Assessment :Firewall Setup & Configuration
Added on 2022-09-09
14 Pages1431 Words14 Views
Assessment 1:Firewall Setup & Configuration
Executive Summary
This project assesses the understanding of the firewall and design configuration. It also
helps to reduce the potential security risks for performing the network’s security testing, which is
used for determining threats and prepares a report on risk mitigation. The analysis is used for
securing a network, including the distributed application.
This project assesses the understanding of the firewall and design configuration. It also
helps to reduce the potential security risks for performing the network’s security testing, which is
used for determining threats and prepares a report on risk mitigation. The analysis is used for
securing a network, including the distributed application.
Table of Contents
1. Project Outline........................................................................................................................1
2. Part A.......................................................................................................................................1
2.1 Use Nmap.........................................................................................................................1
2.2 Description of Nmap.......................................................................................................3
2.3 Nmap Analysis.................................................................................................................4
2.4 Risk Mitigation Plan.......................................................................................................7
3. Part B.......................................................................................................................................8
3.1 Firewall Setup Configuration........................................................................................8
4. Conclusion.............................................................................................................................10
References.....................................................................................................................................11
1. Project Outline........................................................................................................................1
2. Part A.......................................................................................................................................1
2.1 Use Nmap.........................................................................................................................1
2.2 Description of Nmap.......................................................................................................3
2.3 Nmap Analysis.................................................................................................................4
2.4 Risk Mitigation Plan.......................................................................................................7
3. Part B.......................................................................................................................................8
3.1 Firewall Setup Configuration........................................................................................8
4. Conclusion.............................................................................................................................10
References.....................................................................................................................................11
1. Project Outline
This report intends on conducting network security test and also wish to evaluate the
understanding on firewall and design configuration, which are used to reduce the potential
security risks. The performance of the security testing is used to determine the threats and
prepares a risk mitigation report. The analysis is utilized for securing the network, including the
distributed applications. This project is divided into two parts, part A is used to perform the
security testing in Kali Linux that performs the Pen testing on a network by using the Nmap tool.
It prepares short risk mitigation plan for determining the threats of asset which are used for
proceeding the firewall setting essential for an organization. The part B is used to configure a
network firewall setting with the help of Kali Linux commands for achieving the required level
of security.
2. Part A
In this part, the Nmap tool is used to perform the penetration testing on Kali Linux which
is used to determine the threats and prepares the mitigation report.
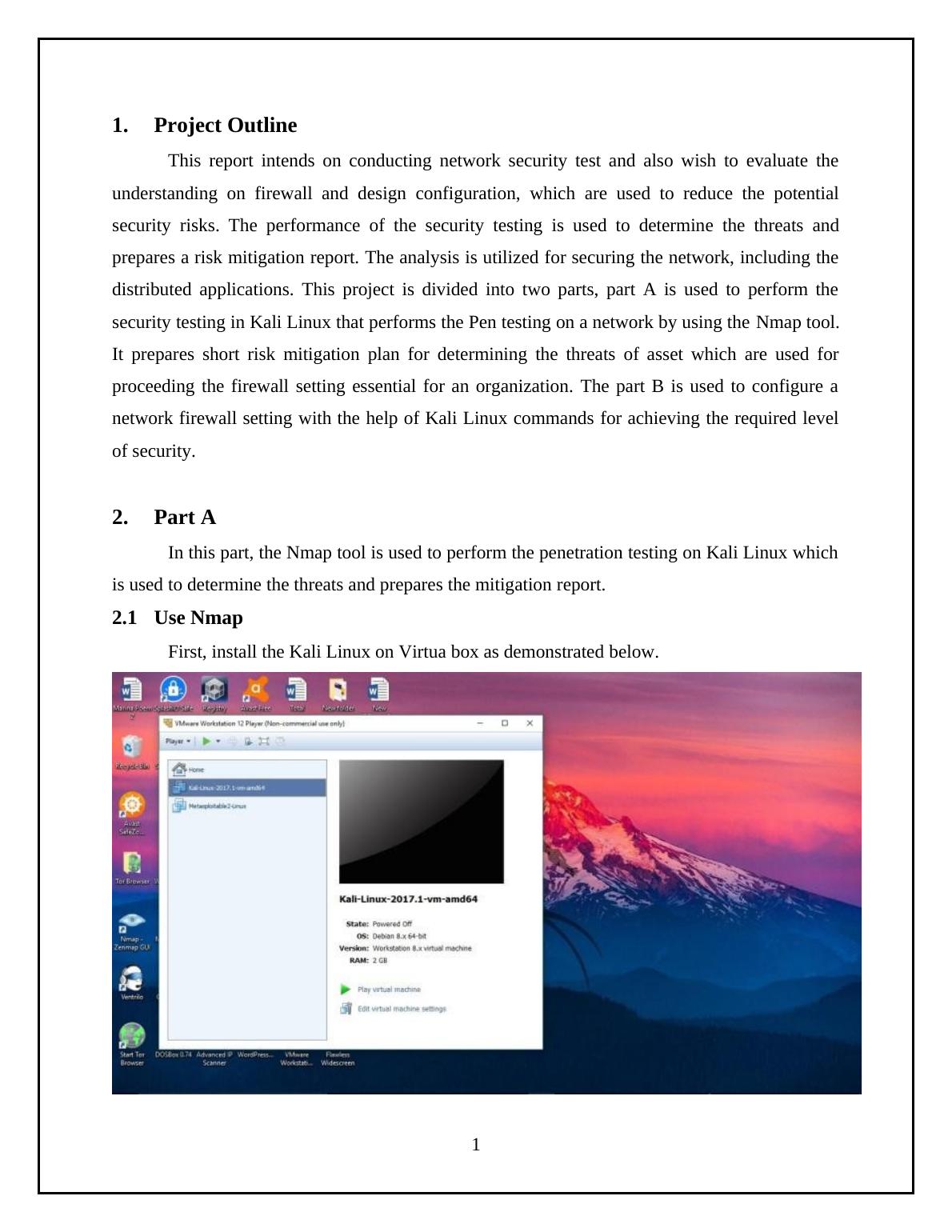
2.1 Use Nmap
First, install the Kali Linux on Virtua box as demonstrated below.
1
This report intends on conducting network security test and also wish to evaluate the
understanding on firewall and design configuration, which are used to reduce the potential
security risks. The performance of the security testing is used to determine the threats and
prepares a risk mitigation report. The analysis is utilized for securing the network, including the
distributed applications. This project is divided into two parts, part A is used to perform the
security testing in Kali Linux that performs the Pen testing on a network by using the Nmap tool.
It prepares short risk mitigation plan for determining the threats of asset which are used for
proceeding the firewall setting essential for an organization. The part B is used to configure a
network firewall setting with the help of Kali Linux commands for achieving the required level
of security.
2. Part A
In this part, the Nmap tool is used to perform the penetration testing on Kali Linux which
is used to determine the threats and prepares the mitigation report.
2.1 Use Nmap
First, install the Kali Linux on Virtua box as demonstrated below.
1
End of preview
Want to access all the pages? Upload your documents or become a member.
Related Documents
Penetration Testing on Linux Machine: Task 3lg...
|32
|3649
|332
Network Vulnerability And Cyber Securitylg...
|15
|1453
|15
Penetration Testing: Techniques and Toolslg...
|26
|2326
|63
Firewall Testing on Kali Linux using Nmaplg...
|18
|1810
|98
Firewall and Configuration Report 2022lg...
|22
|1741
|23
Security Assessment on a Firewalllg...
|11
|891
|145