Basic Project Information Definition
VerifiedAdded on 2022/08/15
|10
|1683
|12
AI Summary
Contribute Materials
Your contribution can guide someone’s learning journey. Share your
documents today.
CE 3.1 Information on the Project
Project Name: Implementation of an Intrusion Detection System or IDS with Canary
Tokens
Project’s Location: Please fill
Duration of the Project: Please fill
Organization’s Name: Please fill
Role as well as Designation in the project: Team Member of the project
CE 3.2 Background of the Project
CE 3.2.1 Basic Characteristics of the Project
An intrusion detection system or IDS can be referred to as a specific system, which
monitors the network traffic for any type of suspicious activity as well as issue for altering as
soon as any such activity is being discovered. IDS is the software application, which scans a
system or a network for any such policy breaching and harmful activity. It helps in
monitoring the network for identification of any type of malicious activity or policy violation.
In this project, I have successfully implemented an Intrusion Detection system for the IoT
enabled sensor networks. The growth of this Internet is evolving majorly for ensuring
effectiveness. An early warning system runs natively on the client side like canary token for
actively tracking each and every trace of the user, who is trying to login to the system and
then dumping the data within real time to the configured dumping methodologies like activity
log and email. One of the major reasons for selection of this specific project was to check for
the lack of security within IoT and since there are no cryptographic protocols present for this
Internet of Things technology. I have used canary tokens, so that we are able to gain update
Project Name: Implementation of an Intrusion Detection System or IDS with Canary
Tokens
Project’s Location: Please fill
Duration of the Project: Please fill
Organization’s Name: Please fill
Role as well as Designation in the project: Team Member of the project
CE 3.2 Background of the Project
CE 3.2.1 Basic Characteristics of the Project
An intrusion detection system or IDS can be referred to as a specific system, which
monitors the network traffic for any type of suspicious activity as well as issue for altering as
soon as any such activity is being discovered. IDS is the software application, which scans a
system or a network for any such policy breaching and harmful activity. It helps in
monitoring the network for identification of any type of malicious activity or policy violation.
In this project, I have successfully implemented an Intrusion Detection system for the IoT
enabled sensor networks. The growth of this Internet is evolving majorly for ensuring
effectiveness. An early warning system runs natively on the client side like canary token for
actively tracking each and every trace of the user, who is trying to login to the system and
then dumping the data within real time to the configured dumping methodologies like activity
log and email. One of the major reasons for selection of this specific project was to check for
the lack of security within IoT and since there are no cryptographic protocols present for this
Internet of Things technology. I have used canary tokens, so that we are able to gain update
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
for server breach. Therefore, with this particular project work, I had executed the work
successfully with canary tokens.
CE 3.2.2 Developed Objectives for this project
This work was being executed by me after proper understanding about various
specifications related to IoT technology and Raspberry Pi. For the purpose of reflecting the
real time working of the application, the canary is being implemented over the Raspberry Pi
that is utilized as the sensor monitoring as well as controlling system. The most significant
and vital objectives in this project work are:
To implement a successful and proper intrusion detection system or IDS, so that the
user is able to get early warning or update for any type of server breach.
To ensure that the proposed system in this work is similar to a specific real time
device of Internet of Things.
To deploy an early warning system that would run natively on the user or canary side
like canary token for actively tracking all the traces of the users, who are logging into
the system as well as dumping the data within real time to the configured dumping
methodologies like activity log and electronic mails.
To reflect the real time working of the application that the canary token in being
implemented over the Raspberry Pi for the purpose of a sensor monitoring and
controlling system.
To use Raspberry Pi as an IoT device with Cayenne IoT for controlling and
monitoring sensors as well as actuators through the Internet connection.
To use Python code for SMTP trigger of the canary tokens.
successfully with canary tokens.
CE 3.2.2 Developed Objectives for this project
This work was being executed by me after proper understanding about various
specifications related to IoT technology and Raspberry Pi. For the purpose of reflecting the
real time working of the application, the canary is being implemented over the Raspberry Pi
that is utilized as the sensor monitoring as well as controlling system. The most significant
and vital objectives in this project work are:
To implement a successful and proper intrusion detection system or IDS, so that the
user is able to get early warning or update for any type of server breach.
To ensure that the proposed system in this work is similar to a specific real time
device of Internet of Things.
To deploy an early warning system that would run natively on the user or canary side
like canary token for actively tracking all the traces of the users, who are logging into
the system as well as dumping the data within real time to the configured dumping
methodologies like activity log and electronic mails.
