtual Private Network", International Journal of Mobile Network Communications &
Telematics, vol. 3, no. 2, pp. 1-9, 2013.
[3]M. Liyanage and A. Gurtov, "Securing virtual private LAN service by efficient key
management", Security and Communication Networks, vol. 7, no. 1, pp. 1-13, 2013.
[4]M. Sathyan.K, "Security Enhancement of Firewall Policies in Virtual Private Network", IOSR Journal of
Engineering, vol. 02, no. 02, pp. 197-202, 2012.
[5]H. Lian and A. Faragó, "Optimizing Virtual Private Network Design Using a New Heuristic Optimization
Method", ISRN Communications and Networking, vol. 2012, pp. 1-9, 2012.
[6]F. Ibikunle, S. Oloja and E. Philip O., "Campus Network Virtualization using Multiprotocol Label
Switching Virtual Private Networks (MPLS-VPNs)", International Journal of Applied Information Systems,
vol. 5, no. 8, pp. 1-9, 2013.
[7]J. Guichard, MPLS and VPN architectures. Cisco Press, 2012.
[8]H. Hooper, CCNP security VPN 642-647 official cert guide. Indianapolis, Ind.: Cisco Press, 2012.
[9]K. Grewal and R. Dangi, "Comparative Analysis of QoS VPN Provisioning Algorithm on Traditional IP
based VPN and MPLS VPN using NS-2", International Journal of Computer Applications, vol. 48, no. 1, pp.
43-46, 2012.
[10]V. Perta, M. Barbera, G. Tyson, H. Haddadi and A. Mei, "A Glance through the VPN Looking Glass:
IPv6 Leakage and DNS Hijacking in Commercial VPN clients", Proceedings on Privacy Enhancing
Technologies, vol. 2015, no. 1, 2015.
[11]B. BĂNUȚĂ, "Security Technologies Implemented in MPLS VPN Networks", International Journal of
Information Security and Cybercrime, vol. 1, no. 2, pp. 9-16, 2012.
⊘ This is a preview!⊘
Do you want full access?
Subscribe today to unlock all pages.

Trusted by 1+ million students worldwide
1 out of 13
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
Copyright © 2020–2026 A2Z Services. All Rights Reserved. Developed and managed by ZUCOL.