To reflect the real time working of the application that the canary token in being
implemented over the Raspberry Pi for the purpose of a sensor monitoring and
controlling system.
To use Raspberry Pi as an IoT device with Cayenne IoT for controlling and
monitoring sensors as well as actuators through the Internet connection.
To use Python code for SMTP trigger of the canary tokens.
CE 3.2.3 My working areas in this work
Since I was a successful student from a popular and significant university, it was
extremely easy for me to make this project work of intrusion detection system a successful
one. In the beginning, I chose a proper topic for the work. After selection of this project topic,
I decided to research about the aspects and parameters of Raspberry Pi for making the project
work a proper one, as this was the first time that I was using Raspberry Pi. Moreover, I have
worked with IoT devices in several projects and hence I had idea about the specifications of
such devices appropriately. Being an experienced part of the team, I guided the rest of the
members for successful execution.
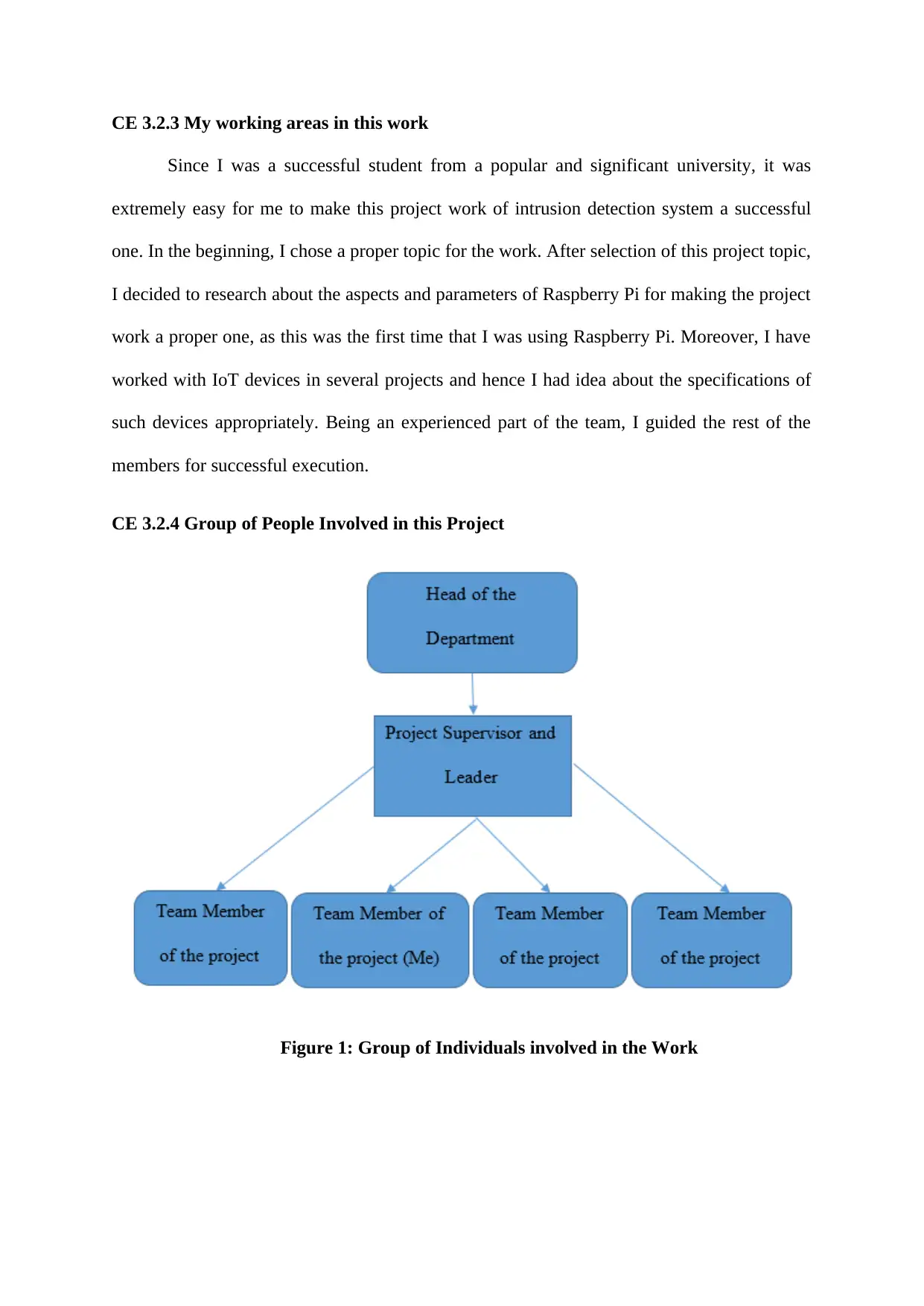
CE 3.2.4 Group of People Involved in this Project
Figure 1: Group of Individuals involved in the Work
Since I was a successful student from a popular and significant university, it was
extremely easy for me to make this project work of intrusion detection system a successful
one. In the beginning, I chose a proper topic for the work. After selection of this project topic,
I decided to research about the aspects and parameters of Raspberry Pi for making the project
work a proper one, as this was the first time that I was using Raspberry Pi. Moreover, I have
worked with IoT devices in several projects and hence I had idea about the specifications of
such devices appropriately. Being an experienced part of the team, I guided the rest of the
members for successful execution.
CE 3.2.4 Group of People Involved in this Project
Figure 1: Group of Individuals involved in the Work
CE 3.2.5 My main responsibilities as well as duties throughout the work
My designation in the specified work of Implementation of an Intrusion Detection
System or IDS with Canary Tokens was a responsible team member, who had the major duty
to execute this complete project work with three other team members and group leader. My
main responsibility was to design a proper intrusion detection system that could have the
capability of detecting any type of breach in the server and the user is able to gain proper
knowledge without any type of complexity. Although, there are several similar systems of
IoT, they lack cryptographic protocols. These IoT devices comprise of methods such as
utilization of modified hash algorithms, they eventually lack the native support of hardware
for encryption functions to be kept for IoT with limited choices. For avoiding such situations,
I have selected Canary Tokens on the client side, only to be warned about a breach in the
server. I even selected Raspberry Pi for controlling and monitoring sensors as well as
actuators through the Internet connection. Moreover, I also had to help my team member in
Python coding of the software.
CE 3.3 Distinct Activities in Work
CE 3.3.1 Comprehending the most Basic Theories Used within this Project
Theoretical understanding for different aspects and features of IoT and IDS were
being used by me in this work. For achieving the distinct objectives of the work, I have used
theories of intrusion detection system and canary tokens. I have understood that this type of
system would be extremely effective for the users and also reducing complexities related to
intrusion detection. For this purpose, I had to check the issues with the current technology of
IoT. There had been lack of security protocols in the current system and as a result, several
threats and issues have been highlighted for the users. I also understood that a canary token is
a specific production honeypot that is eventually utilized for security researches. It is being
My designation in the specified work of Implementation of an Intrusion Detection
System or IDS with Canary Tokens was a responsible team member, who had the major duty
to execute this complete project work with three other team members and group leader. My
main responsibility was to design a proper intrusion detection system that could have the
capability of detecting any type of breach in the server and the user is able to gain proper
knowledge without any type of complexity. Although, there are several similar systems of
IoT, they lack cryptographic protocols. These IoT devices comprise of methods such as
utilization of modified hash algorithms, they eventually lack the native support of hardware
for encryption functions to be kept for IoT with limited choices. For avoiding such situations,
I have selected Canary Tokens on the client side, only to be warned about a breach in the
server. I even selected Raspberry Pi for controlling and monitoring sensors as well as
actuators through the Internet connection. Moreover, I also had to help my team member in
Python coding of the software.
CE 3.3 Distinct Activities in Work
CE 3.3.1 Comprehending the most Basic Theories Used within this Project
Theoretical understanding for different aspects and features of IoT and IDS were
being used by me in this work. For achieving the distinct objectives of the work, I have used
theories of intrusion detection system and canary tokens. I have understood that this type of
system would be extremely effective for the users and also reducing complexities related to
intrusion detection. For this purpose, I had to check the issues with the current technology of
IoT. There had been lack of security protocols in the current system and as a result, several
threats and issues have been highlighted for the users. I also understood that a canary token is
a specific production honeypot that is eventually utilized for security researches. It is being
Secure Best Marks with AI Grader
Need help grading? Try our AI Grader for instant feedback on your assignments.
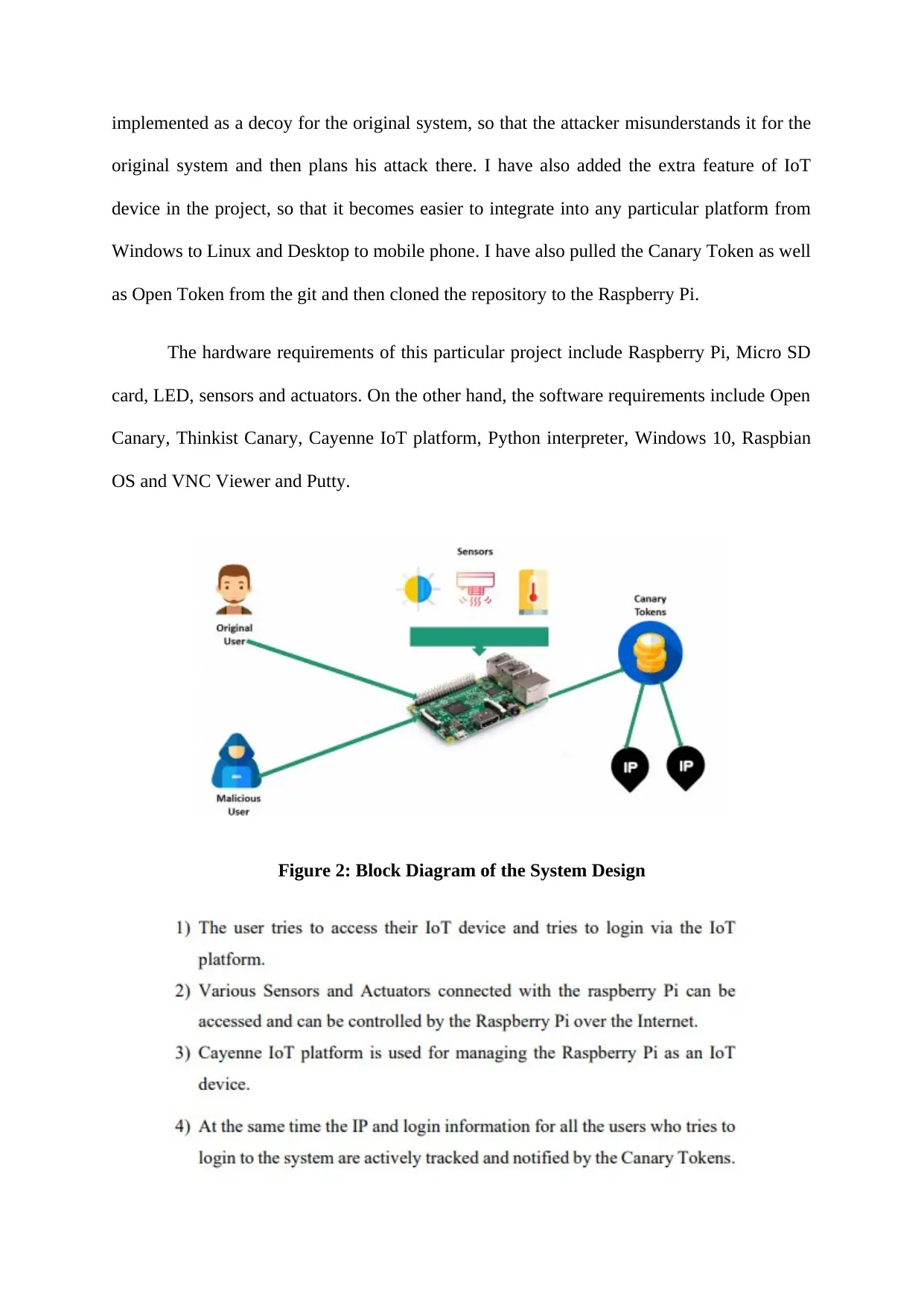
implemented as a decoy for the original system, so that the attacker misunderstands it for the
original system and then plans his attack there. I have also added the extra feature of IoT
device in the project, so that it becomes easier to integrate into any particular platform from
Windows to Linux and Desktop to mobile phone. I have also pulled the Canary Token as well
as Open Token from the git and then cloned the repository to the Raspberry Pi.
The hardware requirements of this particular project include Raspberry Pi, Micro SD
card, LED, sensors and actuators. On the other hand, the software requirements include Open
Canary, Thinkist Canary, Cayenne IoT platform, Python interpreter, Windows 10, Raspbian
OS and VNC Viewer and Putty.
Figure 2: Block Diagram of the System Design
original system and then plans his attack there. I have also added the extra feature of IoT
device in the project, so that it becomes easier to integrate into any particular platform from
Windows to Linux and Desktop to mobile phone. I have also pulled the Canary Token as well
as Open Token from the git and then cloned the repository to the Raspberry Pi.
The hardware requirements of this particular project include Raspberry Pi, Micro SD
card, LED, sensors and actuators. On the other hand, the software requirements include Open
Canary, Thinkist Canary, Cayenne IoT platform, Python interpreter, Windows 10, Raspbian
OS and VNC Viewer and Putty.
Figure 2: Block Diagram of the System Design
The Raspberry Pi comprises of some of the most significant specifications:
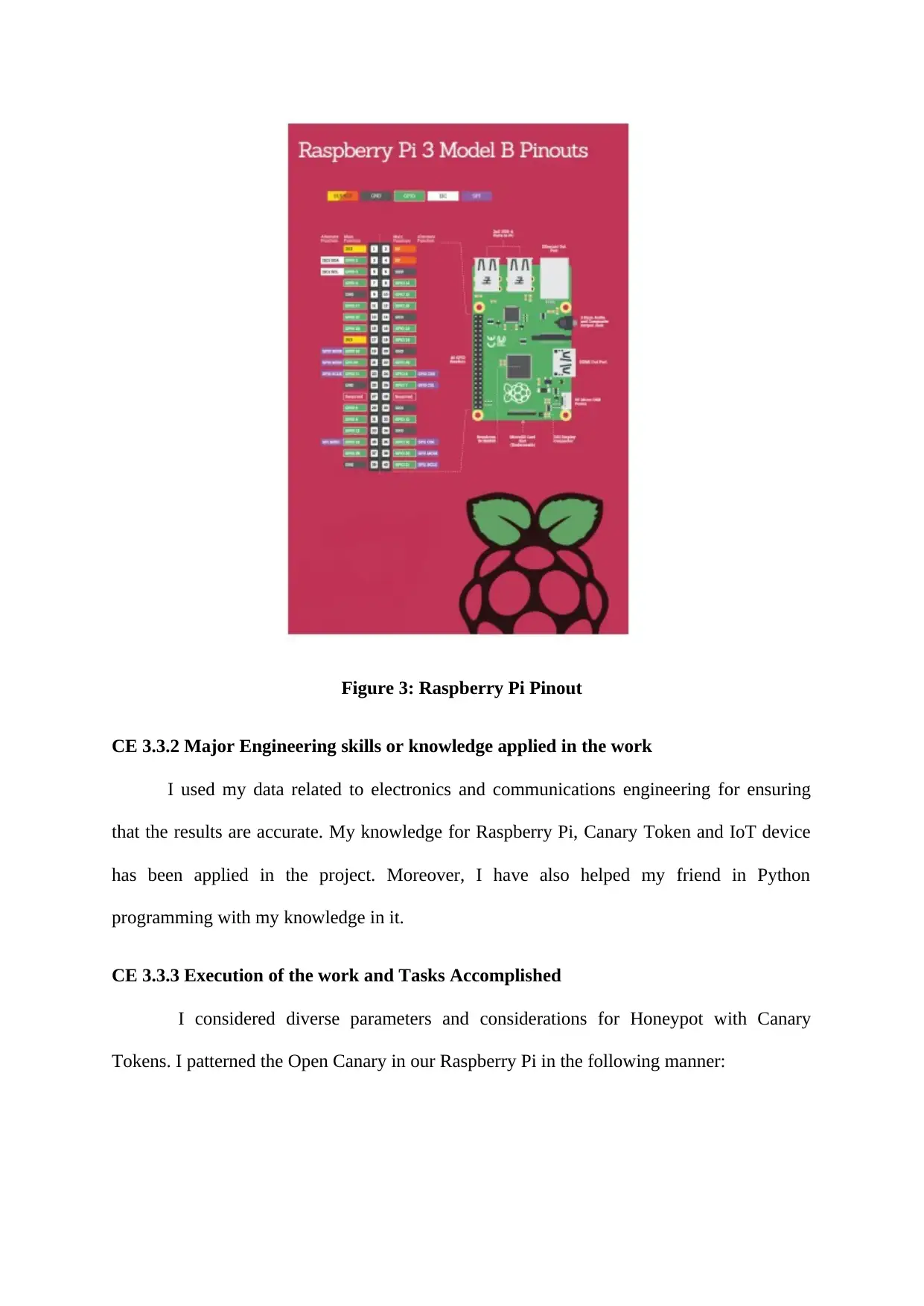
Figure 3: Raspberry Pi Pinout
CE 3.3.2 Major Engineering skills or knowledge applied in the work
I used my data related to electronics and communications engineering for ensuring
that the results are accurate. My knowledge for Raspberry Pi, Canary Token and IoT device
has been applied in the project. Moreover, I have also helped my friend in Python
programming with my knowledge in it.
CE 3.3.3 Execution of the work and Tasks Accomplished
I considered diverse parameters and considerations for Honeypot with Canary
Tokens. I patterned the Open Canary in our Raspberry Pi in the following manner:
CE 3.3.2 Major Engineering skills or knowledge applied in the work
I used my data related to electronics and communications engineering for ensuring
that the results are accurate. My knowledge for Raspberry Pi, Canary Token and IoT device
has been applied in the project. Moreover, I have also helped my friend in Python
programming with my knowledge in it.
CE 3.3.3 Execution of the work and Tasks Accomplished
I considered diverse parameters and considerations for Honeypot with Canary
Tokens. I patterned the Open Canary in our Raspberry Pi in the following manner:
Paraphrase This Document
Need a fresh take? Get an instant paraphrase of this document with our AI Paraphraser
Although, Python programming was not in my part of work, I have helped my friend
to complete it for Raspberry Pi and Cayenne Setup.
CE 3.3.4 Identified issue with its solution
3.3.4.1 Issue faced in this work
I faced an issue while setting the camera with the Raspberry Pi. I followed a proper
procedure for setting this camera. However, I was unable to do it properly. As a result, the
connection was not being set properly and the project got delayed.
to complete it for Raspberry Pi and Cayenne Setup.
CE 3.3.4 Identified issue with its solution
3.3.4.1 Issue faced in this work
I faced an issue while setting the camera with the Raspberry Pi. I followed a proper
procedure for setting this camera. However, I was unable to do it properly. As a result, the
connection was not being set properly and the project got delayed.
3.3.4.2 Solution to the identified Technical Difficulty
I decided to check the process once and finally, I was able to identify the issue. I had
to update the SD card in the beginning and then for using the camera, I checked that I have to
use a recent OS for making the camera existing. The most significant way for this purpose is
to obtain the last Raspbian image from the RaspberryPi.org website as well as make a fresh
SD card.
CE 3.3.5 Plan made to give innovative as well as creative works
I took the decision to research properly about Raspberry Pi and Cayenne Setup. Since,
the tasks were segregated amongst all the team members equally, the entire process did not
take up longer time period.
CE 3.3.6 Work Collaborations
I completed the work after collaborating with the group leader and three other
members. For ensuring collaboration, our group leader had arranged project meetings every
week.
CE 3.4 Overall Reviewing of this Project
CE 3.4.1 Overviewing of this work
I have understood about the concepts of IoT and IDS. I have deployed the Instrusion
Detection System with Canary Tokens on the client side for successfully checking any type
of breach within the server.
I decided to check the process once and finally, I was able to identify the issue. I had
to update the SD card in the beginning and then for using the camera, I checked that I have to
use a recent OS for making the camera existing. The most significant way for this purpose is
to obtain the last Raspbian image from the RaspberryPi.org website as well as make a fresh
SD card.
CE 3.3.5 Plan made to give innovative as well as creative works
I took the decision to research properly about Raspberry Pi and Cayenne Setup. Since,
the tasks were segregated amongst all the team members equally, the entire process did not
take up longer time period.
CE 3.3.6 Work Collaborations
I completed the work after collaborating with the group leader and three other
members. For ensuring collaboration, our group leader had arranged project meetings every
week.
CE 3.4 Overall Reviewing of this Project
CE 3.4.1 Overviewing of this work
I have understood about the concepts of IoT and IDS. I have deployed the Instrusion
Detection System with Canary Tokens on the client side for successfully checking any type
of breach within the server.
CE 3.4.2 My Major Contributions
I had to provide a proper designing to the IDS, which has resemblance to the IoT
device. The issues related to lack of cryptographic protocols were being resolved properly
and security was ensured majorly.
I had to provide a proper designing to the IDS, which has resemblance to the IoT
device. The issues related to lack of cryptographic protocols were being resolved properly
and security was ensured majorly.
1 out of 10
Related Documents
Your All-in-One AI-Powered Toolkit for Academic Success.
+13062052269
info@desklib.com
Available 24*7 on WhatsApp / Email
![[object Object]](/_next/static/media/star-bottom.7253800d.svg)
Unlock your academic potential
© 2024 | Zucol Services PVT LTD | All rights reserved.




